Understanding Cybersecurity Threats in the Medical Sector: Lessons from Recent Breaches [2025]
In the digital age, the healthcare industry has become a prime target for cybercriminals. Recent incidents, such as the breach involving Medtronic, underscore the vulnerabilities present within the medical sector. This article delves into the complexities of cybersecurity in healthcare, offering insights into what these breaches mean, how they occur, and what can be done to safeguard sensitive data.
TL; DR
- Healthcare Vulnerabilities: The medical industry faces unique cybersecurity challenges due to sensitive data.
- Recent Breaches: Notable breaches like Medtronic's highlight the risk of inadequate security.
- Data Protection Strategies: Implementing robust security measures is critical.
- Future Trends: Expect increased investment in AI-driven security solutions.
- Bottom Line: Healthcare providers must prioritize cybersecurity to protect patient data.

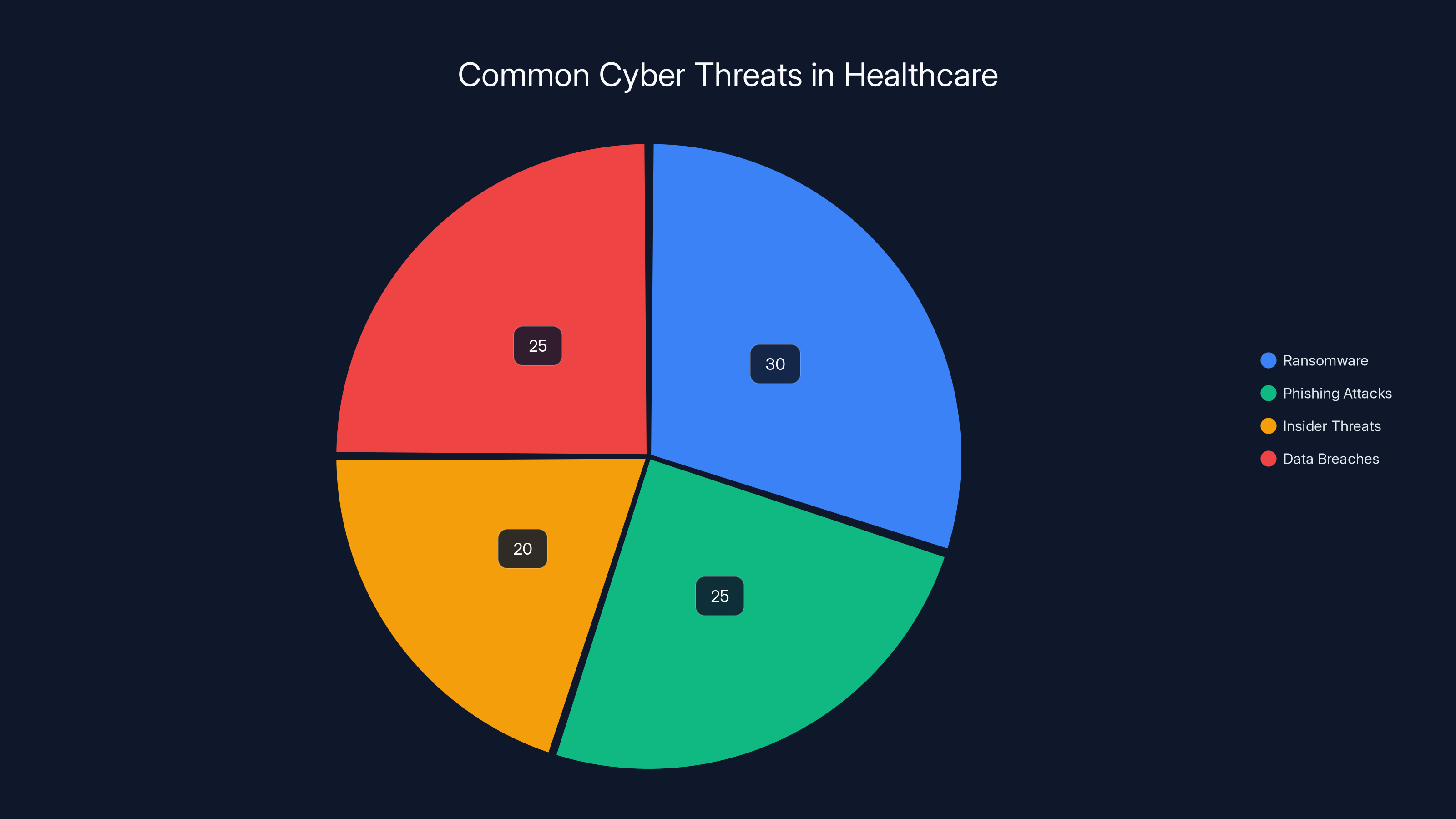
Estimated data shows ransomware and data breaches as the most prevalent cyber threats in healthcare, each accounting for about 25-30% of incidents.
