Unpacking Surfshark's Post-Quantum 'Dausos' and Its Impact on Internet Speeds [2025]
The landscape of internet security is undergoing a seismic shift as post-quantum cryptography becomes a necessity rather than an option. Enter Surfshark's 'Dausos', a pioneering technology promising to enhance internet speeds by up to 30% while securing data against the looming threat of quantum computing. But does it deliver on its promises? Let's dive in.
TL; DR
- Surfshark's 'Dausos': Claims to boost internet speeds by 30% using post-quantum cryptography.
- Post-Quantum Threat: Quantum computers could potentially break current encryption standards.
- Real-World Testing: Initial tests show mixed results, with some users unable to load speed tests.
- Implementation Challenges: Adapting to new cryptographic standards is complex and resource-intensive.
- Future Outlook: As quantum computing evolves, post-quantum security will become standard.
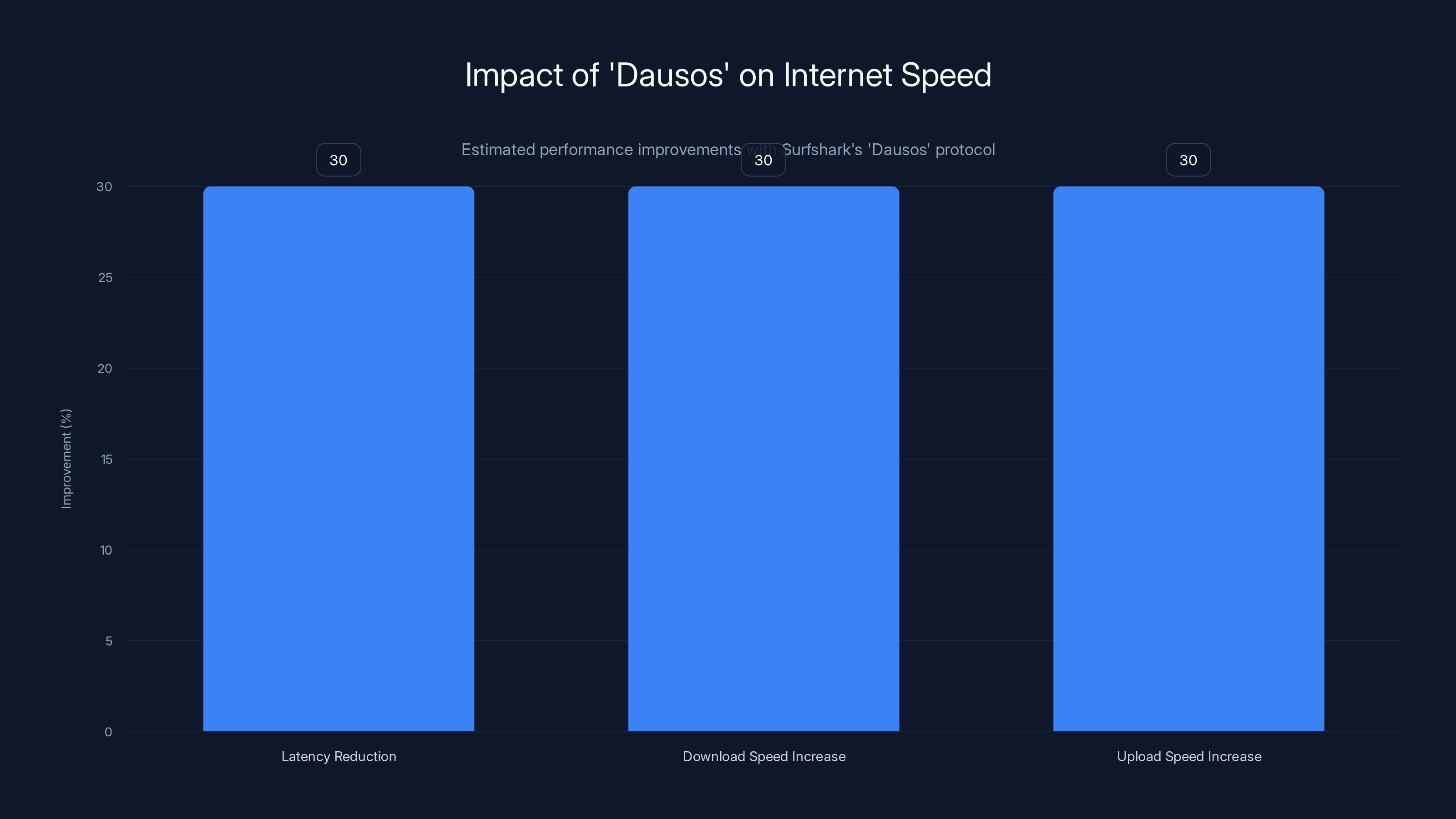
Surfshark's 'Dausos' protocol is estimated to improve internet speeds by up to 30%, enhancing both download and upload speeds while reducing latency.
