Understanding the Impact of DDoS Attacks on Ubuntu Services [2025]
Distributed Denial of Service (DDoS) attacks are a notorious threat in the cybersecurity landscape, often causing significant disruptions to online services. Recently, Ubuntu services experienced a major outage following a DDoS attack, leading to widespread disruptions in installations, updates, and even impacting Canonical's web infrastructure. This article dives deep into the mechanics of such attacks, their impact on Ubuntu services, and provides expert-level insights into mitigation strategies.
TL; DR
- DDoS attacks can severely disrupt Ubuntu services, affecting installs and updates.
- Ubuntu's web infrastructure was significantly impacted, highlighting vulnerabilities in current systems.
- Mitigation strategies include robust network architecture and proactive monitoring.
- Future trends suggest an increase in sophisticated attack methods.
- Key takeaway: Strengthening cybersecurity measures is crucial to maintaining service continuity.

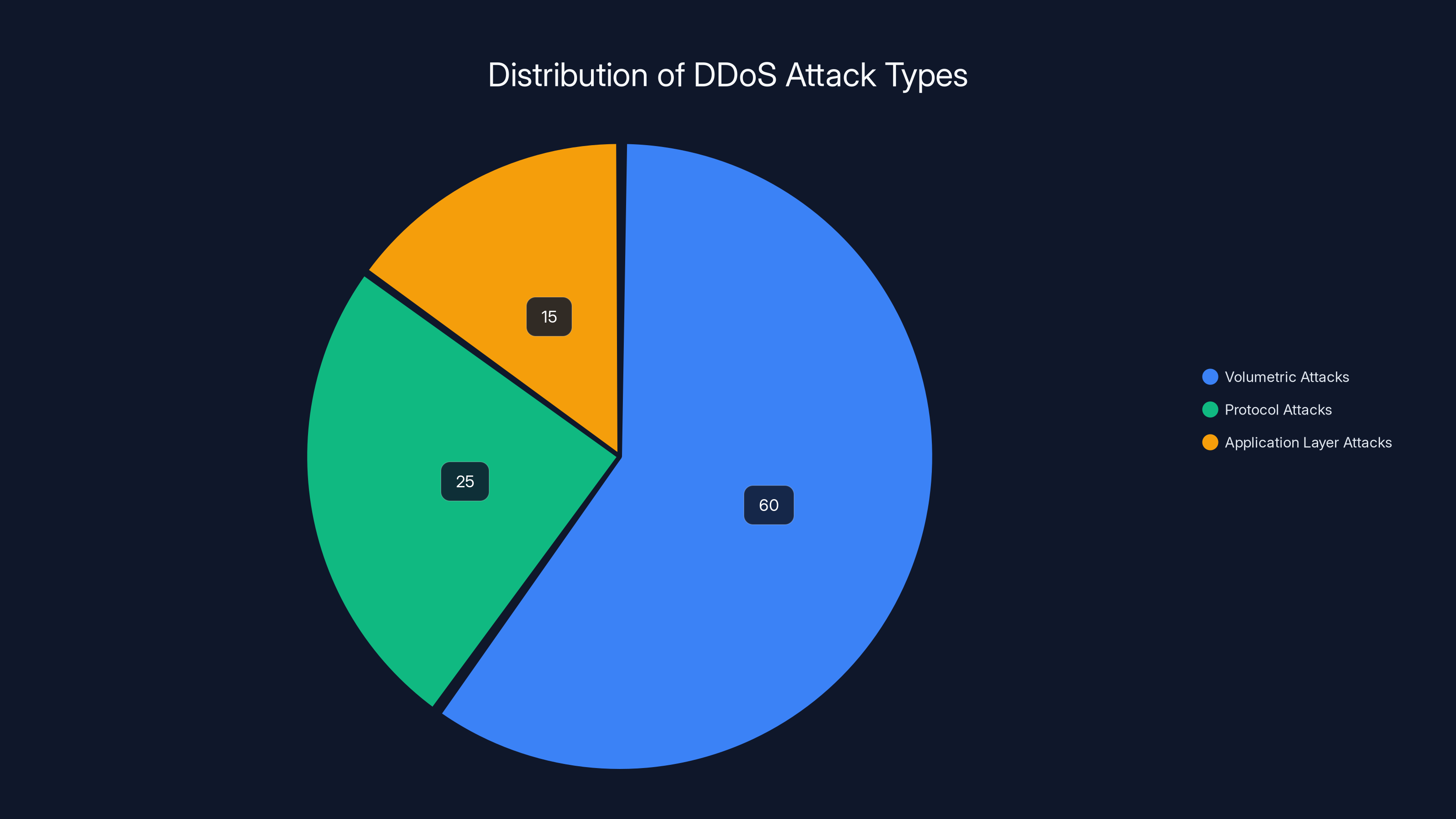
Volumetric attacks are the most common, making up an estimated 60% of DDoS attacks, followed by protocol and application layer attacks. Estimated data.
