Attack of the Killer Script Kiddies: What You Need to Know [2025]
Last year, a small company faced an unexpected $50,000 loss due to a data breach. The culprit? A 17-year-old using pre-written scripts. This isn't an isolated incident. The rise of script kiddies—young hackers using existing code to exploit systems—poses a significant threat to cybersecurity.
TL; DR
- Script kiddies are inexperienced hackers using pre-written scripts for attacks.
- Impact includes financial loss, data breaches, and reputational damage.
- Mitigation strategies involve robust security measures and employee training.
- Trends indicate increasing sophistication and use of AI tools.
- Solution: Implement layered security and continuous monitoring.
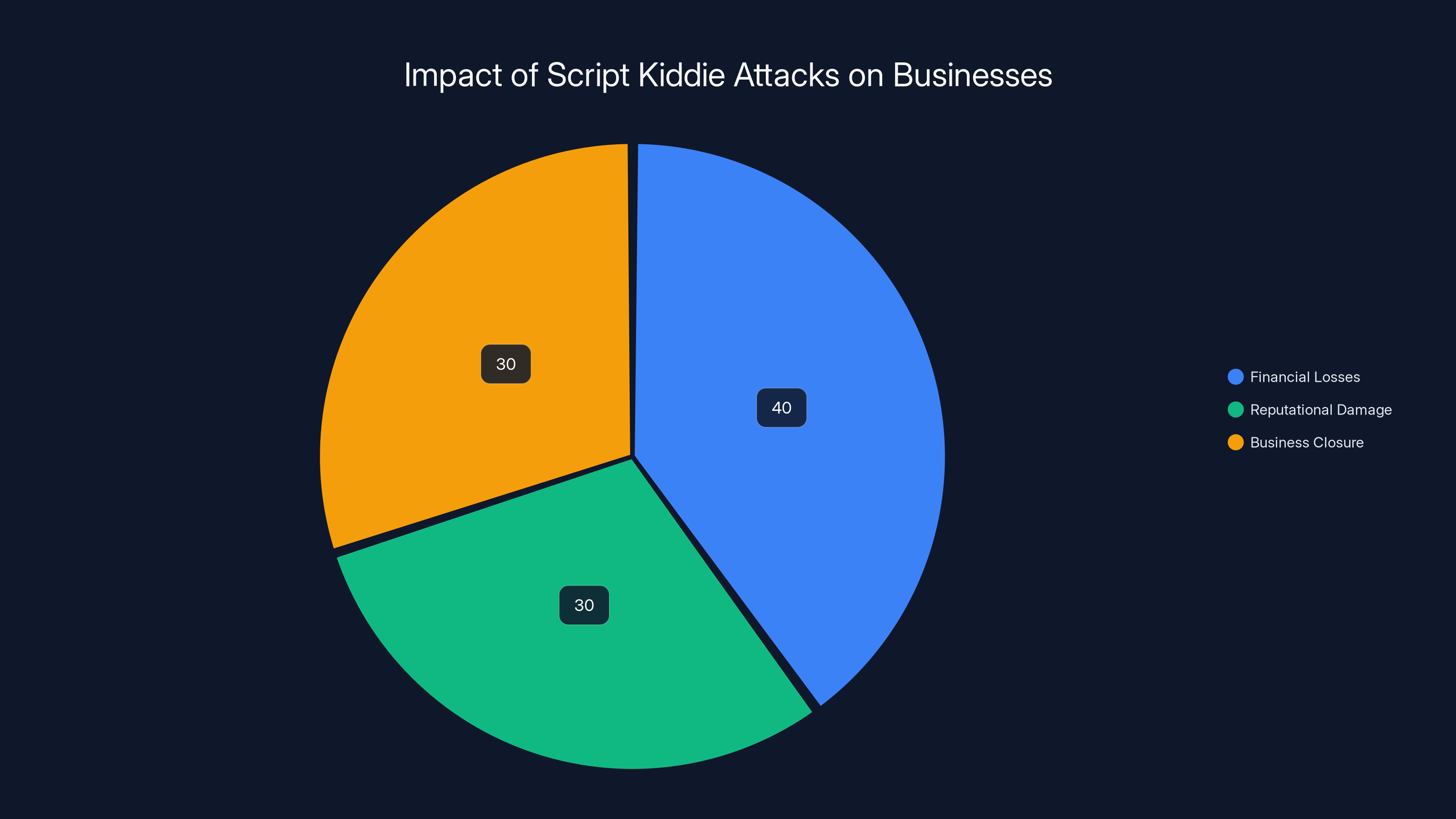
Estimated data shows that financial losses, reputational damage, and business closures are significant impacts of script kiddie attacks, with closures affecting 30% of businesses.
