Unmasking the Hidden Dangers: Backdoors in WordPress Plug-ins [2025]
Last year, a seemingly innocuous acquisition of a WordPress plug-in developer led to a massive security breach affecting thousands of websites. This revelation came to light when a backdoor was discovered in multiple plug-ins, posing a significant threat to site integrity and user data. Let's dive into the intricacies of this breach, understand how it happened, and explore measures to safeguard against similar threats in the future.
TL; DR
- Over 20,000 WordPress sites have been compromised due to backdoors in plug-ins, as detailed in a TechCrunch report.
- Supply chain attacks are becoming more prevalent in open-source communities, highlighted by GitHub's insights on securing the open-source supply chain.
- Best practices include regular code audits and using reputable plug-in sources, as recommended by Search Engine Journal.
- Future trends predict increased focus on AI-driven security tools, as discussed in eSecurity Planet's analysis.
- Immediate action is required to update and secure affected sites, a critical step emphasized by The Hacker News.

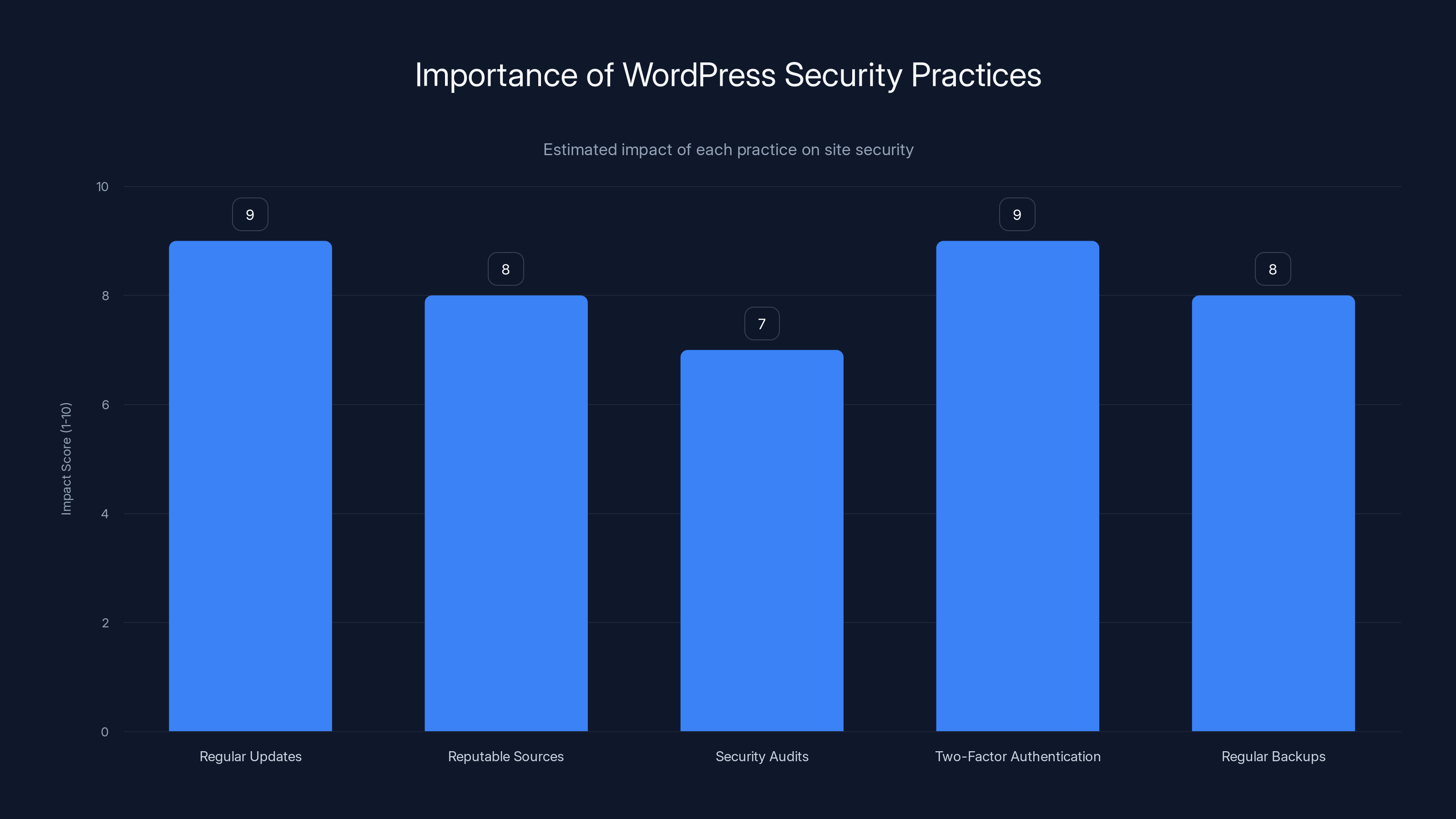
Regular updates and implementing two-factor authentication have the highest impact on securing WordPress sites. Estimated data.
