Understanding the Fragnesia Flaw: How It Threatens Linux Security [2025]
Linux has long been heralded as a bastion of security and stability in the computing world. However, even the most secure systems are not immune to vulnerabilities. Recently, a significant security flaw, dubbed Fragnesia, has been discovered in the Linux kernel. This vulnerability allows attackers to execute malicious code with root privileges, posing a critical risk to systems worldwide.
TL; DR
- Fragnesia Explained: A newly discovered Linux kernel flaw that enables attackers to execute code as root.
- Impact: Affects multiple Linux distributions and could lead to system compromise.
- Mitigation Strategies: Update to the latest kernel version and apply security patches.
- Technical Details: Involves the corruption of the
/usr/bin/supage cache. - Future Outlook: Emphasizes the need for continuous security audits and proactive patch management.
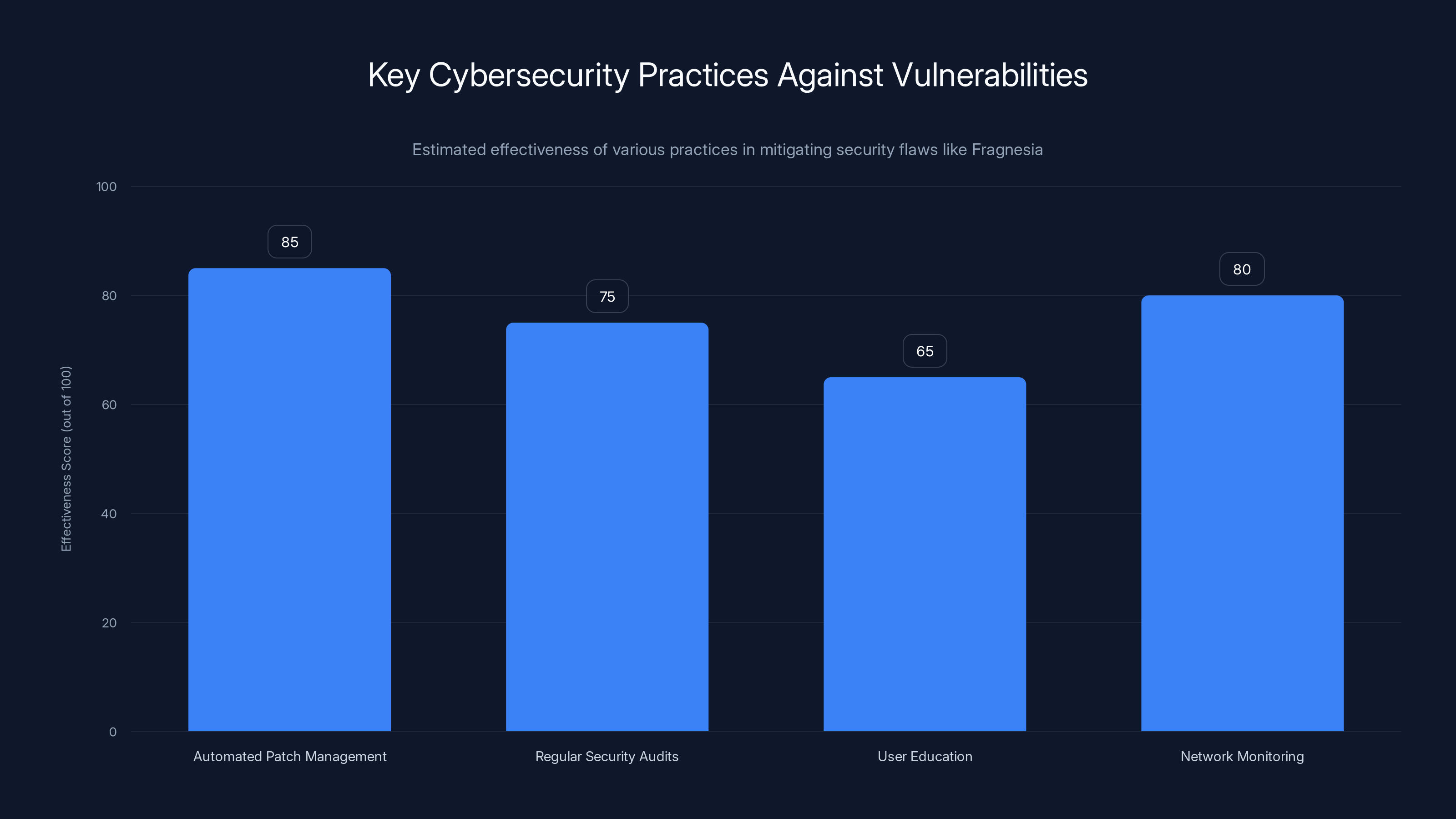
Automated patch management is estimated to be the most effective practice against vulnerabilities like Fragnesia. Estimated data.
