Analyzing the Conduent Data Breach: Impacts and Lessons Learned [2025]
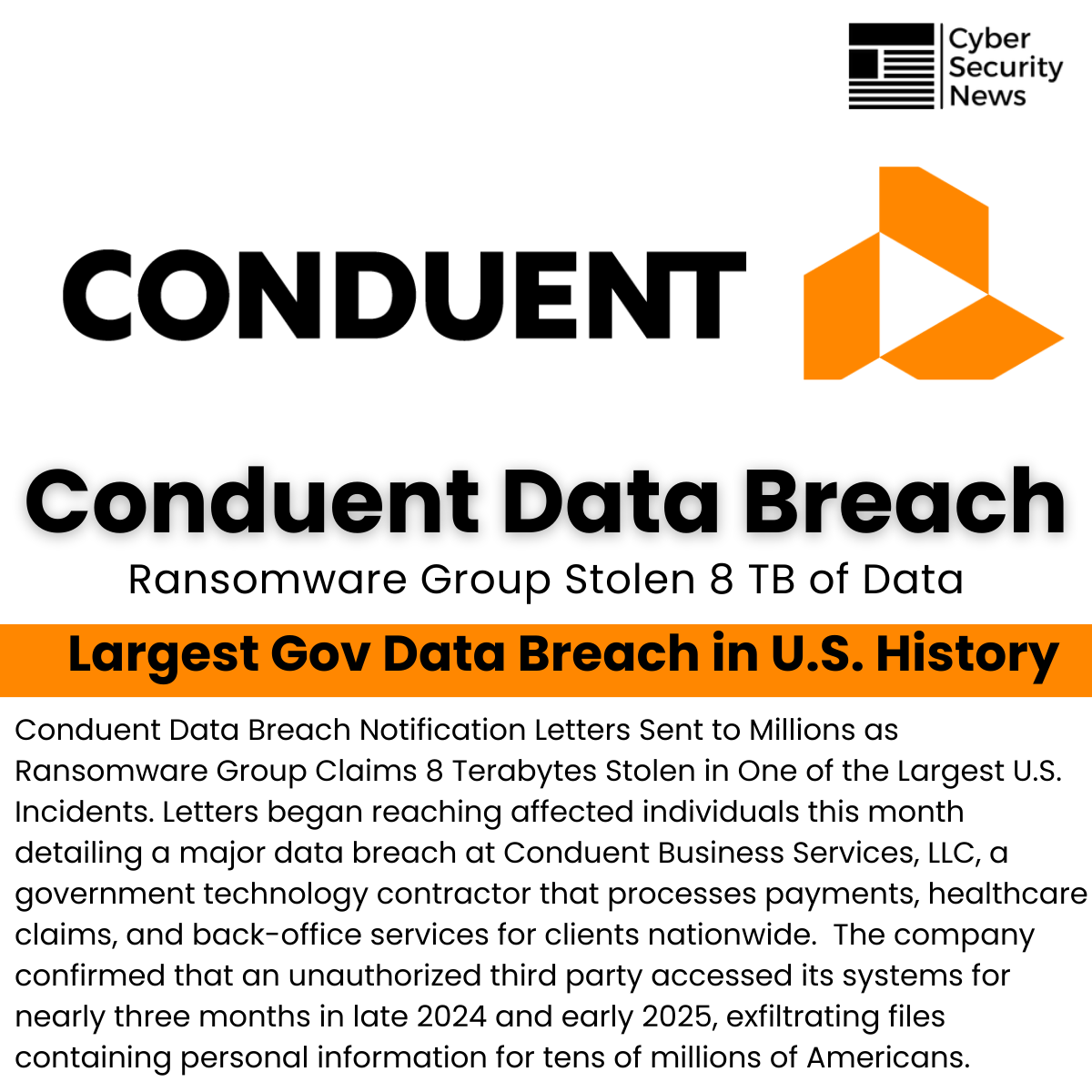
In 2025, Conduent, a major government contractor known for handling sensitive data, faced a massive data breach that exposed the personal information of over 25 million people. This breach, attributed to a ransomware attack, has highlighted significant vulnerabilities in data security practices and has prompted a reevaluation of how such incidents can be prevented. This article delves into the details of the Conduent data breach, its implications, and practical steps to enhance data security.
