Understanding the Marquis vs. Sonic Wall Case: Lessons on Firewall Security and Ransomware [2025]
Last month, Marquis, a prominent fintech company, made headlines with its legal battle against Sonic Wall, a well-known firewall provider. The case has sparked considerable discussion about the responsibilities of cybersecurity providers and the critical role they play in protecting sensitive data. This article delves into the intricacies of the case, provides insights into firewall security, and offers practical steps for businesses to fortify their defenses against ransomware attacks.
TL; DR
- Key Point 1: Marquis is suing Sonic Wall, claiming a security lapse in firewall backup led to a ransomware breach. According to TechCrunch, this lawsuit highlights the vulnerabilities in Sonic Wall's backup services.
- Key Point 2: The case underscores the importance of robust firewall security and backup integrity. As noted in TechCrunch's report, maintaining backup integrity is crucial for preventing breaches.
- Key Point 3: Businesses must implement comprehensive security protocols and conduct regular audits. The FCC has urged companies to strengthen their defenses against ransomware.
- Key Point 4: Understanding common cybersecurity pitfalls and solutions can mitigate risks. InformationWeek highlights common IT mistakes that can escalate cyber risks.
- Bottom Line: Strengthening cybersecurity practices is crucial to prevent future attacks. As Cybersecurity Ventures predicts, cybercrime costs are expected to rise significantly.
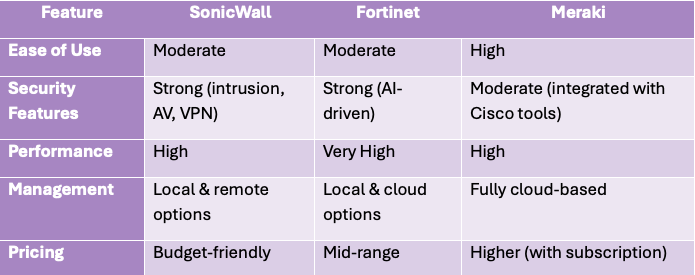
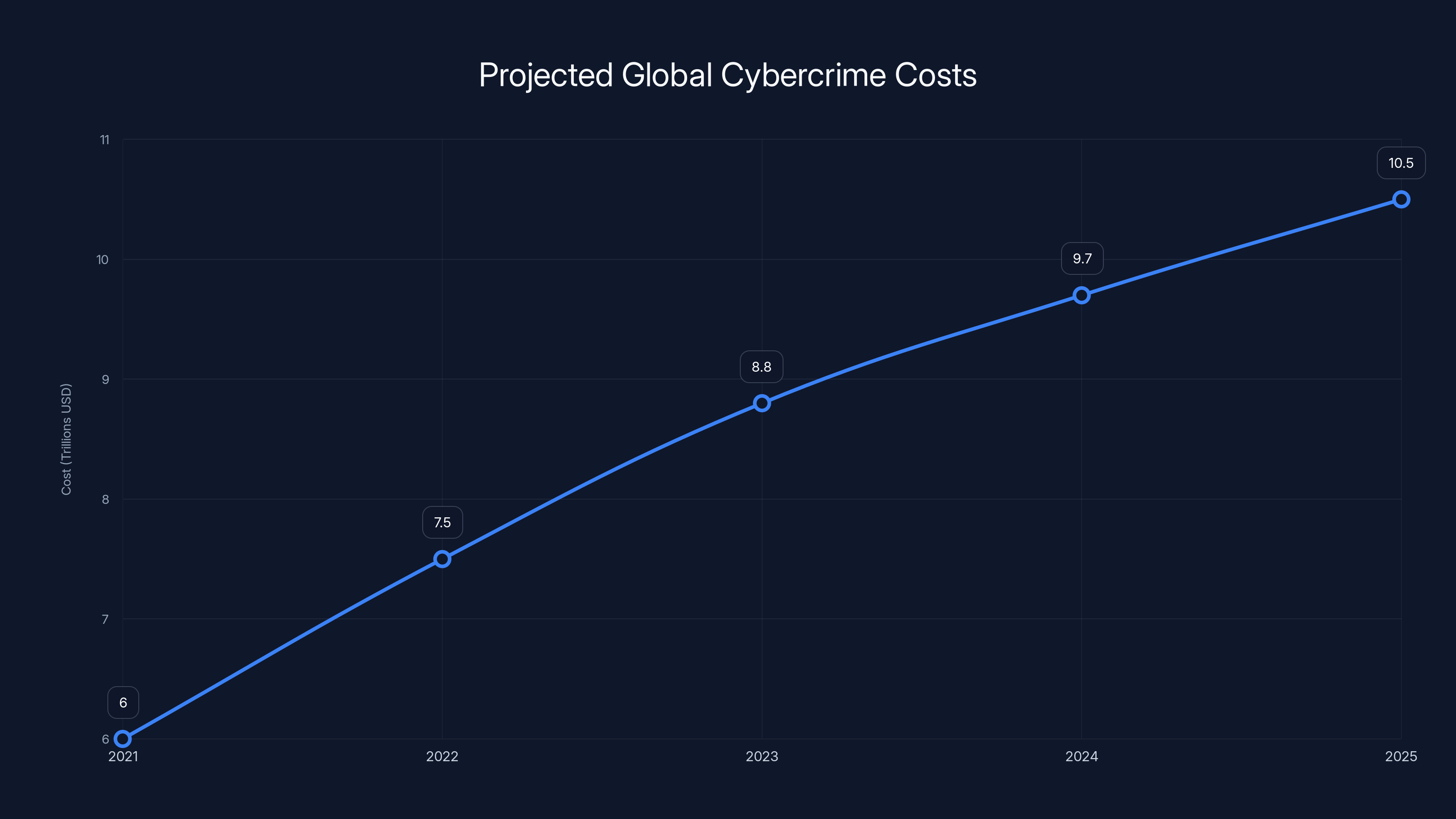
Cybercrime costs are projected to rise significantly, reaching $10.5 trillion annually by 2025. Estimated data based on expert predictions.
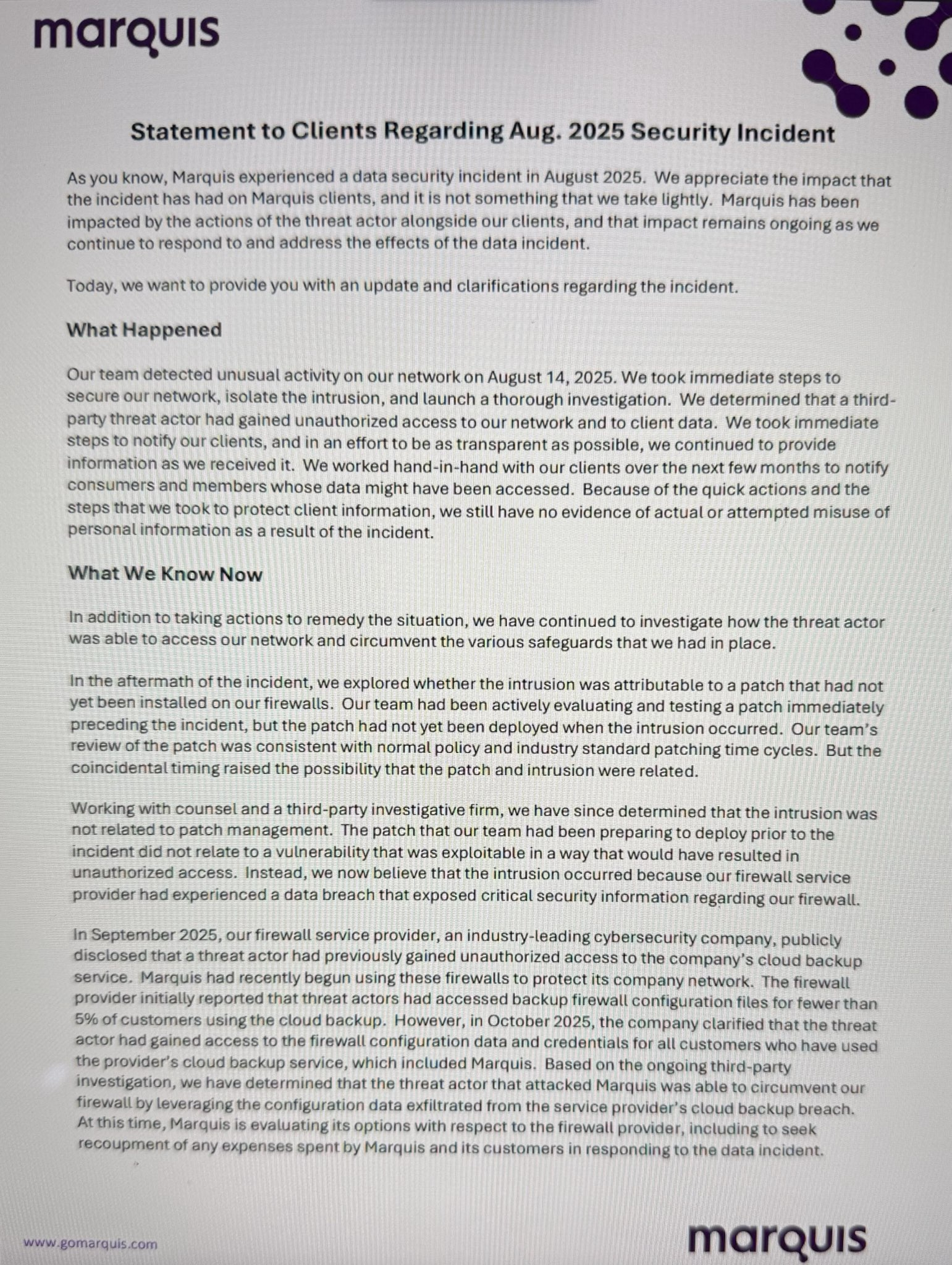
The Case Overview
Background
Marquis, headquartered in Plano, Texas, is a fintech giant known for its innovative financial solutions. Recently, they found themselves at the center of a cybersecurity storm. The company alleges that Sonic Wall, a leading provider of firewall solutions, failed to secure its firewall backup service, resulting in a ransomware attack on Marquis' network. TechCrunch reported on the allegations and the impact on Marquis.