The Emergence of Fragnesia
Discovered by William Bowling of Zellic, the Fragnesia flaw is a vulnerability identified as CVE‑2026‑46300. It belongs to the same family of vulnerabilities as the notorious Dirty COW, which exploited race conditions in the Linux kernel. Fragnesia takes advantage of weaknesses in memory management, specifically targeting the page cache of critical system binaries.
How Fragnesia Works
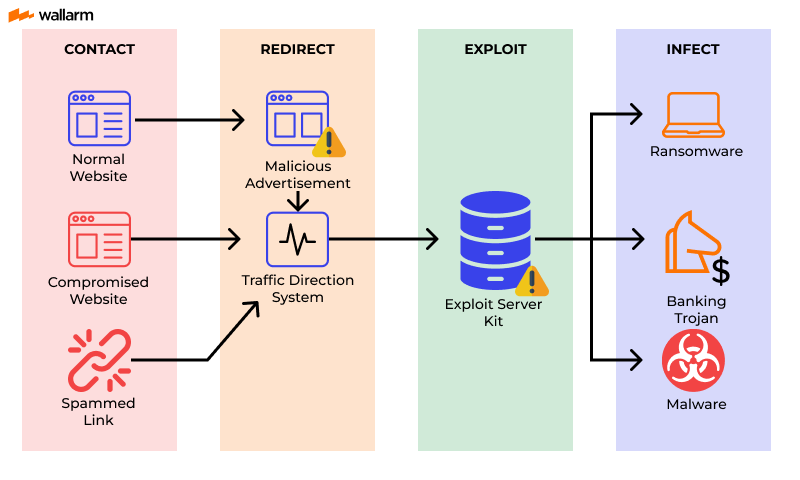
At its core, Fragnesia exploits a flaw in the way Linux handles the page cache for executable files. Attackers can manipulate this cache to inject malicious code into the memory space of critical system processes. The result? Unauthorized code execution with elevated privileges, effectively granting the attacker root access. According to The Hacker News, this vulnerability is particularly concerning due to its potential to bypass traditional security measures.
The proof of concept (PoC) demonstrated by researchers involves corrupting the page cache of the /usr/bin/su binary, a crucial utility for switching user identities. By tampering with this executable, attackers can bypass authentication mechanisms and execute arbitrary commands.

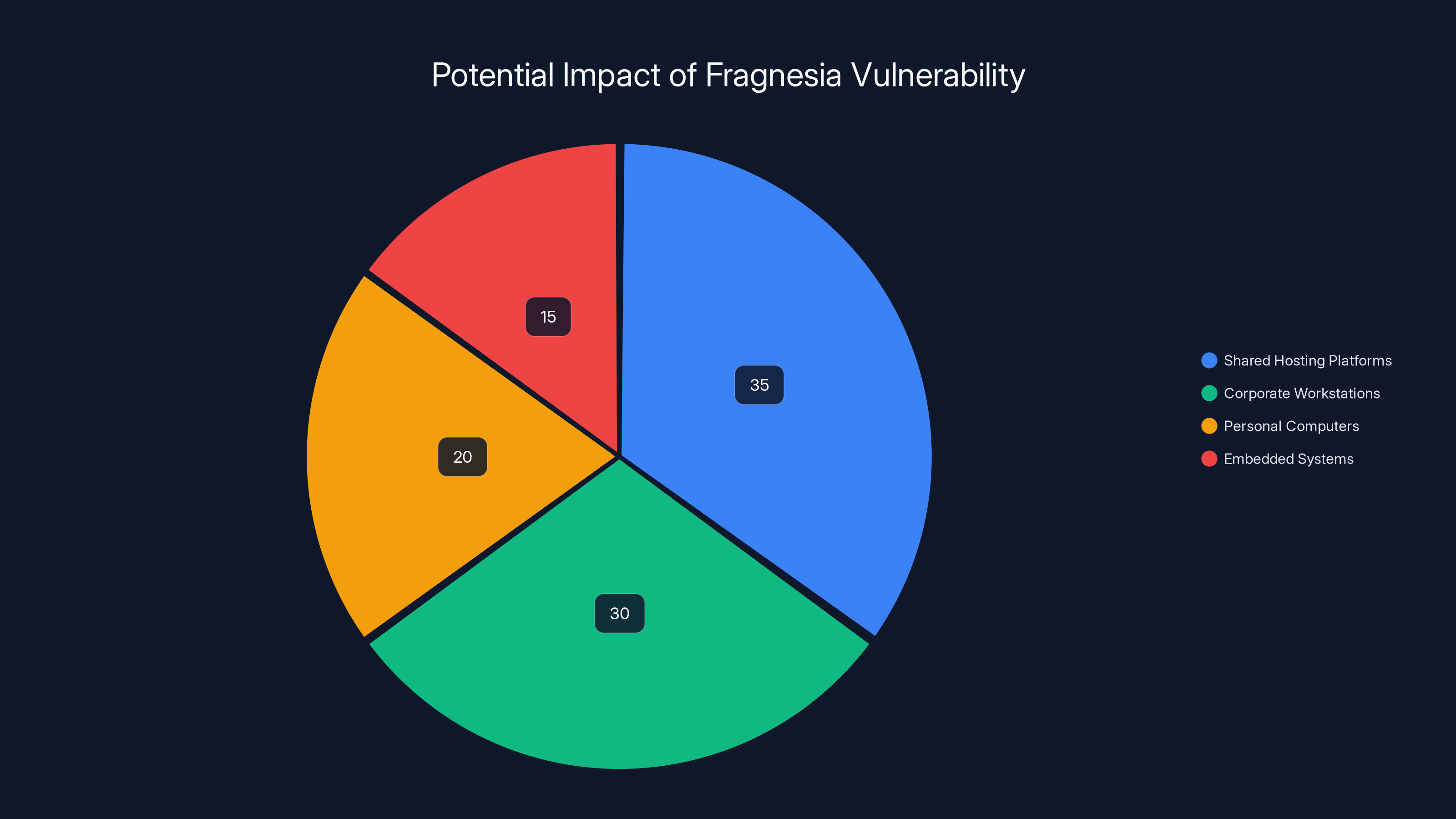
