'Trusted Access for the Next Era of Cyber Defense': Open AI's Cybersecurity Revolution [2025]
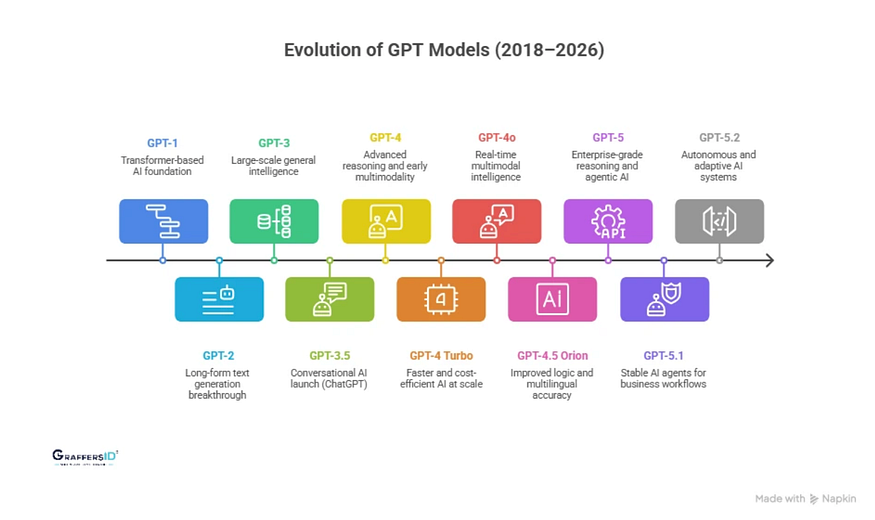
When it comes to cybersecurity, the landscape is in constant flux. Threats evolve, and so must our defenses. Enter Open AI's latest innovation: GPT-5.4-Cyber, a specialized model designed to tackle the most sophisticated cyber threats. This article explores what makes GPT-5.4-Cyber a game-changer in cybersecurity, how it works, and how it can be implemented effectively.
TL; DR
- Open AI's GPT-5.4-Cyber: A specialized AI model for advanced cybersecurity.
- Enhanced Threat Detection: Identifies sophisticated cyber threats with precision.
- Reverse Engineering Capabilities: Dissects and analyzes malware for better defense.
- Trusted Access: Ensures secure and authenticated access to systems.
