VECT: The Ransomware That's Secretly Destroying Your Data [2025]
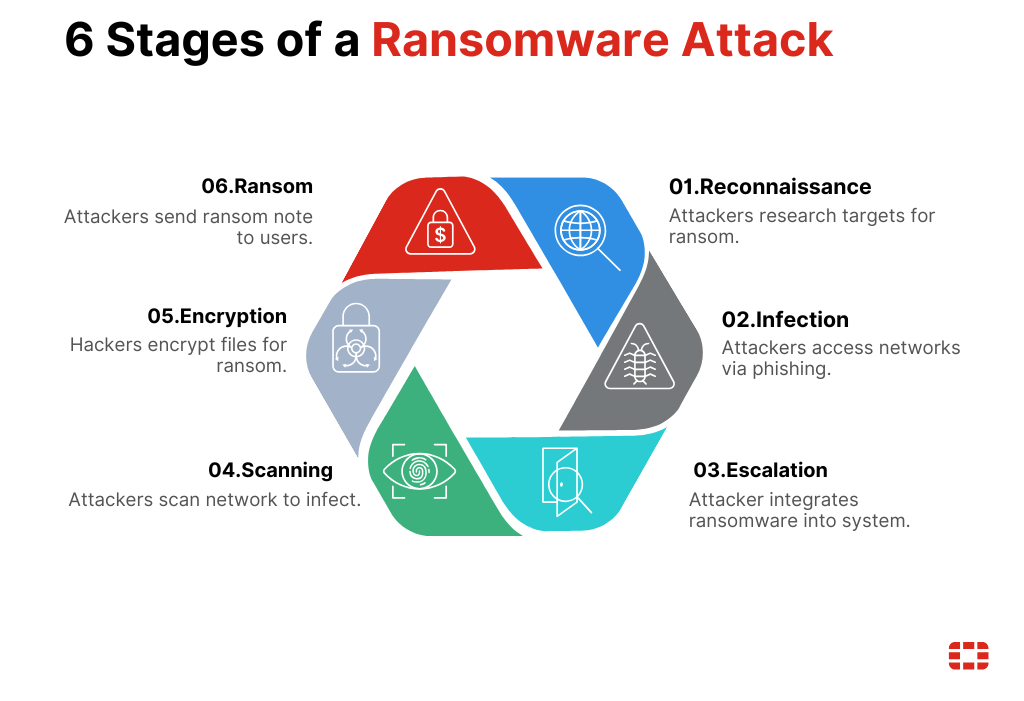
Ransomware has long been the boogeyman of the cybersecurity world, holding data hostage for ransom payments. But a new, sinister twist has emerged with the VECT ransomware. Marketed as a traditional ransomware, it’s actually functioning as a data destruction tool. This article dives into the technical details of how VECT operates, why it's different, and what you can do to protect your data.
TL; DR
- VECT ransomware: Marketed as ransomware but functions as a data wiper, as detailed in Check Point Research.
- Data destruction: Files over 128KB are completely erased, not encrypted.
- Flawed encryption: Uses weak nonce handling, leading to unpredictable outcomes.
- Protection: Backup strategies and robust security measures are crucial.
- Future trends: Expect more ransomware to adapt similar destructive tactics.