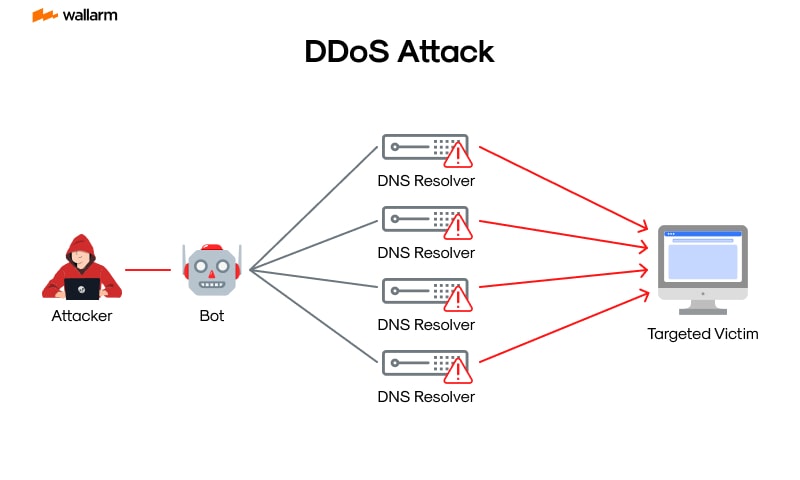
The Anatomy of DDoS Attacks
DDoS attacks involve overwhelming a server, service, or network with a flood of internet traffic. This results in legitimate users being unable to access the services. These attacks are often executed using a network of compromised computers, known as a botnet, which are controlled remotely by attackers. According to BitSight's analysis, botnets like Rondodox are frequently used in such attacks.
How DDoS Attacks Work
- Botnet Creation: Attackers infect computers with malware to create a botnet.
- Command and Control: The botnet is controlled remotely by the attacker through a Command and Control (C&C) server.
- Traffic Flooding: The botnet is instructed to send a flood of requests to the target, overwhelming its capacity.
Types of DDoS Attacks
- Volumetric Attacks: Consume bandwidth by sending massive amounts of data to the target.
- Protocol Attacks: Exploit vulnerabilities in protocols like TCP/IP to disrupt services.
- Application Layer Attacks: Target specific applications with requests that mimic legitimate traffic.