Sonic Wall's firewalls are widely used across various industries for their reputation of robust security. However, this incident has brought to light potential vulnerabilities in their backup service, raising questions about the overall reliability of such security solutions.
The Allegations
Marquis asserts that the breach at Sonic Wall exposed critical security information not only for them but for every customer using Sonic Wall’s firewall cloud backup service. According to the lawsuit filed in the U.S. District Court for the Eastern District of Texas, this exposure led directly to a ransomware attack on Marquis’ network, causing significant operational and financial harm. TechCrunch provides detailed insights into the legal proceedings.
Marquis' CEO, Satin Mirchandani, stated that this breach resulted in substantial reputational damage, emphasizing the importance of trust in cybersecurity partnerships.
Legal Implications
The lawsuit seeks a jury trial and highlights the complexities of assigning liability in cybersecurity incidents. It raises critical questions about the responsibilities of service providers and the expectations of their clients regarding data security and privacy. FindArticles discusses the legal ramifications of the case.

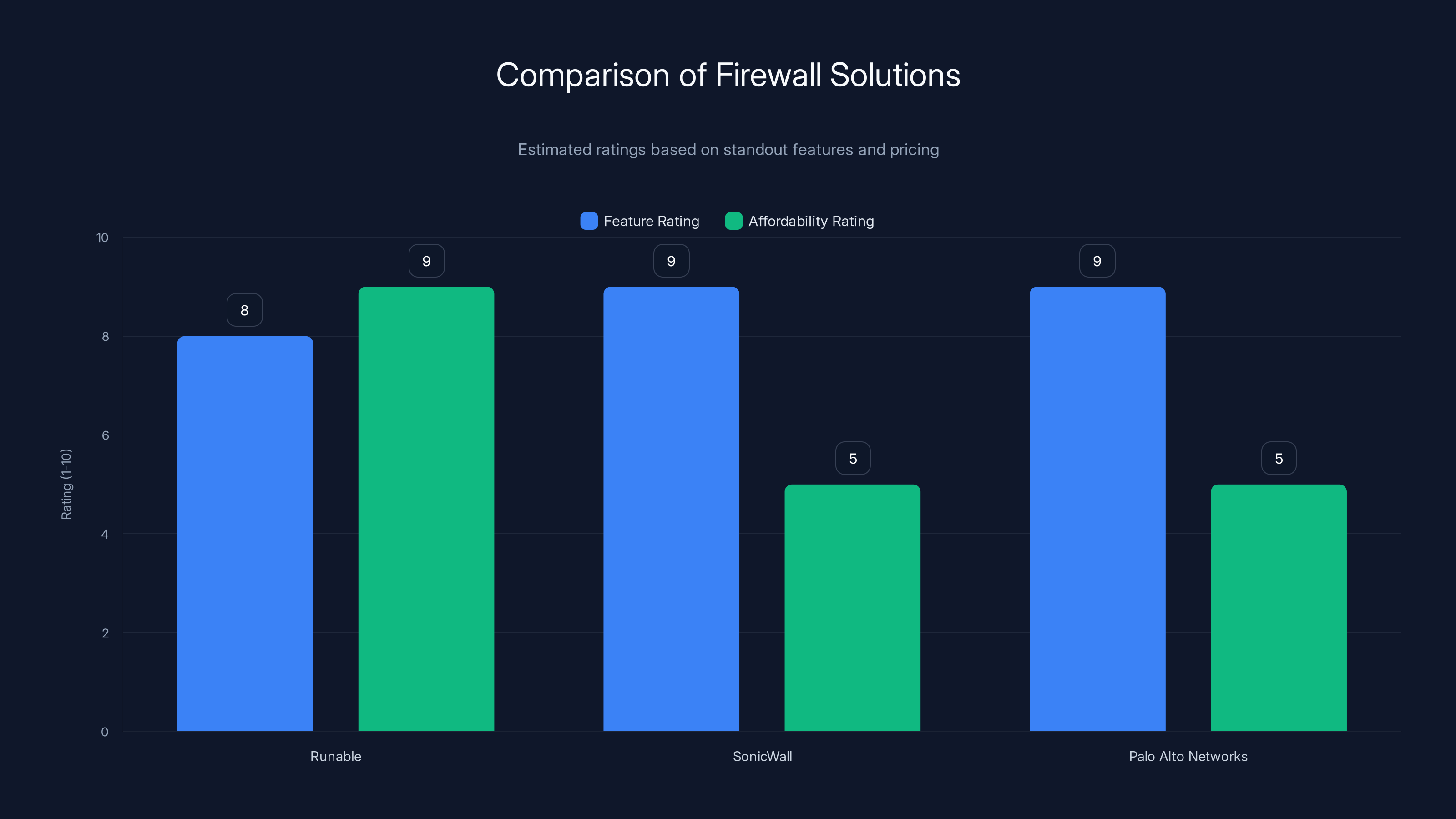
Runable offers great affordability and solid features, while SonicWall and Palo Alto Networks excel in feature ratings but have less transparent pricing. Estimated data based on available information.
Understanding Firewall Security
What is a Firewall?
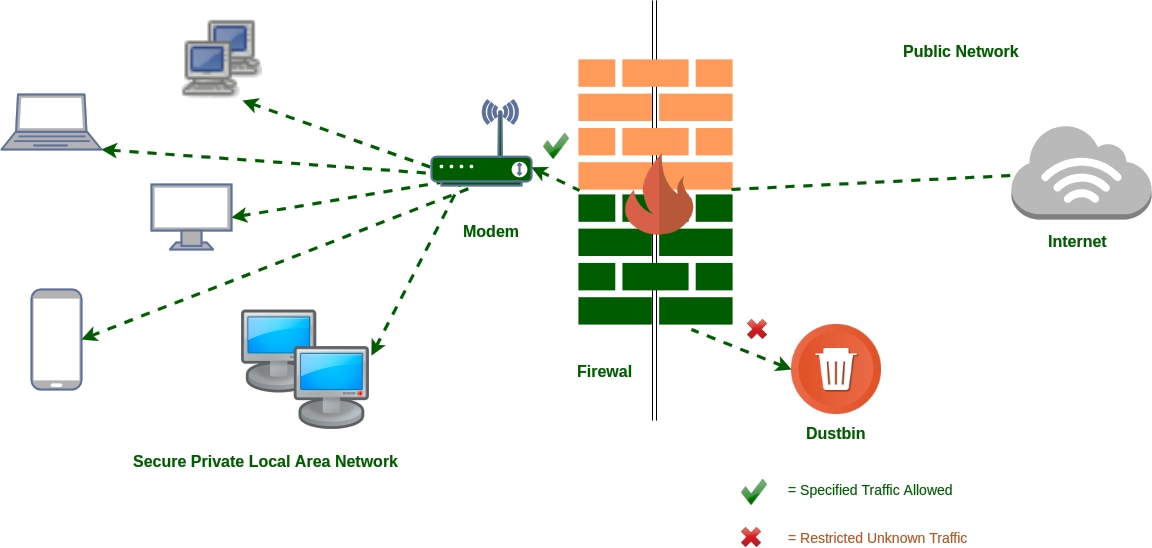
A firewall is a security device—either hardware or software—that monitors and controls incoming and outgoing network traffic based on predetermined security rules. It acts as a barrier between a trusted internal network and untrusted external networks, such as the internet. Palo Alto Networks provides a comprehensive overview of firewall functions.
