Inside the New Cyber Scam: How Hackers Exploit Microsoft Teams to Steal Your Data [2025]
Introduction
Cybersecurity is a never-ending battle of wits between defenders and attackers. In the latest twist, hackers have found a novel way to exploit Microsoft Teams, a tool many organizations rely on for seamless communication. This article delves into the intricacies of this new cyber scam, exploring how it works, its impact, and what you can do to protect your data.


Investing in AI-powered security solutions and staying informed are estimated to have the highest impact on organizational security. Estimated data.
TL; DR
- New Scam Alert: Hackers are using Microsoft Teams to infiltrate organizations, as highlighted in a TechRadar report.
- Social Engineering: They send fake IT support messages to gain trust, a tactic detailed in Microsoft's security blog.
- Data Theft: Once inside, they steal sensitive information and credentials.
- Prevention Tips: Implement multi-factor authentication and employee training.
- Future Trends: Expect more sophisticated social engineering tactics.
Understanding the New Cyber Scam
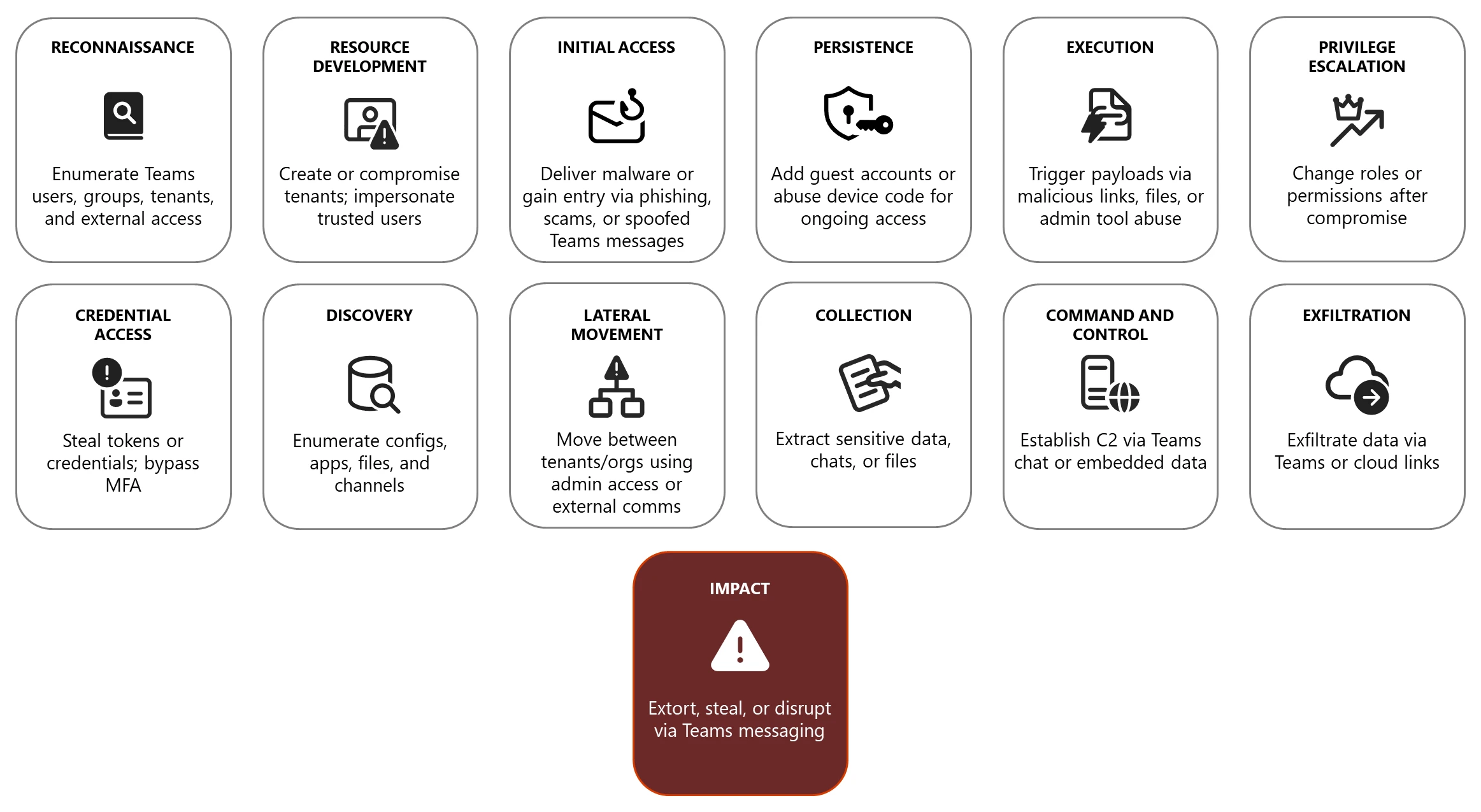
