Understanding and Mitigating the Cisco Catalyst SD-WAN Vulnerability [2025]
Last year, a significant security concern emerged in the realm of enterprise networking. Cisco, a titan in the networking industry, revealed that hackers have been actively exploiting a critical vulnerability in their Catalyst SD-WAN products. This vulnerability, with a severity score of 10.0, has been a gateway for cybercriminals to infiltrate and compromise networks of large enterprises and government agencies. Let's dive into the intricacies of this vulnerability, its potential impacts, and how organizations can safeguard against such threats.
TL; DR
- Critical Bug Identified: A severe vulnerability in Cisco's Catalyst SD-WAN, actively exploited since 2023, allows unauthorized network access. According to The Hacker News, this issue has been a major concern for enterprises.
- Vulnerability Severity: Rated 10.0, enabling hackers to gain high-level permissions and maintain persistent access, as detailed in Help Net Security.
- Impact on Enterprises: Targets large-scale networks, including government and critical infrastructure, risking data theft and espionage. The CyberPress highlights the potential national security implications.
- Mitigation Strategies: Regular patch management, network segmentation, and continuous monitoring are essential, as advised by the Cybersecurity and Infrastructure Security Agency (CISA).
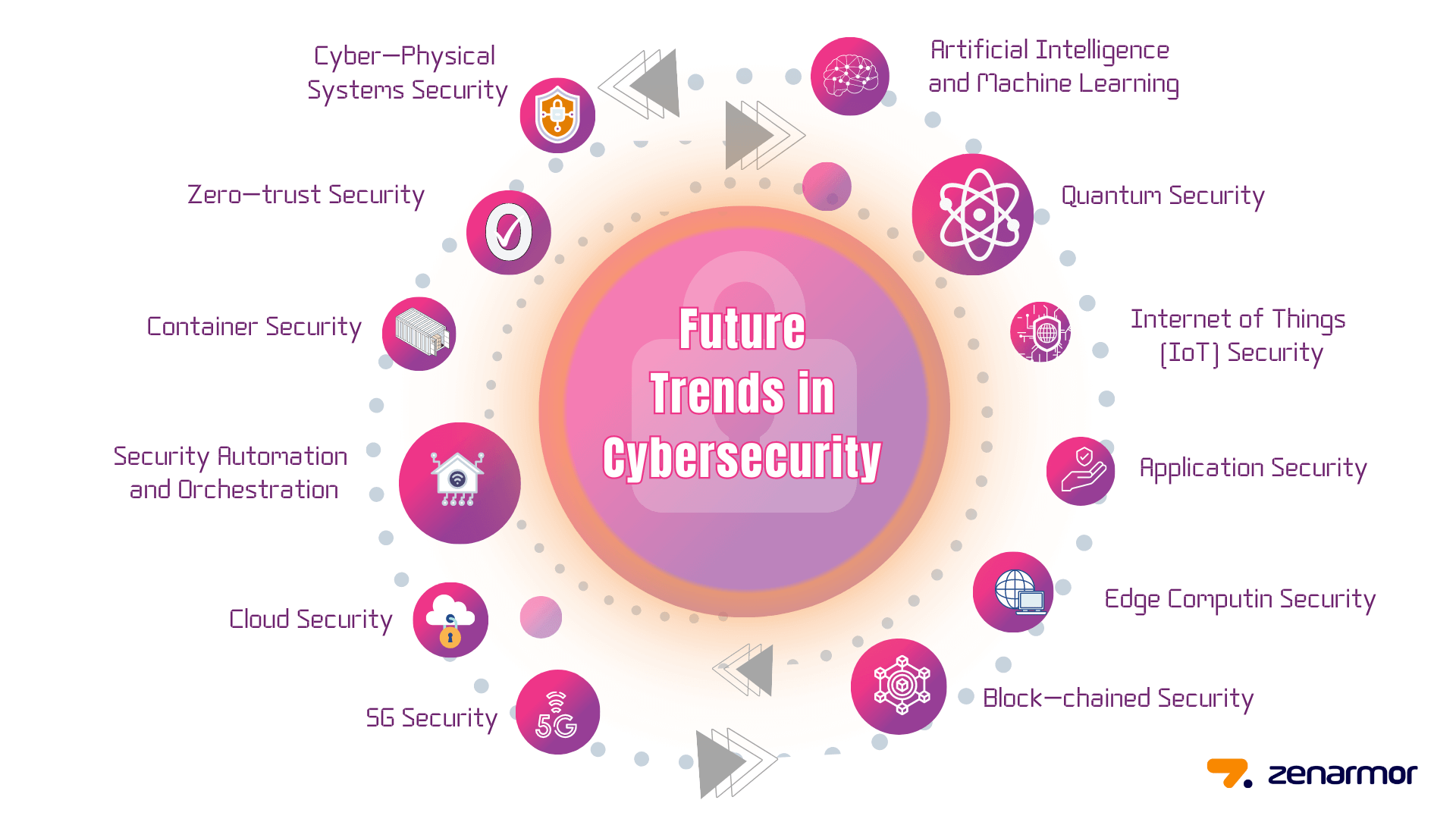
- Future Trends: Increased focus on zero-trust architecture and AI-driven threat detection for enhanced security.
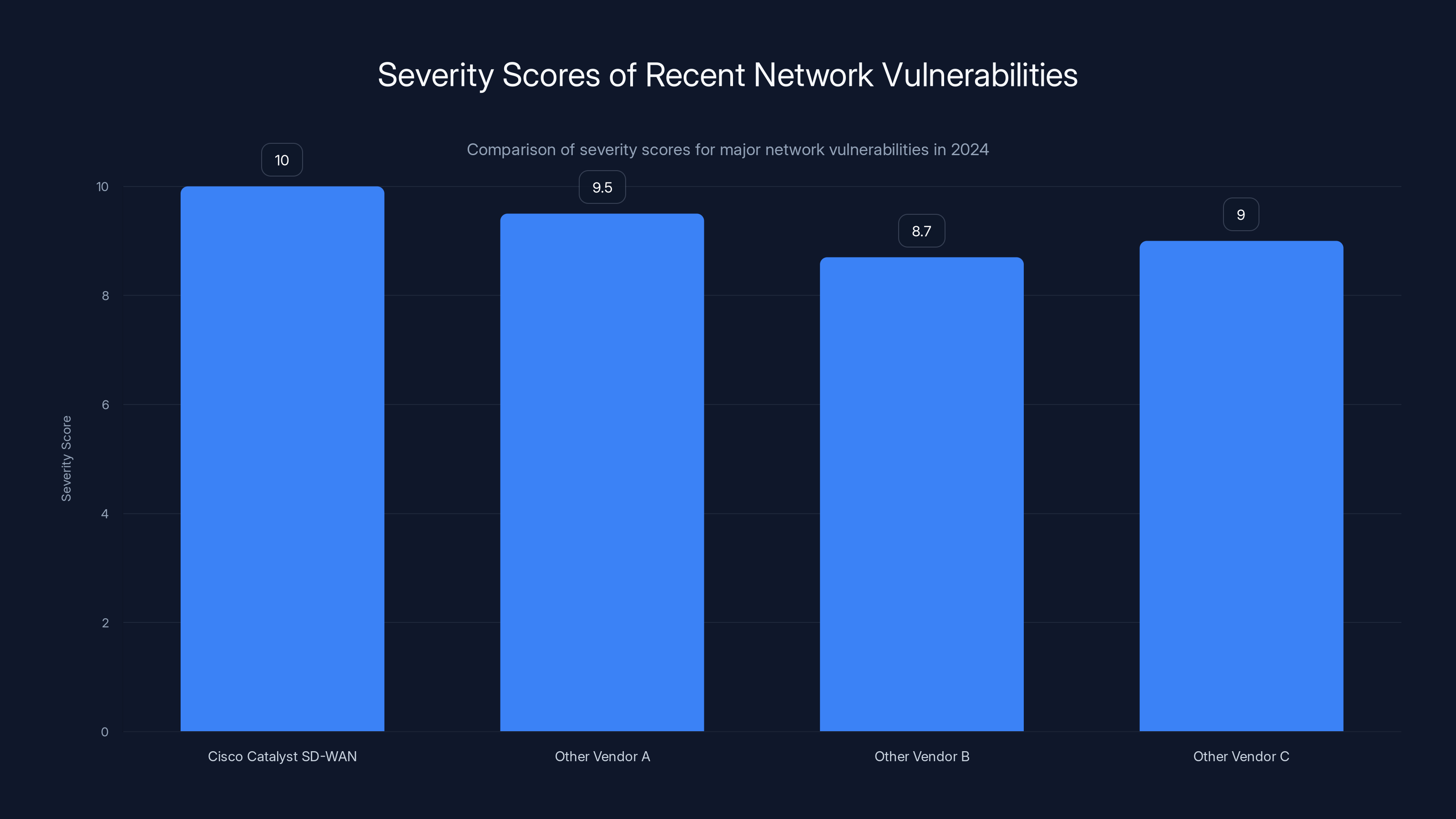
The Cisco Catalyst SD-WAN vulnerability had the highest severity score of 10.0, indicating a critical threat level compared to other network vulnerabilities in 2024. Estimated data.
The Cisco Catalyst SD-WAN Vulnerability Explained
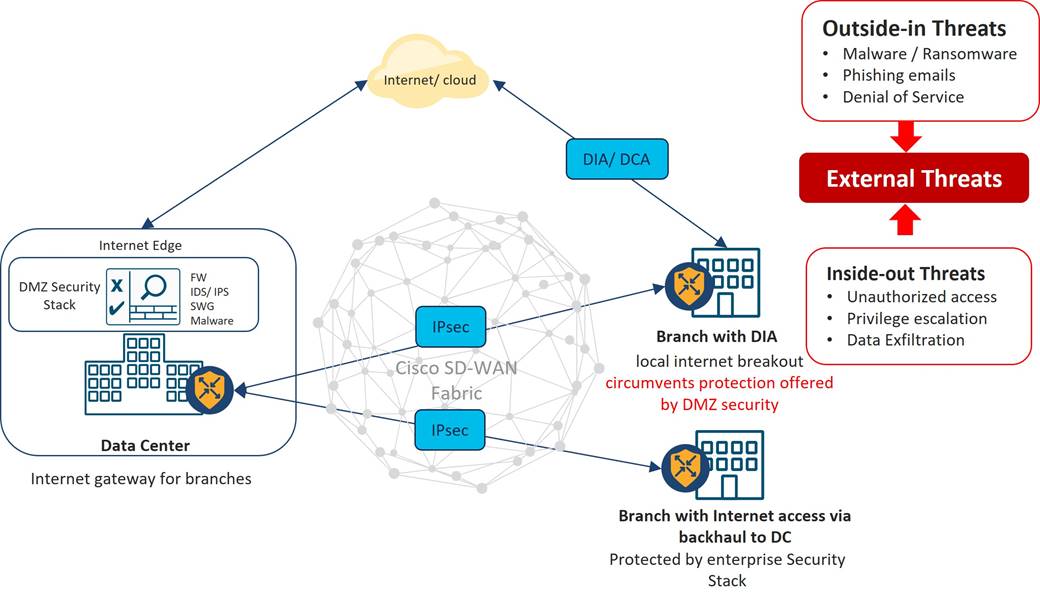
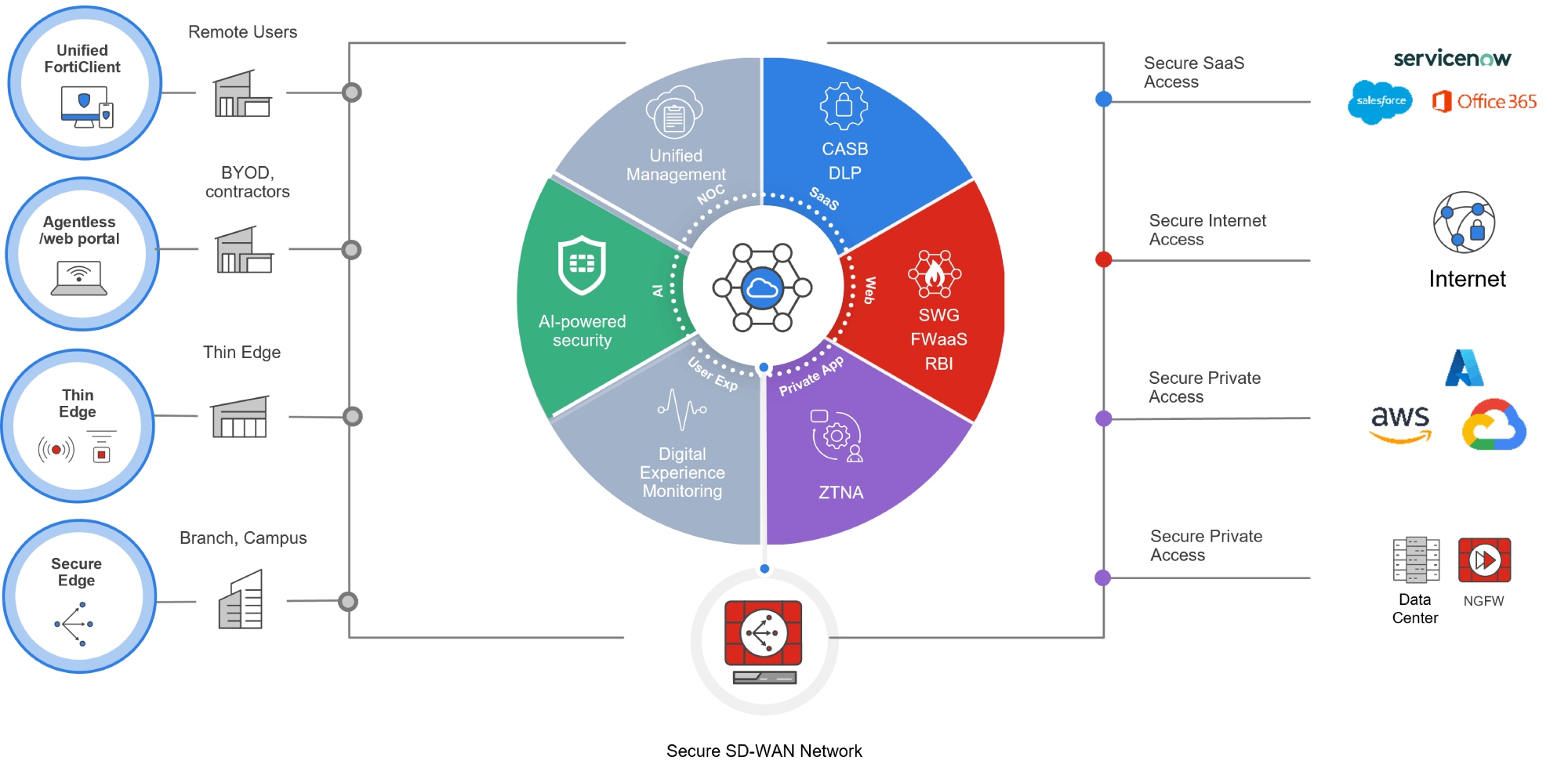
Cisco's Catalyst SD-WAN products are pivotal for organizations with multiple branches, enabling them to securely connect their private networks over vast distances. However, the discovery of a critical bug within these products has put countless enterprises at risk, as reported by Talos Intelligence.
What Makes This Vulnerability So Severe?
The vulnerability allows attackers to gain the highest level of access to the affected SD-WAN devices. This level of access means attackers can not only spy on network traffic but also manipulate data, inject malicious code, and maintain persistent access without being detected, as detailed in Help Net Security.