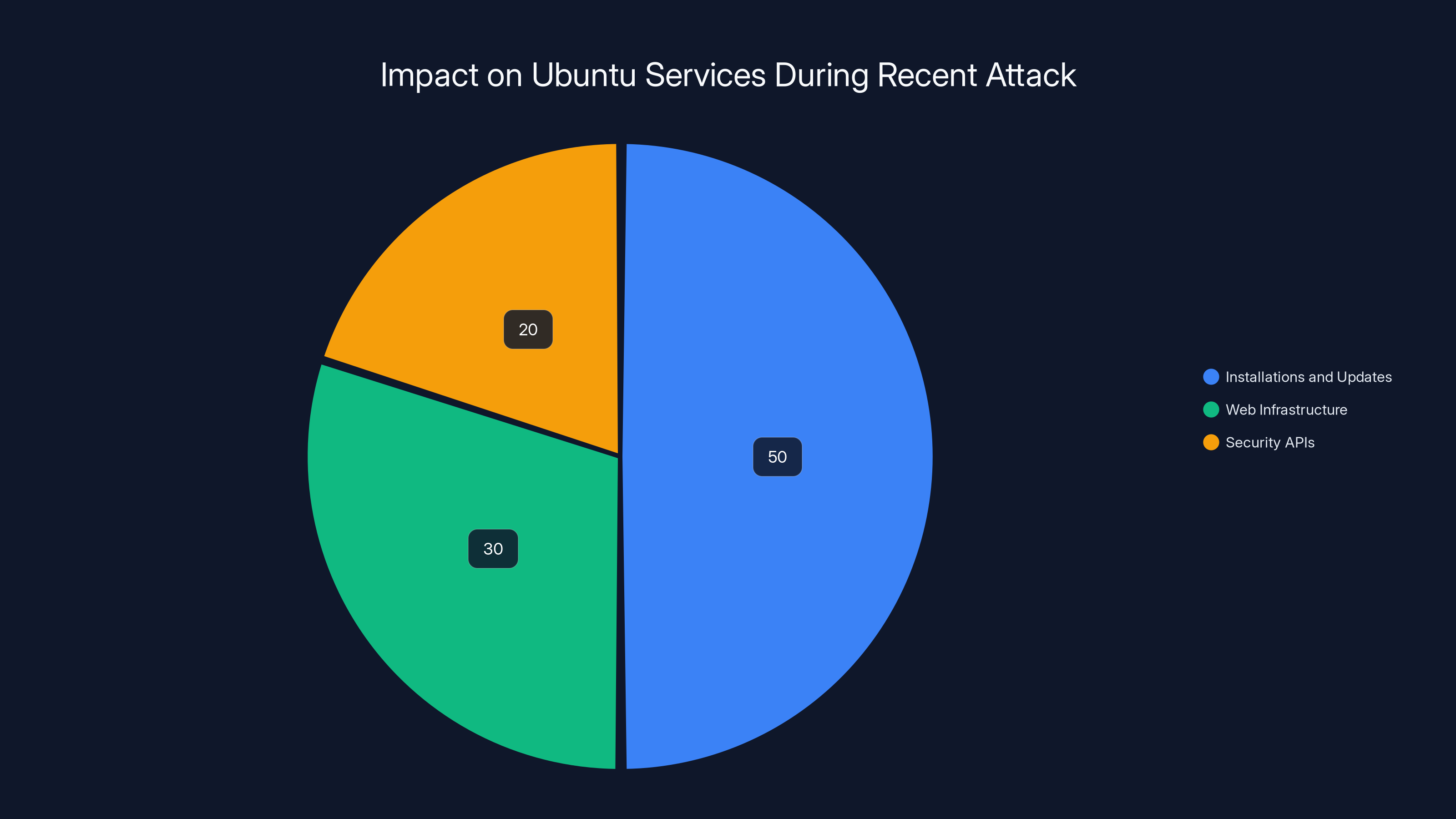
Estimated data shows that installations and updates were the most affected, constituting 50% of the disruption, followed by web infrastructure and security APIs.
Impact on Ubuntu Services
The recent attack on Ubuntu services illustrates the potential for disruption. Key services such as updates and installations were affected, causing inconvenience for users and administrators. Canonical's web infrastructure experienced significant downtime, as reported by eSecurity Planet.
Affected Services
- Installations and Updates: Users faced delays and failures when attempting to install or update Ubuntu packages.