The latest cyber scam involves hackers using Microsoft Teams to infiltrate organizations. It's a clever tactic that leverages the trust many employees have in their company's communication tools. Here's how it typically unfolds:
- Initial Contact: Hackers flood an organization's Microsoft Teams with spam messages, posing as IT support or other trusted entities, as noted in LinkedIn insights.
- Gaining Trust: These messages often include urgent requests for action, such as resetting passwords or updating software.
- Stealthy Infiltration: Once an employee responds, hackers use social engineering to extract credentials or install malware.
- Data Exfiltration: With access secured, they can steal sensitive data or gain further access to the organization's systems.

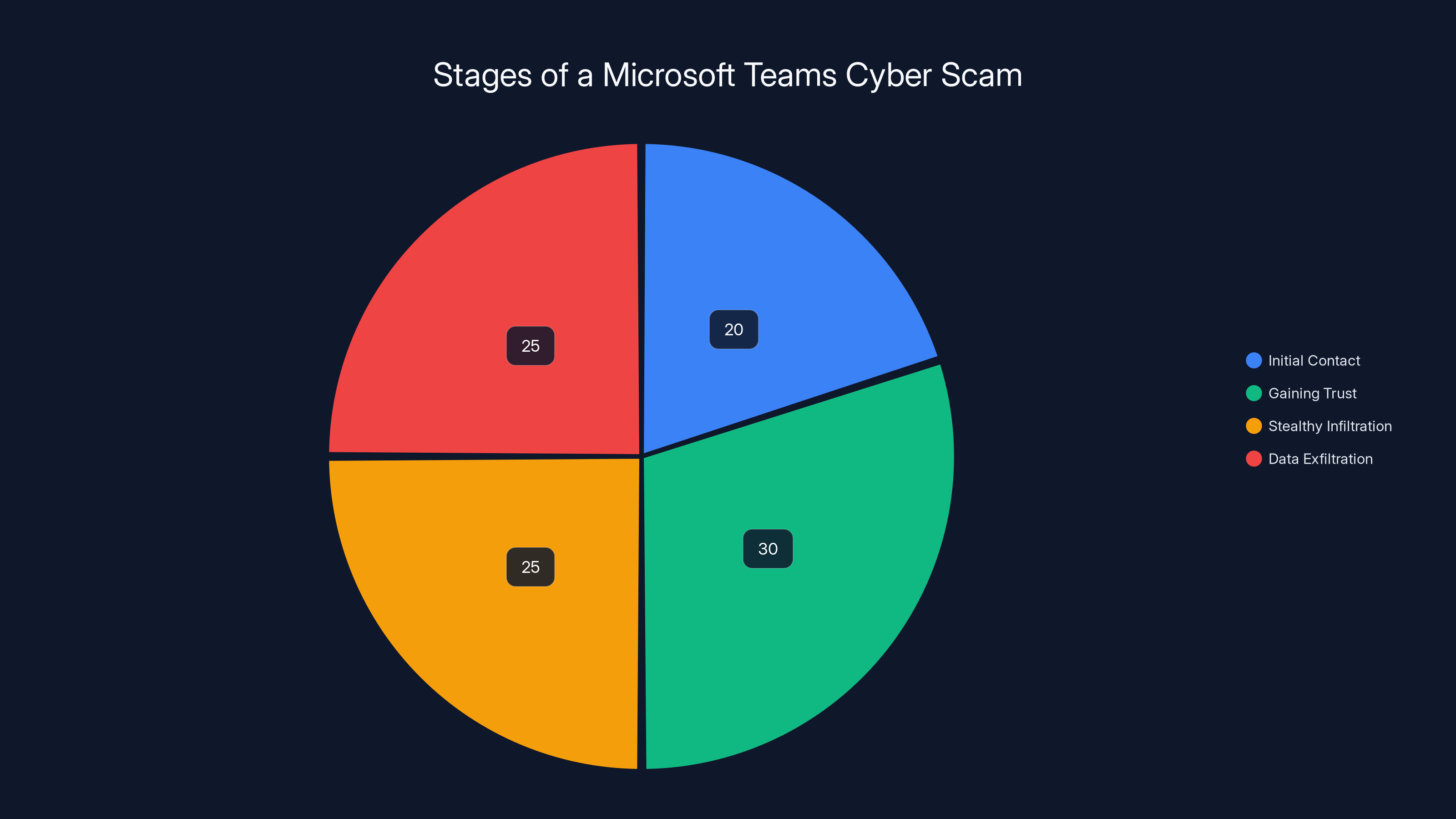
The 'Gaining Trust' stage is estimated to take the most time, as hackers work to convince employees to take action. Estimated data.
How Hackers Exploit Microsoft Teams
Microsoft Teams is widely used in corporate environments, making it an attractive target for cybercriminals. The platform's integration with other Microsoft services and its broad adoption create numerous attack vectors, as explained in Microsoft's analysis of phishing campaigns.
Social Engineering at Its Core
