Understanding Supply Chain Attacks: Lessons from the Open AI Data Breach [2025]
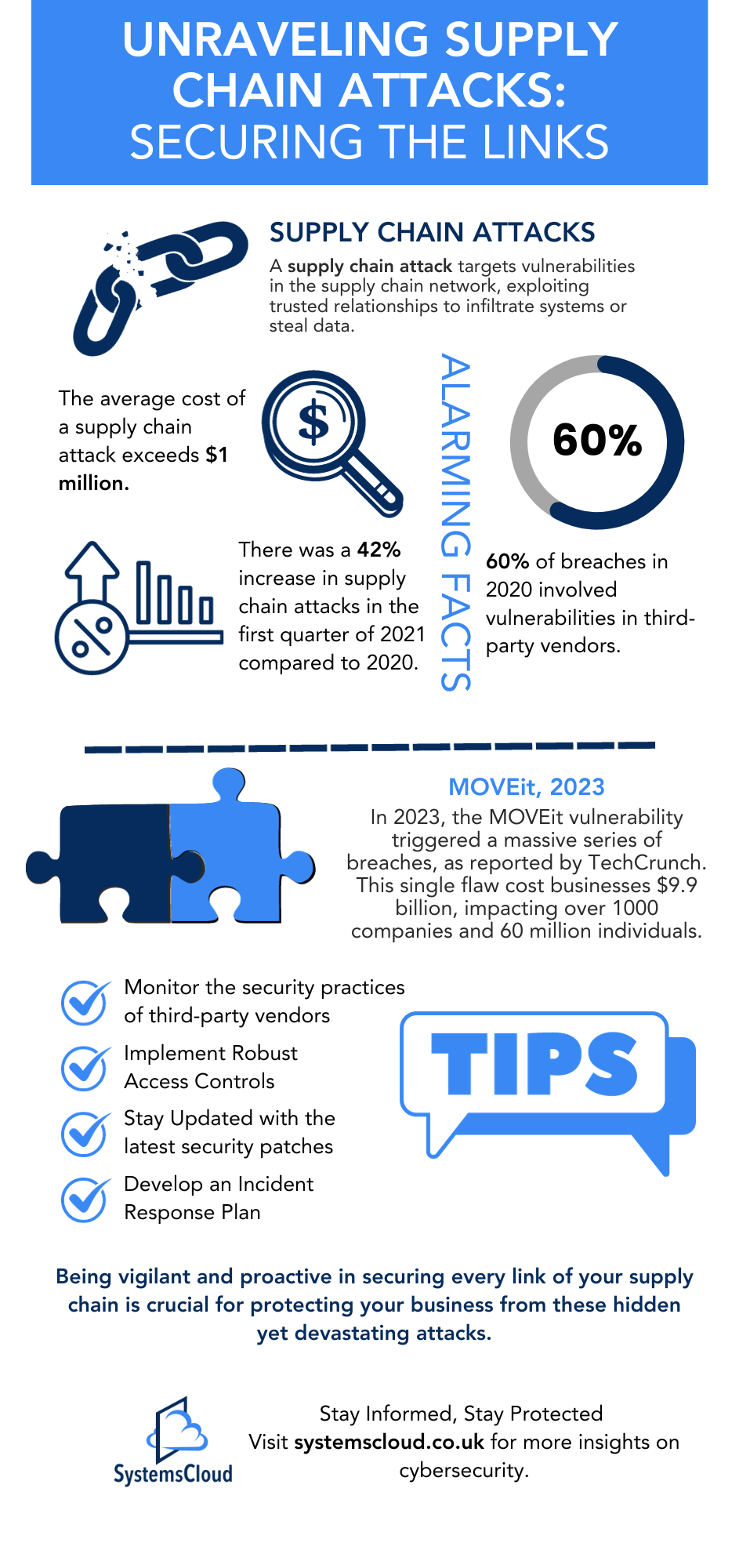
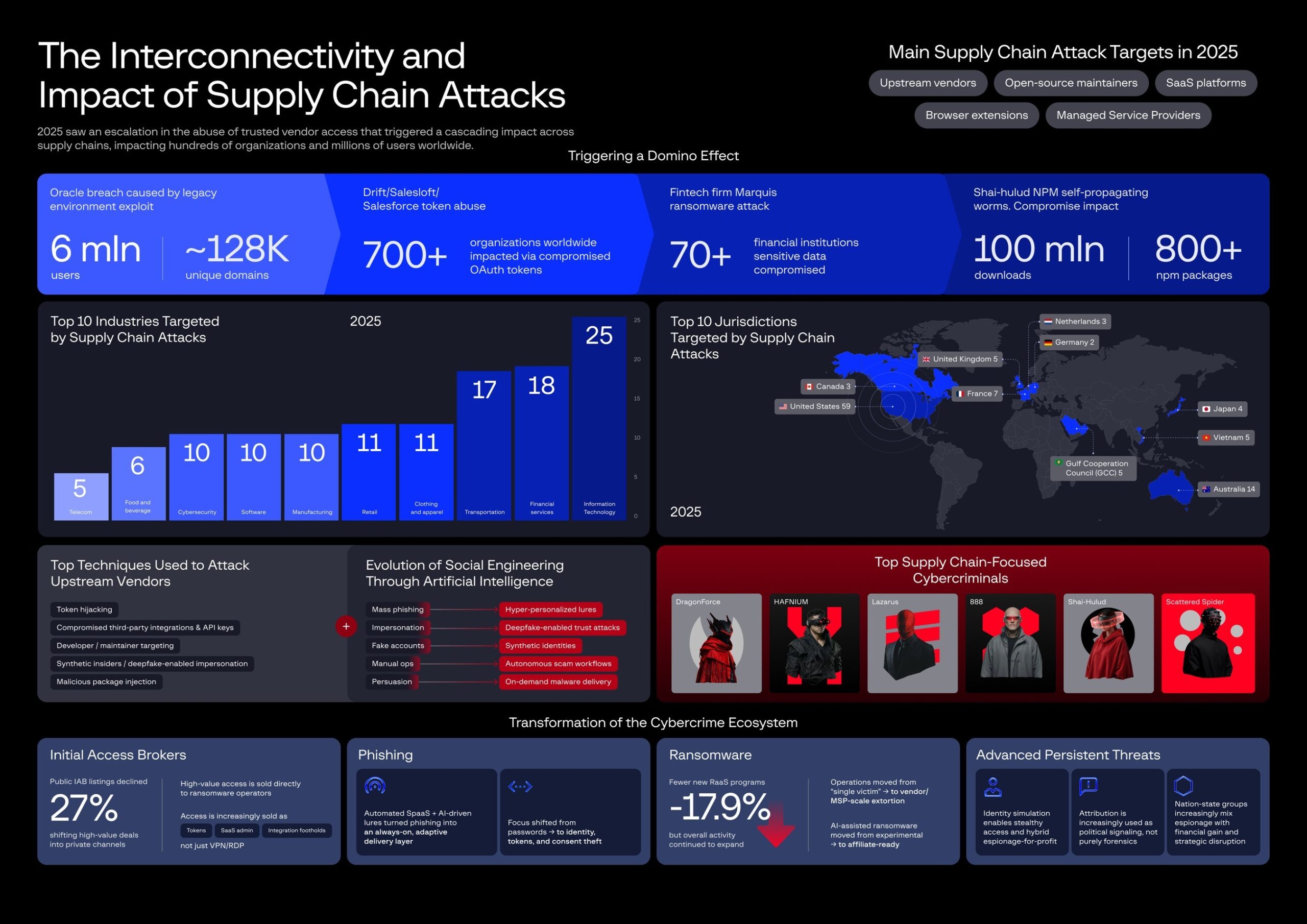
Supply chain attacks have become a significant threat in the cybersecurity landscape, impacting companies worldwide, including tech giants like OpenAI. These attacks exploit vulnerabilities in the software supply chain, allowing malicious actors to inject harmful code into widely-used open source projects. This article explores the recent OpenAI data breach, the mechanics of supply chain attacks, and strategies to mitigate such risks.
TL; DR
- Supply Chain Attacks Explained: Attackers compromise software dependencies, affecting many users.
- OpenAI Incident: Two employee devices were compromised, but no user data was accessed, as confirmed by OpenAI.
- The Tan Stack Breach: A key vector in the attack, leading to malicious software versions.
- Mitigation Strategies: Regular audits, code signing, and dependency checks are crucial.
- Future Trends: Expect more sophisticated attacks as software dependencies grow.

