Unveiling the Precursor: The Hidden Malware Before Stuxnet [2025]
In the realm of cybersecurity, the discovery of historical malware can provide invaluable insights into the evolution of state-sponsored cyber operations. This article delves into the recently deciphered malware that predates the infamous Stuxnet, offering a comprehensive analysis of its technicalities, implications, and future trends.
TL; DR
- Early Malware Discovery: A newly uncovered malware predates Stuxnet, revealing advanced capabilities.
- Historical Context: This malware offers insights into early cyber espionage techniques used in state-sponsored attacks.
- Technical Features: Advanced techniques for undetectable sabotage in industrial systems.
- Implementation Challenges: Lessons learned from past cyber operations to enhance current cybersecurity measures.
- Future Cybersecurity Trends: The need for robust defenses against sophisticated malware threats.
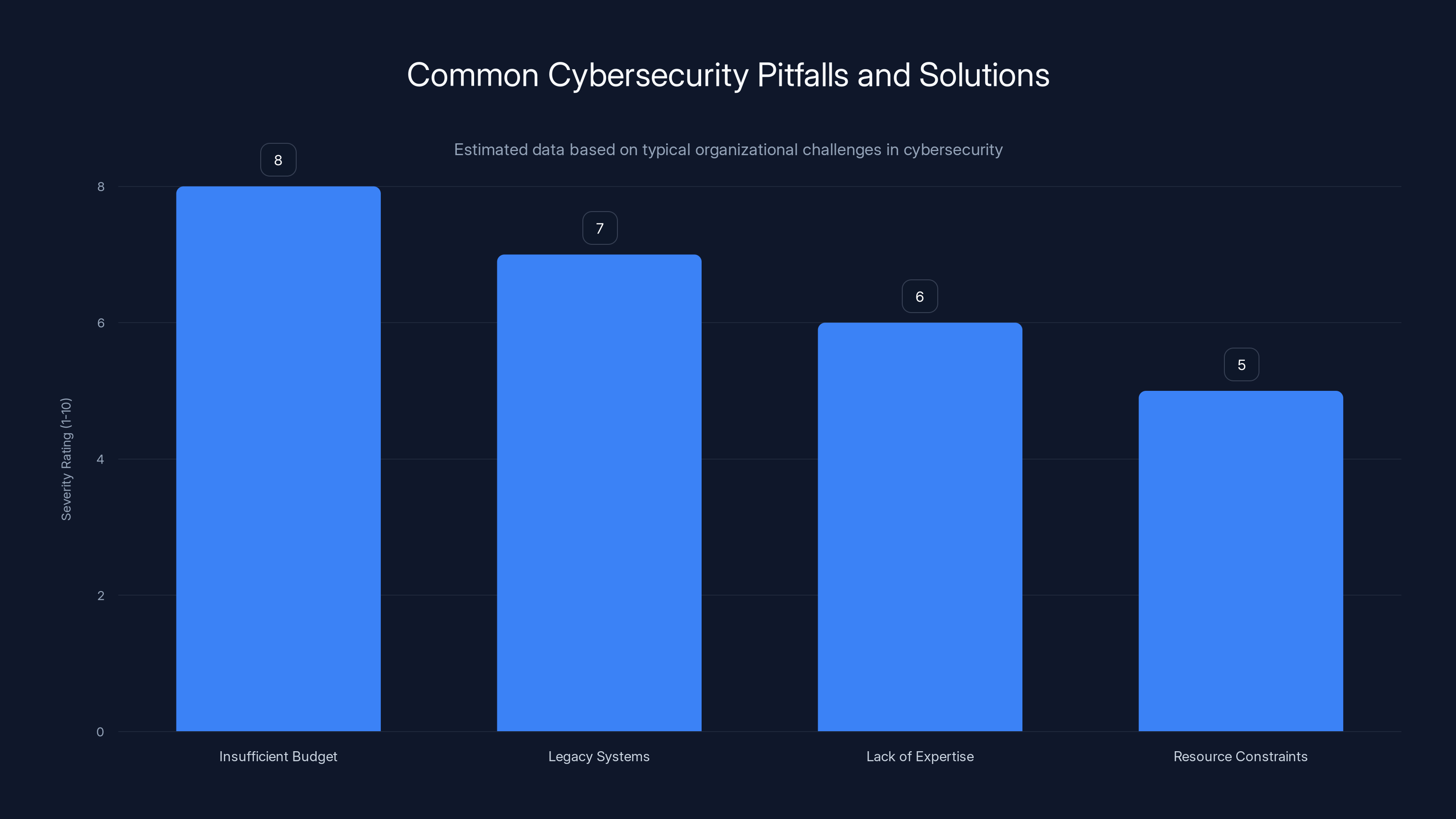
Organizations face various cybersecurity challenges, with insufficient budget and legacy systems being the most severe. Estimated data.
