Exposing Cyber Intruders: A Deep Dive into Russian Government Hackers Targeting Signal Accounts [2025]
Last month, an unexpected message landed on the phone of a seasoned spyware investigator, Donncha Ó Cearbhaill. The message, posing as a Signal Security Support Chat Bot, claimed suspicious activity on his device. This wasn't just a casual phishing attempt; it was a calculated attack allegedly linked to Russian government hackers. But how did this happen, and what can we learn from it?
TL; DR
- Russian hackers targeted Signal accounts using phishing tactics disguised as security alerts.
- Security experts like Donncha Ó Cearbhaill play a crucial role in exposing these threats.
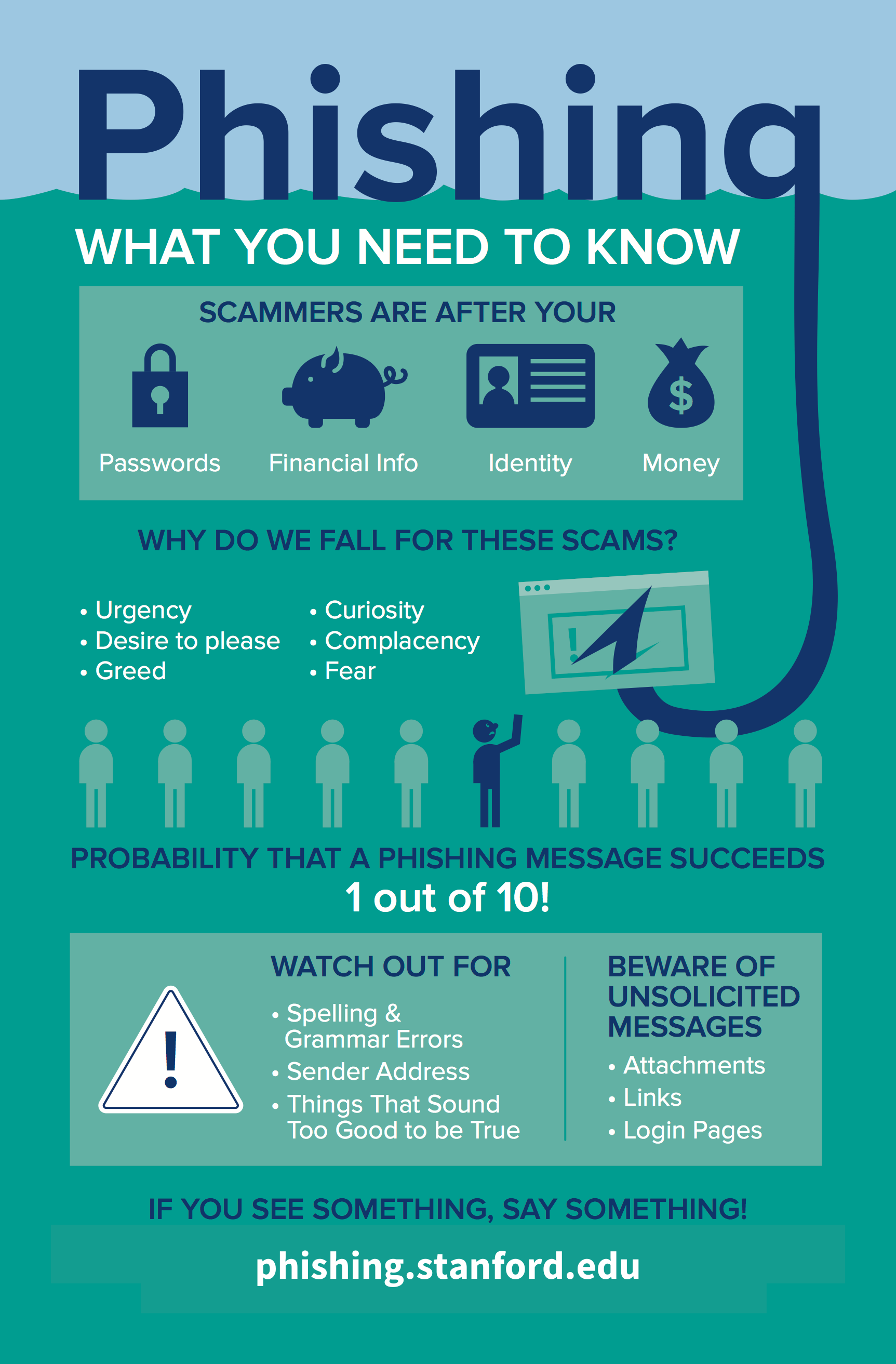
- Phishing remains a potent tool for cybercriminals, exploiting human trust.