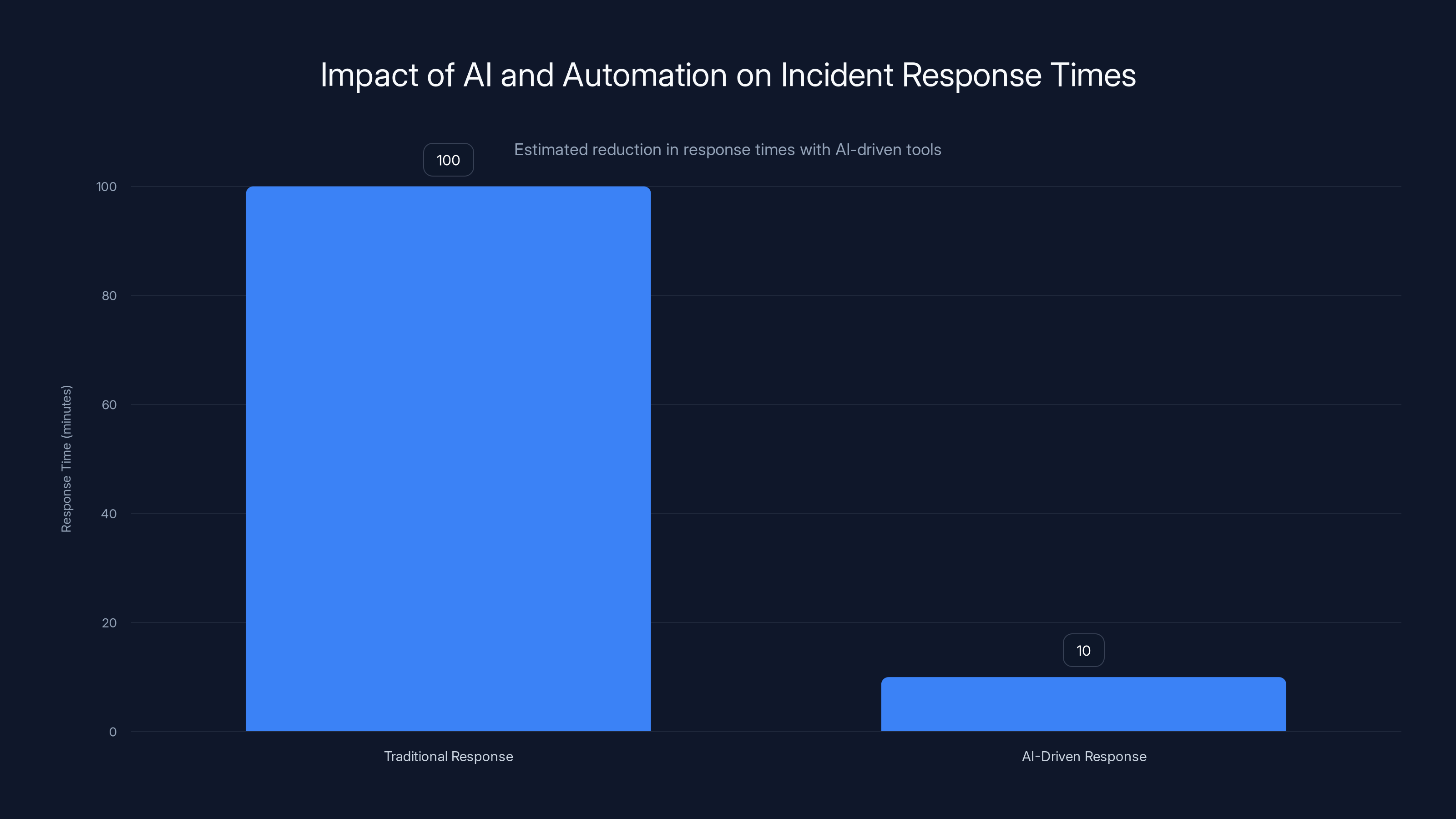
AI-driven security tools can significantly reduce incident response times, potentially by up to 90%, enhancing supply chain security. (Estimated data)
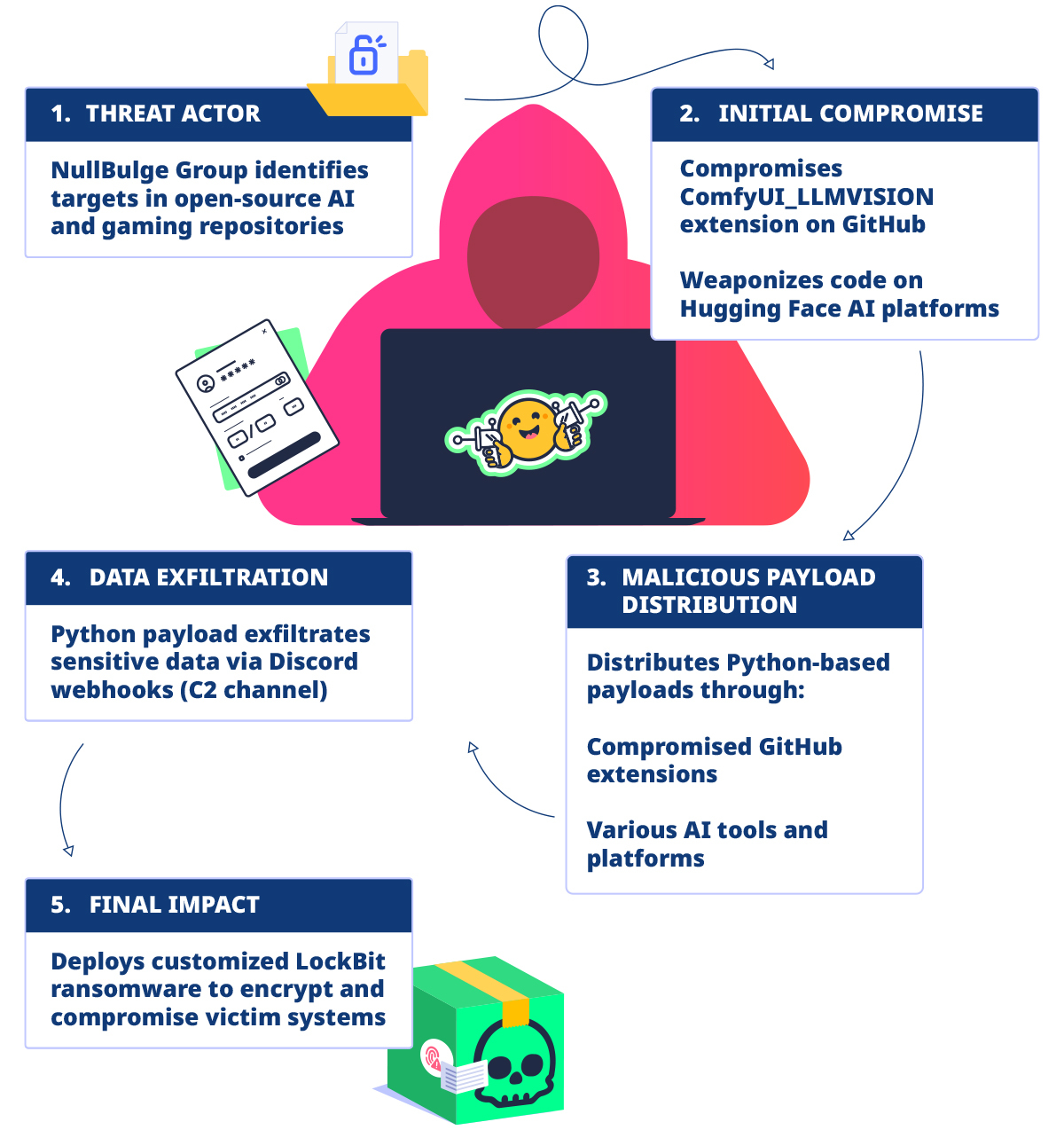
What Are Supply Chain Attacks?
Supply chain attacks target the software development process by infiltrating the development or distribution systems to introduce malicious code. This type of attack is particularly insidious because it leverages trusted relationships and components, making detection challenging.
How They Work
Attackers typically identify a vulnerability in a popular open source project or a widely-used library. By compromising this component, they can introduce malicious code that propagates to any software built with that component.
- Step 1: Identify Target: Hackers choose a target with a broad user base to maximize impact.
- Step 2: Exploit Vulnerability: They exploit a known or new vulnerability in the software or its processes.
- Step 3: Deploy Malicious Code: The compromised component is updated with malicious code.
- Step 4: Spread Through Updates: The infected component spreads as users download updates.