The History of Cyber Espionage
The Rise of Cyber Sabotage
The landscape of cyber sabotage has evolved significantly over the past decades. What started as isolated incidents of digital vandalism has now transformed into sophisticated state-sponsored attacks aimed at crippling national infrastructures. The discovery of a malware predating Stuxnet marks a crucial point in understanding this evolution, as detailed by Wired.
Stuxnet, known for targeting Iran's nuclear program, set a precedent in how malware could be used to achieve covert sabotage. However, this newly discovered malware suggests that similar operations may have been in place even earlier, as discussed in War on the Rocks.
The Birth of Sabotage Malware
The late 1990s saw the emergence of the first known sabotage malware, which aimed to interfere with industrial processes without detection. Unlike the crude "wiper" attacks that erased data, this malware was designed to alter operational parameters subtly, causing physical damage over time.
Such malware targeted SCADA systems (Supervisory Control and Data Acquisition), which are critical for controlling industrial processes. By manipulating these systems, attackers could cause physical disruptions while remaining undetected for extended periods, as noted by CSIS.

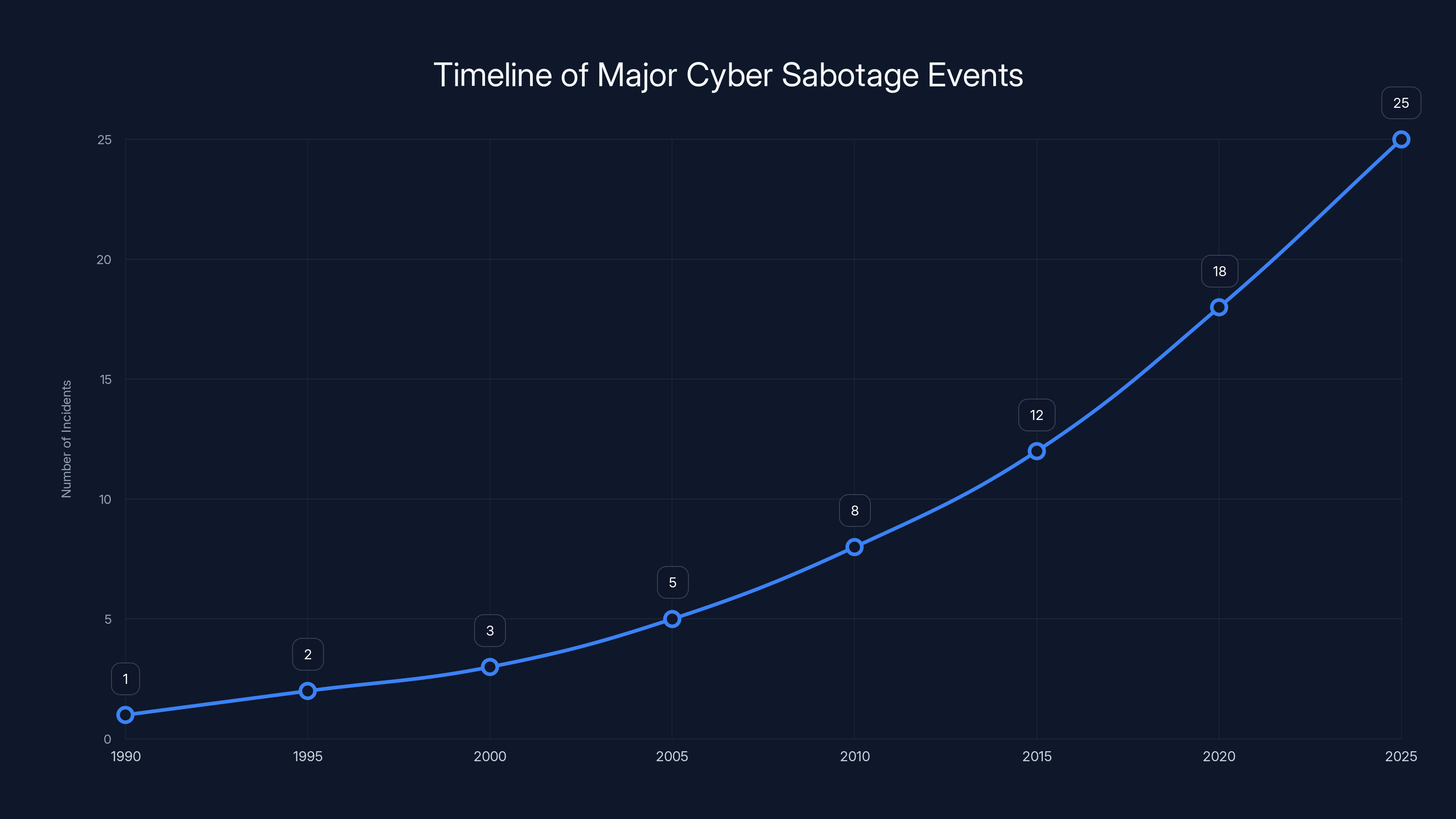
The timeline illustrates the increasing frequency of major cyber sabotage incidents over the years, highlighting the shift from isolated attacks to sophisticated operations. Estimated data.