- Canonical's Web Infrastructure: Websites and security APIs experienced downtime.
Real-World Example
Consider a company relying on Ubuntu for its server infrastructure. During the attack, critical updates were delayed, exposing the servers to potential security vulnerabilities.
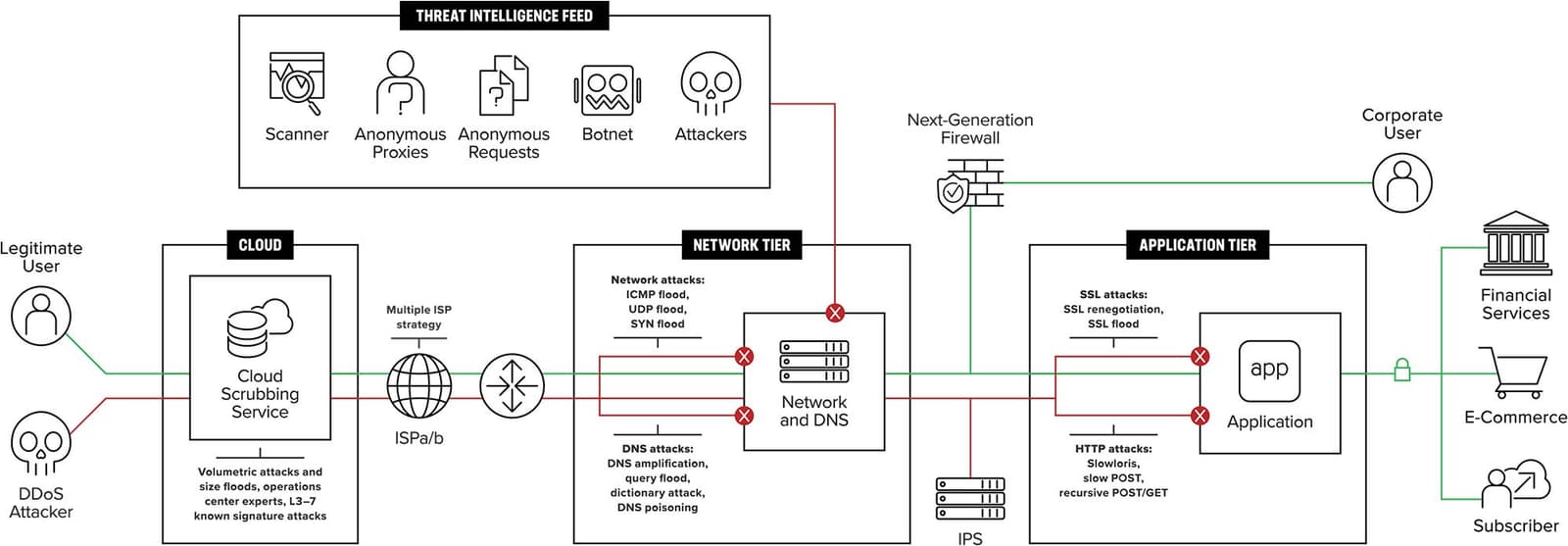
Mitigating DDoS Attacks
Effective mitigation requires a combination of preventive measures and responsive strategies.