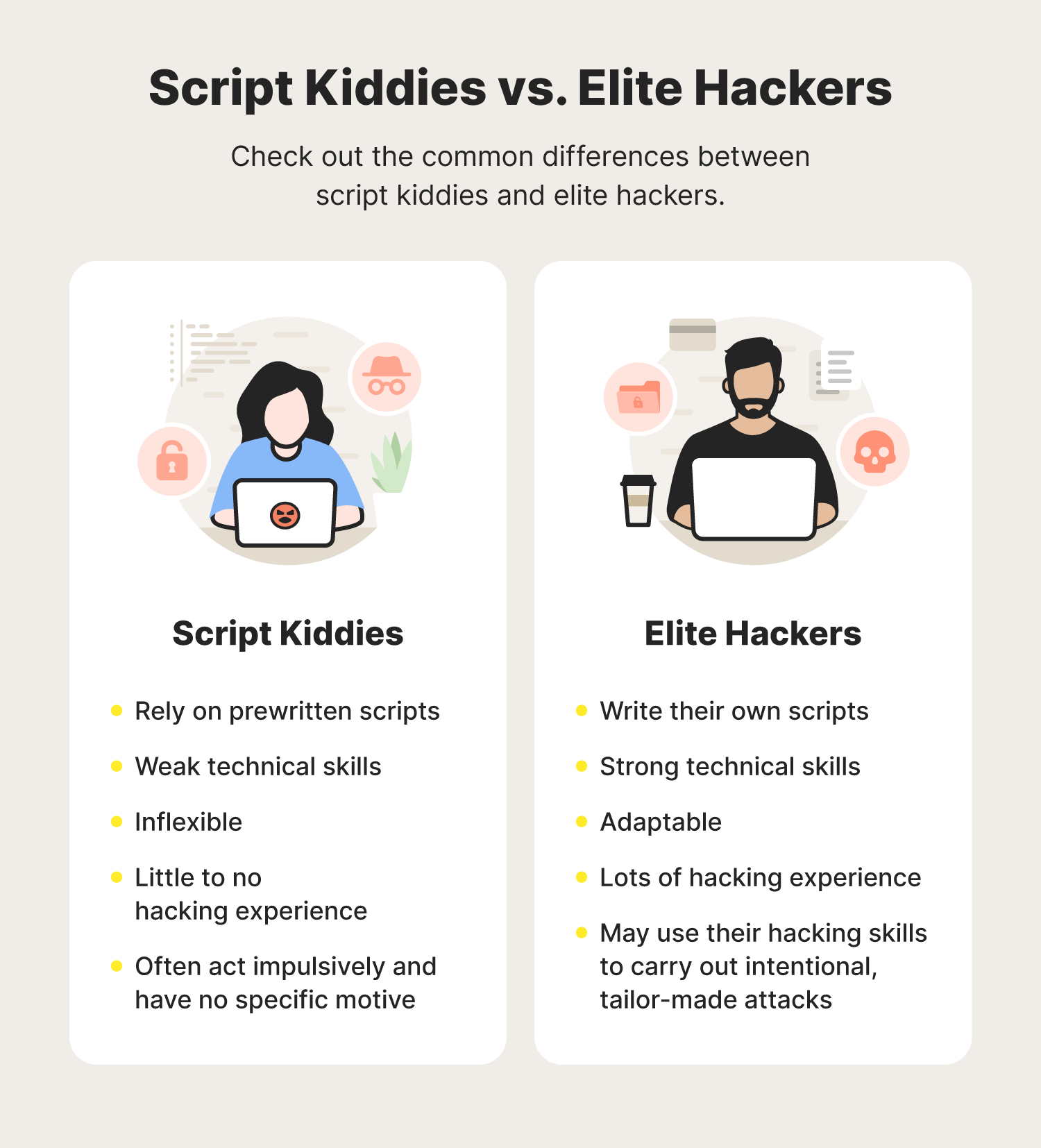
What Are Script Kiddies?
