Understanding Cybersecurity Threats: Lessons from the Stryker Cyberattack [2025]
In today's interconnected digital landscape, cybersecurity threats have become a pressing concern for organizations worldwide. The recent cyberattack on Stryker, a leading medtech company, serves as a stark reminder of the vulnerabilities inherent in even the most fortified networks. This article delves into the Stryker incident, exploring the nuances of cyber threats, the implications of the attack, and strategies for fortifying defenses against similar threats.
TL; DR
- Cybersecurity threats are evolving, with attackers employing sophisticated tactics to breach systems. According to a report by Cybersecurity Dive, the threat level from Iranian hackers has increased significantly, affecting U.S. allies.
- The Stryker attack highlights vulnerabilities in global networks, emphasizing the need for robust security measures. The Irish Examiner reported that the attack had far-reaching implications for healthcare systems worldwide.
- Organizations must adopt proactive strategies to mitigate risks and protect sensitive data. Insights from San Diego Business Journal suggest that AI can play a crucial role in mitigating cybersecurity risks.
- Regular updates and employee training are crucial in maintaining a secure environment. The importance of patch management is emphasized in a Channel Insider article discussing managed services.
- Future trends in cybersecurity point towards increased automation and AI-driven defenses. A Qualys blog post highlights how AI is being leveraged to enhance cybersecurity measures.

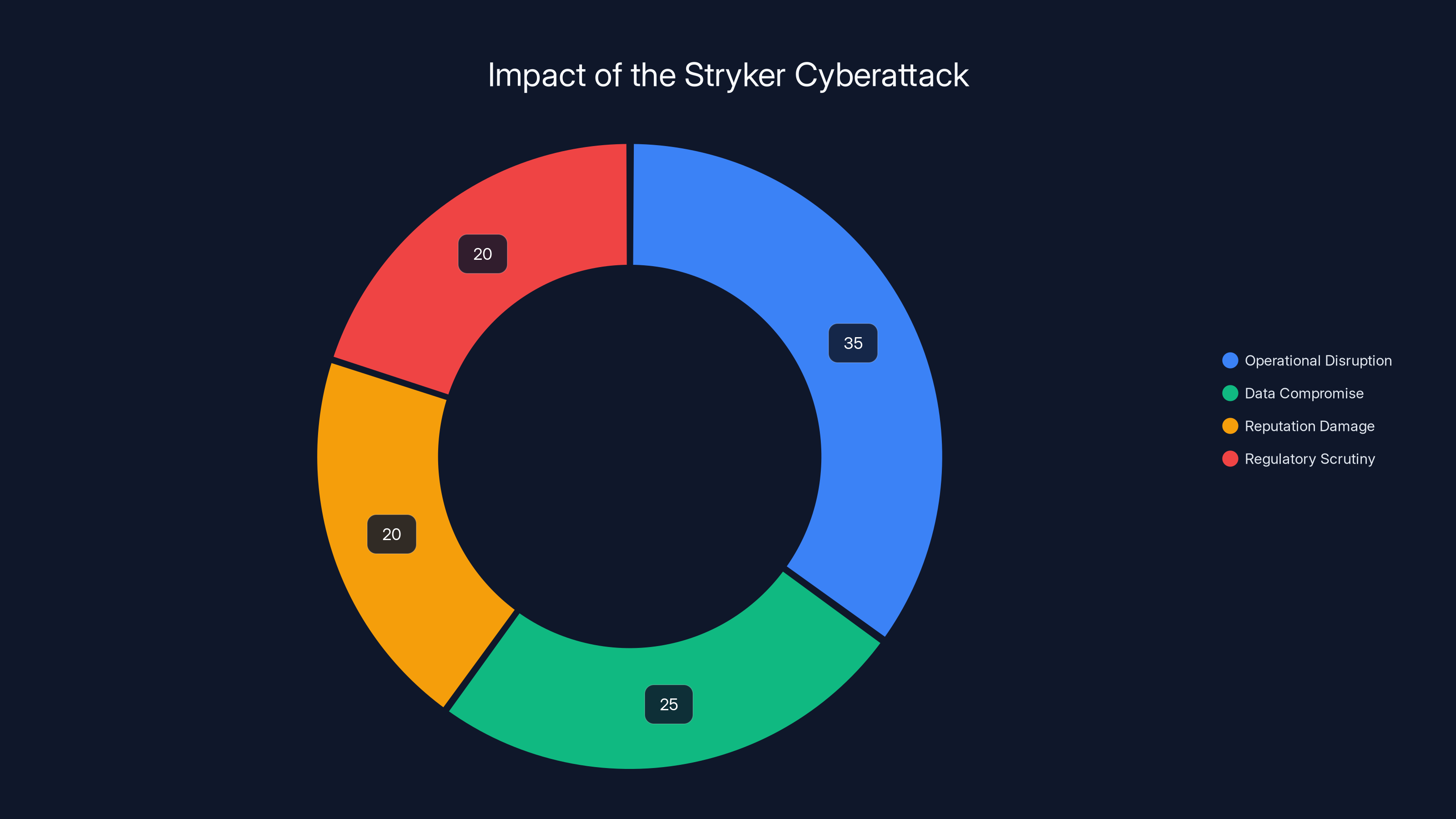
The Stryker cyberattack had a significant impact, with operational disruption being the largest consequence, followed by data compromise and reputation damage. (Estimated data)
