Unmasking Spyware: How Fake Android Apps Are Weaponized [2025]
In the ever-evolving landscape of cybersecurity threats, spyware remains one of the most pernicious. Its ability to infiltrate devices and extract sensitive information without users' knowledge makes it a preferred tool for surveillance, both by governments and malicious actors. Recently, another spyware maker was caught distributing fake Android apps designed to snoop on unwitting users. This case highlights the ongoing battle between privacy advocates and those who seek to exploit digital vulnerabilities.
TL; DR
- Rising Threat: Fake Android apps are increasingly used to deploy spyware, posing significant privacy risks.
- Technical Sophistication: Modern spyware can masquerade as legitimate apps, complicating detection.
- User Awareness: Educating users about app permissions and security settings is crucial.
- Developer Responsibility: App stores must enhance vetting processes to curb malicious apps.
- Future Outlook: Expect more advanced spyware techniques as cyber threats evolve.
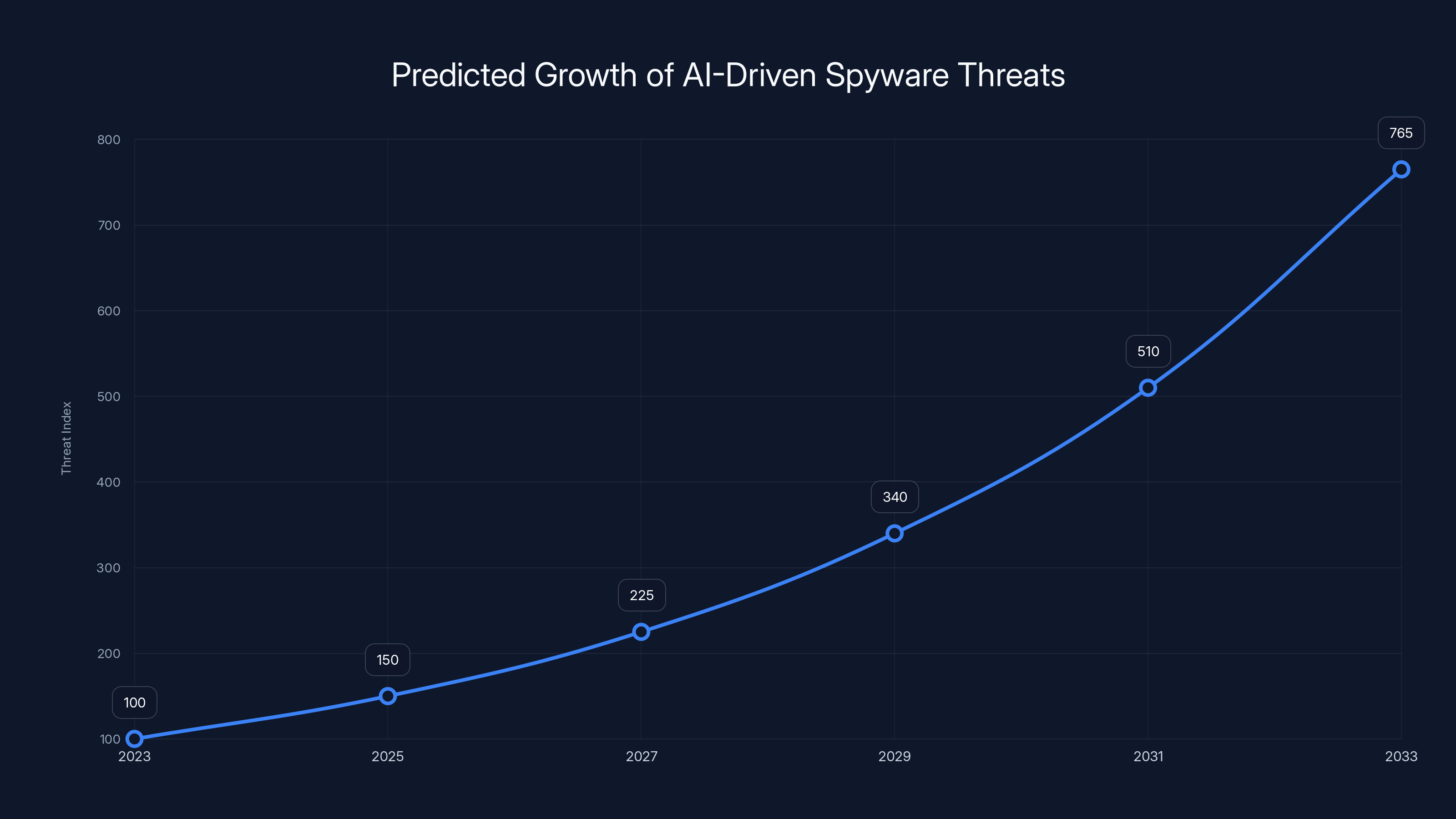
AI-driven spyware threats are projected to increase significantly over the next decade, driven by advancements in technology and the proliferation of connected devices. (Estimated data)
Understanding Spyware and Its Evolution
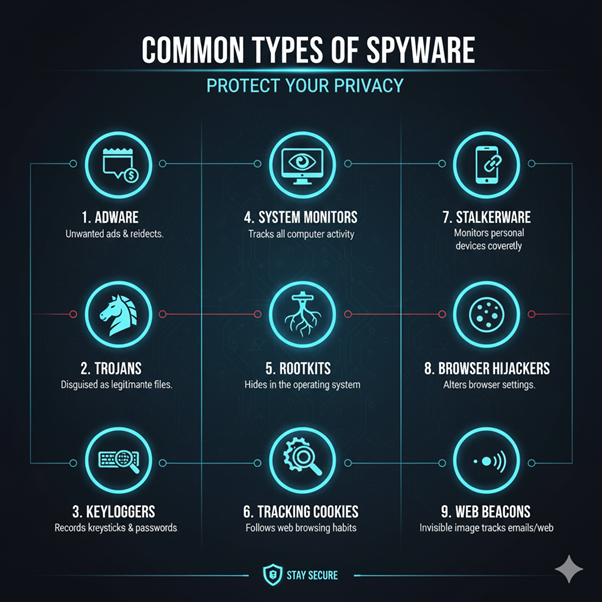
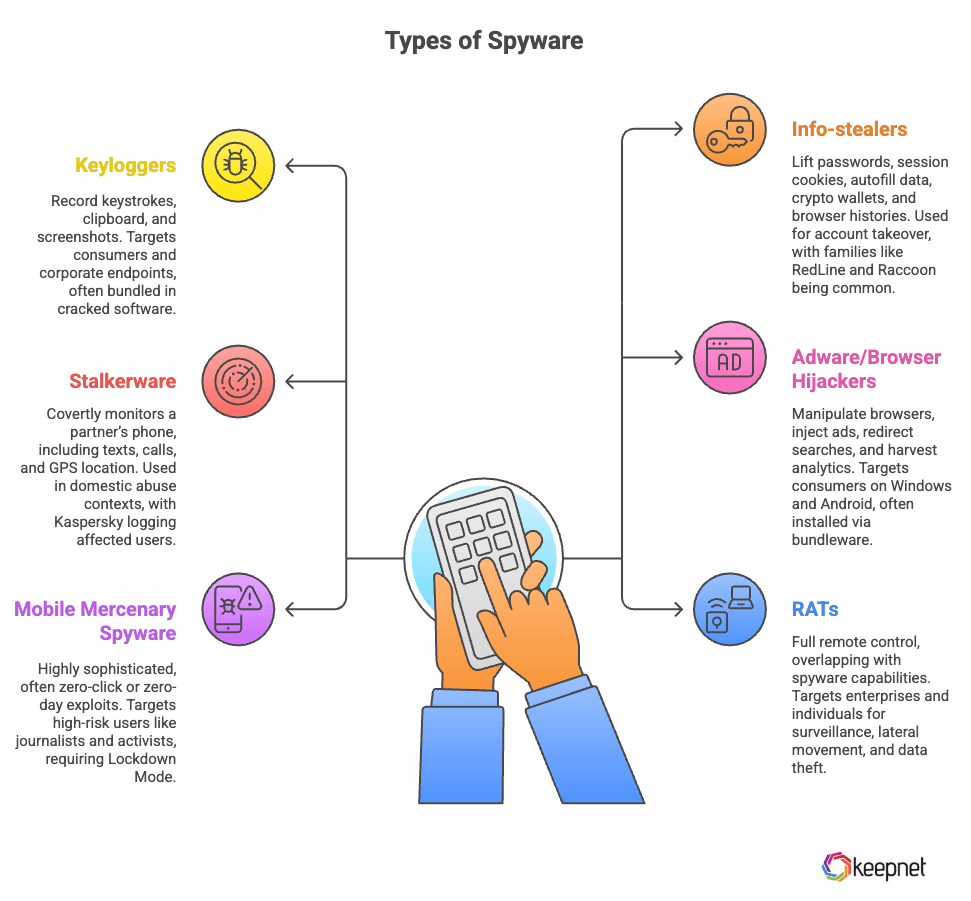