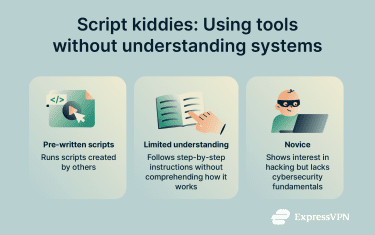
Script kiddies, often teenagers or inexperienced individuals, leverage pre-existing scripts or programs to hack into systems. Unlike seasoned hackers who write their own code, script kiddies rely on tools developed by others, making them a unique threat in the cybersecurity landscape.

The Emergence of Script Kiddies
The democratization of hacking tools has contributed to the rise of script kiddies. With the proliferation of online forums and dark web marketplaces, acquiring hacking tools and step-by-step guides has never been easier. This accessibility lowers the barrier for entry into cybercrime.
Real-World Impact
In 2023, a major retail chain suffered a data breach affecting millions of customers. The attack was traced back to a script kiddie who exploited an unpatched vulnerability in the company’s outdated software. The financial and reputational damage was immense, highlighting the serious threat posed by these amateur hackers.
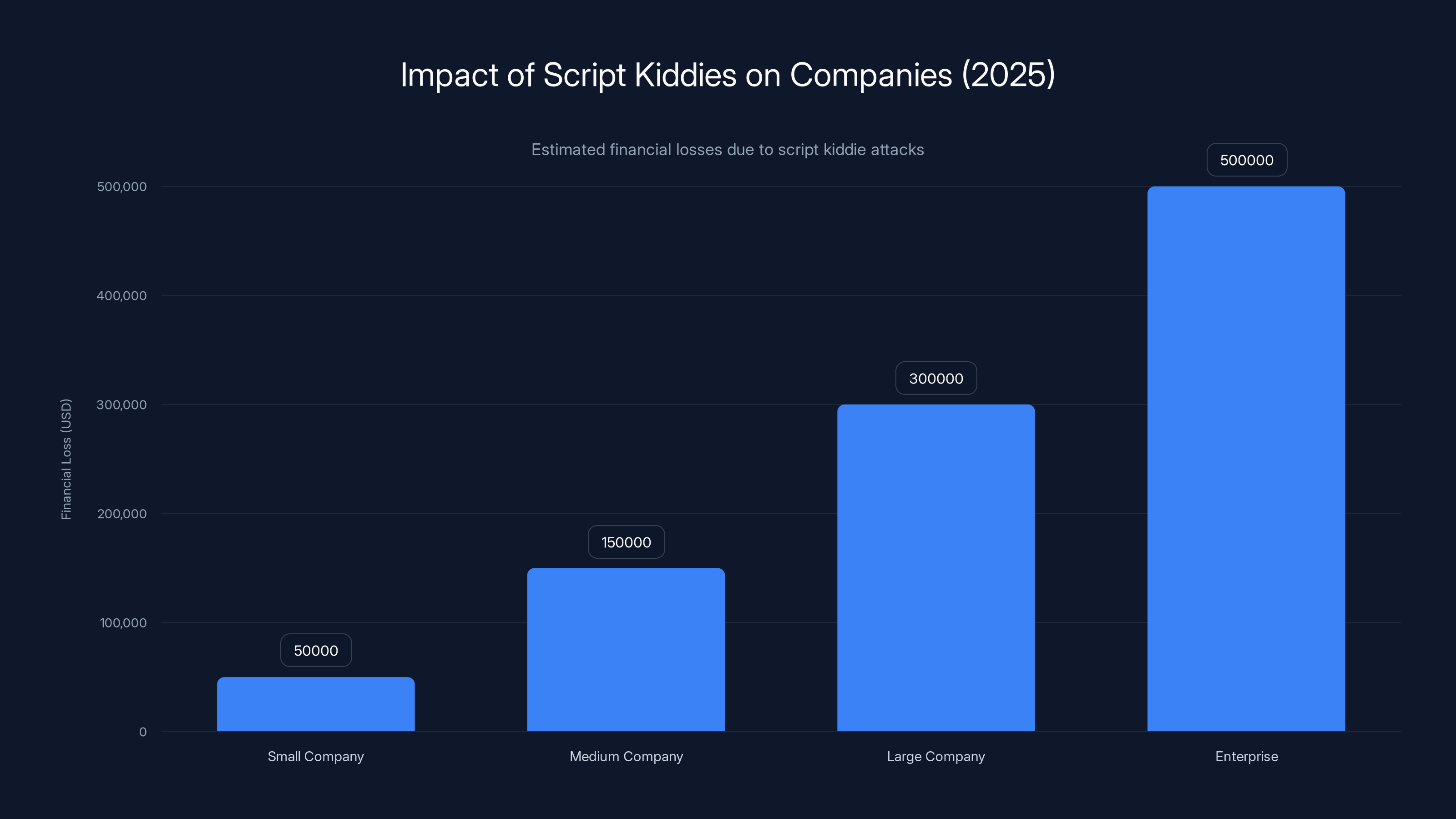
Estimated data shows that script kiddie attacks can cause significant financial losses, with larger companies potentially facing up to $500,000 in damages.
How Script Kiddies Operate
Tools of the Trade
Script kiddies often use readily available tools such as:
- Metasploit: A penetration testing framework that provides information about security vulnerabilities.
- Nmap: A network scanning tool used to discover hosts and services on a computer network.
- LOIC: Low Orbit Ion Cannon, a DDoS tool.
These tools require minimal technical knowledge, allowing script kiddies to launch effective attacks.