- Signal and similar platforms must enhance user education on security practices.
- Future cybersecurity trends point towards AI-driven defenses and increased threat intelligence sharing.

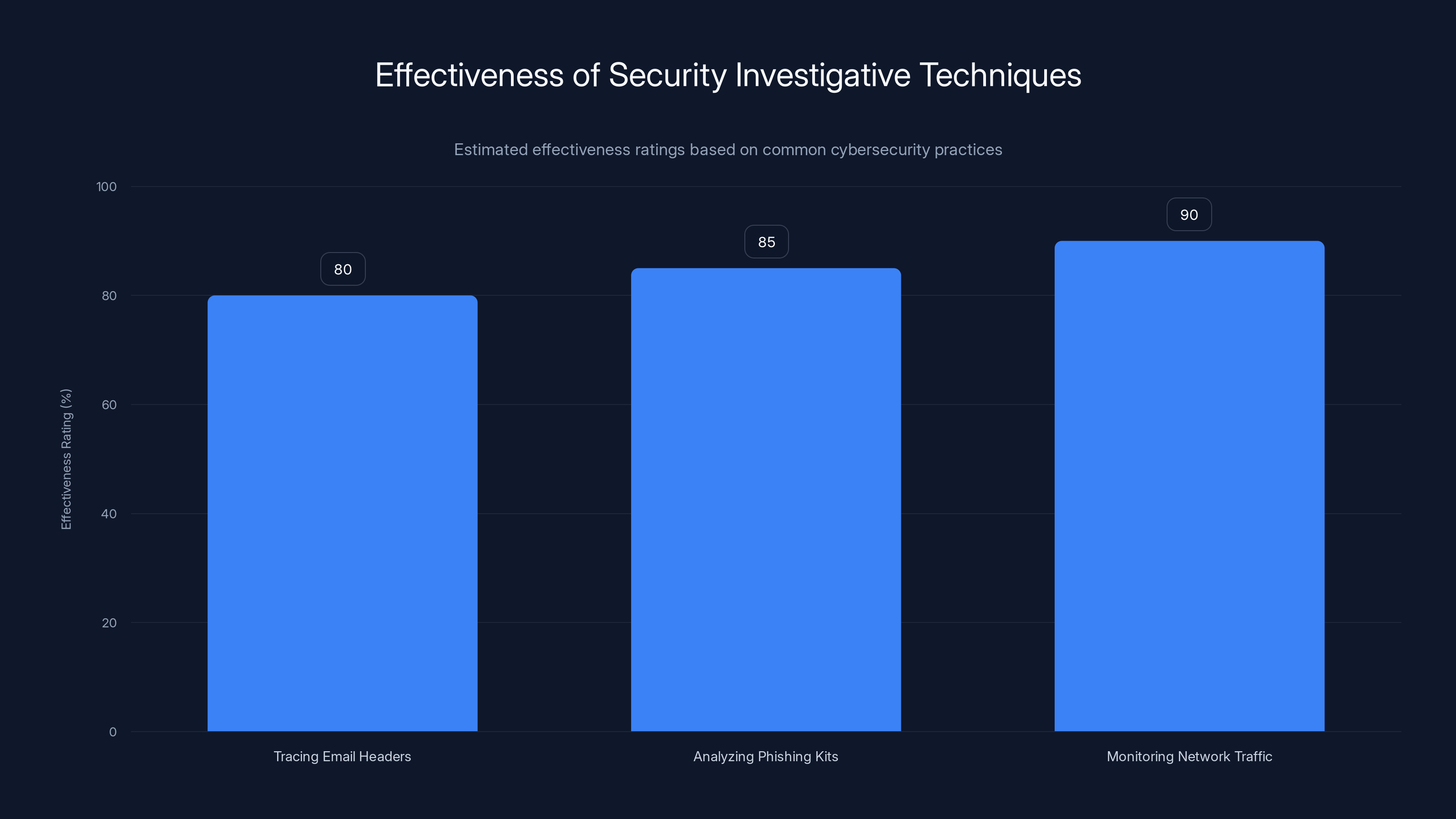
Monitoring network traffic is estimated to be the most effective technique in detecting cyber threats, with a rating of 90%. Estimated data.
