Shiny Hunters Hits Wynn Resorts: Inside the $1.5 Million Ransomware Demand
Wynn Resorts just joined an exclusive club nobody wants to be in. The Las Vegas hospitality giant became the latest victim of Shiny Hunters, a ransomware group that's apparently treating major hospitality targets like a shopping list. And this time, the hackers want $1.55 million to delete what they're claiming is 800,000 employee records.
Here's what makes this breach particularly alarming: it's not some isolated incident from an unknown cybercriminal operation. Shiny Hunters already demonstrated its capabilities by hitting both Caesars Entertainment and MGM Resorts just a few months earlier. Wynn's breach represents the third major domino to fall in Las Vegas's gaming and hospitality sector, and it reveals something crucial about modern ransomware tactics that every executive, security professional, and frankly, every employee should understand.
The attackers claim they gained access via an Oracle People Soft vulnerability, leveraging stolen employee credentials to infiltrate Wynn's network in September 2025. They're demanding 23.34 Bitcoin as a "starting price," which is code for "we're willing to negotiate." The deadline? February 23, 2026. That's pressure tactics meeting dark web economics in real time.
But here's what really matters beyond the headline numbers: this breach exposes the fragile security posture even massive corporations maintain. Wynn Resorts operates some of the world's most sophisticated hospitality operations, yet somehow their enterprise systems remained vulnerable to a group that's been making waves for years. The sample data shared publicly includes employee names, emails, phone numbers, positions, salaries, start dates, and birth dates. That's not just personally identifiable information, that's a complete identity theft package delivered via ransomware gang.
The hospitality and gaming industry has become a hunting ground for ransomware operations because these businesses operate with razor-thin margins, massive customer databases, and the pressure to keep operations running 24/7. When your casino floor generates millions daily, paying a ransom sometimes seems cheaper than dealing with encrypted systems and operational downtime. That calculus is exactly what groups like Shiny Hunters are banking on.
What happened at Wynn is a masterclass in how modern ransomware attacks combine multiple failure points: unpatched legacy systems, credential mismanagement, insufficient segmentation, and perhaps most critically, inadequate detection and response capabilities. Let's dig into how this happened, why it matters, and what every organization should actually be doing differently.
The Shiny Hunters Threat Group: What You're Actually Dealing With
Shiny Hunters isn't some basement operation run by script kiddies. This is a sophisticated ransomware group that emerged on the dark web with a clear operational model: identify high-value targets in hospitality, gaming, and financial services, compromise their networks, exfiltrate sensitive data, and then leverage the threat of public disclosure to extract payment.
The group made international headlines when it targeted Caesars Entertainment in September 2023, eventually securing a settlement that cybersecurity researchers estimated at around $30 million when you factor in recovery, legal, and incident response costs. MGM Resorts fell just weeks later to the same group. These weren't fumbling attacks. These were precision operations that demonstrated deep understanding of enterprise networks, incident response playbooks, and the psychology of ransom negotiations.
What distinguishes Shiny Hunters from other ransomware operations is their focus on data exfiltration as the primary leverage mechanism rather than simple encryption. They don't just lock files and demand payment. They steal databases first, prove they have it by publishing samples, then threaten to dump everything on the dark web or sell it to competitors and criminal syndicates. This "double extortion" model has become the standard playbook because it works. Organizations that maintain good backups can recover from encryption, but they can't un-leak sensitive employee and customer data.
The group operates with a level of professionalism that suggests experienced developers, network administrators, and security specialists are likely involved either directly or as consultants. Their infrastructure includes professional-looking leak sites on the dark web, structured communication with victims, and what appears to be legitimate negotiation processes. Several security researchers have noted that Shiny Hunters victims have reported receiving detailed settlement negotiations, sometimes spanning weeks of back-and-forth communications with specific payment terms and data deletion verification processes.
The financial motivation is straightforward. A demand of
What's particularly concerning about Shiny Hunters' operations is their apparent understanding of corporate decision-making processes. They give companies deadlines that feel real, publish samples that verify legitimacy, and maintain communication channels that make negotiation possible. Unlike some ransomware groups that simply demand payment or trash data, Shiny Hunters operates almost like a criminal consulting firm. This sophistication suggests they've studied previous breaches, learned what works, and refined their approach.
The group's targeting of three major Las Vegas properties within months suggests they may have identified a vulnerability or vulnerability class that affects multiple hospitality providers. Whether it's specific to Oracle People Soft deployments, a broader HRMS vulnerability, or targeting of specific contractors who service multiple properties, the pattern indicates strategic intelligence gathering behind the scenes.
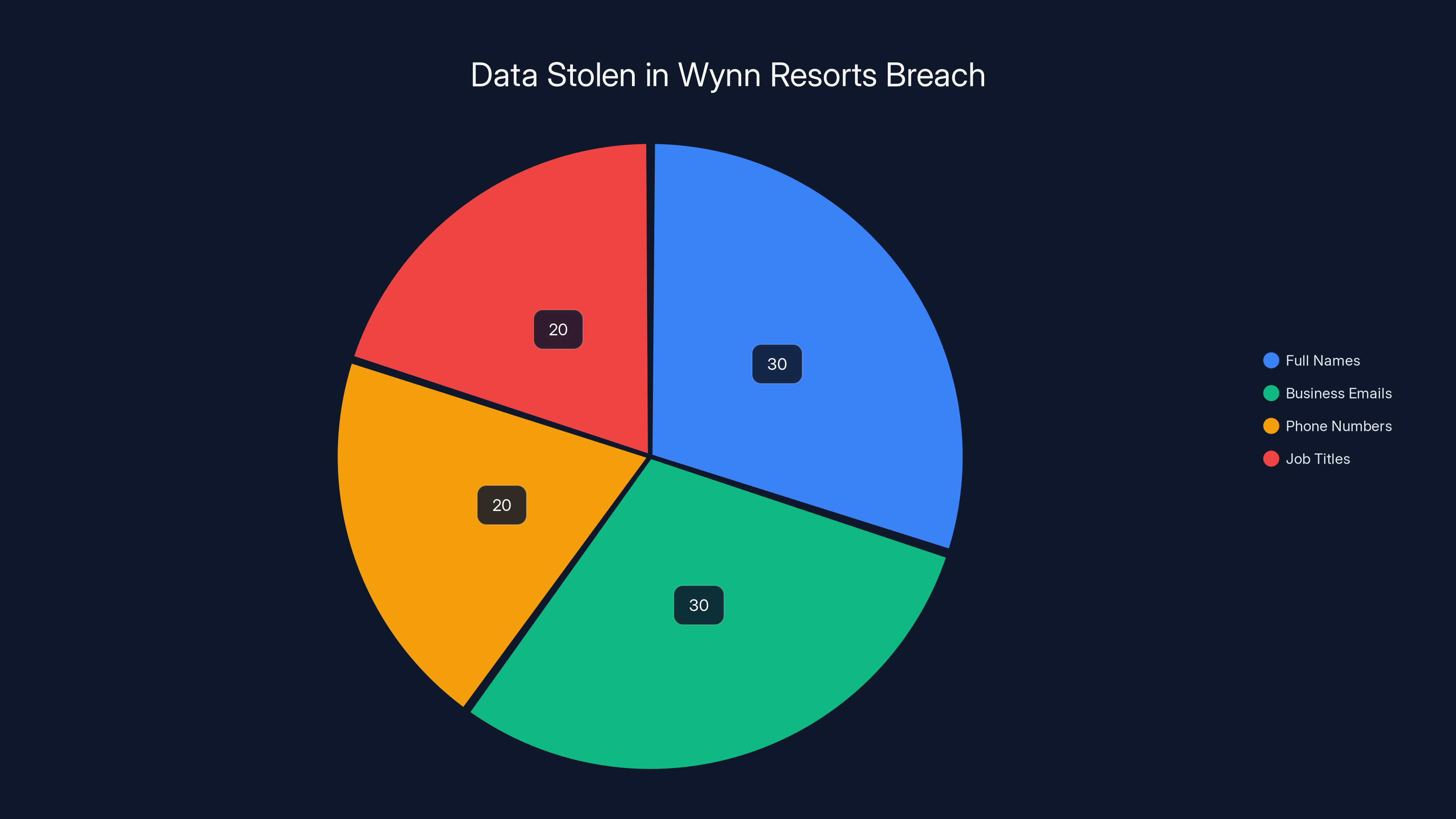
The breach exposed approximately 800,000 employee records, with full names and business emails being the most common data types stolen. Estimated data distribution.