The Stryker Incident: A Wake-Up Call
The cyberattack on Stryker unfolded as a well-coordinated operation allegedly orchestrated by the Iranian-linked Handala group. This incident resulted in the theft of a staggering 50 terabytes of data and the disruption of over 200,000 systems globally. The attack not only compromised sensitive information but also crippled Stryker's operations, forcing a revert to manual processes. According to WION News, the attack had severe implications for millions of patients worldwide.
Anatomy of the Attack
The nature of the attack suggests a multi-faceted approach, combining several tactics to penetrate Stryker's defenses. Key elements included:
- Phishing Campaigns: Attackers often initiate breaches via phishing, tricking employees into divulging credentials.
- Exploiting Vulnerabilities: Known software vulnerabilities were likely targeted to gain access to critical systems. The SentinelOne report on cloud security trends underscores the importance of addressing these vulnerabilities.
- Data Exfiltration: Once inside, attackers extracted vast amounts of data, leveraging automated tools.
Impact and Consequences
The ramifications of the Stryker breach extend beyond immediate operational disruptions. This incident:
- Compromised sensitive data, including patient records and proprietary technology. The HIPAA Journal provides statistics on healthcare data breaches, highlighting the scale of such incidents.
- Eroded trust among stakeholders, impacting market reputation. According to Irish Mirror, the attack led to significant concerns among stakeholders.
- Triggered regulatory scrutiny, necessitating a comprehensive response plan.
