How AI Is Turning Amateur Hackers Into Serious Threats
Here's something that should keep security teams up at night: a Russian hacker with seemingly minimal technical expertise just broke into hundreds of firewalls. Not because they were a genius. Because they had AI.
This isn't theoretical. In early 2025, researchers uncovered a campaign that exposed a chilling reality about modern cybersecurity. A threat actor with basic skills orchestrated a systematic attack against FortiGate firewalls across multiple targets. They brute-forced credentials, extracted sensitive data, moved laterally through networks, and targeted backup systems. All using AI-generated tools and scripts.
The scary part? The attacker wasn't particularly sophisticated. Their code was clunky. Their tactics were straightforward. They abandoned hardened systems when they met resistance. But they didn't need to be sophisticated anymore. AI did the heavy lifting.
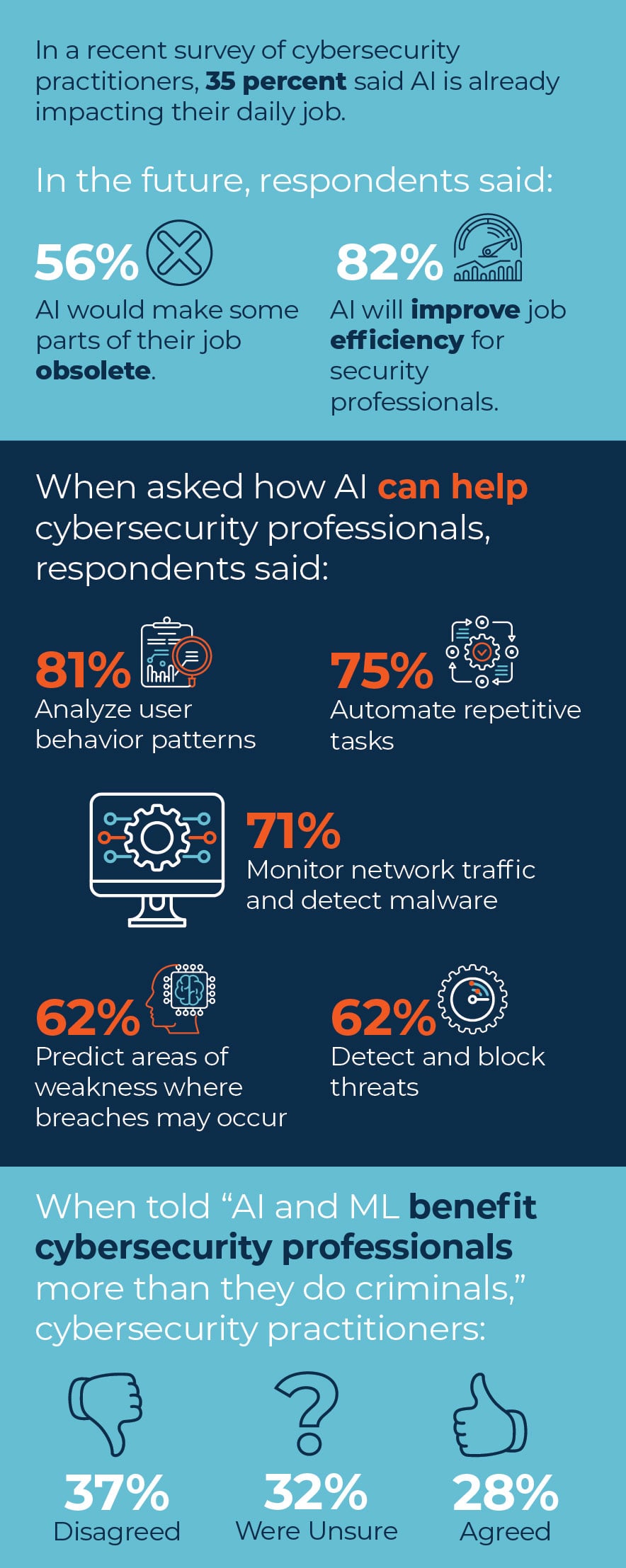
What's happening here is a fundamental shift in cybersecurity dynamics. For decades, the barrier to entry for hacking was high. You needed deep technical knowledge, years of experience, and persistence to pull off serious attacks. AI is demolishing that barrier.
In this article, we're diving deep into exactly how this attack unfolded, why it represents a watershed moment for security, and most importantly, what you need to do about it right now. Because this isn't the end of AI-assisted attacks. It's just the beginning.
TL; DR
- The Core Threat: A low-skilled Russian hacker used AI to brute-force hundreds of FortiGate firewalls and extract sensitive credentials and network data over just 39 days.
- How AI Enabled It: AI-generated Python and Go scripts automated reconnaissance, credential parsing, decryption, and lateral movement through networks without human coding expertise.
