Vercel's Security Incident: A Deep Dive into Compromised Accounts [2025]
In the digital age, security breaches are an inevitable part of the landscape. An incident involving Vercel, a popular platform for frontend development, has recently highlighted the vulnerabilities that can exist even in well-protected systems. This article explores the intricacies of Vercel's security breach, delves into the technical details of the compromise, and outlines best practices for safeguarding digital assets.
TL; DR
- Vercel's security breach revealed more compromised accounts than initially reported, emphasizing the need for robust security measures. According to Bleeping Computer, the breach was more extensive than initially thought.
- Technical vulnerabilities were exploited, showcasing the importance of continuous monitoring and patch management. As detailed by Trend Micro, the vulnerabilities were linked to OAuth supply chain issues.
- Proactive measures like multi-factor authentication and regular audits are crucial in preventing such incidents. Industrial Cyber highlights the importance of these measures in reducing breach costs.
- Future trends suggest an increase in automated security solutions and AI-driven threat detection. McKinsey discusses the role of AI in future cybersecurity strategies.
- Collaboration between cybersecurity experts and the developer community is essential to enhance security protocols. CyberScoop emphasizes the need for such collaboration in response to the breach.

Multi-Factor Authentication (MFA) is rated as the most effective strategy, significantly reducing unauthorized access risks. Estimated data.
Understanding the Vercel Breach
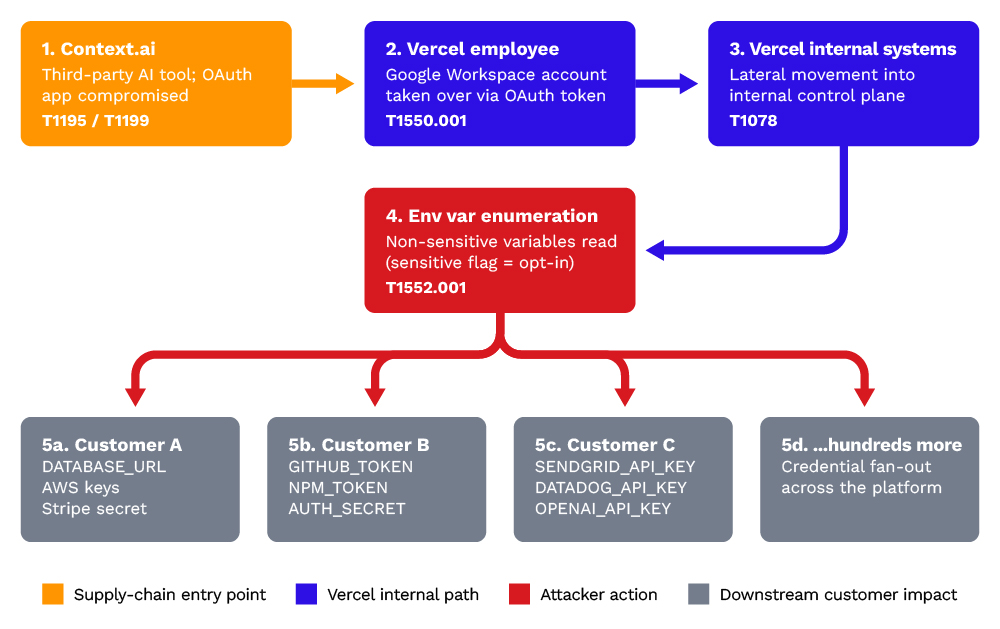
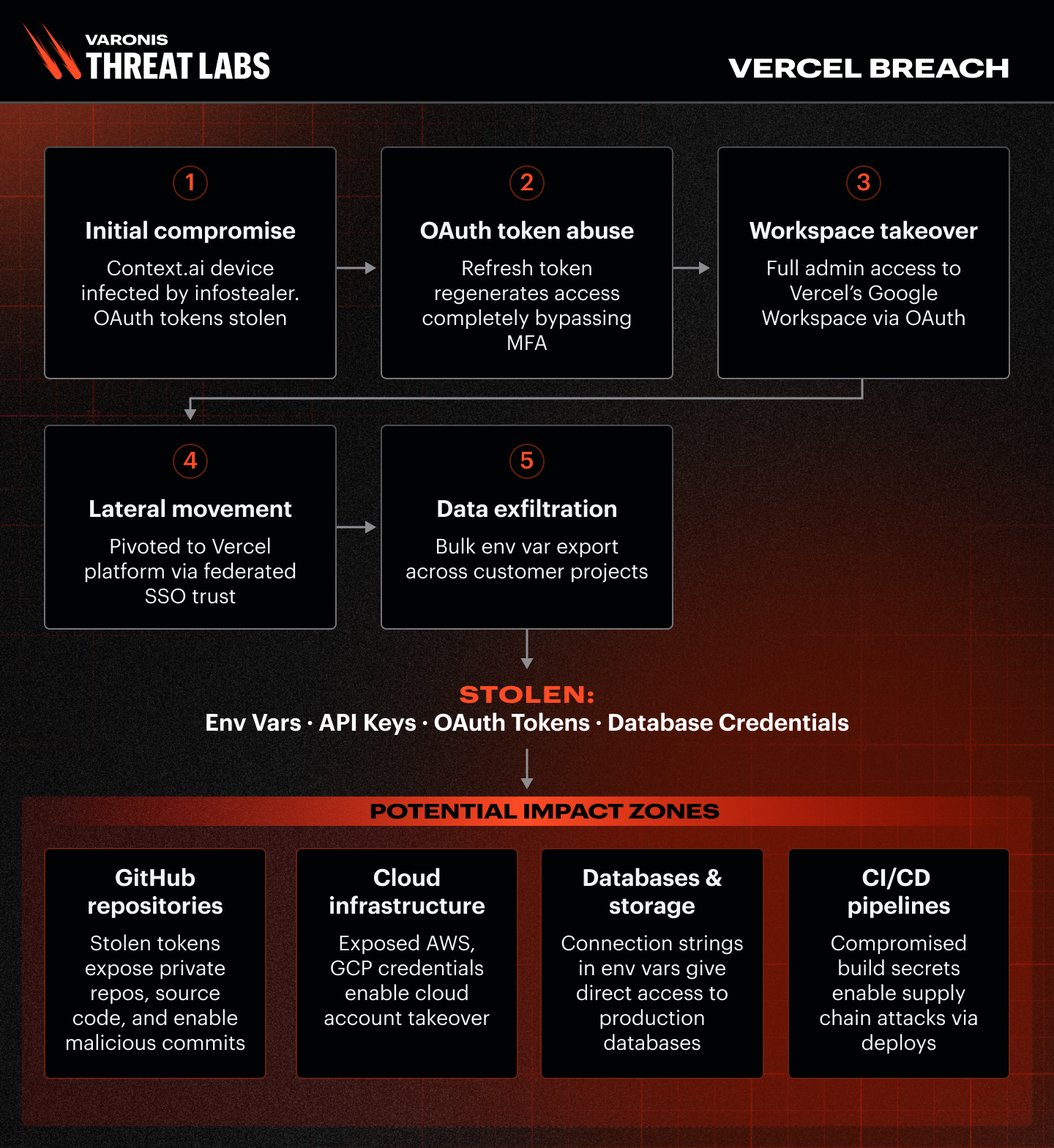
When Vercel expanded its investigation into a security incident, it unearthed a more extensive network of compromised accounts than initially anticipated. The breach highlighted several core vulnerabilities and underscored the importance of a comprehensive security approach. As reported by The Hacker News, the breach was tied to a Context.ai hack.
Vercel, known for streamlining the development of web applications, found that the initial breach was linked to an infected Context.ai account, which was compromised by a malware known as Lumma Stealer. This malware, notorious for its ability to siphon sensitive data, served as the entry point for further breaches, as detailed by CyberNews.