Spyware is a type of malware designed to gather information from a device without the user's consent. Initially, spyware was relatively unsophisticated, often bundled with seemingly harmless software downloads. However, as cybersecurity measures have advanced, so too has spyware.
The Evolution of Spyware
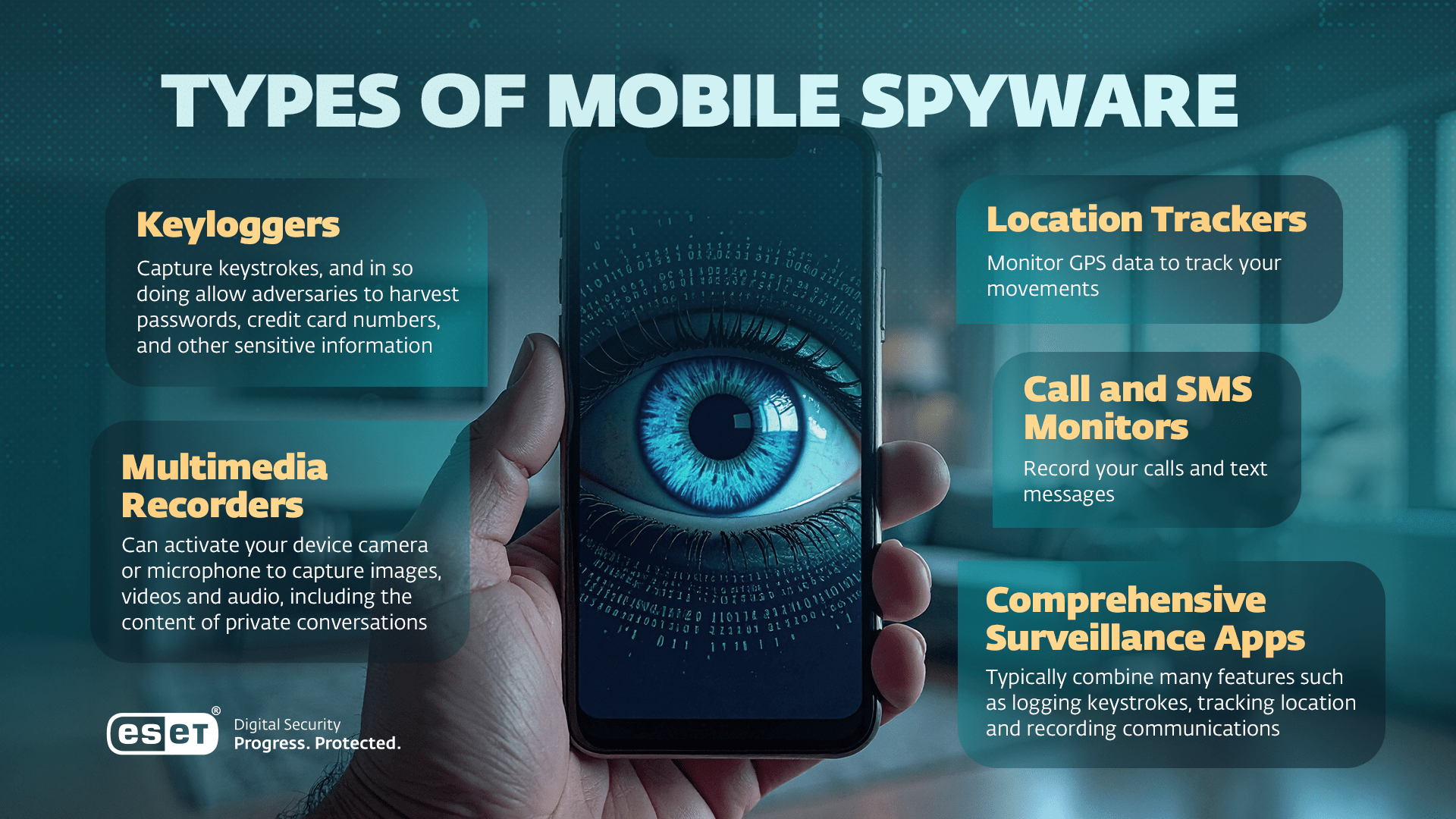
Spyware has evolved from simple keyloggers and adware to complex software capable of accessing GPS data, call logs, and even real-time microphone and camera feeds. The sophistication of modern spyware lies in its ability to remain undetected while extracting valuable data.
- Early Spyware: Focused on tracking online behavior for advertising purposes.
