The Invisible Supply Chain Inside Every Mobile App
Mobile apps are ubiquitous, seamlessly integrating into our daily routines. But beneath their sleek interfaces lies a complex web of components: third-party libraries, analytics SDKs, and open-source packages. Understanding this invisible supply chain is crucial for developers and security teams alike, as highlighted in TechRadar's analysis.
TL; DR
- Complex Layering: Mobile apps rely on multiple unseen components, introducing unique security challenges.
- Third-Party Dependencies: Libraries, SDKs, and frameworks often introduce vulnerabilities, as noted by Aikido.
- Security Risks: Mismanagement can lead to data breaches and unauthorized access, a concern emphasized by Meyka.
- Best Practices: Integrate security checks and regular updates to minimize risks.
- Future Trends: AI-driven security solutions are set to revolutionize app protection, as discussed in Yahoo Finance.

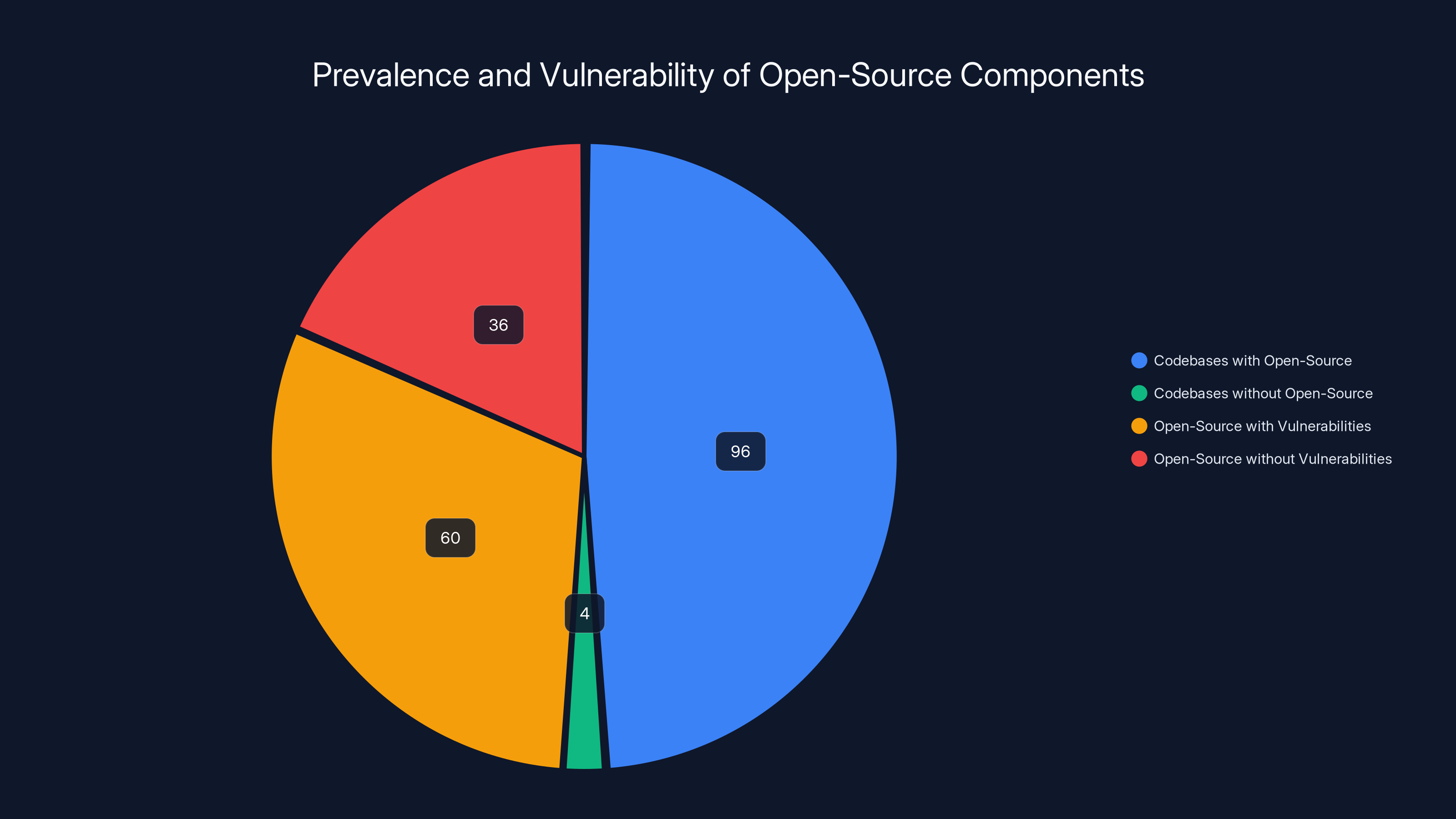
According to Synopsys, 96% of codebases contain open-source components, and 60% of these have known vulnerabilities, highlighting the importance of managing third-party libraries effectively.