Estimated data shows shared hosting platforms and corporate workstations are most at risk from Fragnesia, due to their exposure to multiple users and sensitive data.
Technical Breakdown
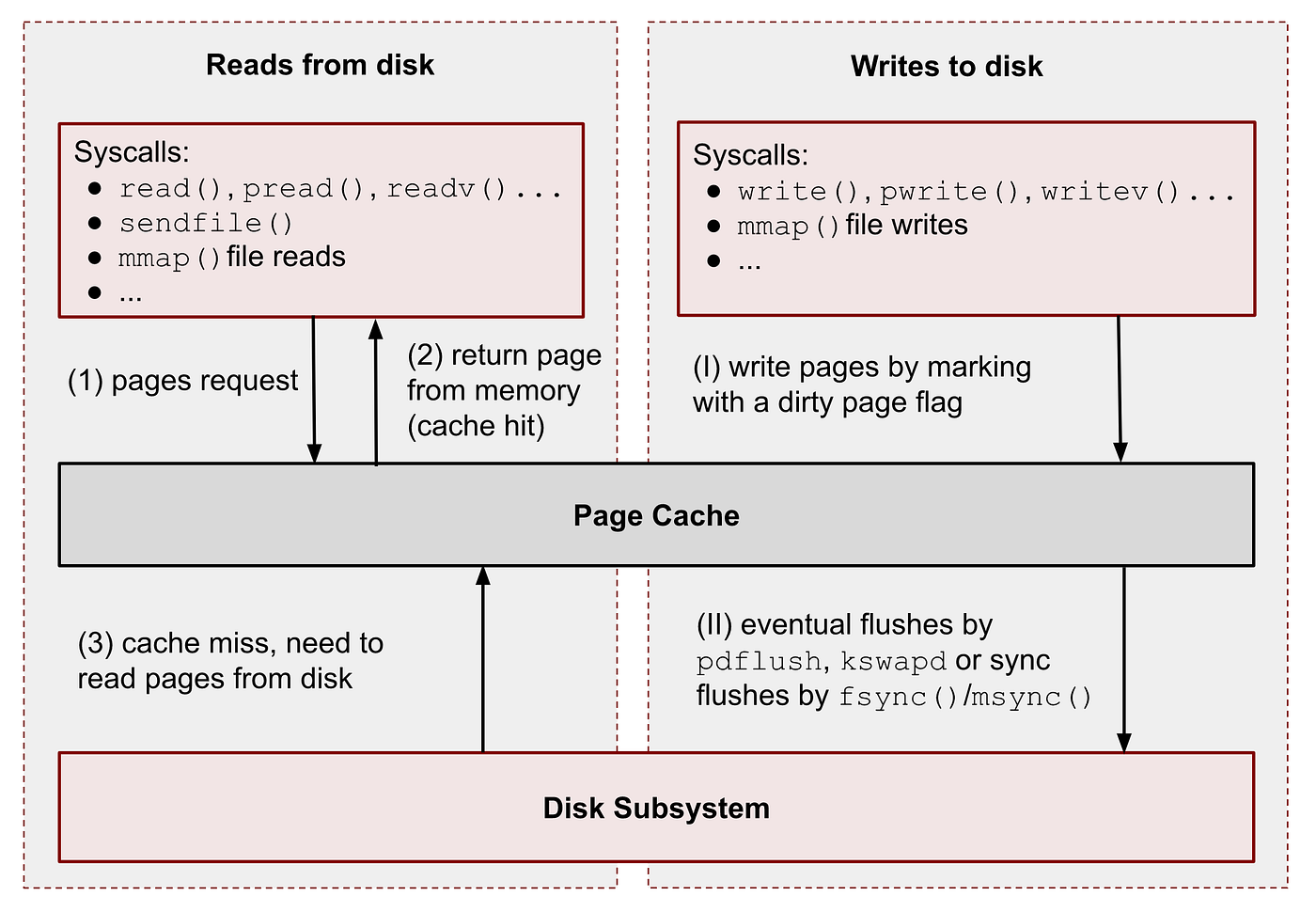
To understand Fragnesia, it's essential to grasp the basics of Linux's page cache mechanism. The page cache is a layer between the filesystem and physical memory, designed to improve performance by storing frequently accessed disk data in RAM. This caching reduces disk I/O operations, making the system more efficient.
Exploiting the Page Cache
The flaw exploited by Fragnesia lies in the ability to manipulate this cache. Normally, the page cache should be a read-only area for executables, but due to improper handling of race conditions, an attacker can write to it under specific circumstances. Wiz.io provides a detailed breakdown of how this manipulation is achieved.
- Triggering the Vulnerability: The attacker first launches a legitimate process that uses a target binary, like
/usr/bin/su. - Cache Manipulation: By exploiting a race condition, the attacker can write to the cached pages of this binary.
- Executing Malicious Code: Once the cache is compromised, the attacker can insert and execute unauthorized code with the privileges of the original process.
Real-World Implications
The implications of Fragnesia are significant. Any system running an affected Linux kernel version is at risk, especially those exposed to untrusted local users. Servers, personal computers, and even embedded systems could be compromised if not properly secured. Infosecurity Magazine highlights the widespread impact this vulnerability could have on various systems.
Use Cases and Examples
Consider a shared server environment where multiple users have shell access. An attacker with even limited access could leverage Fragnesia to escalate their privileges, potentially disrupting services, stealing sensitive data, or deploying ransomware.
-
Case Study: Shared Hosting Platforms
- Scenario: A shared web hosting service where users deploy custom applications.
- Risk: Malicious users exploit Fragnesia to gain root access, defacing websites or accessing customer databases.
-
Case Study: Corporate Workstations
- Scenario: A corporate environment with developers using Linux machines.
- Risk: An insider threat uses Fragnesia to install backdoors, exfiltrate intellectual property, or sabotage projects.