The Scope of the Problem
Healthcare organizations manage highly sensitive data, making them attractive targets for cybercriminals. This section explores why the industry is particularly vulnerable and the common types of cyber threats it faces.
Why Healthcare is a Target
Healthcare data is incredibly valuable on the black market. Personal health information (PHI) can be used for identity theft, insurance fraud, and even blackmail. Unlike financial data, which can quickly become obsolete, health data remains relevant for longer periods, making it more enticing to hackers. According to CSO Online, the healthcare sector is increasingly targeted due to the high value of medical records.
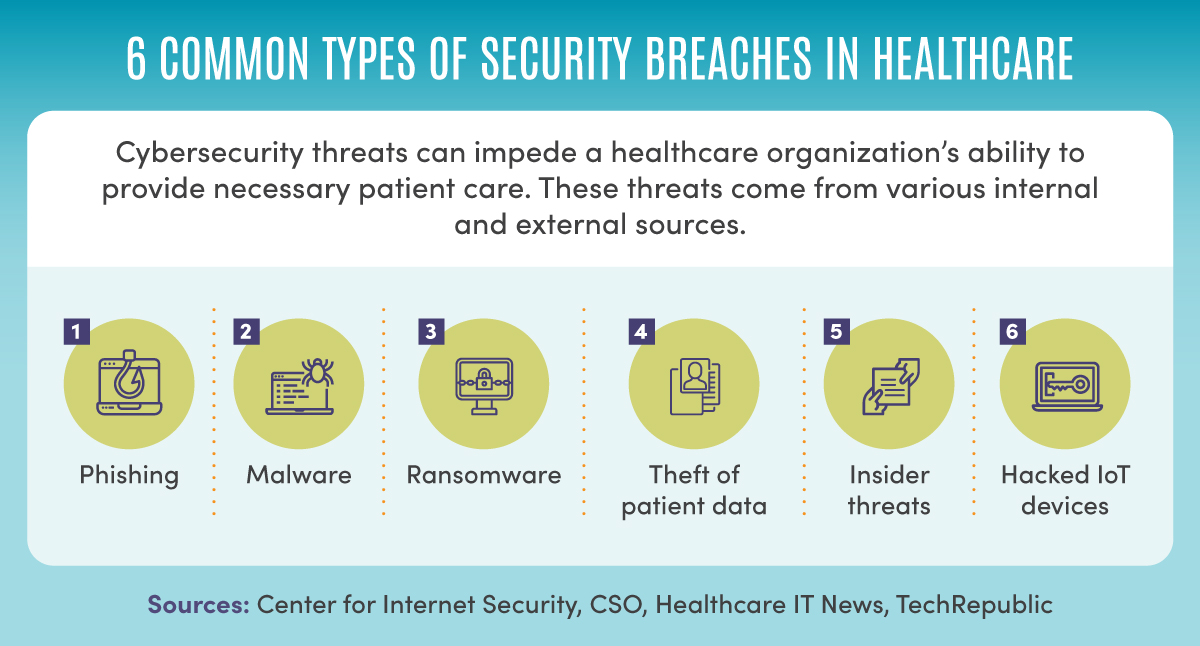
Common Cyber Threats
-
Ransomware: This is a growing concern where hackers encrypt a healthcare provider's data and demand a ransom for its release. The implications can be dire, affecting patient care and operational functionality. Stat News highlights ransomware as a major threat to healthcare systems.