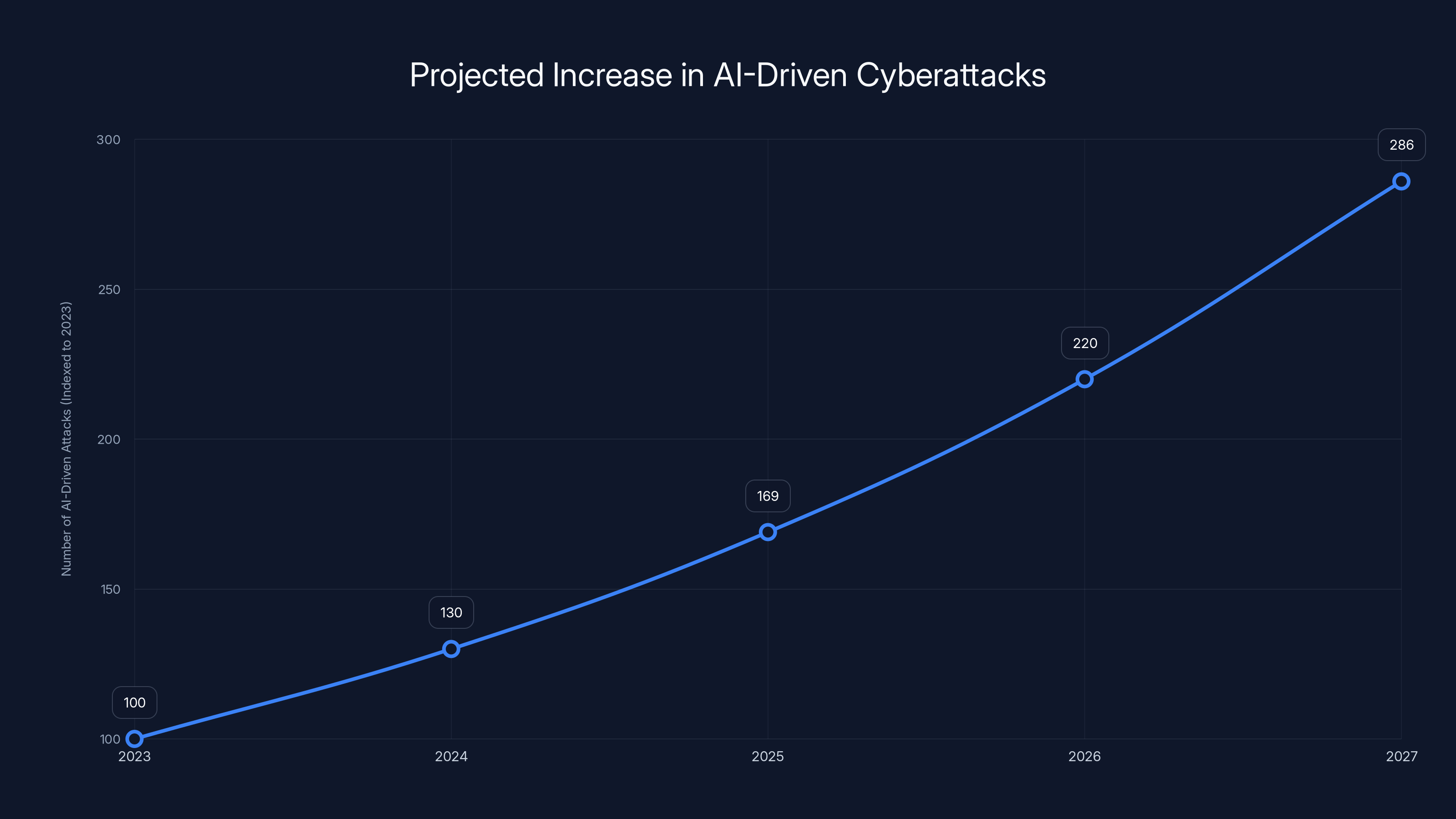
AI-driven cyberattacks are projected to increase by 30% annually, highlighting the growing integration of machine learning in ransomware strategies. Estimated data.