Understanding the Breach
In a recent alarming development, dozens of WordPress plug-ins were found to contain backdoors, malicious elements in the code allowing unauthorized access. The breach came to light after a new corporate owner acquired Essential Plugin, a company responsible for developing these popular extensions. The backdoor remained dormant until activated, compromising installations on over 20,000 active WordPress sites, as reported by TechCrunch.
What Are Backdoors?
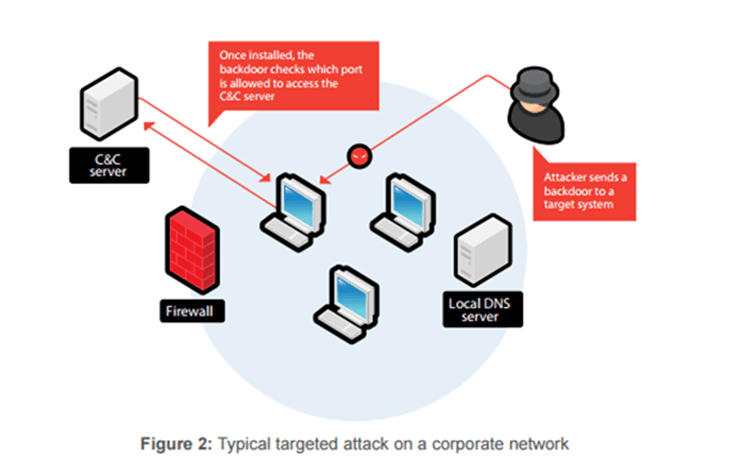
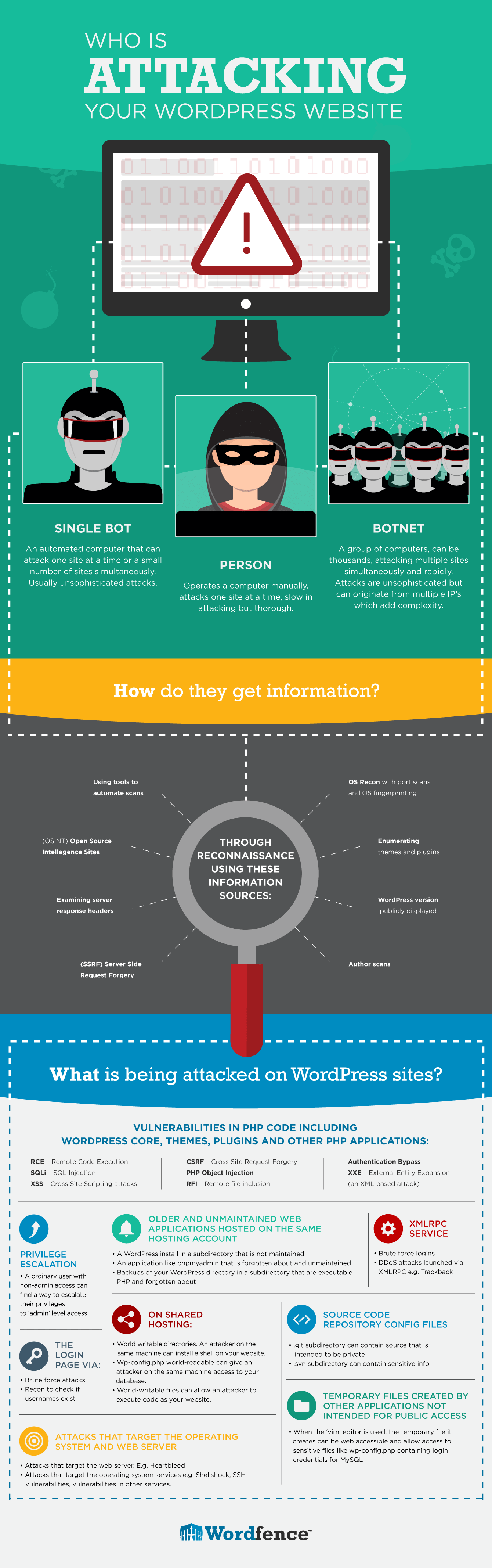
A backdoor is a method for bypassing normal authentication procedures to gain unauthorized access to a system. Backdoors can be planted in software as part of a supply chain attack, where malicious code is inserted during the development or update phases, as explained by Palo Alto Networks' Unit 42.