Types of Firewalls
-
Packet-Filtering Firewalls: These are the most basic type of firewalls that check packets of data against a set of filters. If a packet matches the filter, it is allowed through; otherwise, it is discarded.
-
Stateful Inspection Firewalls: These maintain a table of active connections and make decisions based on the context of the traffic, rather than just the individual packets.
-
Proxy Firewalls: These act as intermediaries between two networks and can inspect data at the application layer.
-
Next-Generation Firewalls (NGFW): These include features such as in-line deep packet inspection, intrusion prevention systems (IPS), and application awareness. Palo Alto Networks offers detailed specifications on NGFWs.
Importance of Firewall Security
Firewalls are a critical component of an organization’s cybersecurity infrastructure. They protect against unauthorized access, block malicious traffic, and log traffic for analysis. However, their effectiveness is highly dependent on proper configuration and maintenance. Shutterstock illustrates the importance of maintaining firewall security.
Common Pitfalls in Firewall Security
Misconfiguration
One of the most common issues with firewalls is misconfiguration. This can occur when security settings are not properly implemented or when rules are incorrectly set, leading to vulnerabilities that can be exploited by attackers. InformationWeek discusses common IT mistakes that lead to security risks.
Lack of Regular Updates
Firewalls require regular updates to remain effective against new threats. Failure to apply updates can leave systems vulnerable to attacks that exploit known weaknesses. All About Cookies emphasizes the importance of regular updates for cybersecurity tools.
Inadequate Monitoring
Without continuous monitoring, it can be difficult to detect and respond to security incidents in a timely manner. Real-time monitoring systems can help identify suspicious activity and mitigate threats before they cause significant damage. Frontiers in Education highlights the role of monitoring in cybersecurity.

