Understanding the March 2026 Android Security Update: Key Vulnerabilities and Protecting Your Device [2026]
Security in the digital age is a game of cat and mouse. The March 2026 Android security update is a testament to that dynamic, addressing 129 security flaws that have emerged over time. Among these vulnerabilities is a particularly concerning one, linked to Qualcomm chipsets, that has been exploited in the wild. In this article, we'll break down what these vulnerabilities mean for you, explore the technical details behind them, and provide a guide on how to keep your devices secure.
TL; DR
- 129 Security Flaws: Google's March 2026 update patches 129 vulnerabilities, including 10 critical ones.
- Qualcomm Zero-Day: A vulnerability within Qualcomm chipsets was actively exploited.
- Patch Levels: Two patch levels were released (2026-03-01 and 2026-03-05).
- Device Rollout: Pixel devices received patches first, with other OEMs to follow.
- User Action: Regular updates and awareness are key to maintaining device security.
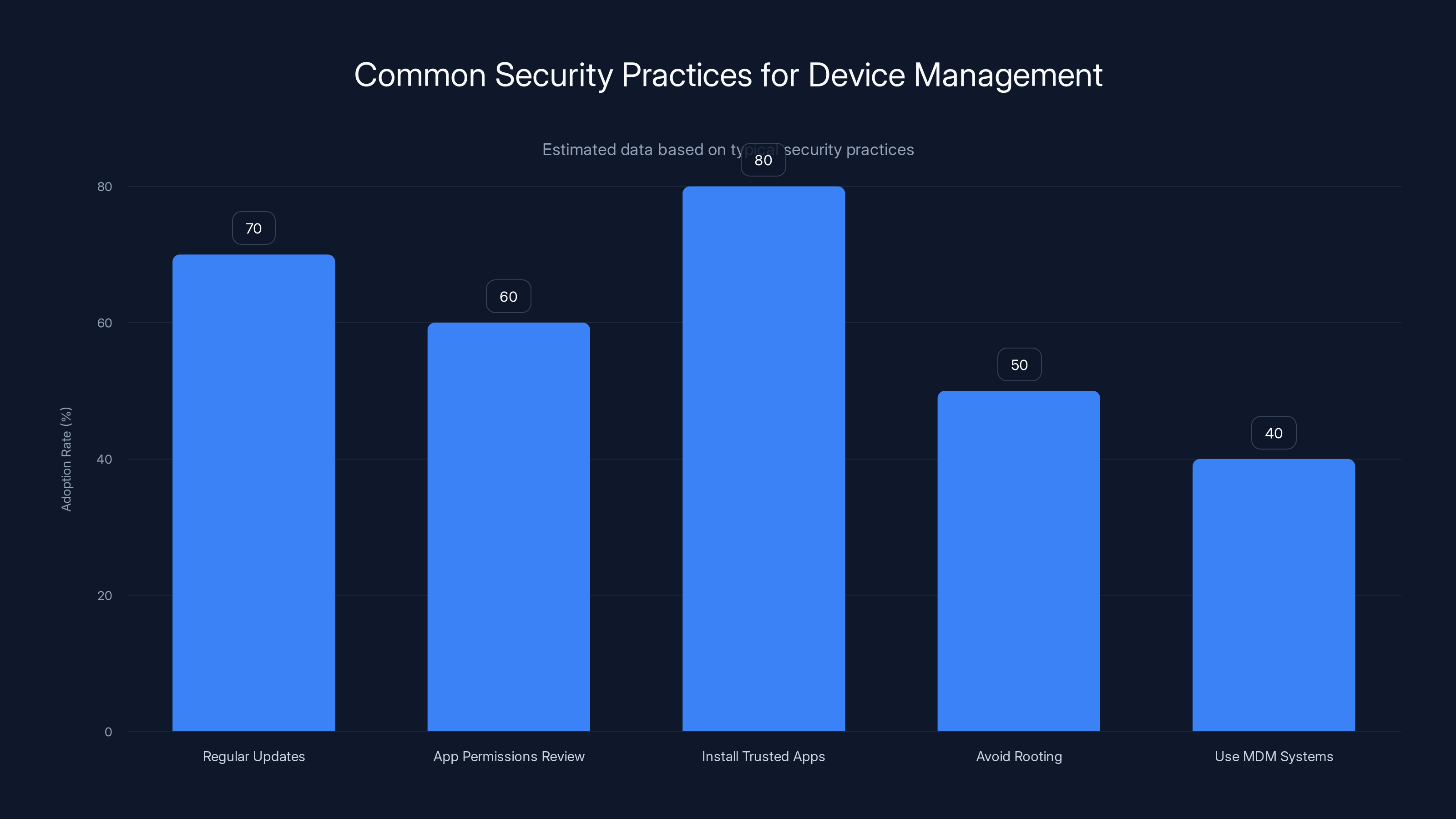
Regular updates and installing trusted apps are the most commonly adopted security practices. Estimated data based on typical security practices.