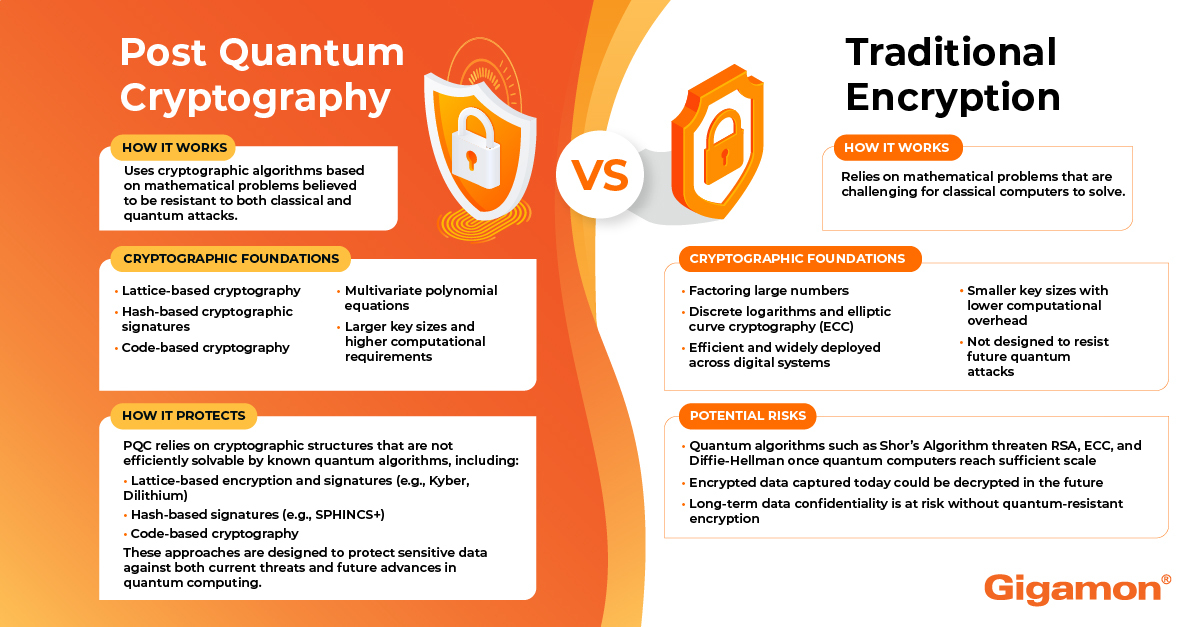
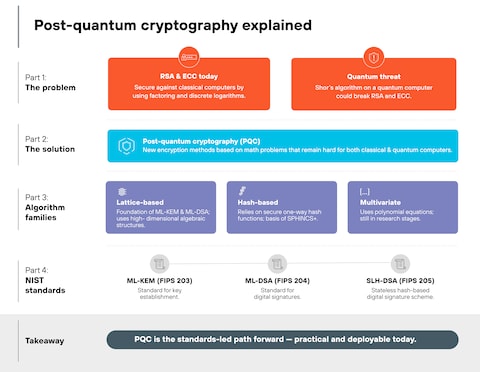
What is Post-Quantum Cryptography?