Key Features of the Vulnerability:
- Remote Exploitation: Attackers can exploit the vulnerability over the internet, making any exposed device a potential target, as noted by The Hacker News.
- Persistent Access: Once compromised, hackers can maintain access to the network, often unnoticed for extended periods, according to CyberPress.
- High-Level Permissions: Allows attackers to execute commands with admin-level privileges, increasing the potential damage, as explained by InfoSecurity Magazine.
Real-World Implications and Examples
Imagine a multinational corporation with branches across continents. Using Cisco's SD-WAN, all branches can securely communicate. However, if an attacker exploits this vulnerability, they could intercept sensitive communications, disrupt operations, or even steal intellectual property, as highlighted by Talos Intelligence.
Another example involves governmental agencies. A compromised SD-WAN device in a critical infrastructure agency could lead to national security threats, as attackers might access confidential data or disrupt essential services, according to CISA.
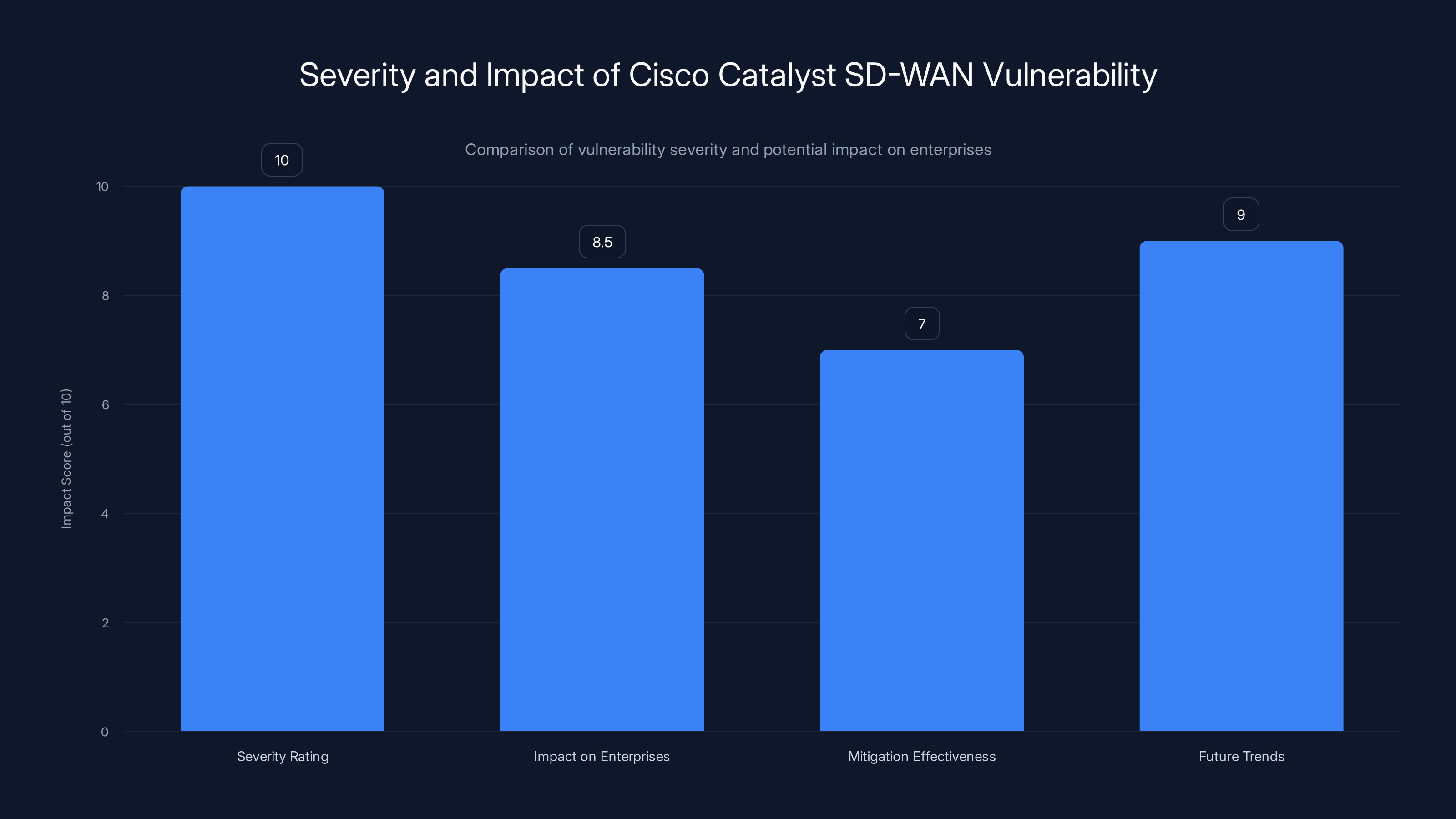
The Cisco Catalyst SD-WAN vulnerability has a critical severity rating of 10.0, posing significant risks to enterprises. Effective mitigation and future trends in security strategies are crucial to counteract these threats. (Estimated data)
Identifying and Mitigating the Risk
Addressing such a critical vulnerability requires a multifaceted approach. Organizations must not only patch the vulnerability but also strengthen their overall security posture, as advised by Talos Intelligence.
Best Practices for Mitigation
-
Patch Management:
- Regularly update all devices to the latest firmware provided by Cisco, as recommended by CISA.
- Implement automated patch management solutions to ensure timely updates, as suggested by InfoSecurity Magazine.
-
Network Segmentation:
- Divide the network into smaller, isolated segments, as detailed in CyberPress.
- Restrict access between segments to minimize the impact of a potential breach, as recommended by Help Net Security.
-
Continuous Monitoring:
- Deploy tools for real-time monitoring of network activity, as advised by Talos Intelligence.
- Use anomaly detection systems to identify and alert on suspicious behavior, as noted by CISA.
-
Access Control:
- Implement strict access controls and regularly review permissions, as suggested by The Hacker News.
- Use multi-factor authentication (MFA) to enhance security, as recommended by InfoSecurity Magazine.
-
Incident Response Plan:
- Develop and regularly update an incident response plan, as advised by CyberPress.
- Conduct drills to ensure the team is prepared for potential breaches, as suggested by Help Net Security.
Common Pitfalls and Solutions
Pitfall: Relying solely on perimeter defenses.
Solution: Adopt a zero-trust architecture, where every device and user must be verified before accessing the network, as recommended by CISA.
Pitfall: Delaying patch updates due to compatibility concerns.
Solution: Use a testing environment to verify updates before deployment, ensuring minimal disruption, as suggested by Talos Intelligence.
The Role of AI and Automation in Cybersecurity
With the increasing complexity of cyber threats, traditional security measures are no longer sufficient. Organizations are turning to AI and automation to enhance their security frameworks, as noted in a recent study.
AI-Driven Threat Detection
AI can analyze vast amounts of data to identify patterns indicative of a security breach. By learning from past incidents, AI systems can predict and prevent future attacks, as highlighted by Nature.
Benefits of AI in Cybersecurity:
- Proactive Threat Identification: Detect threats before they cause harm, as detailed in Nature.
- Reduced Response Time: Automate responses to common threats, reducing human intervention, as suggested by Nature.
- Enhanced Accuracy: Minimize false positives and improve threat detection accuracy, as noted in Nature.
Automation in Incident Response
Automation can streamline the incident response process, ensuring swift action in the event of a breach. Automated systems can isolate affected segments, notify relevant personnel, and even initiate recovery procedures, as explained by Nature.