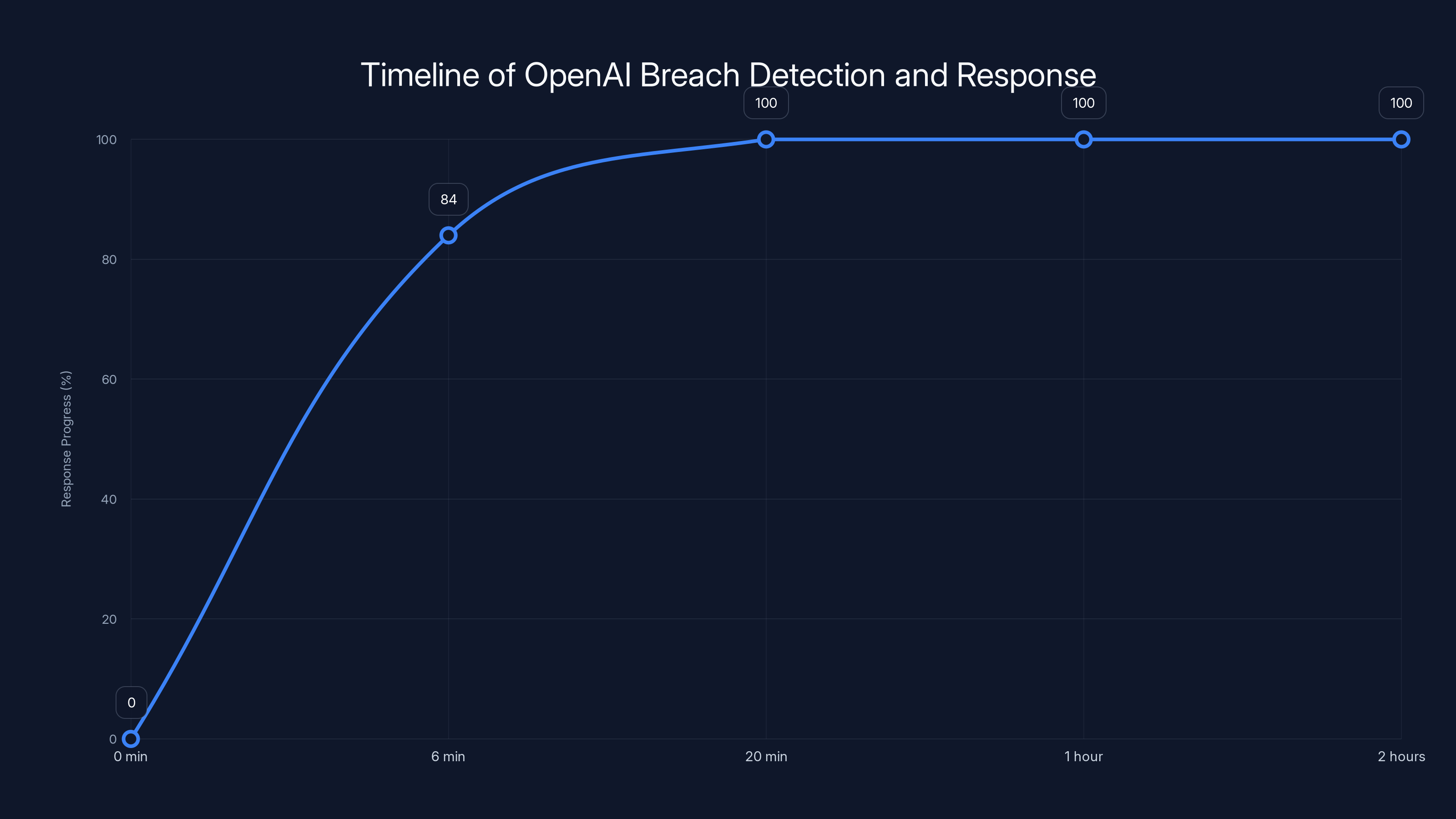
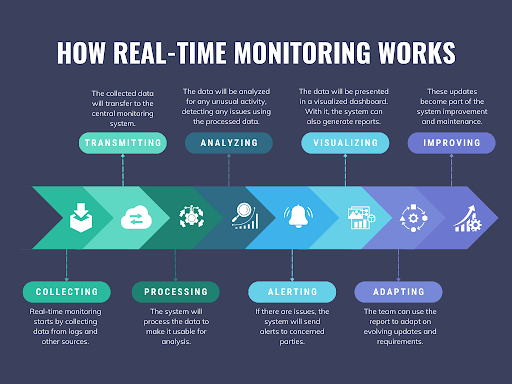
OpenAI detected the breach within 20 minutes and initiated containment, showcasing effective real-time monitoring and response. Estimated data based on incident details.
The Open AI Breach: A Case Study
In a recent incident, OpenAI reported that two of its employees' devices were compromised due to a supply chain attack targeting Tan Stack, an open source library. Despite this breach, OpenAI stated that no user data was accessed, and their core systems remained secure, as detailed by Reuters.
Incident Overview
The breach was traced back to a vulnerability in Tan Stack, which hackers exploited to publish 84 malicious versions of the software in a brief six-minute window, according to GBHackers. OpenAI's swift response and robust security measures prevented further damage.
- Detection & Response: The attack was detected within 20 minutes, highlighting the importance of real-time monitoring.
- Containment: OpenAI isolated the affected devices and conducted a thorough investigation to ensure no further systems were compromised.