The Mechanics of the Breach
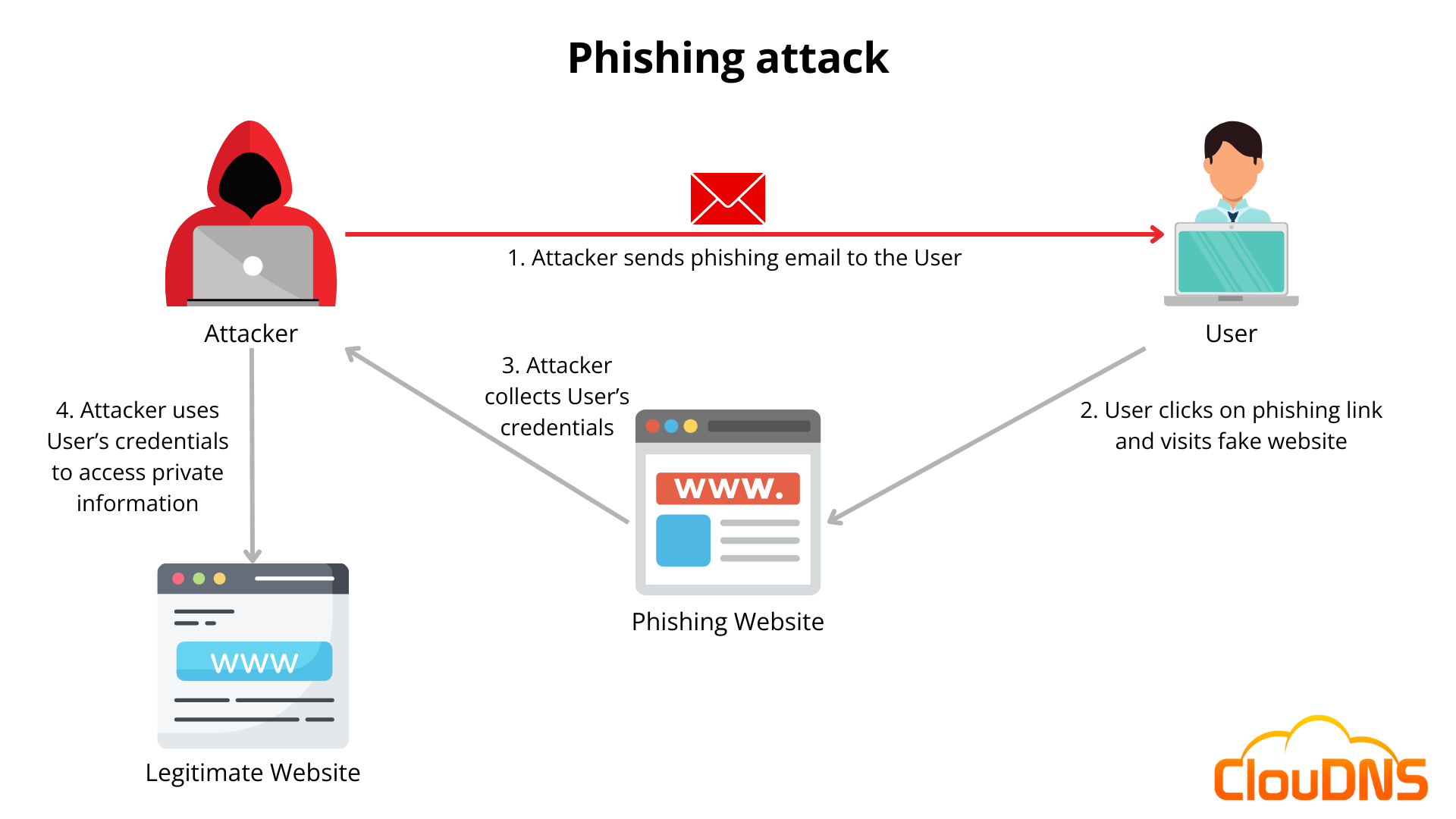
The breach's expansion stemmed from a combination of social engineering tactics and exploited software vulnerabilities. Attackers often use phishing emails to trick users into revealing credentials. In this case, the Lumma Stealer malware was likely delivered through such a vector, allowing unauthorized access to sensitive information, as noted by InfoSecurity Magazine.
Technical Analysis:
- Malware Delivery: Typically through phishing or drive-by downloads.
- Data Exfiltration: Lumma Stealer collects data such as login credentials, personal information, and browser histories.
- Propagation: Once inside, the malware can spread laterally, compromising additional accounts.
