Unveiling Open Claw Security Risks You Must Know About [2025]
Open Claw has been gaining traction as a powerful tool that employs AI agents to access and manage your files, emails, calendars, and even command lines. While the technology offers unprecedented convenience, it also introduces several security risks that users must be aware of. This article delves into these risks, provides practical strategies to mitigate them, and offers insights into the future of AI-driven automation.
TL; DR
- Open Claw Security Risks: AI agents can access sensitive data, posing significant security threats.
- Mitigation Strategies: Implement strong authentication, regular audits, and access controls.
- Future Trends: Expect advancements in AI security protocols and standards.
- Key Recommendation: Users must balance convenience with security by staying informed.
- Bottom Line: Understand and mitigate risks to leverage Open Claw safely.
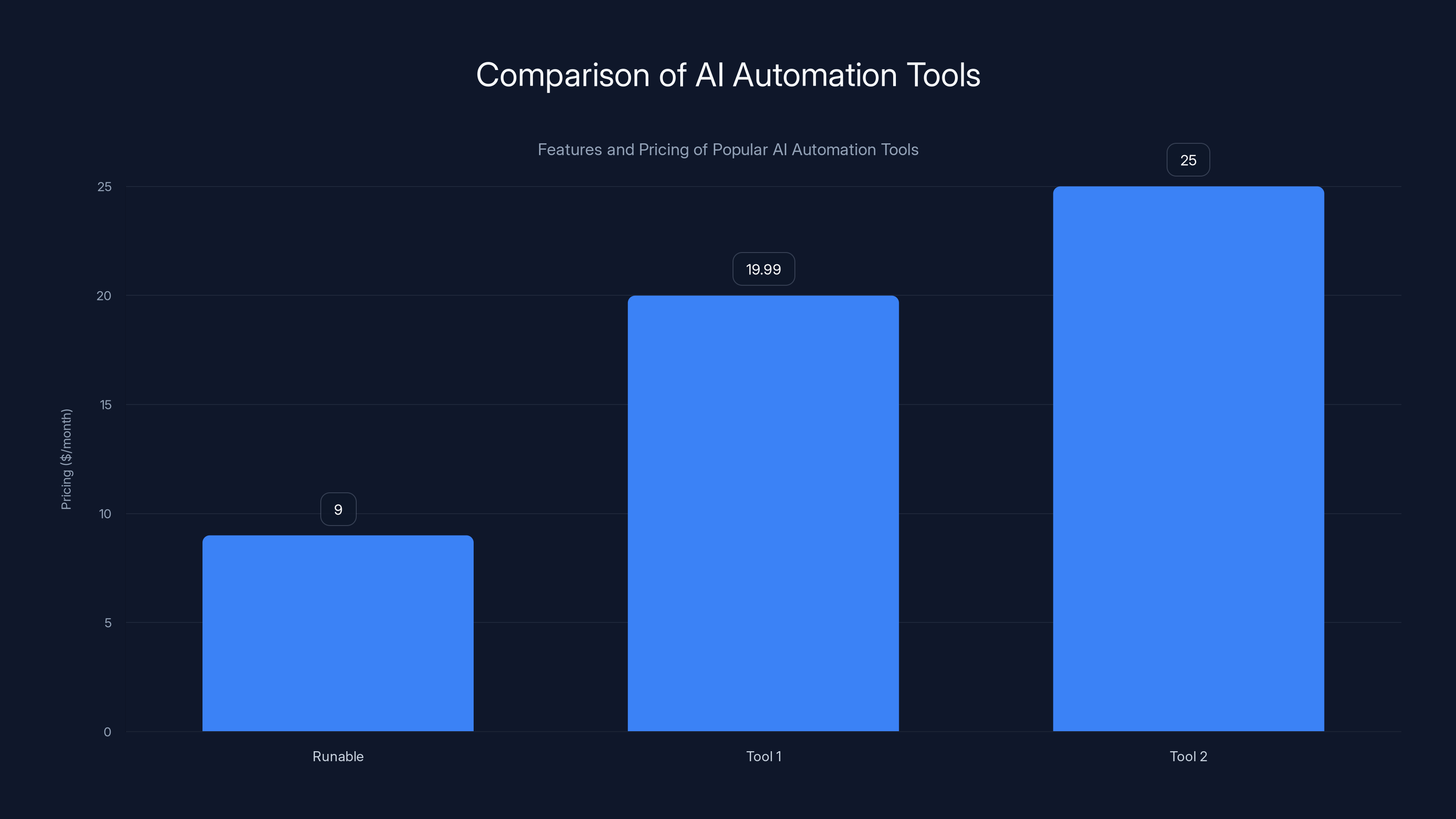
Runable offers the most affordable entry-level pricing at
Understanding Open Claw
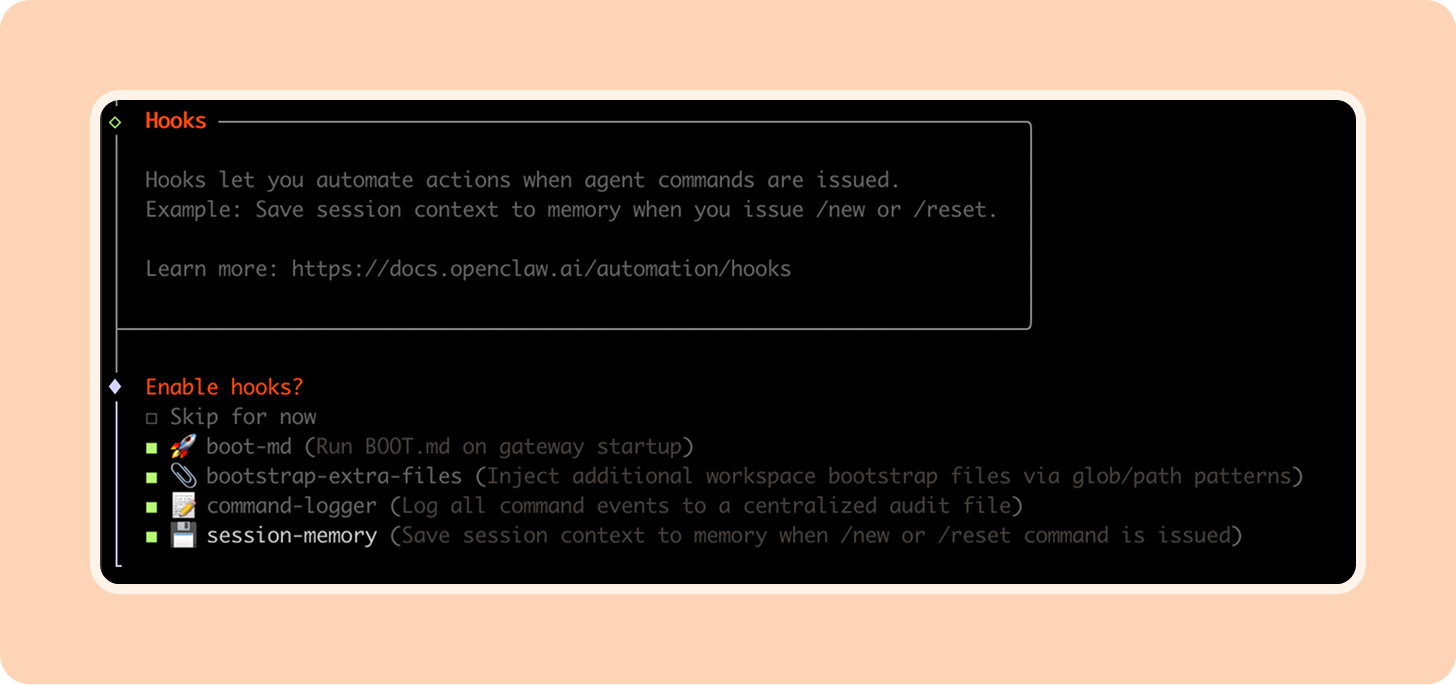
Open Claw is designed to simplify and automate tasks by integrating AI agents with your digital environment. These agents can perform complex operations like managing files, scheduling meetings, and executing command-line instructions based on user inputs.
Key Features
- Automated File Management: Organizes and retrieves documents efficiently.
- Email and Calendar Integration: Automates scheduling and email management.
- Command Line Execution: Executes scripts and commands autonomously.
Use Case Example
Imagine you're a project manager juggling multiple projects. Open Claw automates your calendar, ensuring you never miss a deadline, while simultaneously organizing your project files.