- The Real Problem: The attacker's code was sloppy and inefficient, yet still devastated multiple targets, proving that AI doesn't need to be perfect to be effective at scale.
- Target Selection: The attacker prioritized Veeam Backup servers and abandoned well-patched or hardened systems, showing that even AI-assisted attackers follow paths of least resistance.
- What You Must Do: Organizations need zero-trust architecture, behavioral analytics, credential rotation, and security automation to detect and stop these campaigns before they spread.
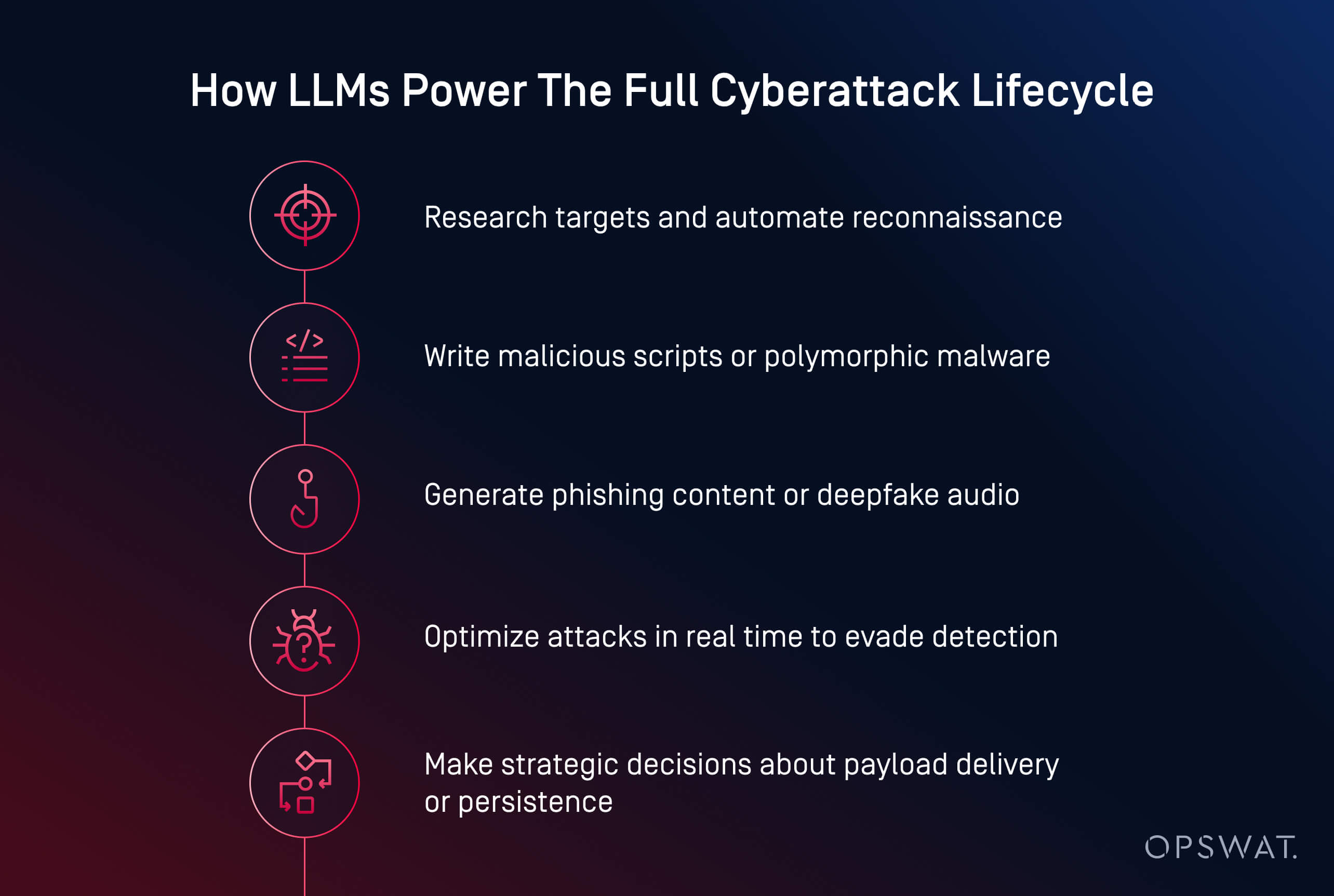

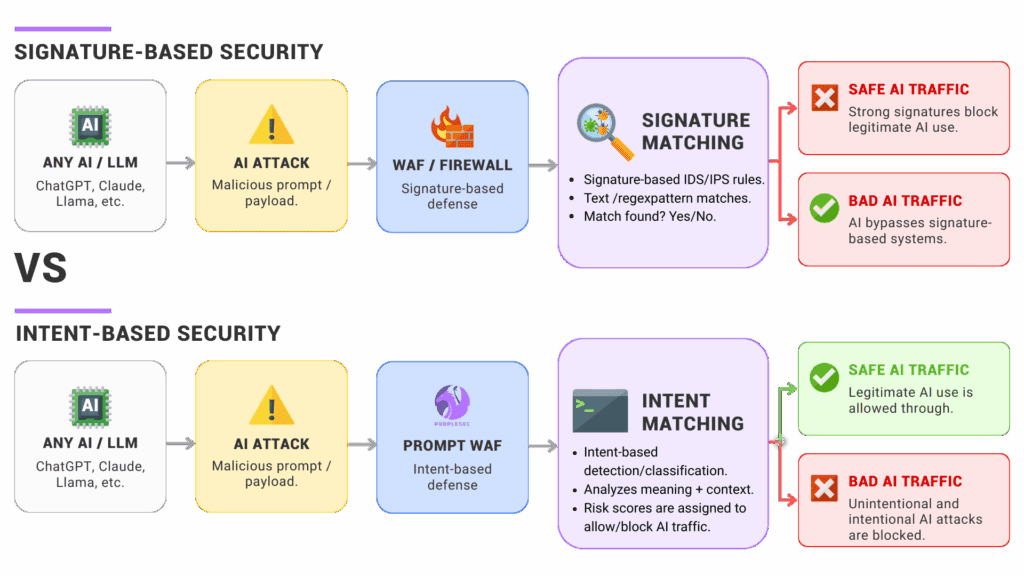
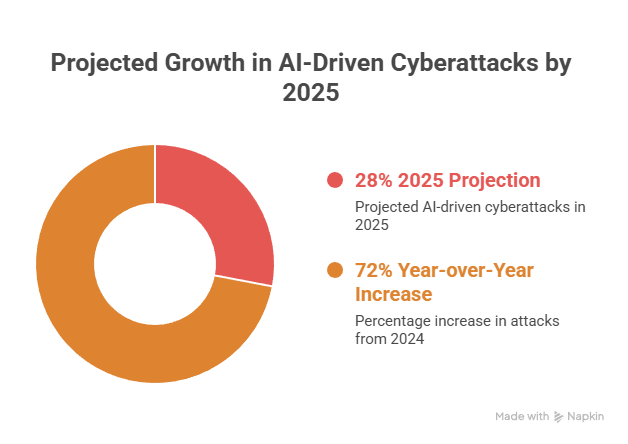
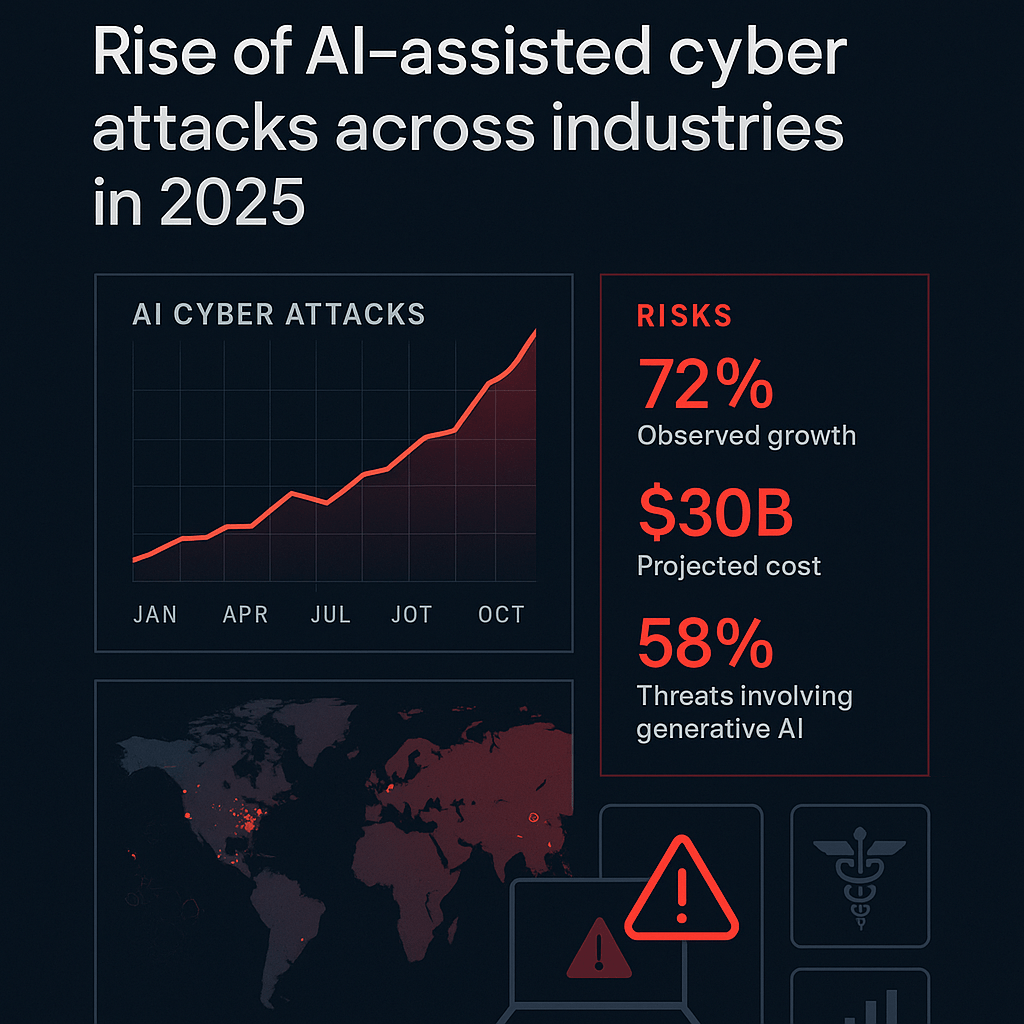
AI significantly lowers skill barriers, increases attack speed, and complicates detection, making attacks more efficient and harder to defend against. Estimated data.
The Attack That Changed Everything
Let's establish the facts first, because they're more alarming than any speculation.
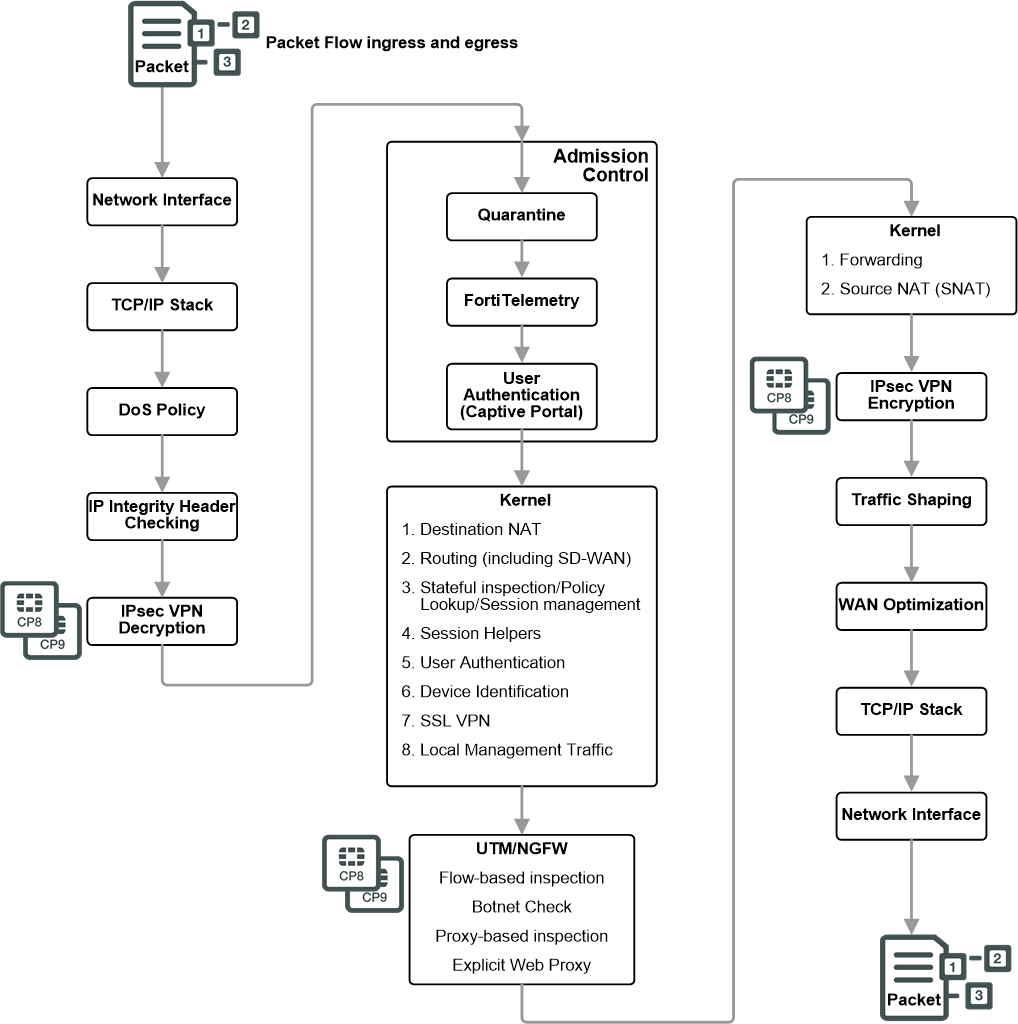
Between January 11 and February 18, 2025, security researchers at Amazon tracked a coordinated campaign targeting FortiGate firewalls across multiple organizations. The attacker scanned for exposed management interfaces on ports 443, 8443, 10443, and 4443—the standard ports where administrators access these devices remotely.
Once they found an exposed interface, they launched a brute-force attack. No sophistication. No exploits. Just trying credential combinations until one worked. Thousands of attempts. Weak passwords like "admin/admin" or "FortiGate/FortiGate" or credentials left over from initial setup.
And it worked. Again and again.