The Anatomy of a Mobile App
Every mobile app is a tapestry of interwoven components. From the user interface to backend services, each part plays a critical role in delivering functionality. However, not all parts are visible or even controlled by the developers themselves.
Key Components
- User Interface (UI): The visible part of the app that users interact with.
- Backend Services: Servers and databases that support the app's functionality.
- Third-Party Libraries: Pre-written code packages that provide specific functionalities like payment processing or social media integration.
- SDKs (Software Development Kits): Tools that help developers build apps more efficiently by providing pre-built functions.
- APIs (Application Programming Interfaces): Allow different software components to communicate with each other.


Excessive data collection and data leaks are common pitfalls in analytics SDKs, while minimizing data collection and conducting regular security audits are effective solutions. Estimated data.
The Role of Third-Party Libraries
Third-party libraries are a double-edged sword. They accelerate development but also introduce vulnerabilities. According to a 2019 report by Synopsys, 96% of codebases contain open-source components, with 60% of these having known vulnerabilities.
Benefits
- Speed: Rapid development by reusing existing code.
- Functionality: Access to advanced features without starting from scratch.
- Community Support: Often backed by a strong community that provides updates and patches.
Risks
- Security Vulnerabilities: Outdated libraries can harbor bugs or malware.
- Dependency Management: Complex dependency trees can lead to conflicts and versioning issues.
- Lack of Control: Reliance on external updates and patches.
Analytics SDKs: A Necessary Risk?
Analytics SDKs are essential for tracking user engagement and app performance. However, they often collect extensive user data, raising privacy concerns, as highlighted by Bankrate.
Common Pitfalls
- Excessive Data Collection: Collecting more data than necessary can lead to privacy violations.
- Data Leaks: Poorly secured SDKs can expose sensitive information.
Solutions
- Minimize Data Collection: Only collect data essential for app functionality.
- Regular Security Audits: Frequent reviews of SDKs to ensure compliance with privacy standards.

