Defend Your Enterprise from the Shai-Hulud Worm and npm Vulnerability: 6 Actionable Steps [2025]
In the fast-paced world of software development, security threats are ever-evolving. One of the latest, most concerning threats is the Shai-Hulud worm and its associated npm vulnerability. This malicious code has the potential to wreak havoc on development environments, harvesting sensitive credentials and installing itself persistently across systems. In this comprehensive guide, we'll explore six actionable steps to fortify your enterprise against this threat.
TL; DR
- Immediate Action: Identify and remediate all systems affected by compromised npm or Py PI packages.
- Credential Management: Implement robust credential storage and regularly rotate keys and tokens.
- Code Integrity: Utilize code signing and verification to ensure source authenticity.
- Monitoring and Alerts: Deploy advanced monitoring tools to detect unusual activities.
- User Education: Train your employees on the latest security practices and vulnerabilities.
- Future Readiness: Prepare for evolving threats with continuous security audits and updates.

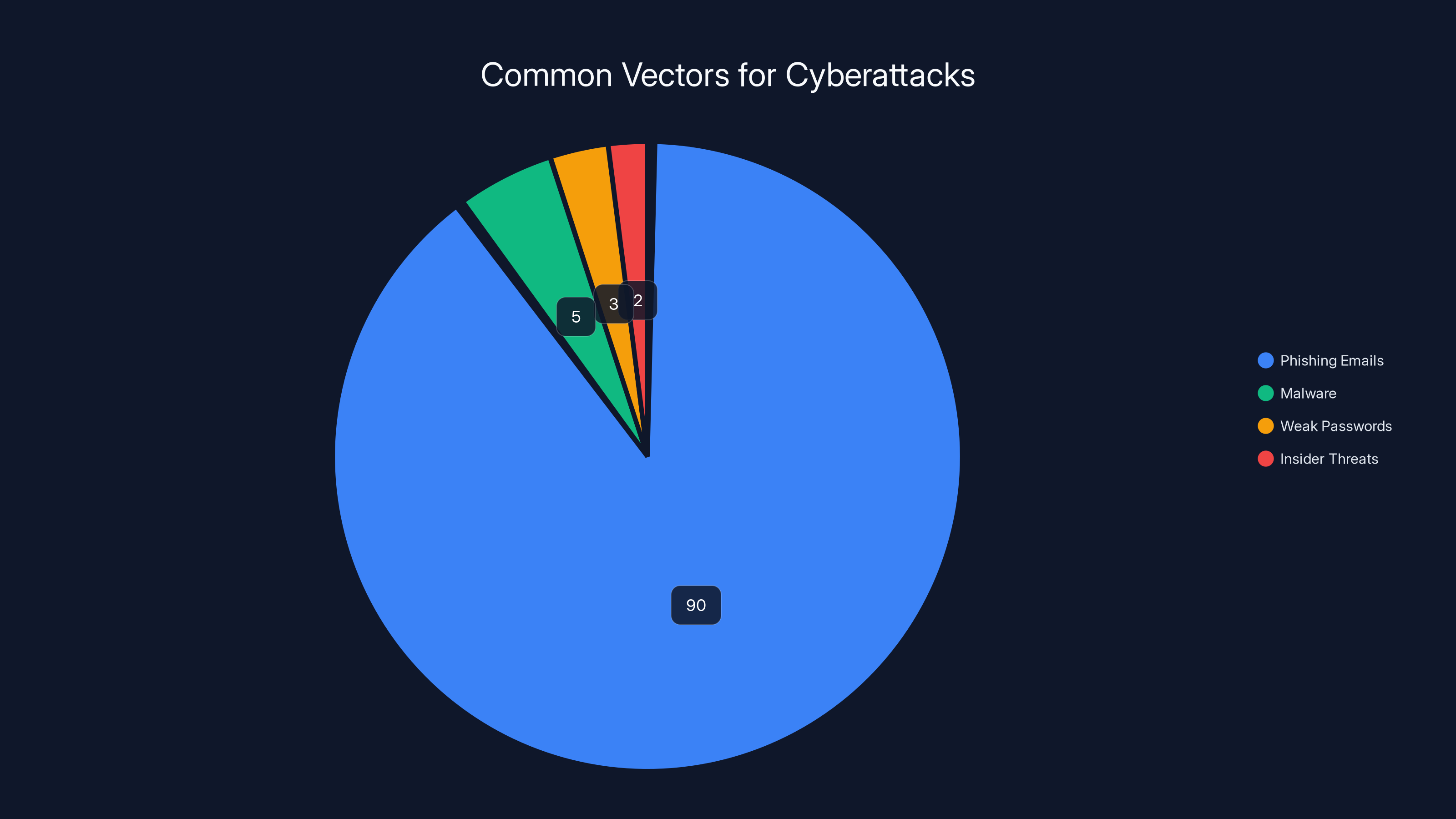
Phishing emails account for over 90% of cyberattacks, underscoring the need for robust security awareness training. (Estimated data)
Understanding the Shai-Hulud Worm and npm Vulnerability
The Shai-Hulud worm is a sophisticated piece of malware that primarily targets development environments. Its primary strategy involves exploiting vulnerabilities in npm and Py PI packages to infiltrate systems. Once inside, it seeks out credentials from over 100 file paths, including AWS keys, SSH private keys, and GitHub PATs.
What Makes Shai-Hulud Dangerous?