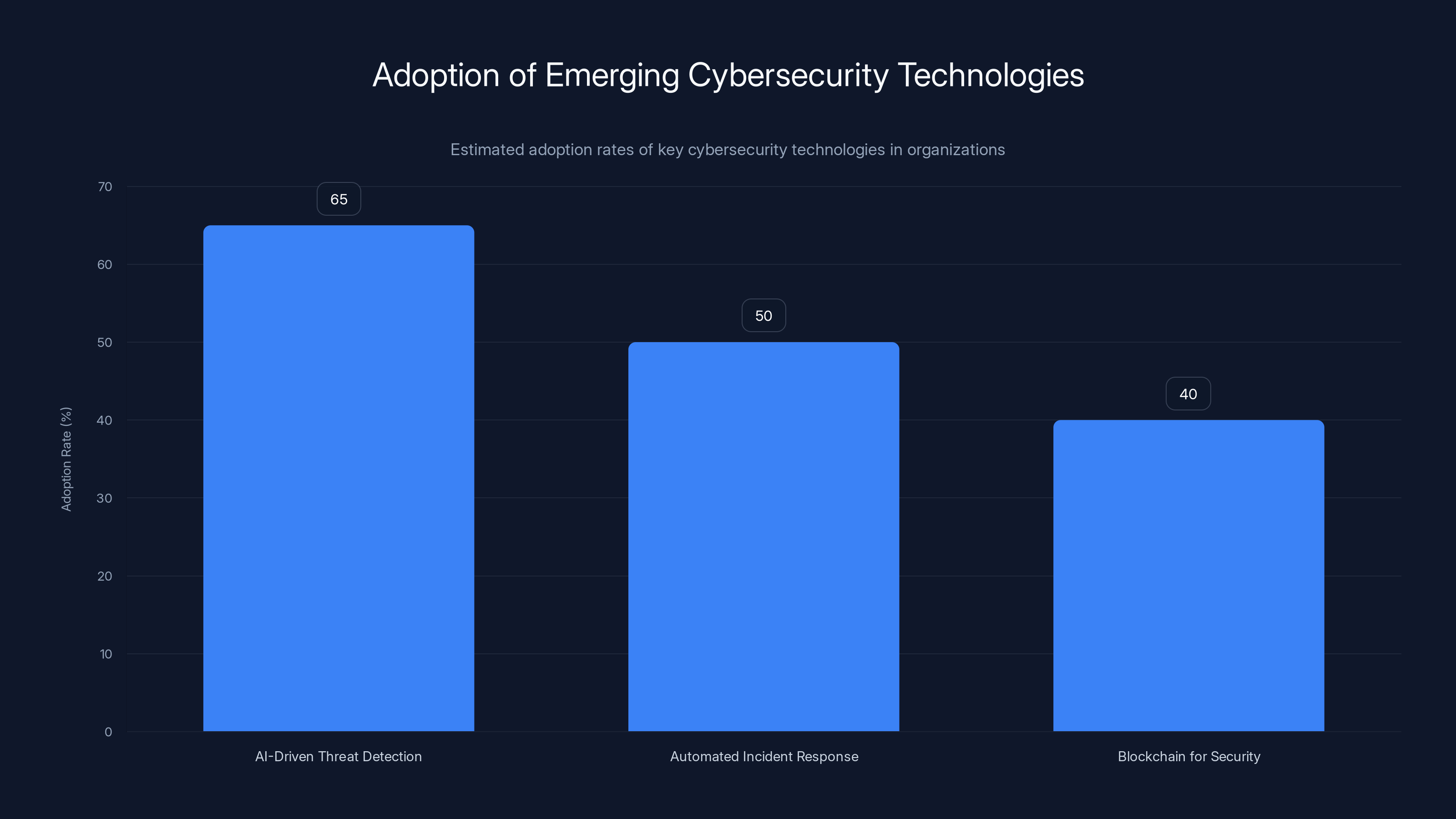
Estimated data shows AI-driven threat detection is leading in adoption, with 65% of organizations implementing it, followed by automated incident response at 50%, and blockchain for security at 40%.
Common Cybersecurity Pitfalls
Organizations often fall prey to cyberattacks due to a combination of technical and human factors. Some common pitfalls include:
- Inadequate Patch Management: Failing to update systems regularly leaves vulnerabilities exposed. As noted by Channel Insider, effective patch management is crucial for cybersecurity.
- Weak Password Policies: Simple or reused passwords make unauthorized access easy.
- Lack of Employee Training: Uninformed staff are more susceptible to phishing schemes.
Best Practices for Cyber Defense
To safeguard against attacks like the one on Stryker, organizations should adopt a multi-layered defense strategy:
- Conduct Regular Security Audits: Identify and address vulnerabilities before they can be exploited.
- Implement Strong Authentication: Use multi-factor authentication (MFA) to enhance security.
- Educate Employees: Regular training sessions can help employees recognize and avoid phishing attempts.