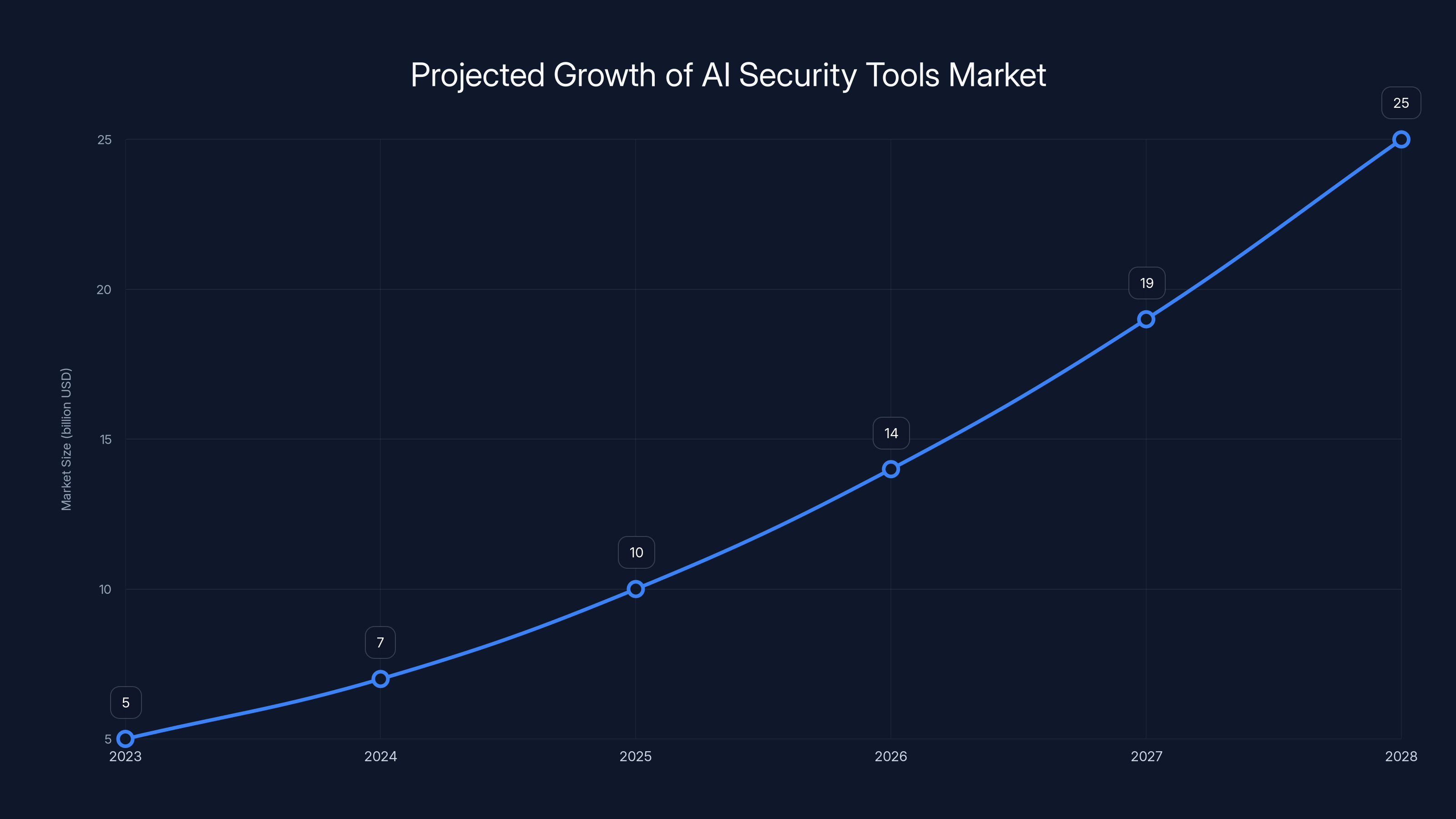
The AI security tools market is projected to grow significantly, reaching an estimated $25 billion by 2028, driven by advancements in protocols and integration with blockchain technology. (Estimated data)
Security Risks Associated with Open Claw
While Open Claw's capabilities are impressive, they come with significant security risks. Here are the most critical ones:
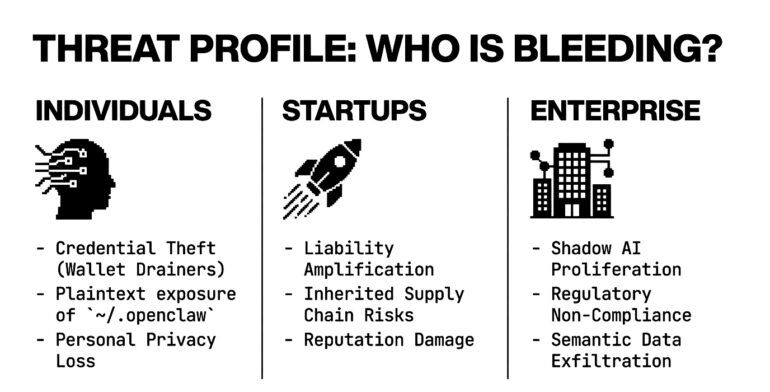
1. Unauthorized Data Access
AI agents have access to sensitive data, increasing the risk of unauthorized access if the system is compromised. According to Dark Reading, this is a major concern for users.