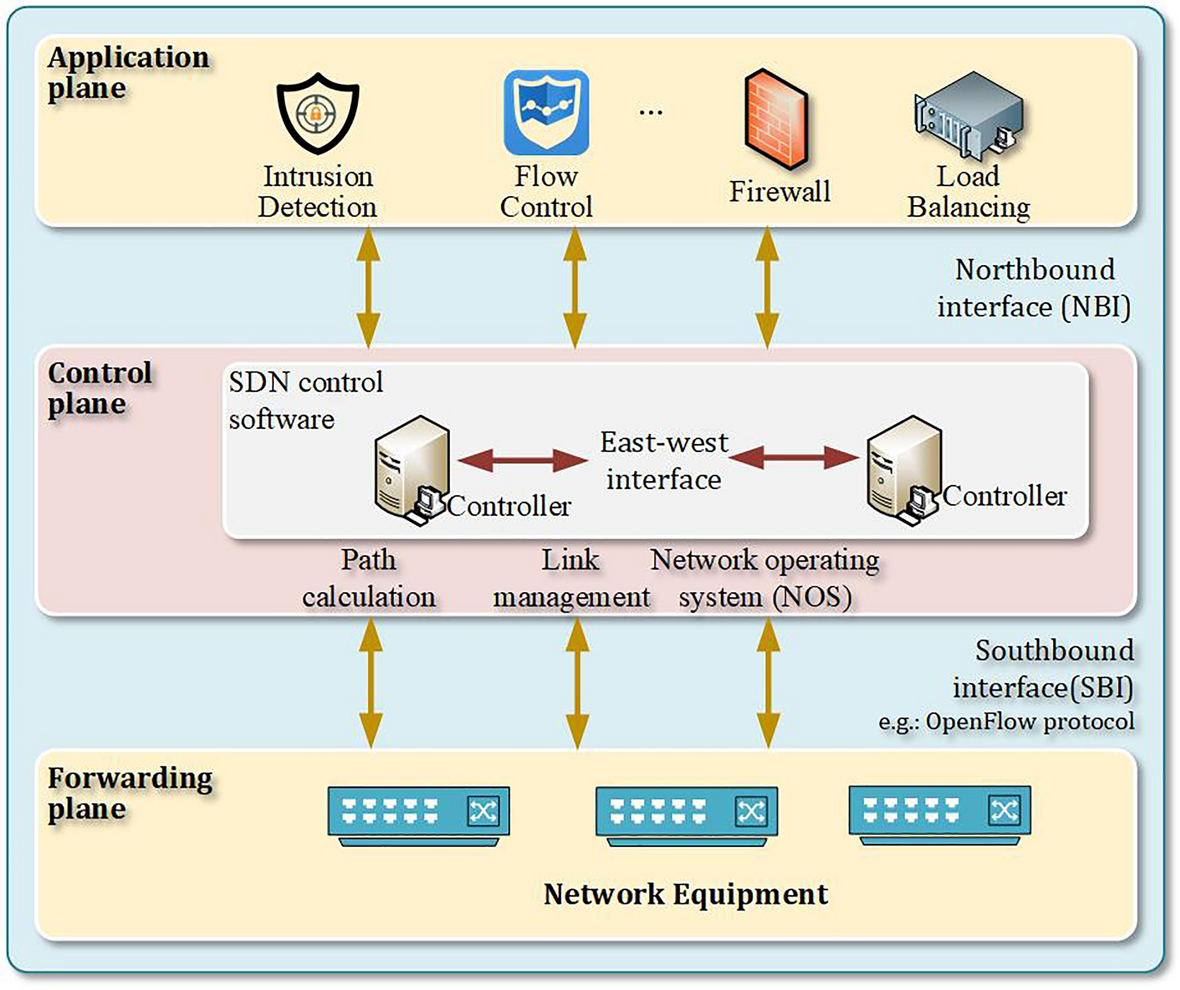
Best Practices for Mitigation
- Network Architecture: Implement redundant and geographically dispersed servers to distribute load.
- Traffic Filtering: Use firewalls and intrusion detection systems to identify and block malicious traffic.
- Rate Limiting: Limit the number of requests from a single IP to prevent overwhelming the server.
Tools and Technologies
- Content Delivery Networks (CDNs): Distribute traffic across multiple servers to reduce the impact of an attack.
- Load Balancers: Distribute incoming traffic evenly across servers.
- DDoS Protection Services: Services like Cloudflare and Akamai offer specialized DDoS mitigation solutions.