Shai-Hulud is particularly dangerous because it targets a wide array of sensitive information. From AWS keys to cryptocurrency wallets, the worm's reach is extensive. Moreover, it marks the first time password managers like 1Password and Bitwarden have been targeted in a Team PCP campaign. The worm doesn't just leave when a compromised package is removed; it establishes persistence, making eradication more challenging.
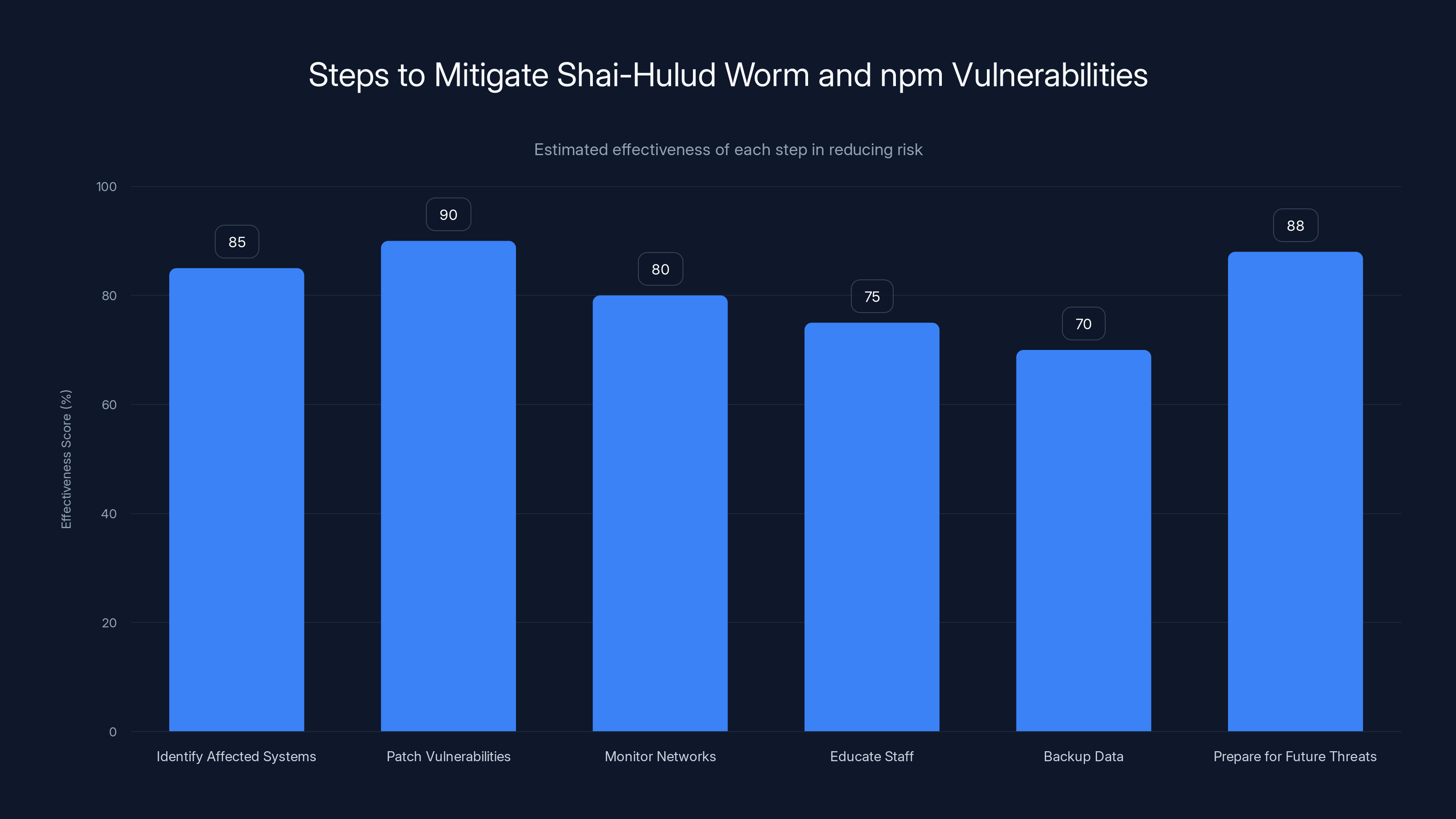
Estimated data shows that patching vulnerabilities and preparing for future threats are the most effective steps in reducing risk from Shai-Hulud worm and npm vulnerabilities.
Step 1: Identify and Remediate Affected Systems
The first step in defending against the Shai-Hulud worm is to identify which systems have been compromised. This involves scanning all development environments that have installed the affected npm or Py PI packages since May 11.
Tools for Detection
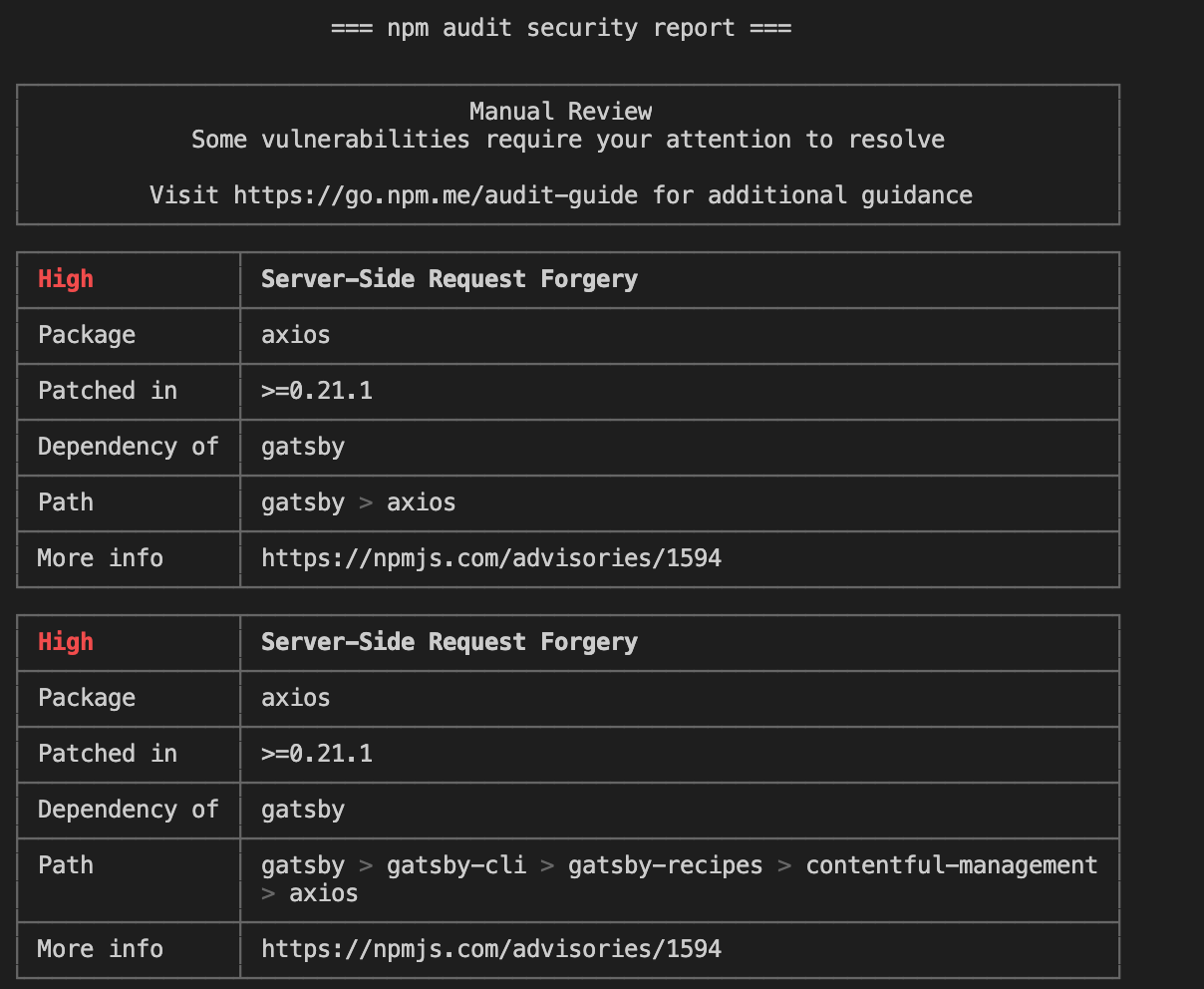