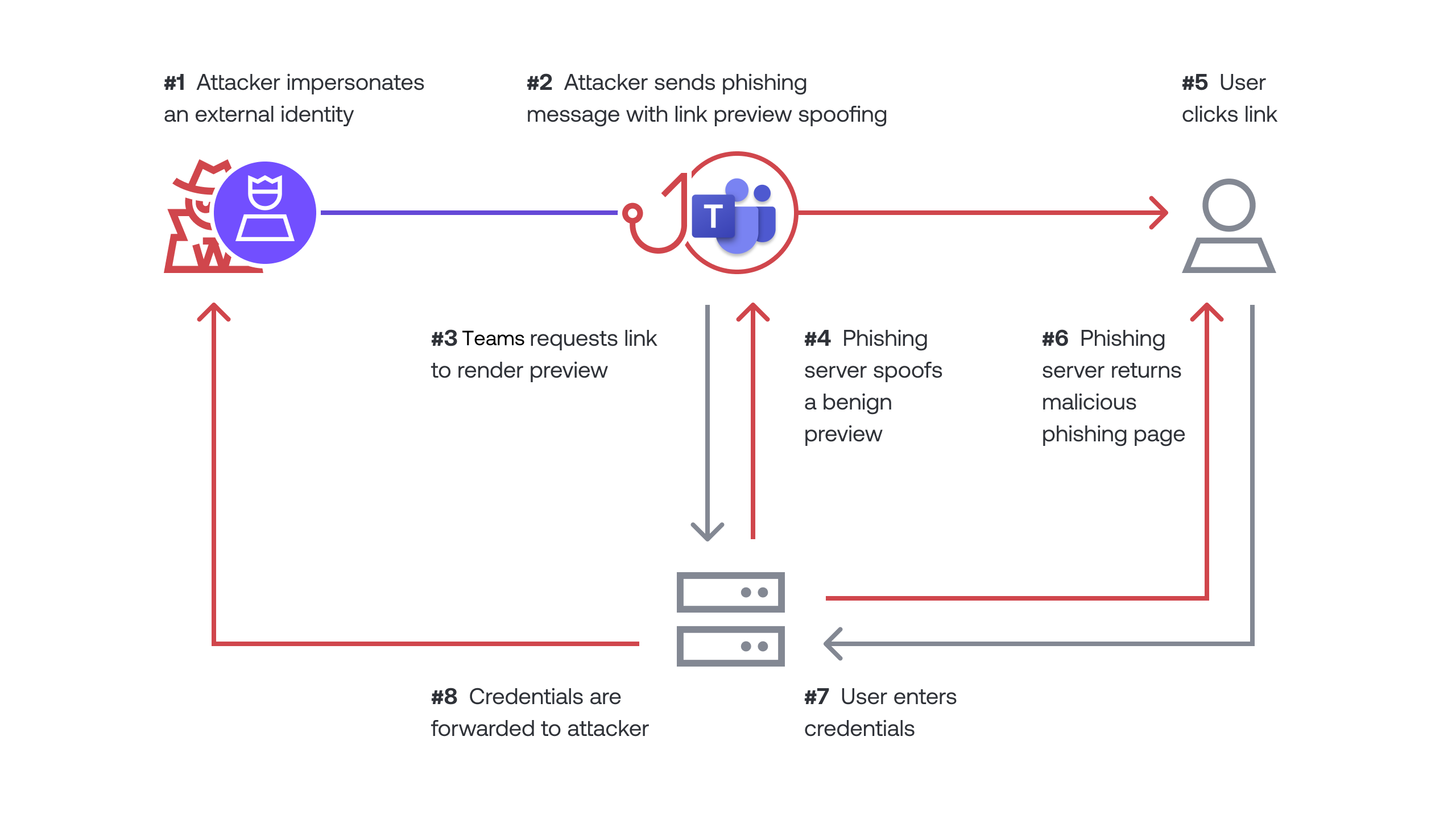
At the heart of this scam is social engineering—a technique that manipulates people into divulging confidential information. Hackers craft messages that mimic legitimate communications, often using logos, names, and writing styles familiar to the target.
Example Scenario:
Imagine an employee receives a message from what appears to be the IT department, asking for their login details to resolve a network issue. The message looks official, complete with the company logo and a familiar IT support name. Trusting the source, the employee complies, inadvertently handing over their credentials to the attacker.
Abuse of Trusted Platforms
Microsoft Teams is trusted by millions of users worldwide, which makes it a prime vector for scams. Hackers exploit this trust by embedding malicious links in messages. When clicked, these links can download malware or direct users to phishing sites designed to capture sensitive information, as reported by TechRadar.
Common Pitfalls and Solutions
Pitfall 1: Lack of Employee Training
Many organizations fail to adequately train their employees on cybersecurity best practices. This oversight can leave them vulnerable to social engineering attacks.
Solution: Implement regular cybersecurity training sessions that cover the latest threats, phishing tactics, and safe communication practices.
Pitfall 2: Weak Authentication Protocols
Relying solely on passwords for authentication is a significant security risk.
Solution: Adopt multi-factor authentication (MFA) across all platforms. MFA adds an additional layer of security, making it harder for hackers to gain access even if they have a user's password.
Pitfall 3: Inadequate Monitoring
Without proper monitoring, suspicious activities can go unnoticed until it's too late.
Solution: Use advanced monitoring tools to track interactions on Microsoft Teams. Look for unusual patterns such as multiple failed login attempts or messages sent from unfamiliar locations, as suggested by Microsoft's detection strategies.

Best Practices for Securing Microsoft Teams
- Regularly Update Software: Ensure that all software, including Microsoft Teams, is up-to-date with the latest security patches.
- Restrict Access: Limit permissions to sensitive data and systems. Only allow access to those who need it for their job.
- Implement Strong Password Policies: Encourage the use of complex passwords and regular updates.