How Shiny Hunters Breached Wynn Resorts: The Technical Attack Chain
According to information provided to security researchers at The Register, Shiny Hunters accessed Wynn's systems in September 2025 through an Oracle People Soft vulnerability, using an employee's credentials. Let's break down what this actually means and why each link in this chain matters.
Oracle People Soft is an enterprise human resources and financial management system deployed at thousands of organizations worldwide. It's deeply embedded in enterprise operations, meaning it's not something you can quickly patch or shut down without operational consequences. When vulnerabilities are discovered in systems like this, they affect an entire class of targets simultaneously, and the window between disclosure and widespread exploitation is compressed.
The specific vulnerability used isn't publicly named in reports, but the pattern is consistent with how modern ransomware attacks unfold. Here's the chain: a vulnerability exists in the software, the attacker identifies it or acquires information about it through underground forums or direct discovery, and then they begin scanning the internet for exposed instances. Organizations running unpatched versions become targets.
But here's where it gets interesting: access via a software vulnerability often requires the attacker to establish persistence and elevate privileges before they can do meaningful damage. Simply exploiting a People Soft vulnerability and getting shell access to a web server isn't enough to access sensitive HR data or exfiltrate 800,000 employee records. You need to navigate the network, identify where sensitive data lives, move laterally to systems you don't have direct access to, and establish command and control infrastructure that remains undetected long enough to steal massive amounts of data.
The mention of "using an employee's credentials" suggests that either the initial vulnerability exploitation led to credential harvesting, or that Shiny Hunters obtained credentials through other means (phishing, credential stuffing, dark web purchases, etc.) and used the People Soft vulnerability to establish the initial foothold. Once inside, they likely moved laterally through the network, potentially compromising domain credentials, establishing persistence through backdoors, and conducting reconnaissance to map data stores.
This attack pattern reveals critical gaps in Wynn's security posture:
- Unpatched systems: People Soft deployments remain vulnerable to known exploits
- Insufficient network segmentation: Once an attacker gets in, they can move freely to critical systems
- Credential reuse: Employee credentials being valid across multiple systems
- Inadequate detection: The attackers were presumably in the network for months without detection
- Missing endpoint protection: No prevention of credential theft or lateral movement
The data exfiltration itself is another technical hurdle. Moving 800,000 employee records off a network without detection requires either incredibly patient attackers (weeks or months of slow data transfer), or attackers who successfully disabled or bypassed detection systems. Given Shiny Hunters' operational history, they likely employed both strategies: establishing persistence through legitimate administrative tools, then exfiltrating data through encrypted channels that blend in with normal network traffic.
One detail that stands out: Wynn didn't detect the breach until after Shiny Hunters already announced it on their leak site. This suggests their detection capabilities failed to identify either the compromise or the exfiltration. This isn't uncommon with sophisticated attacks, but it indicates that endpoint detection and response (EDR) systems, network intrusion detection, and data loss prevention (DLP) systems either weren't properly configured or were already compromised.

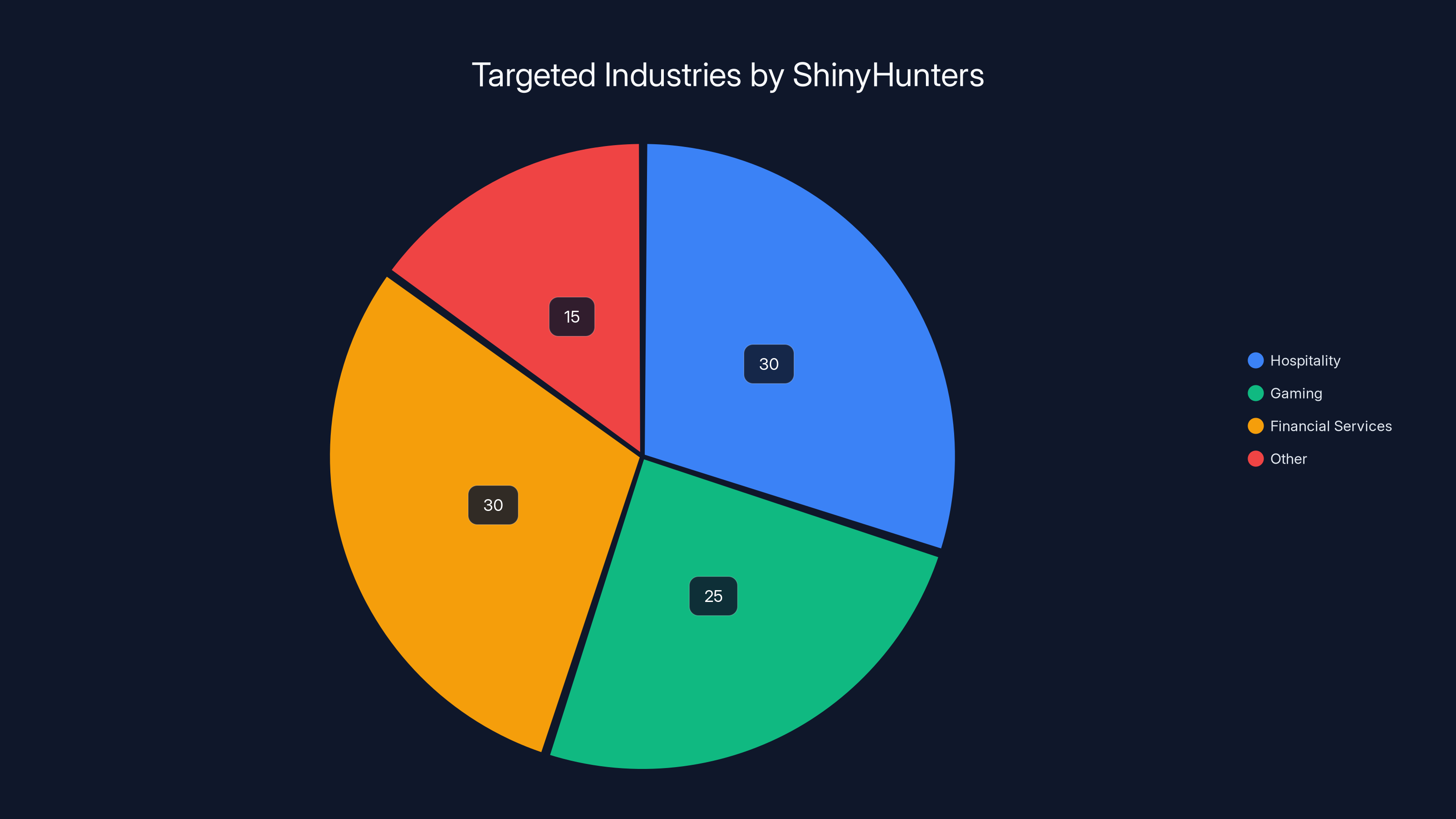
ShinyHunters primarily targets hospitality, gaming, and financial services, with each sector representing a significant portion of their attacks. Estimated data.
The Data Exposed: What Employees and the Organization Face
The breach sample analyzed by security researchers included some of the most sensitive employee data: full names, business email addresses, phone numbers, job titles, departments, salary information, start dates, and birth dates. For an 800,000-record breach, that data volume could include decades of historical employment records, potentially including terminated employees whose data was never purged.