TL; DR
- Massive Impact: The breach affected over 25 million individuals, exposing sensitive personal data.
- Ransomware Attack: A sophisticated ransomware group claimed responsibility, showcasing the growing threat of cybercriminals.
- Widespread Consequences: Conduent's role in government and corporate services means the breach has far-reaching implications.
- Cybersecurity Weaknesses: The attack highlights critical gaps in data protection strategies.
- Future Recommendations: Organizations must adopt multi-layered security approaches to mitigate risks.

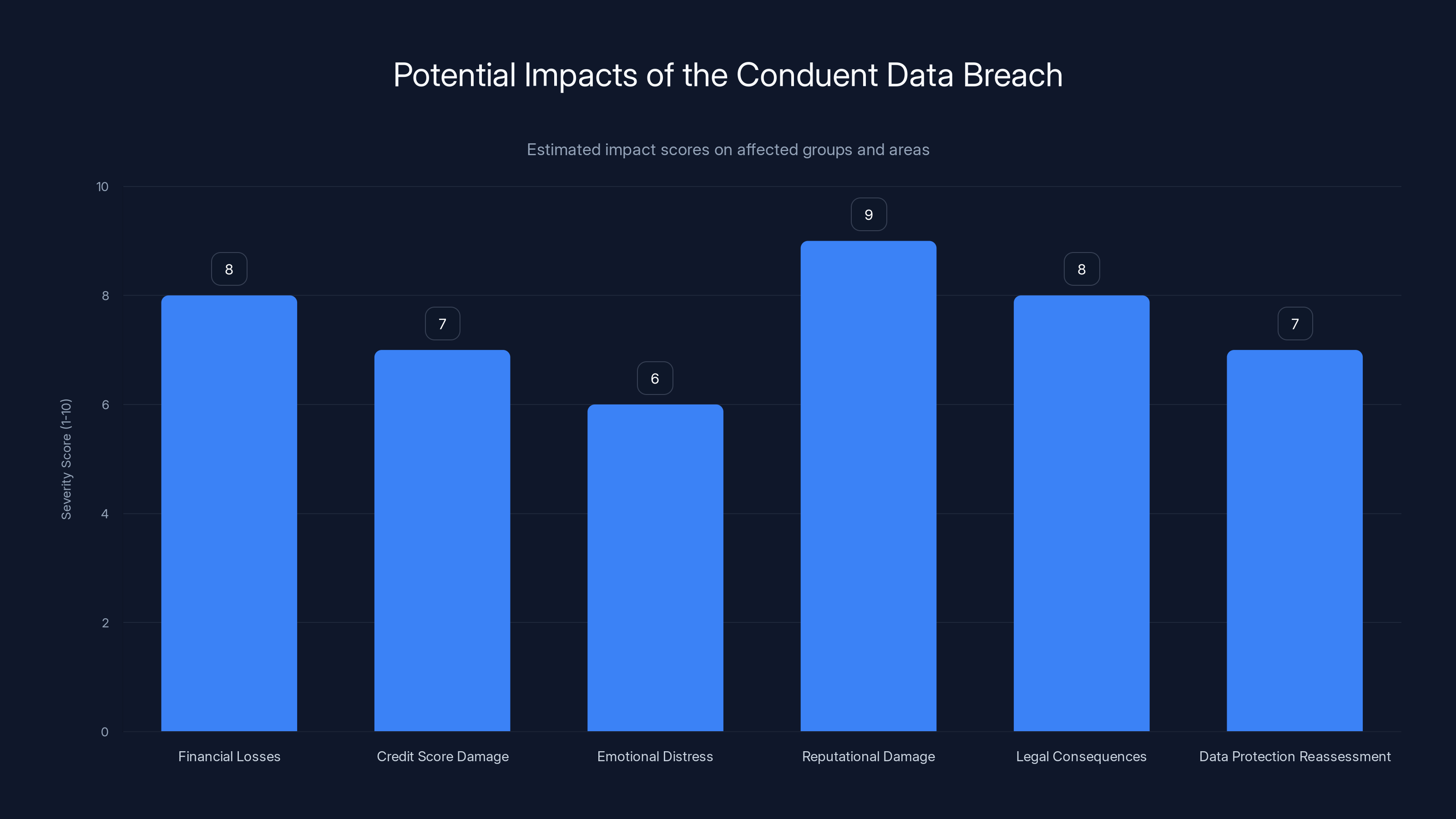
The Conduent breach has significant impacts, notably high reputational damage and financial losses. Estimated data.