The Threat Landscape: Phishing in Focus
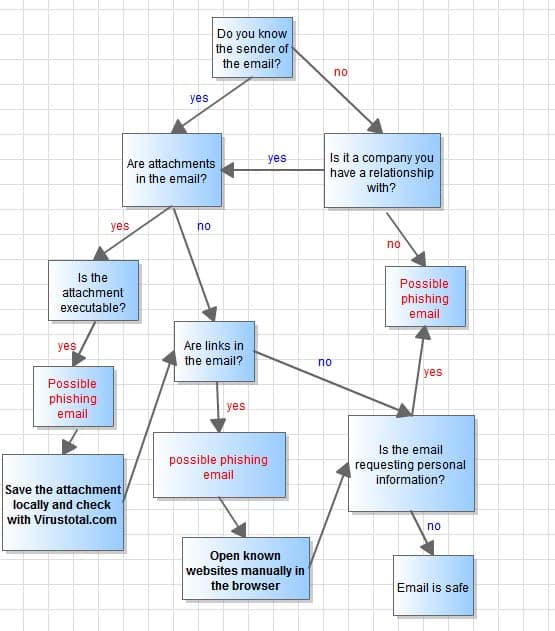
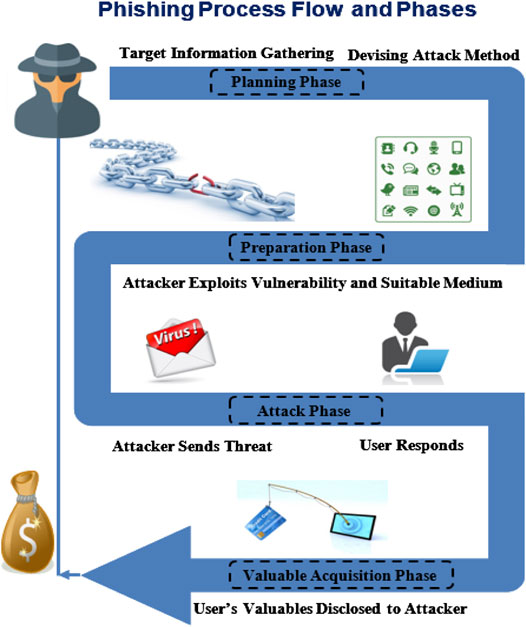
Phishing has long been a staple in the cybercriminal's toolkit. It's simple, effective, and often exploits the weakest link in the security chain: the user. In this case, hackers posed as Signal's security team, urging users to verify their identity by sharing a code. This tactic, while not new, is alarmingly effective, as highlighted by recent studies.
Anatomy of a Phishing Attack
A phishing attack typically starts with an email or message that appears to be from a trusted source. The goal is to trick the recipient into revealing personal information or downloading malware. In the case of Ó Cearbhaill, the hackers used a fake Signal support message to lure him into a false sense of security.
Key Elements of Phishing Attacks:
- Spoofed Sender Address: Appears to come from a legitimate source.
- Urgent Language: Creates a sense of urgency to prevent rational thinking.
- Malicious Links or Attachments: Leads to fraudulent websites or downloads malware.
- Requests for Personal Information: Aims to gather passwords, security codes, etc.