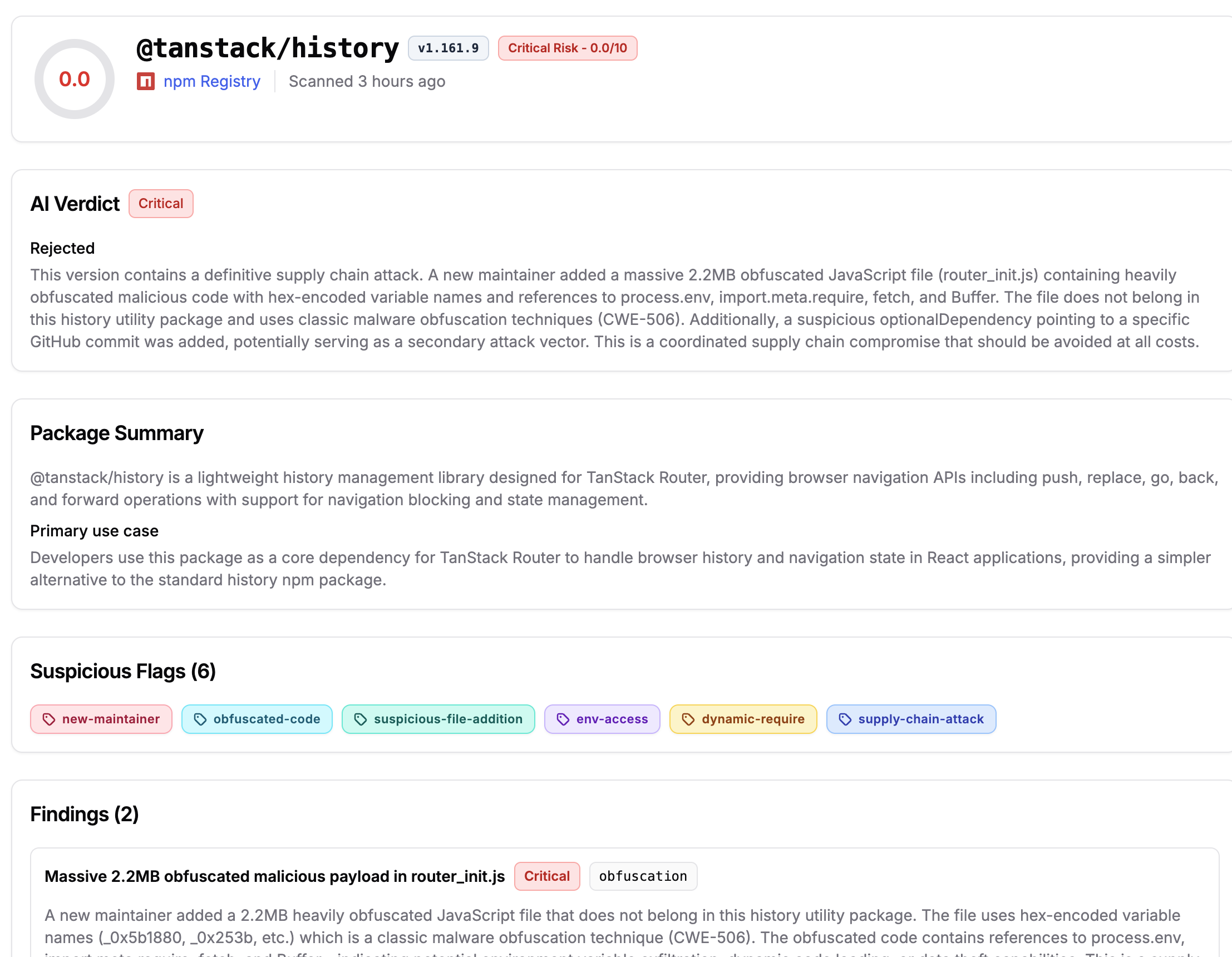
Technical Breakdown: How Tan Stack Was Compromised
Tan Stack, used by many developers for building web applications, became the focal point of this attack. Let's delve into how the attackers breached Tan Stack and the lessons learned.
Exploiting Vulnerabilities
The attackers gained access to Tan Stack's update mechanism, allowing them to inject malicious code into the library. This code was then distributed unknowingly to users updating their software dependencies, as reported by Rescana.
- Code Injection: Malicious code was injected into Tan Stack's repository, unnoticed due to insufficient security checks.
- Rapid Propagation: Within minutes, developers using Tan Stack began integrating the compromised code into their projects.
Lessons Learned
- Regular Audits: Conduct frequent security audits of all components and dependencies.
- Code Signing: Implement cryptographic code signing to ensure authenticity and integrity of software updates.
- Dependency Management: Use tools that monitor and alert on changes to dependencies.