The Scope of the Update
Overview of Security Flaws
The March 2026 security update by Google is a comprehensive effort to tackle a range of vulnerabilities in the Android ecosystem. These include 10 critical-severity bugs, which could potentially allow remote code execution, data theft, or even complete device takeover if left unpatched.
Key Vulnerability: Qualcomm Zero-Day
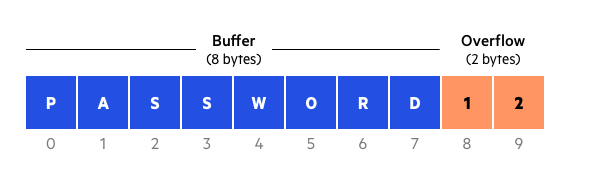
The most alarming flaw, CVE-2026-21385, is a zero-day vulnerability found in Qualcomm chipsets. This vulnerability, rated at 7.8/10 on the severity scale, involves a buffer over-read in the graphics component. Exploiting this flaw could allow attackers to access sensitive information from your device memory.
Patch Levels Explained
Google issued two distinct patch levels: 2026-03-01 and 2026-03-05. These represent stages of vulnerability coverage, with the latter encompassing additional fixes beyond the initial set. Pixel devices were prioritized for these patches, with OEMs expected to roll out updates to other Android devices subsequently.

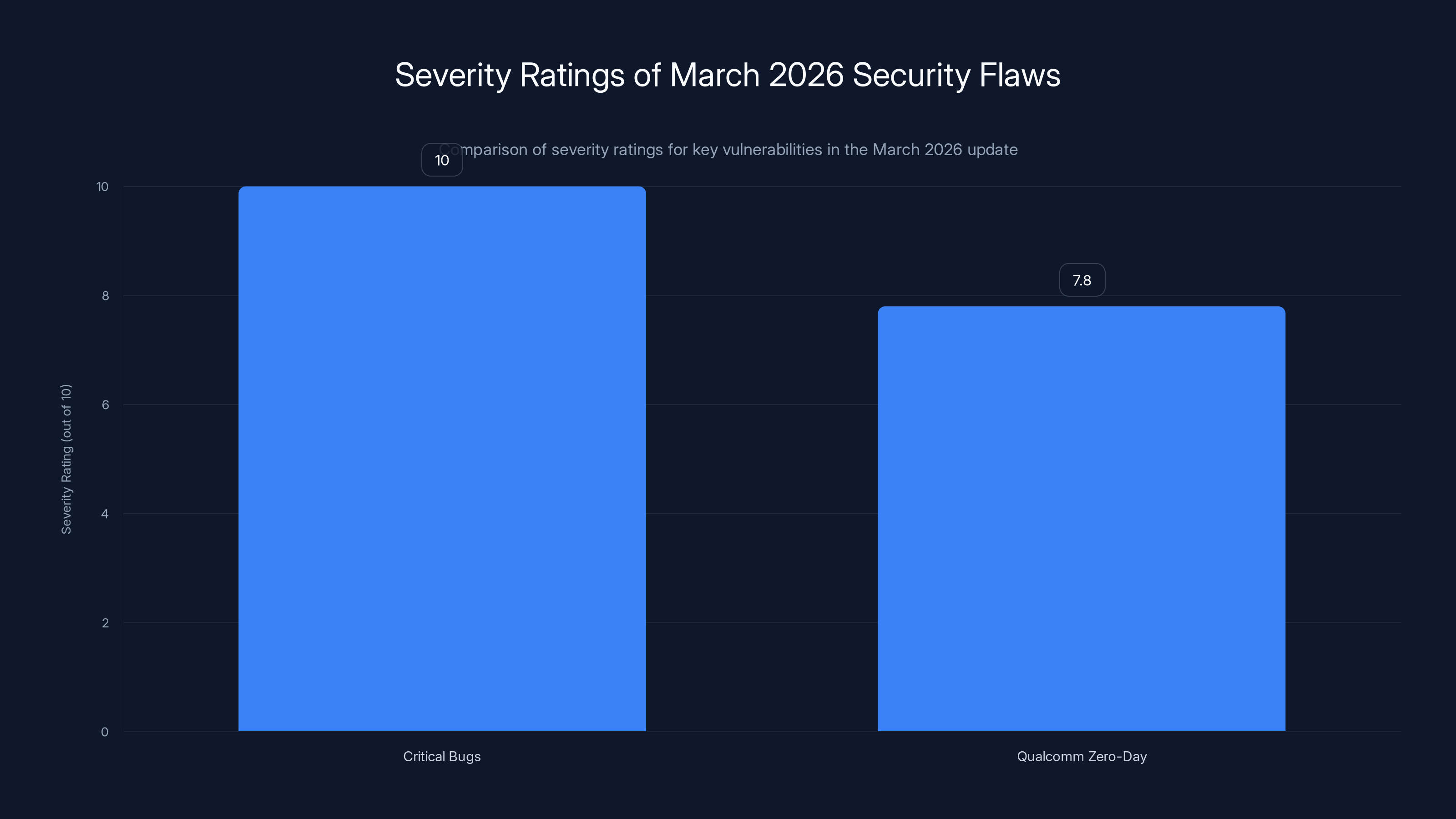
The Qualcomm Zero-Day vulnerability, rated at 7.8, is a major concern, though not as severe as the critical bugs rated at 10. Estimated data based on severity scale.
Technical Deep Dive
Understanding Buffer Over-Read
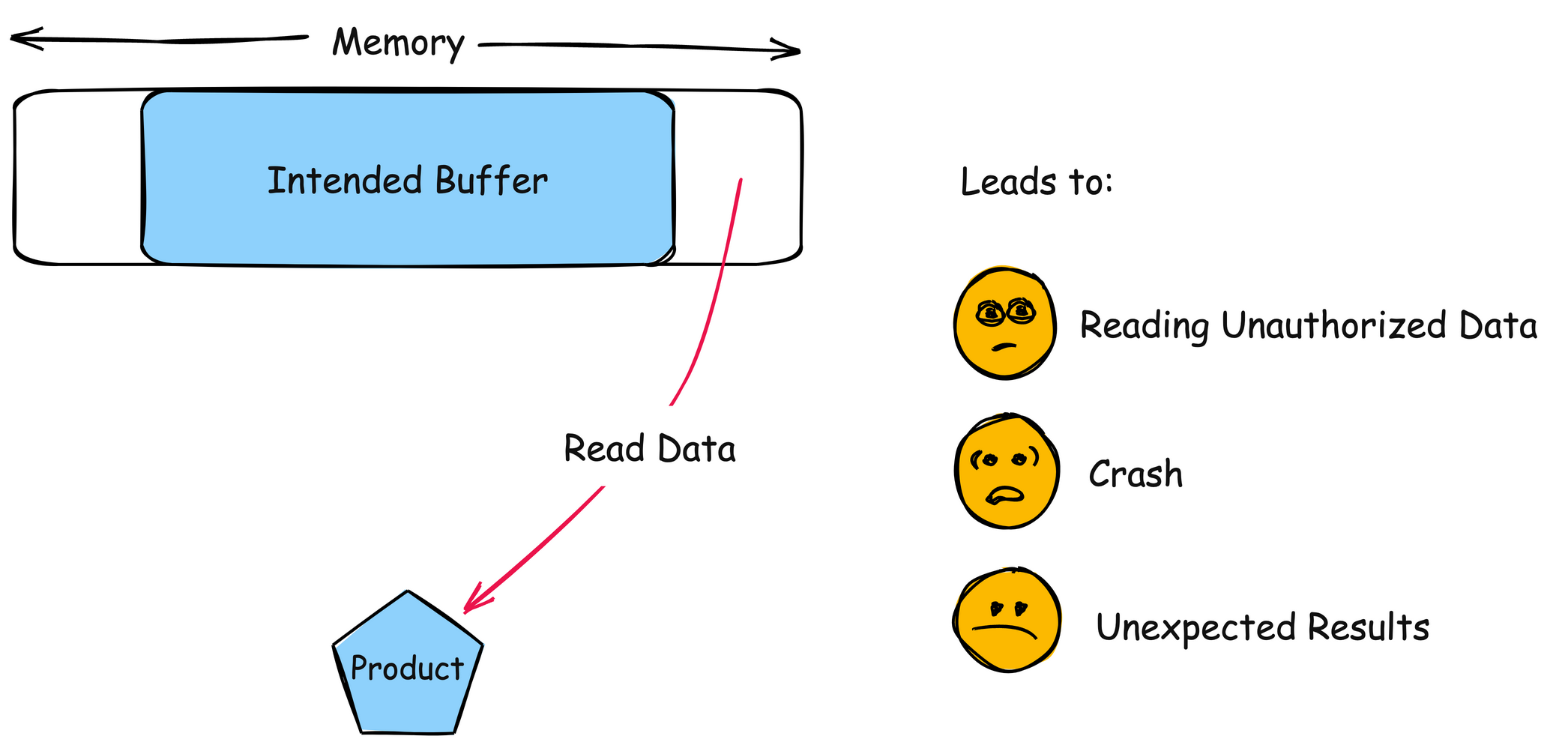
Buffer over-read vulnerabilities occur when software reads more data than it should from a buffer. In the context of CVE-2026-21385, this flaw arises from improper boundary checks in Qualcomm's graphics component, potentially exposing sensitive data.
How Exploits Work
Attackers exploit buffer over-reads by sending specially crafted data to the vulnerable component. This data manipulates the program's logic, causing it to read beyond the intended memory area. The unintended data can reveal sensitive information, which attackers might use for further malicious activities.