This specific combination of data elements is particularly dangerous because it provides everything needed for sophisticated social engineering, identity theft, and targeted phishing campaigns. A criminal now knows:
- Who the target is (name)
- How to reach them (email, phone)
- What they do (job title and department)
- How valuable they likely are (salary level)
- When they were hired (tenure affects seniority and access levels)
- Their age/generation (affects phishing message targeting)
Salary information is especially problematic. In competitive industries like hospitality, salary data reveals compensation structures, identifies high-value employees, and can be used for targeted recruitment of critical staff by competitors. It also enables calculation of someone's actual net worth, which informs ransom negotiations for targeted extortion.
The birth dates are another critical exposure. When combined with other public information (Linked In profiles, corporate bios, social media), birth dates enable full social engineering attacks and identity theft. You need five specific data points to commit identity fraud, and this breach includes several of them.
For Wynn specifically, the exposure creates multiple problems:
- Regulatory obligations: GDPR, CCPA, and other privacy laws require notification and often trigger investigations
- Litigation risk: Class action lawsuits from affected employees are nearly guaranteed
- Credit monitoring costs: The company will likely need to offer credit monitoring to all affected employees
- Reputation damage: Trust with employees erodes immediately
- Operational security impact: Knowing their organization was breached affects employee behavior and productivity
The fact that the attackers claim they still possess the data and threaten public release means this isn't over even if the ransom is paid. There's no guarantee that paying the group results in actual deletion of stolen data. Plenty of cybersecurity experts recommend against paying ransoms precisely because it reinforces the business model and provides no assurance of data destruction.

Why Hospitality Is a Ransomware Bullseye
Wynn is the third major Las Vegas hospitality target to fall to Shiny Hunters in recent months. This isn't coincidence. The hospitality and gaming industry has become one of the most targeted sectors for ransomware operations, and the reasons are both economic and operational.
First, the economics. Las Vegas casinos and major resorts operate on astronomical turnovers. A property that generates
Second, the operational model. Hospitality properties must maintain 24/7 operations. You can't shut down casino floors for a security update. You can't take your reservation system offline for patching without customer impact. This creates a perverse incentive: organizations delay security updates because the operational risk of patching exceeds the perceived threat risk. This is called "security debt," and the hospitality industry is drowning in it.
Third, the data. Hotels maintain guest data, employee records, payment card information, and behavioral profiles. A guest who spent $50,000 on a weekend trip is identifiable and potentially vulnerable to targeted extortion. Employee records provide personal information that enables social engineering and financial crimes. Payment data attracts financial criminals specifically. The combination is irresistible.
Fourth, the staffing model. Hospitality operates with high workforce turnover, significant seasonal variation, and distributed responsibilities across multiple properties and contractors. This creates numerous weak links in the security chain. A contractor with access to corporate systems might be a single phishing attack away from compromise. An employee accessing systems remotely without a VPN becomes a network entry point. The scale of personnel involved creates exponential complexity.
Fifth, the security maturity. Many hospitality organizations are operationally mature (running complex properties is genuinely difficult) but security-immature. Legacy systems remain in place because they work, not because they're secure. Security budgets are often inadequate relative to operational budgets. Executive leadership sometimes views security as a cost center rather than a risk mitigation function.
Final factor: insurance. Many hospitality properties maintain cyber insurance that covers ransomware payments. This creates a perverse incentive where paying the ransom is sometimes the economically optimal decision from an insurance perspective. The insurance company might approve payment faster than the organization could recover from backups.
All of these factors combine to create an environment where ransomware operations like Shiny Hunters thrive. They've identified a sector with strong financial motivation to pay, weak detection capabilities, vulnerable legacy systems, and operational pressures that discourage aggressive security postures.


Estimated data shows potential costs of different negotiation outcomes. Initial demand is
The Oracle People Soft Vulnerability: What's Actually Vulnerable
Oracle People Soft is an enterprise system used for human resources, payroll, benefits administration, and financial management. It's deployed at thousands of organizations globally, from Fortune 500 companies to mid-market enterprises. A single vulnerability affecting People Soft potentially impacts an enormous attack surface.
Oracle releases regular security patches, but the gap between patch release and deployment at organizations is often measured in months or even years. Organizations running older versions of People Soft (7.x, 8.x, 9.x variants) are particularly vulnerable because Oracle has ended support for these versions, yet they remain in production at many sites.
The specific vulnerability used against Wynn wasn't publicly disclosed in initial reports, but the pattern matches historical People Soft vulnerabilities that involve remote code execution or authentication bypass. When Shiny Hunters can execute arbitrary code on a People Soft instance through a known vulnerability, they gain initial access to the network. From there, privilege escalation, lateral movement, and persistence become possible.
What's particularly dangerous about People Soft vulnerabilities is that the system has direct access to sensitive data. Unlike a compromise of a web-facing application that requires additional lateral movement, compromising People Soft immediately provides access to employee records, payroll information, tax documents, and in many cases, access to other systems that trust People Soft for authentication.
The fact that Shiny Hunters could establish persistence for months and exfiltrate 800,000 records suggests that either patching was severely delayed, or the vulnerability was zero-day or otherwise unknown to Oracle at the time of exploitation. The group's operational history suggests they're capable of identifying and exploiting zero-day vulnerabilities or acquiring information about them before public disclosure.
For organizations running People Soft, the response should be immediate:
- Identify your People Soft version and verify it's receiving security updates
- Apply all available patches immediately (treat this as critical priority)
- Isolate People Soft systems from general network access and implement strong access controls
- Monitor for indicators of compromise including unusual data access, unexpected user accounts, and abnormal query patterns
- Review access logs for the past 90 days to identify potential breach window
- Implement network segmentation so that even if People Soft is compromised, attackers can't immediately access other critical systems

Credential Compromise: The Bridge from Initial Access to Full Network Control
The attack narrative includes "using an employee's credentials," which is a critical detail often overlooked in breach summaries. How did Shiny Hunters obtain legitimate employee credentials? The possibilities include:
- Phishing attack: A targeted phishing campaign convincing an employee to enter their credentials on a fake login page
- Credential stuffing: Using leaked credentials from other breaches to attempt access
- Password spraying: Attempting common passwords against known usernames
- Social engineering: Calling an employee and convincing them to provide credentials or reset them
- Malware: Previous malware infection harvesting credentials
- Insider threat: A current or former employee providing credentials
- Dark web purchases: Credentials acquired from criminal forums or data brokers
Each possibility indicates different failure points in security controls. If it was phishing, then email security and user training failed. If it was credential stuffing, then password security practices failed. If it was social engineering, then access controls and verification procedures failed.
The use of legitimate credentials is actually worse than exploiting vulnerabilities alone. With credentials, attackers can blend in with normal network activity. Their actions appear as legitimate user behavior. Security tools that flag suspicious behavior might not trigger because the user account is real and authorized. This makes detection significantly harder.
Once inside with legitimate credentials, the attacker's next steps involve privilege escalation. A regular employee account might have access to their own HR records but not organizational payroll data or system administration functions. To access 800,000 records, the attacker needed either elevated credentials or the ability to move laterally to systems with broader data access.
This likely involved either compromising a system administrator account, exploiting service accounts with excessive permissions, or identifying systems where access controls were inadequate. Many organizations maintain overly permissive access controls where a business justification existed at some point but the access was never revoked. An employee who moved departments years ago might retain access to their old department's sensitive systems.
The credential compromise also reveals something about Wynn's detection capabilities. If someone is accessing HR systems and downloading employee records at unusual times, unusual locations, or in unusual volumes, that activity should trigger alerts. The fact that the attackers successfully exfiltrated 800,000 records without detection suggests that either:
- Detection systems weren't configured for this activity
- Alert thresholds were set too high
- Alerts were generated but not reviewed
- The attacker used legitimate business processes to access the data (requesting periodic exports, using standard reporting tools)
The third-party perspective reveals this as a detection failure, not just an access control failure. Detecting credential compromise requires understanding baseline user behavior. An employee who normally accesses systems during business hours from the office but suddenly accesses systems at 3 AM from an IP address in another country is suspicious. These behavioral analytics are standard in modern EDR systems but aren't deployed everywhere.