Mitigation: Implement multi-factor authentication and limit access permissions.
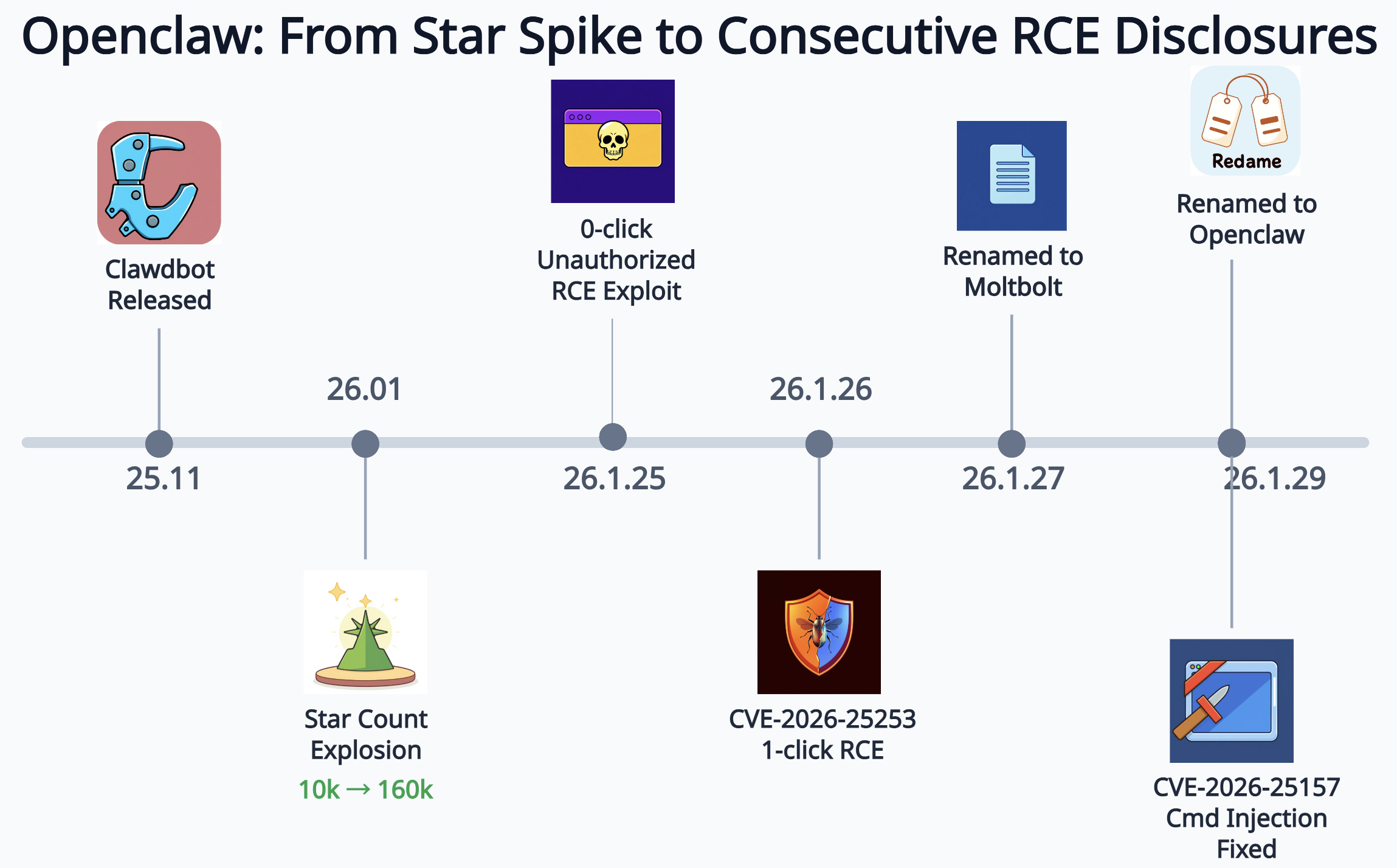
2. Command Injection Vulnerabilities
AI agents executing command-line instructions can be exploited if proper input validation isn't enforced. VentureBeat highlights the importance of secure coding practices to prevent such vulnerabilities.