Exploitation Methods
- Phishing Attacks: Script kiddies often use phishing to gain access to sensitive information. By mimicking legitimate websites, they trick users into revealing credentials.
- DDoS Attacks: Using tools like LOIC, script kiddies can flood a target with traffic, causing service disruptions.
- Vulnerability Scanning: They exploit known vulnerabilities in software, often targeting unpatched systems.

The Impact of Script Kiddies
Financial Consequences
Businesses face significant financial losses due to script kiddie attacks. From data breaches to service disruptions, the cost of remediation and lost revenue can be substantial.
Reputational Damage
The public exposure of a breach can damage a company's reputation, leading to a loss of customer trust and potentially impacting the bottom line.
Mitigation Strategies
Implementing Robust Security Measures
To combat script kiddie threats, businesses must implement comprehensive security measures:
- Regular Software Updates: Ensure all systems are updated with the latest security patches.
- Firewalls and Intrusion Detection Systems (IDS): Deploy firewalls and IDS to monitor and block unauthorized access.
- Strong Password Policies: Enforce the use of strong, unique passwords and enable multi-factor authentication.
Employee Training and Awareness
Educating employees about cybersecurity best practices can reduce the risk of successful phishing and social engineering attacks. Regular training sessions and simulated phishing exercises can help maintain vigilance.