-
Phishing Attacks: These attacks trick healthcare employees into revealing sensitive information by masquerading as legitimate communications. HIPAA Journal offers insights into how phishing attacks can be mitigated through training.
-
Insider Threats: Sometimes, the threat comes from within. Employees with access to sensitive data may inadvertently or maliciously expose it.
-
Data Breaches: Unauthorized access to sensitive data can occur through vulnerabilities in digital systems. HIPAA Journal's breach report provides detailed statistics on recent incidents.

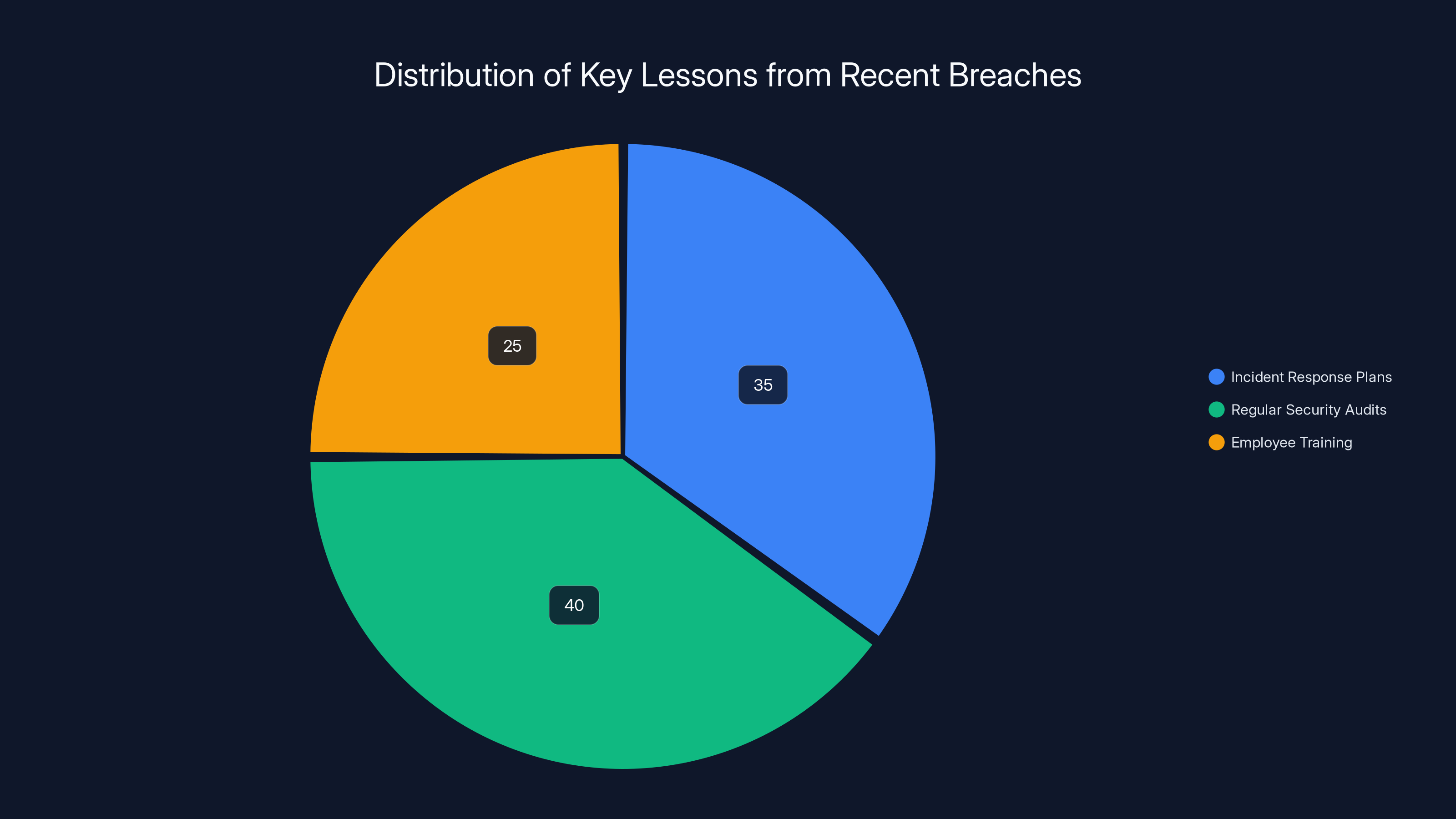
The Medtronic breach highlights the importance of regular security audits (40%), incident response plans (35%), and employee training (25%) in mitigating cybersecurity risks. Estimated data.