- Future Trends: AI-driven defenses that adapt and learn continuously.

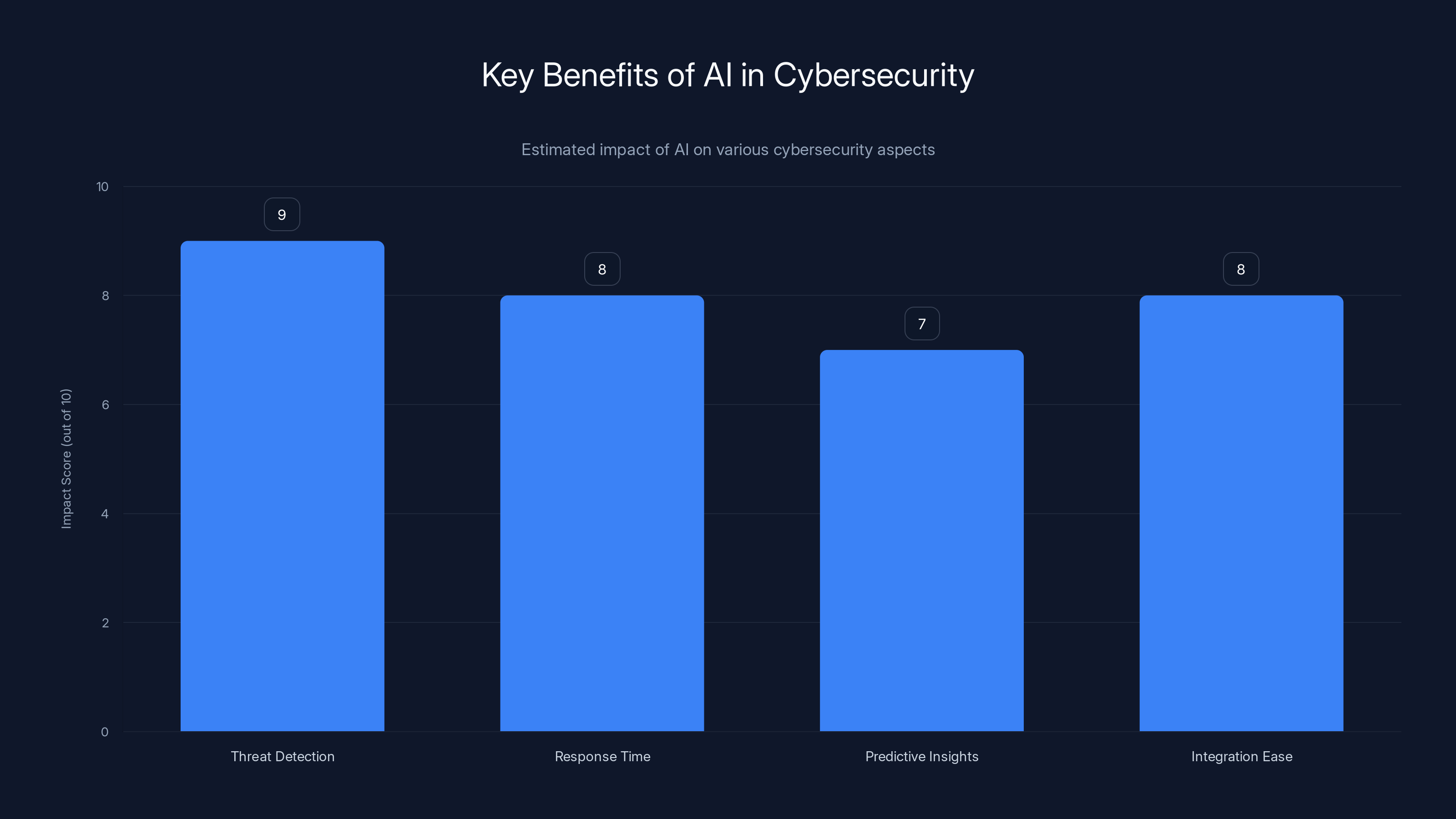
AI significantly enhances threat detection and response times, providing predictive insights and seamless integration. (Estimated data)
The Evolution of Cyber Threats
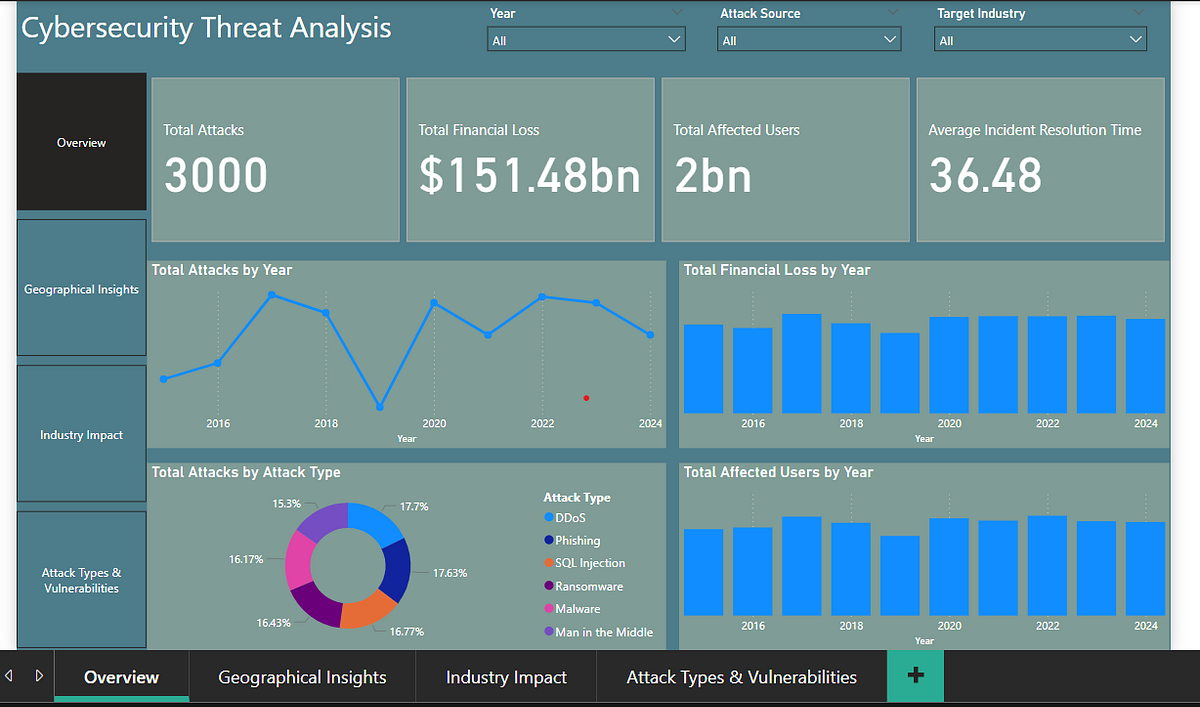
Cyber threats have become increasingly complex, targeting vulnerabilities at all levels. From ransomware to phishing schemes, attackers are more sophisticated than ever. Traditional defenses often fall short, necessitating a proactive approach that anticipates and neutralizes threats before they can cause damage. According to Booz Allen Hamilton, AI-driven cyberattacks are increasingly outpacing human-driven defenses, especially across critical infrastructure.