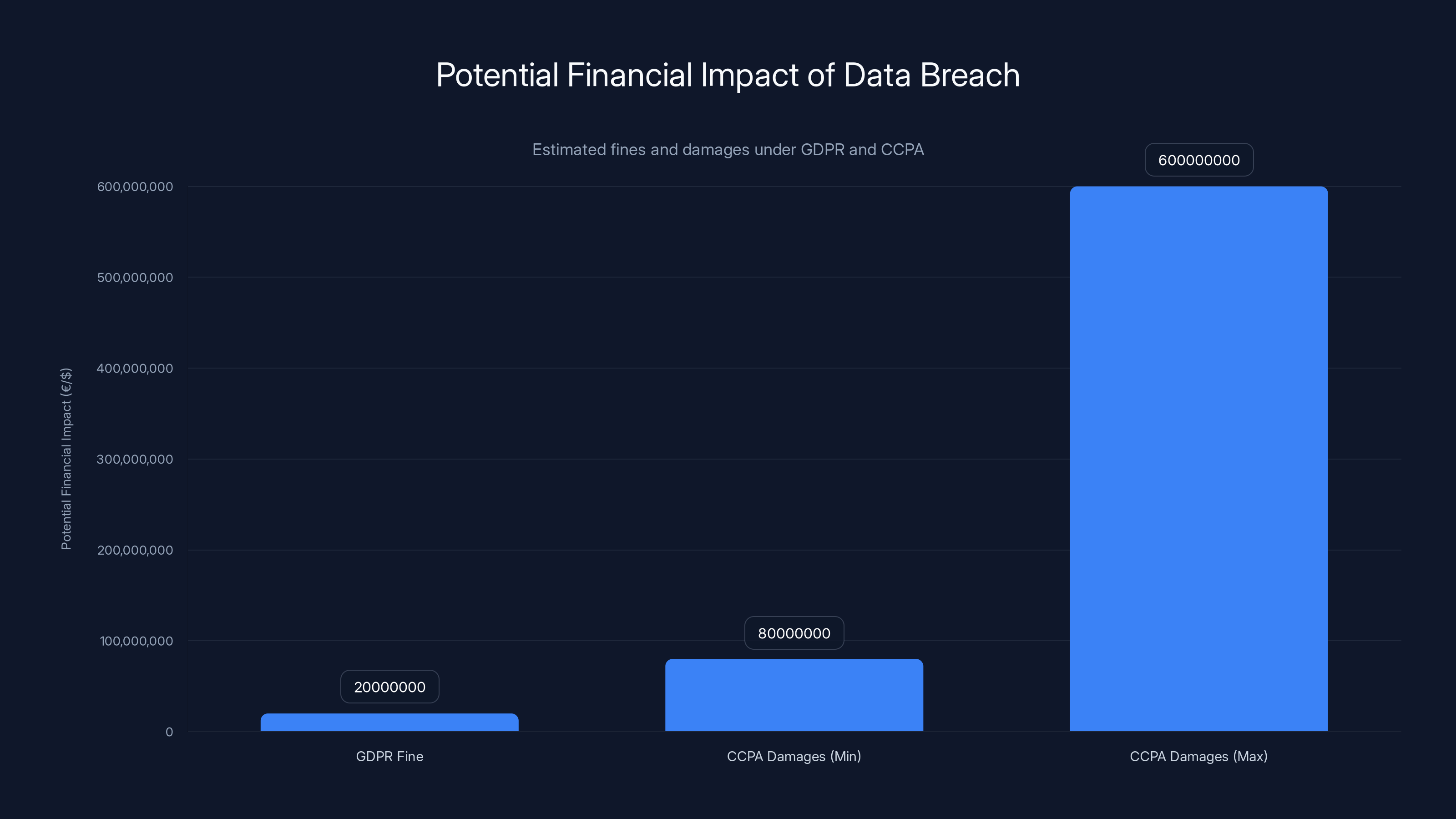
Estimated financial impact of Wynn Resorts' data breach could reach up to €20 million under GDPR and between
The Ransom Demand: Economics and Negotiation Tactics
Shiny Hunters is demanding 23.34 Bitcoin, equivalent to approximately $1.55 million at current exchange rates. The amount is strategic, not random. It's high enough to represent real money that gets someone's attention, but low enough that it's negotiable and potentially justifiable as a business decision.
The "starting price" language is important. This isn't the final ask. It's the opening position in a negotiation. Shiny Hunters likely expects to negotiate down to 30-60% of the opening demand. If they get
The Bitcoin denomination is also strategic. Bitcoin provides pseudonymity (not true anonymity, but harder to trace), enables cross-border payment without traditional financial controls, and moves the negotiation to a technical domain where Wynn might be less comfortable. The cryptocurrency also protects against payment reversal or chargeback, which could happen if payment was made through traditional financial channels.
The February 23, 2026 deadline creates pressure. It's distant enough that it seems real (companies might actually meet that deadline), but near enough that executives feel urgency. Missing a deadline triggers data release, which would be worse than paying. This timeline psychology is well-established in negotiation and extortion research.
From Wynn's perspective, the decision tree looks roughly like this:
Option A: Pay the ransom
- Immediate cost: ~$1.55 million (or negotiated amount)
- Long-term risk: No guarantee of data deletion, might encourage future attacks
- Regulatory risk: Paying ransoms to sanctioned entities could violate OFAC rules if the group has connections
- Insurance impact: Insurance might cover, reducing direct cost
- Operational impact: Low—core operations continue
Option B: Refuse and deal with data release
- Immediate cost: $0 for ransom
- Long-term risk: 800,000 employee records publicly available
- Regulatory risk: Data breach notifications, potential GDPR fines, regulatory investigations
- Legal risk: Class action lawsuits from employees
- Operational impact: Reputational damage, potential loss of employee trust
Option C: Recover from backups
- Immediate cost: Incident response, recovery operations
- Long-term risk: Data already exfiltrated, ransom demand remains
- Timeline: Recovery might take weeks, during which operations are degraded
- Detection risk: Recovery might reveal the breach to the broader organization
- Long-term: Still must deal with external disclosure threat
The economic calculus favors paying in many corporate decision-making frameworks, which is exactly why ransomware remains so profitable. The numbers work out better than customers expect.
Another factor: insurance. Many large organizations carry cyber insurance that covers ransomware costs. If Wynn's insurance covers the incident, the
Shiny Hunters has also positioned itself as a professional operation willing to negotiate. They're not demanding payment via untraceable methods that suggest they're unsophisticated. They're using standard cryptocurrency, providing deadlines, and maintaining communication channels. This professionalism makes negotiation seem feasible, which makes organizations more likely to engage.
Data Breach Notification and Legal Consequences
Wynn Resorts will face a complex landscape of notification requirements, regulatory consequences, and legal liability following this breach. The specifics depend on several factors: where affected employees live, where the company operates, and how aggressively regulators decide to pursue the matter.
Under GDPR (if any EU employees are affected), Wynn must notify the relevant supervisory authorities within 72 hours of learning about the breach and notify affected individuals without undue delay. GDPR violations carry fines up to 4% of global revenue or €20 million, whichever is higher. For a company with billions in annual revenue, that's potentially substantial.
In the United States, the breach triggers notification requirements under state breach notification laws, which vary by state but generally require notification of affected residents without unreasonable delay. Nevada (Wynn's home state) requires notification without unreasonable delay, and companies must preserve evidence. The company must also determine whether the breach involved unencrypted personal information (which it did—full names, emails, phone numbers, etc.).