Real-World Example
Consider a malicious app that leverages this vulnerability. By exploiting the buffer over-read, it could access user data, such as passwords or cryptographic keys, stored in adjacent memory areas.

Implementation and Best Practices
Keeping Your Device Secure
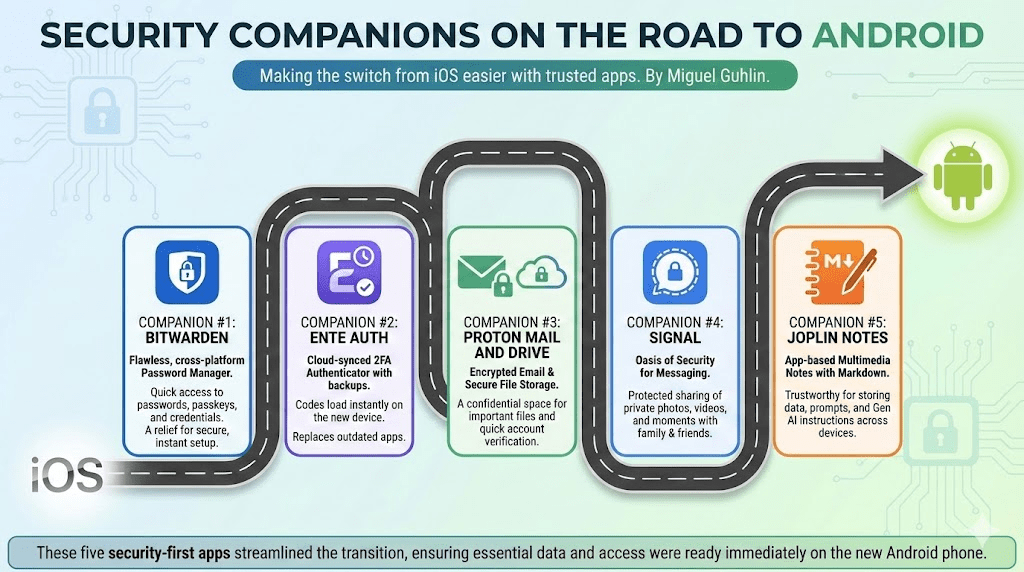
- Regular Updates: Ensure your device automatically installs security updates. Check your settings to confirm this feature is enabled.
- App Permissions: Review app permissions regularly. Limit access to sensitive data and features unless absolutely necessary.
- Install Trusted Apps: Only download apps from official sources like the Google Play Store.
Common Pitfalls
- Ignoring Updates: Many users delay updates due to inconvenience, leaving devices vulnerable.