Integration is rated as the most crucial step in implementing GPT-5.4-Cyber, followed closely by assessing security needs and continuous monitoring. Estimated data.
Enter GPT-5.4-Cyber
Open AI's GPT-5.4-Cyber is not just an AI; it's a paradigm shift in how we approach cybersecurity. Unlike its predecessors, this model is tailored specifically for cyber defense, boasting capabilities such as reverse engineering and anomaly detection. As reported by SiliconANGLE, this model has been vetted by security professionals to ensure its effectiveness against next-level cyber threats.
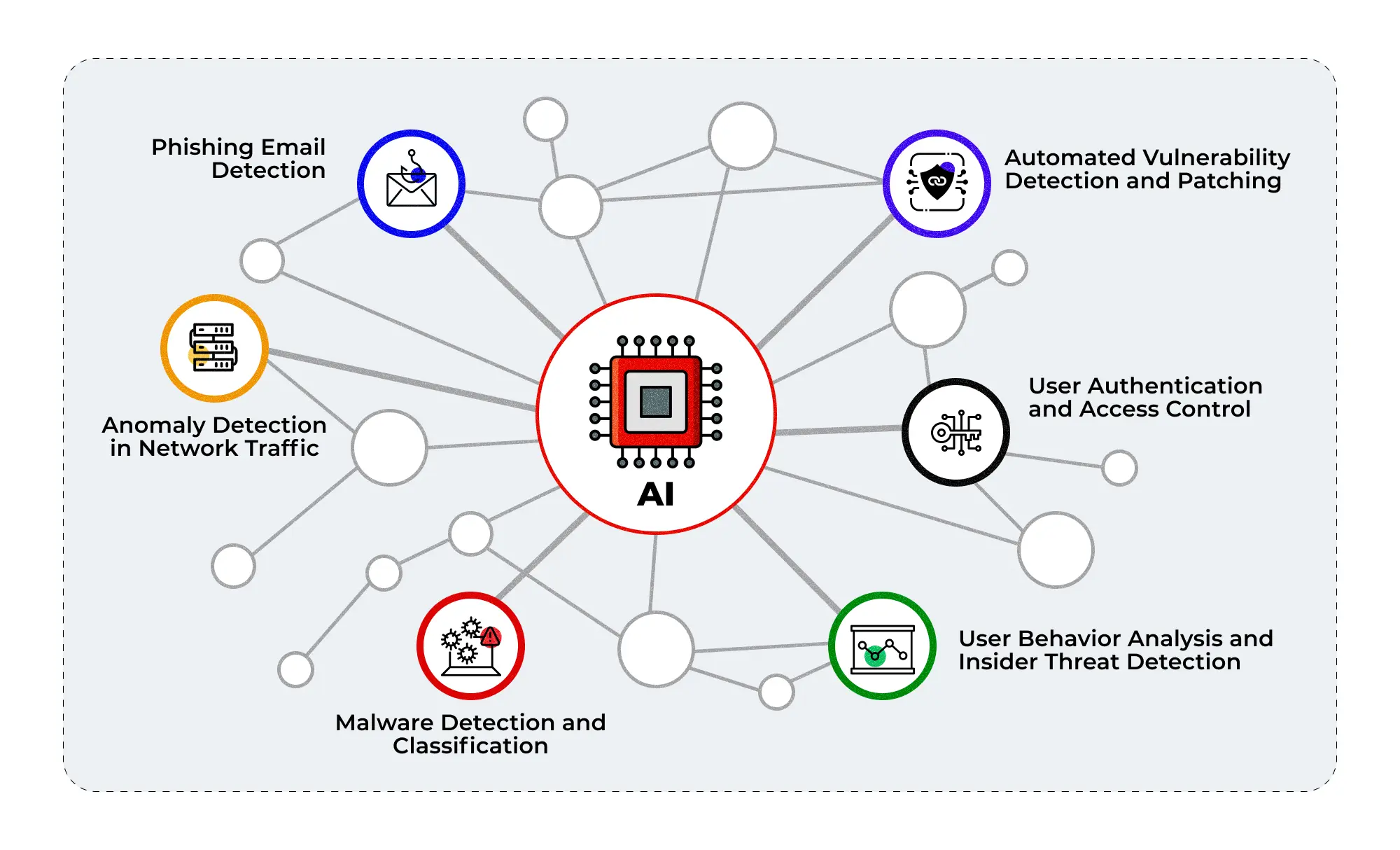
What Sets GPT-5.4-Cyber Apart?