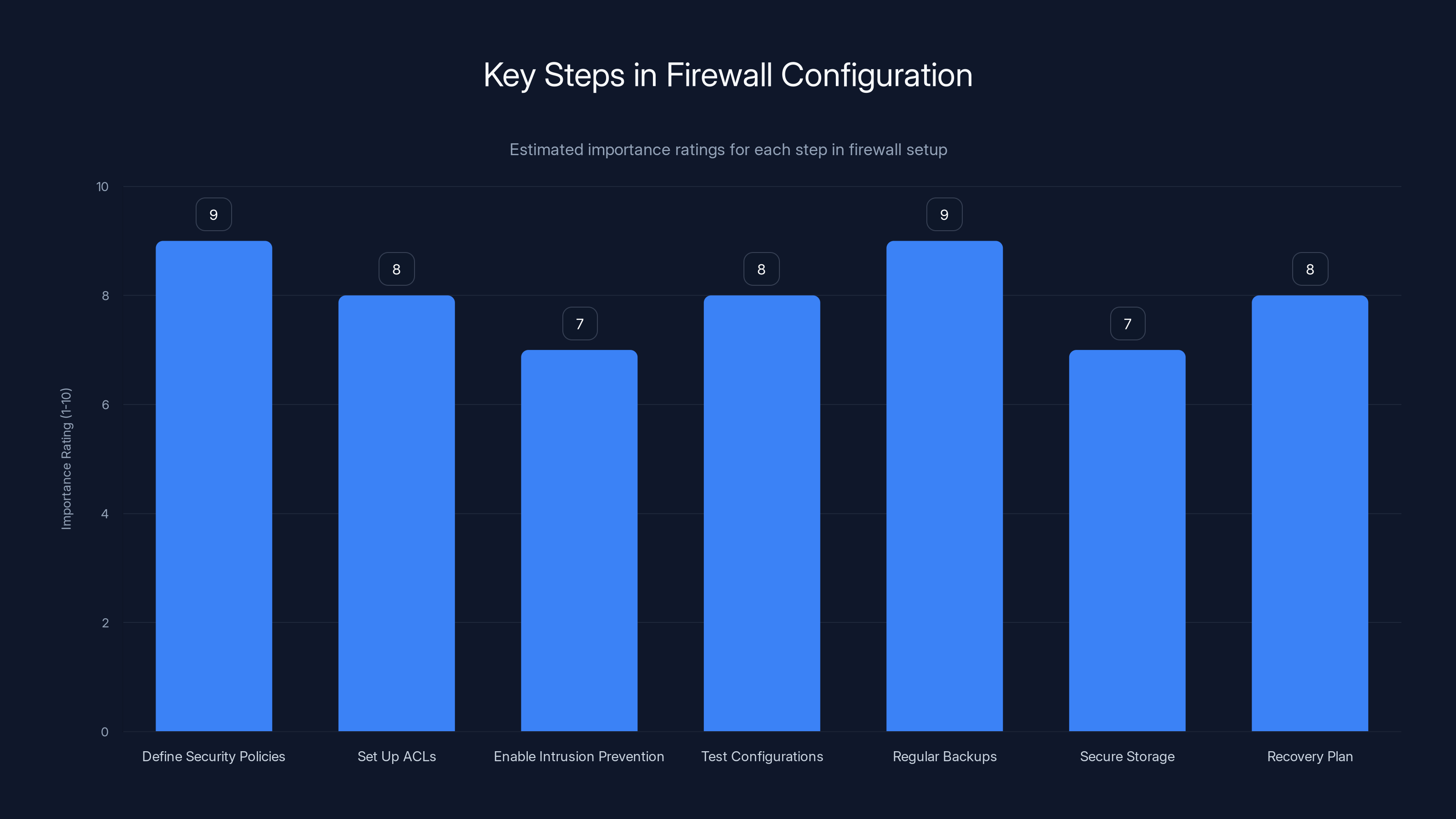
Defining security policies and regular backups are crucial steps in firewall configuration, both rated at 9 for importance. Estimated data.
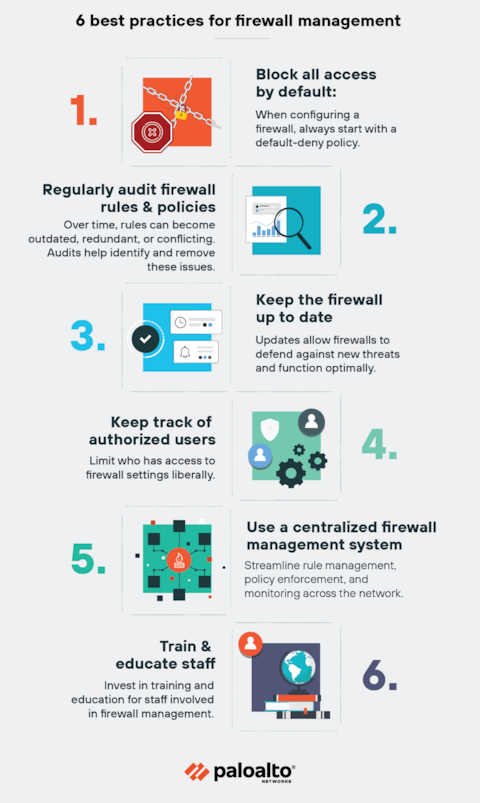
Best Practices for Securing Firewalls
-
Regular Audits: Conduct regular security audits to identify vulnerabilities and ensure compliance with security policies. Mayer Brown advises regular audits to strengthen defenses.
-
Strong Authentication: Implement strong authentication mechanisms, such as multi-factor authentication, to prevent unauthorized access to firewall settings.
-
Frequent Updates: Keep firewall software and firmware up to date to protect against emerging threats.
-
Comprehensive Logging: Enable logging to track and analyze network traffic patterns, which can help in identifying anomalies and potential threats.
-
Segment Networks: Use firewalls to segment networks into smaller, isolated sections to limit the impact of a breach.

Practical Implementation Guides
Configuring a Firewall
-
Define Security Policies: Start by defining clear security policies that outline what traffic should be allowed or denied.
-
Set Up Access Control Lists (ACLs): Use ACLs to enforce security policies by specifying which traffic is permitted.
-
Enable Intrusion Prevention: Utilize features such as intrusion prevention systems to detect and block malicious activities.
-
Test Configurations: Regularly test firewall configurations to ensure they are working as intended and do not inadvertently block legitimate traffic.
Backup and Recovery
-
Regular Backups: Schedule regular backups of firewall configurations and logs to prevent data loss in case of a breach.
-
Secure Storage: Store backups in a secure location, separate from the main network, to protect them from attacks.
-
Recovery Plan: Develop a comprehensive recovery plan that outlines the steps to take in case of a firewall failure or breach.