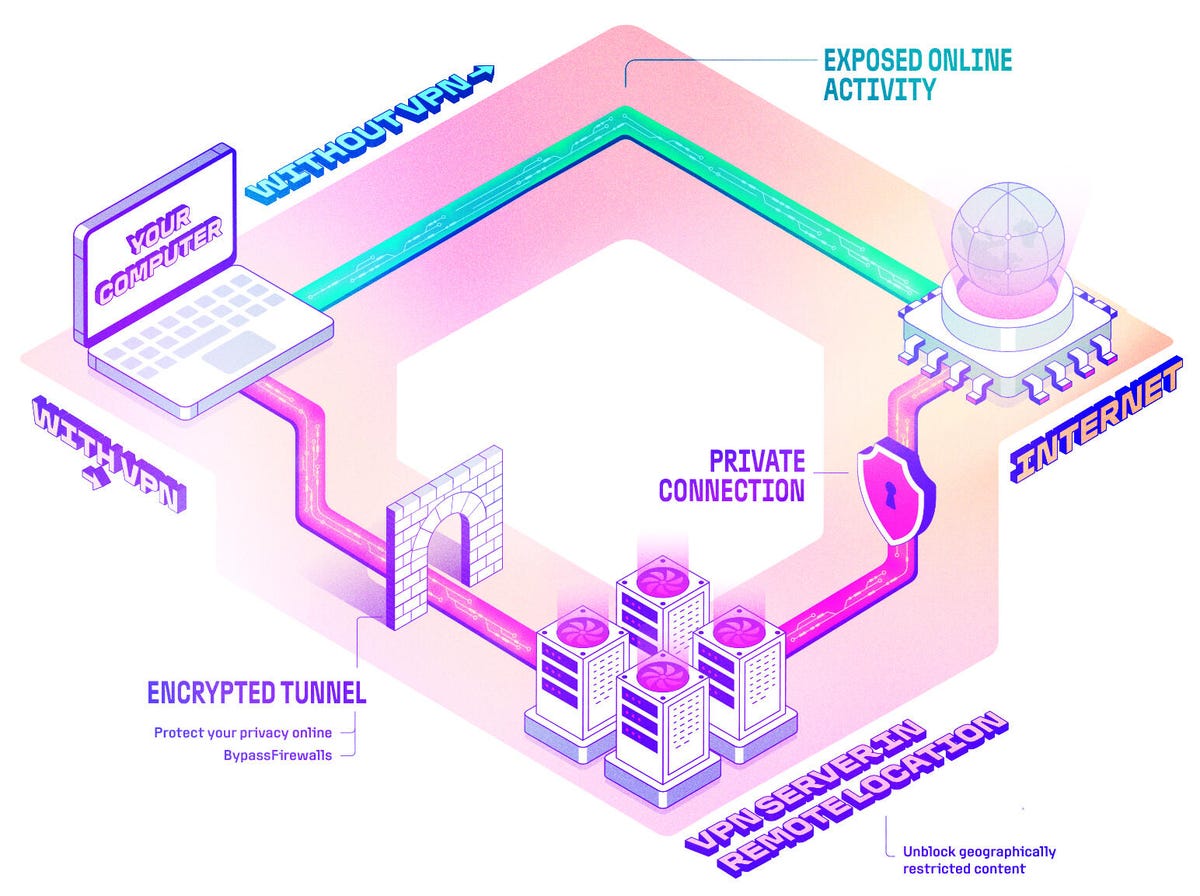
Post-quantum cryptography refers to cryptographic algorithms that are thought to be secure against an attack by quantum computers. Quantum computers have the potential to break widely used encryption methods, such as RSA, that underpin much of today's internet security.
Why Quantum Computers are a Threat
Quantum computers leverage quantum bits, or qubits, to perform calculations at unprecedented speeds. This capability poses a threat to current encryption standards that rely on the difficulty of factoring large numbers or the discrete logarithm problem.