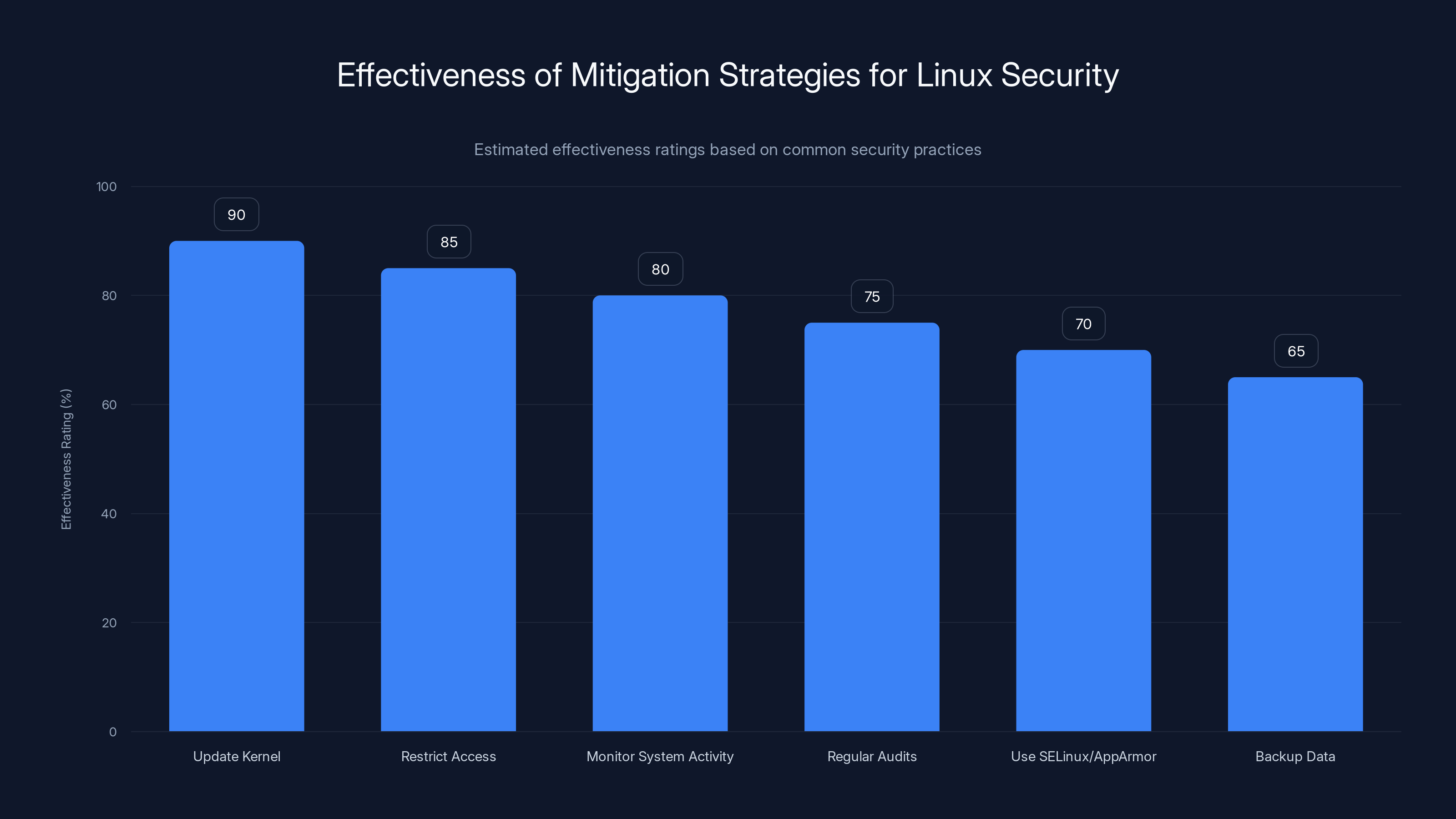
Updating the kernel and restricting access are the most effective strategies, with ratings of 90% and 85% respectively. Estimated data.
Mitigation Strategies
Addressing such a critical flaw requires a multi-faceted approach, focusing on patch management, system hardening, and monitoring.
Immediate Actions
-
Update Kernel: Ensure all systems are running the latest kernel version with security patches applied. The Linux community has released updates to mitigate this flaw. Kaseya emphasizes the importance of timely patch management in mitigating vulnerabilities like Fragnesia.
bashsudo apt-get update sudo apt-get upgrade sudo reboot -
Restrict Access: Limit shell access to trusted users only. Implement access control mechanisms to minimize the risk of an untrusted user exploiting the flaw.
-
Monitor System Activity: Deploy intrusion detection systems (IDS) to monitor unusual activity, such as unauthorized privilege escalation attempts.
Best Practices for Linux Security
- Regular Audits: Conduct regular security audits to identify and address vulnerabilities.