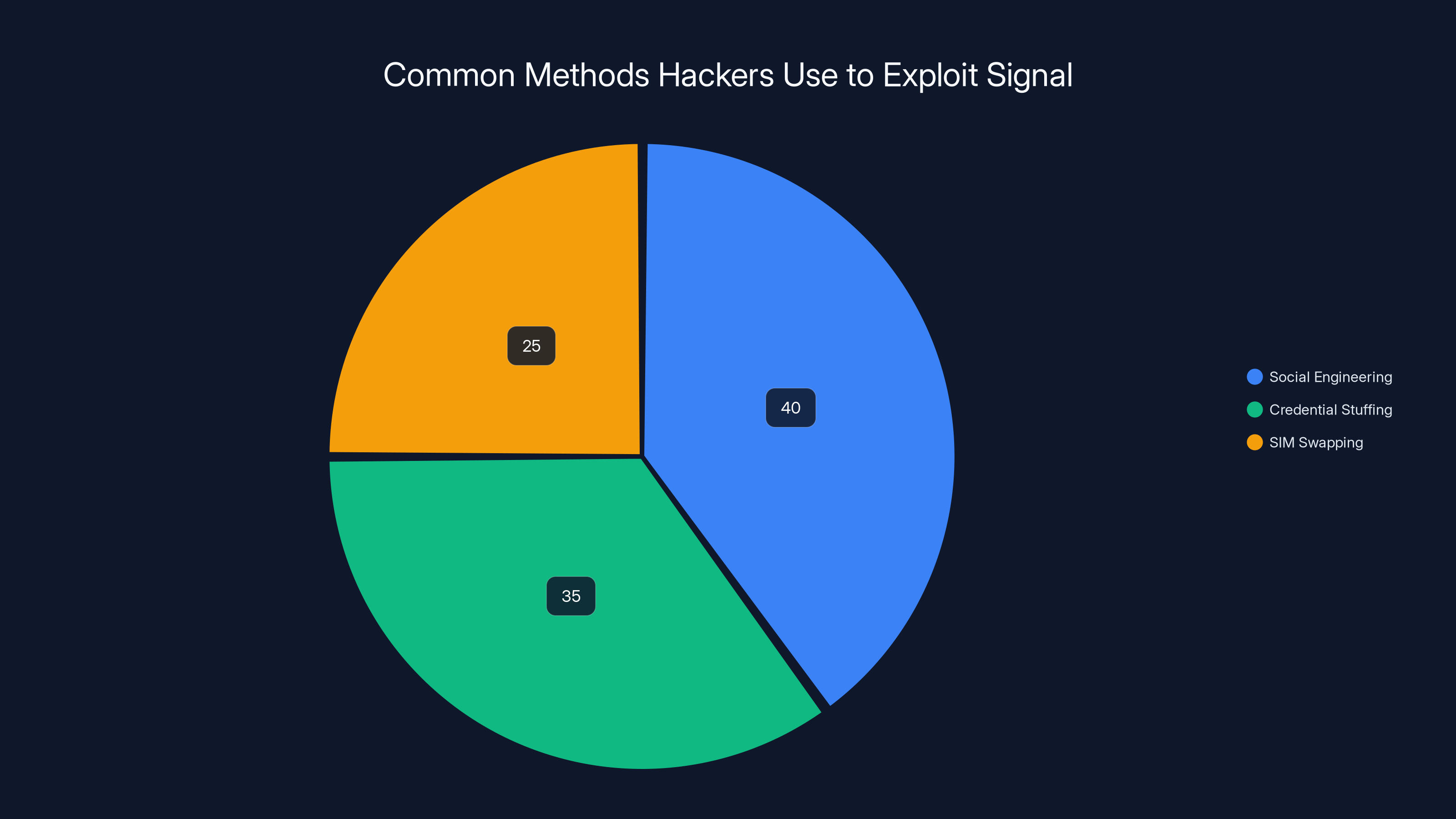
Social engineering is the most common method used by hackers, accounting for an estimated 40% of attacks on Signal users. Estimated data.
The Role of Security Professionals
Security researchers like Donncha Ó Cearbhaill are on the front lines of cybersecurity. When faced with a phishing attempt, Ó Cearbhaill didn’t fall for the trap. Instead, he leveraged the opportunity to investigate the attackers. This proactive approach is vital in understanding and combating cyber threats, as noted by cybersecurity experts.
Investigative Techniques
- Tracing Email Headers: Identifying the real sender's IP address.
- Analyzing Phishing Kits: Dissecting the tools used by attackers.
- Monitoring Network Traffic: Detecting unusual patterns that indicate data exfiltration.
Common Pitfalls and Solutions
While phishing attacks are common, they can be thwarted with proper awareness and tools. Here are some common pitfalls and how to avoid them:
- Ignoring Security Warnings: Always heed browser and security software warnings about suspicious sites.