- Advanced Spyware: Now targets sensitive data, including financial and personal information.
- State-Sponsored Spyware: Used by governments for surveillance, often with sophisticated capabilities.
How Spyware Operates
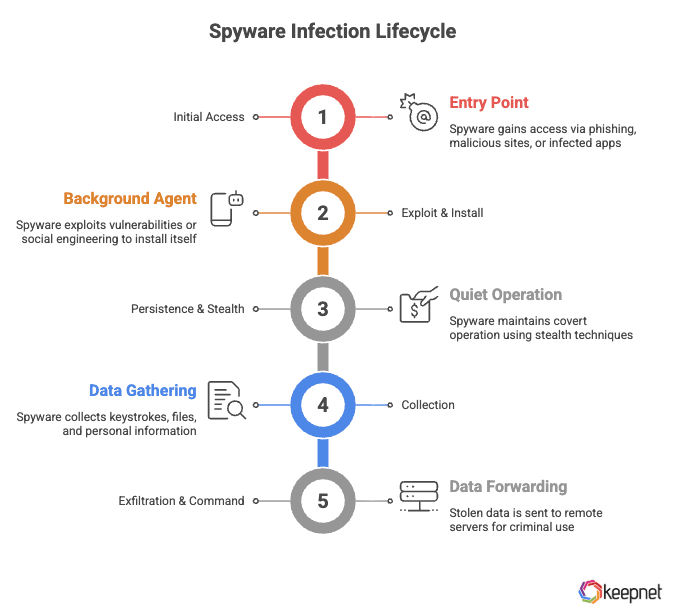
Spyware typically operates by exploiting vulnerabilities in software or through deceptive practices, such as tricking users into downloading malicious apps disguised as legitimate ones.
- Exploitation of Vulnerabilities: Targets unpatched software or uses zero-day exploits.
- Deceptive Practices: Fake apps mimic legitimate ones, luring users into a false sense of security.
- Social Engineering: Manipulates users into granting permissions that enable data access.