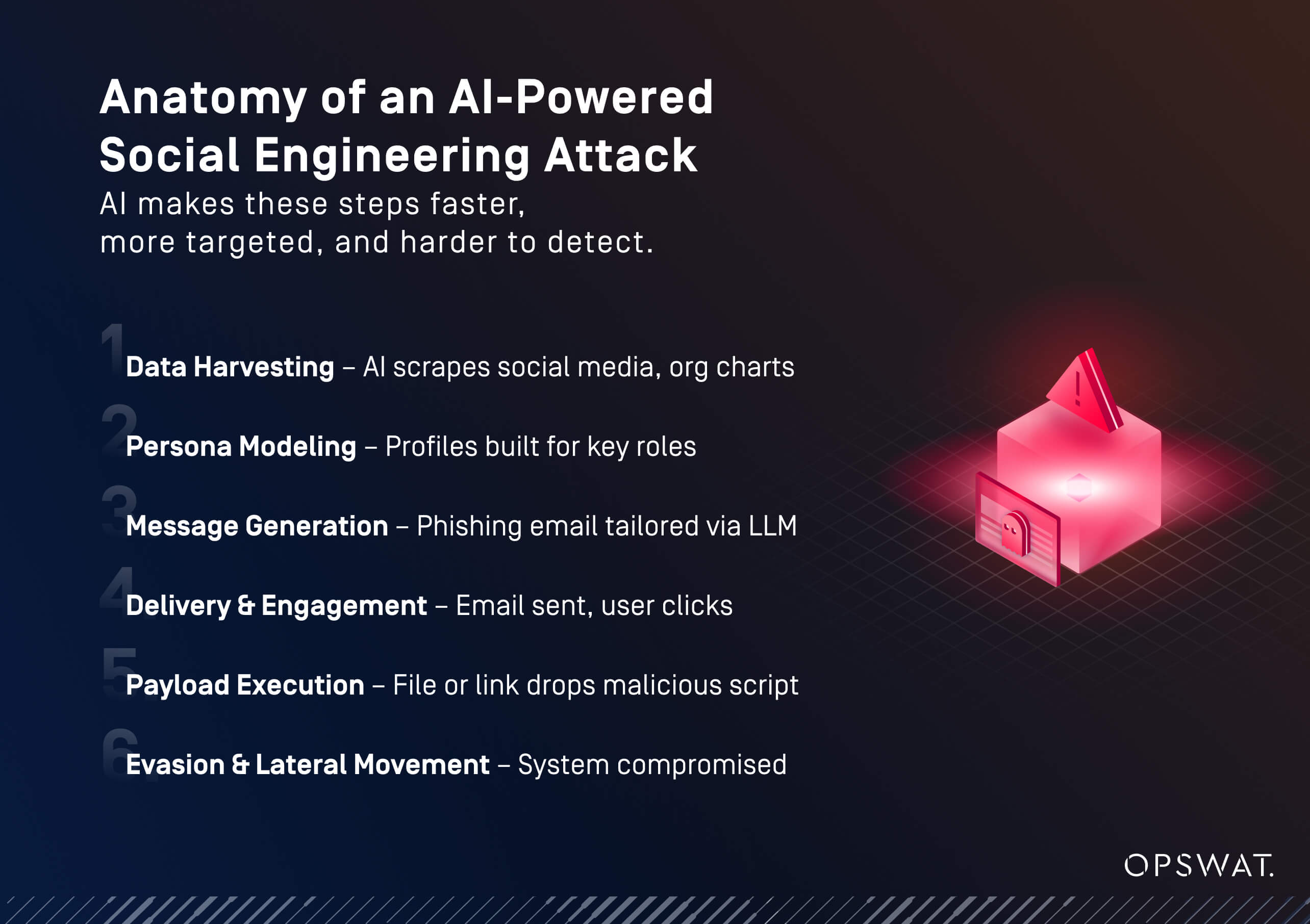
What made this campaign different was what happened next. Instead of fumbling through manual steps, the attacker deployed AI-generated Python scripts. These scripts did something critical: they parsed the extracted firewall configuration files, decrypted the stored credentials (many were recoverable), organized the data, and prepared it for the next phase.
The attacker then used recovered VPN credentials to gain access to internal networks. Here's where it gets serious. They deployed custom reconnaissance tools written in both Python and Go. AI-generated tools. Tools that would normally take weeks to write correctly if you were doing it manually. These tools mapped the internal environment, identified Active Directory systems, and prepared the ground for lateral movement.
All of this happened in 39 days. All orchestrated by someone who, by all evidence, wasn't a world-class coder.
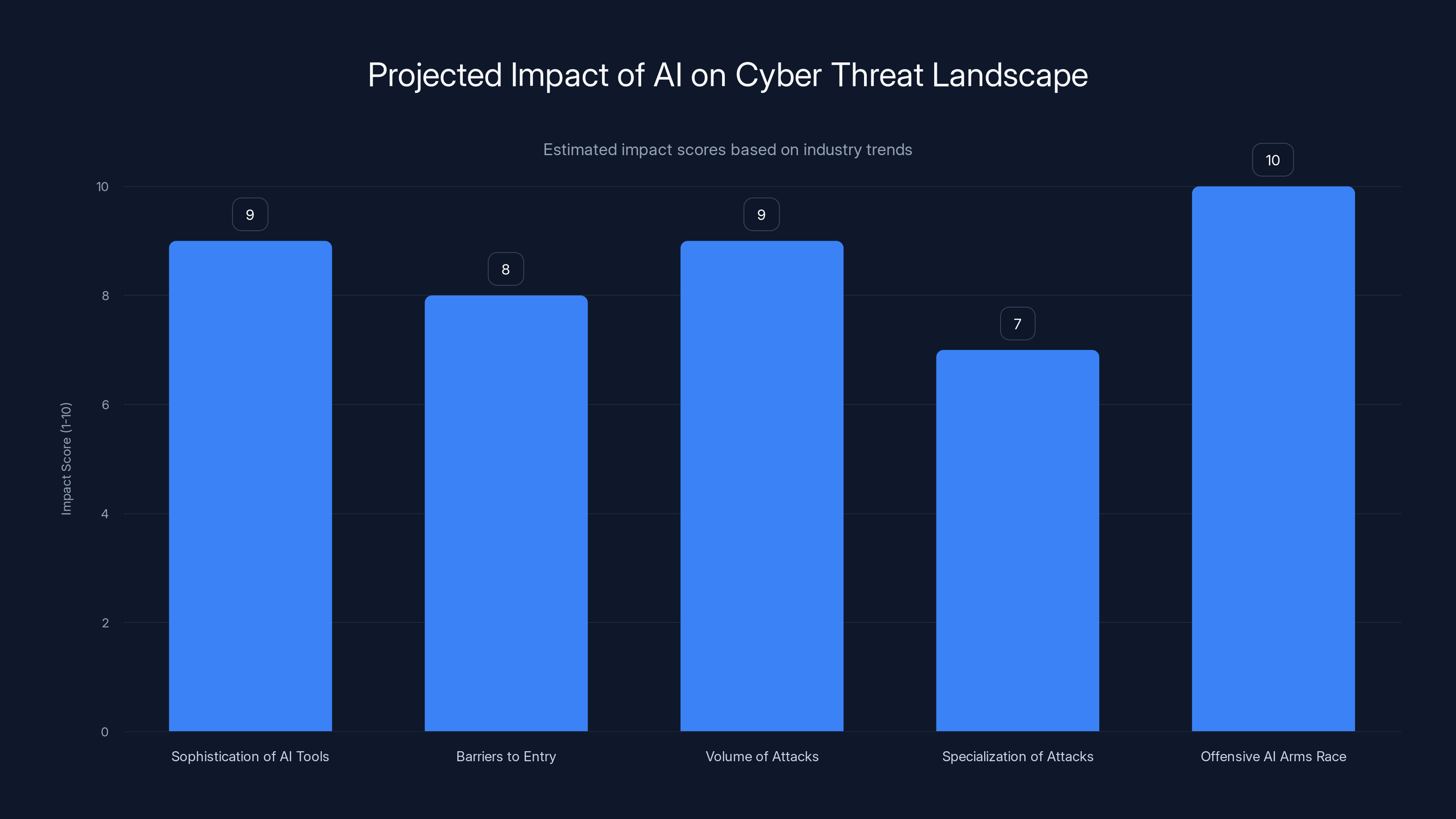
The AI-enabled threat landscape is expected to see significant increases in sophistication, volume, and specialization of attacks, with an ongoing AI arms race. (Estimated data)
Why This Attack Matters More Than You Think
On the surface, this looks like a typical breach. Weak credentials. Lateral movement. Data exfiltration. We've seen this story a hundred times.
But dig deeper and you see the real inflection point.
Previously, attacks at this scale required either: a skilled team with years of experience, significant financial resources, or both. Building custom reconnaissance tools meant writing clean, robust code. Parsing encrypted credentials meant understanding cryptography. Automating across multiple targets meant orchestrating complex operations.
Now? An attacker with basic Python knowledge and access to an AI chatbot can do all of that. And not just competently. Successfully.
The code the researchers analyzed was frankly embarrassing from a software engineering perspective. It had redundant comments. Simplistic architecture. Poor JSON parsing using string matching instead of proper deserialization. It had compatibility shims for language built-ins with zero documentation. Under normal circumstances, a code review would reject it immediately.
But here's the thing: it worked. It worked well enough. It accomplished the mission. In the real world of attacker operations, "good enough" at scale beats "perfect" at a smaller scale.
This represents democratization of hacking. That's the real danger.
When you combine accessible AI tools with public information about common vulnerabilities, you create an environment where motivation and access become the primary barriers to launching attacks. Not skill. Not expertise. Not intelligence.
A motivated attacker with basic technical knowledge can now do damage that previously required a team.