Technical Analysis of the Newly Discovered Malware
Architecture and Design
This early malware was sophisticated for its time, featuring modular architecture allowing for easy updates and modifications. The design included several components:
- Payload Delivery: Utilized phishing emails and infected USB drives as initial vectors.
- Command and Control (C2): Established a covert channel to receive instructions from the attackers.
- Data Exfiltration: Collected sensitive information to aid in further attacks, as explained by ABC7 News.
Stealth Techniques
The malware employed advanced stealth techniques to avoid detection:
- Code Obfuscation: Used to disguise the malicious code, making it harder to analyze.
- Rootkit Capabilities: Granted the malware deep access to the host system, allowing it to hide its presence.
- Environmental Awareness: Detected if it was running in a virtual environment or sandbox, altering its behavior to avoid analysis, as highlighted by Industrial Cyber.
Targeted Systems
Primarily aimed at industrial control systems, the malware targeted software used in nuclear facilities and other critical infrastructure. By altering control parameters, it could cause machinery to malfunction, leading to significant damage, as reported by MSN.
Real-World Impact
While the full extent of this malware's deployment remains unknown, its capabilities suggest it may have been used in high-stakes espionage against national infrastructure, potentially targeting Iran's nuclear facilities even before Stuxnet, as noted by BitSight.

Practical Implementation Guides
Enhancing Cyber Defense
Given the sophistication of early malware, modern cybersecurity measures must evolve to address similar threats. Here are some practices for bolstering defenses:
- Regular System Audits: Conduct thorough audits of industrial systems to identify vulnerabilities.
- Network Segmentation: Isolate critical systems from general IT networks to limit exposure, as recommended by CXO Digital Pulse.
- Intrusion Detection Systems (IDS): Deploy IDS to monitor for suspicious activity within ICS networks.