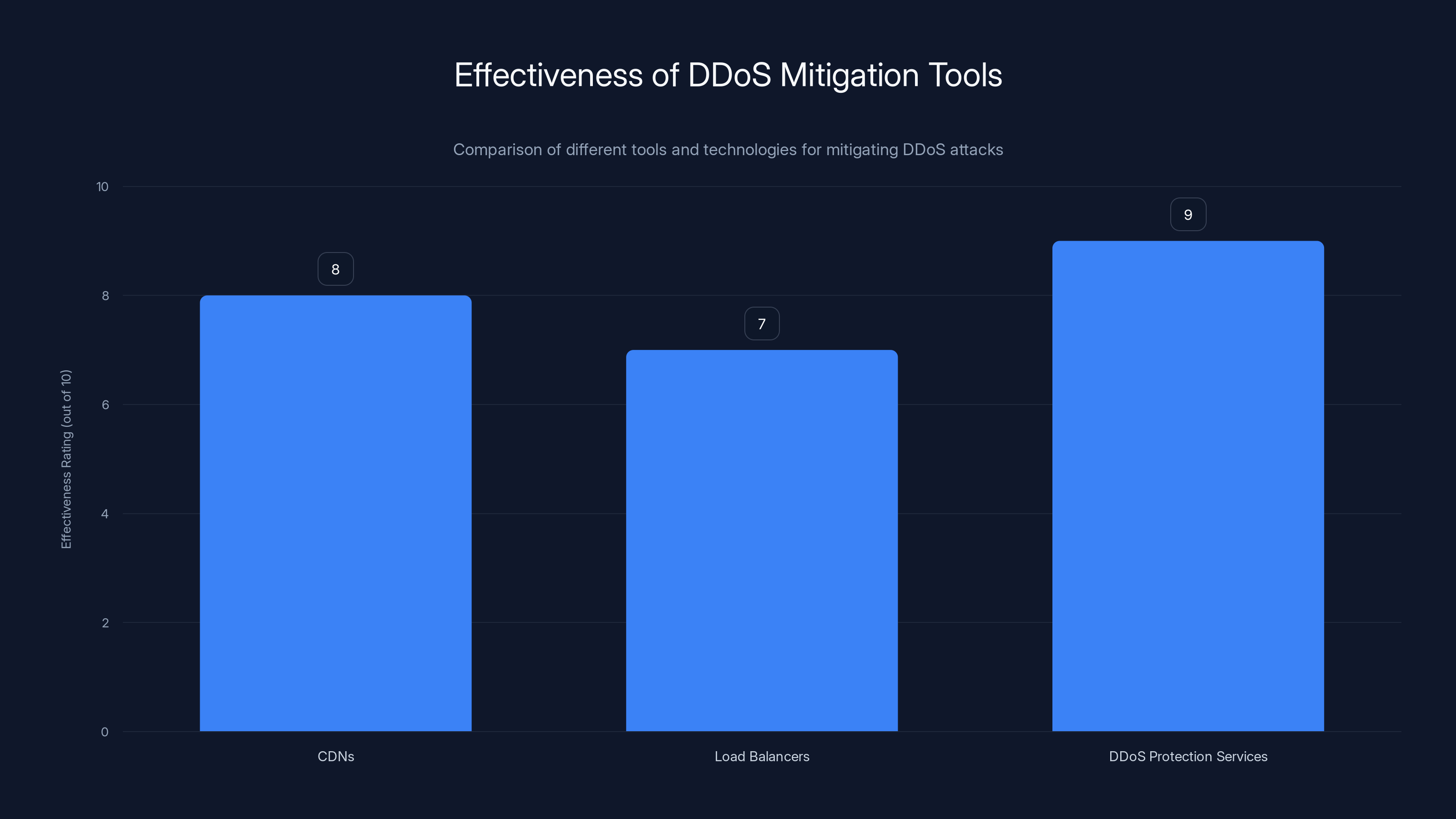
DDoS Protection Services are rated highest in effectiveness, followed by CDNs and Load Balancers. Estimated data based on typical industry assessments.