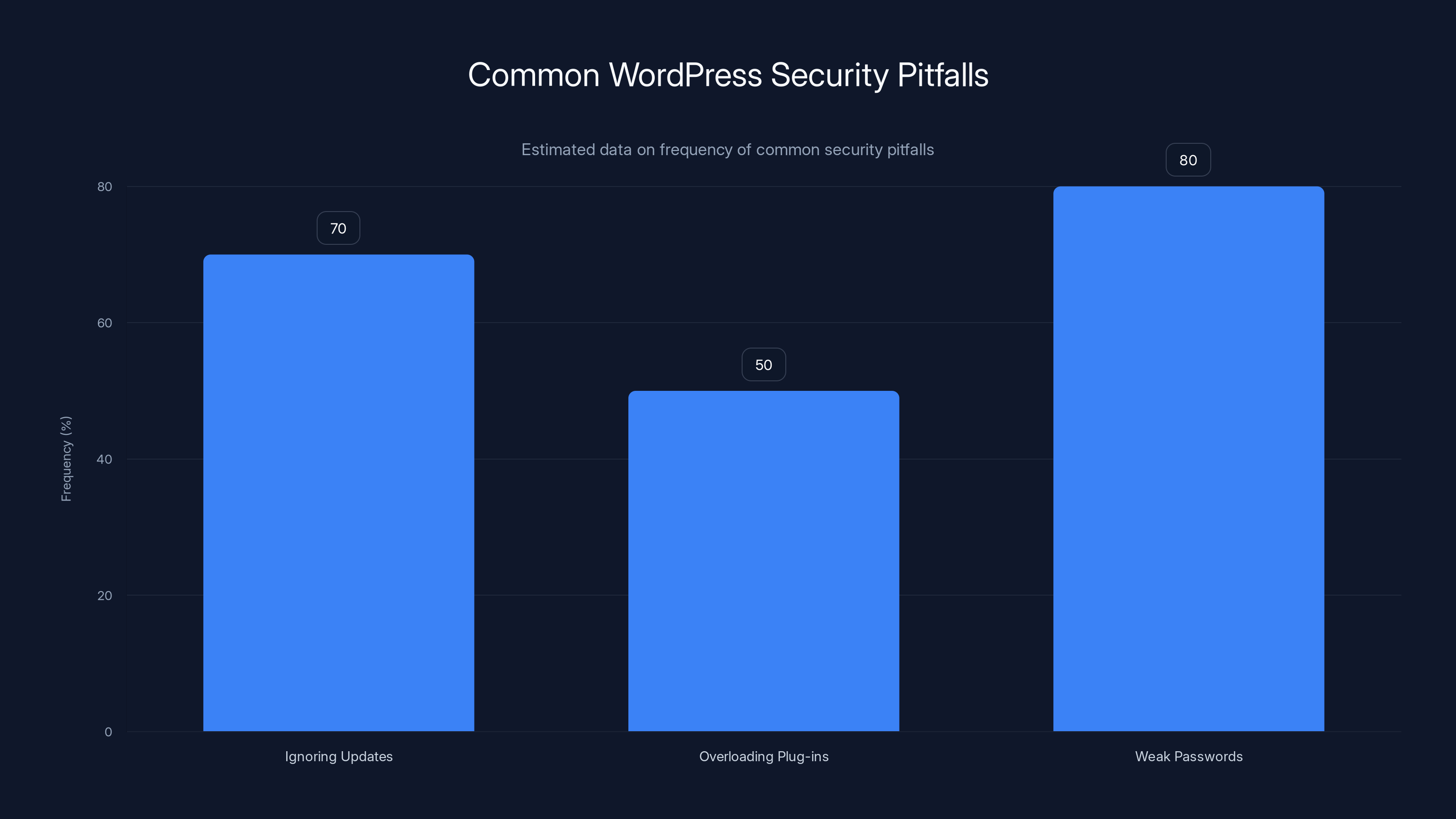
Ignoring updates and weak password practices are the most common security pitfalls in WordPress sites. Estimated data based on typical issues.
