Introduction
Last month, a startling revelation shook the gaming world: North Korean hackers, specifically the APT37 group, also known as Scar Cruft, targeted a popular gaming platform with a trojanized version of their software. This attack, codenamed Bird Call, underscores a growing trend of cybercriminals setting their sights on the gaming community. In this comprehensive guide, we will explore the technical intricacies of this attack, what makes gamers a lucrative target, and how you can protect yourself from similar threats.
TL; DR
- Trojanized Software: North Korean hackers used a compromised gaming platform to deliver malicious payloads.
- Multi-Platform Threat: The attack affected both Windows and Android systems.
- Data Exfiltration: Hackers aimed to steal sensitive data and execute commands on infected devices.
- Vulnerable Community: Gamers are increasingly becoming targets due to the value of in-game assets and personal data.
- Protective Measures: Use antivirus software, be cautious with downloads, and stay informed on cybersecurity trends.

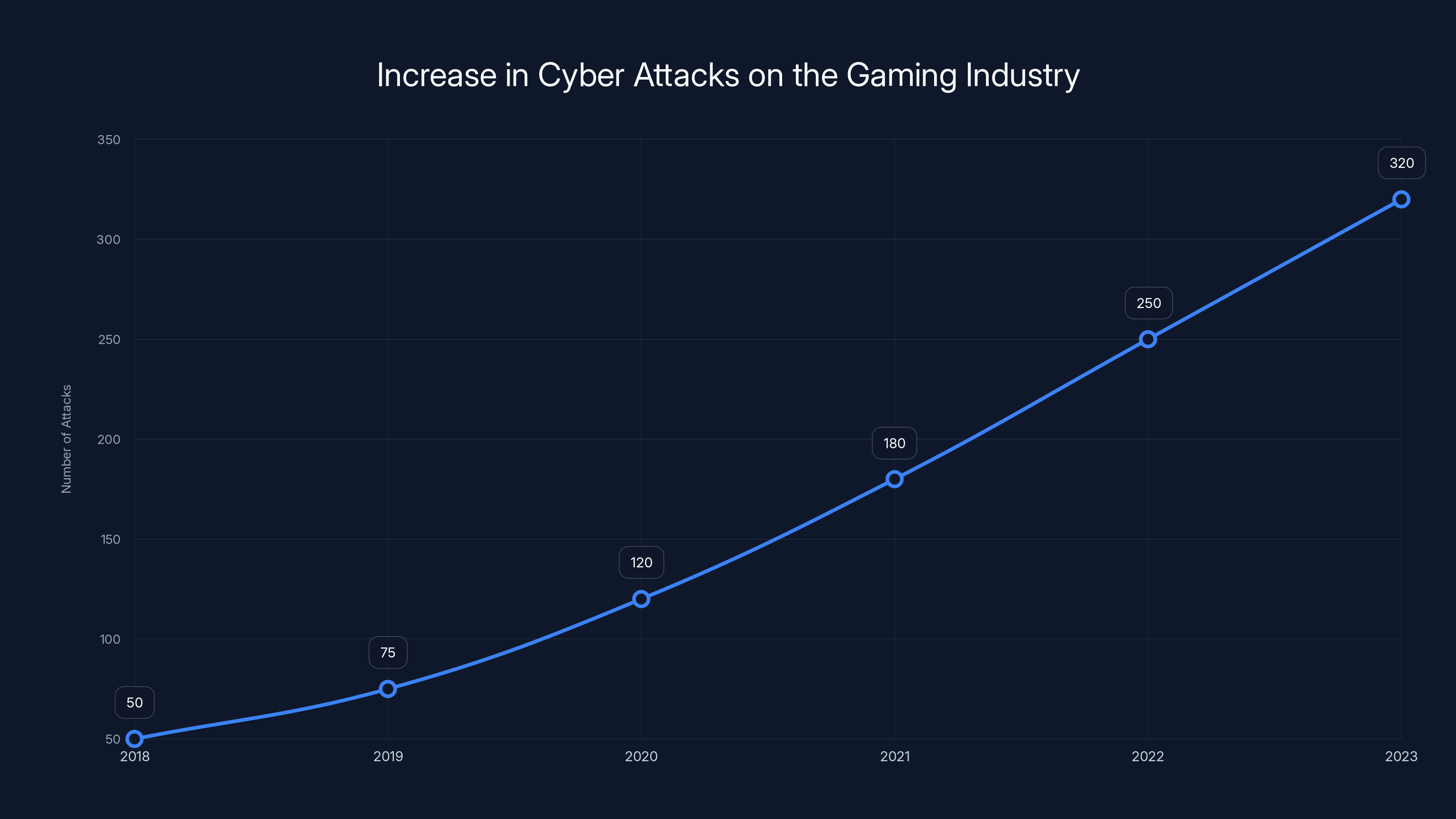