- npm audit: Use this tool to scan for vulnerabilities in your npm packages.
- Py PI security checks: Regularly check for known vulnerabilities in Python packages.
Once identified, remove the compromised packages and any associated persistence files. This may include cleaning up configuration files such as .claude/settings.json and .vscode/settings.json.
Step 2: Strengthen Credential Management
Shai-Hulud's primary goal is to harvest credentials. To counteract this, enterprises must bolster their credential management practices.
Best Practices
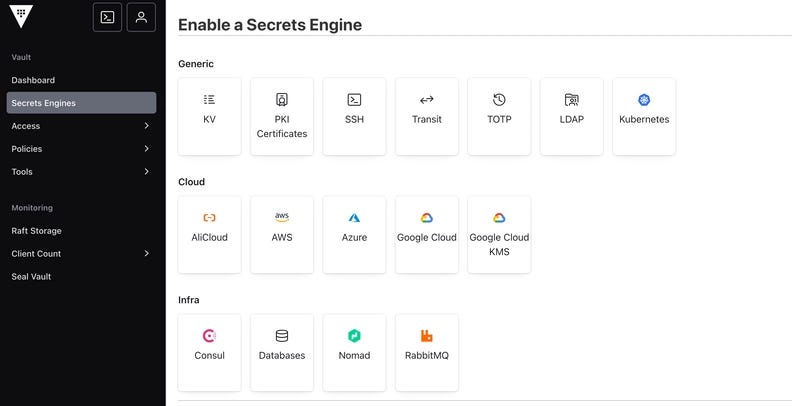
- Use a Credential Management Tool: Tools like HashiCorp Vault can securely store and manage access to sensitive data.
- Regularly Rotate Keys: Implement policies to rotate keys and tokens frequently to minimize exposure.
- Adopt Multi-Factor Authentication (MFA): Require MFA for accessing critical systems and services.