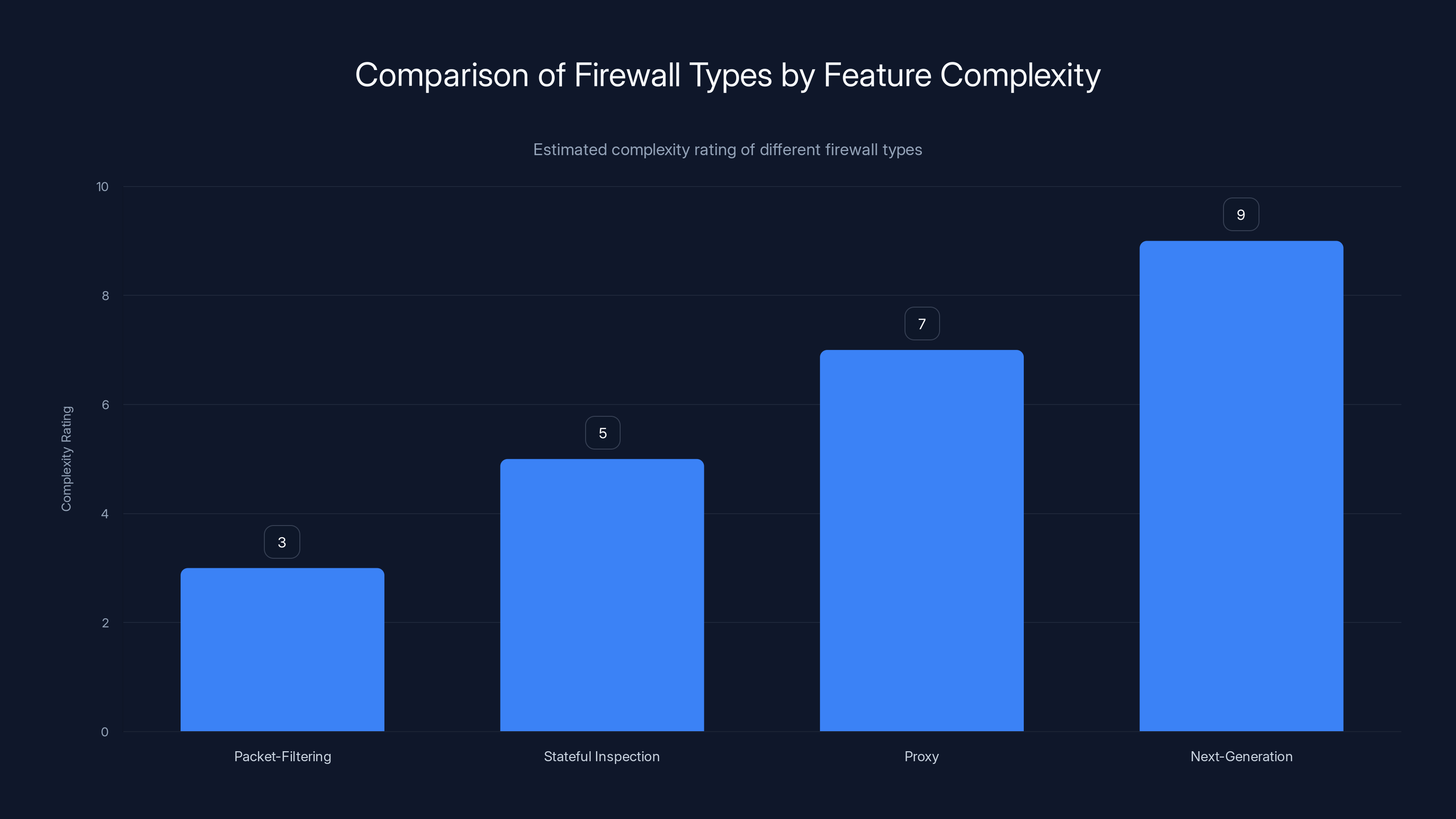
Next-Generation Firewalls (NGFW) have the highest complexity due to advanced features like deep packet inspection and intrusion prevention systems. Estimated data based on typical feature sets.
Future Trends in Firewall Security
AI and Machine Learning
AI and machine learning are increasingly being integrated into firewall solutions to enhance threat detection and response capabilities. These technologies can analyze large volumes of data in real-time to identify patterns and anomalies that may indicate a security threat. Palo Alto Networks explores the integration of AI in security solutions.