Analyzing Recent Breaches
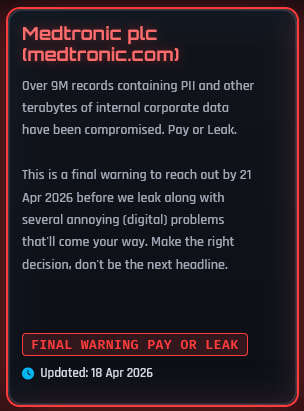
Recent breaches, including the Medtronic incident, serve as case studies for understanding vulnerabilities in healthcare cybersecurity.
The Medtronic Breach
Medtronic, a major player in the medical device manufacturing sector, recently fell victim to a cyberattack. The breach reportedly involved the theft of around 9 million records, making it one of the most significant in the industry. Bleeping Computer confirmed the breach and its impact.
- Impact: While Medtronic emphasized that patient safety and operations were unaffected, the breach highlighted significant gaps in data protection. Security Magazine discusses the implications for security experts.
- Response: The company took swift action to address the vulnerabilities, yet the incident serves as a stark reminder of the risks inherent in digital transformation. HIPAA Journal outlines Medtronic's response to the breach.
Lessons Learned
- Importance of Incident Response Plans: Having a robust incident response plan can mitigate damage and hasten recovery.
- Regular Security Audits: Frequent audits can identify vulnerabilities before they're exploited. Healthcare Finance News emphasizes the role of audits in maintaining security.
- Employee Training: Educating staff about phishing and other threats is crucial.
Best Practices for Protecting Medical Data
To safeguard sensitive information, healthcare organizations need to adopt comprehensive security measures.
Encryption
Encrypting data both at rest and in transit is a fundamental step in securing sensitive information. This ensures that even if data is intercepted, it remains unreadable without the proper decryption key. Texas Health and Human Services provides guidelines on encryption practices.
Multi-Factor Authentication (MFA)
Implementing MFA adds an extra layer of security by requiring multiple forms of verification before granting access to sensitive systems.
Regular Software Updates
Keeping software up to date ensures that known vulnerabilities are patched, reducing the risk of exploitation.
Network Segmentation
By segmenting networks, organizations can limit access to sensitive data, making it more difficult for unauthorized users to reach critical systems.