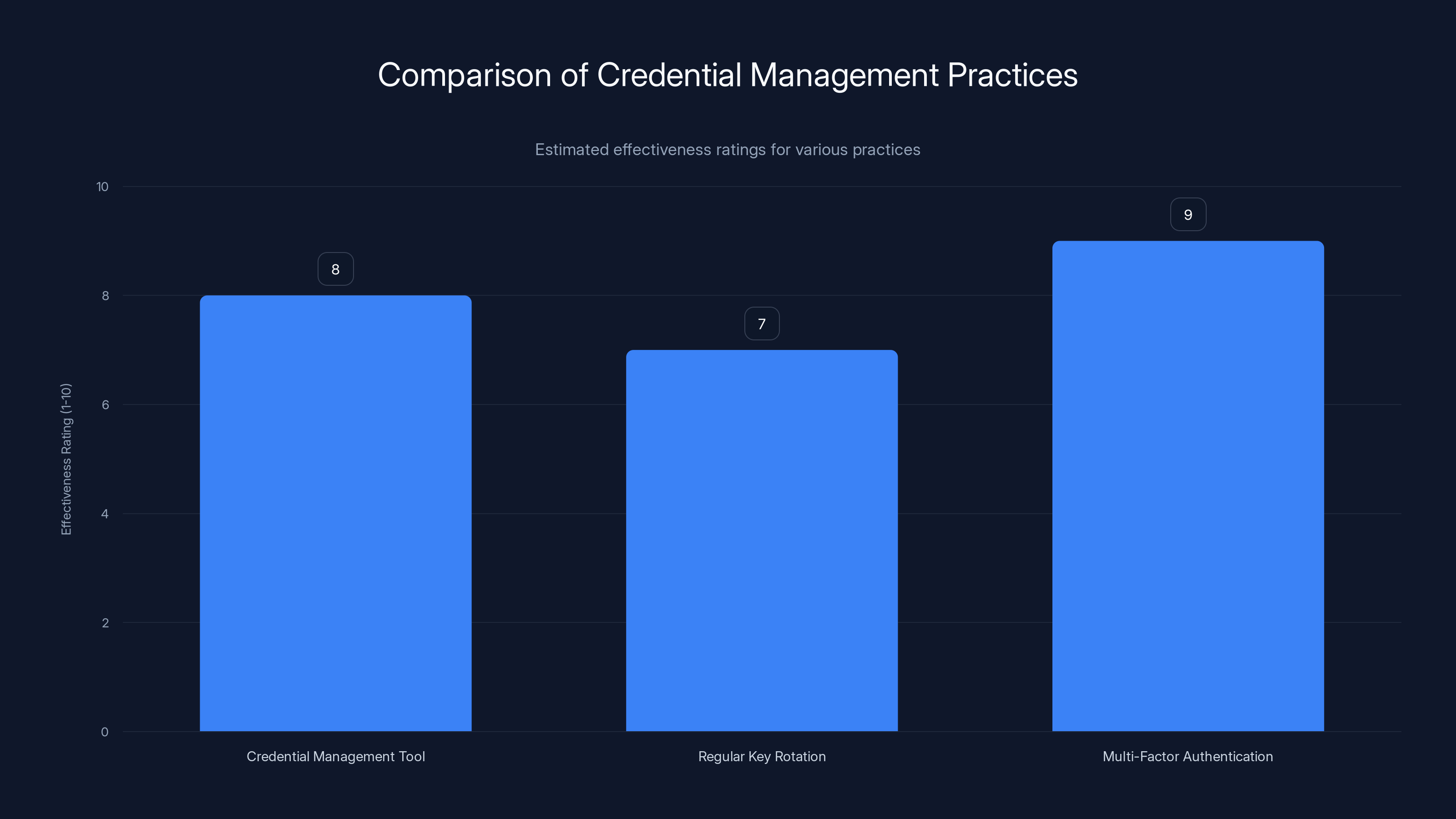
Multi-Factor Authentication (MFA) is rated as the most effective practice for strengthening credential management, followed closely by using a credential management tool. Estimated data.