Breaking Down the Attack Flow: Step by Step
Phase 1: Reconnaissance and Initial Access
The attacker started with something simple: port scanning. They systematically scanned for FortiGate management interfaces exposed on the internet. This isn't a vulnerability in FortiGate—it's a configuration problem. Many organizations expose management interfaces because they want remote access for administration.
Once they identified targets, the real attack began. Brute-force attacks against credential databases are ancient tactics. But they work. Most organizations still use weak passwords. Many don't rotate default credentials. Some have credentials that have been exposed in previous breaches circulating on dark web forums.
The attacker tried common combinations first. When those failed, they likely used wordlists from leaked password databases. Eventually, credentials worked. This happens thousands of times across the internet every day.
But what made this attacker different was automation. They automated the entire scanning and credential-testing process across hundreds of targets simultaneously. No human intervention. Just waiting for success.
Phase 2: Credential Extraction and Parsing
Once inside a FortiGate system, the attacker gained access to the full device configuration file. This file contains gold-level intelligence:
SSL-VPN user credentials (often with recoverable passwords stored in weak encryption), administrative credentials, firewall policies and rules, internal network architecture and IP ranges, Active Directory integration details, and third-party system connections.
Normally, extracting and parsing this data would be tedious manual work. The attacker couldn't just search for "password" and grab every value. They needed to understand the file format, identify which fields contained what data, and organize it for the next steps.
Instead of writing this themselves, they generated Python scripts using AI. The scripts parsed the configuration files, identified credential fields, attempted decryption using known weak encryption keys, and organized the results into usable format.
This is where AI's capability becomes truly dangerous. Writing a parser that works for a specific file format requires understanding structure, syntax, and sometimes cryptography. Teaching an AI to generate that code? Takes seconds. Maybe a minute.
Phase 3: Network Reconnaissance and Lateral Movement
With recovered VPN credentials in hand, the attacker now had access to the internal network. They deployed custom reconnaissance tools written in Go and Python—again, AI-generated.
These tools scanned the internal network to identify systems, services, and potential targets. They checked for Active Directory, file servers, backup systems, and other critical infrastructure. They mapped out network topology.
From there, the attacker used standard lateral movement techniques. They moved from the VPN access point toward more sensitive systems. They looked for privilege escalation opportunities. They scanned for systems running known vulnerable software.
And they specifically targeted Veeam Backup & Replication servers. Why? Because backup systems are often the crown jewels of an organization. They contain copies of everything. They're often less hardened than production systems. Compromising a backup system means you've got leverage—either you can exfiltrate the backup data, or you can threaten to delete it.
The attacker deployed credential extraction tools against the Veeam systems and attempted exploitation of known Veeam vulnerabilities.
Phase 4: The Abandonment Pattern
Here's what's fascinating about the attacker's behavior: they didn't persist in hardened environments.
When they encountered well-patched systems or environments with security controls in place, they simply moved on. They tried to exploit CVEs but failed when targets were defended. They hit dead ends and abandoned those targets.
This is actually a positive indicator (though you don't want to be in a position to witness it). It suggests that even AI-assisted attackers follow economic logic. They're looking for return on investment of their time and effort. If a target is hard, they move to an easier one.
But this also reveals the asymmetry of modern attacks: attackers only need to succeed once. Defenders need to succeed every time. When there are hundreds of potential targets, attackers can afford to abandon the 80% that are well-defended and focus on the 20% that aren't.
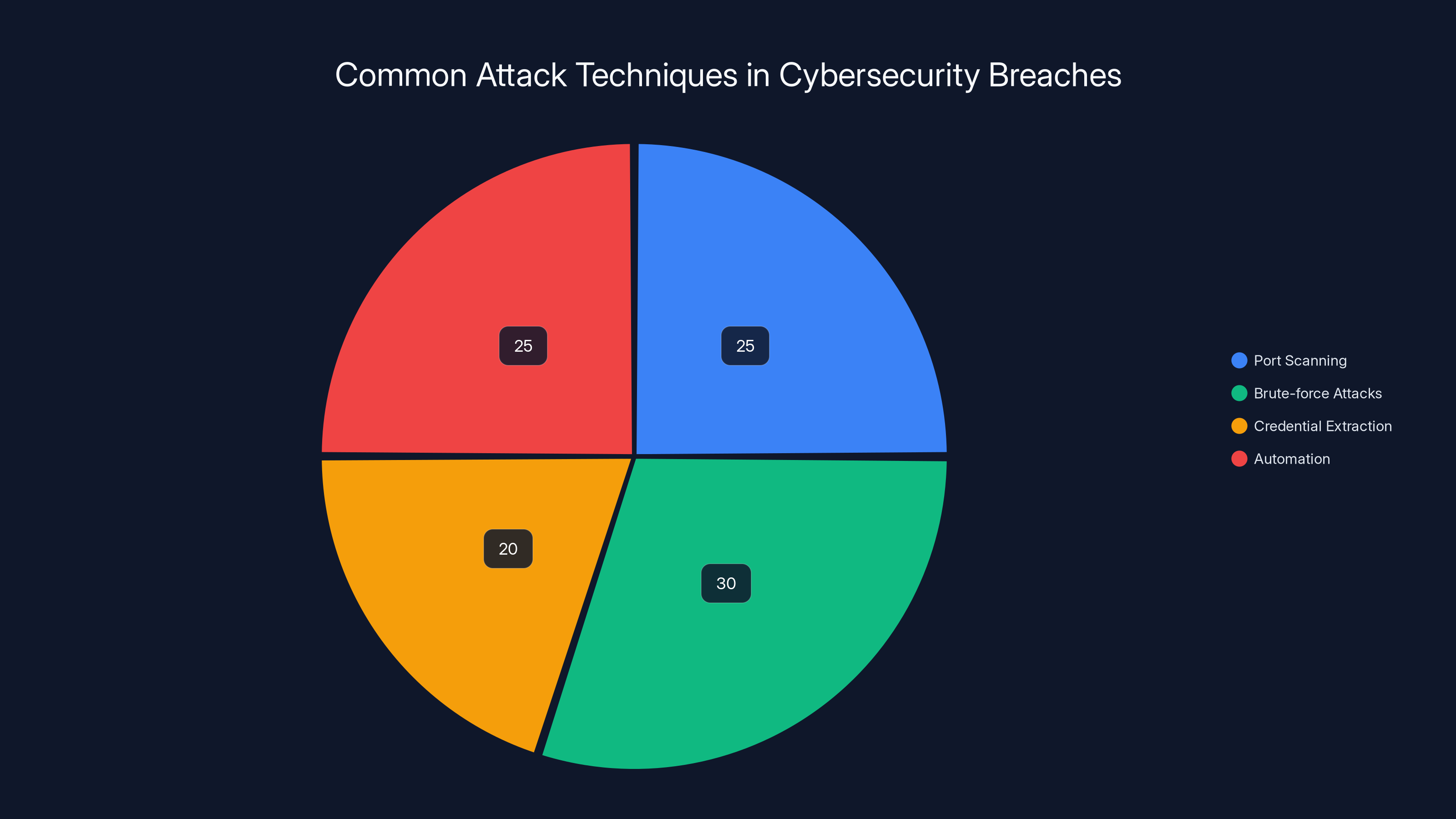
Port scanning and brute-force attacks are common, each making up about 25-30% of attack techniques, with automation playing a significant role in modern breaches. (Estimated data)
The Role of AI in Modern Attacks
How AI Enabled This Attack
Let's be specific about where AI made the difference.
First, code generation. The attacker needed multiple tools: a parser for configuration files, a credential decryption utility, a network reconnaissance scanner, and a lateral movement toolkit. Writing all of that from scratch, testing it, and debugging it would take weeks for a skilled developer. For an unskilled one? Months.
Using AI, they could generate functional code in hours. The code wasn't elegant. It wasn't optimized. But it worked.
Second, automation. Deploying reconnaissance and exploitation tools across multiple networks simultaneously requires understanding how to package and distribute tools, how to execute them remotely, and how to aggregate the results. AI-generated scripts handled all of that.
Third, problem-solving. When a script encountered unexpected data formats or parsing errors, the attacker could describe the problem to an AI and get working solutions. No deep debugging required. No need to understand why something failed. Just "my script doesn't parse this format correctly," and get code that handles it.
Fourth, scale. One human can only do so much in a day. AI can generate dozens of variants of attack tools, test them across multiple environments, and adapt when they fail. The attacker could test multiple credential variations, multiple network scanning approaches, multiple exploitation attempts—all in parallel.
What AI Didn't Do
It's important to note what didn't happen in this attack. The attacker didn't use AI to discover zero-day vulnerabilities. They didn't use AI to bypass security controls through novel methods. They used known vulnerabilities and common attack patterns.
AI didn't make them more intelligent. It made them more efficient at executing conventional tactics.
That distinction matters because it means the defenses against these attacks are well-understood. Organizations know how to defend against brute-force attacks, weak credentials, lateral movement, and exploitation of known vulnerabilities. The problem is execution.
The Firewall Industry's Vulnerability Problem
Why FortiGate Specifically?
FortiGate is one of the most widely deployed firewall platforms globally. Millions of devices are in production. When a large percentage of devices are exposed to the internet with weak credentials, they become targets.
But FortiGate itself isn't uniquely vulnerable. The problem is a combination of factors:
Exposed management interfaces: Many organizations expose firewall management to the internet for convenience. Remote administration is a legitimate need, but it's often done insecurely.
Weak credential practices: Default credentials left unchanged, weak passwords, credentials shared across multiple systems, credentials embedded in configuration files.
Configuration file extraction: FortiGate configuration files contain sensitive data that isn't always encrypted with strong keys. Once extracted, much of the sensitive information is recoverable.
Known exploits: Veeam has had publicized vulnerabilities that attackers can attempt to exploit.
None of these are unique to FortiGate. This same pattern plays out across firewalls, routers, load balancers, and other network infrastructure.