Understanding Conduent's Role in Data Management
Conduent is a key player in providing services such as printing, mailroom operations, and document processing for government agencies and large corporations. Handling data for more than 100 million people in the U.S., Conduent is responsible for managing sensitive information, including personal identification and financial data for various state benefits programs.
What Happened in the Conduent Data Breach?
In January 2025, Conduent fell victim to a ransomware attack, a type of cyberattack where malicious actors encrypt a victim's data and demand a ransom to restore access. The attack compromised sensitive information, affecting millions of individuals relying on Conduent's services for government benefits and corporate functions. According to SecurityWeek, the breach also impacted the Volvo Group, exposing data of nearly 17,000 employees.

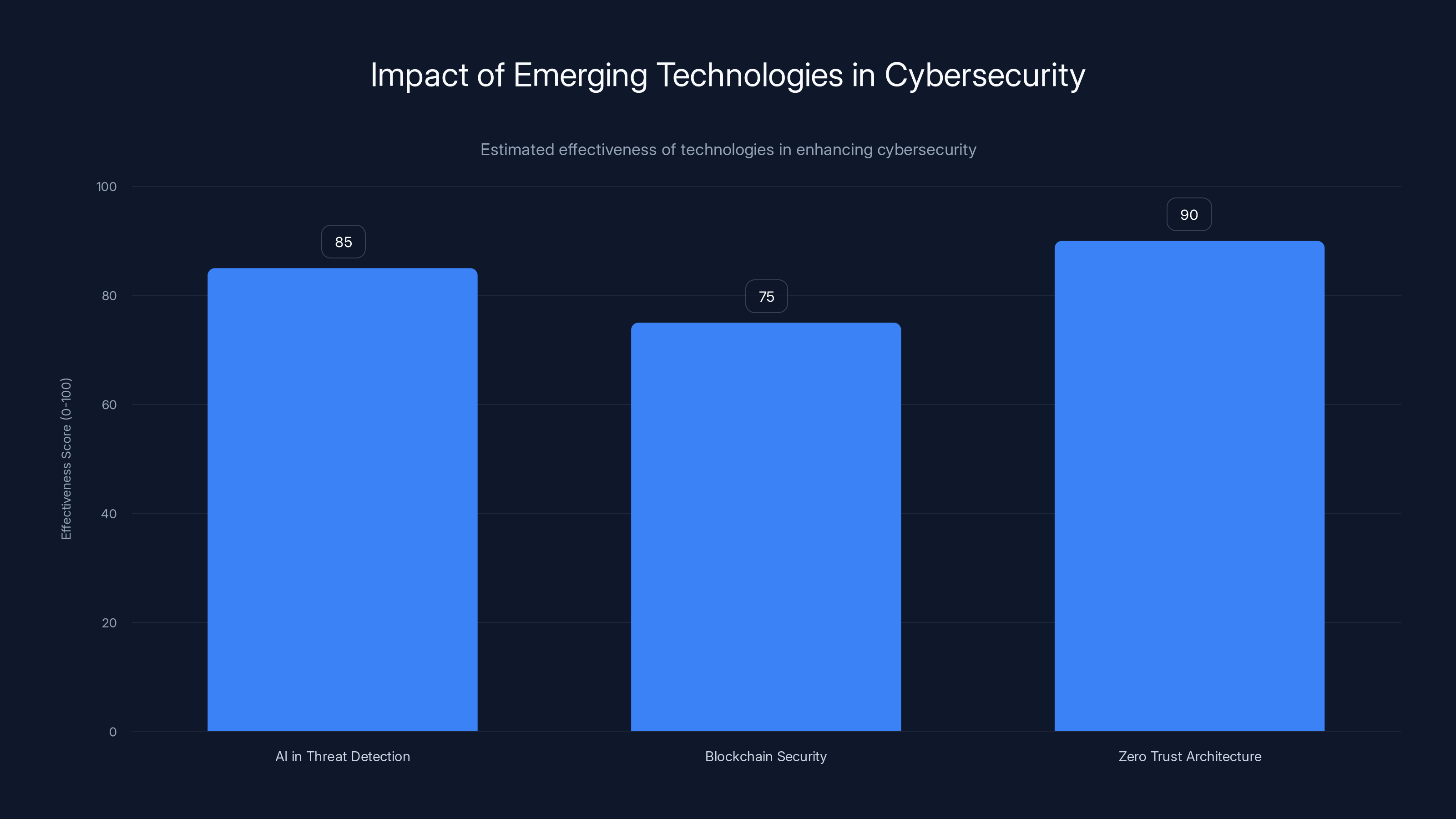
AI, blockchain, and zero trust architecture are projected to significantly enhance cybersecurity, with zero trust architecture being the most effective. Estimated data.