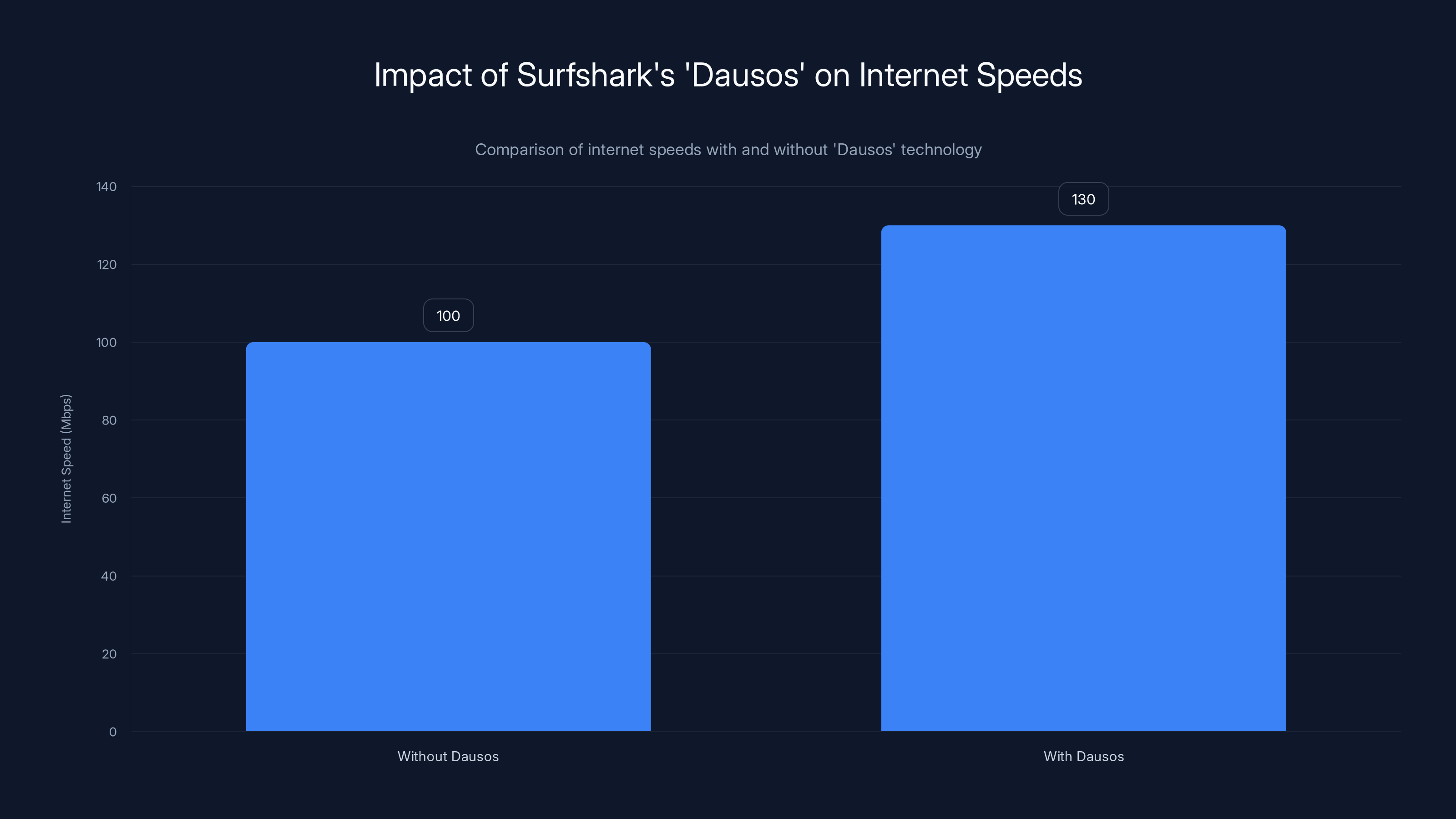
Surfshark's 'Dausos' technology is estimated to increase internet speeds by up to 30%, enhancing both security and performance. Estimated data.