The Anatomy of the Attack
The attack on Essential Plugin is a classic supply chain compromise. After acquisition, the new owners introduced a backdoor into the plug-in's source code. This backdoor lay dormant until a predetermined trigger activated it, as detailed in Trend Micro's research.
How it Worked
- Initial Acquisition: A new corporate entity purchases Essential Plugin.
- Code Modification: Backdoor code is inserted into multiple plug-ins during updates.
- Dormancy Phase: The backdoor remains inactive, avoiding detection.
- Activation: Upon reaching a specific condition, the backdoor is activated.
- Malicious Code Execution: The backdoor begins executing harmful scripts across all infected sites.
Detection and Response
The backdoor was uncovered by Austin Ginder, founder of Anchor Hosting, who raised the alarm. Upon discovery, WordPress removed the affected plug-ins from its repository, and site owners were urged to uninstall or update their plug-ins immediately, as reported by TechCrunch.
Why WordPress Plug-ins Are Vulnerable
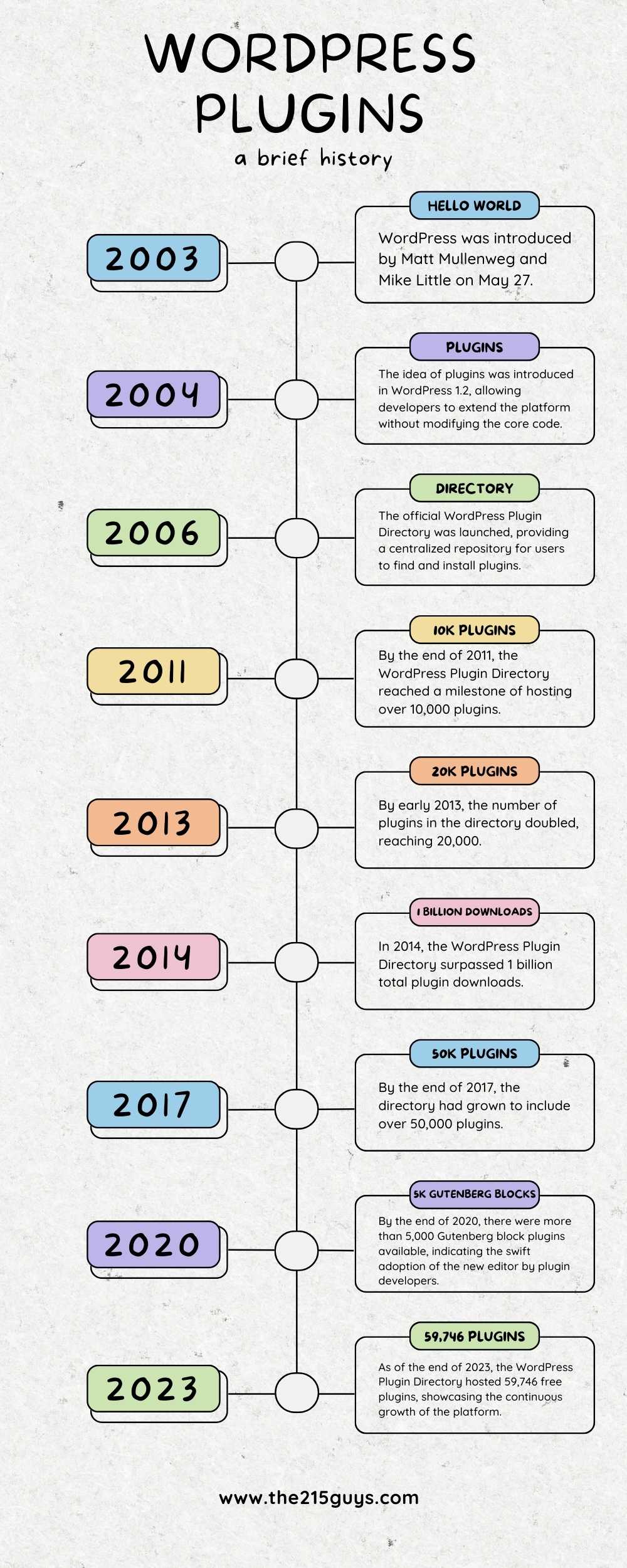
WordPress, powering over 40% of all websites, relies heavily on plug-ins. These add-ons enhance functionality but also introduce risks.