California's CCPA provides private right of action for data breaches involving specific categories of personal information, including Social Security numbers or financial account information. If California residents are among the 800,000 affected, they can potentially sue individually for damages. The CCPA also provides for statutory damages of
Beyond regulatory consequences, Wynn will face civil litigation. Class action lawsuits from affected employees are nearly inevitable. These cases typically claim breach of contract, negligence, failure to implement adequate security, and unjust enrichment. They might also allege that Wynn failed to maintain reasonable security measures despite its obligations as an employer holding sensitive personal data.
The litigation costs alone can exceed the ransom demand. A major breach class action can cost millions in legal defense, settlement negotiations, and if the company loses, damages and attorneys' fees. Even if Wynn wins on the merits, the legal costs are substantial.
Wynn will also face notification costs. The company will need to offer credit monitoring services to all affected employees, likely for multiple years (industry standard is 2-3 years). Credit monitoring subscriptions cost $10-30 per person annually. For 800,000 people over three years, that's easily tens of millions of dollars.
Insurance will potentially cover some of these costs, but not all. Most cyber liability insurance policies include coverage for notification costs, credit monitoring, regulatory fines, and legal defense. However, policies have limits, deductibles, and exclusions. An 800,000-record breach affecting multiple jurisdictions could easily exceed standard policy limits.
The regulatory investigation side is another concern. State attorneys general and federal agencies (FBI, Secret Service, CISA) often investigate significant data breaches. They can subpoena records, demand forensic reports, and require the company to demonstrate compliance with security standards. These investigations are time-consuming and can reveal additional vulnerabilities or failures.
For Wynn employees specifically, the breach exposure is personal and immediate. Their salary information is potentially public, which could affect personal financial planning, identity theft risk, and even future employment opportunities if they compete for jobs where salary history is used in negotiation.

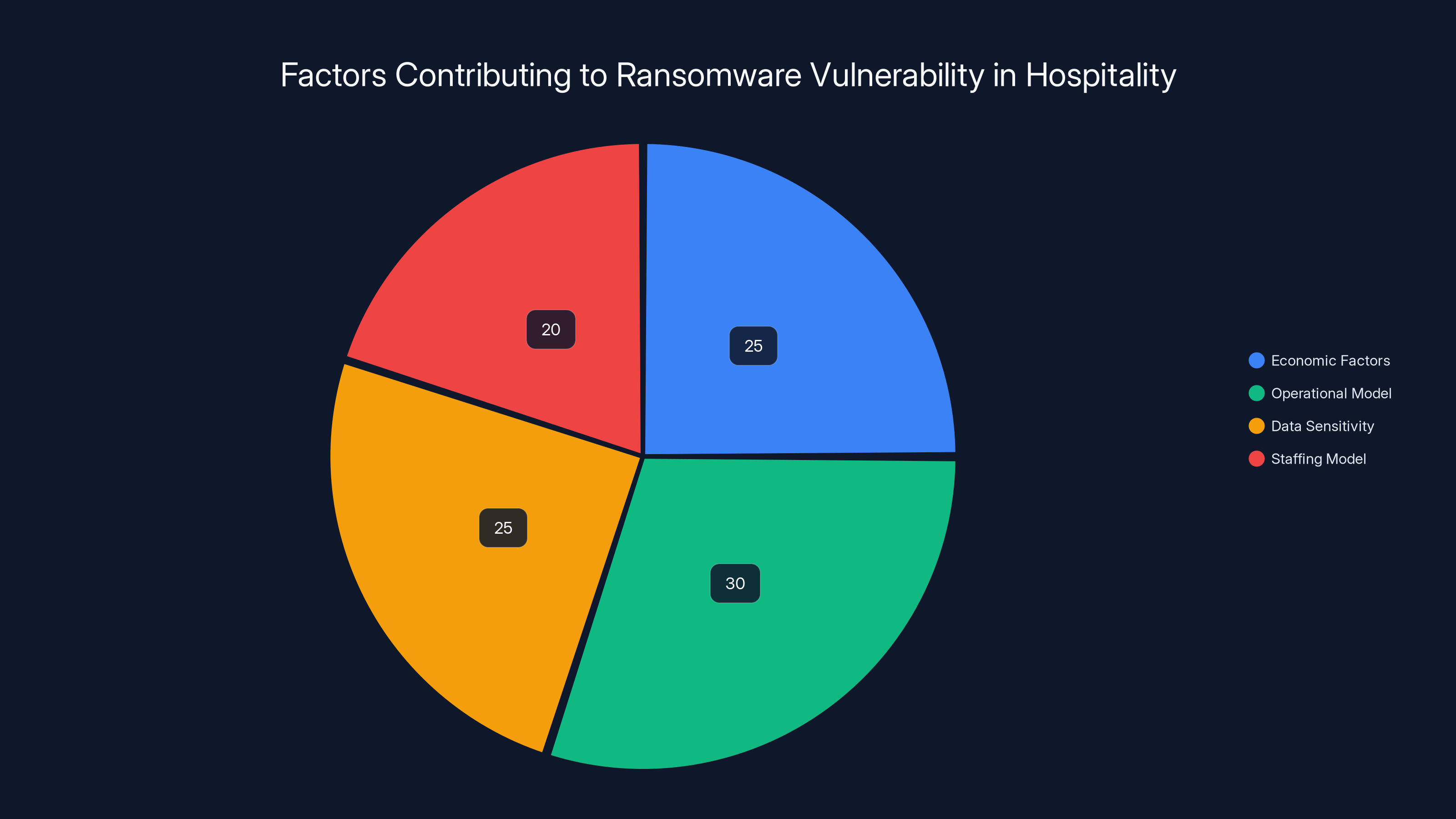
Operational challenges and data sensitivity are major factors making hospitality a prime ransomware target. Estimated data.
Organizational Response and Recovery: What Wynn Faces Now
In the immediate aftermath of the breach disclosure, Wynn must execute a complex organizational response that balances multiple competing priorities: stopping ongoing attacks, recovering systems, preserving evidence for investigation, communicating with stakeholders, managing legal and regulatory obligations, and protecting reputation.
The first 72 hours are critical. Wynn needs to:
- Identify the scope: Determine exactly what systems were accessed, when access began, and what data was exfiltrated
- Isolate compromised systems: Disconnect systems from the network to prevent further lateral movement
- Engage incident response: Bring in external forensic experts (this is not something to do alone)
- Preserve evidence: Collect logs, system images, memory dumps, and network traffic for investigation and litigation
- Notify leadership and board: Get decision-makers in the loop immediately
- Activate insurance: Notify cyber liability insurance carriers
- Contact legal counsel: Brief external counsel on the situation
The 72-hour period extends to the first week, during which Wynn must determine the full scope of the breach, identify the attack vector (already partially known), and develop a recovery plan. This week typically includes:
- Forensic analysis: Understanding exactly how the attackers moved through the network
- Threat hunting: Looking for additional compromise, backdoors, or persistence mechanisms
- Notification planning: Determining which individuals to notify and by what means
- Communications strategy: Developing messages for employees, customers, regulators, and media
- Remediation roadmap: Creating a plan to fix vulnerabilities and prevent recurrence
Weeks two through four focus on execution: notifications go out, investigation deepens, recovery operations begin, and remediation work accelerates. Investigators will be looking for:
- How did attackers enter? (People Soft vulnerability via stolen credentials)
- When did they enter? (September 2025, apparently)
- What systems did they access? (HR databases with 800,000 records)
- Did they install persistence? (Likely, given the time available)
- How long were they present? (Could be months)
- Were other systems affected? (Unknown without full investigation)
The recovery phase involves patching the People Soft vulnerability, resetting all compromised credentials, reviewing and tightening access controls, implementing new monitoring and detection capabilities, and potentially replacing key systems.
For a company the size of Wynn, full recovery could take months or years depending on system architecture and complexity. Even after systems are recovered and patched, the organization needs to rebuild trust, update security practices, train employees on the new reality, and implement the structural changes that prevent recurrence.