The Scope of Compromise
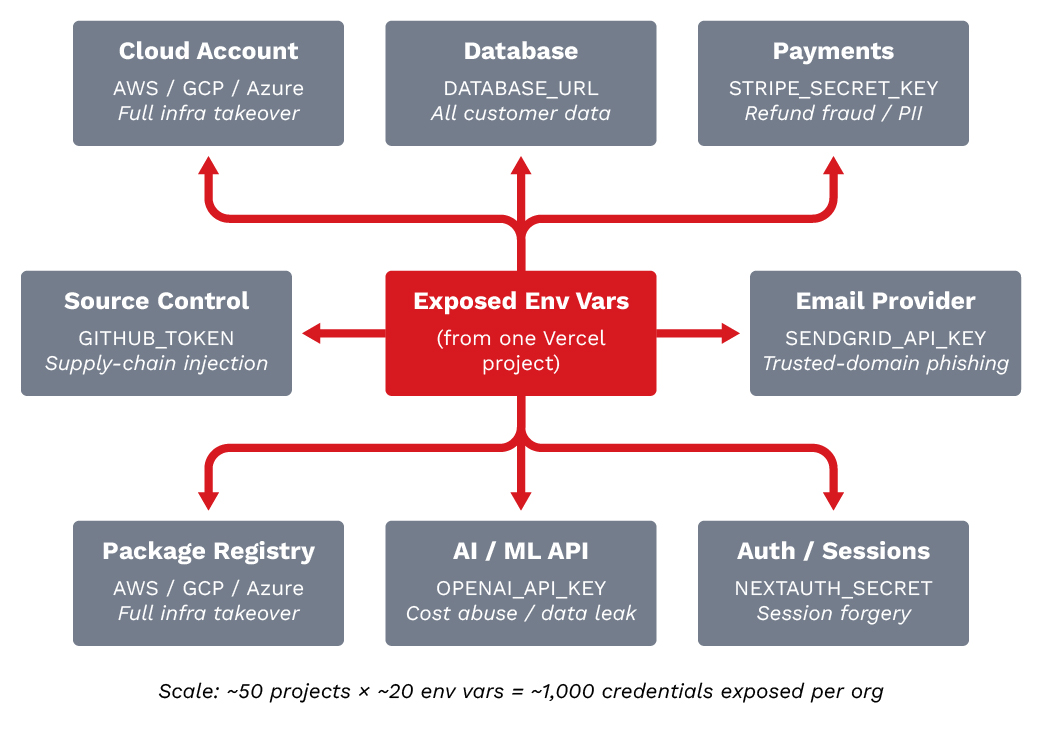
Initial assessments underestimated the breach's reach. However, further investigation revealed that multiple accounts were indeed compromised, each potentially exposing sensitive data. According to ITWeb, the breach exposed a significant portion of the developer community.
Commonly Exposed Data:
- Usernames and passwords
- Email addresses
- API keys and tokens
Implications:
- Data Sensitivity: Compromised accounts can lead to data leaks, financial loss, and reputational damage.
- Systemic Risk: Each compromised account potentially serves as a bridge to others, exacerbating the breach's impact.
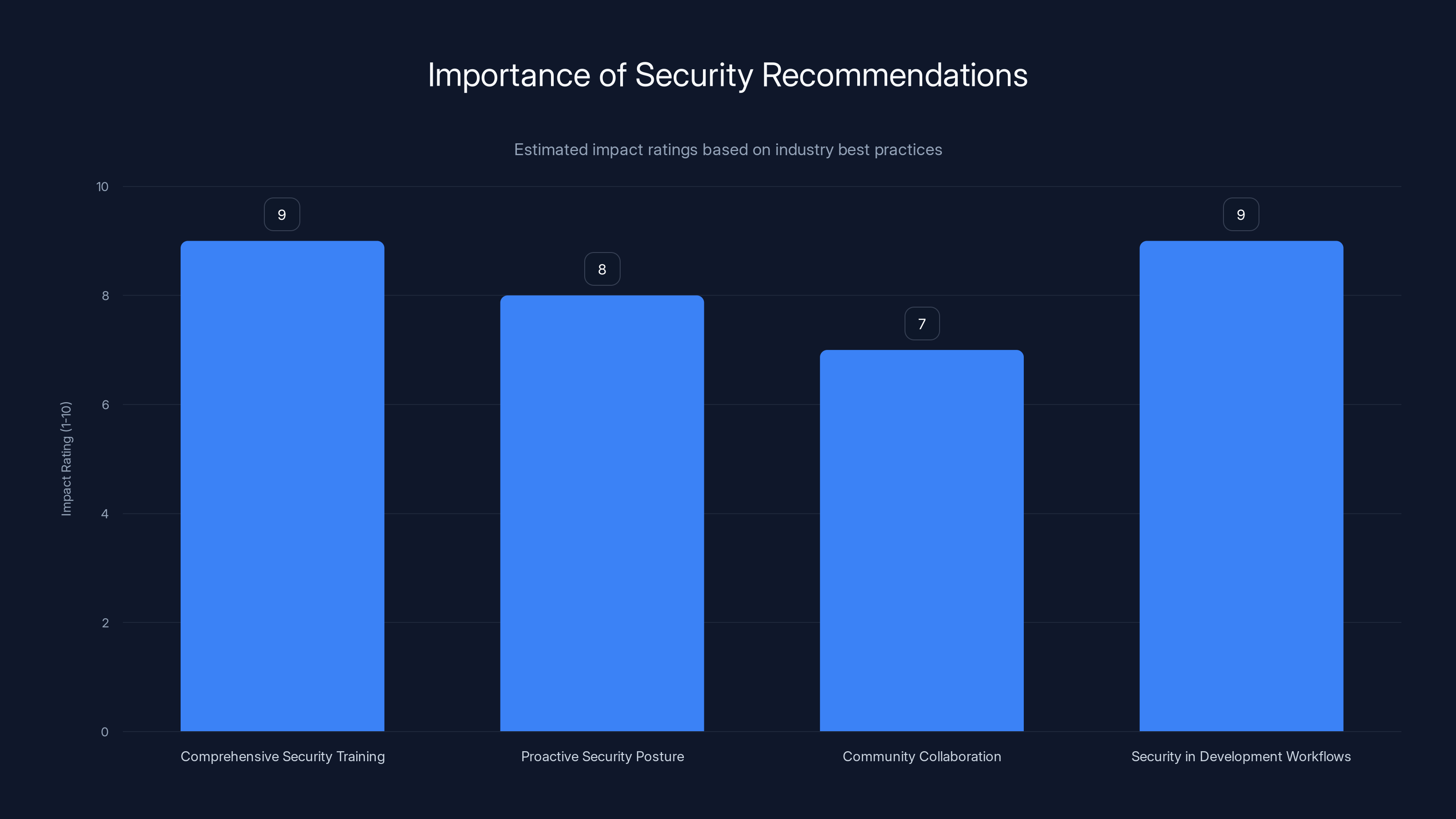
Investing in comprehensive security training and integrating security into development workflows are rated highest in impact. (Estimated data)
Mitigation Strategies
In the wake of such incidents, organizations must adopt a multi-faceted approach to security. Here are some recommended strategies:
Strengthening Authentication Mechanisms
Multi-Factor Authentication (MFA): MFA adds an extra layer of security by requiring users to provide two or more verification factors. This significantly reduces the risk of unauthorized access, as highlighted by Industrial Cyber.
Implementation Tips:
- Adopt MFA across all platforms to ensure comprehensive coverage.
- Educate users on its importance and ease of use.
- Integrate with existing authentication systems for seamless operation.
[CODE EXAMPLE: Implementing MFA with Node.js and Express]
javascriptconst express = require('express');
const speakeasy = require('speakeasy');
const qrcode = require('qrcode');
const app = express();
app.get('/generate', (req, res) => {
const secret = speakeasy.generateSecret({ length: 20 });
qrcode.toDataURL(secret.otpauth_url, (err, data_url) => {
res.send({ secret: secret.base32, qr: data_url });
});
});
Regular Security Audits
Conducting regular security audits helps identify vulnerabilities before they can be exploited. These audits should encompass network infrastructure, application code, and user access controls. As noted by CyberScoop, regular audits are crucial in maintaining security integrity.
Audit Checklist:
- Review access logs for unauthorized attempts.
- Conduct penetration testing to simulate attack scenarios.
- Update security policies based on audit findings.
Common Pitfalls and Solutions
Despite the best intentions, security implementations often fall short. Here are some pitfalls to avoid:
Over-reliance on Single Security Measures
Relying solely on firewalls or antivirus software can create a false sense of security. A layered approach is essential. As emphasized by Trend Micro, a multi-layered defense strategy is vital.