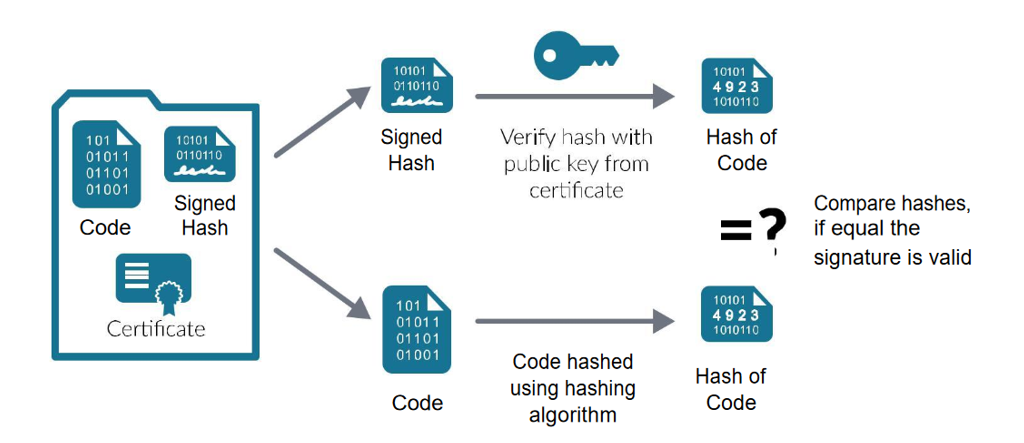
Step 3: Ensure Code Integrity
Ensuring the integrity of your code is crucial in preventing unauthorized changes and backdoors.
Implementation Strategies
- Code Signing: Sign your code to verify its origin and integrity.
- Continuous Integration (CI) Security Checks: Incorporate security checks into your CI pipeline to catch vulnerabilities early.
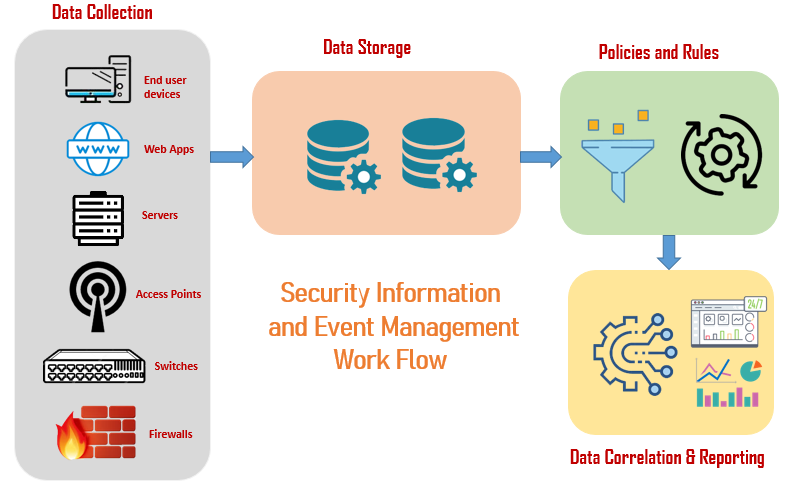
Step 4: Deploy Advanced Monitoring and Alerts
Monitoring your systems for unusual activity is a proactive way to detect and respond to threats quickly.
Recommended Tools
- SIEM (Security Information and Event Management): Tools like Splunk or LogRhythm can centralize logs and detect anomalies.
- Network Intrusion Detection Systems (NIDS): Deploy NIDS to monitor network traffic for suspicious activities.