The Rise of VECT: A New Threat
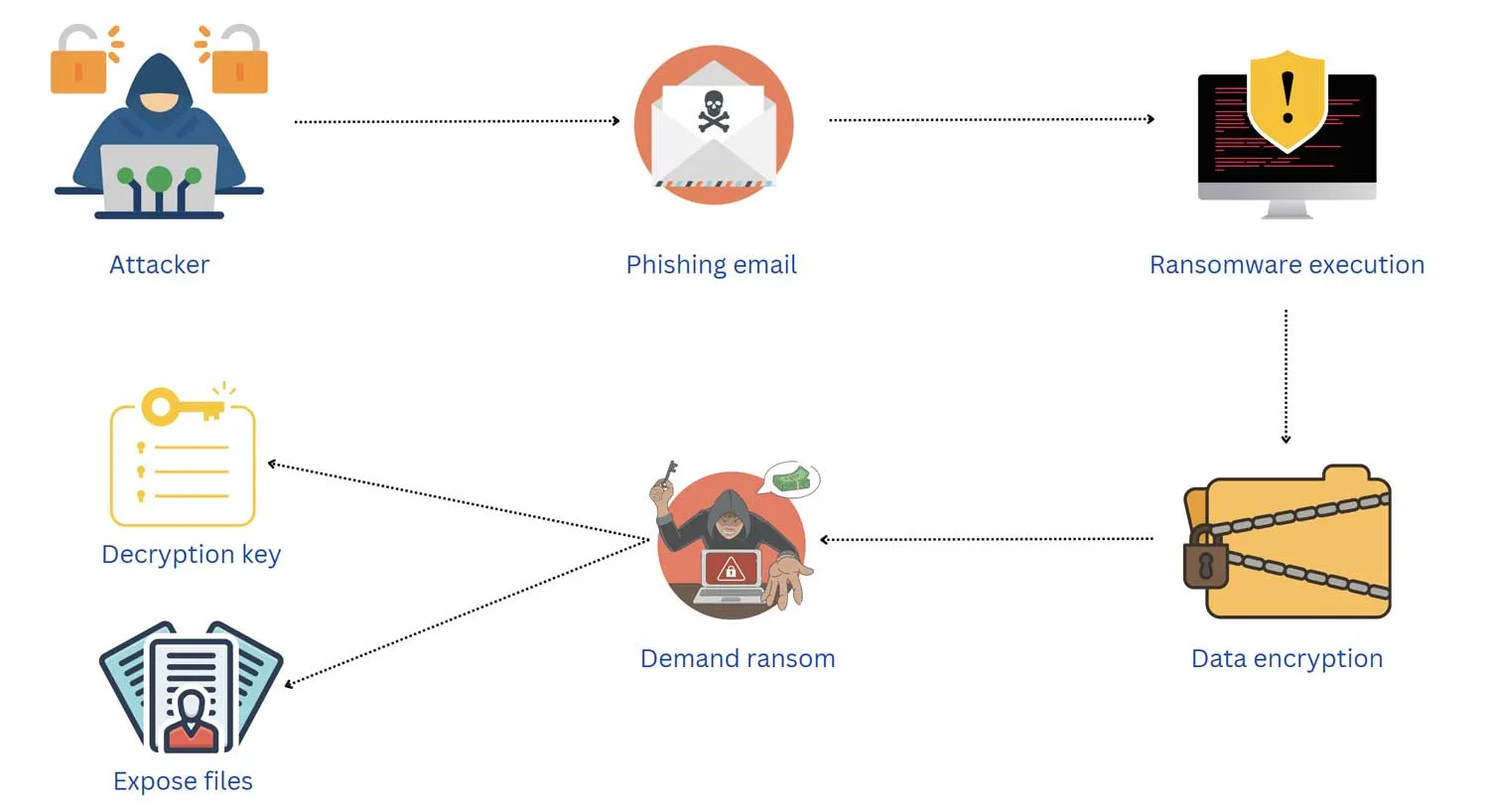
Cybercriminals are always looking for new ways to exploit vulnerabilities. VECT, a relatively new entry in the ransomware market, was initially believed to be another encrypt-and-ransom tool. However, experts soon discovered a more insidious behavior: VECT doesn’t just encrypt data; it destroys it.
How VECT Operates
VECT masquerades as standard ransomware. Upon infection, it claims to encrypt files and demands a ransom for decryption keys. But here's the catch: files larger than 128KB are irreversibly destroyed. This is due to flawed nonce handling in its encryption process, leading to data loss rather than encryption.
Technical Breakdown:
- File Targeting: VECT specifically targets files over 128KB.
- Encryption Flaw: Utilizes non-unique nonces, causing encryption errors.
- Data Wiping: Instead of encrypting, it zeros out data, making recovery impossible.
Why the Misleading Marketing?