- Open Source Nature: Anyone can develop and distribute WordPress plug-ins, making it easier for malicious actors to infiltrate, as noted by Cloudflare's blog.
- Volume and Variety: With thousands of plug-ins available, maintaining quality and security across the board is challenging.
- Lack of Regular Audits: Not all plug-ins undergo thorough security audits, leading to vulnerabilities, as highlighted by Search Engine Journal.
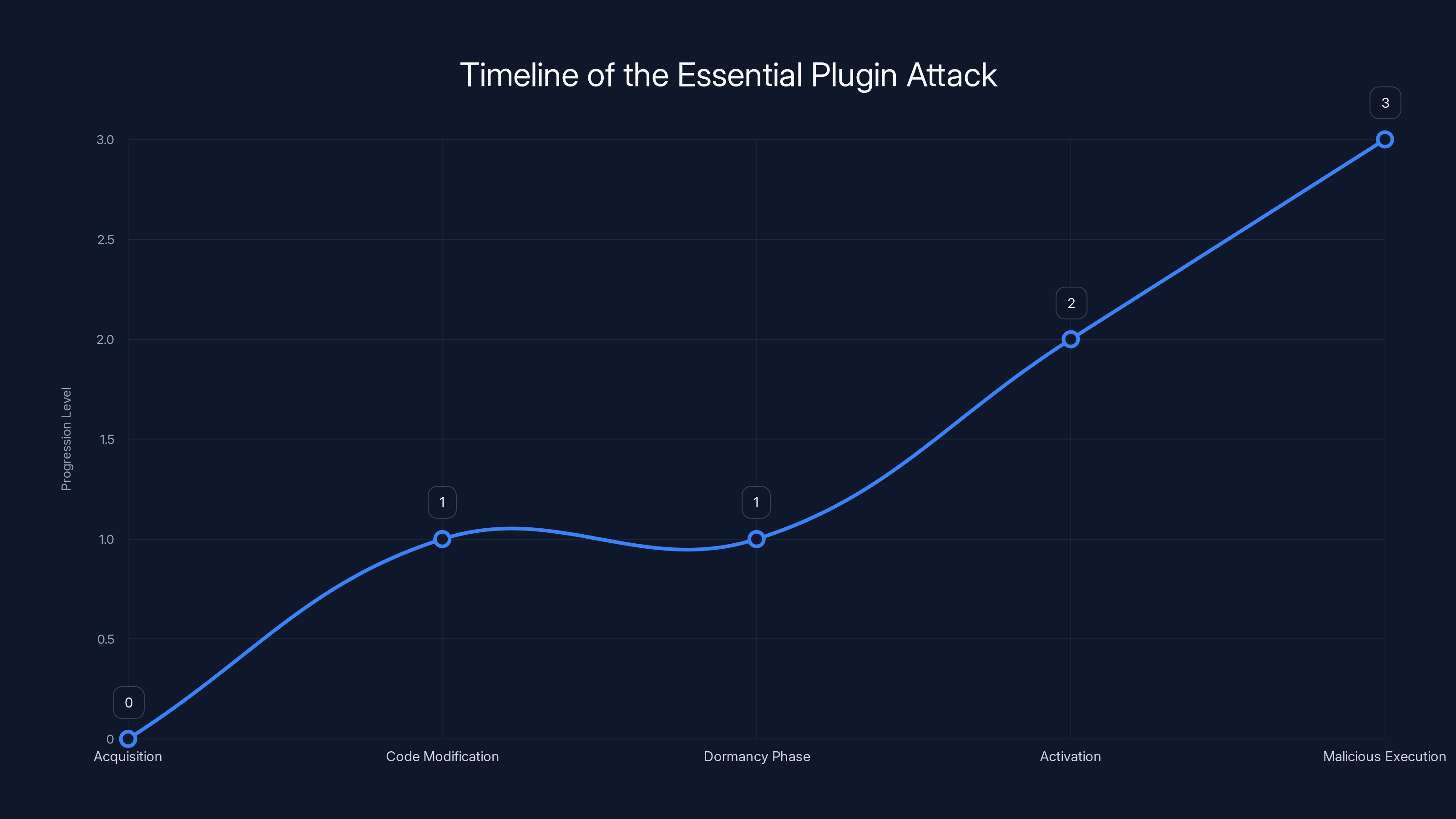
The attack on Essential Plugin progressed through distinct phases, culminating in the activation and execution of malicious code. Estimated data.