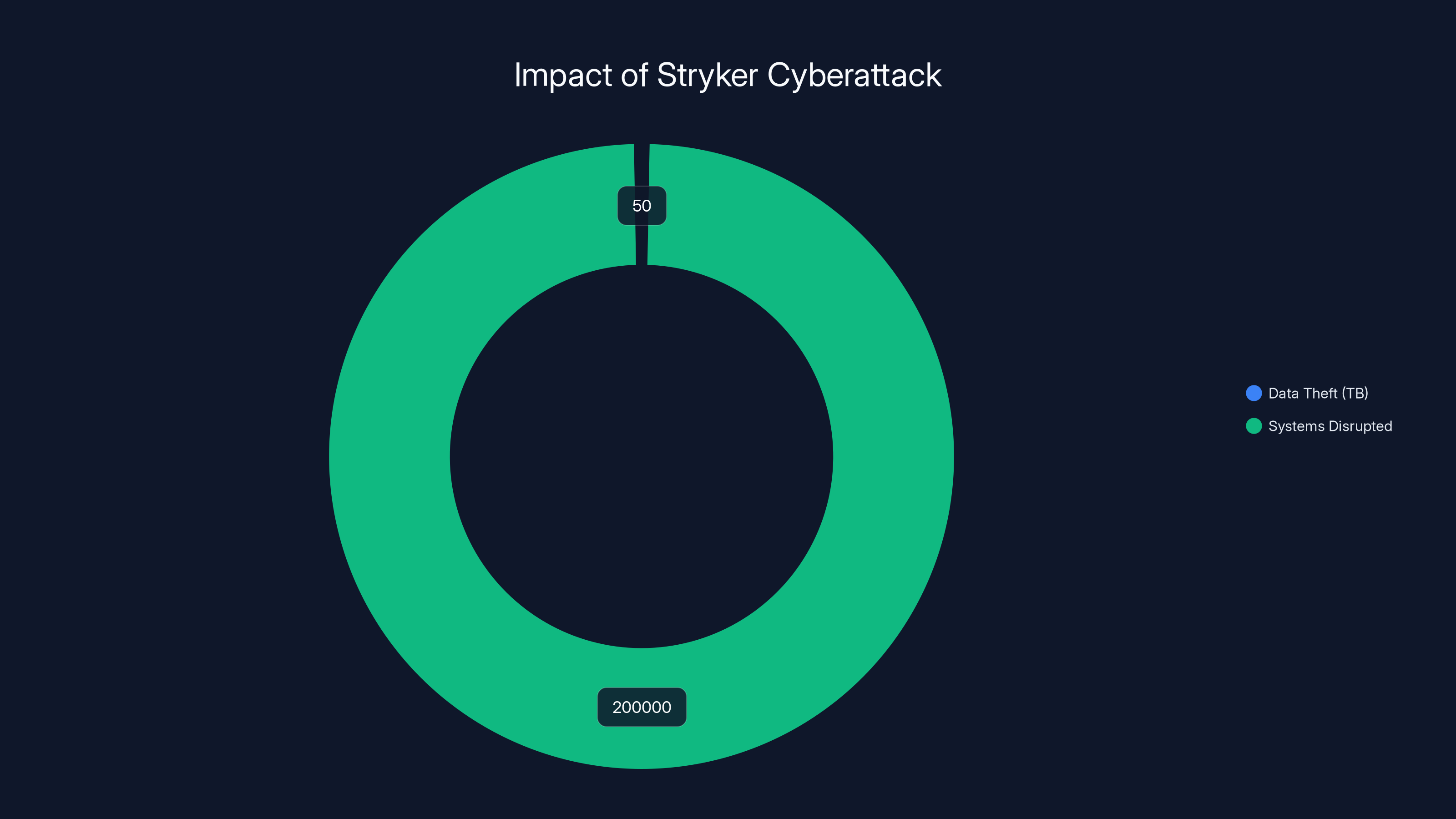
The Stryker cyberattack resulted in the theft of 50 terabytes of data and disrupted over 200,000 systems worldwide, highlighting the severe impact on operations and trust.