-
Reverse Engineering: This feature allows cybersecurity professionals to dissect malware and understand its structure and behavior. By analyzing code and identifying malicious patterns, organizations can preemptively block future attacks. The Hacker News highlights how this capability is crucial for understanding and mitigating complex threats.
-
Anomaly Detection: The model excels at spotting irregular patterns that could indicate a breach. By continuously learning from new data, it adapts to emerging threats. Help Net Security notes that this feature significantly enhances the model's threat detection capabilities.
-
Natural Language Processing (NLP): GPT-5.4-Cyber utilizes NLP to understand and interpret threat intelligence reports, providing context-aware insights that enhance decision-making. This is particularly useful for analyzing vast amounts of data quickly, as discussed in Wiz.io's insights on AI's role in cybersecurity.
-
Trusted Access: With a focus on secure authentication, it ensures that only verified users can access sensitive information, mitigating the risk of unauthorized access. This aspect is crucial for maintaining data integrity and security, as emphasized by AISI's evaluation of similar models.
Practical Implementation of GPT-5.4-Cyber
Implementing GPT-5.4-Cyber in an organization requires strategic planning and integration into existing security frameworks. Here's a step-by-step guide:
Step 1: Assess Your Security Needs
Before deploying GPT-5.4-Cyber, conduct a thorough assessment of your current security posture. Identify gaps and areas where AI can enhance protection. ExecutiveBiz suggests that understanding your specific needs is critical for effective AI deployment.
Step 2: Integration
Seamless Integration is key. GPT-5.4-Cyber should be integrated with existing security tools and platforms. This ensures a unified approach to threat detection and response. As noted by MSN, integration challenges can be mitigated with careful planning and the use of middleware solutions.
Step 3: Training and Customization
AI models require training to adapt to specific environments. Customize GPT-5.4-Cyber to understand your organization's unique data patterns and threat landscape. Storyboard18 emphasizes the importance of customization in maximizing AI effectiveness.
Step 4: Monitoring and Evaluation
Continuous monitoring is crucial. Evaluate the model's performance regularly and adjust its parameters to improve accuracy and efficiency. This approach is supported by Techzine, which highlights the need for ongoing evaluation to ensure AI models remain effective.