The Broader Firewall Landscape
FortiGate represents roughly 20-25% of the global firewall market. Palo Alto Networks, Cisco, Check Point, and others control significant shares. The attack pattern we're discussing could work against any of them if they're deployed with the same configuration weaknesses.
The attacker chose FortiGate because it was exposed and weak, not because it was inherently the easiest to compromise. If another platform had more exposed, poorly-credentialed devices, that would have been the target.

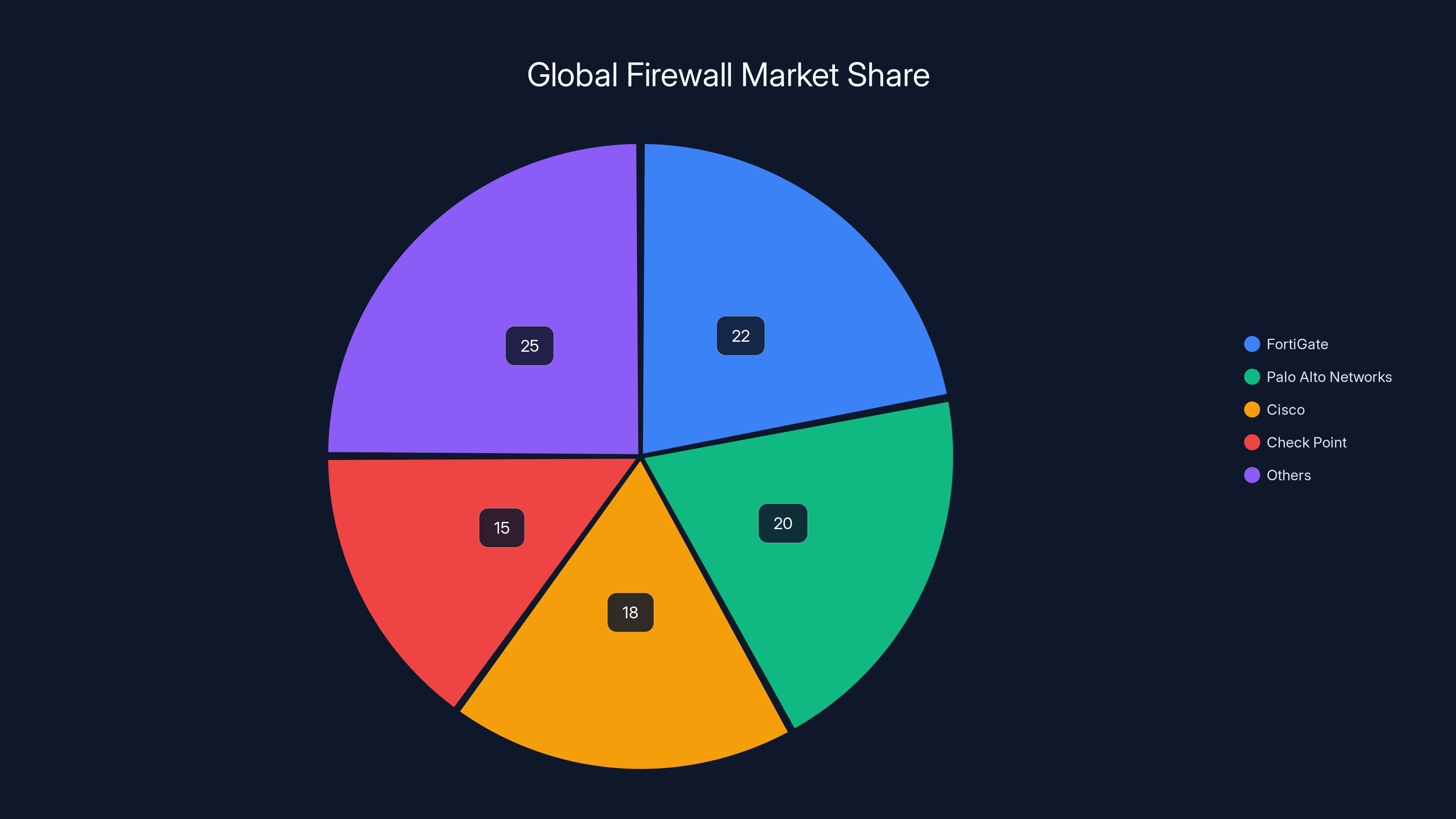
FortiGate holds approximately 22% of the global firewall market, with Palo Alto Networks and Cisco also having significant shares. Estimated data.
Credential Security: The Weakest Link
Why Weak Credentials Remain the Biggest Problem
This entire attack hinged on one thing: weak credentials.
Not a zero-day exploit. Not a sophisticated hack. Weak credentials.
In 2024-2025, we're still fighting this battle. Organizations still use passwords like "FortiGate 123" or "admin" for critical infrastructure. They still reuse credentials across systems. They still leave default credentials unchanged.
Why? Because credential management is boring. It's not flashy. It doesn't impress executives. And it requires constant vigilance.
But it's also where attackers have the best return on investment. If 90% of your targets have weak credentials, you can compromise the vast majority without needing any sophistication.
The Credential Extraction Problem
Once an attacker has access to a firewall configuration file, extracting credentials is often trivial. FortiGate stores some credentials using weak encryption that's easily reversible with known techniques.
This means the attacker doesn't need to crack a password hash. They just need to decrypt it. And many configuration file credentials aren't even hashed—they're stored in ciphertext using keys that are embedded in the firmware or configuration.
Organizations that have been breached and had credentials extracted from configuration files should assume those credentials are compromised across their entire network. Changing the affected credentials everywhere they're used becomes a massive operation.
Multi-Factor Authentication Opportunity
Here's what stops this attack cold: multi-factor authentication.
If the FortiGate management interface required MFA, the attacker's stolen credentials would be useless. They'd have the username and password, but they couldn't authenticate without the second factor.
Yet MFA adoption for network device management remains shockingly low. Many organizations don't deploy MFA because their device management systems don't support it, or because they think the risk isn't high enough to justify the operational complexity.
This attack should serve as a wake-up call.
The Veeam Connection: Why Backup Systems Matter
Backup Systems as Attack Targets
The attacker specifically targeted Veeam Backup & Replication servers. This wasn't random. Backup systems are increasingly valuable targets in modern attacks.
Why? Because backups contain complete copies of your data and systems. Compromising a backup server means you can:
- Exfiltrate data: Copy everything the organization backs up
- Encrypt backups: Execute ransomware against backups, destroying recovery options
- Modify backups: Introduce malware into backups, ensuring persistence after recovery
- Leverage backups: Threaten to delete or release backups unless ransom is paid
The attacker in this campaign deployed credential extraction tools against the Veeam systems. This suggests they were attempting to move from the Veeam server into backup storage, or extract administrative credentials from the Veeam system itself.
Backup Security in Practice
Most organizations treat backups as trusted infrastructure. They assume that if you have access to the backup system, you've already won. Backup systems typically have less stringent security controls than production systems.
But when backups themselves become targets, that assumption breaks down. Organizations now need to apply the same security rigor to backup infrastructure as they do to production:
- Immutable backups: Store backups in immutable mode where they can't be modified or deleted
- Isolated networks: Keep backup systems on separate networks with restricted access
- Strong authentication: MFA on backup system access
- Encryption: Encrypt backup data both in transit and at rest
- Monitoring: Alert on unusual backup access patterns
- Regular testing: Test restore procedures to ensure backups are actually usable
The attacker abandoned backup systems when they found them well-protected. This is important: it confirms that even AI-assisted attackers respect defensive controls.
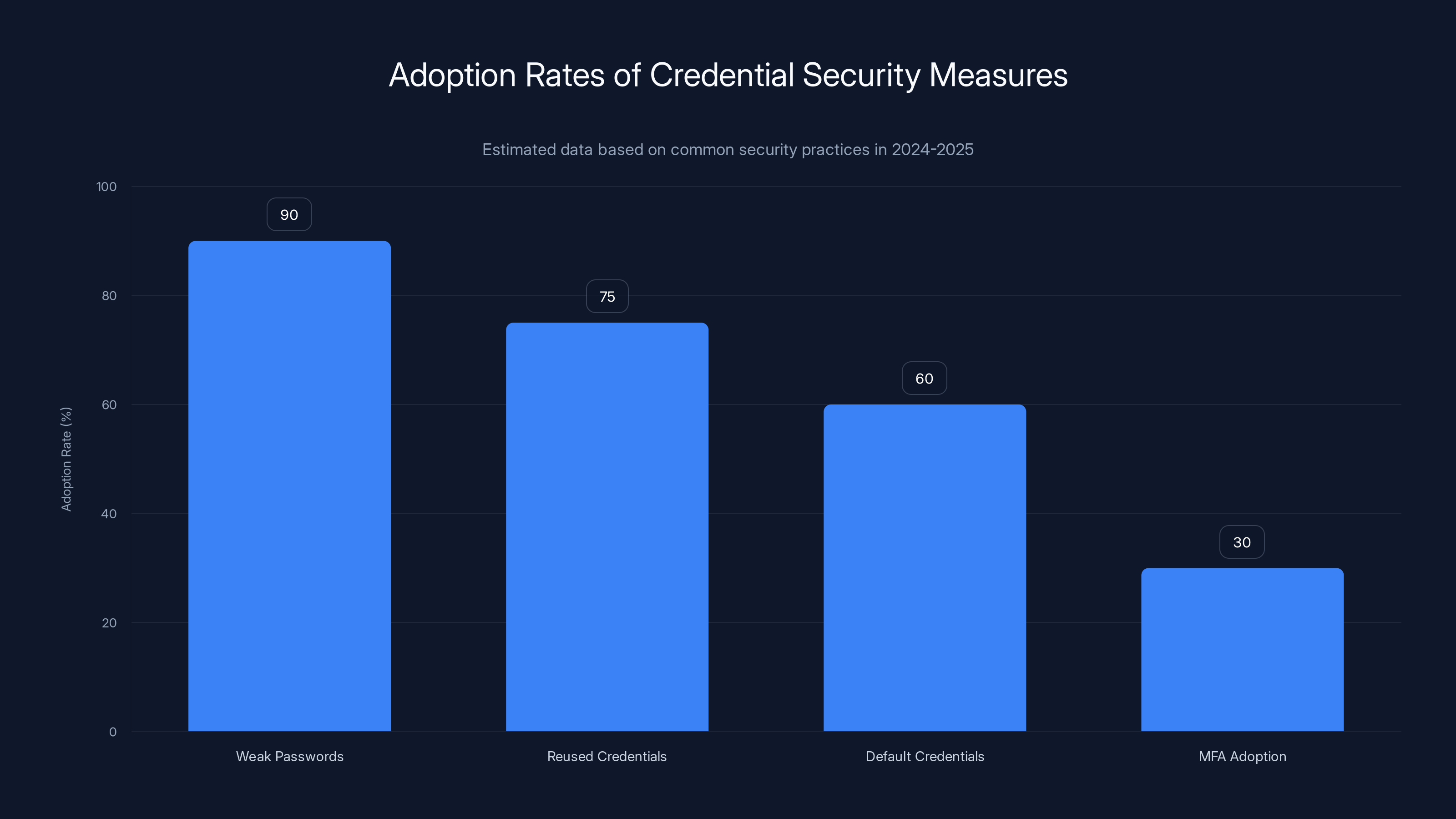
Weak passwords and reused credentials are highly prevalent, with an estimated 90% and 75% adoption rate respectively, while multi-factor authentication (MFA) adoption remains low at 30%. Estimated data.