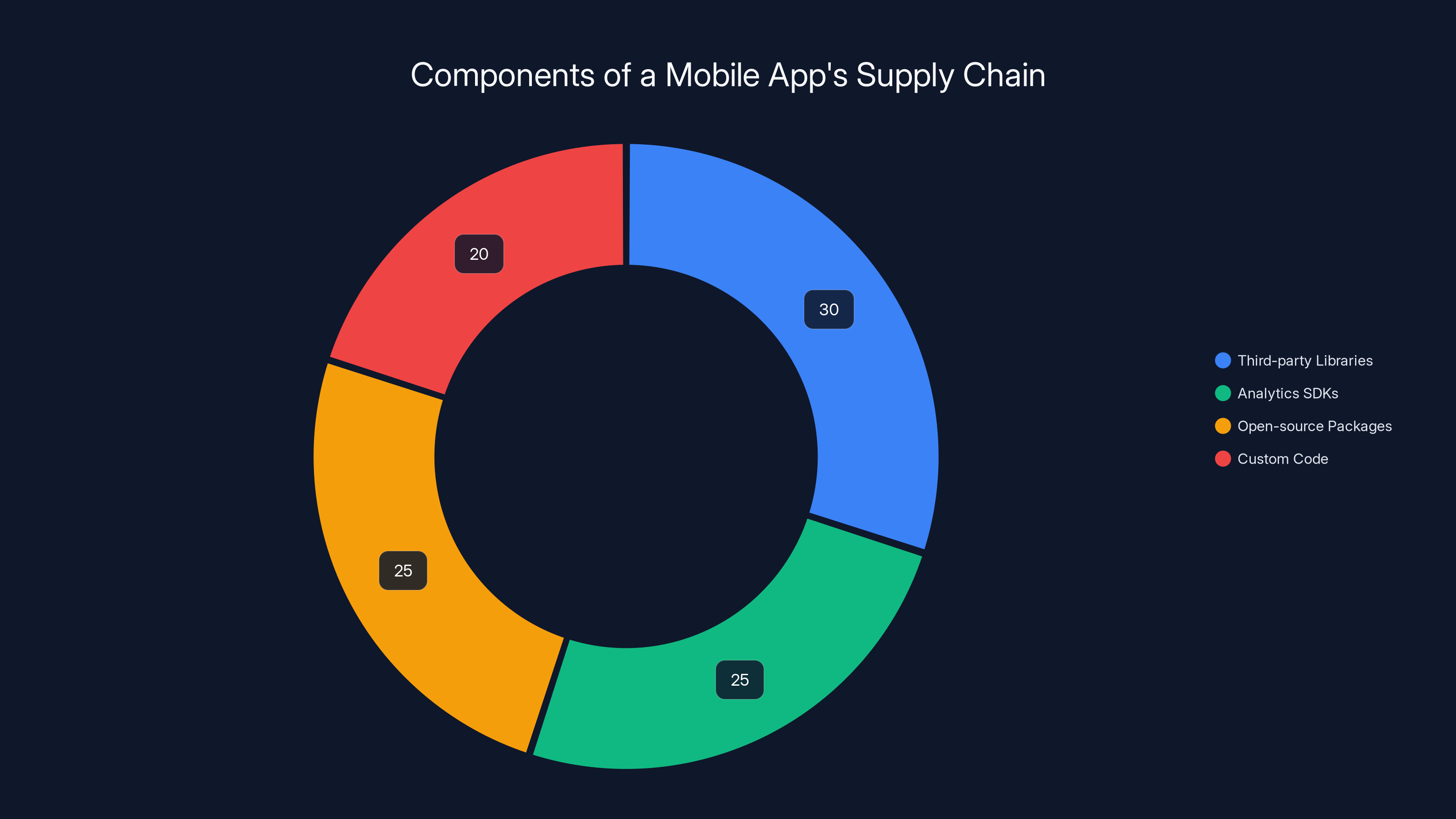
Estimated data: Third-party libraries and analytics SDKs make up over half of a typical mobile app's supply chain, highlighting the importance of managing these components.