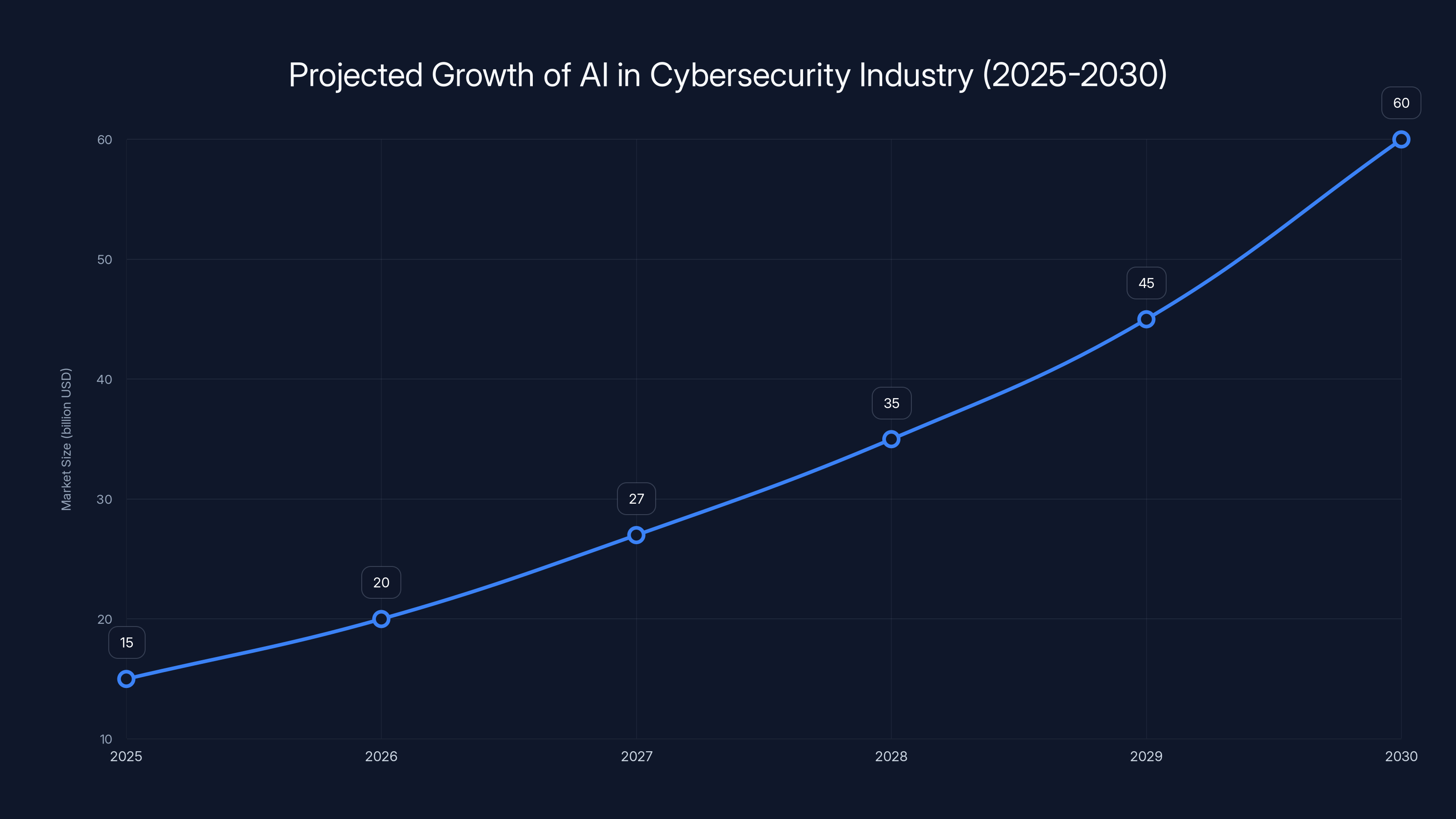
The AI-driven cybersecurity market is projected to grow significantly, reaching an estimated $60 billion by 2030, driven by advancements in adaptive learning and autonomous defense systems. Estimated data.
Common Pitfalls and Solutions
Implementing advanced AI models like GPT-5.4-Cyber isn't without challenges. Here are some common pitfalls and solutions:
Pitfall 1: Overreliance on AI
While AI is powerful, it's not infallible. Overreliance can lead to complacency. Solution: Maintain a balance between AI-driven insights and human expertise. This balance is crucial, as discussed in Help Net Security.
Pitfall 2: Integration Challenges
Integrating AI with legacy systems can be daunting. Solution: Employ middleware solutions that facilitate communication between new and existing systems. The Hacker News provides insights into overcoming these challenges.
Pitfall 3: Data Privacy Concerns
Handling sensitive data with AI raises privacy concerns. Solution: Implement robust encryption and access controls to protect data integrity. This approach is recommended by Wiz.io.
Future Trends in AI-Driven Cybersecurity
As technology advances, so too will the capabilities of AI in cybersecurity. Here are some trends to watch:
Adaptive Learning
Future AI models will feature adaptive learning, enabling them to evolve alongside emerging threats without human intervention. Booz Allen Hamilton discusses the potential of adaptive learning in AI models.