Solution: Implement a combination of perimeter defenses, endpoint security, and user education to create a robust defense-in-depth strategy.
Neglecting User Education
Users are often the weakest link in security. Without proper training, they may fall prey to phishing attacks or poor password practices. InfoSecurity Magazine highlights the importance of ongoing user education.
Solution: Conduct regular training sessions and provide resources on security best practices. Encourage the use of password managers to strengthen credentials.
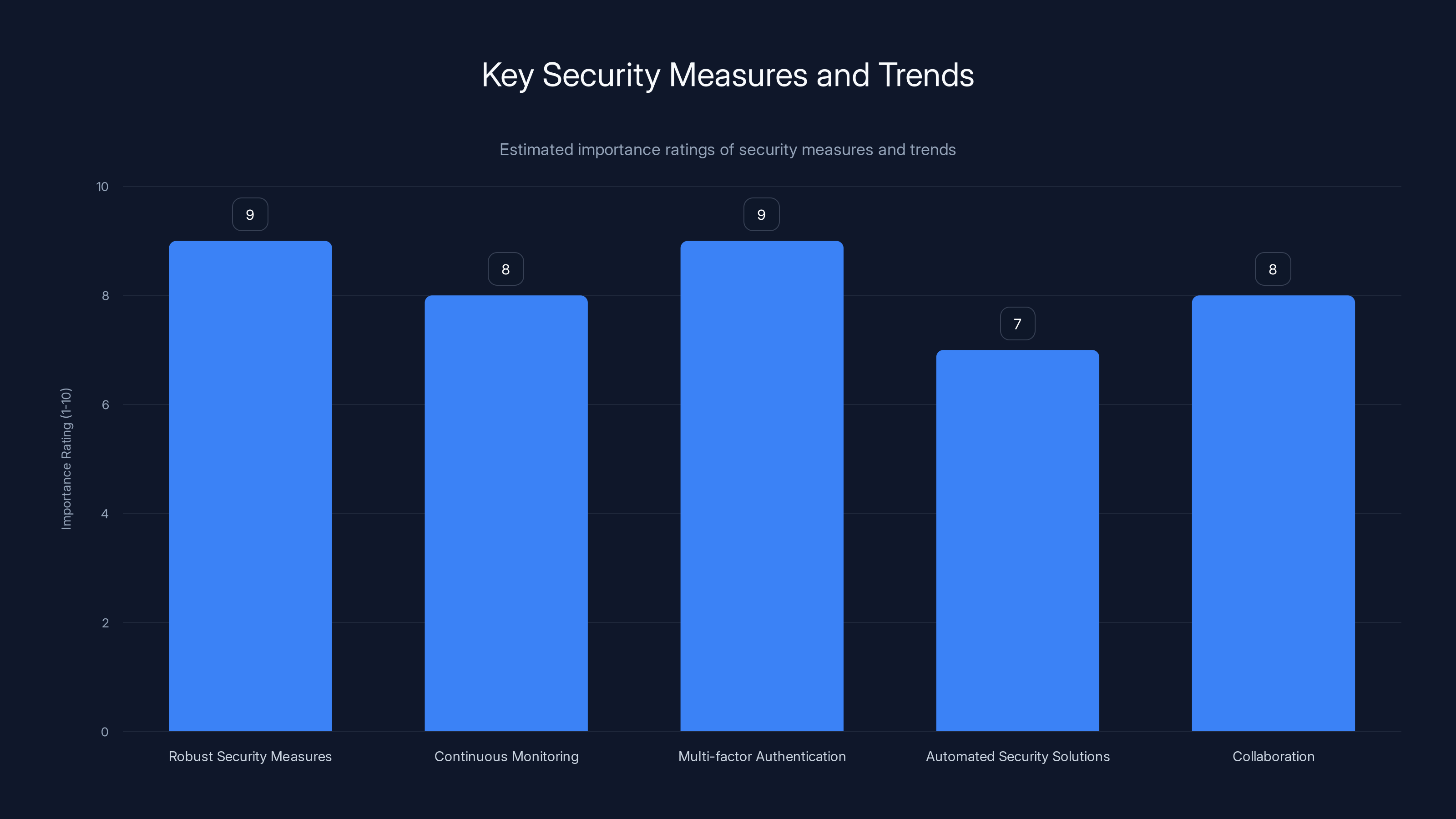
Proactive security measures like multi-factor authentication and collaboration are rated highly for their importance in preventing breaches. Estimated data.