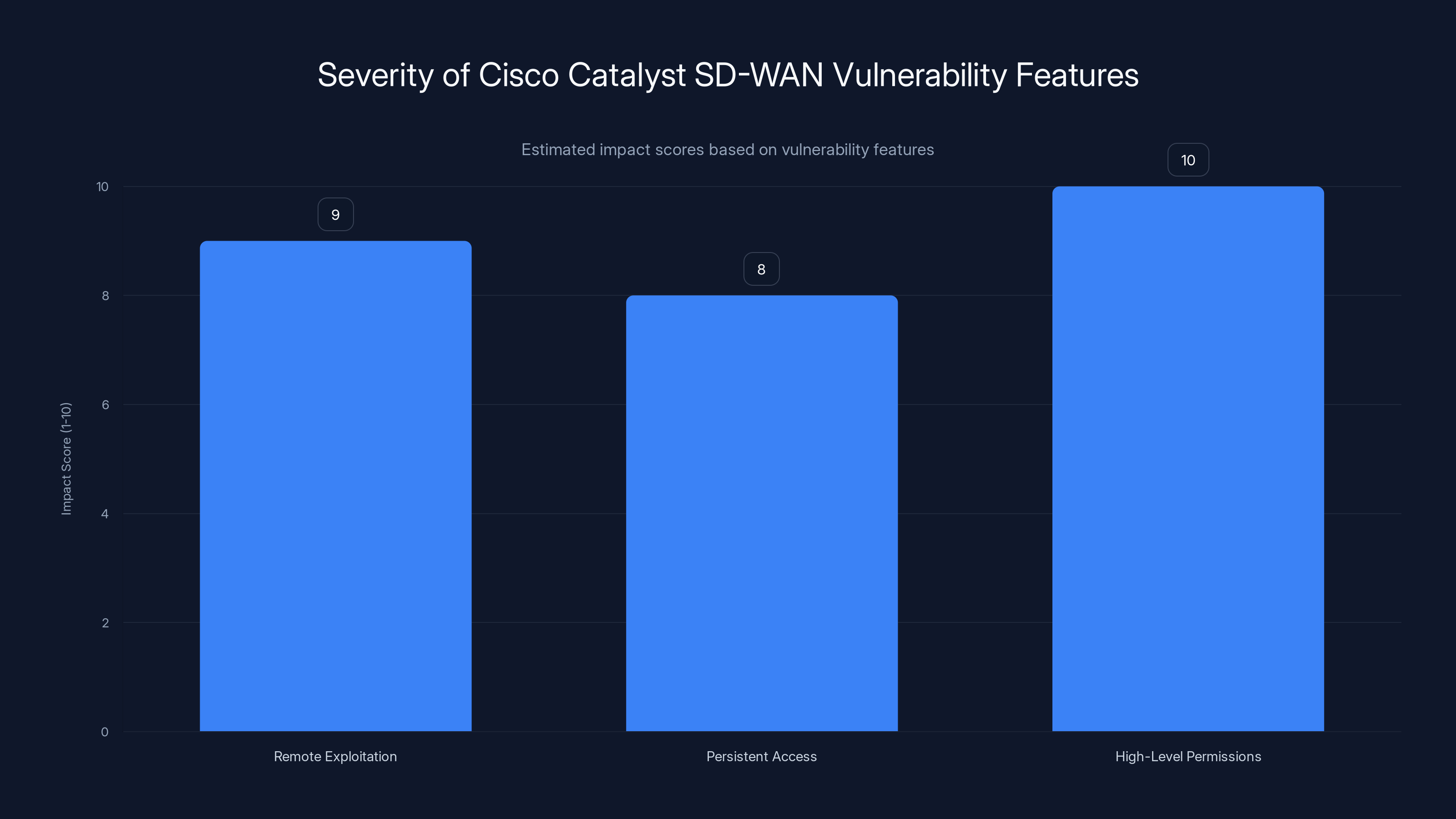
The Cisco Catalyst SD-WAN vulnerability's most severe feature is its ability to grant high-level permissions (score: 10), followed by remote exploitation (score: 9) and persistent access (score: 8). Estimated data.
Future Trends and Recommendations
As cyber threats evolve, so too must our defenses. Here are some key trends and recommendations for the future, as outlined by CISA.