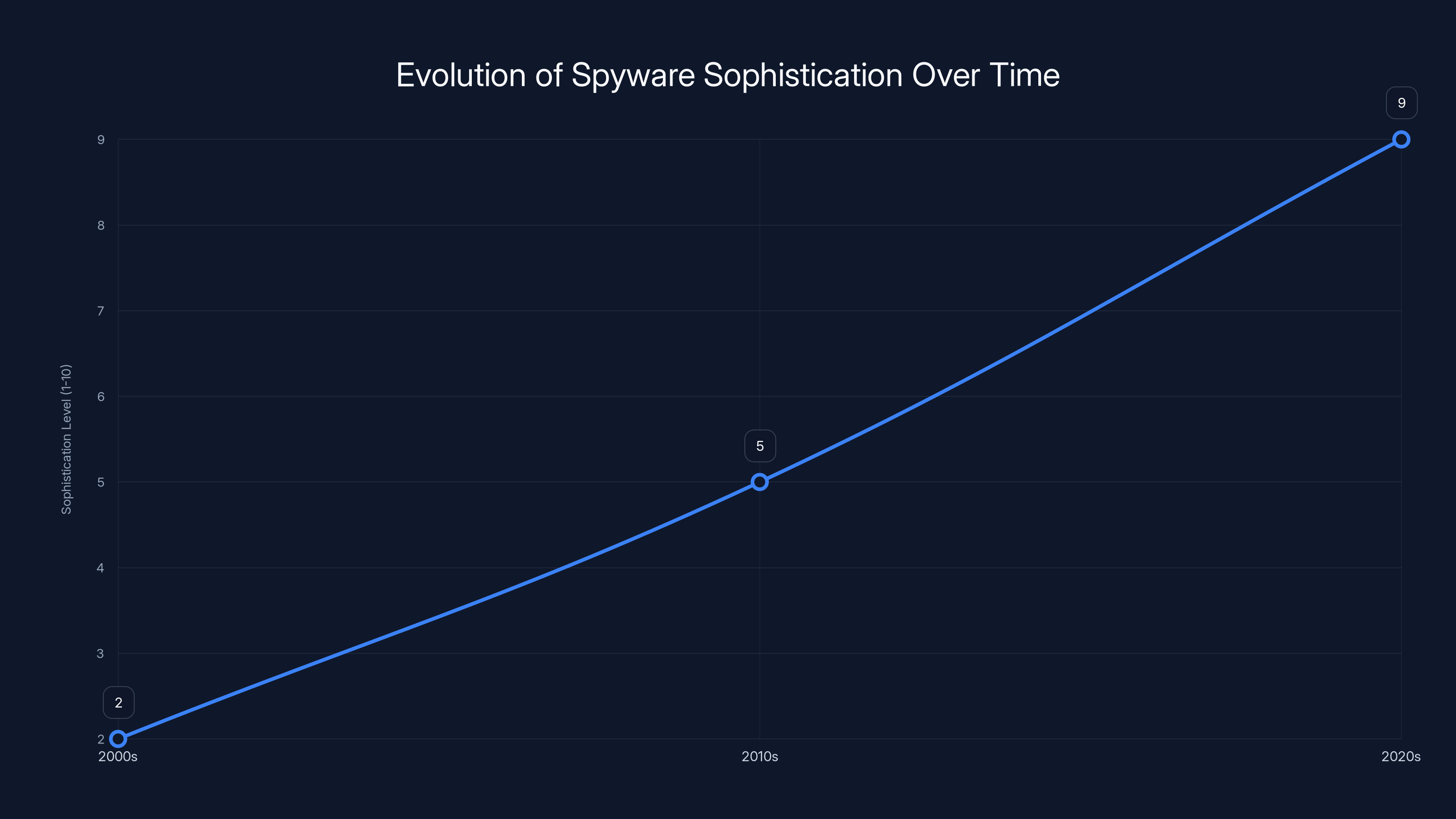
Spyware has evolved significantly, from simple adware in the 2000s to highly sophisticated state-sponsored tools in the 2020s. (Estimated data)
Case Study: The Morpheus Spyware
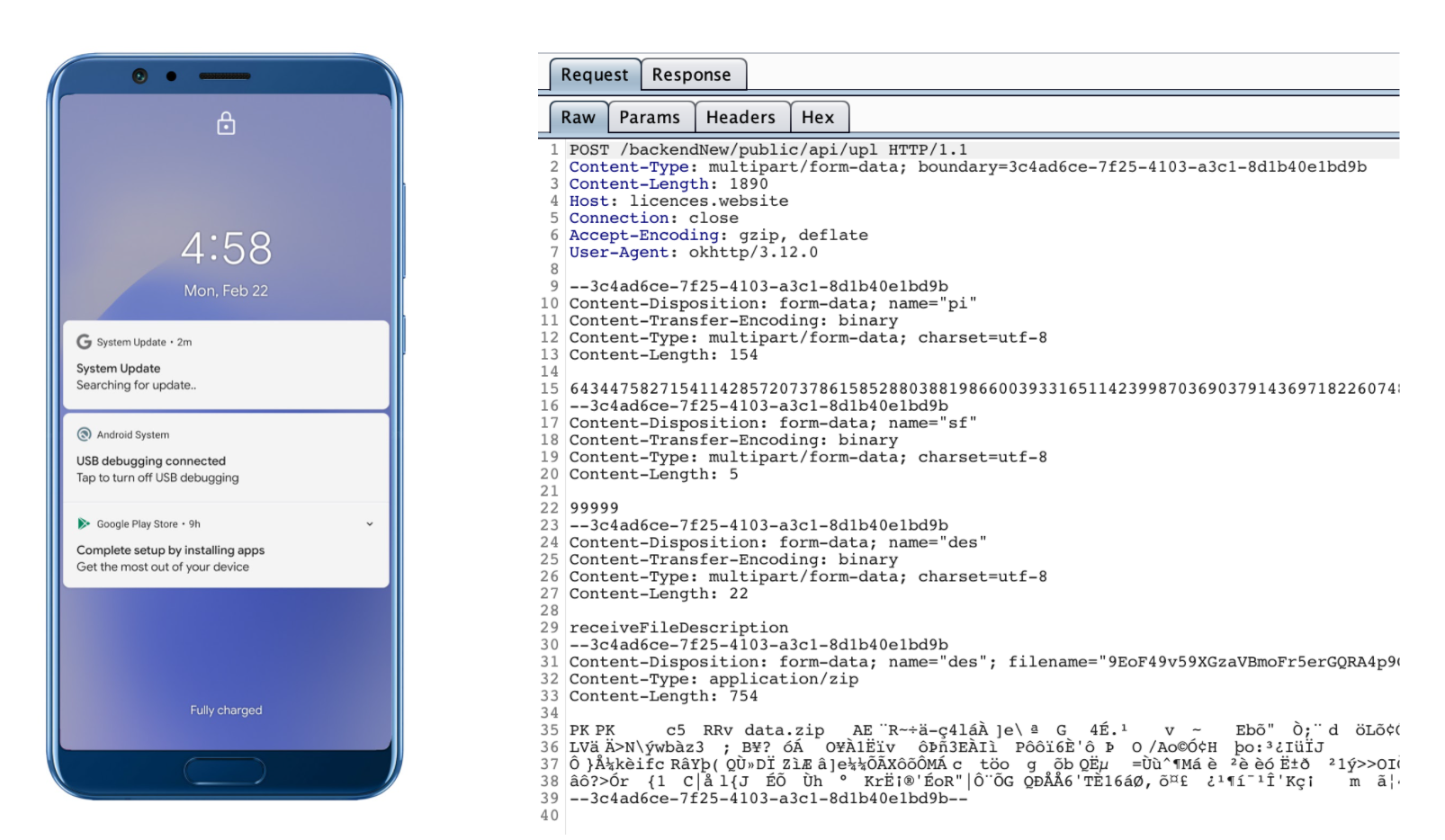
Recently, a report by Osservatorio Nessuno revealed the existence of Morpheus, a spyware masquerading as a phone updating app. This spyware is linked to IPS, an Italian company known for providing lawful interception technology.
How Morpheus Works
Morpheus functions by posing as a legitimate system update app. Once installed, it gains extensive access to the device's data, allowing it to steal sensitive information.
- Installation Vector: Presented as a necessary system update.
- Data Access: Steals contacts, messages, call logs, and more.
- Network Communication: Sends data to remote servers controlled by the attackers.
Implications of Morpheus
The discovery of Morpheus underscores the demand for spyware technology and the lengths to which some entities will go to obtain it. It also highlights the need for robust cybersecurity measures to protect against such threats.
- Privacy Concerns: Potential for misuse by unauthorized entities.