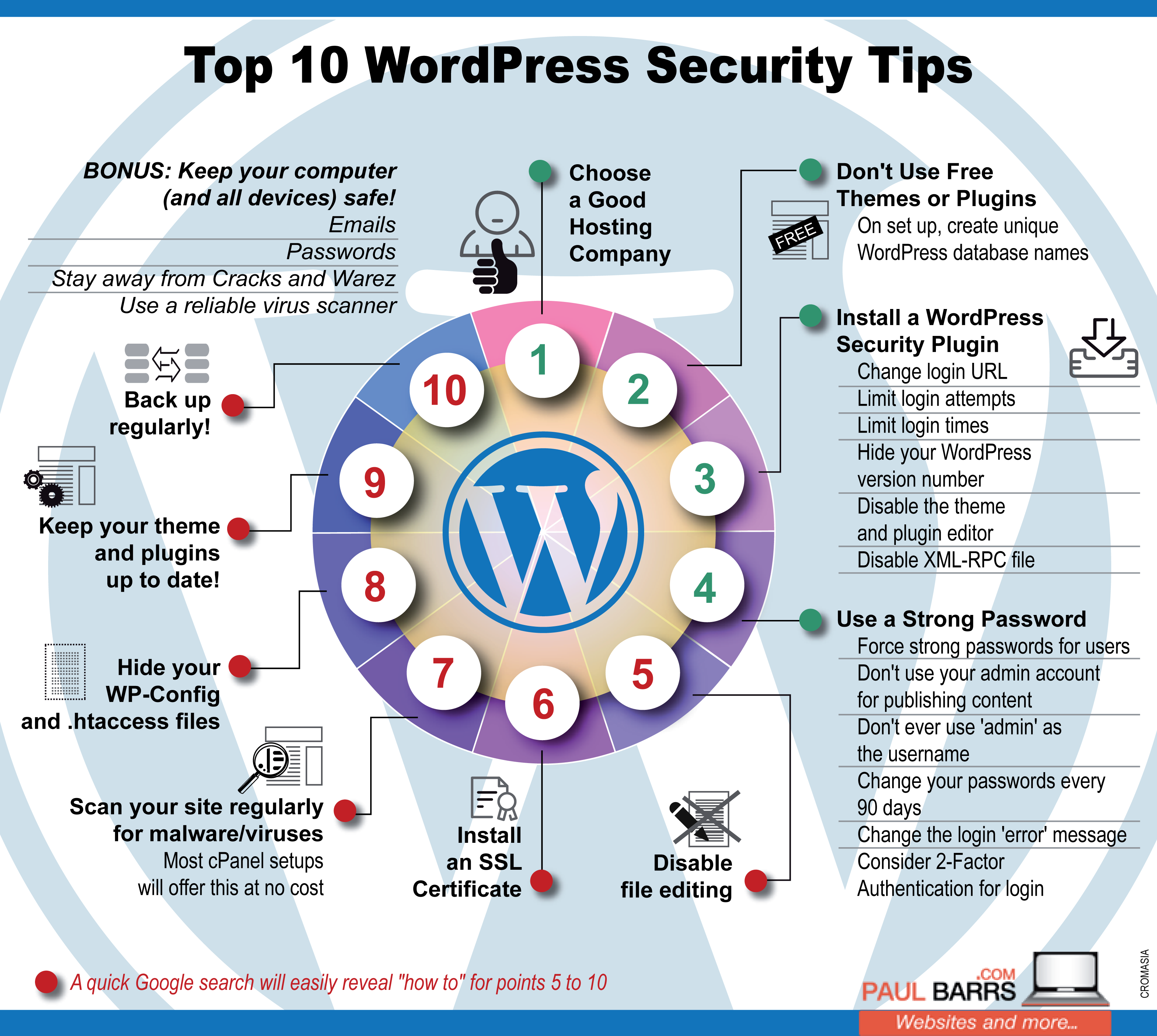
Best Practices for Securing WordPress Sites
Ensuring the security of a WordPress site involves a combination of vigilance and proactive measures.
1. Regular Updates
Keeping WordPress, themes, and plug-ins updated is crucial. Updates often contain patches for known vulnerabilities, as advised by The Hacker News.
2. Use Reputable Sources
Only download plug-ins from trusted sources. Check reviews, ratings, and update history before installation, as recommended by Search Engine Journal.