Embracing Zero-Trust Architecture
Zero-trust shifts the focus from perimeter security to a more comprehensive approach where every request is verified. This approach is crucial given the rise of remote work and cloud services, as noted by CyberPress.
Enhanced Collaboration Between Vendors and Organizations
Vendors like Cisco must work closely with their clients to ensure vulnerabilities are promptly identified and addressed. Regular communication and collaboration can lead to faster resolution times and improved security, as suggested by Help Net Security.
Continuous Education and Training
Cybersecurity is a rapidly changing field. Organizations must invest in continuous education and training for their IT staff to keep them updated on the latest threats and mitigation techniques, as recommended by InfoSecurity Magazine.
Investing in Advanced Threat Intelligence
Threat intelligence provides insights into potential threats, allowing organizations to prepare and defend against them proactively. By leveraging global threat intelligence networks, companies can stay ahead of emerging threats, as highlighted by Talos Intelligence.
Conclusion
The discovery of the critical vulnerability in Cisco's Catalyst SD-WAN products underscores the importance of robust cybersecurity measures. As cyber threats become more sophisticated, organizations must adopt a proactive approach to security, leveraging the latest technologies and best practices to protect their networks. By staying informed and vigilant, enterprises can mitigate risks and safeguard their critical assets, as emphasized by CISA.
FAQ
What is the Cisco Catalyst SD-WAN vulnerability?
The vulnerability is a critical flaw in Cisco's Catalyst SD-WAN products that allows attackers to remotely access and compromise networks, as explained by The Hacker News.
How does this vulnerability affect enterprises?
It enables attackers to gain high-level permissions, maintain persistent access, and potentially steal or manipulate data within enterprise networks, as detailed by CyberPress.
What steps can organizations take to mitigate this risk?
Organizations should implement patch management, network segmentation, continuous monitoring, strict access controls, and develop an incident response plan, as advised by CISA.
Why is zero-trust architecture important?
Zero-trust architecture ensures that every device and user is verified before accessing the network, reducing the risk of unauthorized access, as noted by Help Net Security.
How can AI enhance cybersecurity?
AI can proactively identify threats, reduce response times, and improve the accuracy of threat detection, making it a valuable tool in cybersecurity, as highlighted by Nature.
What trends should organizations watch in cybersecurity?
Organizations should focus on zero-trust architecture, enhanced collaboration with vendors, continuous education, and investing in advanced threat intelligence for future security, as suggested by Talos Intelligence.
Key Takeaways
- The Cisco Catalyst SD-WAN vulnerability has been actively exploited since 2023, posing significant risks to enterprise networks, as reported by The Hacker News.
- With a severity score of 10.0, the vulnerability allows remote attackers to gain high-level access and maintain persistent network control, as detailed by CyberPress.
- Organizations must implement a multi-faceted security approach, including patch management, network segmentation, and continuous monitoring, as advised by CISA.
- AI and automation are critical in enhancing cybersecurity through proactive threat detection and streamlined incident response, as noted by Nature.
- Future trends in cybersecurity include the adoption of zero-trust architecture and increased collaboration between vendors and organizations, as suggested by Talos Intelligence.
Related Articles
- Understanding the AirSnitch Attack: Wi-Fi Encryption Risks and Mitigation [2025]
- Understanding the Marquis vs. SonicWall Case: Lessons on Firewall Security and Ransomware [2025]
- Ivanti VPN Breach: How Chinese Hackers Hit 119 Customers [2025]
- AI-Powered Hacking: How Low-Skill Attackers Break Firewalls [2025]
- Analyzing the Conduent Data Breach: Impacts and Lessons Learned [2025]
- ShinyHunters Hits Wynn Resorts: $1.5M Ransomware Demand [2025]
![Understanding and Mitigating the Cisco Catalyst SD-WAN Vulnerability [2025]](https://tryrunable.com/blog/understanding-and-mitigating-the-cisco-catalyst-sd-wan-vulne/image-1-1772123824644.jpg)