The number of cyber attacks on the gaming industry has increased significantly from 2018 to 2023, highlighting the growing threat posed by groups like North Korea's Lazarus Group. (Estimated data)
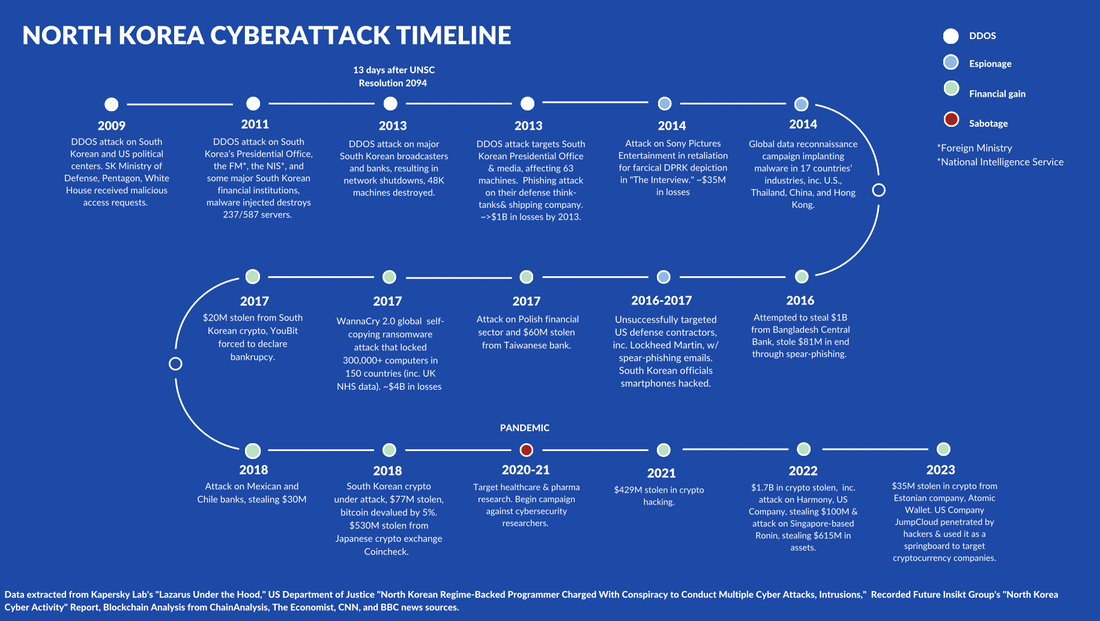
The Rise of North Korean Cyber Threats
North Korea's cyber capabilities have evolved dramatically over the past decade. The country's cyber units, often referred to as Lazarus Group, APT38, and Scar Cruft, have been implicated in numerous high-profile cyberattacks worldwide. Their focus has shifted from traditional espionage to financially motivated operations, with the gaming industry becoming an attractive target due to its lucrative in-game economies and vast user base.
The Bird Call Backdoor Explained
The Bird Call backdoor is a sophisticated piece of malware designed to infiltrate systems through a seemingly innocuous gaming application. Once installed, it establishes a secure connection with a command-and-control server, allowing hackers to execute commands remotely. This can lead to data theft, system manipulation, and further propagation of the malware.
Technical Breakdown
- Infection Vector: The malware is delivered through a trojanized installer of the gaming platform, often bundled with legitimate software to avoid detection.