- Conduct Phishing Simulations: Test employee awareness with simulated phishing attacks to identify vulnerabilities.
- Utilize Security Tools: Employ tools that can detect and prevent suspicious activities within Microsoft Teams.
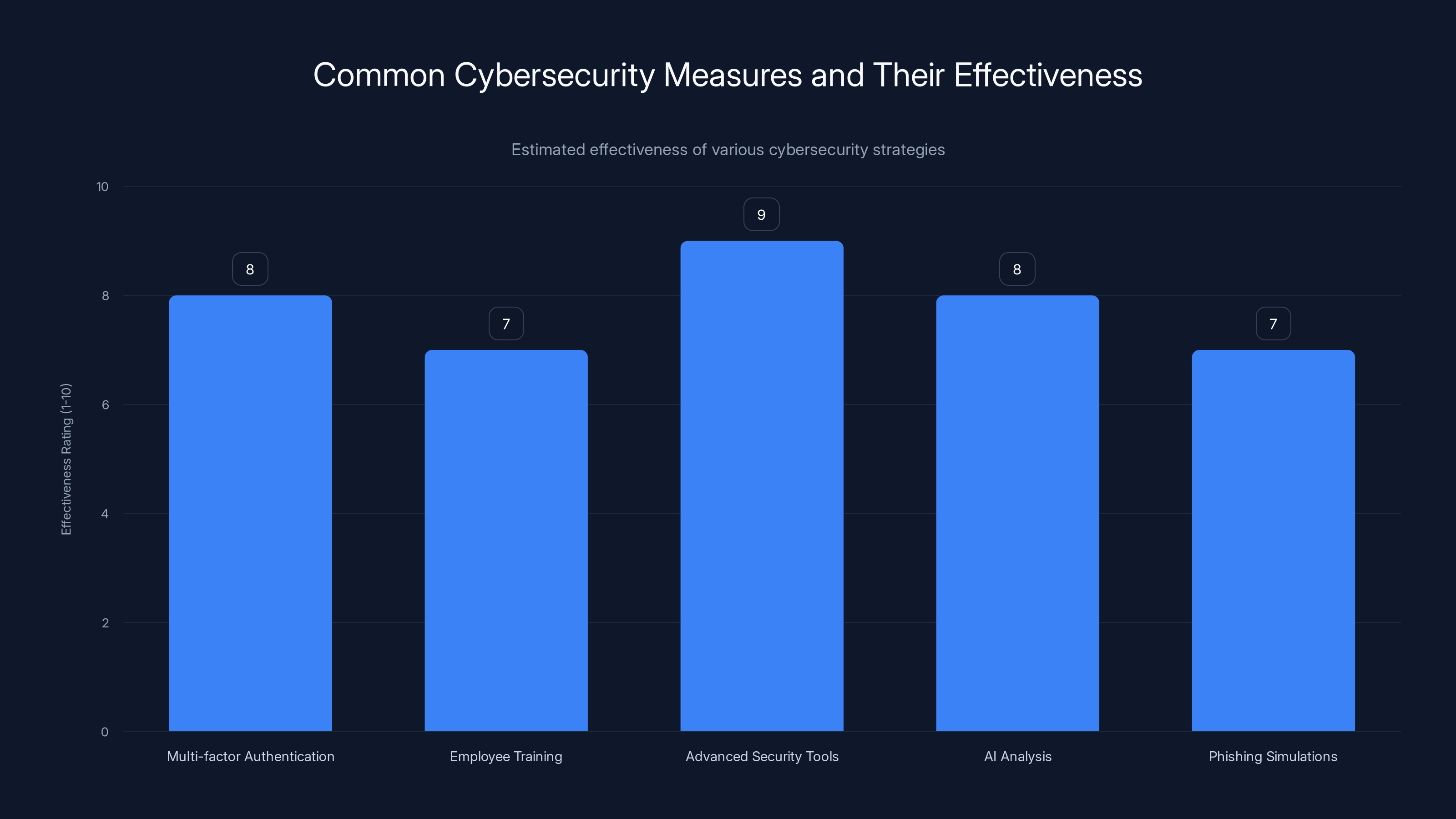
Implementing advanced security tools and AI analysis are rated as highly effective measures in combating cyber threats. Estimated data.
