Unmasking the Latest Phishing Threat: Fake Google Security Pages [2025]
In the ever-evolving landscape of cybersecurity threats, phishing campaigns remain among the most pernicious. A recent campaign has taken a particularly insidious approach by masquerading as a Google Account security page to trick victims into divulging their passcodes and other sensitive information. Let's delve into the mechanics of this campaign, how it operates, and what individuals and organizations can do to protect themselves.
TL; DR
- New Phishing Tactic: Attackers use fake Google Account security pages to harvest sensitive data.
- Progressive Web Apps (PWA) Exploitation: Malicious PWAs are employed to capture clipboard data, OTPs, and more.
- User Awareness: Crucial to recognize phishing emails and fake sites.
- Security Best Practices: Implement multi-factor authentication and regular security training.
- Future Threats: Expect more sophisticated phishing tactics leveraging AI.
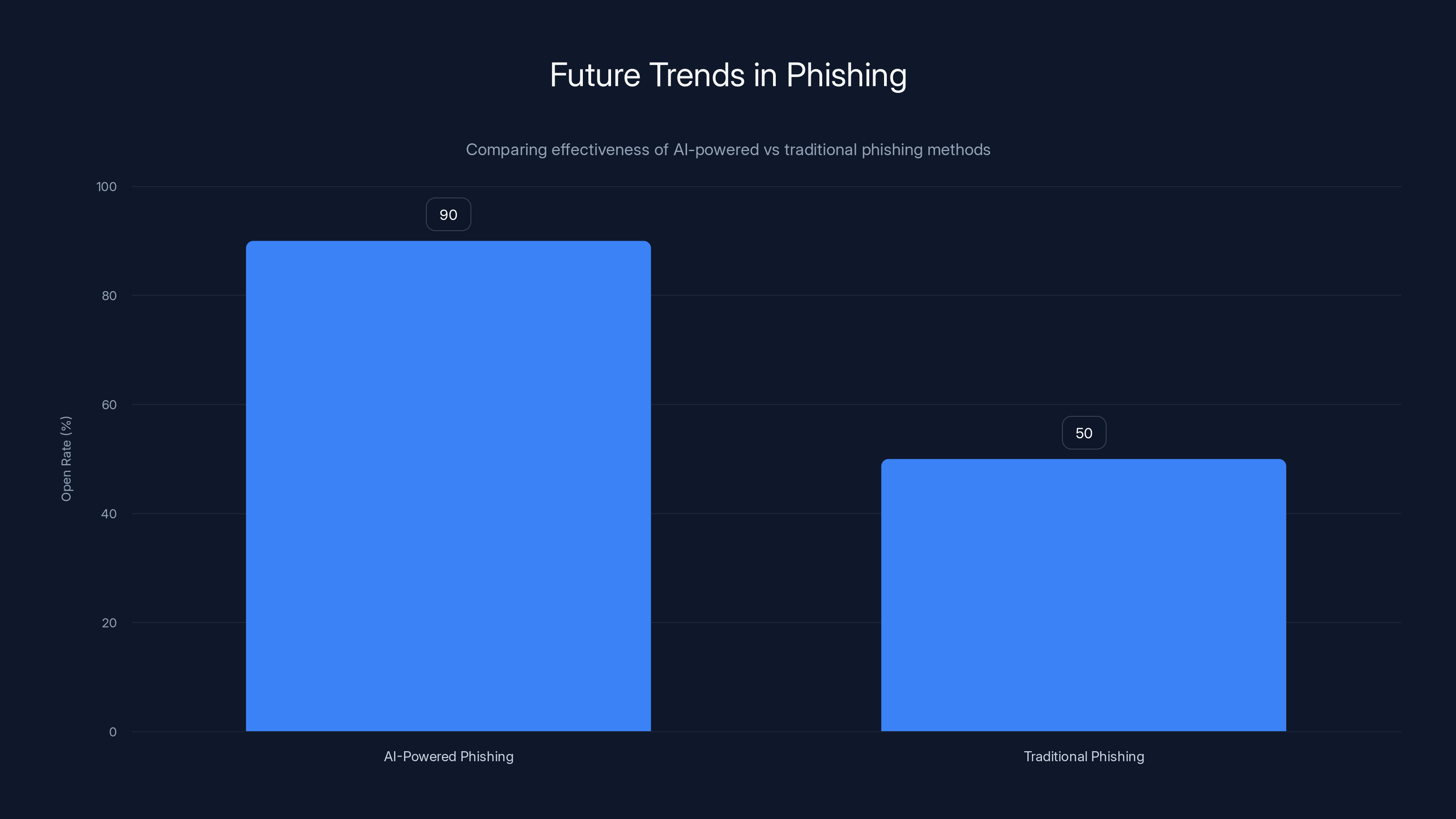