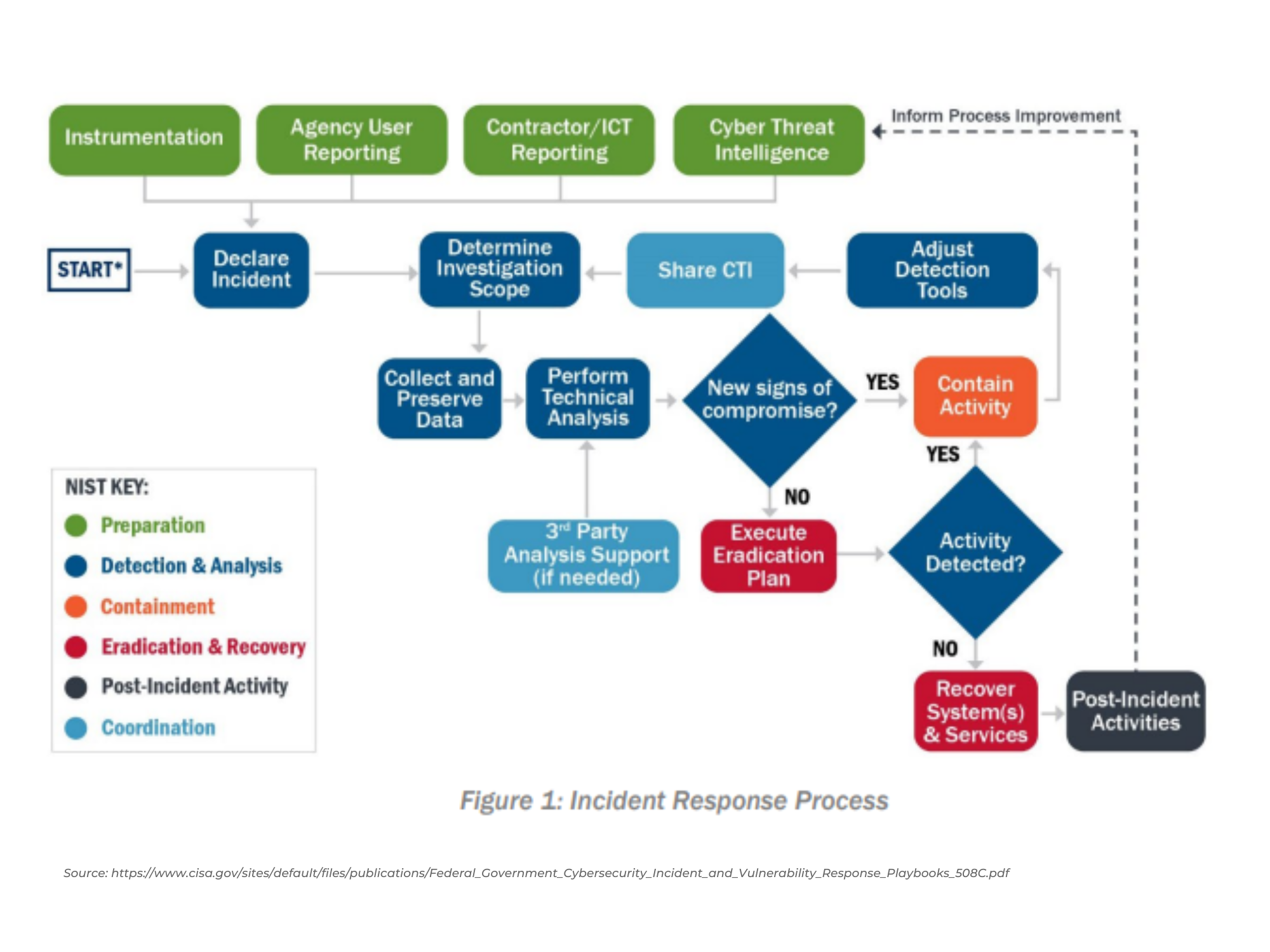
Incident Response Strategies
A robust incident response plan is crucial for mitigating the impact of a cyber attack:
- Preparation: Develop comprehensive response protocols and conduct regular drills.
- Detection and Analysis: Implement real-time monitoring to detect anomalies quickly.
- Containment and Eradication: Isolate affected systems and remove the malicious code, as detailed by Infosecurity Magazine.
Common Pitfalls and Solutions
While implementing cybersecurity measures, organizations often face challenges such as resource constraints and lack of expertise. Here are solutions to common pitfalls:
-
Pitfall: Insufficient budget for cybersecurity.
- Solution: Prioritize investments in critical areas, such as IDS and staff training.
-
Pitfall: Complexity of managing legacy systems.
- Solution: Gradually upgrade systems and integrate modern security solutions, as suggested by Nature.