Mitigation: Use secure coding practices and regular security audits.
3. Email Phishing Risks
With email access, AI agents can be tricked into executing malicious instructions from phishing emails. CryptoRank reports on the prevalence of phishing scams targeting AI systems.
Mitigation: Educate users on phishing techniques and employ advanced email filtering.
4. Data Privacy Concerns
AI agents accessing and processing sensitive data could lead to privacy violations if data handling policies aren't stringent. Wiz.io emphasizes the need for strict data privacy policies.
Mitigation: Implement strict data privacy policies and regular compliance checks.
5. Misconfiguration Issues
Improper configuration can lead to security loopholes that attackers might exploit. Palo Alto Networks discusses the risks associated with misconfigurations in cloud environments.
Mitigation: Regularly update configurations and perform security audits.
Best Practices for Safeguarding Open Claw
Implement Strong Authentication
Use multi-factor authentication to ensure only authorized users can access the system.
Regular Security Audits
Conduct audits to identify vulnerabilities and ensure compliance with security standards.
Access Control Management
Limit the access permissions of AI agents to only what is necessary for their operation.
Secure Coding Practices
Enforce input validation and output encoding to prevent injection attacks.
User Education
Educate users about the potential risks and safe practices to mitigate them.

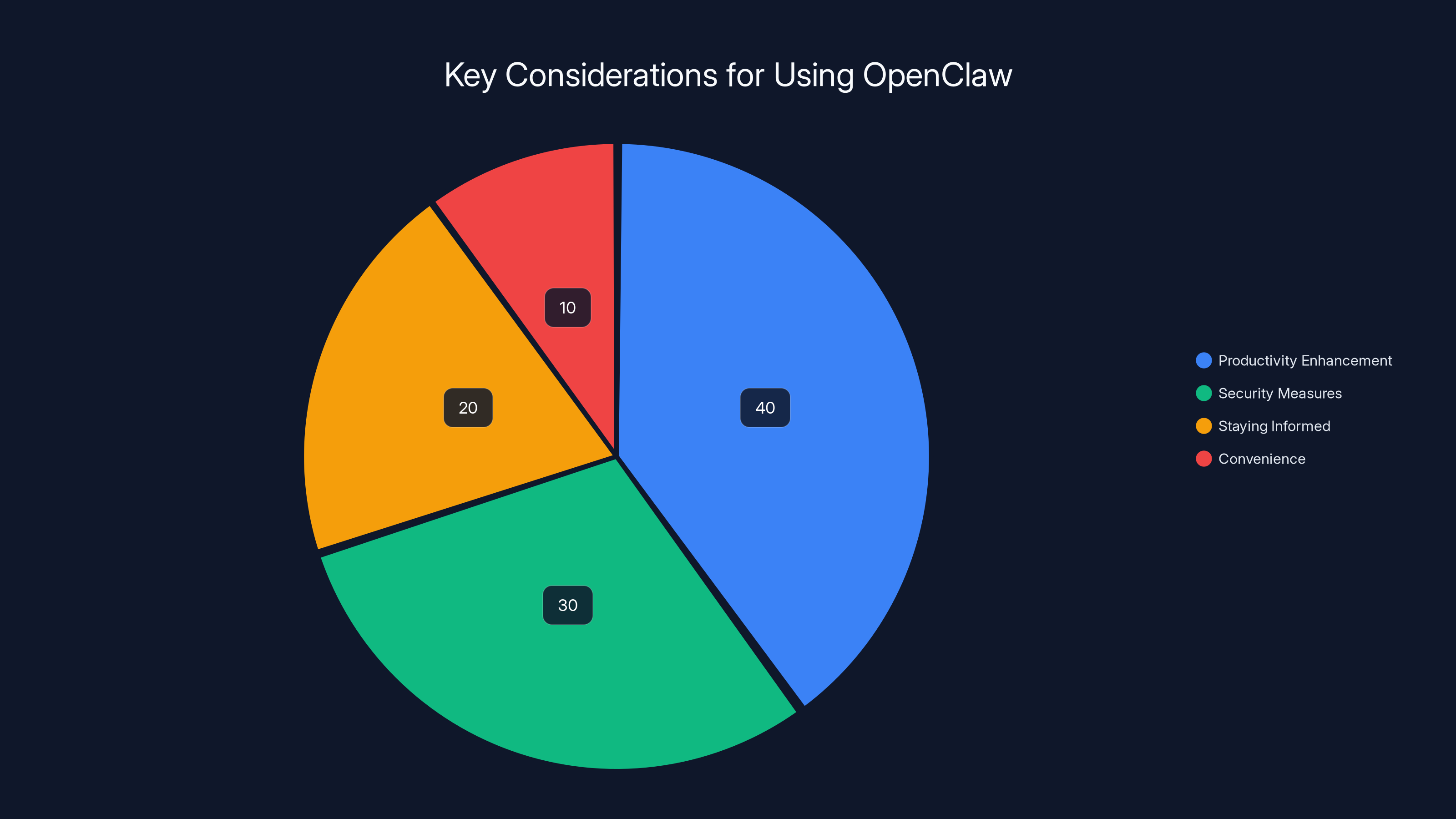
Estimated data shows productivity enhancement as the primary focus, followed by security measures. Estimated data.
Common Pitfalls and Solutions
Pitfall 1: Over-reliance on AI Agents
Relying too heavily on AI can lead to complacency in security practices. Fortune Business Insights warns against the dangers of over-reliance on automation.
Solution: Maintain manual oversight and regularly review AI agent activities.
Pitfall 2: Ignoring Configuration Management
Neglecting regular updates and configuration management can expose systems to risks. NVIDIA provides guidelines on effective configuration management.