AI-powered phishing campaigns can achieve up to a 90% open rate, significantly outperforming traditional methods. (Estimated data)
Understanding the Threat Landscape
Phishing has long been a favored tactic among cybercriminals due to its simplicity and effectiveness. By impersonating legitimate entities, attackers can dupe users into handing over sensitive information, such as passwords and credit card details. The latest campaign exploits our trust in Google's security infrastructure.
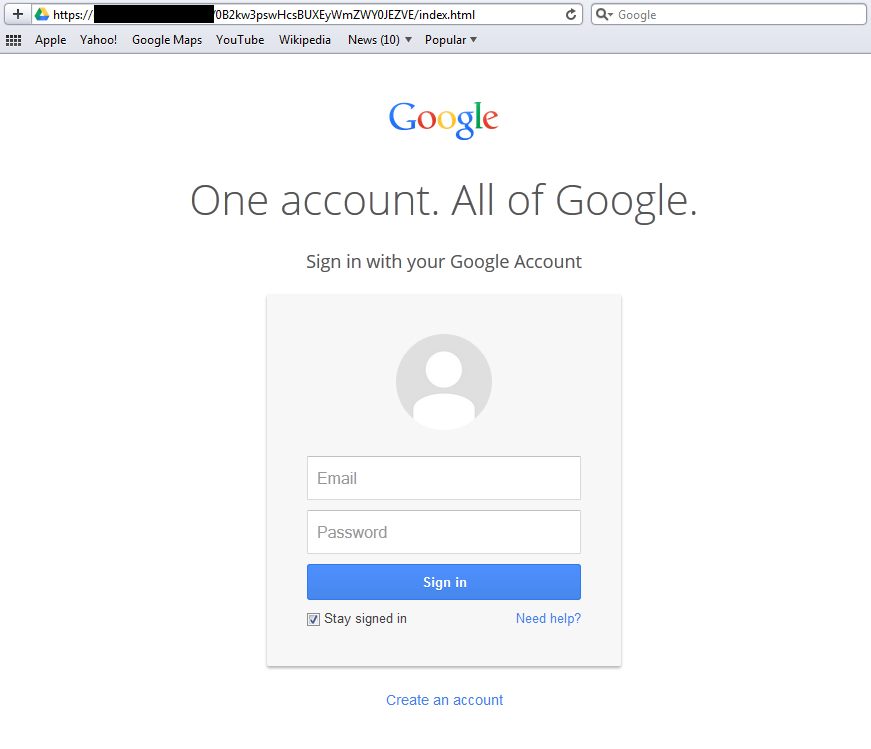
Anatomy of the Attack
This campaign begins with a phishing email that appears to come from Google, alerting the recipient to a supposed security issue with their account. The email contains a link to a fake Google site, cleverly disguised to look like a legitimate Google Account security page. Known as google-prism[dot]com, this site is the gateway to the attack.
Once the victim lands on the fake page, they are guided through a series of steps designed to bolster their account's security. However, the process is a ruse to install a malicious Progressive Web App (PWA) on their Android device.