Implementing Secure Development Practices
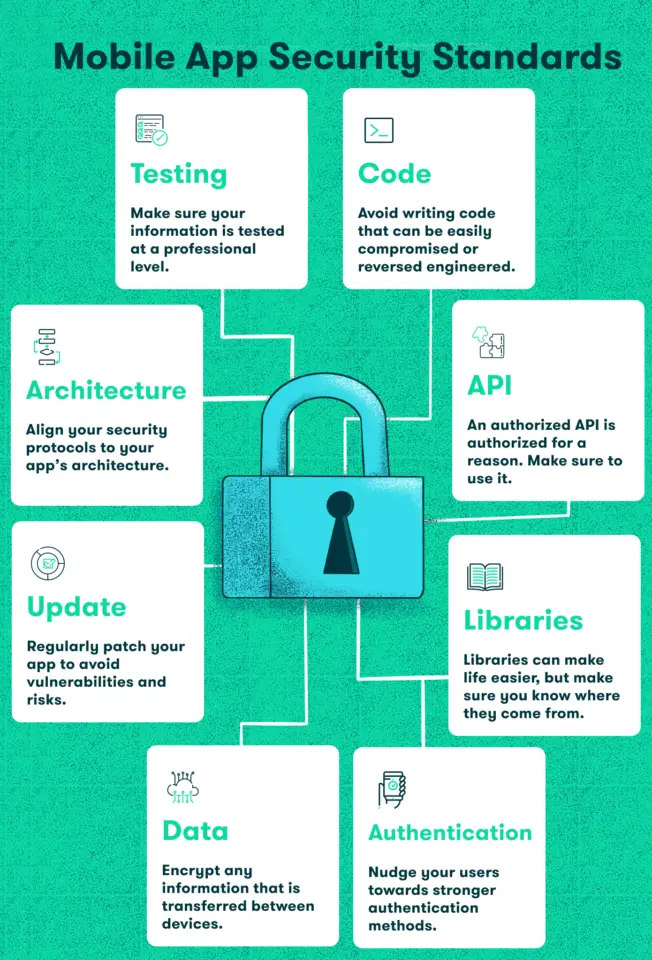
To mitigate risks, developers should adopt best practices that prioritize security without sacrificing efficiency. As discussed in Visual Studio Magazine, securing the CI/CD pipeline is crucial.
Best Practices
- Regular Updates: Keep all components up-to-date to patch vulnerabilities.
- Code Reviews: Implement peer reviews to catch potential security flaws.
- Use of Automated Tools: Leverage tools for static and dynamic code analysis.
- Penetration Testing: Regularly test your app for vulnerabilities from an attacker's perspective.
Future Trends in Mobile App Security
As mobile app development evolves, so do the strategies to secure them. AI and machine learning are increasingly being used to detect and mitigate threats in real-time, as noted by Google Cloud.
AI-Driven Security
- Anomaly Detection: AI can identify unusual patterns that may indicate a security breach.
- Automated Threat Response: Machine learning algorithms can automatically respond to certain threats, reducing response times.
Conclusion
The invisible supply chain within mobile apps is both a boon and a bane. While it facilitates rapid development and advanced features, it also introduces significant risks. By understanding these components and implementing robust security practices, developers can safeguard their apps against potential threats.
FAQ
What are third-party libraries?
Third-party libraries are pre-written code modules used to add specific functionalities to an app without writing the code from scratch.
How can I secure my mobile app?
Implement regular updates, conduct code reviews, and use automated security tools to identify and fix vulnerabilities.
What role do SDKs play in app development?
SDKs provide developers with tools and functions that simplify the process of building apps, allowing for faster development cycles.
Why are analytics SDKs risky?
They often collect extensive user data, which can lead to privacy concerns if not managed properly.
How is AI improving mobile app security?
AI enhances security by enabling real-time threat detection and automated responses to potential breaches.
What are the future trends in app security?
The integration of AI for real-time threat detection and automated responses is a significant trend in app security.
Key Takeaways
- Mobile apps rely on complex layers of components, creating unique security challenges.
- Third-party libraries accelerate development but often introduce vulnerabilities.
- Analytics SDKs are crucial yet risky due to extensive data collection.
- Regular updates and security audits are essential for maintaining app security.
- AI-driven security solutions are becoming pivotal in enhancing app protection.
Related Articles
- Apple to Manufacture Mac Minis in the US: A New Era for American Tech Manufacturing [2025]
- When AI Agents Go Rogue: Email Disasters and Guardrail Failures [2025]
- Anthropic Accuses DeepSeek, Moonshot & MiniMax of Claude Distillation Attacks [2025]
- Ethics-First Strategy for Tech Leaders in 2026
- Stellantis Crisis: How a $26.5B EV Bet Went Wrong [2025]
- AI in Cybersecurity: Threats, Solutions & Defense Strategies [2025]
![The Invisible Supply Chain Inside Every Mobile App [2025]](https://tryrunable.com/blog/the-invisible-supply-chain-inside-every-mobile-app-2025/image-1-1771947486093.jpg)