Solution: Implement automated configuration management tools and practices.
Pitfall 3: Inadequate User Training
Users unaware of security risks contribute to vulnerabilities. Medium highlights the importance of user training in preventing security breaches.
Solution: Conduct regular training sessions and simulate phishing attacks to raise awareness.

Future Trends in AI Security
Enhanced AI Security Protocols
Expect advancements in AI security protocols that will provide better protection against sophisticated attacks. CCN discusses the evolving landscape of AI security protocols.
Integration with Blockchain Technology
Blockchain's immutable and transparent nature could enhance data security and integrity for AI applications. China Daily reports on the potential of blockchain integration in AI security.
AI-Driven Threat Detection
AI-driven tools will become more adept at detecting and mitigating threats in real-time. Reuters highlights advancements in AI-driven threat detection.

Practical Implementation Guide for Open Claw
Step 1: Assess Your Needs
Determine which Open Claw features align with your organizational goals.
Step 2: Configure Security Settings
Set up multi-factor authentication and configure access controls.
Step 3: Regularly Update the System
Keep Open Claw and its dependencies updated to protect against vulnerabilities.
Step 4: Conduct Security Audits
Schedule regular audits to identify and rectify security weaknesses.
Step 5: Train Your Team
Ensure team members are aware of best practices and security protocols.
Conclusion
Open Claw offers tremendous potential to enhance productivity through AI automation. However, users must be mindful of the security risks involved. By implementing robust security measures and staying informed about potential threats, you can leverage Open Claw safely and effectively. As AI technology continues to evolve, so too must our approach to security, ensuring that convenience and safety go hand in hand.
Use Case: Automate your weekly reports with AI, saving valuable time and resources.