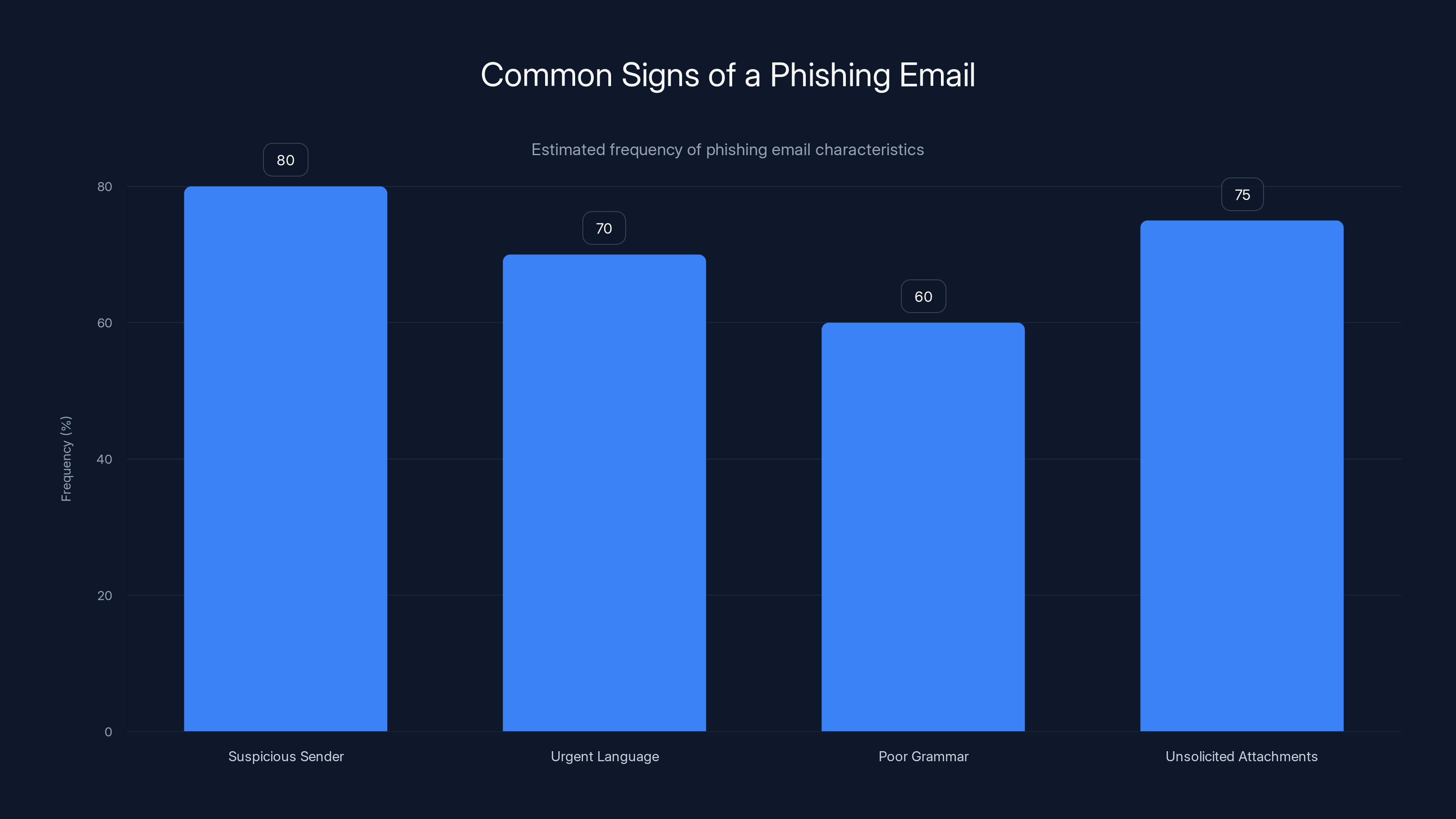
Suspicious sender addresses and unsolicited attachments are the most common signs of phishing emails. Estimated data based on typical phishing characteristics.
