Understanding and Mitigating Phishing Scams: Lessons from the Robinhood Incident [2025]
Last year, a significant breach revealed vulnerabilities in Robinhood's account creation tool. Hackers exploited these flaws, redirecting users to phishing sites. This incident underscores the need for robust security measures.
TL; DR
- Phishing Threats: Exploited Robinhood vulnerabilities led to credential theft.
- Security Measures: Implement multi-factor authentication (MFA) and regular audits.
- User Education: Critical in identifying phishing attempts.
- Future Trends: AI-driven tools to enhance detection.
- Bottom Line: Vigilance and proactive measures are essential.

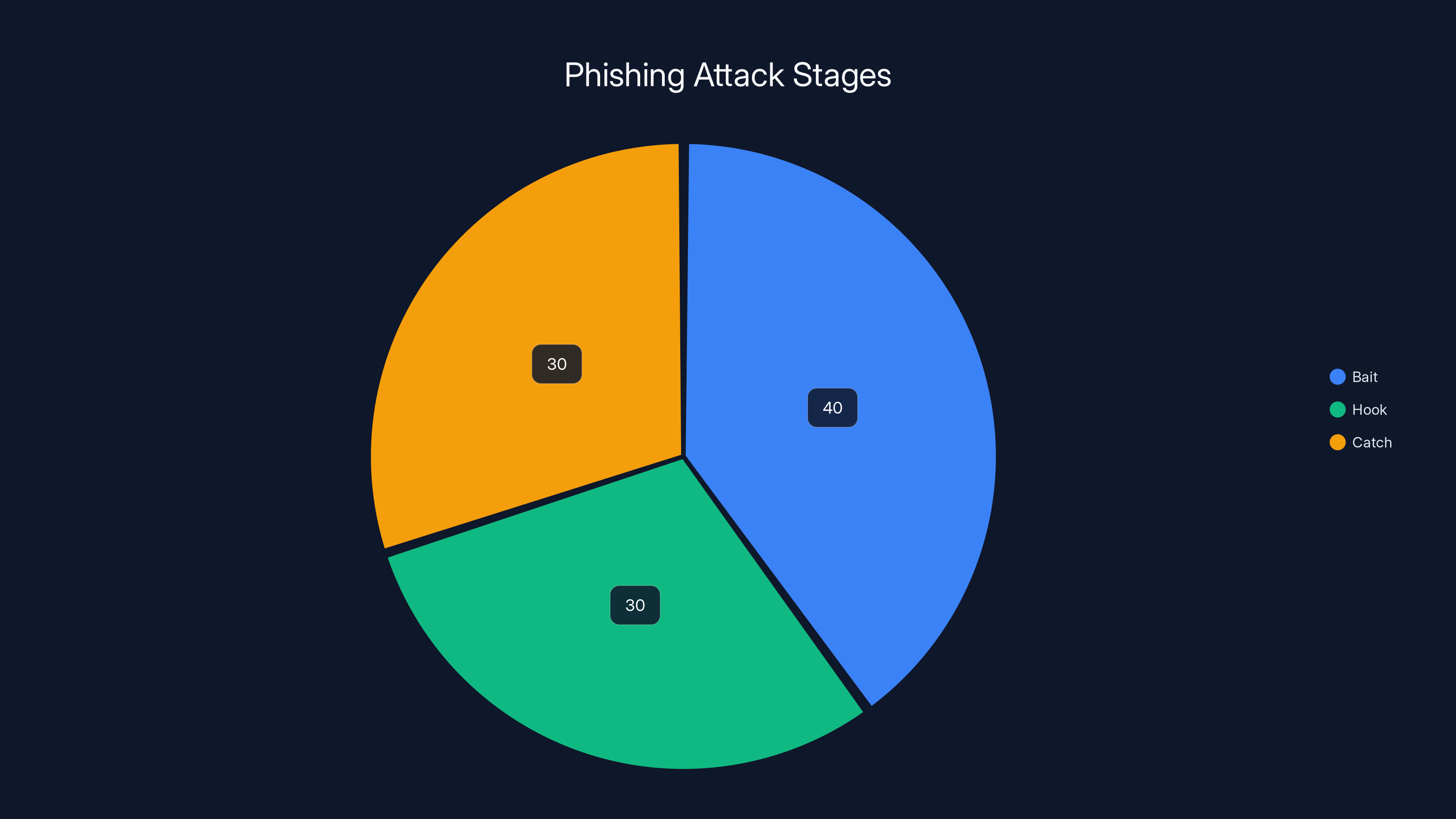
The 'Bait' stage often takes the longest as attackers craft convincing messages. 'Hook' and 'Catch' stages are quicker but crucial. Estimated data based on typical phishing attack flow.