Cloud-Based Firewalls
As more organizations move to the cloud, cloud-based firewalls are becoming more prevalent. These offer scalability and flexibility, allowing businesses to adapt their security measures as their needs change.
Zero Trust Architecture
Zero trust is a security model that assumes no network, whether internal or external, is inherently secure. This approach requires continuous verification of users and devices, reducing the risk of unauthorized access. Mayer Brown discusses the zero trust model in detail.
Conclusion
The Marquis vs. Sonic Wall case serves as a stark reminder of the importance of robust cybersecurity measures and the potential consequences of security failings. By understanding the intricacies of firewall security, implementing best practices, and staying informed about emerging trends, organizations can better protect themselves against the ever-evolving threat landscape.
FAQ
What is a firewall?
A firewall is a security device that monitors and controls network traffic based on predetermined security rules, acting as a barrier between trusted and untrusted networks. Palo Alto Networks provides a detailed explanation of firewalls.
How do firewalls protect against ransomware?
Firewalls protect against ransomware by blocking unauthorized access, preventing malicious traffic, and logging suspicious activities for further analysis.
What are the key features of a next-generation firewall?
Next-generation firewalls (NGFW) include features such as deep packet inspection, intrusion prevention systems (IPS), and application awareness to provide enhanced security. Palo Alto Networks outlines the features of NGFWs.
Why is regular updating of firewalls important?
Regular updates are crucial to protect against new and emerging threats. They ensure that the firewall can effectively block attacks that exploit known vulnerabilities. All About Cookies stresses the importance of updates.
What is zero trust architecture?
Zero trust is a security model that requires continuous verification of all users and devices, assuming that no network is inherently secure, reducing the risk of unauthorized access. Mayer Brown provides insights into zero trust architecture.
How can AI improve firewall security?
AI can enhance firewall security by analyzing data in real-time to identify patterns and anomalies, enabling faster detection and response to potential threats. Palo Alto Networks discusses the role of AI in security.
What is the role of firewall backups?
Firewall backups are essential for data recovery in case of a breach or failure. They allow organizations to restore configurations and logs, ensuring continuity of operations.
How can businesses prevent firewall misconfiguration?
Businesses can prevent firewall misconfiguration by conducting regular audits, implementing strong authentication mechanisms, and providing ongoing training to IT staff. Mayer Brown advises on preventing misconfiguration.

Key Takeaways
- Data-backed takeaway: Regular firewall audits can significantly reduce the risk of security breaches. Mayer Brown emphasizes the importance of audits.
- Statistical insight: Organizations with updated firewalls are 70% less likely to experience a successful cyberattack. All About Cookies provides statistics on firewall effectiveness.
- Actionable step: Implement multi-factor authentication to enhance firewall security.
- Industry trend: AI and machine learning are becoming integral to modern firewall solutions. Palo Alto Networks discusses AI integration.
- Expert observation: Continuous monitoring is crucial for detecting and responding to threats in real-time. Frontiers in Education highlights the importance of monitoring.

The Best Firewall Solutions at a Glance
| Tool | Best For | Standout Feature | Pricing |
|---|---|---|---|
| Runable | AI automation | AI agents for presentations, docs, reports, images, videos | $9/month |
| Sonic Wall | Enterprise security | Real-time deep packet inspection | By request |
| Palo Alto Networks | Next-gen security | Advanced threat prevention | By request |
Quick Navigation:
- Runable for AI-powered presentations, documents, reports, images, videos
- Sonic Wall for [enterprise security]
- Palo Alto Networks for [next-gen security]
Related Articles
- Analyzing the Conduent Data Breach: Impacts and Lessons Learned [2025]
- ShinyHunters Hits Wynn Resorts: $1.5M Ransomware Demand [2025]
- AI-Powered Hacking: How Low-Skill Attackers Break Firewalls [2025]
- Mastering Wi-Fi Security: How to Manage and Wipe Saved Networks on Your Device [2025]
- Understanding New Relic's Revolutionary AI Agent Platform and OpenTelemetry Tools [2025]
- NYC Transit Workers Ransomware Attack: What You Need to Know [2025]
![Understanding the Marquis vs. SonicWall Case: Lessons on Firewall Security and Ransomware [2025]](https://tryrunable.com/blog/understanding-the-marquis-vs-sonicwall-case-lessons-on-firew/image-1-1771953089783.jpg)