- Rooted Devices: Rooting can disable security measures, increasing susceptibility to exploits.
- Unverified Apps: Installing apps from unofficial sources can introduce malware.
Solutions for Enterprises
For businesses, device management platforms like Mobile Device Management (MDM) systems can automate security updates and enforce policies, ensuring all devices remain secure.
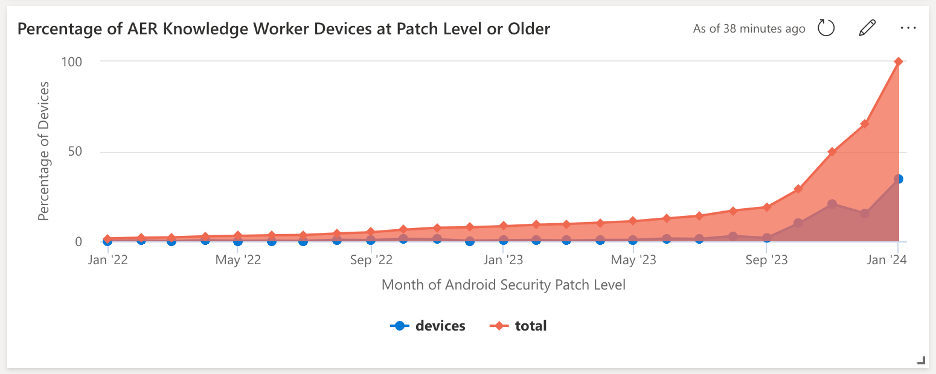
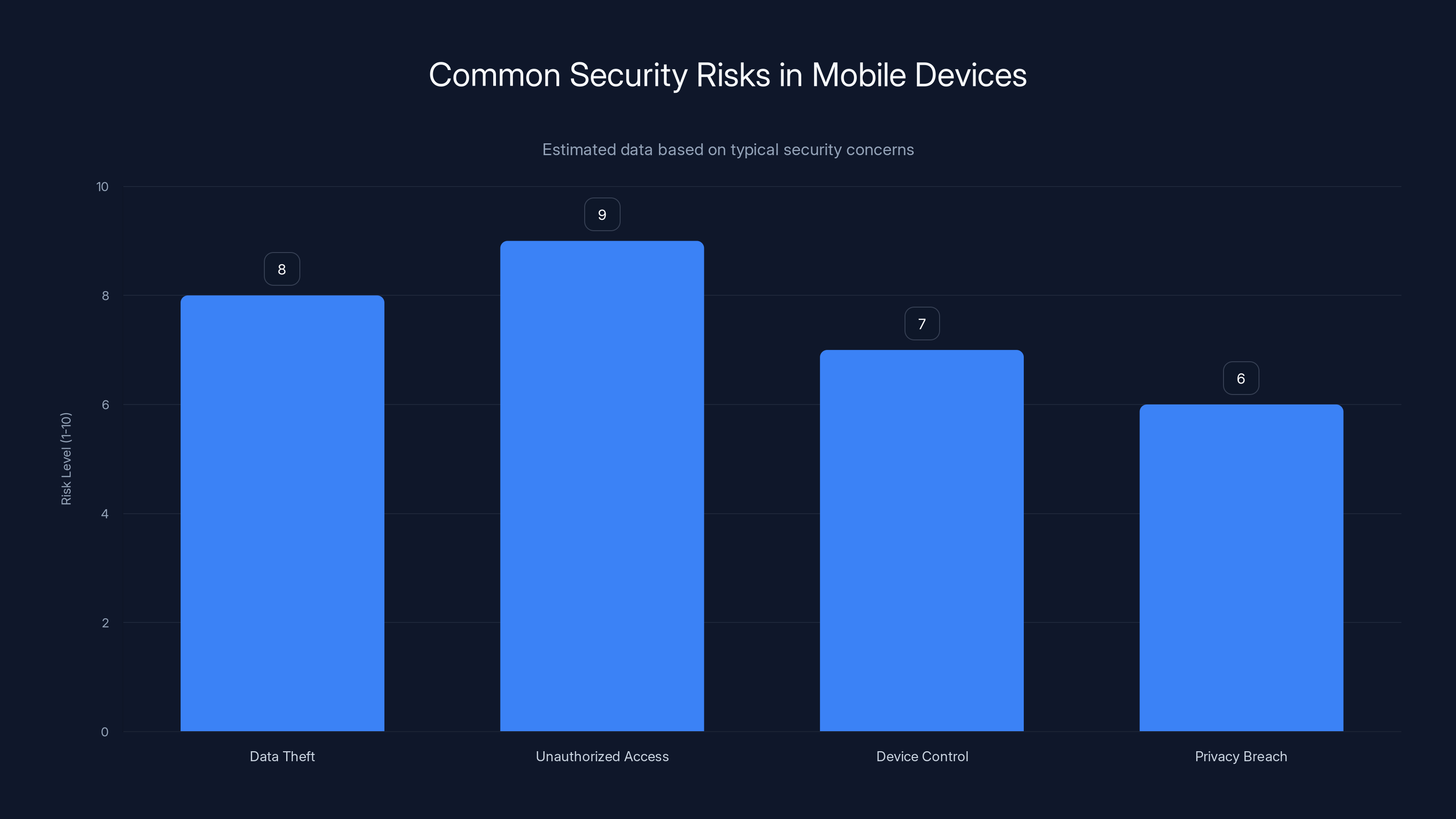
Ignoring security updates can lead to high risk levels for data theft and unauthorized access. Estimated data.