The Mechanics of a Ransomware Attack
Ransomware attacks typically follow a structured approach:
- Infiltration: Attackers gain access to the target's network, often through phishing emails or exploiting software vulnerabilities.
- Encryption: Once inside, they deploy malware to encrypt critical files, rendering them inaccessible.
- Ransom Demand: Attackers demand payment, usually in cryptocurrency, for decrypting the data.
- Decryption or Data Leak: If the ransom is paid, decryption keys are provided; otherwise, data may be leaked or sold on the dark web.
How the Conduent Breach Occurred
While specific details of the Conduent breach are limited, it's likely that the attackers exploited vulnerabilities in Conduent's IT infrastructure, such as outdated software or insufficiently protected network access points. This underscores the importance of regular security audits and updates, as noted in the HIPAA Journal.
Common Vulnerabilities in Data Security
Organizations like Conduent often face several cybersecurity challenges, including:
- Phishing Attacks: Email scams that trick employees into revealing credentials.
- Unpatched Software: Failing to update software can leave systems vulnerable to known exploits.
- Inadequate Access Controls: Poor management of user permissions can allow unauthorized access.
- Weak Password Policies: Using simple passwords makes it easier for attackers to breach accounts.
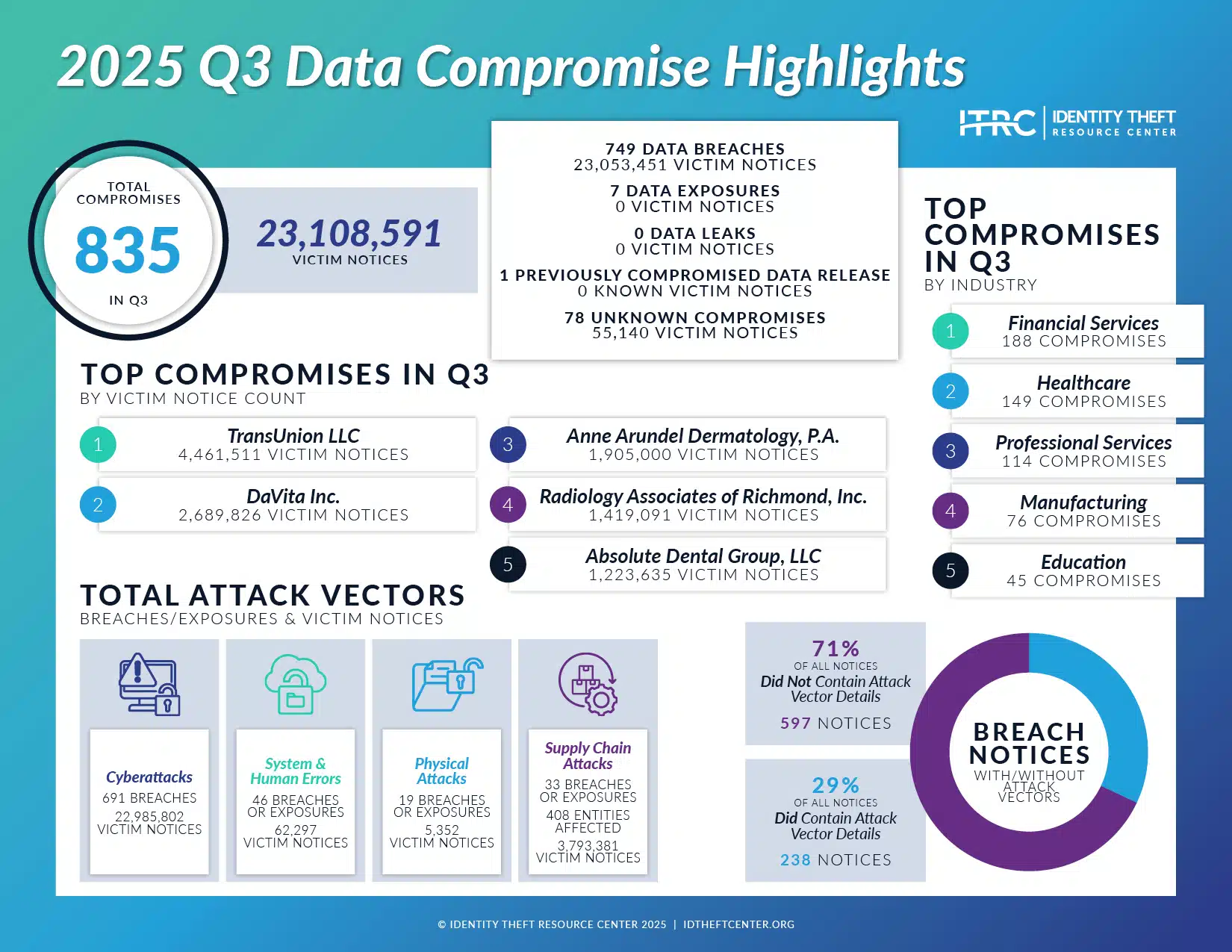
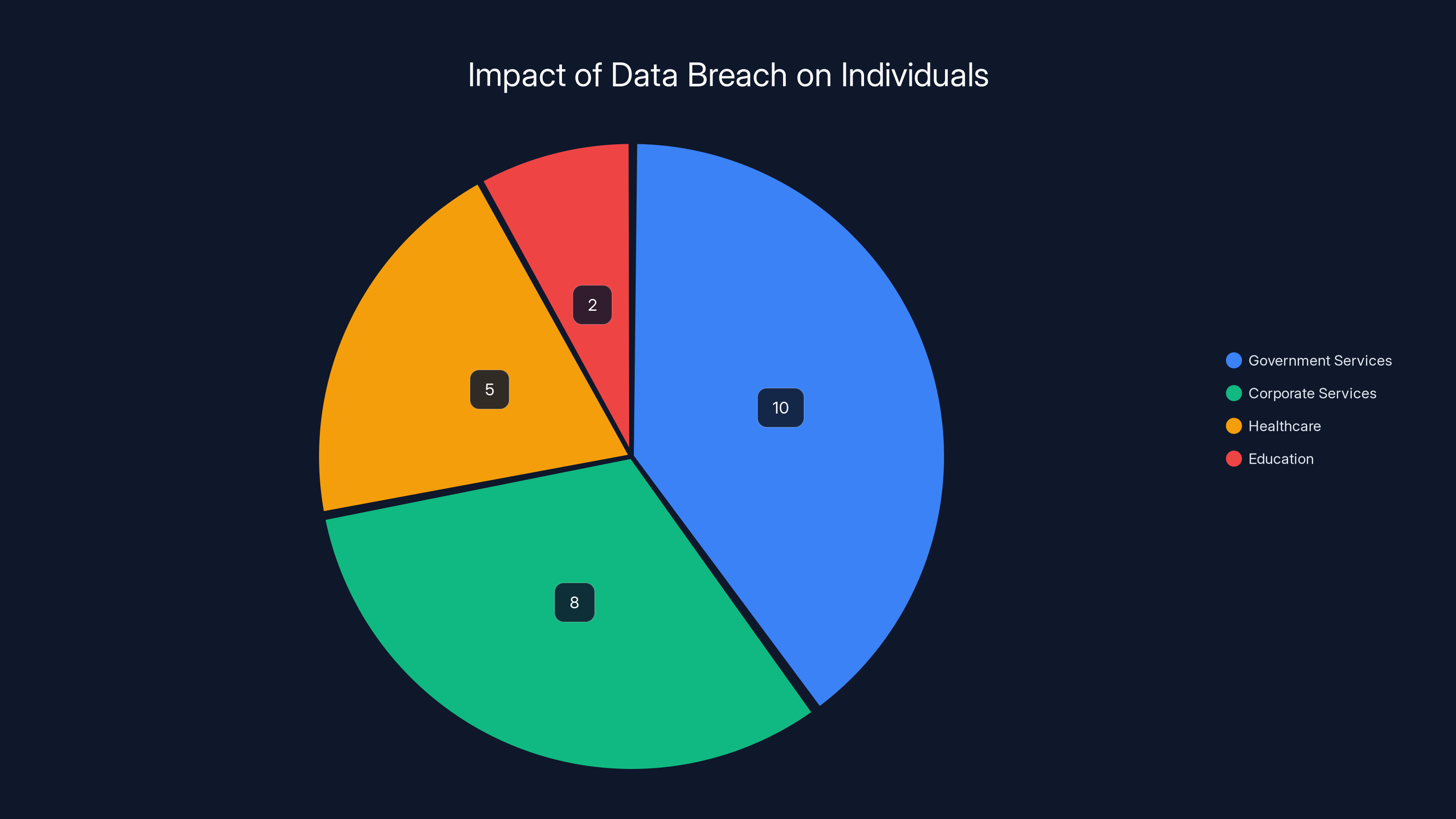