Ransomware groups often rely on fear and urgency to extract payments. By posing as ransomware, VECT creators hope victims will pay up quickly, not realizing their data is already gone. This marketing ploy exploits the typical fear-driven ransom payment model.

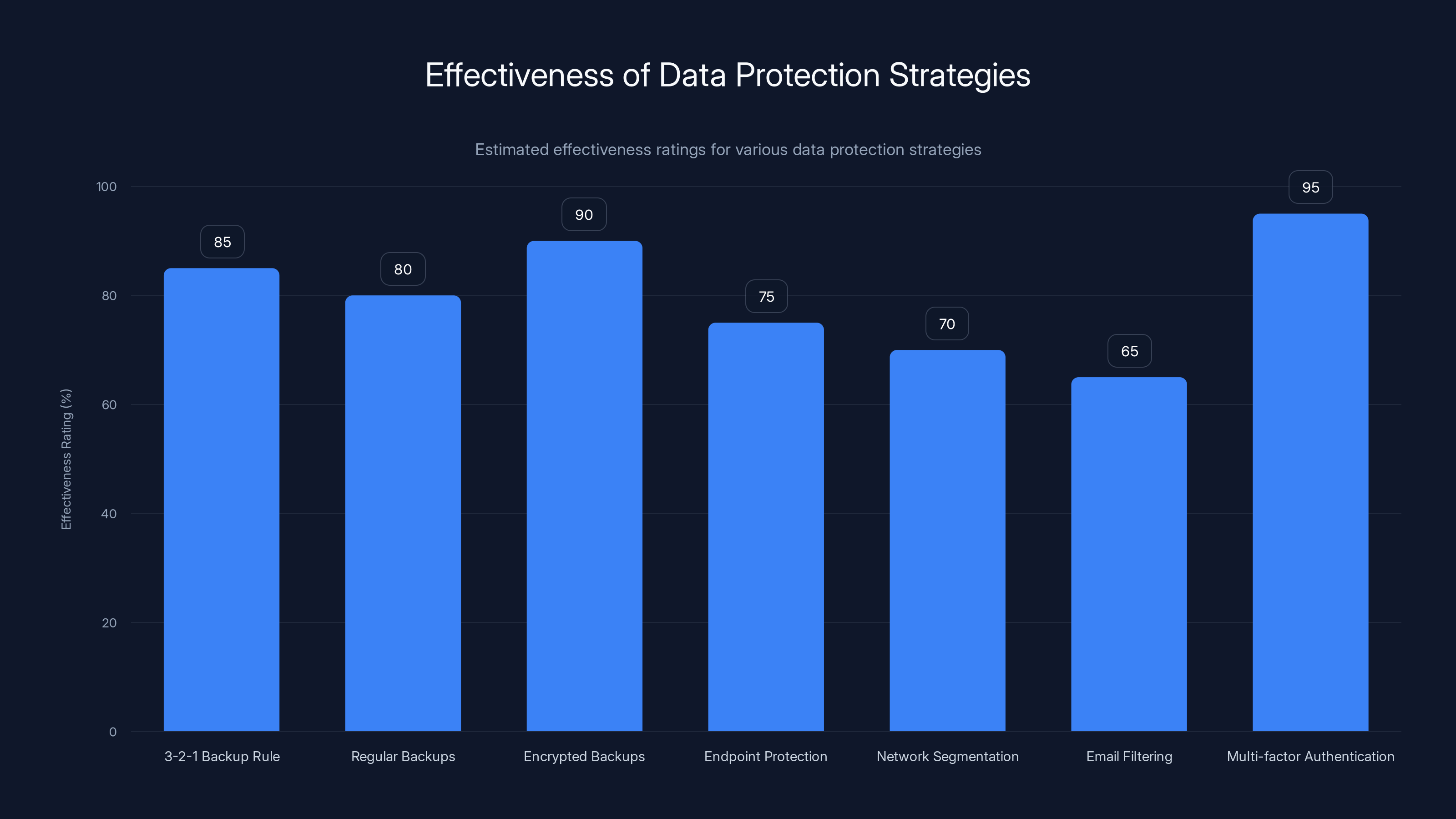
Estimated data shows that multi-factor authentication and encrypted backups are among the most effective strategies for data protection.