Future Trends and Recommendations
Anticipating New Threats
As technology evolves, so do the methods attackers use. Future vulnerabilities are likely to target more integrated systems, such as IoT devices, which share similar chipset vulnerabilities.
Emphasis on AI in Security
Artificial Intelligence (AI) can enhance threat detection by analyzing patterns and anomalies. Implementing AI-driven security solutions will be crucial in staying ahead of emerging threats.
Proactive Security Measures
Organizations and individuals alike should adopt a proactive approach to security, focusing on prevention rather than mere reaction. Regular security audits and employee training on cyber hygiene can significantly reduce risk.
FAQ
What is CVE-2026-21385?
CVE-2026-21385 is a zero-day vulnerability in Qualcomm chipsets that could allow unauthorized access to sensitive data through a buffer over-read flaw.
How can I ensure my Android device is secure?
Keep your device updated with security patches, only install trusted apps, and regularly review app permissions to ensure they are necessary.
What are the risks of ignoring security updates?
Ignoring updates can leave devices vulnerable to exploits, resulting in data theft, unauthorized access, and potential device control by attackers.
How do buffer over-read vulnerabilities work?
Buffer over-read vulnerabilities occur when software reads more data than intended from a buffer, potentially exposing sensitive information.
Why are Qualcomm chipsets frequently targeted?
Qualcomm chipsets are widely used in Android devices, making them a lucrative target for attackers seeking to exploit vulnerabilities en masse.
How does AI improve security?
AI enhances security by detecting patterns and anomalies in data, allowing for faster and more accurate threat detection and response.
Conclusion
The March 2026 Android security update underscores the importance of staying vigilant in the ever-evolving landscape of digital security. By understanding these vulnerabilities and taking proactive steps, you can better protect your devices from potential threats.
Key Takeaways
- Google's March 2026 security update addresses 129 Android vulnerabilities, including 10 critical ones.
- A zero-day vulnerability (CVE-2026-21385) in Qualcomm chipsets was actively exploited.
- Two patch levels (2026-03-01 and 2026-03-05) were released, prioritizing Pixel devices.
- Buffer over-read vulnerabilities can expose sensitive data by reading beyond allocated memory.
- Regular updates and app verification are crucial for maintaining mobile device security.
- AI-driven security solutions are pivotal in detecting and mitigating emerging threats.
Related Articles
- The Unihertz QWERTY Revival: A Modern Take on Classic Blackberry Features [2025]
- How Google's Developer Verification Impacts Android's Open Legacy [2025]
- Unmasking the Latest Phishing Threat: Fake Google Security Pages [2025]
- Understanding Oblivion Malware: A New Threat to Android Security [2025]
- The Week in Tech: Seven Game-Changing Stories You Need to Know [2025]
- Ransomware Payments Plummet Even as Attacks Surge: Insights and Strategies [2025]
![Understanding the March 2026 Android Security Update: Key Vulnerabilities and Protecting Your Device [2026]](https://tryrunable.com/blog/understanding-the-march-2026-android-security-update-key-vul/image-1-1772559309101.jpg)