Future Trends in Cybersecurity
Increasing Sophistication of Social Engineering
As cybersecurity measures become more advanced, so do the tactics of cybercriminals. Expect social engineering attacks to become more sophisticated, leveraging AI to craft highly personalized messages that are harder to distinguish from legitimate communications.
The Rise of AI in Cybersecurity
AI and machine learning will play a crucial role in the future of cybersecurity. These technologies can analyze vast amounts of data quickly, identifying patterns and anomalies that may indicate a security threat, as noted in Microsoft's blog on AI-enabled phishing.
Example: An AI-driven system could flag a message as suspicious if it detects unusual phrasing or if the sender's behavior deviates from the norm.
Recommendations for Organizations
- Invest in AI-Powered Security Solutions: These tools can help detect and respond to threats in real-time.
- Encourage a Culture of Security: Make cybersecurity a priority in your organization's culture. Encourage employees to report suspicious activities without fear of repercussions.
- Stay Informed: Keep up with the latest cybersecurity trends and threats. Regularly review and update security policies to address new challenges.

Conclusion
The evolving tactics of cybercriminals pose a significant threat to organizations worldwide. By understanding the strategies they use and implementing robust security measures, you can protect your data and maintain the integrity of your communication platforms. As technology continues to advance, staying informed and proactive is your best defense against these ever-changing threats.

FAQ
What is social engineering in cybersecurity?
Social engineering is a tactic used by cybercriminals to manipulate individuals into divulging confidential information, often by impersonating trusted sources.
How can I protect my organization from cyber scams?
Implement multi-factor authentication, conduct regular employee training, and use advanced security tools to detect suspicious activities.
Why is Microsoft Teams a target for hackers?
Microsoft Teams is widely used in corporate environments, making it a lucrative target for cybercriminals looking to access sensitive data, as discussed in Healthcare Dive's analysis.
What role does AI play in cybersecurity?
AI can analyze large volumes of data to detect patterns and anomalies, helping to identify potential security threats in real-time.
How can phishing simulations help improve security?
Phishing simulations test employee awareness and identify vulnerabilities, allowing organizations to address weaknesses and improve overall security.
What are the future trends in cybersecurity?
Expect more sophisticated social engineering tactics and the increased use of AI and machine learning to enhance security measures.

Key Takeaways
- Cybercriminals are exploiting Microsoft Teams to steal data through social engineering.
- Multi-factor authentication is crucial for protecting against unauthorized access.
- Employee training and awareness are essential in preventing cyber scams.
- AI and machine learning will play a significant role in future cybersecurity strategies.
- Organizations must stay informed and proactive to defend against evolving threats.

Related Articles
- AI Automation Guide
- Cybersecurity Best Practices for 2025
- Understanding Social Engineering Tactics

Related Articles
- Discord Sleuths Gained Unauthorized Access to Anthropic’s Mythos | WIRED
- Why Your IT Helpdesk is Getting Weird Calls: LinkedIn Data Threats [2025]
- Understanding Data Breaches: Lessons from the Rituals Membership Database Breach [2025]
- China-Nexus Cyber Actors Turning IoT Infrastructure into Botnets [2025]
- Unmasking Spyware: How Fake Android Apps Are Weaponized [2025]
- Anthropic’s Mythos Breach: Lessons Learned and Future Implications [2025]
![Inside the New Cyber Scam: How Hackers Exploit Microsoft Teams to Steal Your Data [2025]](https://tryrunable.com/blog/inside-the-new-cyber-scam-how-hackers-exploit-microsoft-team/image-1-1777287995974.jpg)