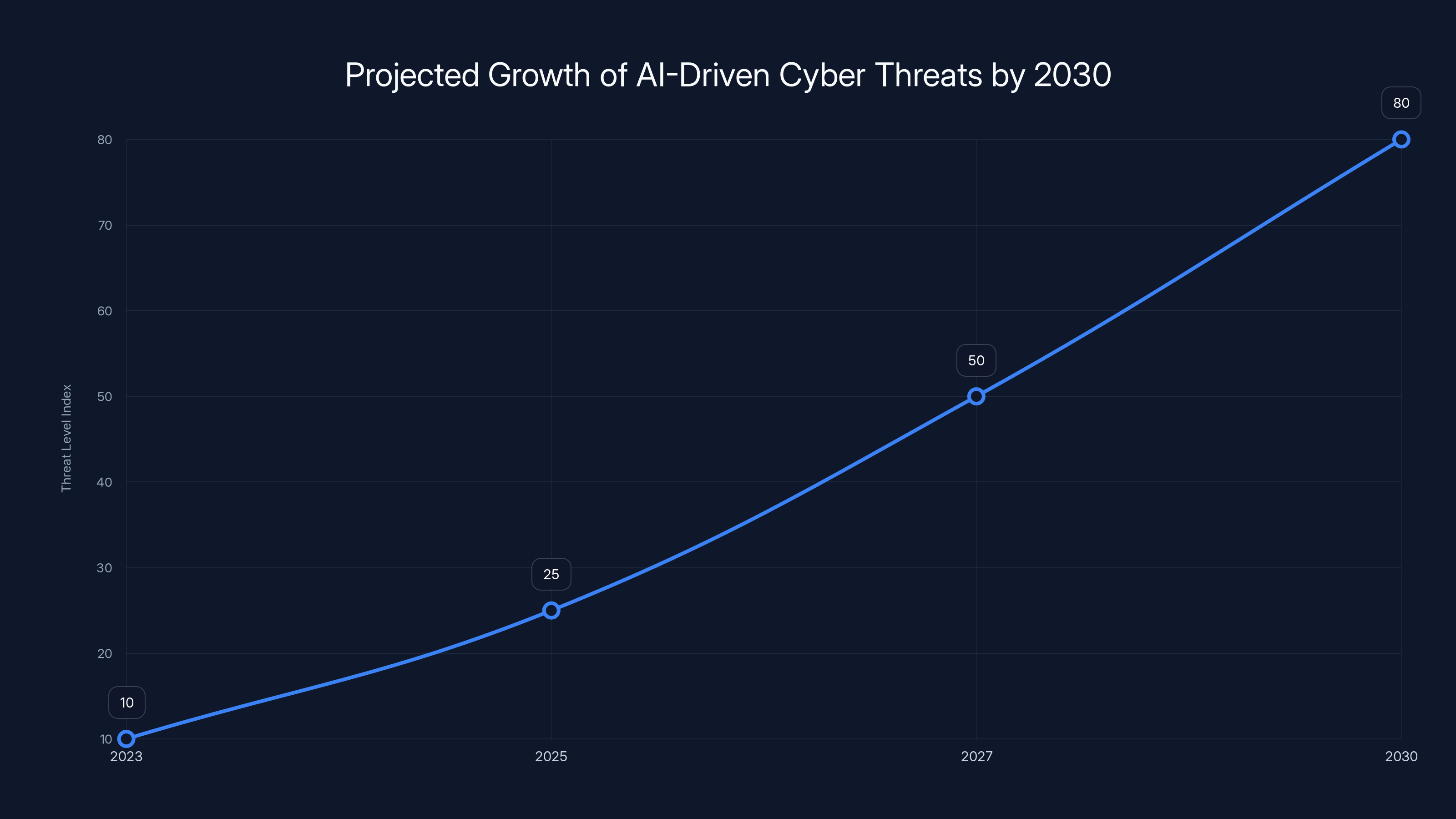
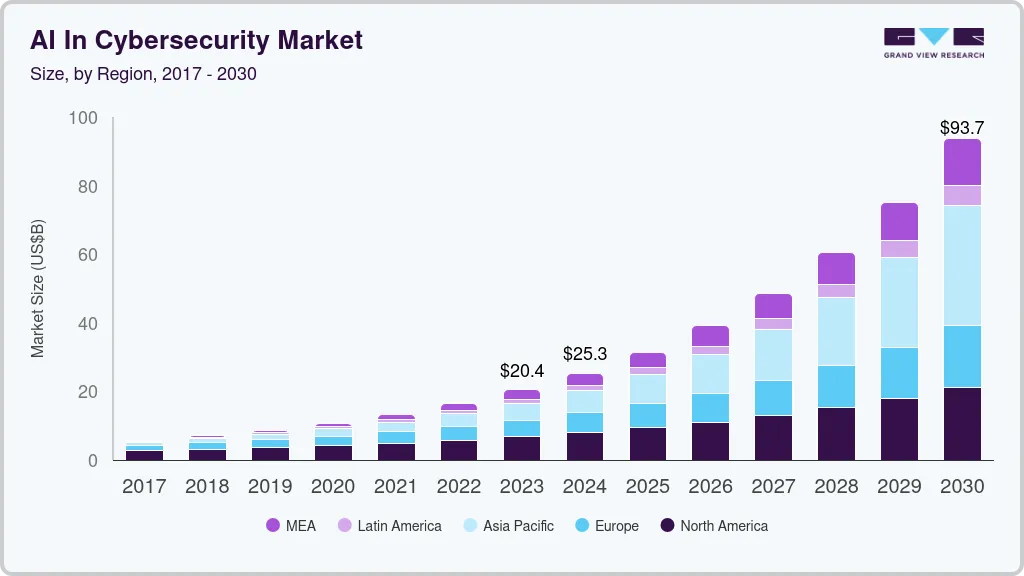
AI-driven cyber threats are projected to significantly increase by 2030, with a potential growth index rising from 10 in 2023 to 80 in 2030. Estimated data based on current trends.