- Legal and Ethical Issues: Challenges in regulating state-sponsored spyware.
- User Education: Importance of vigilance in app downloads and permissions.
Protecting Yourself from Spyware
While spyware continues to evolve, there are steps users can take to protect themselves from these threats.
Best Practices for Users
- Install Apps from Trusted Sources: Only download apps from reputable app stores like Google Play.
- Review App Permissions: Be cautious of apps requesting excessive permissions.
- Keep Software Updated: Regular updates patch vulnerabilities that spyware can exploit.
- Use Security Software: Install reputable antivirus and anti-spyware tools.
- Regular Device Checks: Monitor for unusual activity or unexpected app installations.
Developer and Platform Responsibilities
App developers and platform providers play a crucial role in preventing the distribution of spyware.
- Enhanced Vetting Processes: App stores must improve their review processes to identify and block malicious apps.
- Developer Guidelines: Encourage best practices for app security and privacy.
- User Reporting: Implement mechanisms for users to report suspicious apps easily.
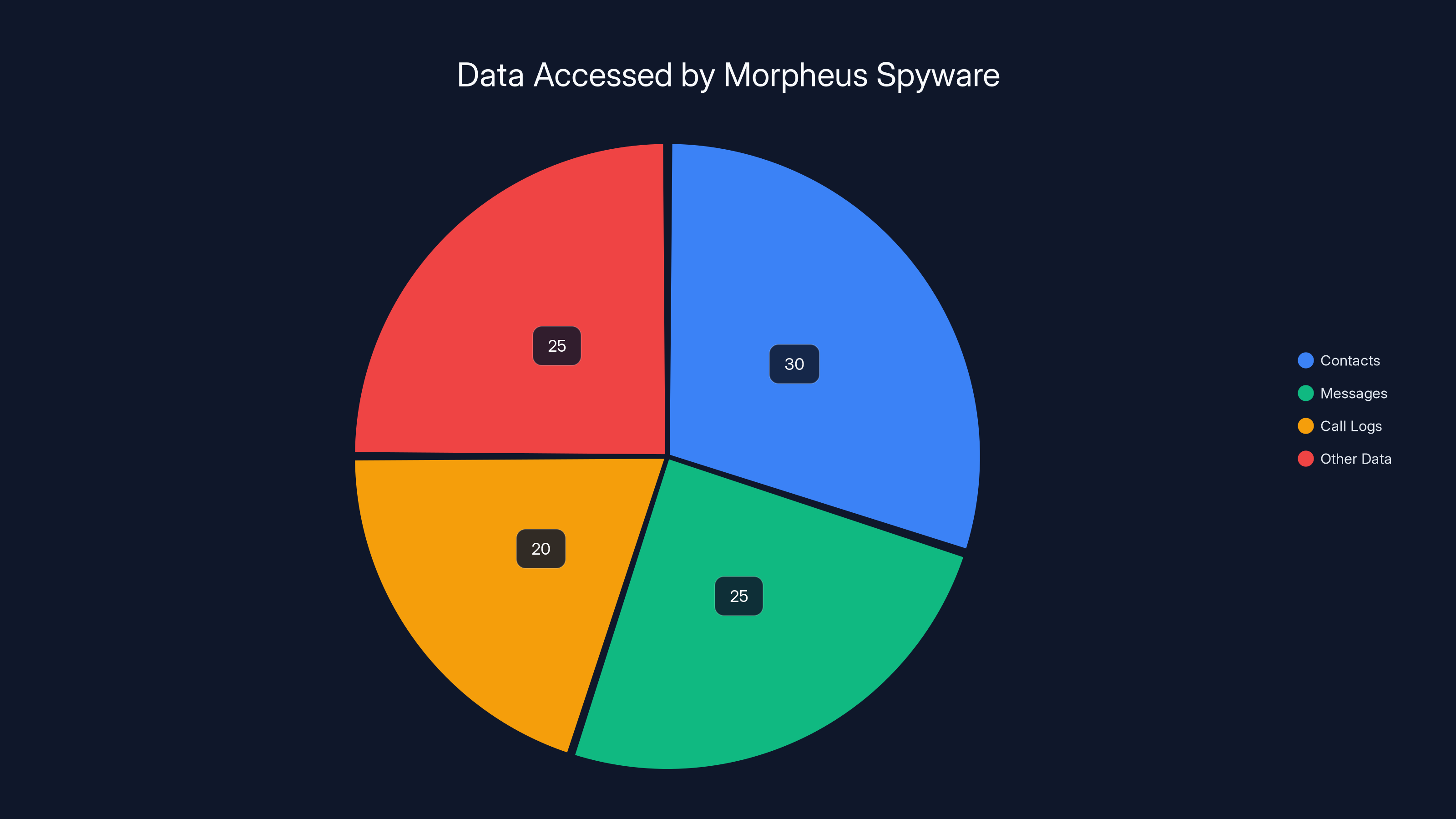
Estimated data shows that Morpheus spyware accesses a variety of data types, with contacts and messages being the most targeted. Estimated data.