AI-Generated Code: Strengths and Weaknesses
Why AI Code Often Looks Weird
The researchers analyzing this attack made an important observation: the code showed clear signs of AI generation.
Redundant comments: The AI wrote comments that just restated what the code was already doing. Instead of explaining why a decision was made, it explained what the code was doing, which the code itself already communicated.
Simplistic architecture: The code was architecturally naive. There wasn't clear separation of concerns. Functions were either trivial or overly complex. It looked like code written without an architectural vision.
Improper parsing: The attacker's JSON parser used string matching instead of proper JSON deserialization. It looked for the literal string "key": " instead of properly parsing the JSON structure. This works until it encounters unexpected formatting, then it fails silently.
Compatibility shims: The code included workarounds for language built-ins that didn't need workarounds, suggesting the AI-generated code was treating language basics as unfamiliar problems.
These are characteristic of current AI code generation. The models generate code that looks correct because it has the right syntax, but lacks understanding of design principles or proper implementation practices.
Yet it still accomplished the mission.
Why It Still Works
Here's the critical insight: the code only needs to work for the specific use case.
The attacker's credential parser only needed to parse FortiGate configuration files, not arbitrary JSON. The reconnaissance tool only needed to detect systems relevant to the attacker's objectives, not comprehensively scan all network infrastructure.
When you optimize for specific use cases instead of general robustness, even poorly designed code works.
Moreover, the attacker could iterate quickly. If a script failed in an unexpected way, they could generate a fixed version in minutes. No debugging needed. No deep understanding required. Just "fix this error" and get working code.
The Efficiency Gain
For an unskilled attacker, the real advantage of AI code generation is efficiency, not quality.
Writing a functional credential parser from scratch requires understanding file formats, data types, encryption, and proper error handling. That might take an experienced developer a few hours, or a junior developer a few days.
Using AI, an attacker with basic Python knowledge could generate working code in 10 minutes. Sure, it's not as good as code written by an expert. But it's infinitely better than what they could write themselves from scratch.
That efficiency multiplies across an attack campaign. More tools, deployed faster, across more targets, with rapid iteration when something breaks.
Defensive Measures: What Actually Works
Zero Trust Architecture
Zero trust means: never trust, always verify. Apply this principle to your network infrastructure.
Instead of assuming that anything inside your network firewall is trustworthy, verify every access request. This means:
- Network segmentation: Isolate management networks from operational networks
- Identity verification: Require strong authentication for every system access
- Continuous validation: Verify access permissions on every request, not just at initial authentication
- Encryption: Encrypt all internal traffic, not just external communications
- Monitoring: Log and analyze all access to critical systems
The attacker in this campaign was able to move laterally from the compromised firewall into the internal network. Zero trust architecture would have forced them to re-authenticate for each system they tried to access, and would have immediately flagged the unusual access patterns.
Credential Management
This is obvious but worth stating clearly: your credentials are only as strong as your weakest system.
Implement proper credential management:
- Rotate credentials regularly: Change critical passwords every 30-60 days
- Use strong passwords: Enforce password policies that require complexity
- Eliminate shared credentials: Every person needs their own account
- Vault sensitive credentials: Use secrets management systems instead of storing credentials in files
- Monitor credential usage: Alert on unusual authentication patterns
- MFA everywhere: Require multi-factor authentication for all critical systems
Most of this campaign could have been stopped by enforcing these practices.
Network Monitoring and Analytics
Detecting attacks requires observing unusual behavior.
Brute-force detection: Most modern firewalls and intrusion detection systems can detect brute-force attacks and block them automatically. This should be configured by default.
Lateral movement detection: When a compromised firewall suddenly starts accessing internal systems it never communicated with before, that's anomalous. Behavioral analytics can flag these patterns.
Credential usage monitoring: If a credential is being used from an unusual location or at an unusual time, that's a red flag. Log and alert on these events.
Backup access monitoring: Unauthorized or unusual access to backup systems should trigger immediate investigation.
The attacker in this campaign probably had a 39-day window before being discovered. During that time, they were doing reconnaissance, moving laterally, and attempting exploits. Any modern security monitoring system should have detected multiple phases of this attack.
Patch Management
The attacker used known vulnerabilities, not zero-days. They attempted to exploit publicized CVEs.
Patching might seem obvious, but it bears repeating: if your systems are running the latest security patches, most known-vulnerability-based attacks fail immediately.
The attacker found hardened, patched systems and moved on to easier targets. That's the behavior you want to induce in attackers.
Patch management best practices:
- Automated patching: Apply security patches automatically when possible
- Rapid deployment: Critical security patches should be deployed within days, not weeks
- Vulnerability tracking: Monitor CVE feeds for vulnerabilities affecting your infrastructure
- Rollback plans: Have a tested procedure to roll back patches if they cause problems
- Prioritization: Apply patches to internet-facing systems and critical infrastructure first
Incident Response and Forensics
If a compromise does occur, rapid detection and response are critical.
Detection capabilities:
- EDR (Endpoint Detection and Response): Software agents on systems that detect suspicious behavior
- SIEM (Security Information and Event Management): Centralized log aggregation and analysis
- Behavioral analytics: Machine learning models that identify unusual activities
- Threat intelligence: Information about known attack patterns and indicators of compromise
Response procedures:
- Containment: Isolate compromised systems to prevent spread
- Evidence preservation: Collect forensic data before wiping systems
- Investigation: Determine what was accessed and what data was exfiltrated
- Recovery: Rebuild systems from clean backups
- Post-mortem: Understand how the breach occurred and prevent recurrence
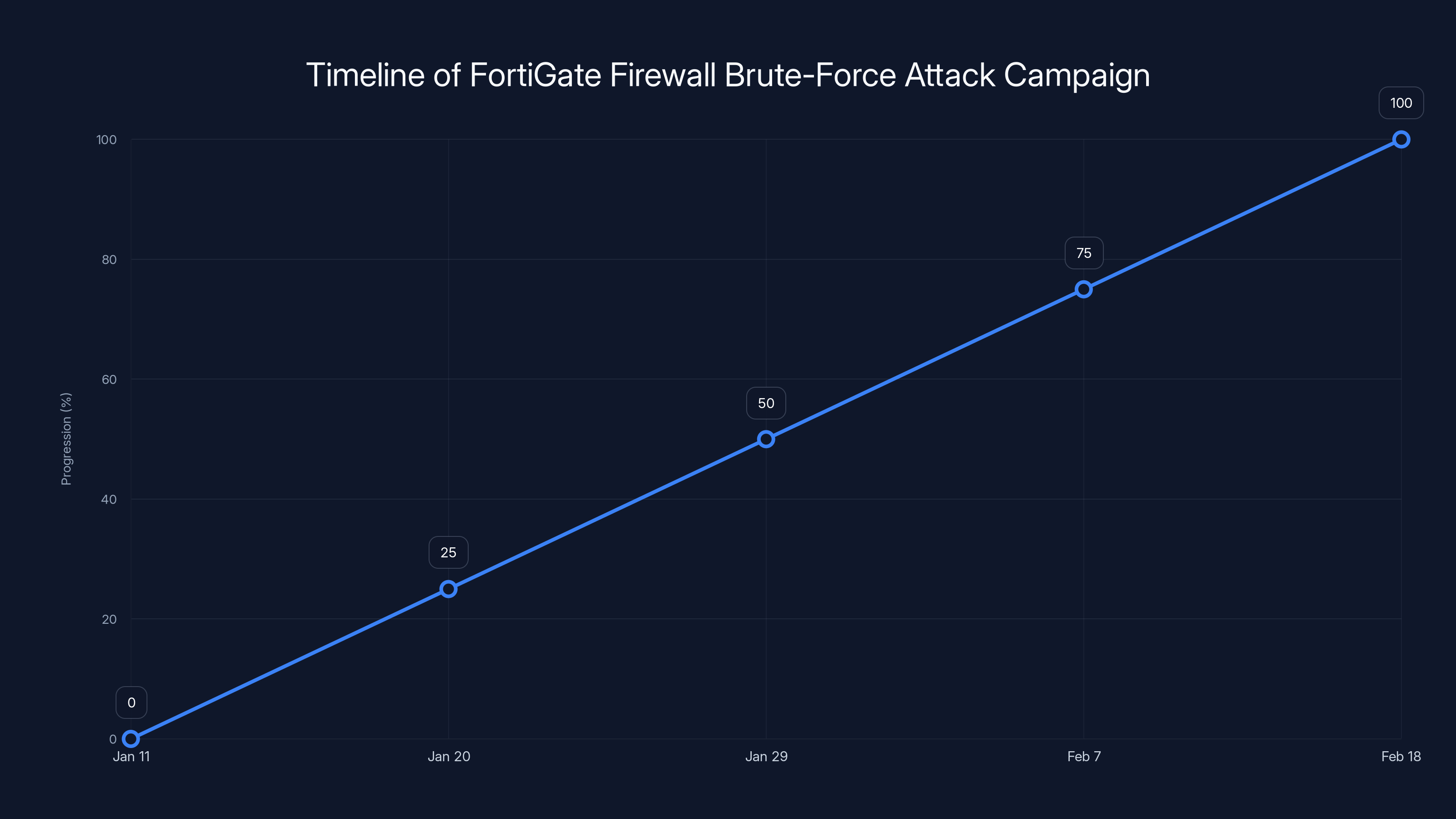
The attack campaign progressed through four main stages over 39 days, from reconnaissance to targeting backup servers. Estimated data.