- Persistence Mechanism: It modifies system settings to ensure it runs at startup, maintaining a foothold in the system even after reboots.
- Command Execution: The backdoor can execute arbitrary commands, providing attackers with full control over the infected system.
python# Example of a simple command execution in Python
import os
os.system('command to execute')
Why Gamers?
Gamers have become a prime target for several reasons:
- Valuable Assets: In-game items, currencies, and accounts can be sold on black markets for real money.
- Large User Base: With millions of players worldwide, the gaming industry provides a vast pool of potential victims.
- Lax Security Practices: Many gamers prioritize performance over security, often disabling protective measures that could prevent attacks.

Using reputable security software and enabling two-factor authentication are highly effective in protecting against trojanized platforms. (Estimated data)
Protecting Yourself Against Trojanized Platforms
To safeguard your gaming and personal data, consider implementing the following best practices:
- Use Reputable Security Software: Install antivirus and anti-malware programs that can detect and neutralize threats before they cause harm.
- Verify Software Sources: Only download games and updates from official sources. Avoid third-party sites and torrents.
- Regular Updates: Keep your operating system and software up to date to patch known vulnerabilities.

Future Trends in Cybersecurity for Gamers
As cyber threats continue to evolve, the gaming industry must adapt to protect its users. Here are some trends and recommendations for the future:
- AI-Powered Security: Leveraging artificial intelligence to detect anomalies and respond to threats in real-time.
- Blockchain for Asset Security: Using blockchain technology to secure in-game transactions and verify asset ownership.
- User Education: Increasing awareness and training for gamers on cybersecurity best practices.
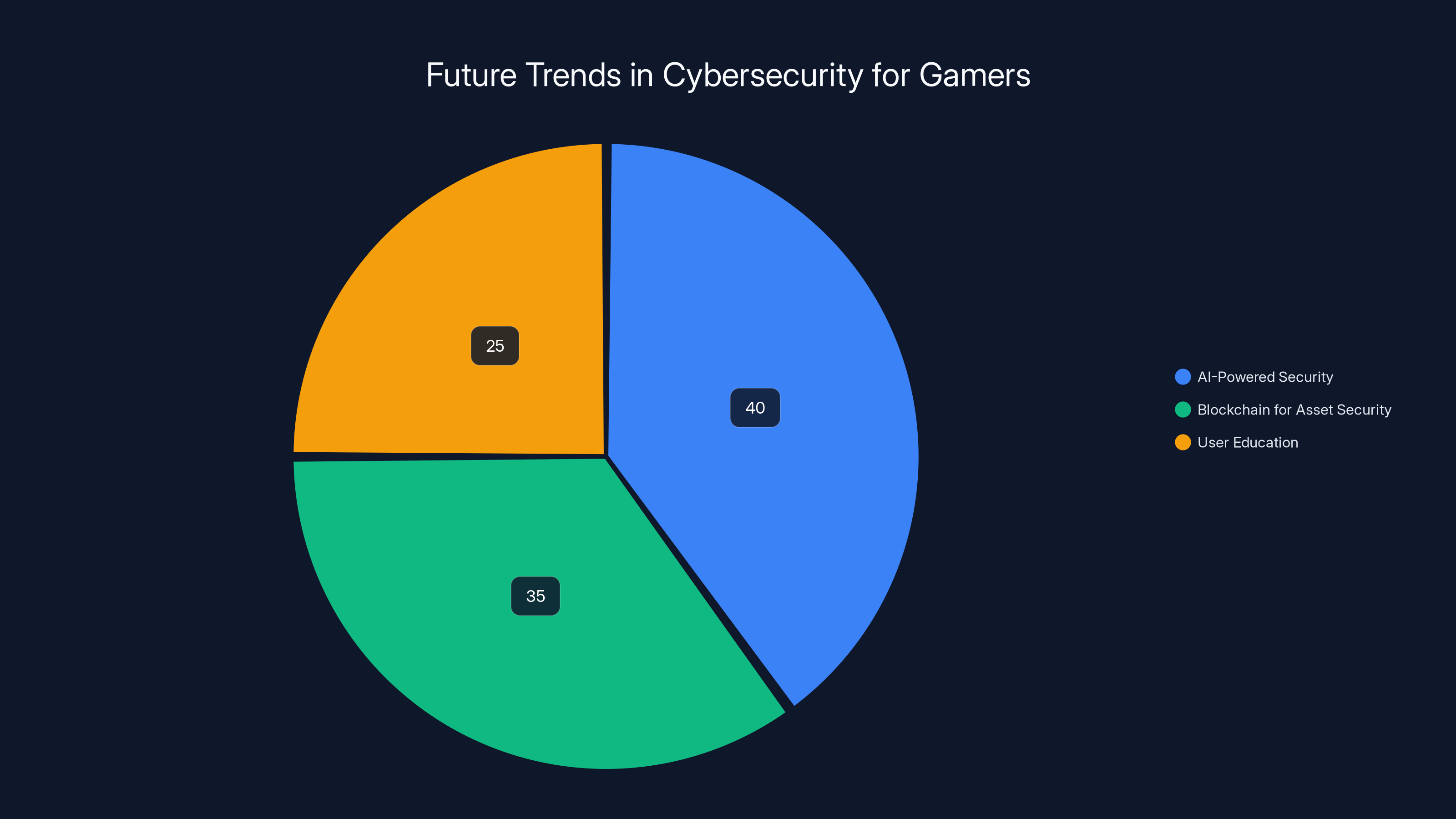
AI-powered security is expected to have the largest impact on gaming cybersecurity, followed by blockchain and user education. Estimated data.
Conclusion
The attack on the Yanbian gaming platform by North Korean hackers serves as a stark reminder of the ever-present cyber threats facing the gaming community. By understanding the tactics used by cybercriminals and implementing robust security measures, gamers can protect themselves and enjoy their favorite pastime without fear of compromise.