Future Trends and Recommendations
Emerging Threats
As cyber operations become more sophisticated, the threat landscape continues to evolve. Future trends may include:
- AI-Driven Attacks: Malware leveraging artificial intelligence to adapt to defenses dynamically.
- Supply Chain Attacks: Targeting vulnerabilities in software and hardware supply chains, as discussed by Runable.
Strengthening Global Cybersecurity
To counter these threats, international cooperation and information sharing are vital. Governments and organizations must collaborate to develop unified standards and share threat intelligence.
Recommendations for Organizations
- Adopt Zero Trust Architecture: Emphasize verification at every access point.
- Invest in Cybersecurity Training: Regularly train employees on the latest threats and response techniques.
- Engage in Threat Intelligence Sharing: Participate in industry forums for sharing insights and best practices, as highlighted by Runable.
Conclusion
The discovery of malware preceding Stuxnet highlights the continuous evolution of cyber threats. By understanding past attacks, organizations can better prepare for future challenges, ensuring robust defenses and resilient infrastructures.
FAQ
What is sabotage malware?
Sabotage malware is designed to disrupt or damage industrial systems by altering operational parameters without detection.
How does early malware differ from modern cyber threats?
Early malware often employed simpler tactics, but some exhibited sophisticated stealth techniques similar to modern threats.
What are the implications of discovering pre-Stuxnet malware?
It provides insights into the evolution of cyber sabotage, highlighting the need for advanced defenses in critical infrastructure.
How can organizations protect against similar threats today?
Organizations should implement network segmentation, IDS, and regular audits to mitigate the risk of sophisticated malware.
What future trends should cybersecurity professionals anticipate?
Professionals should prepare for AI-driven attacks and supply chain vulnerabilities, emphasizing global cooperation and information sharing.
Why is international cooperation crucial in cybersecurity?
Cooperation allows for sharing threat intelligence and developing unified standards to counter global cyber threats effectively.
How can zero trust architecture enhance security?
Zero trust architecture requires verification at every access point, reducing the risk of unauthorized access and data breaches.
What role does employee training play in cybersecurity?
Training equips employees with the knowledge to recognize and respond to threats, significantly enhancing organizational security.

Key Takeaways
- Discovery of pre-Stuxnet malware offers insights into early cyber sabotage techniques.
- Advanced stealth tactics in early malware highlight the sophistication of state-sponsored attacks.
- Implementing network segmentation and IDS is crucial for protecting industrial systems.
- Future cyber threats may leverage AI and target supply chain vulnerabilities.
- International cooperation is vital for developing unified cybersecurity standards.
- Zero trust architecture enhances security by requiring verification at every access point.
- Regular employee training on the latest threats is essential for robust cybersecurity.
- Sharing threat intelligence across organizations strengthens global cyber defenses.
Related Articles
- Anthropic’s Mythos Breach: Lessons Learned and Future Implications [2025]
- Vercel's Security Incident: A Deep Dive into Compromised Accounts [2025]
- Understanding the Vercel Data Breach: Implications, Security Best Practices, and Future Directions [2025]
- Why Your IT Helpdesk is Getting Weird Calls: LinkedIn Data Threats [2025]
- Understanding the Surge: A Tenfold Growth in Botnet Size and the Future of DDoS Attacks [2025]
- Why Passkeys Are the Future of Authentication [2025]
![Unveiling the Precursor: The Hidden Malware Before Stuxnet [2025]](https://tryrunable.com/blog/unveiling-the-precursor-the-hidden-malware-before-stuxnet-20/image-1-1776983761026.jpg)