The Broader Threat Landscape
AI as a Force Multiplier for Attacks
This Russian hacker campaign is an inflection point. It demonstrates that AI is becoming a force multiplier for attacks.
Consider the statistics:
- Skill barriers falling: Attacks that previously required specialized knowledge now require access to AI
- Attack speed increasing: Time from initial compromise to lateral movement to data exfiltration is shrinking
- Attack scale expanding: Single attackers are compromising hundreds of targets in weeks
- Detection difficulty rising: AI-generated tools and tactics are harder to fingerprint and attribute
Organizations that haven't updated their security posture for an AI-assisted threat landscape are increasingly vulnerable.
Who Uses AI for Attacks?
Initially, you might assume only sophisticated state-sponsored actors use AI for hacking. This campaign disproves that.
The attacker was apparently a freelancer or small group, operating outside state sponsorship structure. They had motivation (likely financial), access to AI tools, and basic technical knowledge. That was enough.
As AI tools become more accessible and user-friendly, the pool of potential attackers expands. You're no longer defending against just the most skilled 1% of the hacker population. You're defending against anyone with motivation and a subscription to an AI service.
Defensive AI Opportunities
The flip side: defenders can also use AI.
Security automation: AI can automate threat detection, log analysis, and incident response Behavioral analysis: Machine learning can identify anomalous activity better than static rules Vulnerability prediction: AI can predict which vulnerabilities are likely to be exploited Threat modeling: AI can help organizations model their threat landscape and prioritize defenses
The question isn't whether to use AI in security. It's how to use it most effectively. Organizations that don't develop defensive AI capabilities will fall further behind attackers using offensive AI.

Case Study: What Went Wrong and How It Could Have Been Prevented
Let's walk through this attack and examine each point of failure.
Pre-Breach: The Exposure
What happened: Firewall management interfaces were exposed to the internet.
Why it failed: The organization either intentionally exposed these interfaces for remote administration, or failed to properly restrict access.
How to prevent it:
- Firewall management should never be directly exposed to the internet
- If remote management is required, implement it through a secure jump host or VPN
- Restrict administrative access to known IP ranges
- Use private/internal networks for management traffic
Initial Access: Weak Credentials
What happened: Brute-force attacks against firewall administrative credentials succeeded.
Why it failed: Credentials were weak (common defaults or simple passwords).
How to prevent it:
- Use strong, randomly-generated credentials
- Disable default credentials during initial setup
- Implement account lockout after failed attempts
- Deploy MFA for administrative access
- Monitor failed authentication attempts
Post-Access: Configuration Extraction
What happened: The attacker extracted complete firewall configuration files containing credentials.
Why it failed: Configuration files contained credentials in weak encryption.
How to prevent it:
- Don't store credentials in configuration files
- Use proper secrets management systems
- If credentials must be in configs, encrypt them with strong keys
- Implement access controls on configuration files
- Monitor configuration file access
Lateral Movement: Weak Internal Security
What happened: The attacker moved from the firewall into the internal network.
Why it failed: Internal network assumed anything inside the firewall was safe.
How to prevent it:
- Implement network segmentation
- Require authentication for all internal access
- Monitor internal traffic for anomalies
- Deploy behavioral analytics
- Isolate critical systems
Target Selection: Vulnerable Backup Systems
What happened: The attacker targeted Veeam Backup systems with known vulnerabilities.
Why it failed: Backup systems weren't hardened against determined attackers.
How to prevent it:
- Keep backup systems patched and updated
- Isolate backup systems on separate networks
- Implement strong authentication for backup access
- Monitor backup access patterns
- Implement immutable backups
At any of these points, proper defensive controls would have stopped the attack. But the attacker only needed to succeed once. Defenders needed to succeed everywhere.
What Organizations Should Do Right Now
Immediate Actions (This Week)
-
Audit exposed management interfaces: Scan your network for exposed firewall, router, and device management interfaces. Any found should be immediately restricted or isolated.
-
Review administrative credentials: Audit who has administrative access to critical infrastructure. Rotate any shared credentials. Implement unique credentials for each administrator.
-
Enable brute-force protection: Configure account lockout policies on all remote access systems. Set to lock after 5 failed attempts for 15 minutes.
-
Review firewall logs: Search your firewall logs for brute-force attempts against the management interface. If you find evidence of attacks, assume the password was compromised and change it.
-
Check backup system access: Review who has accessed backup systems in the last 90 days. Look for unusual accounts or access patterns.
Near-Term Actions (This Month)
-
Implement MFA: Deploy multi-factor authentication on all administrative access. Start with critical systems, then expand to all systems.
-
Deploy behavioral analytics: Implement or upgrade your SIEM and behavioral analytics to detect lateral movement patterns.
-
Patch critical systems: Apply all security patches to internet-facing systems and critical infrastructure.
-
Credential management overhaul: If you don't have a secrets management system, implement one. Migrate credentials out of configuration files.
-
Network segmentation: Begin segmenting your network to reduce the blast radius of a compromise.
Strategic Actions (This Quarter)
-
Zero trust architecture: Develop and implement zero trust principles across your infrastructure.
-
Enhanced monitoring: Deploy network monitoring and behavioral analytics across your infrastructure.
-
Incident response plan: Develop and test incident response procedures for breach scenarios.
-
Threat modeling: Conduct threat modeling exercises to identify your highest-risk attack surfaces.
-
Security automation: Implement automated responses to common attack patterns and suspicious behaviors.

The Human Element: Why People Make These Mistakes
Why Do Organizations Expose Management Interfaces?
Exposing firewall management to the internet usually happens for one of a few reasons:
Convenience: Remote administration is easier than being on-site. Administrators want to be able to access the firewall from anywhere.
Lack of alternatives: Some organizations don't have a VPN infrastructure or jump host setup, so they expose the management interface as the simplest way to enable remote access.
Lack of awareness: Many smaller organizations don't realize this is a security risk. They think if the password is complex enough, it's safe.
Operational inertia: The firewall was set up years ago with exposed management, and nobody has reviewed it.
None of these reasons justify the risk. But understanding why organizations make these mistakes helps in fixing them. Solving the problem requires offering better alternatives, not just telling people to stop doing it.
If an organization can remotely administer their firewall through a VPN with MFA, they'll do it. If the only alternative is being on-site or exposing the management interface, many will choose exposure.
Why Do Credentials Stay Weak?
Similarly, weak credentials persist because:
Password complexity is hard: Creating and remembering truly strong passwords is annoying. Many people opt for patterns they can remember instead.
Configuration defaults aren't changed: During initial firewall setup, the installer often leaves default credentials in place, planning to change them later. Then it gets forgotten.
Credential management tools aren't universal: Not all systems support integration with credential management systems. Some administrators still can't use proper secrets management.
Organizational debt: Organizations that have accumulated technical debt often don't have the bandwidth to upgrade credential management practices.
Fixing these requires organizational investment. Better tools. Policies. Training. Automated enforcement.
Defense as a Strategic Competency
The organizations that survive in a landscape where AI-assisted attacks are common will be those that treat security as a core strategic competency.
This means:
- Budget allocation: Adequate funding for security tools, personnel, and training
- Executive commitment: Security decisions made at the leadership level, not as an afterthought
- Technical expertise: Investment in hiring and retaining security talent
- Continuous improvement: Regular updates to defensive systems and strategies
- Incident readiness: Testing and refining incident response procedures
Organizations that treat security as a compliance checkbox—"we passed our audit"—will be vulnerable. Those that treat it as a core competency will be resilient.

Looking Forward: The AI-Enabled Threat Future
What's Coming
Based on this campaign and industry trends, several developments are likely:
More sophisticated AI tools for attack: As AI capabilities improve, the tools generated will be more sophisticated, more evasive, and harder to detect.
Lower barriers to entry: As AI tools become easier to use, attackers with even less skill will be able to launch campaigns. The bar for entry continues to drop.
Higher-volume attacks: Attackers can launch more attacks, faster. We'll see campaign volume increase dramatically.
More specialized attacks: Rather than generic malware, we'll see AI generating highly targeted attack code optimized for specific target architectures and configurations.
Offensive AI arms race: Better offensive AI will drive development of better defensive AI. Organizations without AI-driven security will fall behind rapidly.
Preparing for the Future
How should organizations prepare for this landscape?