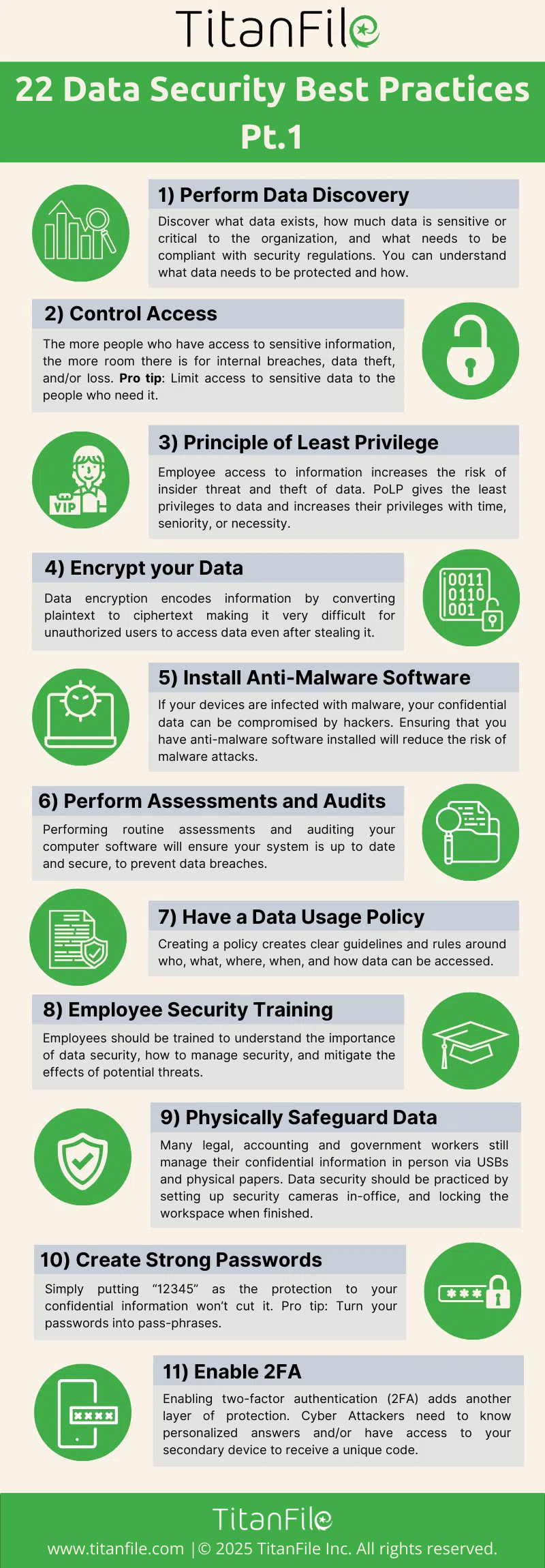
Protecting Your Data: Best Practices
Given the destructive nature of VECT, traditional ransomware defenses might not suffice. Here’s how you can bolster your cybersecurity stance to protect against data-wiping ransomware.