The Future of Spyware
As technology advances, so too will the capabilities of spyware. It's essential to anticipate future trends and prepare accordingly.
Emerging Spyware Trends
- AI-Driven Spyware: Leveraging artificial intelligence to evade detection and enhance data collection.
- Cross-Platform Threats: Targeting a broader range of devices, including Io T and wearables.
- More Sophisticated Social Engineering: Advanced tactics to trick even wary users.
Recommendations for the Future
- Increase Investment in Cybersecurity: Both public and private sectors must prioritize funding for cybersecurity research and development.
- Strengthen International Cooperation: Governments should collaborate to establish norms and regulations governing spyware use.
- Educate the Public: Ongoing awareness campaigns to keep users informed about emerging threats.
Conclusion
The battle against spyware is far from over. As malicious actors continue to innovate, it's vital for users, developers, and governments to work together to protect privacy and security in the digital age. By staying informed and implementing best practices, we can mitigate the risks posed by spyware and safeguard our digital lives.
FAQ
What is spyware?
Spyware is malicious software designed to gather information from a device without the user's consent, often used for surveillance or data theft.
How can I protect my device from spyware?
To protect your device, download apps only from trusted sources, review app permissions carefully, keep your software updated, and use reputable security software.
Why is spyware a significant threat?
Spyware poses a significant threat because it can operate undetected, accessing sensitive personal and financial information which can be exploited by malicious actors.
What are the legal implications of spyware?
The use of spyware raises legal and ethical issues, particularly regarding privacy and unauthorized surveillance. Laws vary by country, but unauthorized use is often illegal.
How does AI influence spyware development?
AI enables more sophisticated spyware by improving its ability to evade detection, automate data collection, and adapt to security measures.
Can spyware affect Io T devices?
Yes, spyware can target Io T devices, exploiting their connectivity to gather data or launch attacks on other networks.
What should developers do to prevent spyware dissemination?
Developers should adhere to security best practices, conduct thorough code reviews, and collaborate with app stores to detect and eliminate malicious apps.
Key Takeaways
- Increasing sophistication of spyware posing as legitimate apps.
- Importance of user vigilance and security best practices.
- Role of AI in evolving spyware threats.
- Need for improved app vetting processes by developers.
- Growing collaboration between international entities for cybersecurity.
- Continuous education and awareness campaigns for users.
Related Articles
- Anthropic’s Mythos Breach: Lessons Learned and Future Implications [2025]
- Unveiling the Precursor: The Hidden Malware Before Stuxnet [2025]
- Vercel's Security Incident: A Deep Dive into Compromised Accounts [2025]
- Navigating Privacy: The Implications of the New Republican Privacy Bill [2025]
- Balancing Trust and Control to Unlock AI-Powered Networking [2025]
- AI is Redefining Product Discovery: Structured Data and Trust are Critical for Visibility [2025]
![Unmasking Spyware: How Fake Android Apps Are Weaponized [2025]](https://tryrunable.com/blog/unmasking-spyware-how-fake-android-apps-are-weaponized-2025/image-1-1777041248559.jpg)