Lessons for Other Organizations: What to Actually Do
The Wynn breach, combined with the earlier Caesars and MGM incidents, provides several critical lessons for any organization holding sensitive data on employees or customers:
Patch management is non-negotiable. The attack leveraged a known vulnerability in Oracle People Soft. If that vulnerability was known and a patch was available, there's no excuse for remaining unpatched on systems this critical. Organizations should:
- Implement a patch management system that automatically identifies missing patches
- Prioritize critical vulnerabilities affecting data-rich systems
- Test patches in development/staging before production deployment
- Track patch status and enforce compliance through automated remediation
- For systems that can't be patched immediately, implement compensating controls
Network segmentation prevents catastrophic spread. Once attackers obtained initial access, they apparently moved freely through the network to reach HR databases. Proper network segmentation would mean that compromising a web-facing system or People Soft instance doesn't immediately grant access to sensitive database servers.
Segmentation best practices include:
- Separate sensitive systems (database servers, file servers, authentication systems) onto different network segments
- Control traffic between segments with firewalls and access control lists
- Require authentication for cross-segment communication
- Implement zero-trust architecture where possible
- Monitor cross-segment traffic for anomalies
Credential security is foundational. The attack involved compromised employee credentials. Better credential security includes:
- Enforcing strong, unique passwords (or better, passphrases)
- Implementing multi-factor authentication (MFA) everywhere possible, especially for administrative accounts
- Removing shared credentials and service accounts with excessive permissions
- Implementing password managers that prevent credential reuse
- Detecting compromised credentials and forcing resets
Detection and response capability must exist. The attackers exfiltrated 800,000 records without detection. This indicates either no detection capability or detection capability that wasn't monitoring this activity. Organizations need:
- EDR (Endpoint Detection and Response) tools on critical systems
- Network intrusion detection monitoring unusual data flows
- User behavior analytics identifying suspicious user activity
- Regular security audits and penetration testing
- Security operations center (SOC) staff reviewing alerts
- Documented incident response procedures
- Regular incident response drills
Data access should be minimized. In an ideal world, 800,000 employee records wouldn't all be accessible in a single place to a single administrative interface. Data minimization strategies include:
- Storing only the data that's actually needed
- Encrypting sensitive data even when stored in databases
- Limiting who can export or access employee records in bulk
- Implementing data loss prevention (DLP) tools that alert on unusual data movements
- Maintaining an audit log of all access to sensitive databases
Insurance is not a security strategy. While cyber insurance helps with financial recovery, insurance doesn't prevent breaches, doesn't restore reputation, and doesn't eliminate business disruption. Insurance should be one layer of a comprehensive risk management strategy, not a substitute for actual security controls.
The organizations that respond best to the Wynn breach will be those that use it as a catalyst for improvement, not as a signal that they should "hope it doesn't happen here." History shows it happens everywhere eventually. The question is whether you're ready.
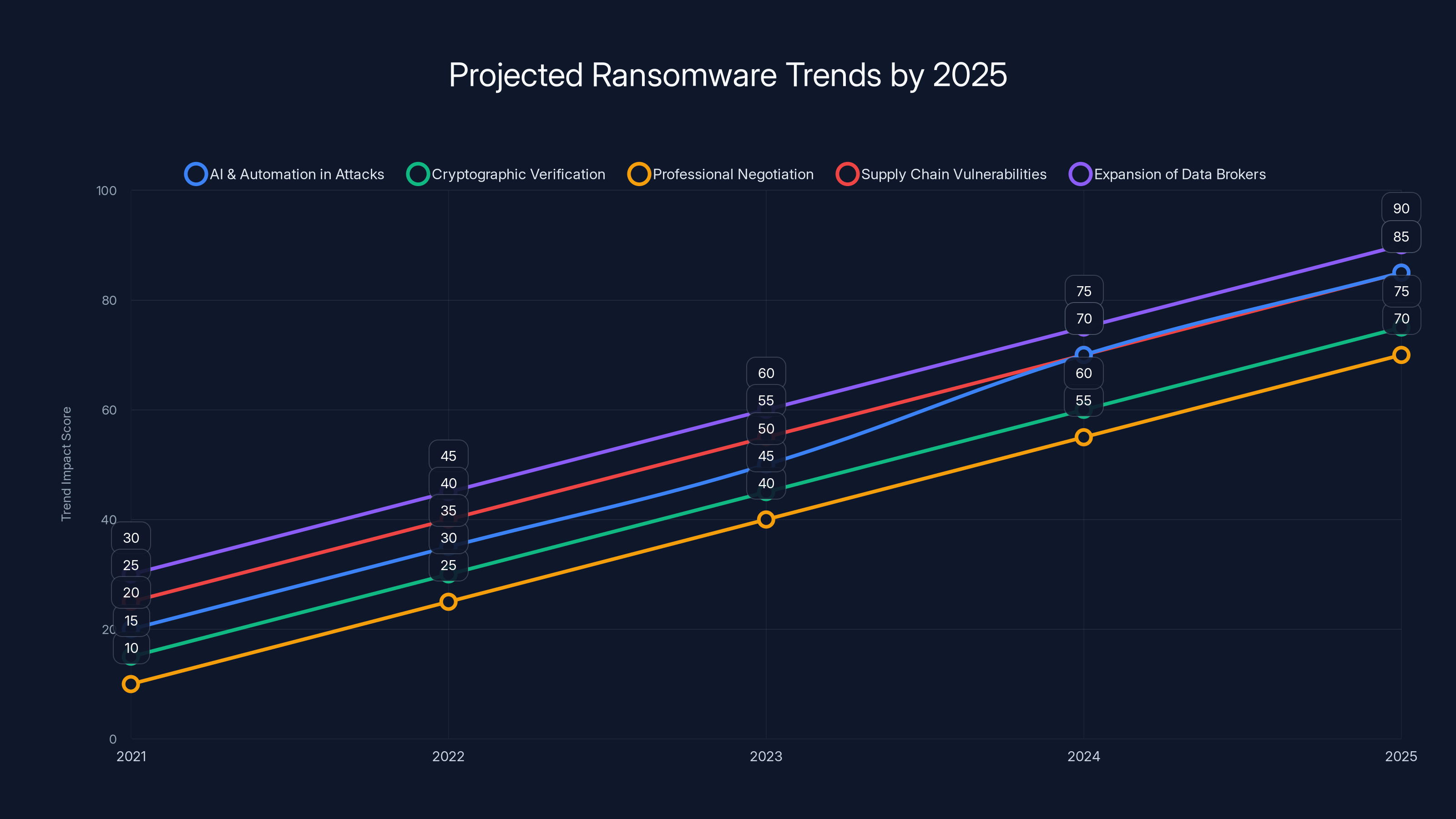
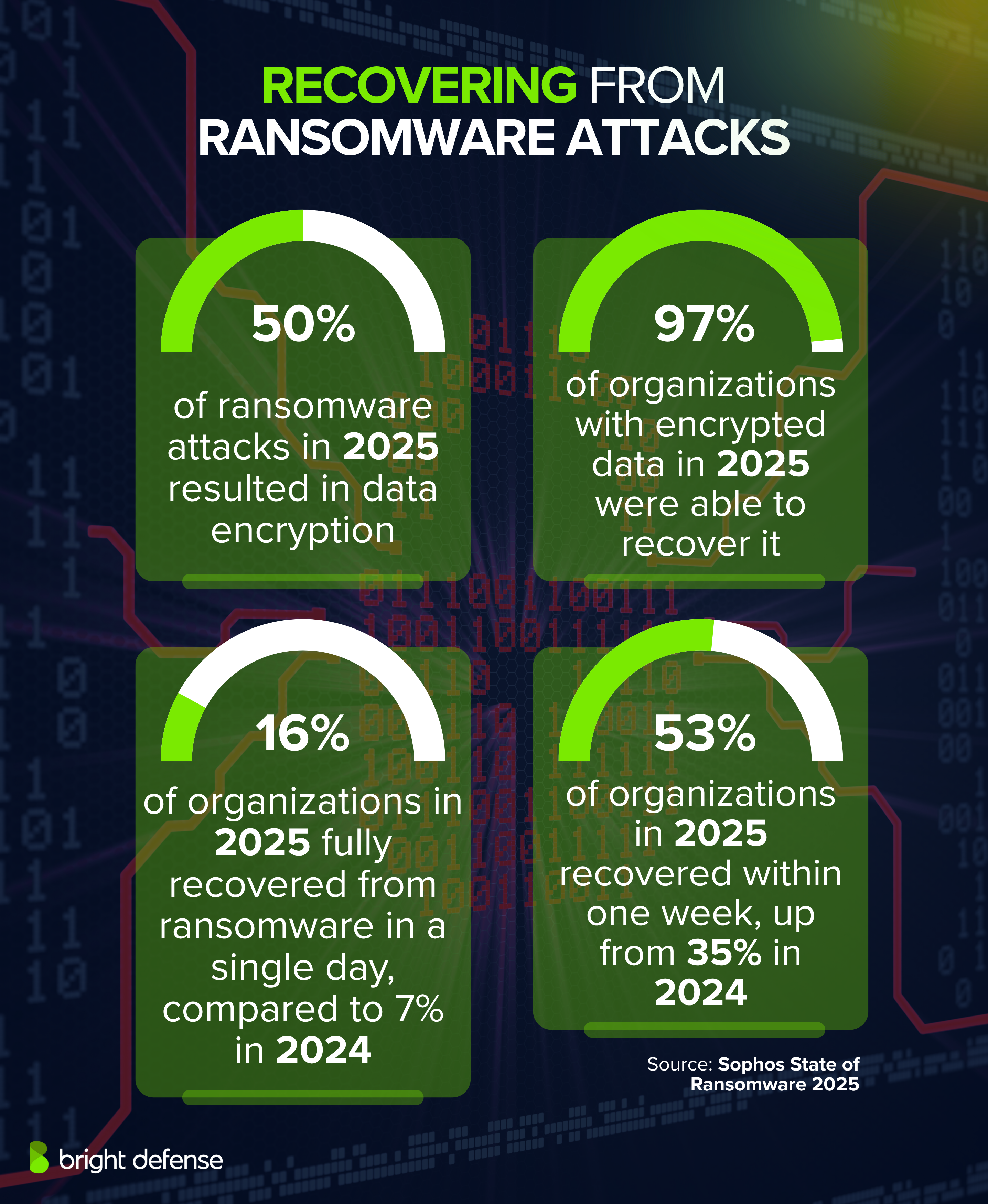
Estimated data shows significant growth in ransomware sophistication and impact by 2025, driven by AI, professionalization, and supply chain vulnerabilities.
Looking Forward: The Ransomware Landscape in 2025 and Beyond
The Wynn breach is part of a broader trend: ransomware operations are becoming more sophisticated, more targeted, and more profitable. Shiny Hunters and groups like them represent a new generation of cybercriminal enterprise.
Several trends are accelerating the ransomware problem:
AI and automation are making attacks easier. Threat actors increasingly use machine learning to identify vulnerable systems, automate exploitation, and accelerate data exfiltration. As AI tools become more accessible, the barrier to entry for ransomware operations decreases.
Cryptographic verification is becoming standard. Shiny Hunters provides samples of stolen data to prove legitimacy. As these practices become standard, the threat becomes more credible and organizations become more likely to pay.
Negotiation is becoming professionalized. Some ransomware groups now employ "customer service" processes, provide status updates, negotiate settlement terms, and even refund money if they promise data deletion but don't deliver. This professionalization makes ransomware more like a criminal business and less like random extortion.
Supply chain vulnerabilities are being weaponized. Attackers are increasingly targeting contractors, managed service providers, and software vendors who have access to multiple victim networks. A single compromised vendor can unlock access to dozens of organizations.