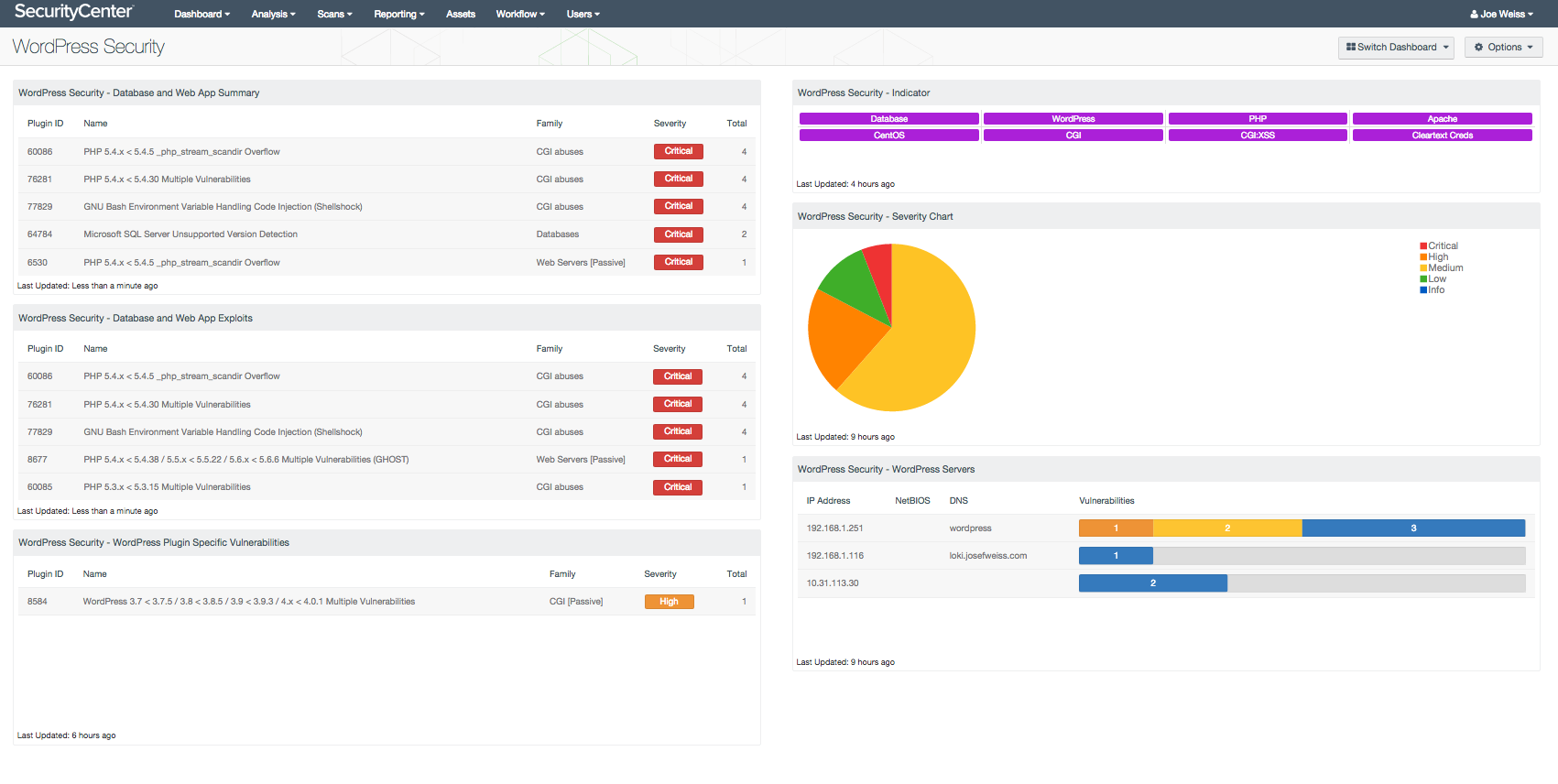
3. Conduct Security Audits
Regularly audit your site's codebase for vulnerabilities. Use tools like Sucuri or Wordfence for comprehensive scans.
4. Implement Two-Factor Authentication (2FA)
Adding 2FA to your login process significantly reduces unauthorized access risks.
5. Backup Regularly
Maintain regular backups of your site to ensure you can recover quickly from a compromise.