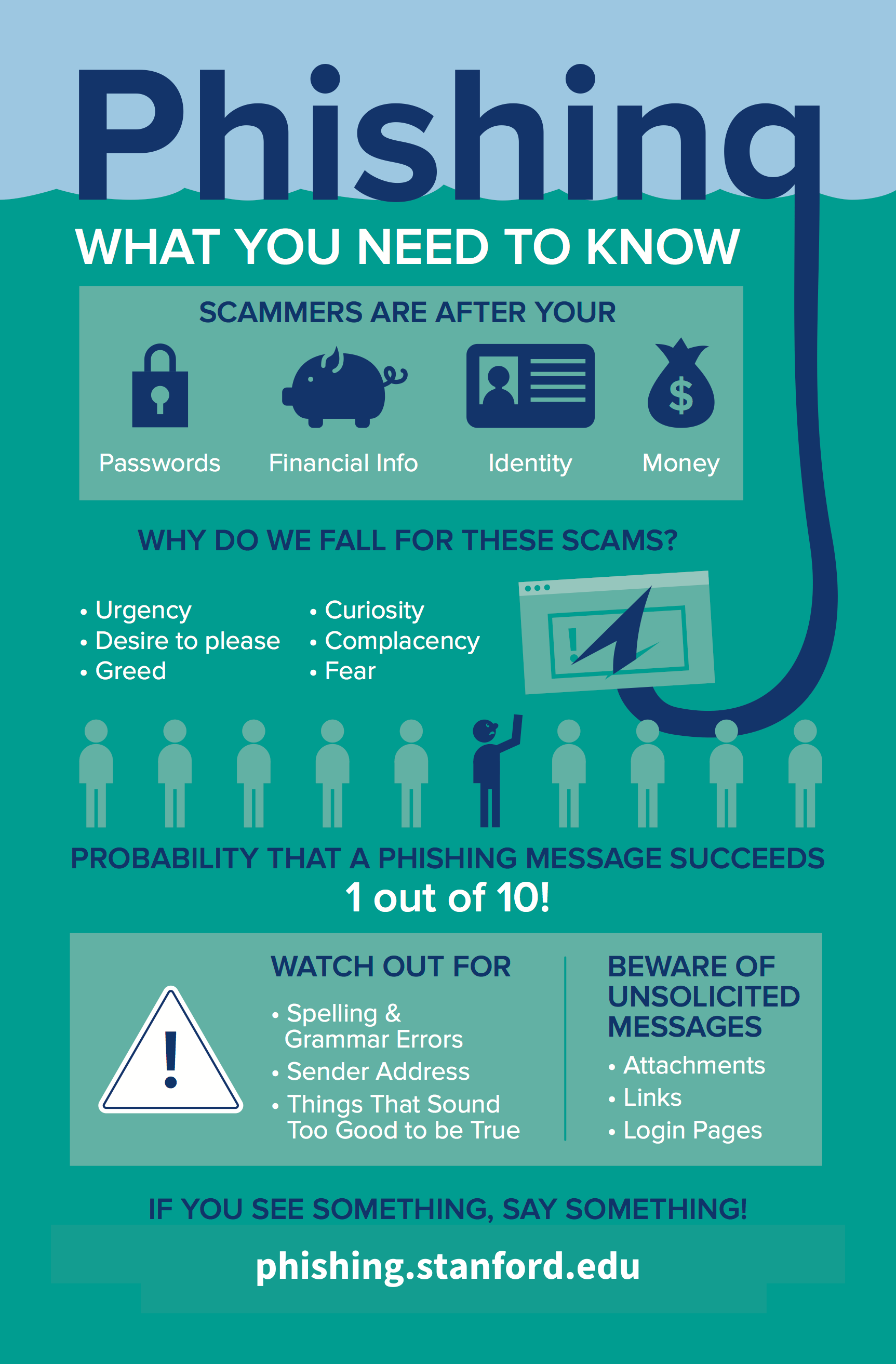
Step 5: Educate Your Workforce
Human error remains a significant vector for security breaches. Educating your workforce is vital in creating a security-conscious culture.
Training Focus
- Phishing Awareness: Conduct regular training on recognizing and reporting phishing attempts.
- Security Best Practices: Teach employees about secure coding practices and the importance of software updates.
Step 6: Prepare for Future Threats
The landscape of cybersecurity threats is constantly evolving. Staying ahead requires continuous vigilance and adaptation.
Future-Proofing Strategies
- Regular Security Audits: Conduct audits to identify and address vulnerabilities before they are exploited.
- Patch Management: Keep software and systems up-to-date with the latest security patches.
- Threat Intelligence: Leverage threat intelligence to anticipate and mitigate potential threats.
Conclusion
Defending against the Shai-Hulud worm and npm vulnerabilities requires a multifaceted approach. By following these six actionable steps, enterprises can significantly reduce their risk of compromise. From identifying affected systems to preparing for future threats, each step is crucial in maintaining a robust security posture.
Use Case: Automate your security audits with AI-powered tools from Runable, ensuring consistent and thorough vulnerability checks.