Data brokers and cybercriminal marketplaces are expanding. Even if an organization pays a ransom, there's no guarantee the stolen data is deleted. The data might be sold on underground forums, used for identity theft, sold to competitors, or leveraged in additional extortion campaigns.
From a strategic perspective, organizations should expect that ransomware will remain a persistent threat. The economics work too well for attackers and the defenses are inconsistent enough that group success rates remain high.
The most realistic organizational response is:
- Assume breach: Design systems with the assumption that attackers will eventually get in
- Minimize blast radius: Use segmentation, encryption, and access controls to limit what attackers can access and do
- Detect quickly: Invest in detection capability so breaches are identified before data exfiltration completes
- Maintain backups: Keep offline, encrypted backups so you can recover without ransom payment
- Plan recovery: Document incident response procedures and regularly drill them
- Invest continuously: Security is an ongoing investment, not a one-time purchase
The Wynn breach is significant, but it's not unique. Thousands of organizations face similar threats daily. The question for any organization is whether they're treating security with the seriousness it deserves or whether they're banking on luck.
From Incident to Industry Change: What Should Actually Happen
Wynn Resorts has an opportunity to drive meaningful change in the hospitality industry's approach to security. Here's what that could look like:
Industry-wide vulnerability sharing. If the People Soft vulnerability can be exploited against one hospitality company, it can likely be exploited against others. Wynn could work with peers to identify other potentially vulnerable organizations and coordinate remediation.
Security standard development. The hospitality industry could develop security standards specific to their operational challenges. What does baseline security look like for a 24/7 operation with high workforce turnover? What's reasonable for organizations operating at the scale of major casinos?
Incident response coordination. When one major organization is breached, competitors face elevated risk (attackers often target multiple organizations in a sector). Wynn could work with industry peers and law enforcement to share intelligence about attack patterns and response strategies.
Employee support programs. The 800,000 affected employees deserve more than just notification and credit monitoring. Wynn could fund identity theft insurance, financial counseling, or other support services.
Transparency about recovery. Many organizations go quiet after breaches. Wynn could demonstrate genuine commitment to change by transparently sharing what they've learned and how they're improving.
Whether Wynn chooses to use this breach as a catalyst for change or views it as a contained incident remains to be seen. The organization clearly has the resources to address security seriously. The question is whether this breach serves as sufficient impetus to justify the investment.
FAQ
What is ransomware and how does it work?
Ransomware is malicious software that encrypts an organization's files or systems, making them inaccessible to legitimate users. Attackers then demand payment (ransom) in exchange for providing decryption keys or deleting stolen data. Modern ransomware often combines encryption with data theft, threatening to publicly release sensitive information if the ransom isn't paid. This "double extortion" model makes ransom threats more credible because even organizations with good backups can't recover from public data disclosure.
Why would Wynn Resorts be targeted by Shiny Hunters?
Wynn Resorts was targeted because the hospitality and gaming industry represents an attractive target profile for ransomware groups. Major casino resorts operate with high revenues, handle sensitive employee and customer data, maintain complex 24/7 operations that can't tolerate extended downtime, and often run legacy systems that prioritize availability over security. Shiny Hunters demonstrated this targeting pattern by also attacking Caesars Entertainment and MGM Resorts within the same timeframe, suggesting systematic targeting of a specific sector rather than random incident selection.
How did Shiny Hunters access Wynn's network?
According to reports, Shiny Hunters exploited a vulnerability in Oracle People Soft, Wynn's human resources management system, and used stolen employee credentials to gain initial access. The attackers apparently obtained valid employee login credentials through phishing, credential stuffing, or other means, then used the People Soft vulnerability to escalate access and move through the network. Once established, they navigated to systems containing employee records and exfiltrated the data over a period of months without detection.
What data was stolen in the Wynn Resorts breach?
The breach exposed approximately 800,000 employee records containing full names, business email addresses, phone numbers, job titles, departments, salary information, start dates, and birth dates. This combination of data is particularly dangerous because it provides everything needed for identity theft, sophisticated social engineering attacks, competitive recruitment of key employees, and targeted phishing campaigns. The salary information also reveals compensation structures and identifies high-value employees by seniority level.
How much did Shiny Hunters demand from Wynn?