- Use SELinux or App Armor: Implement security modules like SELinux or App Armor to enforce stricter access controls.
- Backup Data: Regularly back up critical data to mitigate the impact of potential attacks.

Common Pitfalls and Solutions
While the above measures are effective, there are common pitfalls that organizations must avoid to ensure comprehensive protection.
- Ignoring Updates: Delaying kernel updates can leave systems vulnerable. Automate the update process to ensure timely patching.
- Overlooking Insider Threats: Fragnesia's exploitation requires local access. Implementing least privilege principles and monitoring internal activity can mitigate insider threats.
- Neglecting Backup Integrity: Regular backups are crucial, but they must be tested for integrity. Ensure backups are not compromised by ransomware.
Future Trends and Recommendations
The discovery of Fragnesia highlights the evolving nature of cybersecurity threats. As attack vectors become more sophisticated, security measures must also advance.
Predictive Threat Modeling
Organizations should invest in predictive threat modeling to anticipate future vulnerabilities. By analyzing current trends and historical data, security teams can proactively address potential risks.
Embracing AI and Machine Learning
AI and machine learning can enhance threat detection capabilities. These technologies can identify patterns and anomalies that might indicate an attack, allowing for quicker response times.
Community Collaboration
The open-source nature of Linux encourages community collaboration. Engaging with the broader community can lead to quicker identification and resolution of security flaws. Participating in forums, attending conferences, and contributing to projects can strengthen security postures.
Conclusion
The Fragnesia flaw underscores the importance of vigilance in cybersecurity. While Linux remains a robust and secure operating system, no system is impervious to vulnerabilities. By understanding the mechanics of Fragnesia, adopting best practices, and staying informed about emerging threats, organizations can protect their systems and data from compromise.
Use Case: Protect your servers from the Fragnesia flaw by automating security patch management with Runable's AI-powered workflows.
Try Runable For FreeFAQ
What is the Fragnesia flaw?
Fragnesia is a vulnerability in the Linux kernel that allows attackers to execute malicious code with root privileges by exploiting flaws in the page cache.
How can I protect my Linux system from Fragnesia?
Update your Linux kernel to the latest version, apply security patches, restrict shell access, and monitor system activity with IDS.
What are the risks associated with Fragnesia?
The primary risk is unauthorized code execution with root privileges, leading to potential data breaches, system compromise, and service disruption.
Can Fragnesia affect all Linux distributions?
Yes, any Linux distribution running an affected kernel version is vulnerable to Fragnesia. It's crucial to stay updated with security patches.
What are some best practices for Linux security?
Regularly update your system, conduct security audits, use security modules like SELinux, and implement access controls and backups.
How does Fragnesia differ from other Linux vulnerabilities?
Fragnesia specifically targets the page cache mechanism in Linux, similar to Dirty COW, but with unique exploitation techniques and potential impacts.
What role does community collaboration play in addressing vulnerabilities like Fragnesia?
Community collaboration allows for faster identification and resolution of security flaws, leveraging the collective expertise of the open-source community.
What future trends should organizations consider in cybersecurity?
Organizations should explore predictive threat modeling, AI-driven threat detection, and continuous security audits to address evolving threats effectively.
Key Takeaways
- Fragnesia is a Linux kernel flaw allowing root access via page cache manipulation.
- Immediate system updates and access restrictions are critical mitigations.
- AI and machine learning enhance threat detection and response capabilities.
- Community collaboration accelerates vulnerability identification and resolution.
- Predictive threat modeling is essential for future-proofing against emerging threats.
Related Articles
- Unveiling the Microsoft BitLocker USB Backdoor: Risks, Solutions, and Future Implications [2025]
- Understanding Supply Chain Attacks: Lessons from the OpenAI Data Breach [2025]
- Understanding Data Security in the Age of AI: Lessons from a US Bank Security Lapse [2025]
- Cisco's Record Revenue and Layoffs: Navigating Growth and Workforce Restructuring [2025]
- Cisco's Strategic Shift: Embracing AI and Cybersecurity Amid Workforce Reductions [2025]
- Exposing Cyber Intruders: A Deep Dive into Russian Government Hackers Targeting Signal Accounts [2025]
![Understanding the Fragnesia Flaw: How It Threatens Linux Security [2025]](https://tryrunable.com/blog/understanding-the-fragnesia-flaw-how-it-threatens-linux-secu/image-1-1778783648254.jpg)