Future Trends and Recommendations
The cybersecurity landscape is continuously evolving, with emerging technologies offering new opportunities and challenges. Key trends include:
- AI-Driven Threat Detection: Machine learning algorithms can analyze patterns to identify potential threats in real-time. As discussed in the Qualys blog, AI is increasingly being used to enhance threat detection capabilities.
- Automated Incident Response: Automation streamlines response times, minimizing damage during an attack.
- Blockchain for Security: Blockchain technology offers a decentralized approach to securing data transactions.

Conclusion
The Stryker cyberattack serves as a potent reminder of the ever-present threats in our digital world. By understanding the intricacies of such attacks and adopting proactive defense strategies, organizations can better protect their assets and maintain operational integrity. As cybersecurity threats continue to evolve, staying informed and prepared is crucial for resilience.
FAQ
What was the impact of the Stryker cyberattack?
The Stryker cyberattack led to the theft of 50 terabytes of data and the disruption of over 200,000 systems globally, affecting operations and stakeholder trust. This was extensively covered in the WION News.
How can organizations protect against similar attacks?
Implementing strong authentication, conducting regular security audits, and educating employees on cybersecurity best practices are key defensive measures. Insights from San Diego Business Journal emphasize these strategies.
What are the emerging trends in cybersecurity?
AI-driven threat detection, automated incident response, and blockchain technology are among the leading trends shaping the future of cybersecurity, as noted in the Qualys blog.
Why is employee training important in cybersecurity?
Trained employees are better equipped to identify phishing attempts and other threats, reducing the risk of unauthorized access.
How does AI contribute to cybersecurity?
AI algorithms can analyze vast amounts of data to detect anomalies and potential threats, enabling real-time threat detection and response.
What is the significance of a zero-trust architecture?
A zero-trust architecture minimizes the risk of unauthorized access by requiring verification for every access attempt, regardless of location.
How does blockchain enhance security?
Blockchain offers a decentralized approach to securing data transactions, reducing the risk of tampering and fraud.
What role does automation play in incident response?
Automation streamlines incident response processes, allowing for faster detection and mitigation of threats, thereby minimizing potential damage.
Why is patch management critical in cybersecurity?
Regular patch management addresses known vulnerabilities, preventing attackers from exploiting outdated software to gain access to systems, as emphasized in the Channel Insider article.
How can multi-factor authentication improve security?
Multi-factor authentication adds an additional layer of security by requiring more than one form of verification to access systems, making unauthorized access more difficult.

Key Takeaways
- Cybersecurity threats are evolving, with sophisticated tactics being used to penetrate systems.
- The Stryker attack exposed vulnerabilities in global networks, necessitating robust security measures.
- Proactive strategies, including regular updates and employee training, are crucial for maintaining security.
- Emerging trends in cybersecurity feature increased automation and AI-driven defenses.
- Organizations must adopt a zero-trust architecture to minimize unauthorized access.
Related Articles
- Ericsson Data Breach: Analysis and Strategies [2025]
- Asus Routers Hijacked to Power a Cybercrime Proxy Network: What We Know [2025]
- Securing 6G Networks: Global Efforts and Future Trends [2025]
- The Evolution of Dark Web Monitoring: From Google's Exit to NordVPN’s Latest Innovations [2025]
- The Rise of KadNap: Understanding and Combating a Resilient Router Botnet [2025]
- WhatsApp Introduces Parent-Linked Accounts for Pre-Teens: A Comprehensive Guide [2025]
![Understanding Cybersecurity Threats: Lessons from the Stryker Cyberattack [2025]](https://tryrunable.com/blog/understanding-cybersecurity-threats-lessons-from-the-stryker/image-1-1773322519764.jpg)