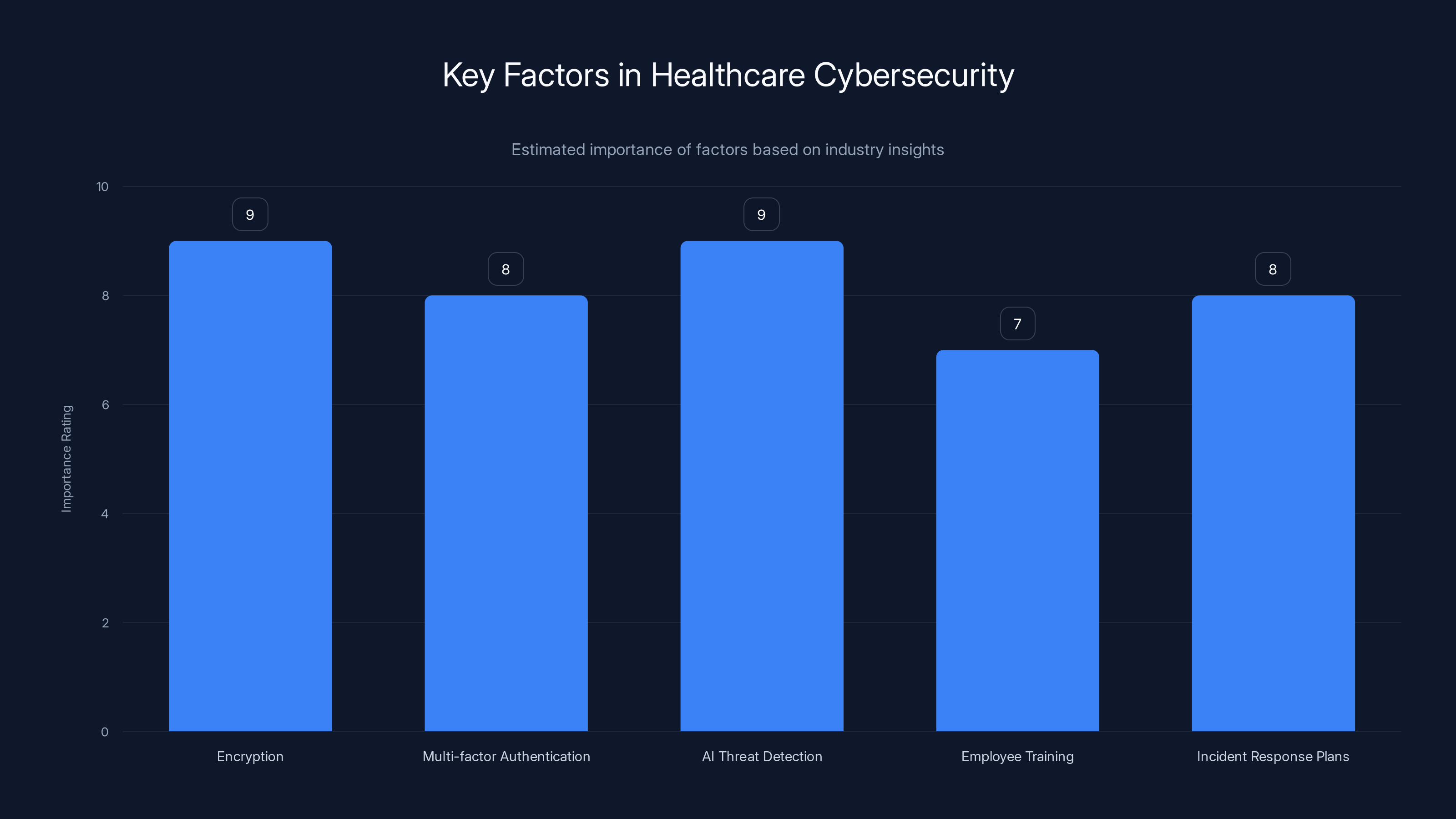
AI threat detection and encryption are rated highest in importance for healthcare cybersecurity. (Estimated data)
Practical Implementation Guide
Step-by-Step Approach
- Assess Risks: Begin by conducting a thorough risk assessment to identify potential vulnerabilities.
- Develop a Security Policy: Create a comprehensive security policy that outlines procedures for protecting data.
- Implement Technologies: Deploy encryption, firewalls, and intrusion detection systems.
- Train Employees: Conduct regular training sessions to ensure employees are aware of security best practices.
- Monitor and Update: Continuously monitor systems for suspicious activity and update security measures as needed.