The Rise of Phishing Attacks
Phishing scams have become increasingly sophisticated, leveraging human psychology and technical flaws. The Robinhood incident is a classic case, where hackers used official-looking emails to extract user credentials.
What Happened with Robinhood?
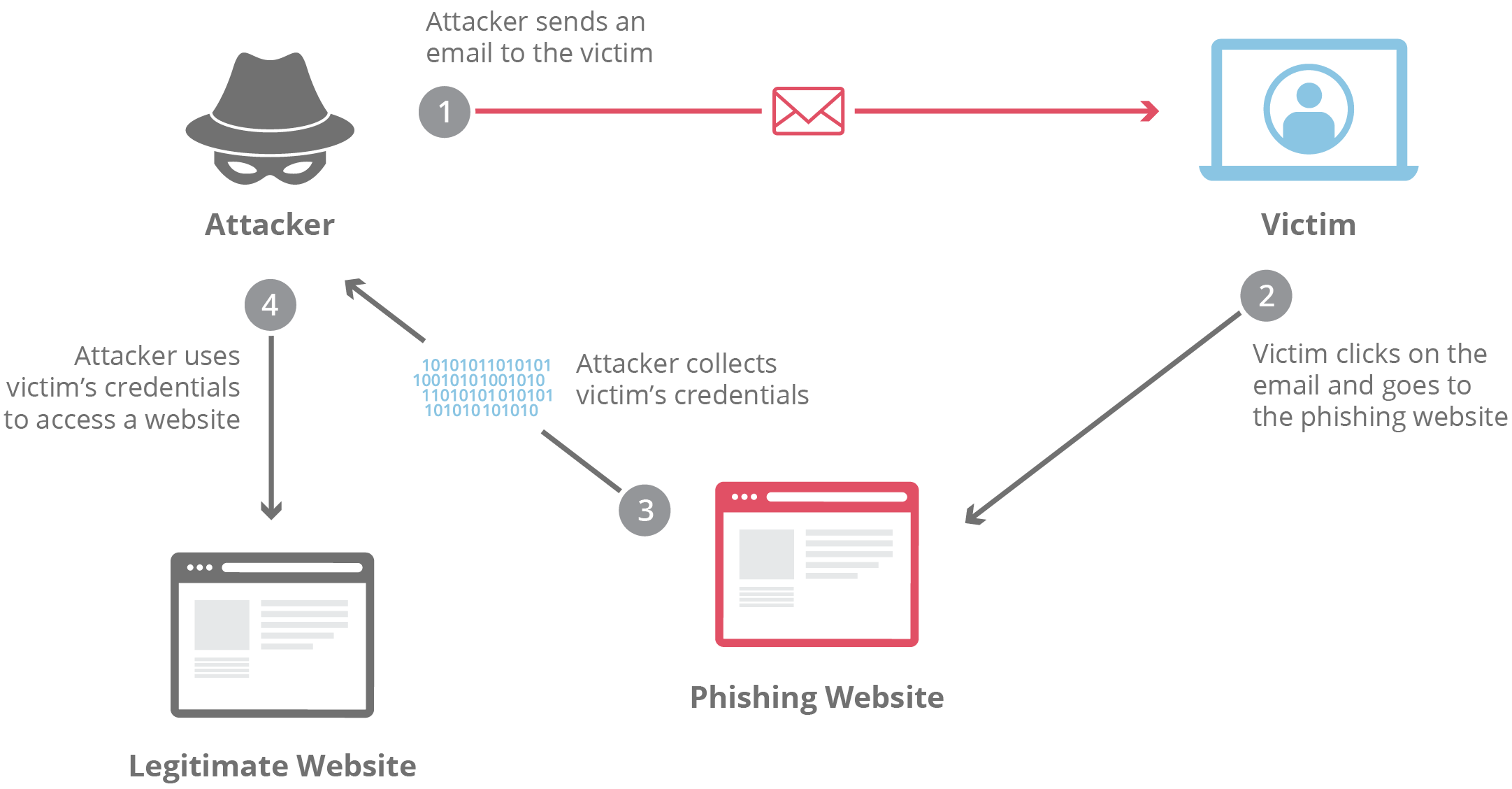
Hackers exploited vulnerabilities in the email system of Robinhood, sending phishing emails from what appeared to be the official domain. These emails redirected users to fake login pages designed to steal credentials.