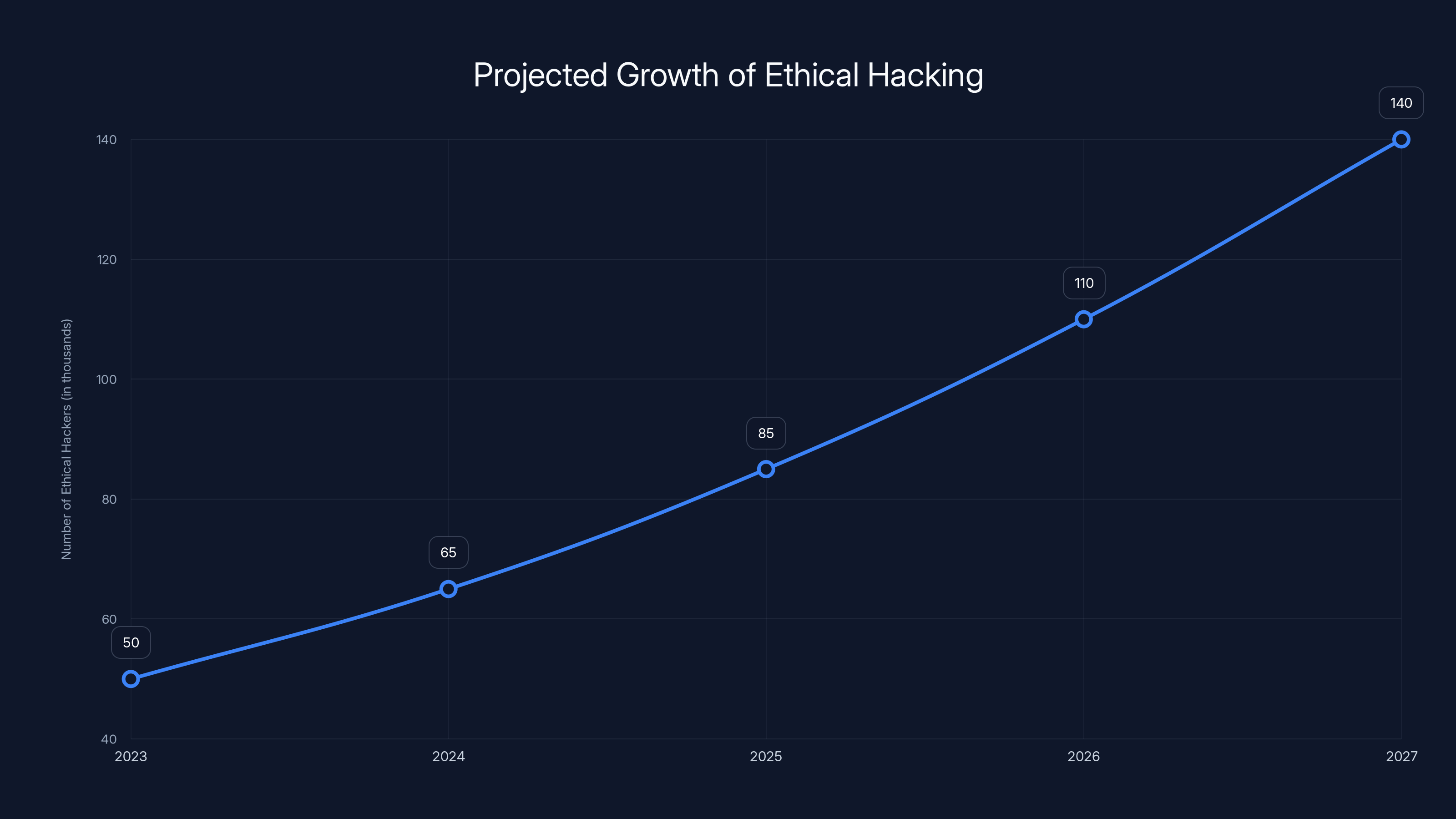
The number of ethical hackers is projected to nearly triple over the next five years, highlighting the increasing importance of cybersecurity. (Estimated data)
Future Trends
Increasing Sophistication
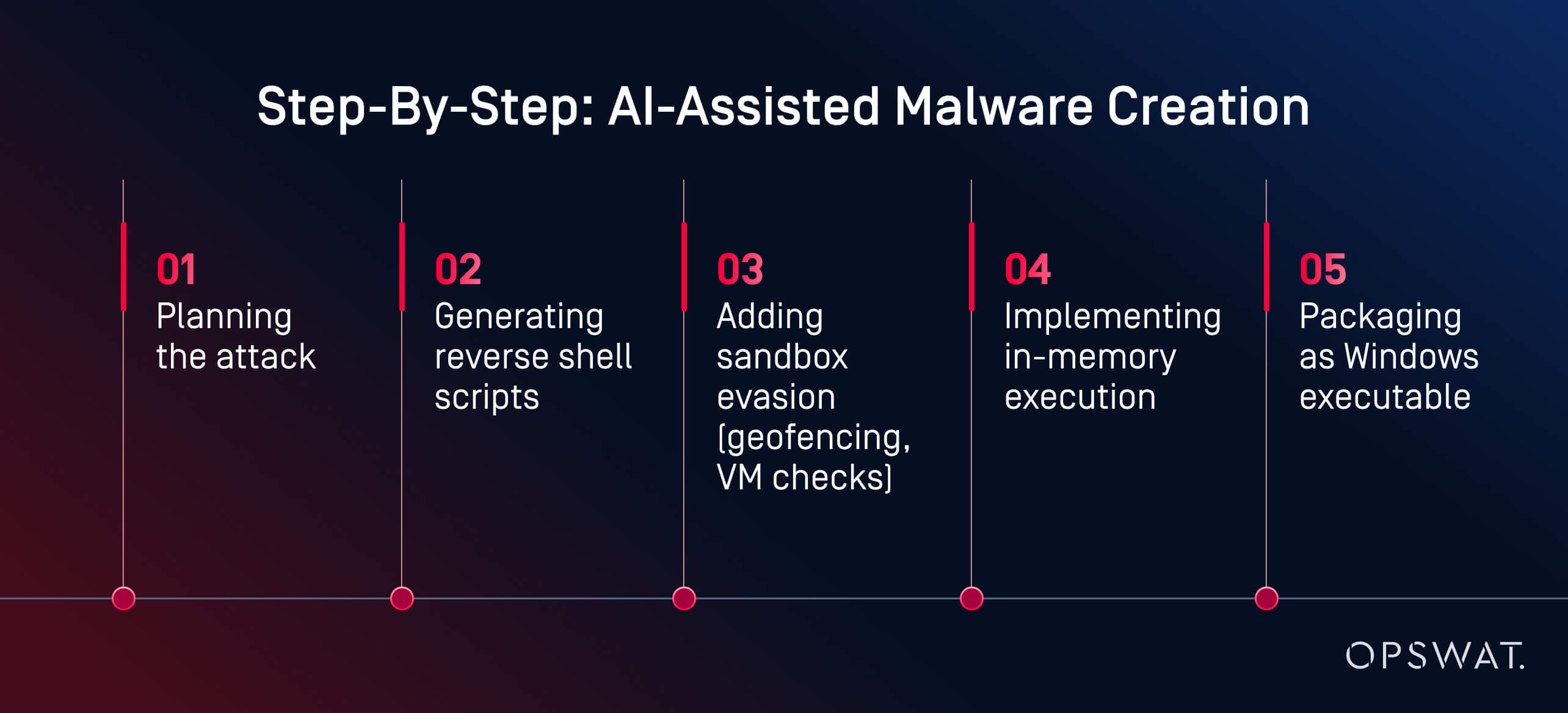
Script kiddies are becoming more sophisticated, leveraging AI and machine learning to enhance their attack capabilities. As technology advances, so do the tools available to these amateur hackers.
The Role of AI
AI-powered tools can automate the discovery of vulnerabilities and the execution of attacks, making it easier for script kiddies to launch complex operations without deep technical knowledge.
Recommendations for Organizations
Layered Security Approach
Implement a layered security approach to provide multiple lines of defense against attacks. This includes:
- Network Segmentation: Divide the network into segments to limit the spread of an attack.