- Weak Passwords: Use complex passwords and enable two-factor authentication (2FA) wherever possible.
- Lack of User Training: Regularly educate users about new phishing tactics and security best practices.
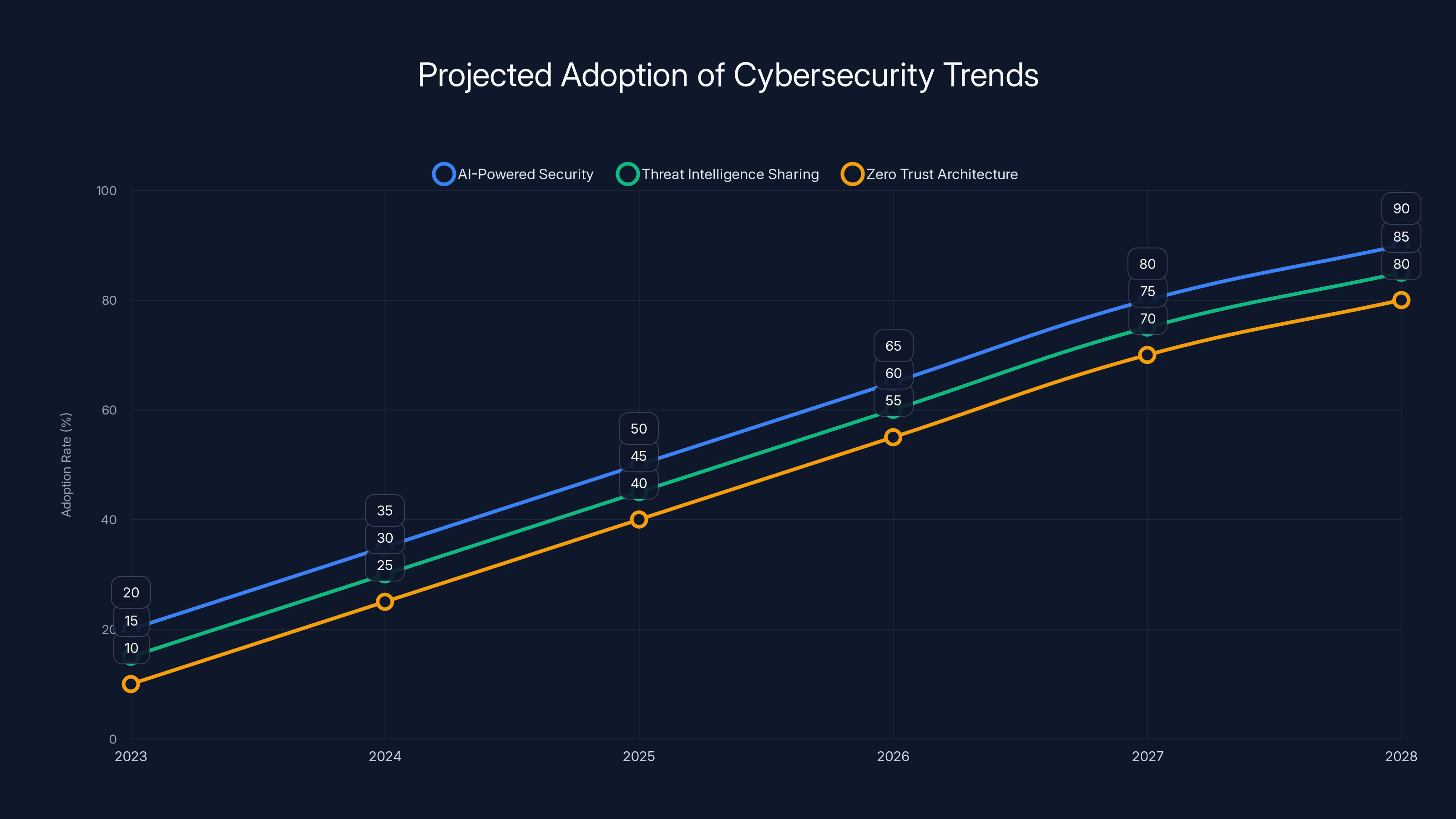
Estimated data shows a significant increase in the adoption of AI-powered security, threat intelligence sharing, and zero trust architecture by 2028, reflecting the growing need for advanced cybersecurity measures.