Autonomous Defense Systems
AI will power autonomous defense systems that can independently identify and neutralize threats, reducing response times significantly. This trend is highlighted by Techzine.
Enhanced Collaboration
Collaboration between AI models and human analysts will become more seamless, enhancing the speed and accuracy of threat detection. AISI emphasizes the importance of this collaboration.
Legal and Ethical Considerations
As AI becomes more prevalent in cybersecurity, legal and ethical considerations will play a crucial role in its development and deployment. This aspect is explored by ExecutiveBiz.
Recommendations for Cybersecurity Professionals
- Stay Informed: Keep abreast of the latest advancements in AI and cybersecurity.
- Continuous Learning: Encourage ongoing training for cybersecurity teams to leverage new tools effectively.
- Invest in AI: Allocate resources towards AI solutions that enhance security measures.
- Collaborate with AI Experts: Work closely with AI experts to understand and implement new technologies effectively.
Conclusion
Open AI's GPT-5.4-Cyber represents a significant leap forward in cybersecurity. By enhancing threat detection and providing trusted access, it empowers organizations to stay ahead of cyber threats. As AI continues to evolve, its role in cybersecurity will only grow, making it an indispensable tool for defending against the next generation of cyber attacks.
Use Case: Automate threat detection and analysis with Runable's AI-powered solutions.
Try Runable For FreeFAQ
What is GPT-5.4-Cyber?
GPT-5.4-Cyber is a specialized AI model by Open AI designed for advanced cybersecurity applications, including threat detection and reverse engineering.
How does GPT-5.4-Cyber improve threat detection?
It uses advanced machine learning algorithms and natural language processing to identify and analyze complex cyber threats. SiliconANGLE provides insights into its capabilities.
What are the benefits of using AI in cybersecurity?
AI enhances threat detection, improves response times, and provides predictive insights, making cybersecurity measures more effective. Help Net Security discusses these benefits in detail.
Can GPT-5.4-Cyber be integrated with existing systems?
Yes, it is designed to integrate seamlessly with current security frameworks, enhancing overall threat detection and response capabilities. The Hacker News highlights its integration features.
What are the future trends in AI cybersecurity?
Future trends include adaptive learning, autonomous defense systems, and enhanced collaboration between AI models and human analysts. Booz Allen Hamilton provides insights into these trends.
How can organizations ensure data privacy with AI?
By implementing strong encryption, access controls, and compliance with data protection regulations, organizations can safeguard sensitive information. Wiz.io offers guidance on maintaining data privacy.
What role does human expertise play alongside AI?
Human expertise is crucial for interpreting AI insights, making informed decisions, and addressing ethical considerations in cybersecurity. AISI emphasizes this role.
Why is continuous learning important in cybersecurity?
Continuous learning ensures that cybersecurity professionals stay updated on the latest threats and technologies, enabling them to respond effectively. ExecutiveBiz discusses the importance of ongoing education.
Key Takeaways
- OpenAI's GPT-5.4-Cyber enhances threat detection with reverse engineering and anomaly detection.
- The model integrates with existing security frameworks for seamless threat response.
- AI-powered cybersecurity systems offer adaptive learning and autonomous defense.
- Continuous learning and collaboration with AI experts are crucial for effective implementation.
- Future trends include AI-driven autonomous defense systems and enhanced human-AI collaboration.
- Privacy concerns can be mitigated with robust encryption and access controls.
- AI models like GPT-5.4-Cyber offer predictive insights, improving security measures.
- Investing in AI solutions is essential for staying ahead of evolving cyber threats.
Related Articles
- Understanding the Basic-Fit Data Breach: A Comprehensive Guide to Data Security [2025]
- OpenAI's Strategic Shift: Embracing Amazon to Expand Horizons [2025]
- Secure Your Digital Life: Keeper Password Manager's Big Discounts [2026]
- Booking.com Data Breach: What Customers Need to Know [2025]
- Anthropic’s Ascendance: A New Contender in the AI Arena [2025]
- Unmasking the Hidden Dangers: Backdoors in WordPress Plug-ins [2025]
!['Trusted Access for the Next Era of Cyber Defense': OpenAI's Cybersecurity Revolution [2025]](https://tryrunable.com/blog/trusted-access-for-the-next-era-of-cyber-defense-openai-s-cy/image-1-1776247488101.jpg)