Common Pitfalls and Solutions
While implementing mitigation strategies, organizations often encounter challenges.
Pitfall 1: Insufficient Monitoring
Solution: Utilize advanced monitoring tools to detect anomalies in traffic patterns early.
Pitfall 2: Over-reliance on a Single Solution
Solution: Employ a multi-layered defense strategy, combining different technologies and practices.
Future Trends in DDoS Attacks
As technology evolves, so do the tactics of attackers. The future landscape of DDoS attacks is expected to be characterized by increased sophistication. ENISA's updated NCAF 2.0 highlights the need for enhanced cybersecurity measures to address these evolving threats.
Emerging Threats
- IoT Botnets: With the proliferation of IoT devices, attackers have more endpoints to compromise.
- AI and Machine Learning: Attackers are leveraging AI to craft more effective and adaptive attacks.
Recommendations for the Future
- Invest in Research and Development: Stay ahead of attackers by continuously improving security technologies.
- Collaborate with Industry Peers: Share information and strategies to build a united defense against DDoS attacks.
Conclusion
The recent DDoS attack on Ubuntu services serves as a stark reminder of the vulnerabilities inherent in our digital infrastructure. By understanding the mechanics of these attacks and implementing robust mitigation strategies, organizations can better protect themselves from future disruptions. As attackers continue to evolve, so too must our defenses. Krebs on Security emphasizes the importance of staying vigilant and proactive in the face of these threats.
Use Case: Optimize your Ubuntu server security with automated DDoS protection using Runable's AI-powered platform.
Try Runable For Free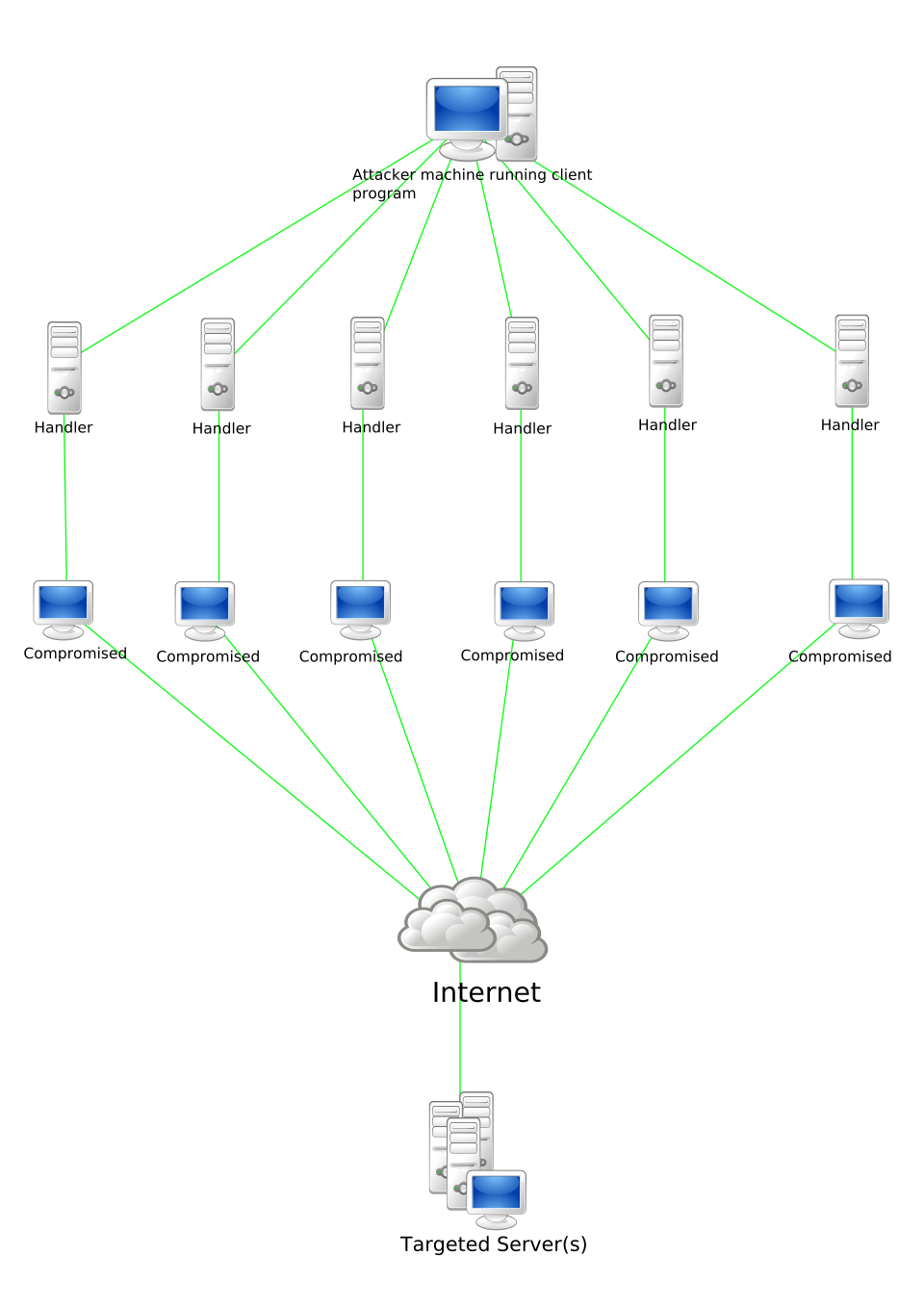
Key Takeaways
- DDoS attacks can severely impact service availability and user experience.
- Implementing robust network architecture is crucial for mitigating DDoS attacks.
- Proactive monitoring and response can minimize the impact of attacks.