Key Lessons:
- Email Authentication: Implement DKIM, SPF, and DMARC to verify email legitimacy, as discussed in TrustNFT's white paper on DMARC limitations.
- User Vigilance: Educate users to recognize phishing attempts by scrutinizing email senders and links.
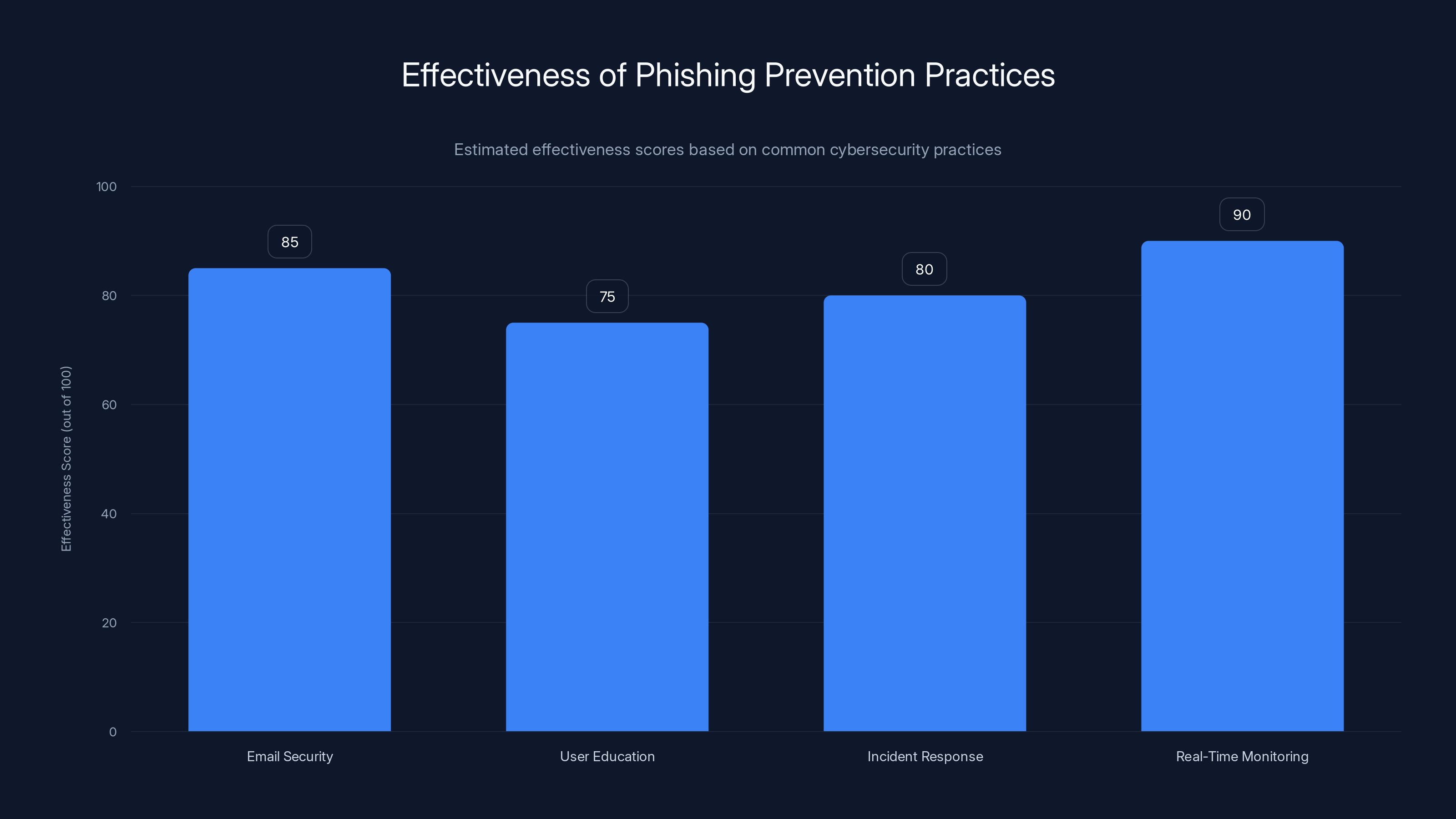
Real-time monitoring is estimated to be the most effective practice with a score of 90, followed by email security at 85. Estimated data based on typical cybersecurity evaluations.
Anatomy of a Phishing Attack
Phishing attacks often follow a predictable pattern:
- Bait: An urgent or enticing message prompts the user to act.
- Hook: The user is redirected to a spoofed website.
- Catch: User credentials are captured and misused.
Real-World Examples
Consider the attack on a major bank last year, where phishing emails mimicked customer service communications. Victims entered their login credentials into a fake site, leading to unauthorized account access.
Preventative Measures:
- Regular Training: Conduct phishing simulations to improve user awareness, as recommended by election officials preparing for AI cyberattacks.
- Technical Solutions: Use email filters and web gateway defenses.
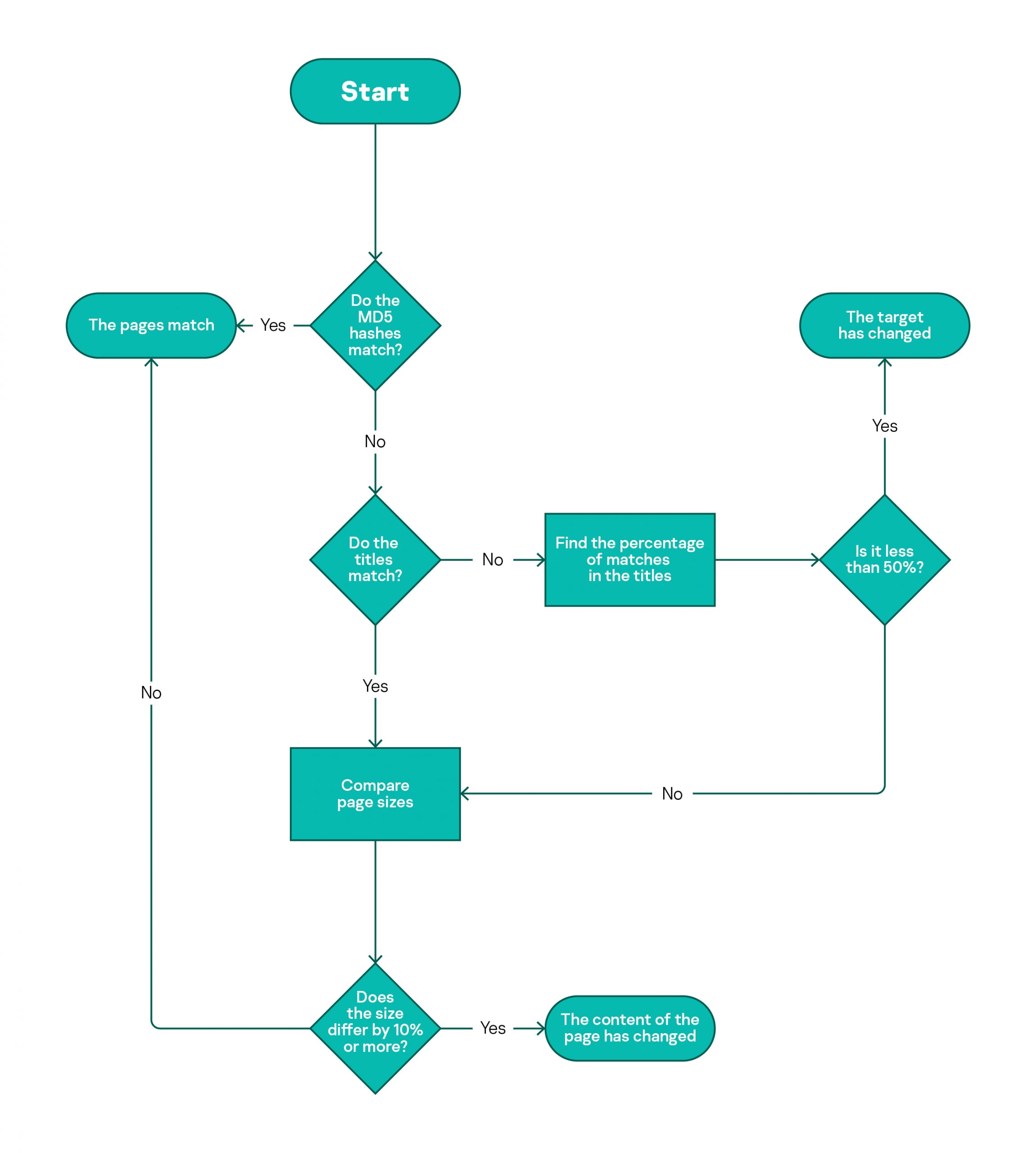
Technical Safeguards Against Phishing
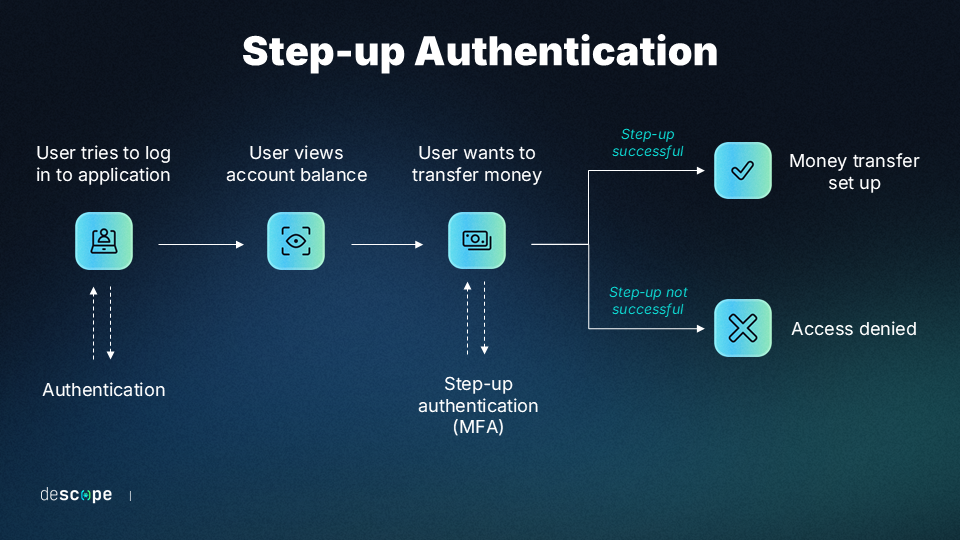
To protect against such threats, organizations must employ a multi-layered security approach:
- Multi-Factor Authentication (MFA): Adds an extra layer of security by requiring additional verification methods.
- Intrusion Detection Systems (IDS): Detect unusual activity and alert IT teams to potential breaches.
Implementation Guide
- Set Up MFA: Use apps like Google Authenticator or Microsoft Authenticator to secure accounts.