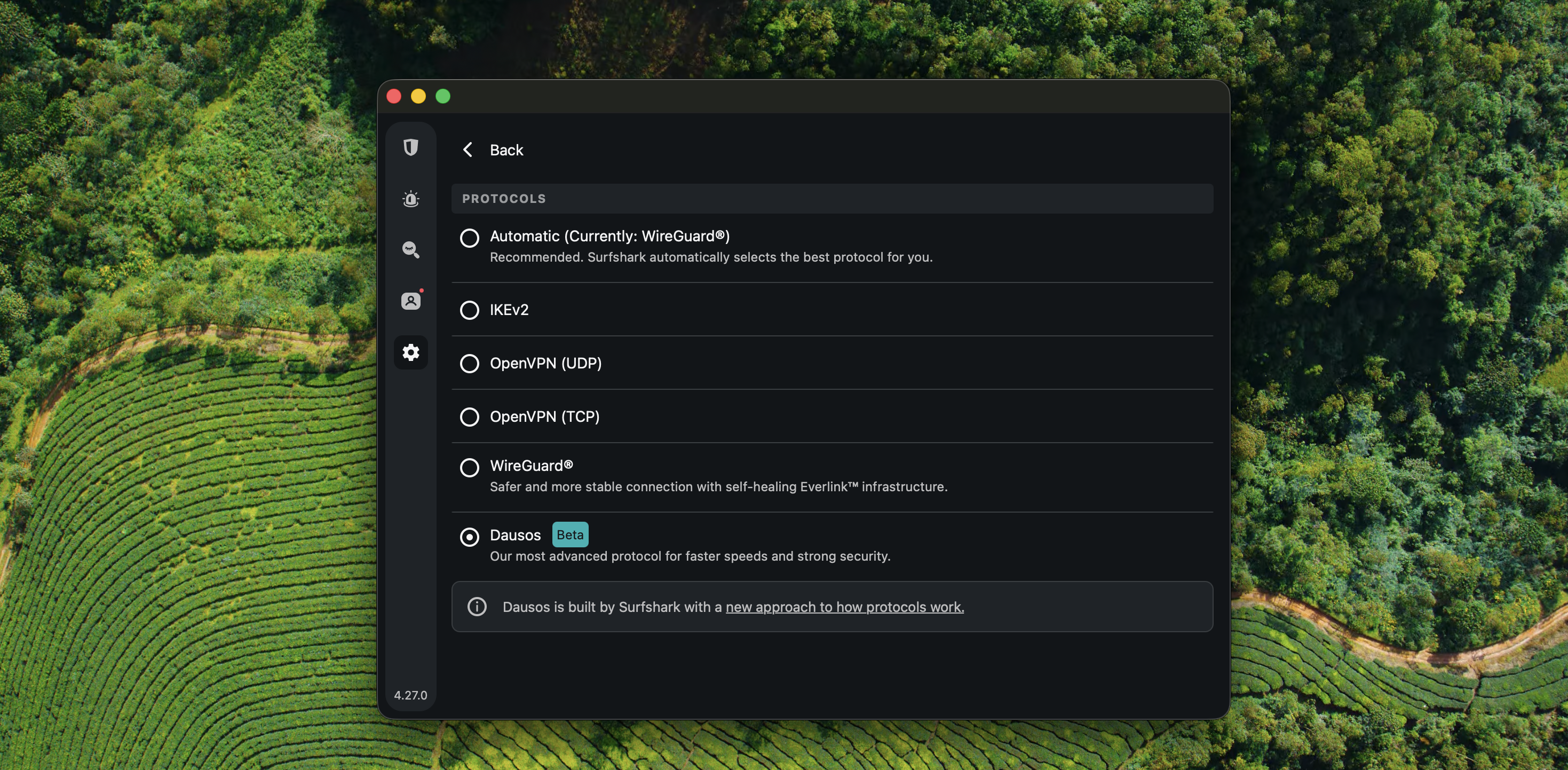
Introducing Surfshark's 'Dausos'
Surfshark has introduced 'Dausos', a post-quantum encryption protocol designed to enhance internet speed and security. By implementing new cryptographic standards, Surfshark aims to safeguard data against potential quantum attacks while improving connection speeds.