The Role of Progressive Web Apps
What Are PWAs?
PWAs are increasingly popular due to their flexibility and the seamless experience they offer across different devices. However, they also present new opportunities for exploitation.
How PWAs Are Exploited
In this campaign, the malicious PWA is designed to harvest a variety of data from the victim's device, including:
- Clipboard contents
- Cryptocurrency wallets
- One-Time Passcodes (OTPs)
- GPS location
This comprehensive data theft allows attackers to compromise not only the victim's Google account but potentially other services and accounts linked to their personal information.
Recognizing Phishing Emails
Phishing emails are often the first point of contact in these attacks. Here are some key indicators that an email might be part of a phishing campaign:
- Suspicious Sender Address: Phishing emails often come from addresses that mimic legitimate ones but contain subtle differences.
- Urgent or Threatening Language: Phrases like "immediate action required" are red flags.
- Poor Grammar and Spelling: Many phishing emails originate from non-native speakers and contain errors.
- Unusual Attachments or Links: Be wary of unsolicited attachments or links, especially those claiming to be important documents or security alerts.
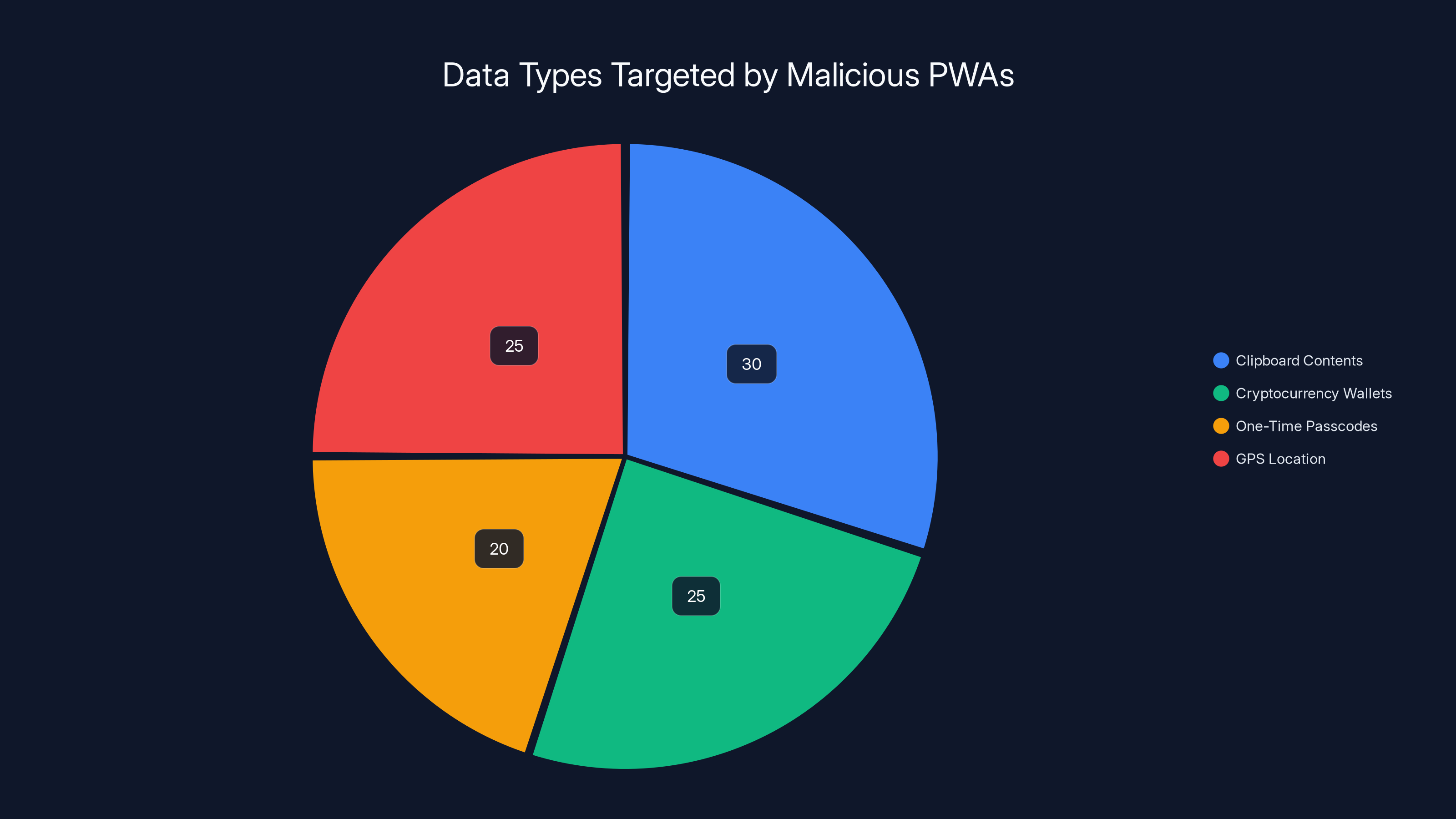
Estimated data shows that clipboard contents and GPS location are the most targeted by malicious PWAs, each accounting for 25-30% of the data theft focus.
Best Practices for Prevention
Multi-Factor Authentication
One of the most effective defenses against phishing is multi-factor authentication (MFA). By requiring an additional verification step, such as a code sent to your phone, MFA can prevent unauthorized access even if your password is compromised.
Regular Security Training
Organizations should conduct regular security training sessions to educate employees about the latest phishing tactics and how to recognize them.
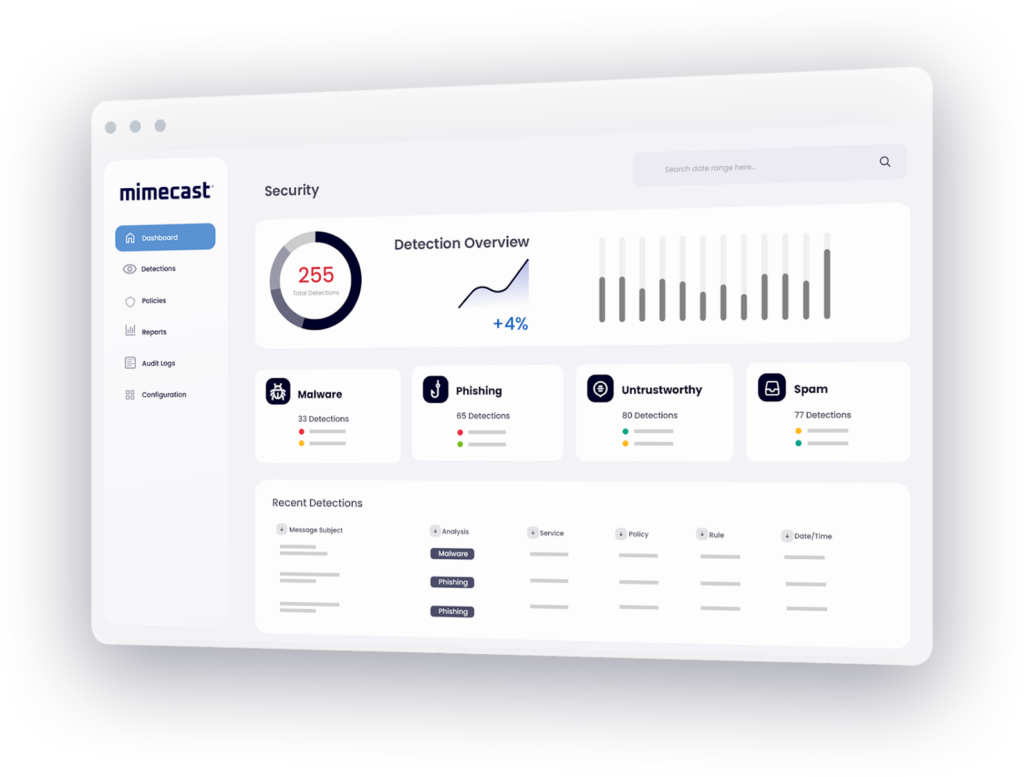
Use of Anti-Phishing Software
Investing in robust anti-phishing software can help detect and block phishing attempts before they reach the end user.