The breach affected over 25 million individuals, with the majority impacted in government and corporate services sectors. Estimated data.
The Broader Impact of the Conduent Breach
The consequences of the Conduent data breach extend beyond the immediate victims. With Conduent's involvement in processing sensitive data for government programs, there are significant implications for data privacy and security at a national level.
Impact on Individuals
Individuals affected by the breach face potential identity theft, financial fraud, and privacy violations. This can lead to:
- Financial Losses: Unauthorized transactions or loans in the victim's name.
- Credit Score Damage: Impacted individuals may see their credit scores drop due to fraudulent activities.
- Emotional Distress: Victims often experience stress and anxiety over potential misuse of their data.
Corporate and Government Ramifications
For Conduent, the breach results in reputational damage, potential legal consequences, and financial losses. Government agencies relying on Conduent's services must also reassess their data protection measures, as highlighted in the Evrim Ağacı report.
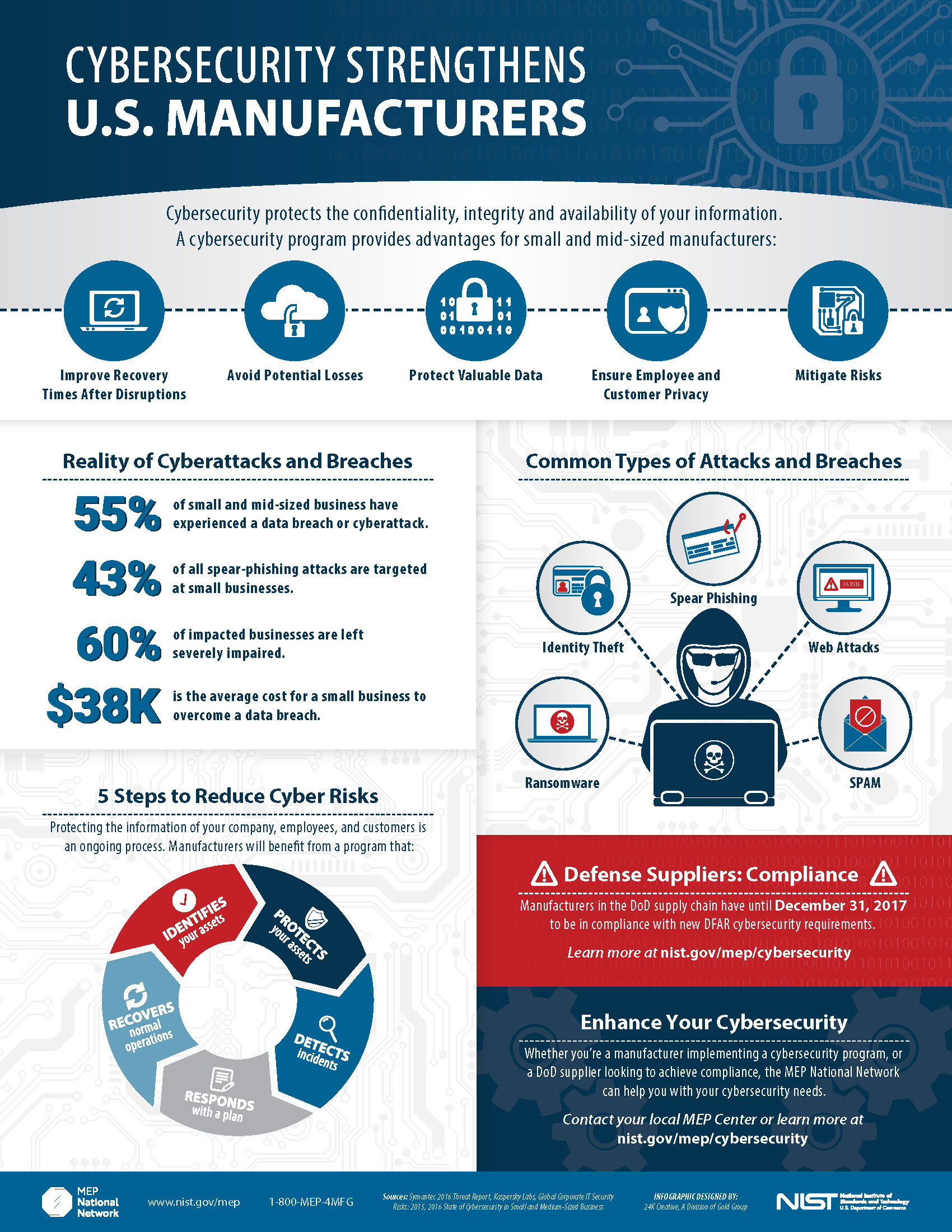
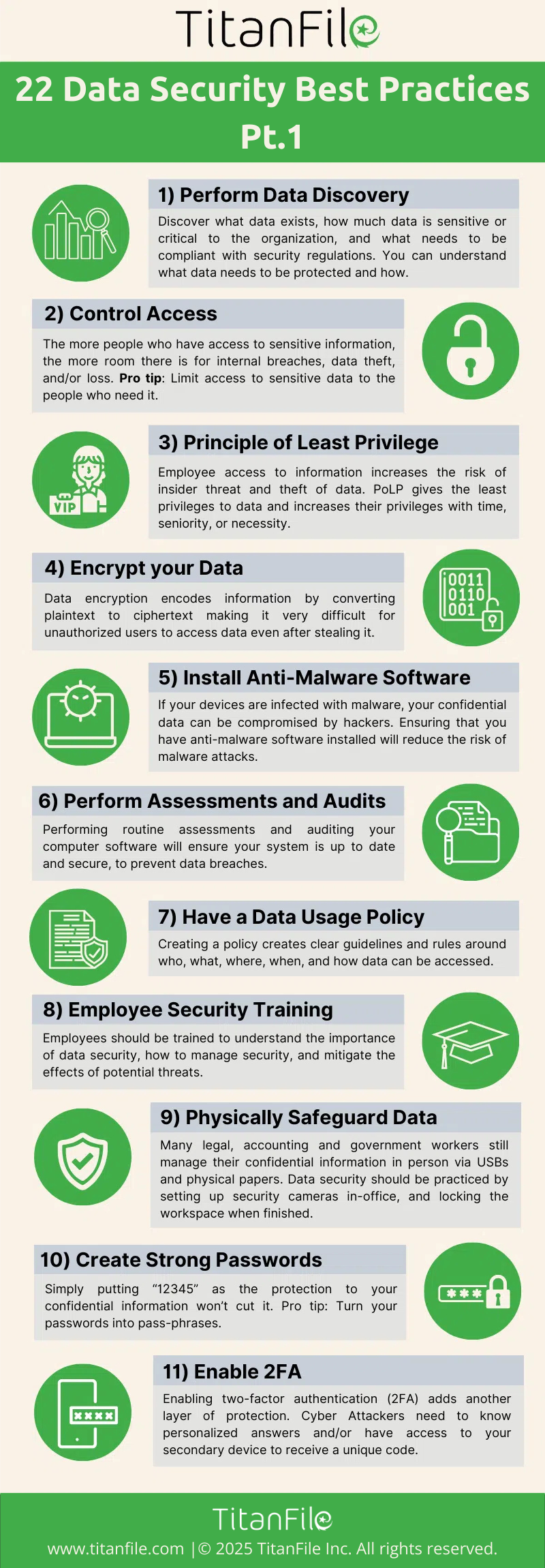
Best Practices for Data Security
To prevent similar incidents, organizations must adopt robust cybersecurity measures. Here are some best practices:
1. Implement Multi-Factor Authentication (MFA)
MFA adds an extra layer of security by requiring users to provide two or more verification factors. This makes it harder for attackers to gain unauthorized access.