Key Features of 'Dausos'
- Enhanced Security: Utilizes lattice-based cryptography to secure data.
- Faster Speeds: Claims to reduce latency and improve download/upload speeds by up to 30%.
- Future-Proofing: Designed to withstand quantum computing advancements.
Real-World Use Cases
Use Case 1: Streaming and Gaming
For avid gamers and streamers, speed is crucial. 'Dausos' promises to reduce buffering and lag, providing a smoother experience. In theory, this should allow gamers to enjoy higher frame rates and streamers to maintain higher resolution streams with fewer interruptions.
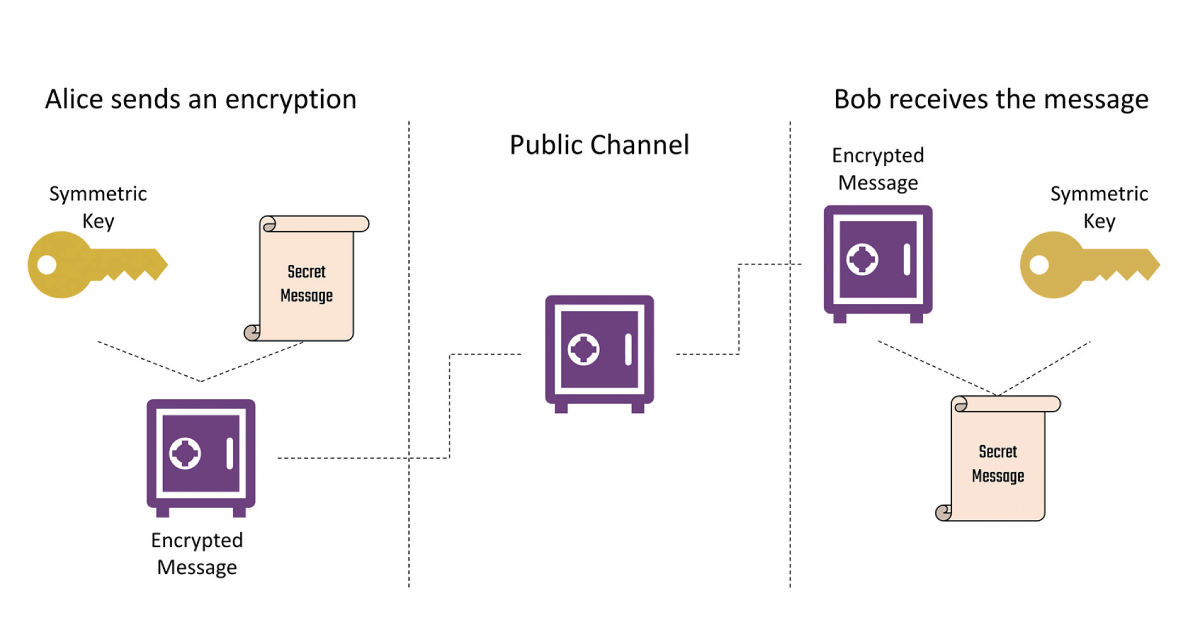
Use Case 2: Secure Communications
With 'Dausos', encrypted communications become more secure, making it ideal for businesses and individuals concerned about privacy. The protocol's post-quantum encryption ensures that messages remain confidential even if intercepted by malicious actors using quantum technology.