The Technical Side: How Hackers Exploit Signal
Signal is renowned for its end-to-end encryption, but no system is impervious to all forms of attack. Hackers often exploit user habits rather than the technology itself, as detailed in media reports.
Exploiting User Behavior
- Social Engineering: Convincing users to bypass security protocols.
- Credential Stuffing: Using previously breached data to access accounts.
- SIM Swapping: Hijacking a phone number to intercept SMS-based authentication codes.
Implementation Guides for Enhanced Security
To safeguard against these threats, both users and organizations must adopt robust security measures.
Best Practices for Users
- Verify Sender Information: Always double-check the sender’s details before responding.
- Use a Password Manager: Generate and store complex passwords securely.
- Stay Informed: Subscribe to security bulletins for the latest updates.
Organizational Measures
- Implement Security Awareness Programs: Regular training sessions on cybersecurity threats.
- Deploy Anti-Phishing Solutions: Tools that scan for and block phishing attempts.
- Conduct Regular Penetration Testing: Identify and fix vulnerabilities proactively.
Future Trends in Cybersecurity
As cyber threats evolve, so too must our defenses. Here are some trends to watch:
AI-Powered Security
Artificial Intelligence (AI) is increasingly being used to detect and respond to cyber threats. Machine learning algorithms can identify patterns and anomalies that might indicate an attack, providing real-time alerts and automated responses, as discussed in recent reports.
Increased Threat Intelligence Sharing
Organizations are beginning to share threat intelligence data to collectively bolster their defenses. This collaborative approach allows for faster identification and mitigation of emerging threats, as noted by industry analysts.
Zero Trust Architecture
Adopting a zero-trust approach means never trusting, always verifying. This model assumes that threats can come from both outside and inside the network, prompting stringent access controls and monitoring.

Conclusion: Navigating the Cybersecurity Landscape
The incident involving Donncha Ó Cearbhaill and the Russian hackers attempting to hijack Signal accounts serves as a stark reminder of the ever-present threat of cybercrime. By understanding the tactics used by attackers and implementing robust security measures, both individuals and organizations can protect themselves against such threats.
In an era where data is the new oil, safeguarding it is imperative. As we look to the future, embracing new technologies and fostering a culture of security awareness will be key in building resilient defenses against cyber threats.
FAQ
What is phishing?
Phishing is a type of cyberattack where attackers send fraudulent messages to trick individuals into revealing sensitive information or downloading malware.
How can I protect my Signal account?
Use two-factor authentication, verify sender information, and stay informed about the latest phishing tactics.
Why are hackers targeting Signal?
Signal's popularity and its focus on privacy make it a prime target for hackers looking to access private communications.
What role does AI play in cybersecurity?
AI helps in detecting and responding to threats in real-time, identifying patterns and anomalies that might indicate an attack.
How does SIM swapping work?
SIM swapping involves transferring a victim’s phone number to a SIM card controlled by the attacker, allowing them to intercept SMS-based authentication codes.
What is Zero Trust architecture?
Zero Trust is a security model that requires strict identity verification for every person and device trying to access resources on a private network.
Key Takeaways
- Phishing remains a top cyber threat, exploiting user trust.
- Security experts play a crucial role in identifying and mitigating threats.
- AI and machine learning are pivotal in modern cybersecurity defenses.
- Zero Trust architecture enhances security by assuming all network traffic is untrusted.
- SIM swapping is a growing threat to account security.
- Increased threat intelligence sharing improves collective defenses.
Related Articles
- Identity is the New Perimeter: The Shift from Breaking In to Logging In [2025]
- The Massive Banks of Malware: Visualizing the Data Giants [2025]
- The FBI's Remote Router Resets: What It Means for Your Network [2025]
- Microsoft's MDASH AI Security Platform: A Game Changer? [2025]
- Training Custom AI Models from Production Workflows: A New Era for Enterprises [2025]
- The Big Three's Plan to Eradicate Coverage Dead Zones [2025]
![Exposing Cyber Intruders: A Deep Dive into Russian Government Hackers Targeting Signal Accounts [2025]](https://tryrunable.com/blog/exposing-cyber-intruders-a-deep-dive-into-russian-government/image-1-1778769363032.jpg)