Build resilience: Design systems that can continue functioning even when parts are compromised. Assume breach will happen and focus on limiting damage.
Invest in detection: It's increasingly hard to prevent all breaches. Focus on detecting them quickly and responding.
Develop internal capabilities: Don't outsource all security. Build internal expertise to understand and respond to threats.
Adopt security standards: Follow established frameworks like NIST Cybersecurity Framework, CIS Critical Security Controls, and others.
Engage with the community: Share threat intelligence. Participate in information sharing. Learn from others' mistakes.
Prepare for scale: Design systems assuming you might face sophisticated attackers. Build redundancy and failover.
The Role of Automation
Automation will increasingly define security effectiveness.
Organizations that automate:
- Threat detection
- Incident response
- Patch management
- Credential rotation
- Threat intelligence integration
...will be able to defend against attacks that require rapid response.
Those that rely on manual processes will struggle to keep pace with AI-assisted attackers.
What This Means for Different Stakeholder Groups
For Security Professionals
This attack represents both a challenge and an opportunity.
The challenge: Threats are evolving faster than your organization might be able to respond. Attackers with AI can now execute campaigns that previously required teams.
The opportunity: Organizations will increasingly invest in security. Teams that can demonstrate capability in detecting and stopping AI-assisted attacks will be in high demand.
The action: Develop expertise in behavioral analytics, threat hunting, and incident response. These skills will be critical.
For Enterprise Leaders
If you're a CIO, CISO, or executive responsible for infrastructure:
This attack demonstrates that security isn't a checkbox. It's a strategic imperative. Organizations that don't invest in proper security controls will face breach costs that dwarf the cost of prevention.
The action: Ensure your security team has proper budget, talent, and authority to implement controls. Security decisions should be made with executive input, not delegated entirely to the technical team.
For Developers and Dev Ops
Secure infrastructure design is increasingly important.
When you build applications and infrastructure, assume they might be compromised. Design with defense in depth in mind. Implement logging and monitoring. Make things defensible.
The action: Adopt secure development practices. Understand the attack surface you're creating. Work with security teams during design, not after deployment.
For Smaller Organizations
If you run a smaller organization with limited security resources, you're vulnerable to these attacks. But you're not helpless.
Focus on fundamentals:
- Change default credentials
- Don't expose management interfaces
- Use strong passwords and MFA
- Keep systems patched
- Monitor for unusual activity
- Back up your data
- Have an incident response plan
Small organizations often can't match the security spending of enterprises, but they can focus on fundamentals that prevent most attacks.
FAQ
What is the FortiGate firewall brute-force attack from 2025?
A campaign where a Russian hacker systematically scanned for exposed FortiGate firewall management interfaces and used brute-force attacks to gain access with weak credentials. The attacker then used AI-generated scripts to extract credentials from firewall configurations, gain access to internal networks, and target backup systems. The campaign lasted 39 days, from January 11 to February 18, 2025, affecting hundreds of organizations.
How did AI enable this attack if the attacker wasn't highly skilled?
AI enabled the attack by automating tasks that normally require significant coding expertise. The attacker used AI to generate Python and Go scripts for credential parsing, decryption, network reconnaissance, and lateral movement. This allowed someone with basic technical knowledge to execute a sophisticated multi-stage attack across hundreds of targets in a matter of weeks—something that would take a skilled team months to accomplish manually.
What were the main stages of this attack campaign?
The attack progressed through four main stages: reconnaissance and brute-force access to firewall management interfaces, credential extraction and parsing from firewall configuration files using AI-generated scripts, network reconnaissance and lateral movement to internal systems using AI-generated tools, and finally targeting of Veeam Backup servers for credential extraction and exploitation of known vulnerabilities. The attacker abandoned well-hardened systems and focused on easier targets.
Why did the attacker specifically target Veeam Backup servers?
Backup systems are high-value targets because they contain complete copies of an organization's data and systems. Compromising a backup server allows attackers to exfiltrate sensitive data, encrypt backups to create leverage for ransom demands, or introduce malware that persists after system recovery. The attacker attempted to deploy credential extraction tools and exploit known Veeam vulnerabilities to gain control of the backup infrastructure.
What defensive controls would have stopped this attack at each stage?
Multiple controls could have stopped this attack: not exposing management interfaces to the internet (prevents initial access), implementing multi-factor authentication (prevents brute-force success), using proper secrets management instead of storing credentials in configuration files (prevents credential extraction), implementing network segmentation and behavioral analytics (prevents lateral movement), keeping systems patched (prevents known vulnerability exploitation), and monitoring for unusual access patterns to backup systems (enables detection and rapid response).
Why is this attack significant beyond the specific victims?
This attack demonstrates that AI is democratizing access to sophisticated attack capabilities. Previously, campaigns of this scale and sophistication required either highly skilled attackers or well-funded threat groups. Now, any attacker with motivation, basic technical knowledge, and access to AI tools can execute complex attacks at scale. This fundamentally shifts the threat landscape and requires organizations to reevaluate their defensive posture.
What should my organization do immediately to prevent similar attacks?
Implement these controls immediately: audit for exposed management interfaces and restrict or isolate them, rotate administrative credentials and implement unique credentials for each administrator, enable account lockout policies to prevent brute-force attacks, deploy multi-factor authentication on all critical system access, enable brute-force protection on remote access systems, review logs for evidence of previous attacks, and ensure firewall configuration files don't store credentials or encrypt them with strong keys. Start with these fundamentals before moving to more complex architectural changes.
How can organizations detect attacks like this if they occur?
Detection requires multiple layers: brute-force detection systems that flag repeated authentication failures, behavioral analytics that identify unusual credential usage patterns or access from unexpected locations, network monitoring that detects lateral movement between systems that normally don't communicate, log analysis of management interface access and backup system access, and employee reports of unusual system behavior. Implementing SIEM (Security Information and Event Management) systems that centralize and analyze logs from across your infrastructure is critical for detecting multi-stage attacks.
Is multi-factor authentication enough to prevent these attacks?
MFA is a critical control that would have stopped this specific attack because the attacker would have had the username and password but not the second factor. However, MFA is one layer of defense. A complete defensive strategy also requires strong credential practices, network segmentation, behavioral monitoring, and incident response capabilities. MFA blocks this specific attack path, but other attack paths might exist depending on your infrastructure configuration.
What's the difference between this AI-assisted attack and traditional hacking campaigns?
Traditional hacking campaigns required attackers to personally write or customize their tools, understand the target systems deeply, and manually execute each step of the attack. This attack leveraged AI to generate code, automate tool deployment, handle unexpected situations, and scale across hundreds of targets. The attacker didn't need to understand cryptography to decrypt credentials—they asked AI to write the decryption code. This dramatic reduction in required expertise and time is what makes AI-assisted attacks fundamentally different and more dangerous.
The Bottom Line
The Russian hacker campaign of early 2025 represents an inflection point in cybersecurity. It proves that low-skilled attackers with access to AI can now execute sophisticated, multi-stage attacks against hundreds of targets.
This changes the threat model. Organizations can no longer assume that only the most sophisticated attackers pose significant risk. Any attacker with motivation, basic technical knowledge, and access to AI tools now represents a serious threat.
The good news is that the defenses against these attacks are well-understood. Weak credentials, exposed management interfaces, lack of network segmentation, and unpatched systems are all preventable problems. Organizations that implement proper controls can significantly raise the attacker's cost and effort.
The bad news is that many organizations still haven't implemented these fundamental controls. They're exposed to exactly the kind of attack this campaign exemplifies.
If your organization is still managing this risk through "security through obscurity" or hoping attackers won't find you, you're overdue for a security reckoning. The attacker in this campaign didn't need to be special. They just needed basic tools and motivation.
The question isn't whether you'll face attacks like this. It's whether you'll be ready when you do.
Start with the fundamentals: don't expose what shouldn't be exposed, use strong credentials with MFA, segment your network, patch your systems, and monitor for anomalies. These controls aren't flashy, but they work.
In a landscape where AI is commoditizing attack capabilities, the organizations that survive and thrive will be those that treat security as a core strategic competency. Not a compliance checkbox. Not an afterthought. A fundamental part of how you build, operate, and defend your infrastructure.
The attacks are coming. Your job is to make sure you're ready.

Key Takeaways
- A low-skilled Russian hacker used AI-generated scripts to break into hundreds of FortiGate firewalls in just 39 days by automating credential brute-forcing and lateral movement
- AI enabled the attack by automating code generation for credential parsing, decryption, reconnaissance, and exploitation—tasks that normally require significant expertise
- The attacker's code was poorly designed with redundant comments and naive architecture, yet still successfully compromised multiple organizations at scale
- Weak credentials and exposed management interfaces were the critical failure points; multi-factor authentication alone would have stopped this entire attack
- Organizations must immediately audit exposed interfaces, rotate administrative credentials, deploy MFA, and implement behavioral analytics to detect similar campaigns
- This attack demonstrates that AI is democratizing access to sophisticated attack capabilities, requiring a fundamental shift in how organizations approach defensive security strategy
Related Articles
- Ransomware Targeting Firewalls: The Critical 2025 Security Crisis [2025]
- Honeywell CCTV Camera Vulnerability: Complete Security Guide [2025]
- Why AI-Generated Passwords Are Dangerously Weak [2025]
- AI Content Moderation and Legal Liability in Crisis Prevention [2025]
- Password Manager Security Flaws Exposed: What You Need to Know [2025]
- Google Play's AI Defenses Block 1.75M Bad Apps in 2025 [Analysis]
![AI-Powered Hacking: How Low-Skill Attackers Break Firewalls [2025]](https://tryrunable.com/blog/ai-powered-hacking-how-low-skill-attackers-break-firewalls-2/image-1-1771861037419.jpg)