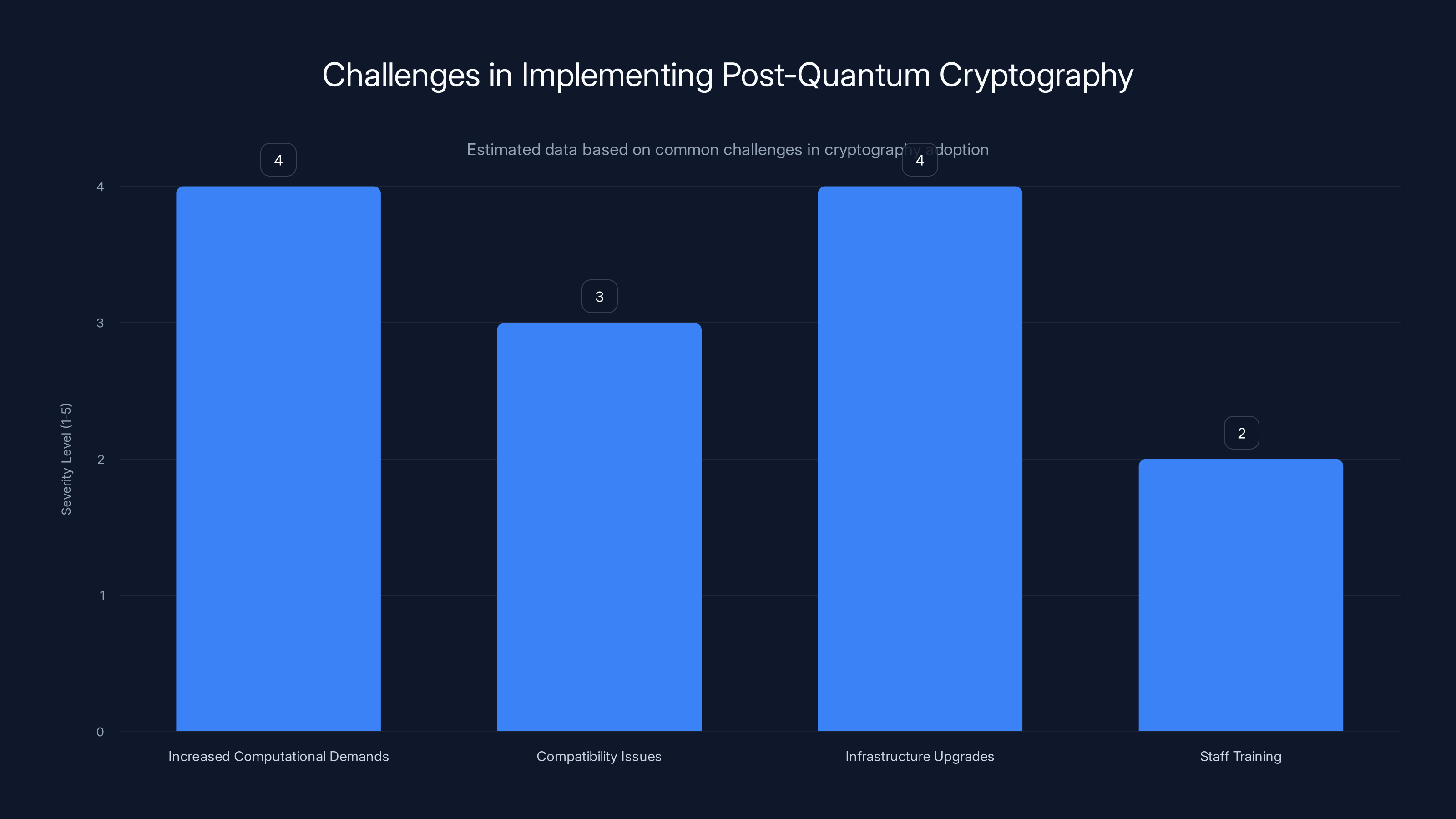
Increased computational demands and infrastructure upgrades are the most significant challenges in adopting post-quantum cryptography. (Estimated data)
Testing 'Dausos': Does It Deliver?
Initial tests of 'Dausos' have produced mixed results. While some users report noticeable improvements in speed, others encounter issues, such as being unable to load speed tests. This discrepancy highlights the challenges of real-world implementation.
Technical Challenges and Implementation
The Complexity of Lattice-Based Cryptography
Lattice-based cryptography forms the backbone of 'Dausos'. This method involves complex mathematical structures that are more resistant to quantum attacks. However, implementing these algorithms can be resource-intensive and may require significant infrastructure updates.
- Key Generation: Involves large keys that are difficult to manage.
- Computational Load: Increased processing power required for encryption and decryption.
- Compatibility: Ensuring new protocols work seamlessly with existing systems.