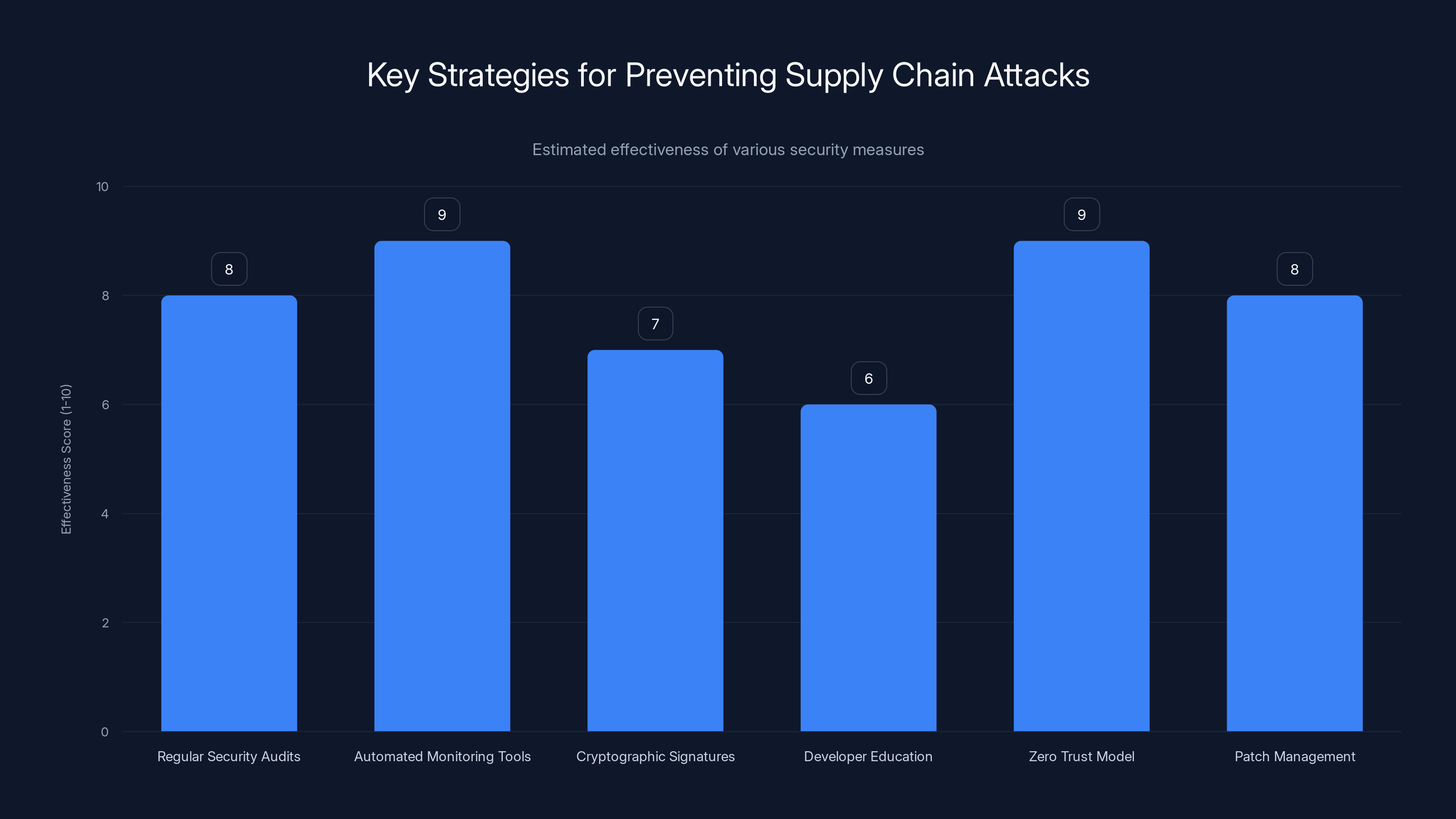
Automated monitoring tools and zero trust models are among the most effective strategies for preventing supply chain attacks. (Estimated data)
Mitigation Strategies Against Supply Chain Attacks
To protect against supply chain attacks, organizations must adopt a multi-layered approach to security, focusing on both prevention and rapid response.
Best Practices
- Conduct Security Audits: Regularly audit code and dependencies for vulnerabilities.
- Implement Code Signing: Use cryptographic signatures to verify the integrity of software packages.
- Use Automated Tools: Deploy tools that track and alert on changes to software dependencies.
- Educate Developers: Train developers on secure coding practices and awareness of supply chain risks.
Real-Time Monitoring
Implementing real-time monitoring systems can drastically reduce the time to detect and respond to breaches, as demonstrated by the quick detection in the OpenAI incident.
- Log Analysis: Continuously analyze logs for unusual activity.
- Anomaly Detection: Use machine learning to identify patterns that deviate from the norm.
Common Pitfalls and Solutions
Even with robust security measures, organizations can fall victim to supply chain attacks if they're not vigilant. Here are common pitfalls and how to avoid them.
Overlooking Small Dependencies
Small, seemingly insignificant dependencies can pose significant risks if overlooked. Always vet and monitor even minor components in your software stack.