Future Trends in Security
As threats evolve, so too must the strategies to combat them. Here are some trends to watch:
AI and Machine Learning in Threat Detection
AI and machine learning algorithms are increasingly used to detect anomalies and predict potential threats before they materialize. McKinsey discusses the transformative potential of AI in cybersecurity.
Potential Benefits:
- Real-time monitoring of network traffic to identify unusual patterns.
- Automated response systems that can neutralize threats without human intervention.
Zero Trust Architecture
The zero trust model assumes that threats could be inside or outside the network. It requires verification at every step of data access. CyberScoop highlights the importance of adopting a zero trust approach.
Key Principles:
- Verify explicitly: Use all available data points to ensure access is granted only to authorized users.
- Assume breach: Design systems with the assumption that breaches will occur.

Industry Recommendations
Based on the lessons learned from the Vercel incident, here are some recommendations for organizations:
-
Invest in Comprehensive Security Training: Regular, up-to-date training programs for employees to recognize and respond to security threats.
-
Adopt a Proactive Security Posture: Utilize tools that provide real-time insights into security postures and potential vulnerabilities.
-
Foster Community Collaboration: Engage with cybersecurity communities to share knowledge and strategies for threat mitigation.
-
Integrate Security into Development Workflows: Implement security checks into CI/CD pipelines to catch vulnerabilities early in the development process.
Conclusion
The Vercel security breach serves as a stark reminder of the ever-present threats in the digital landscape. By understanding the mechanics of such breaches and adopting a proactive, well-rounded security approach, organizations can significantly reduce the risk of similar incidents. As technology evolves, so too must our strategies to protect valuable digital assets.
FAQ
What led to the Vercel security breach?
The breach was initiated through a compromised Context.ai account infected with the Lumma Stealer malware, which exploited software vulnerabilities and social engineering tactics, as reported by The Hacker News.
How can organizations prevent similar breaches?
Organizations should implement multi-factor authentication, conduct regular security audits, and provide comprehensive security training to employees, as recommended by Industrial Cyber.
What is the role of AI in enhancing security?
AI can detect anomalies in real-time, predict potential threats, and automate responses to neutralize threats without human intervention, as discussed by McKinsey.
Why is user education important in cybersecurity?
User education is crucial as users are often the weakest link in security. Educating them on best practices reduces the risk of falling prey to phishing and other attacks, as noted by InfoSecurity Magazine.
What is Zero Trust Architecture?
Zero Trust Architecture is a security model that requires verification at every step of data access, assuming that threats could be both inside and outside the network, as highlighted by CyberScoop.
How do security audits help in preventing breaches?
Security audits help identify vulnerabilities before they can be exploited by reviewing access logs, conducting penetration testing, and updating security policies, as recommended by CyberScoop.
What are the common pitfalls in security implementations?
Common pitfalls include over-reliance on single security measures and neglecting user education, both of which can create vulnerabilities in an organization's security posture, as noted by Trend Micro.
Key Takeaways
- Vercel's breach revealed more accounts compromised than initially thought, as reported by Bleeping Computer.
- Lumma Stealer malware was the key vector used in the breach, according to CyberNews.
- Implementing MFA is crucial in safeguarding against unauthorized access, as highlighted by Industrial Cyber.
- Regular security audits can prevent potential vulnerabilities, as recommended by CyberScoop.
- AI and machine learning are critical in future threat detection, as discussed by McKinsey.
Related Articles
- France's Identity Management Agency Faces Data Breach: Implications and Next Steps [2025]
- Understanding the Vercel Data Breach: Implications, Security Best Practices, and Future Directions [2025]
- Why Passkeys Are the Future of Authentication [2025]
- The Hidden Risks of AI-Generated Passwords [2025]
- How AI Tools Empower North Korean Hackers to Steal Millions [2025]
- The Silent Legacy of FTP Servers: Still Running and Still Vital [2025]
![Vercel's Security Incident: A Deep Dive into Compromised Accounts [2025]](https://tryrunable.com/blog/vercel-s-security-incident-a-deep-dive-into-compromised-acco/image-1-1776962302184.jpg)