Common Pitfalls and Solutions
Pitfall 1: Transitioning to New Standards
Transitioning to post-quantum cryptography is not without its hurdles. Organizations must ensure compatibility with existing systems and software.
Solution: Conduct thorough testing and gradual rollouts to identify and address compatibility issues early.
Pitfall 2: Resource Allocation
The computational demands of post-quantum encryption can strain existing resources, leading to slower performance in some cases.
Solution: Invest in hardware upgrades and optimize software to handle increased loads efficiently.
Future Trends in Post-Quantum Cryptography
The Rise of Hybrid Cryptography
As post-quantum cryptography develops, hybrid approaches combining classical and quantum-resistant algorithms will likely become commonplace. This strategy ensures a layered defense against potential threats.
Regulatory Developments
Governments and regulatory bodies are beginning to recognize the importance of post-quantum security. Expect to see new standards and guidelines that mandate the adoption of quantum-resistant encryption.

Recommendations for Organizations
- Evaluate Current Infrastructure: Assess whether existing systems can support post-quantum cryptography without significant degradation in performance.
- Stay Informed: Keep up with developments in quantum computing and related security technologies.
- Invest in Training: Ensure IT staff are knowledgeable about post-quantum technologies and their implementation.
- Pilot Projects: Implement pilot projects to test post-quantum encryption in controlled settings before widespread adoption.
Conclusion
While Surfshark's 'Dausos' shows promise, the journey to full post-quantum security is complex. Organizations need to balance speed with security, ensuring that they are ready for a quantum future. The key is to stay informed, invest in the right technologies, and prepare for a gradual transition to new cryptographic standards.
FAQ
What is post-quantum cryptography?
Post-quantum cryptography is a field of cryptography that develops algorithms secure against quantum computer attacks, which threaten existing encryption standards.
How does Surfshark's 'Dausos' work?
'Dausos' uses lattice-based cryptography to enhance security and potentially improve internet speeds by leveraging post-quantum encryption techniques.
What are the benefits of post-quantum cryptography?
Benefits include enhanced security against quantum attacks, improved data privacy, and future-proofing existing systems.
Are there challenges in implementing post-quantum cryptography?
Yes, challenges include increased computational demands, compatibility issues, and the need for infrastructure upgrades.
How can organizations prepare for post-quantum encryption?
Organizations should evaluate their current infrastructure, invest in staff training, and conduct pilot projects to test new cryptographic standards.
What is lattice-based cryptography?
Lattice-based cryptography is a type of post-quantum cryptography that uses mathematical lattice structures to create secure encryption methods.
Why is hybrid cryptography important?
Hybrid cryptography offers a layered approach, using both classical and quantum-resistant algorithms to provide comprehensive security.
What should I consider when choosing a post-quantum solution?
Consider factors like ease of implementation, compatibility with existing systems, and the level of security provided against quantum threats.
Key Takeaways
- Surfshark's 'Dausos' claims to boost speeds by 30% with post-quantum cryptography.
- Quantum computers pose a threat to current encryption standards.
- Real-world testing shows mixed results, highlighting implementation challenges.
- Post-quantum cryptography requires significant resource and infrastructure investments.
- Hybrid cryptography will likely become standard for layered security.
- Organizations should prepare for the quantum future by evaluating and upgrading systems.
Related Articles
- Microsoft's Shift from Surface Hub: Understanding the Transition [2025]
- Press Freedom and VPN Surveillance: Navigating the Complexities [2025]
- Future-Proof Your Privacy with Next-Generation VPN Encryption [2026]
- Secure Your Digital Life: Keeper Password Manager's Big Discounts [2026]
- Understanding the Basic-Fit Data Breach: A Comprehensive Guide to Data Security [2025]
- 'Trusted Access for the Next Era of Cyber Defense': OpenAI's Cybersecurity Revolution [2025]
![Unpacking Surfshark's Post-Quantum 'Dausos' and Its Impact on Internet Speeds [2025]](https://tryrunable.com/blog/unpacking-surfshark-s-post-quantum-dausos-and-its-impact-on-/image-1-1776249273080.png)