- Deploy IDS: Tools like Snort or Suricata provide real-time analysis of network traffic.
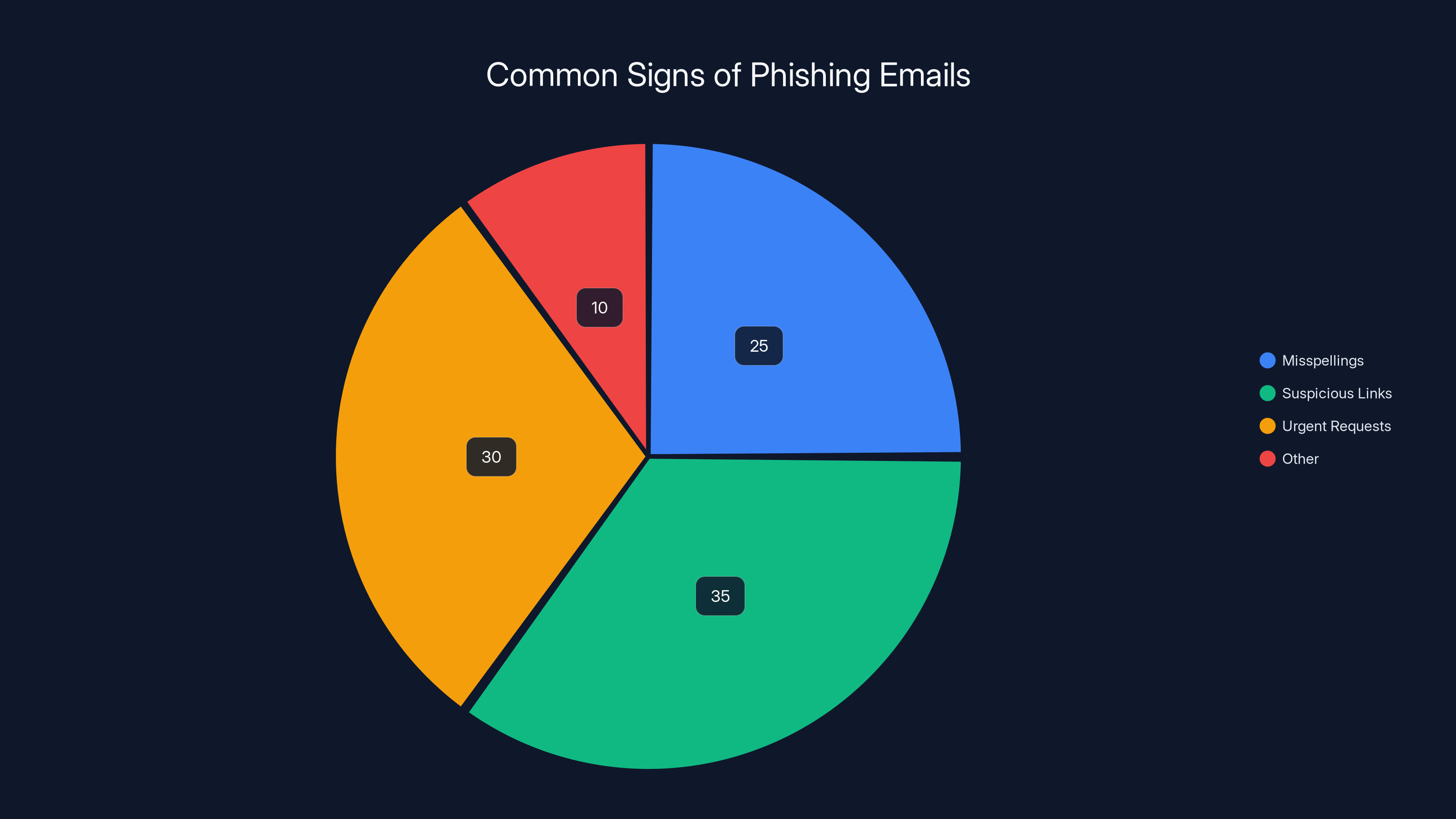
Suspicious links and urgent requests are the most common signs of phishing emails, followed by misspellings. Estimated data.