Shiny Hunters demanded 23.34 Bitcoin, equivalent to approximately $1.55 million at current exchange rates. The group specifically stated this was a "starting price," indicating willingness to negotiate for a lower amount. This opening position is strategic: high enough to represent significant money that gets executive attention, but low enough to be potentially justifiable as a business decision for a company generating billions in annual revenue. Ransomware groups typically expect to settle for 30-60% of their opening demand.
What are the likely consequences for Wynn Resorts?
Wynn faces multiple consequences across financial, legal, regulatory, and reputational domains. Financially, the company must notify affected employees, potentially provide years of credit monitoring services, invest in incident response and recovery, and likely settle lawsuits. Legally, the company faces class action lawsuits from affected employees alleging negligence and breach of duty. Regulators in multiple jurisdictions will investigate whether Wynn violated data protection laws. Reputationally, employee trust erodes significantly when personal data is breached, affecting recruitment and retention. The total cost from all sources could easily exceed the ransom demand many times over.
Should Wynn pay the ransom demand?
Most cybersecurity professionals recommend against paying ransoms because it reinforces the business model that makes attacks profitable, provides no guarantee of data deletion or lack of further exploitation, and may violate sanctions laws if the group has certain connections. However, the financial and operational decision-making process at a major corporation often weighs differently than security professionals expect. Paying might seem economically justified compared to recovery costs, litigation expenses, regulatory fines, and extended operational disruption. There's no universal right answer, but transparency and legal consultation are essential to any decision.
How can organizations prevent similar breaches?
Organizations should implement multiple layers of security controls: patch management systems that ensure critical vulnerabilities are remediated quickly, network segmentation that limits lateral movement if attackers gain entry, strong credential security including multi-factor authentication, detection systems that identify suspicious activity, regular security audits and penetration testing, and offline encrypted backups for business-critical systems. Additionally, organizations should maintain an inventory of sensitive data, limit access to only those who need it, and implement data loss prevention tools that alert on unusual data movements. No single control prevents all breaches, but a comprehensive program significantly reduces breach likelihood and impact.
What is an Oracle People Soft vulnerability and who else might be affected?
Oracle People Soft is an enterprise system for human resources and financial management used by thousands of organizations globally. A vulnerability in People Soft could affect all organizations running vulnerable versions of the software. If the vulnerability Shiny Hunters exploited against Wynn is known and affects other organizations, those organizations are likely at risk unless they've already patched. Other companies running unpatched People Soft should immediately verify their patch status and apply updates, as the vulnerability has been weaponized by an active threat group with demonstrated capability and motivation.
What does "double extortion" mean in ransomware context?
Double extortion refers to a ransomware model where attackers both encrypt systems and steal sensitive data before demanding payment. The first extortion vector is encryption: if you don't pay, your systems remain locked. The second extortion vector is data theft: if you don't pay, stolen data is publicly released or sold. This approach is more effective than simple encryption because many organizations maintain good backups and can recover encrypted data without paying. But organizations can't unspill publicly released sensitive data, so the data theft threat becomes the primary leverage point.
How long will it take Wynn to fully recover from this breach?
Full recovery from a breach of this magnitude typically takes months to years, not weeks. Wynn must complete forensic analysis to identify all affected systems, conduct threat hunting to find persistence mechanisms, patch vulnerable systems, reset all potentially compromised credentials, rebuild affected systems from clean copies, implement new security controls, navigate regulatory investigations and legal proceedings, notify affected parties, and ultimately rebuild organizational trust. The operational timeline might be weeks for core systems, but the broader recovery including legal resolution and reputation rebuilding could span 12-24 months or longer.

Conclusion
Wynn Resorts' breach serves as the latest chapter in an increasingly sophisticated ransomware narrative. Shiny Hunters didn't stumble upon Wynn by accident. The group identified a sector vulnerable to their methods, targeted the organization methodically, and executed a breach that revealed numerous security gaps in an enterprise that clearly has the resources to secure itself better.
The fundamental problem isn't that ransomware is new or particularly sophisticated. The problem is that the economics of ransomware remain heavily tilted toward attackers. A group like Shiny Hunters can attack thousands of organizations, succeed with 5-10%, and generate millions in revenue. They've professionalized their operations, offering negotiation services and proving data legitimacy before demanding payment. They've learned from previous breaches and refined their approach.
Meanwhile, defender-side economics remain challenging. Proper security requires consistent investment: skilled personnel, modern tools, regular training, continuous testing, and organizational discipline. Security provides no revenue, no competitive advantage, and no direct customer value. It's purely a risk mitigation function. This creates a perverse incentive where organizations underinvest in security relative to actual risks.
The Wynn breach reveals something important about the current state of enterprise security: the gaps aren't primarily about technology. They're about operational choices and organizational priorities. Wynn had the resources to patch People Soft. They had the resources to implement network segmentation. They had the resources to deploy endpoint detection tools. They had the resources to train employees on security. The breach happened because somewhere in organizational decision-making, those resources were allocated to other priorities.
For security leaders at other organizations, the Wynn incident should trigger an honest self-assessment: Could this happen to us? Almost certainly, yes. The question is whether your organization is taking steps to minimize the probability and impact, or whether you're betting on luck.
The good news is that the primary controls preventing breaches like this are well-understood. They're not mysterious or cutting-edge. They're fundamental hygiene: patch systems, segment networks, enforce strong credentials, monitor activity, maintain backups, and respond quickly when something seems wrong. Organizations that do these things consistently still get breached sometimes, but when they do, the impact is dramatically smaller.
Wynn's breach will eventually resolve. The company will pay negotiated settlement (either to the attackers or through litigation and recovery costs), implement security improvements, and gradually rebuild employee and customer trust. What matters now is whether the organization uses this breach as a catalyst for genuine change or whether it's viewed as an exceptional incident unlikely to recur.
Historically, most organizations fall into the second category. They respond to the breach, implement specific fixes for the known vulnerability, and gradually return to pre-breach security posture. Shiny Hunters and similar groups are counting on exactly this pattern. When the pressure passes and budgets tighten, security investments get deferred. New vulnerabilities emerge. Legacy systems remain unpatched. And eventually, the next target emerges.
Breaches of this scale are no longer exceptional events. They're part of the operational landscape for organizations handling sensitive data. The real question is whether that fact drives organizational change or whether it just gets filed away as an unfortunate incident that shouldn't happen again.

Key Takeaways
- ShinyHunters successfully breached Wynn Resorts and obtained 800,000 employee records, demanding $1.55 million Bitcoin—the third major Las Vegas property targeted in 18 months
- Attack vector combined Oracle PeopleSoft vulnerability exploitation with stolen employee credentials, revealing critical gaps in patch management, network segmentation, and detection capabilities
- Total breach cost to Wynn will likely exceed $20 million when including notification, credit monitoring, legal defense, regulatory investigation, and potential fines—far exceeding the ransom demand
- Hospitality and gaming industry remains disproportionately targeted by ransomware due to 24/7 operational demands, high data value, legacy system dependencies, and operational pressure to pay rather than disrupt services
- Organizations can prevent similar breaches through layered security controls: patch management, network segmentation, multi-factor authentication, endpoint detection and response, and offline encrypted backups
Related Articles
- CarGurus Data Breach: 1.7M Records Stolen by ShinyHunters [2025]
- Ivanti VPN Breach: How Chinese Hackers Hit 119 Customers [2025]
- AI-Powered Hacking: How Low-Skill Attackers Break Firewalls [2025]
- Android AI Photo Editor Data Breach: 2M Users Exposed [2025]
- Honeywell CCTV Camera Vulnerability: Complete Security Guide [2025]
- Texas Sues TP-Link Over China Links and Security Vulnerabilities [2025]
![ShinyHunters Hits Wynn Resorts: $1.5M Ransomware Demand [2025]](https://tryrunable.com/blog/shinyhunters-hits-wynn-resorts-1-5m-ransomware-demand-2025/image-1-1771868353426.jpg)