Try Runable For Free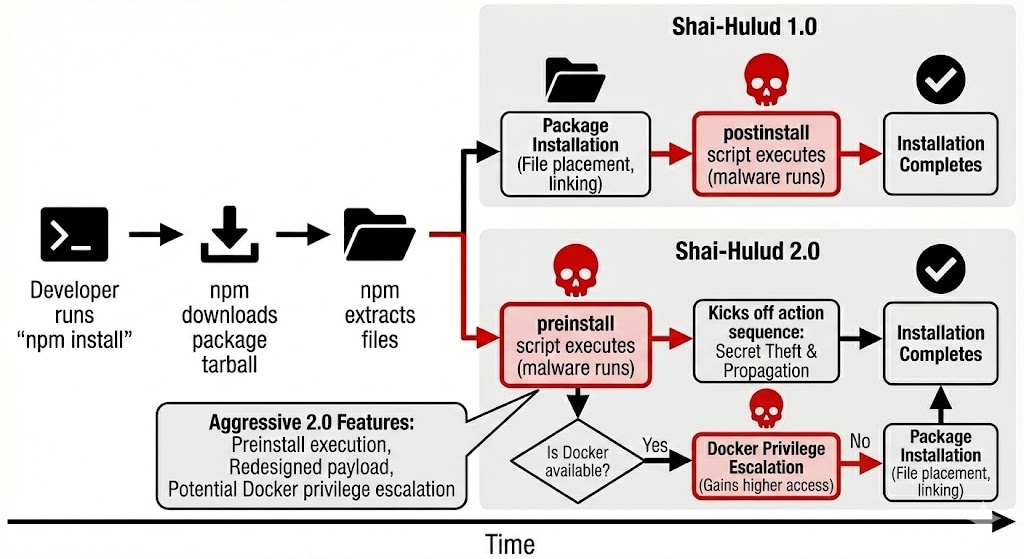
FAQ
What is the Shai-Hulud worm?
The Shai-Hulud worm is a sophisticated piece of malware targeting development environments by exploiting npm and Py PI package vulnerabilities to harvest credentials and install persistence.
How does the Shai-Hulud worm infiltrate systems?
It infiltrates systems by exploiting vulnerabilities in compromised npm or Py PI packages, allowing it to access sensitive information and establish persistence.
What are the risks associated with npm vulnerabilities?
npm vulnerabilities can lead to unauthorized access to sensitive data, system compromises, and the introduction of persistent malware like the Shai-Hulud worm.
How can enterprises protect against these threats?
By implementing strong credential management, ensuring code integrity, deploying monitoring tools, educating employees, and preparing for evolving threats.
Why is employee education important in cybersecurity?
Employees can be a weak link in security. Educating them on best practices and threat recognition can significantly reduce the risk of cyberattacks.
How can advanced monitoring tools help?
They can detect unusual activities quickly, allowing for a rapid response to potential threats and minimizing damage.
What role do security audits play?
Regular security audits help identify vulnerabilities, ensuring they are addressed before they can be exploited by attackers.
Key Takeaways
- Identify and remove compromised packages immediately to stop the spread of the worm.
- Implement robust credential management systems to protect sensitive data.
- Use code signing and continuous integration checks to maintain code integrity.
- Deploy advanced monitoring tools to detect and respond quickly to threats.
- Educate employees on security best practices to prevent human error vulnerabilities.
- Conduct regular security audits and stay updated on the latest threats.
Related Articles
- Why Intelligence and Investigative Capability are Essential to Enterprise Security [2025]
- The Future of Data: Google and SpaceX's Plan to Launch Data Centers into Orbit [2025]
- Understanding the Security Implications of Running Claude Code in Chrome [2025]
- Google's Landmark Discovery: AI-Generated Zero-Day Exploit [2025]
- AI Agents in Healthcare and Manufacturing: Overcoming Enterprise IAM Challenges [2025]
- Smartphone Security Risks and Solutions [2025]
![Defend Your Enterprise from the Shai-Hulud Worm and npm Vulnerability: 6 Actionable Steps [2025]](https://tryrunable.com/blog/defend-your-enterprise-from-the-shai-hulud-worm-and-npm-vuln/image-1-1778612775179.png)