Common Pitfalls and Solutions
Overconfidence in Security Tools
Relying solely on software for security can lead to complacency. While tools are essential, human vigilance is equally important.
- Solution: Encourage a culture of security awareness within the organization, where employees are empowered to question suspicious activities.
Inadequate Patch Management
Outdated software can be a significant vulnerability. Ensure that all systems are regularly updated to protect against known exploits.
- Solution: Implement an automated patch management system to ensure timely updates.
Future Trends in Phishing
AI-Powered Phishing
As artificial intelligence continues to advance, expect phishing campaigns to become more sophisticated. AI can be used to craft more convincing phishing emails and even mimic user behavior to bypass security checks.
Mobile-First Phishing
With the increasing use of mobile devices, phishing campaigns are likely to target these platforms more aggressively. Mobile users are often more vulnerable due to smaller screens and limited visibility of URLs and email addresses.
- Recommendation: Develop mobile-specific security strategies, including mobile-friendly security training and tools.

Conclusion
Phishing attacks remain a significant threat in the digital age, with new tactics evolving constantly. By understanding the mechanics of these attacks and implementing robust security measures, individuals and organizations can protect themselves from falling victim to these schemes. Stay vigilant, stay informed, and prioritize cybersecurity in all digital interactions.
FAQ
What is phishing?
Phishing is a type of cyber attack where attackers impersonate legitimate entities to trick individuals into divulging sensitive information, such as passwords and credit card numbers.
How do Progressive Web Apps contribute to phishing attacks?
PWAs can be used to harvest sensitive data from a device, making them a tool for cybercriminals in phishing campaigns. They can capture information like clipboard contents and GPS location.
What are some signs of a phishing email?
Common signs include suspicious sender addresses, urgent or threatening language, poor grammar, and unsolicited attachments or links.
How can I protect myself from phishing attacks?
Enable multi-factor authentication, stay informed about the latest phishing tactics, use anti-phishing software, and be vigilant about the emails you open and the links you click.
What should I do if I suspect a phishing attempt?
Do not click on any links or download attachments. Report the email to your security team or email provider and delete it from your inbox.

Key Takeaways
- New phishing campaigns use fake Google security pages to steal sensitive info
- Malicious PWAs are central to these attacks, capturing data like OTPs and GPS
- Multi-factor authentication is crucial for protecting against phishing
- Regular security training and awareness can prevent phishing success
- Expect more AI-driven phishing tactics targeting mobile users
Related Articles
- Beware of Google Tasks Scams: Protect Your Workplace from Phishing Attacks [2025]
- The Silent Threat: How Hackers Exploit .arpa Domains for Phishing Schemes [2025]
- Australia's Bold Move on AI Services: Age Verification and App Store Compliance [2025]
- Ensuring Secure AI Usage in the Workplace [2025]
- How to Secure Cryptocurrency Holdings: Lessons from the South Korean Crypto Incident [2025]
- When AI Lies: Navigating the Complexities of Alignment Faking in Autonomous Systems [2025]
![Unmasking the Latest Phishing Threat: Fake Google Security Pages [2025]](https://tryrunable.com/blog/unmasking-the-latest-phishing-threat-fake-google-security-pa/image-1-1772541264394.jpg)