Use Case: Automate security updates and threat detection for your gaming devices with Runable's AI-powered platform.
Try Runable For FreeFAQ
What is the Bird Call backdoor?
Bird Call is a backdoor malware used by North Korean hackers to infiltrate gaming platforms and execute commands on infected systems.
How can I protect my gaming accounts?
Use strong, unique passwords, enable two-factor authentication, and regularly update your software to protect your gaming accounts.
Why are gamers targeted by hackers?
Gamers are targeted due to the value of in-game assets, the large user base, and often lax security practices.
What are the signs of a trojanized platform?
Signs include unexpected system behavior, frequent crashes, and unauthorized access attempts on your gaming accounts.
How does AI help in cybersecurity?
AI helps by detecting anomalies, responding to threats in real-time, and automating security updates to protect against known and unknown threats.
Is downloading from third-party sites safe?
No, it is not safe. Always download games and updates from official sources to reduce the risk of downloading compromised software.
What future trends should gamers be aware of?
Gamers should be aware of AI-powered security, blockchain for asset security, and the importance of user education in cybersecurity.
Key Takeaways
- North Korean hackers target gamers through trojanized platforms.
- The BirdCall backdoor allows remote command execution and data theft.
- Gamers are targeted due to valuable in-game assets and large user base.
- Implement strong passwords and two-factor authentication for protection.
- AI and blockchain are emerging trends in gaming cybersecurity.
Related Articles
- Understanding the Vimeo Data Breach and Protecting Your Digital Footprint [2025]
- AI-Generated Phishing Attacks: Beyond the Inbox and How to Protect Yourself [2025]
- Understanding the Complex Ties Between Ransomware Gangs and Government Infrastructures [2025]
- The Rise of AI in Cybercrime: Understanding the Impact and Challenges [2025]
- Google's $1.5 Million Bounty for Security Bugs in Android and Chrome [2025]
- Understanding Supply-Chain Attacks: The Daemon Tools Incident and Its Implications [2025]
![North Korean Hackers Target Gamers with Trojanized Platform - Here's What to Look Out For [2025]](https://tryrunable.com/blog/north-korean-hackers-target-gamers-with-trojanized-platform-/image-1-1778106829970.jpg)