- Endpoint Protection: Deploy endpoint protection solutions to secure devices against malware and unauthorized access.
- Data Encryption: Encrypt sensitive data both in transit and at rest to protect it from unauthorized access.
Continuous Monitoring and Incident Response
Establish a robust incident response plan and continuously monitor systems for suspicious activity. Early detection can prevent a minor incident from escalating into a major breach.
Common Pitfalls and Solutions
Overreliance on Technology
While technology is crucial, overreliance can lead to complacency. Regular audits and manual checks should complement automated solutions to ensure comprehensive security.
Neglecting Insider Threats
Insider threats can be as damaging as external attacks. Implement strict access controls and regularly review user privileges to mitigate this risk.
Case Studies
Company X: A Lesson in Preparedness
Company X, a mid-sized firm, successfully thwarted a script kiddie attack by implementing a comprehensive security strategy. By regularly updating software, conducting employee training, and monitoring their network, they were able to detect and neutralize the threat quickly.
Company Y: The Cost of Complacency
In contrast, Company Y suffered a significant data breach due to complacency. Their reliance on outdated security measures and lack of employee training left them vulnerable, resulting in a costly recovery process.
Future Predictions
As technology evolves, script kiddies will continue to adapt. Organizations must stay ahead by investing in advanced security solutions and maintaining a proactive cybersecurity posture.
The Rise of Ethical Hacking
To counteract script kiddies, there's a growing trend of ethical hacking. Companies are hiring white-hat hackers to identify and fix vulnerabilities before they can be exploited.
Conclusion
Script kiddies may lack the sophistication of seasoned hackers, but their impact can be just as devastating. By understanding their methods and implementing robust security measures, organizations can protect themselves against this pervasive threat.
FAQ
What is a script kiddie?
A script kiddie is an inexperienced hacker who uses pre-existing scripts or programs to conduct cyberattacks without fully understanding the underlying technology.
How do script kiddies obtain their tools?
Script kiddies often acquire tools from online forums, dark web marketplaces, and open-source repositories that offer hacking scripts and tutorials.
What are the common targets of script kiddies?
Common targets include small to medium-sized businesses, vulnerable websites, and systems with unpatched security vulnerabilities.
How can organizations protect against script kiddies?
Organizations can protect against script kiddies by implementing regular software updates, strong password policies, employee training, and robust security measures like firewalls and intrusion detection systems.
Are script kiddies a growing threat?
Yes, the threat of script kiddies is growing as hacking tools become more accessible and sophisticated, allowing inexperienced individuals to launch effective cyberattacks.
This comprehensive guide on script kiddies explores their impact on cybersecurity and offers strategies for mitigation. By staying informed and proactive, organizations can reduce their risk and protect their assets.

Key Takeaways
- Script kiddies pose a significant threat due to their use of existing hacking tools.
- Financial and reputational damage can result from script kiddie attacks.
- Layered security and employee training are effective mitigation strategies.
- The sophistication of script kiddies is increasing with AI advancements.
- Organizations must adopt a proactive approach to cybersecurity.
- Ethical hacking programs can help identify vulnerabilities before exploitation.
- Continuous monitoring and incident response plans are crucial for defense.
- Overreliance on technology without manual checks can lead to vulnerabilities.
Related Articles
- China-Nexus Cyber Actors Turning IoT Infrastructure into Botnets [2025]
- Unmasking Spyware: How Fake Android Apps Are Weaponized [2025]
- Understanding the Itron Cyberattack: Impacts and Lessons [2025]
- Inside the New Cyber Scam: How Hackers Exploit Microsoft Teams to Steal Your Data [2025]
- Understanding Data Breaches: Lessons from the Rituals Membership Database Breach [2025]
- Navigating Social Media Scams: A $2.1 Billion Lesson for Consumers in 2025
![Understanding the Threat: Attack of the Killer Script Kiddies [2025]](https://tryrunable.com/blog/understanding-the-threat-attack-of-the-killer-script-kiddies/image-1-1777376391888.jpg)