- Future DDoS attacks are expected to become more sophisticated with AI and IoT.
- Collaborative efforts and information sharing can strengthen defense strategies.
Related Articles
- Hackers Drove Through Toronto with Fake Cell Towers, Hijacking Thousands of Phones [2025]
- Dangerous New Linux Exploit Gives Attackers Root Access to Countless Computers | WIRED
- AI is Scaling a Billion-Dollar Fraud Problem, and You’re the Victim [2025]
- How Canada Uses Canary Traps for Election Security: An In-Depth Analysis [2025]
- AI-Generated Phishing Attacks: Beyond the Inbox and How to Protect Yourself [2025]
- Autonomous AI Tools Revolutionize Pentagon Operations [2025]
FAQ
What is Understanding the Impact of DDoS Attacks on Ubuntu Services [2025]?
Distributed Denial of Service (DDoS) attacks are a notorious threat in the cybersecurity landscape, often causing significant disruptions to online services.
What does tl; dr mean?
Recently, Ubuntu services experienced a major outage following a DDoS attack, leading to widespread disruptions in installations, updates, and even impacting Canonical's web infrastructure.
Why is Understanding the Impact of DDoS Attacks on Ubuntu Services [2025] important in 2025?
This article dives deep into the mechanics of such attacks, their impact on Ubuntu services, and provides expert-level insights into mitigation strategies.
How can I get started with Understanding the Impact of DDoS Attacks on Ubuntu Services [2025]?
- DDoS attacks can severely disrupt Ubuntu services, affecting installs and updates.
What are the key benefits of Understanding the Impact of DDoS Attacks on Ubuntu Services [2025]?
- Ubuntu's web infrastructure was significantly impacted, highlighting vulnerabilities in current systems.
What challenges should I expect?
- Mitigation strategies include robust network architecture and proactive monitoring.
![Understanding the Impact of DDoS Attacks on Ubuntu Services [2025]](https://tryrunable.com/blog/understanding-the-impact-of-ddos-attacks-on-ubuntu-services-/image-1-1777991766076.png)