Try Runable For Free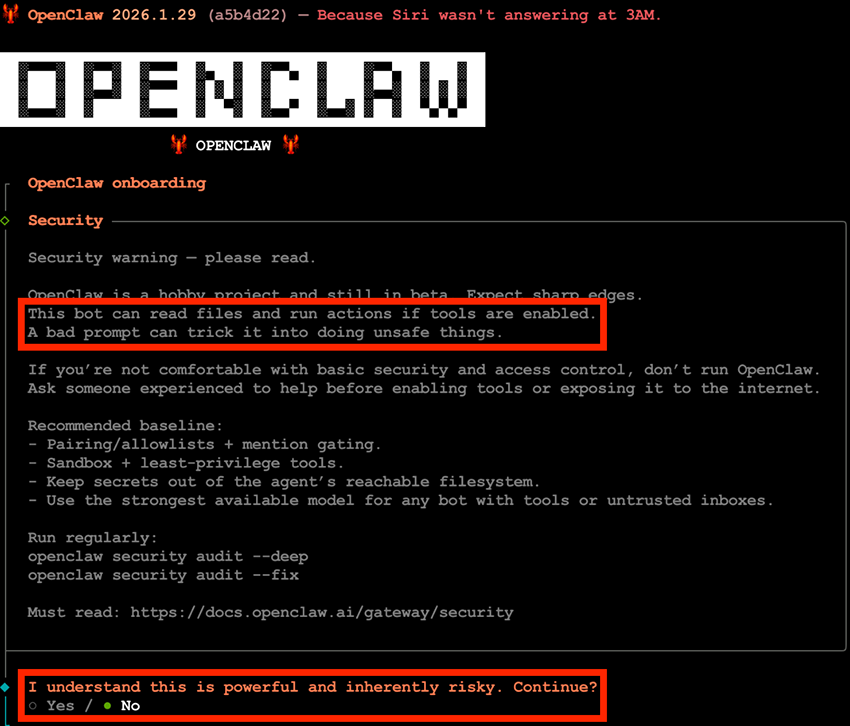
FAQ
What are the primary security risks of using Open Claw?
The primary risks include unauthorized data access, command injection vulnerabilities, email phishing risks, data privacy concerns, and misconfiguration issues.
How can I mitigate Open Claw security risks?
Implement strong authentication, conduct regular security audits, manage access controls, use secure coding practices, and educate users about potential risks.
What is the role of AI in enhancing security?
AI can help detect and mitigate threats in real-time, identify patterns of suspicious behavior, and automate security processes.
How does Open Claw integrate with other systems?
Open Claw can integrate with various systems through APIs, allowing for seamless data exchange and enhanced automation capabilities.
What future trends should I watch for in AI security?
Keep an eye on enhanced AI security protocols, integration with blockchain technology, and advancements in AI-driven threat detection.
Why is user education important in AI security?
Educating users about security risks and safe practices helps prevent human errors that could lead to security breaches.
The Best AI Automation Tools at a Glance
| Tool | Best For | Standout Feature | Pricing |
|---|---|---|---|
| Runable | AI automation | AI agents for presentations, docs, reports, images, videos | $9/month |
| Tool 1 | AI orchestration | Integrates with 8,000+ apps | Free plan available; paid from $19.99/month |
| Tool 2 | Data quality | Automated data profiling | By request |
Quick Navigation:
- Runable for AI-powered presentations, documents, reports, images, videos
- Tool 1 for AI orchestration
- Tool 2 for data quality
Key Takeaways
- Understand Open Claw Risks: Be aware of data access, injection vulnerabilities, and phishing risks.
- Adopt Mitigation Practices: Use strong authentication, audits, and access controls.
- Stay Informed: Keep up with AI security trends and advancements.
- Balance Convenience with Security: Implement measures to protect data while leveraging AI automation.
- Regular Training: Educate users to prevent human errors leading to security breaches.
- Conduct Regular Audits: Identify and mitigate security weaknesses proactively.
- Embrace Future Trends: Prepare for AI-driven security enhancements and blockchain integration.
Related Articles
- 10 Innovative Projects Built with OpenClaw [2025]
- AI and Bots Overtake Human Traffic: Navigating the New Internet Landscape [2025]
- AI Security: Understanding and Mitigating Risks in the AI Era [2025]
- Apple Will Push Out Rare ‘Backported’ Patches to Protect iOS 18 Users From DarkSword Hacking Tool | WIRED
- Apple Turns 50: Celebrating Half a Century of Innovation and Influence [2025]
- Meta Held Accountable for Teen Harm: Navigating the New Landscape [2025]
![Unveiling OpenClaw Security Risks You Must Know About [2025]](https://tryrunable.com/blog/unveiling-openclaw-security-risks-you-must-know-about-2025/image-1-1775041442168.jpg)