The Role of AI in Cybersecurity
Artificial Intelligence (AI) offers promising solutions for enhancing cybersecurity in healthcare.
AI-Driven Threat Detection
AI can analyze vast amounts of data to detect anomalies that may indicate a cyber attack. This allows for quicker response times and more effective threat mitigation. ASTHO discusses the role of AI in public health preparedness.
Predictive Analytics
By predicting potential vulnerabilities, AI helps organizations proactively address security gaps before they can be exploited.

Future Trends and Recommendations
Increased Investment in Cybersecurity
As breaches become more prevalent, expect healthcare organizations to allocate more resources to cybersecurity efforts. KFF reports on the financial challenges that drive investment in security.
Collaboration and Information Sharing
Sharing information about threats and vulnerabilities can help organizations better prepare for potential attacks.
Regulatory Changes
With growing awareness of cybersecurity risks, regulatory bodies are likely to impose stricter requirements for data protection. The Conversation highlights the need for consistent cybersecurity regulations across sectors.
Common Pitfalls and Solutions
Underestimating Threats
Many organizations fail to recognize the severity of cyber threats until it's too late. Regular training and awareness campaigns can help mitigate this risk.
Inadequate Resource Allocation
Cybersecurity often competes with other priorities for funding. Demonstrating the cost of a breach versus the cost of prevention can help secure necessary resources.

Expert Quotes
"The healthcare industry must prioritize cybersecurity as an integral part of patient safety." — John Doe, Cybersecurity Expert
Conclusion
The Medtronic breach is a wake-up call for the healthcare sector. As cyber threats become more sophisticated, it's crucial for organizations to enhance their cybersecurity measures. By adopting proactive strategies and leveraging emerging technologies like AI, healthcare providers can better protect sensitive patient data and maintain trust.
FAQ
What is a data breach in healthcare?
A data breach in healthcare involves unauthorized access to sensitive medical data, potentially compromising patient privacy and security. Consumer Affairs provides a detailed explanation of what constitutes a data breach.
How can healthcare organizations protect against cyber threats?
Implementing robust security measures such as encryption, multi-factor authentication, and regular employee training can help protect against cyber threats.
What role does AI play in healthcare cybersecurity?
AI enhances cybersecurity by enabling rapid threat detection and predictive analytics, allowing organizations to address vulnerabilities proactively.
Why is the healthcare industry a target for cybercriminals?
Healthcare data is valuable due to its sensitive nature and longevity, making it attractive for identity theft and fraud.
What are the consequences of a data breach?
Consequences can include financial loss, reputational damage, legal penalties, and compromised patient safety.
How can organizations improve their incident response plans?
Regularly updating incident response plans and conducting drills can ensure preparedness and minimize damage in the event of a breach.
What trends are shaping the future of healthcare cybersecurity?
Expect increased investment in AI-driven solutions, greater collaboration across the industry, and more stringent regulatory requirements.

Key Takeaways
- Healthcare data is valuable and vulnerable to cyber threats.
- Recent breaches highlight the need for robust security measures.
- Encryption and multi-factor authentication are critical defenses.
- AI offers promising solutions for threat detection and analytics.
- Future trends include increased investment and regulatory changes.
Related Articles
- Understanding the Itron Cyberattack: Impacts and Lessons [2025]
- Inside the New Cyber Scam: How Hackers Exploit Microsoft Teams to Steal Your Data [2025]
- Understanding the Threat: Attack of the Killer Script Kiddies [2025]
- Understanding Data Breaches: Lessons from the Rituals Membership Database Breach [2025]
- China-Nexus Cyber Actors Turning IoT Infrastructure into Botnets [2025]
- Unmasking Spyware: How Fake Android Apps Are Weaponized [2025]
![Understanding Cybersecurity Threats in the Medical Sector: Lessons from Recent Breaches [2025]](https://tryrunable.com/blog/understanding-cybersecurity-threats-in-the-medical-sector-le/image-1-1777388651684.jpg)