Common Pitfalls in Cybersecurity
Even with the best tools, organizations can fall prey to phishing due to common mistakes:
- Over-Reliance on Technology: Neglecting user education can lead to breaches.
- Infrequent Updates: Failing to regularly update systems and software increases vulnerability.
Solutions
- Regular Audits: Conduct security audits to identify and fix vulnerabilities, as suggested by AI cybersecurity risk assessments.
- User Empowerment: Foster a culture where users feel responsible for cybersecurity.

Future Trends in Phishing Defense
The future of phishing defense lies in AI and machine learning. These technologies can analyze patterns and flag suspicious activities faster than traditional methods.
AI-Driven Solutions
- Behavioral Analysis: AI tools can monitor user behaviors to detect anomalies, as highlighted in AI-driven intrusion prevention systems.
- Automated Response Systems: Quickly isolate and mitigate threats without human intervention.
Best Practices for Phishing Prevention
- Enhance Email Security: Implement comprehensive email filtering solutions.
- User Education Programs: Regularly update training materials to cover new phishing tactics.
- Incident Response Plans: Develop and practice response plans for swift action against breaches.
Real-Time Monitoring
Set up dashboards to monitor ongoing threats and user activities, providing timely insights and alerts.

Conclusion: Staying Ahead of Phishing Threats
Phishing attacks will continue to evolve, but organizations can stay ahead by combining technology with user education. The Robinhood incident serves as a cautionary tale, emphasizing the need for vigilance and proactive measures.
Final Thoughts:
- Stay Informed: Keep up with the latest cybersecurity trends and threats, as noted in the IRS warning on AI-driven tax scams.
- Be Proactive: Implement robust security measures before an attack occurs.
FAQ
What is phishing?
Phishing is a cybercrime technique where attackers impersonate legitimate entities to steal sensitive information like passwords and credit card details.
How can I protect myself from phishing?
Use multi-factor authentication, verify email sources, and never click on suspicious links.
What should I do if I suspect a phishing email?
Report it to your IT department or email provider and do not engage with any content within the email.
How does AI help in phishing detection?
AI analyzes user behavior and email patterns to detect anomalies that may indicate phishing attempts.
Why is user education important in cybersecurity?
Educated users are more likely to recognize and report phishing attempts, reducing the success rate of such attacks.
What are the common signs of a phishing email?
Look for misspellings, suspicious links, and urgent requests for personal information.
Can phishing affect mobile devices?
Yes, phishing can target mobile devices through SMS (smishing) or malicious apps.
How often should I update my cybersecurity measures?
Regularly review and update your security protocols, ideally every quarter, or as new threats emerge.
What role does incident response play in cybersecurity?
Incident response helps mitigate damage and recover from breaches quickly and efficiently.
Key Takeaways
- Phishing scams exploit technical vulnerabilities and human psychology.
- Implementing multi-factor authentication can significantly reduce phishing risks.
- Regular user education is crucial for identifying and reporting phishing attempts.
- AI-driven tools enhance phishing detection and response capabilities.
- Proactive security measures are essential in preventing phishing attacks.
- Vigilance and continuous updates are key in maintaining cybersecurity.
Related Articles
- Understanding the Itron Cyberattack: Impacts and Lessons [2025]
- Understanding Cybersecurity Threats in the Medical Sector: Lessons from Recent Breaches [2025]
- Keeping AI Agents in Check: Preventing Unauthorized Use of Your Credit Cards [2025]
- Inside the New Cyber Scam: How Hackers Exploit Microsoft Teams to Steal Your Data [2025]
- Top Geekom Mini PC Deals for 2025: Ultimate Buying Guide
- How Amazon's Kindle Colorsoft Dark Mode Redefines Night Reading [2026]
![Understanding and Mitigating Phishing Scams: Lessons from the Robinhood Incident [2025]](https://tryrunable.com/blog/understanding-and-mitigating-phishing-scams-lessons-from-the/image-1-1777394277747.jpg)