Common Pitfalls and Solutions
Missteps in securing WordPress sites often lead to vulnerabilities. Here are common pitfalls and how to avoid them:
1. Ignoring Update Notifications
Many site owners delay updates, thinking they're inconvenient. However, ignoring updates leaves your site exposed.
Solution: Automate updates where possible, or schedule regular maintenance checks.
2. Overloading with Plug-ins
Installing too many plug-ins can slow your site and increase security risks.
Solution: Only use essential plug-ins. Regularly review and remove unused ones.
3. Weak Password Practices
Using simple passwords makes it easy for attackers to gain access.
Solution: Use strong, unique passwords and change them regularly. Consider a password manager to keep track.
Future Trends in WordPress Security
As cyber threats evolve, so too must our defenses. Here are trends to watch:
1. AI-Driven Security
AI and machine learning are increasingly used to predict and identify threats before they cause harm, as discussed in eSecurity Planet's analysis.
2. Blockchain for Verification
Blockchain technology could provide a tamper-proof way to verify plug-in integrity, ensuring code hasn't been altered.
3. Comprehensive Security Ecosystems
Future platforms may offer integrated security ecosystems, providing everything from scanning to backups in one package.
Practical Steps for Developers
For developers, building secure plug-ins is a responsibility that begins at the code level.
1. Follow Secure Coding Practices
Implement practices like input validation and error handling to prevent vulnerabilities.
2. Conduct Peer Reviews
Having another set of eyes on your code can catch issues you might overlook.
3. Use Version Control
Platforms like GitHub not only help manage code changes but also track who made changes and when, as emphasized by GitHub's security blog.
4. Engage in Security Training
Regularly update your knowledge on security trends and new vulnerabilities.
Conclusion
The discovery of backdoors in WordPress plug-ins is a stark reminder of the vulnerabilities inherent in open-source systems. By understanding these risks and proactively securing our sites, we can mitigate threats and protect our digital assets.
Use Case: Automate security audits and updates with Runable to ensure your WordPress site remains secure and efficient.
Try Runable For Free
Key Takeaways
- Over 20,000 WordPress sites were affected by backdoors in plug-ins, as reported by TechCrunch.
- Supply chain attacks are a rising threat in open-source software, as highlighted by GitHub's insights.
- Regular code audits and updates are essential for security, as recommended by Search Engine Journal.
- AI and blockchain are emerging trends in cybersecurity, as discussed in eSecurity Planet's analysis.
- Developers must adhere to secure coding practices, as emphasized by GitHub's security blog.
Related Articles
- How Hackers Hijack Your Inbox with Clever Tactics [2025]
- Understanding the Basic-Fit Data Breach: A Comprehensive Guide to Data Security [2025]
- Press Freedom and VPN Surveillance: Navigating the Complexities [2025]
- Future-Proof Your Privacy with Next-Generation VPN Encryption [2026]
- FBI Takedown of W3LL: A Cybercrime Platform Exposed [2025]
- Secure Your Digital Life: Keeper Password Manager's Big Discounts [2026]
FAQ
What is Unmasking the Hidden Dangers: Backdoors in WordPress Plug-ins [2025]?
Last year, a seemingly innocuous acquisition of a WordPress plug-in developer led to a massive security breach affecting thousands of websites, as detailed in a TechCrunch report.
What does tl; dr mean?
This revelation came to light when a backdoor was discovered in multiple plug-ins, posing a significant threat to site integrity and user data, as reported by TechCrunch.
Why is Unmasking the Hidden Dangers: Backdoors in WordPress Plug-ins [2025] important in 2025?
Let's dive into the intricacies of this breach, understand how it happened, and explore measures to safeguard against similar threats in the future, as discussed in Trend Micro's research.
How can I get started with Unmasking the Hidden Dangers: Backdoors in WordPress Plug-ins [2025]?
- Over 20,000 WordPress sites have been compromised due to backdoors in plug-ins, as detailed in a TechCrunch report.
What are the key benefits of Unmasking the Hidden Dangers: Backdoors in WordPress Plug-ins [2025]?
- Supply chain attacks are becoming more prevalent in open-source communities, as highlighted by GitHub's insights.
What challenges should I expect?
- Best practices include regular code audits and using reputable plug-in sources, as recommended by Search Engine Journal.
![Unmasking the Hidden Dangers: Backdoors in WordPress Plug-ins [2025]](https://tryrunable.com/blog/unmasking-the-hidden-dangers-backdoors-in-wordpress-plug-ins/image-1-1776193473719.jpg)