2. Regular Security Audits
Conducting frequent security audits helps identify and remediate vulnerabilities. This involves:
- Penetration Testing: Simulating attacks to find weaknesses.
- Network Monitoring: Continuously monitoring for suspicious activity.
- Software Updates: Ensuring all systems are up-to-date with security patches.
3. Employee Training
Educating employees on cybersecurity best practices is crucial. This includes recognizing phishing attempts and handling sensitive data securely.
4. Data Encryption
Encrypting sensitive data both in transit and at rest ensures that, even if data is intercepted, it cannot be read by unauthorized individuals.

Future Trends in Cybersecurity
As cyber threats evolve, organizations must stay ahead by adopting emerging technologies and strategies:
Artificial Intelligence (AI) in Cybersecurity
AI can enhance threat detection by analyzing patterns and identifying anomalies that indicate a potential attack. Machine learning algorithms can automate threat responses, reducing the time needed to mitigate attacks, as discussed in the APA's cybersecurity planning guide.
Blockchain for Secure Transactions
Blockchain technology offers a decentralized and tamper-proof method for verifying transactions, which can enhance the security of financial and data exchange processes.
Zero Trust Architecture
A zero trust approach assumes that threats could be both external and internal. It involves strict identity verification and access control, ensuring that users only have access to the data they need, as recommended by the NSA guidelines.

Conclusion
The Conduent data breach serves as a stark reminder of the persistent threat posed by cybercriminals. Organizations must remain vigilant and proactive in their cybersecurity efforts to protect sensitive information and maintain trust with their clients and partners. By implementing comprehensive security measures and staying informed about emerging threats, businesses can reduce their vulnerability to attacks and safeguard the data of millions.
FAQ
What is the Conduent data breach?
The Conduent data breach occurred in 2025 due to a ransomware attack, exposing the personal data of over 25 million individuals.
How did the Conduent breach happen?
While exact details are scarce, it's believed that attackers exploited vulnerabilities in Conduent's IT infrastructure, likely through phishing or unpatched software.
What was the impact of the breach?
The breach led to potential identity theft, financial fraud, and privacy violations for affected individuals. It also caused reputational and financial harm to Conduent.
What are some best practices for cybersecurity?
Organizations should implement multi-factor authentication, conduct regular security audits, provide employee training, and encrypt sensitive data.
How can AI improve cybersecurity?
AI enhances threat detection by analyzing patterns and identifying anomalies, while machine learning algorithms automate threat responses.
What is zero trust architecture?
Zero trust architecture involves strict identity verification and access control, ensuring that users only have access to necessary data, reducing the risk of internal and external threats.

Key Takeaways
- The Conduent data breach impacted over 25 million people.
- Ransomware attacks exploit vulnerabilities like phishing.
- Multi-layered security measures are essential to prevent breaches.
- AI and blockchain are emerging tools in cybersecurity.
- Zero trust architecture enhances data protection.
Related Articles
- CarGurus Data Breach: 1.7M Records Stolen by ShinyHunters [2025]
- Android AI Photo Editor Data Breach: 2M Users Exposed [2025]
- North Korean Identity Theft Scheme at US Companies [2025]
- Figure Data Breach: What Happened to 967,000 Customers [2025]
- Social Advertising Scams: Unmasking Deceptive Practices on Major Platforms [2025]
- ShinyHunters Hits Wynn Resorts: $1.5M Ransomware Demand [2025]
![Analyzing the Conduent Data Breach: Impacts and Lessons Learned [2025]](https://tryrunable.com/blog/analyzing-the-conduent-data-breach-impacts-and-lessons-learn/image-1-1771943805976.jpg)