- Solution: Maintain an inventory of all dependencies and their sources, as suggested by NetSuite.
Delayed Patch Management
Falling behind on patches and updates can leave systems vulnerable to known exploits.
- Solution: Implement a patch management policy that prioritizes critical updates.

Future Trends in Supply Chain Security
As supply chain attacks become more sophisticated, organizations must evolve their security strategies. Here are some trends to watch.
Increased Adoption of AI and Automation
Artificial intelligence and automation will play key roles in enhancing supply chain security by enabling faster detection and response.
- AI-Driven Analysis: Using AI to analyze vast amounts of data for potential threats, as highlighted by IBM.
- Automated Responses: Automating mitigation actions to reduce response time.
Zero Trust Architectures
Adopting a zero trust model, where every component and user is continuously verified, will become essential in mitigating supply chain risks.
- Continuous Verification: Regularly authenticate and authorize users and components.
- Micro-Segmentation: Divide networks into smaller, isolated segments to contain breaches.

Practical Implementation Guide
Implementing effective supply chain security is a comprehensive process that involves planning, execution, and continuous improvement. Here’s a step-by-step guide to bolster your defenses.
Step 1: Assess Your Current Security Posture
- Conduct a Security Audit: Evaluate current security measures and identify vulnerabilities.
- Inventory Your Software: List all software and dependencies in use.
Step 2: Develop a Security Strategy
- Set Security Policies: Define policies for managing software updates and dependencies.
- Plan Incident Response: Develop a detailed incident response plan for supply chain attacks.
Step 3: Implement Security Tools
- Deploy Monitoring Systems: Use tools like SIEM for real-time threat detection.
- Automate Security Tasks: Implement automated patch management and vulnerability scanning.
Step 4: Train Your Team
- Regular Training Sessions: Conduct workshops and training sessions on supply chain security.
- Phishing Simulations: Test your team's readiness with simulated phishing attacks.
Conclusion: Strengthening Your Defense
Supply chain attacks pose a significant and growing threat, but with the right strategies, organizations can protect themselves against these insidious threats. By learning from incidents like the OpenAI breach and adopting best practices, companies can secure their software supply chain and safeguard their data.
Bottom Line: Proactive security measures and continuous vigilance are essential to defending against supply chain attacks.
FAQ
What is a supply chain attack?
A supply chain attack targets the software development process by infiltrating trusted components, allowing attackers to spread malicious code through software updates.
How did the Open AI breach occur?
The breach occurred through a compromised open source library, Tan Stack, used by OpenAI employees. Hackers exploited a vulnerability to inject malicious code into the library.
What steps can companies take to prevent supply chain attacks?
Companies can implement regular security audits, use automated monitoring tools, sign code with cryptographic signatures, and educate developers on security best practices.
What is the role of AI in supply chain security?
AI enhances supply chain security by enabling faster detection and response to threats through data analysis and automated decision-making.
How does a zero trust model help in securing supply chains?
A zero trust model requires continuous verification of users and components, reducing the risk of unauthorized access and limiting the impact of breaches.
Why is patch management important in supply chain security?
Timely patch management addresses known vulnerabilities, reducing the risk of exploitation by attackers.
What are the future trends in supply chain security?
Future trends include increased use of AI and automation, adoption of zero trust architectures, and heightened focus on real-time monitoring and anomaly detection.

Key Takeaways
- Supply chain attacks exploit trusted software components, making them difficult to detect.
- OpenAI's quick response to the TanStack breach minimized potential damage.
- Regular audits and code signing are critical to preventing supply chain attacks.
- Adopting AI-driven security tools can significantly reduce incident response times.
- Implementing a zero trust model helps continuously verify and secure software components.
- Future trends include increased automation and real-time monitoring for better security.
- Educating developers on secure coding practices is essential to mitigating risks.
- Proactive security measures and continuous vigilance are key to defending against supply chain attacks.
Related Articles
- Exposing Cyber Intruders: A Deep Dive into Russian Government Hackers Targeting Signal Accounts [2025]
- Identity is the New Perimeter: The Shift from Breaking In to Logging In [2025]
- Cisco's Strategic Shift: Embracing AI and Cybersecurity Amid Workforce Reductions [2025]
- Microsoft's MDASH AI Security Platform: A Game Changer? [2025]
- Your iPhone Gets Stolen. Then the Hacking Begins | WIRED
- The Massive Banks of Malware: Visualizing the Data Giants [2025]
![Understanding Supply Chain Attacks: Lessons from the OpenAI Data Breach [2025]](https://tryrunable.com/blog/understanding-supply-chain-attacks-lessons-from-the-openai-d/image-1-1778776521157.png)