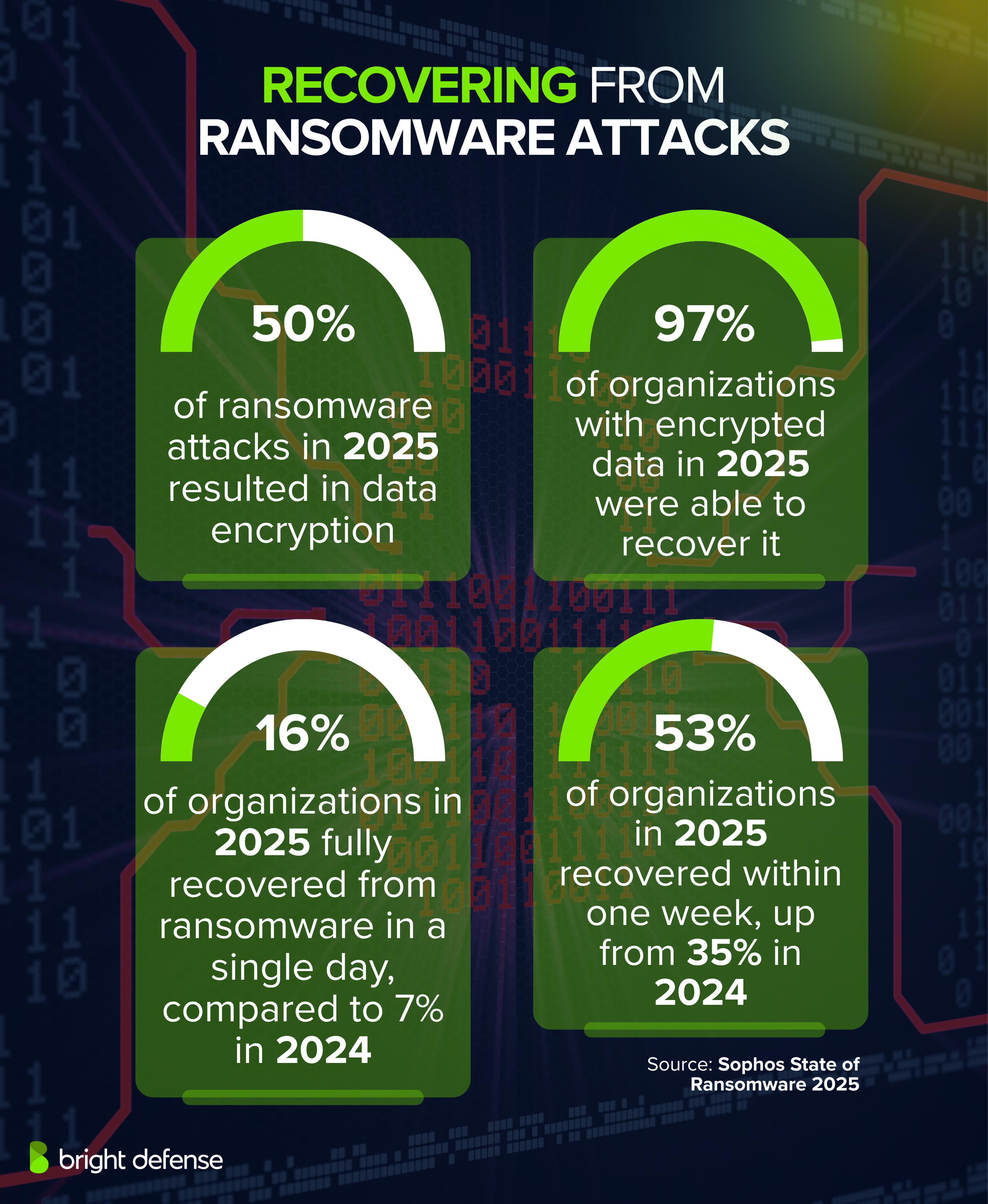
Backup Strategies
- 3-2-1 Rule: Keep three copies of your data, on two different media, with one offsite, as recommended by Forbes.
- Regular Backups: Automate backups daily or weekly, depending on data sensitivity.
- Encrypted Backups: Ensure backups are encrypted to prevent unauthorized access.
Advanced Security Measures
- Endpoint Protection: Use software with real-time scanning and behavior-based detection.
- Network Segmentation: Isolate critical systems to limit the spread of infections.
- Email Filtering: Block malicious attachments and links with advanced filters.
Understanding the Technical Flaws in VECT
VECT’s destructive capabilities stem from its flawed technical implementation. Let’s dig deeper into the encryption issues and how they lead to data wiping.
Nonce and Its Importance
A nonce is a number that can only be used once, essential for secure encryption. VECT’s failure lies in its reuse of nonces, undermining the encryption process.
Consequences of Flawed Nonce Handling
When encryption processes reuse nonces, it can lead to:
- Predictability: Makes cryptographic processes vulnerable to attacks.
- Data Destruction: In VECT’s case, it results in data being overwritten, not just encrypted.
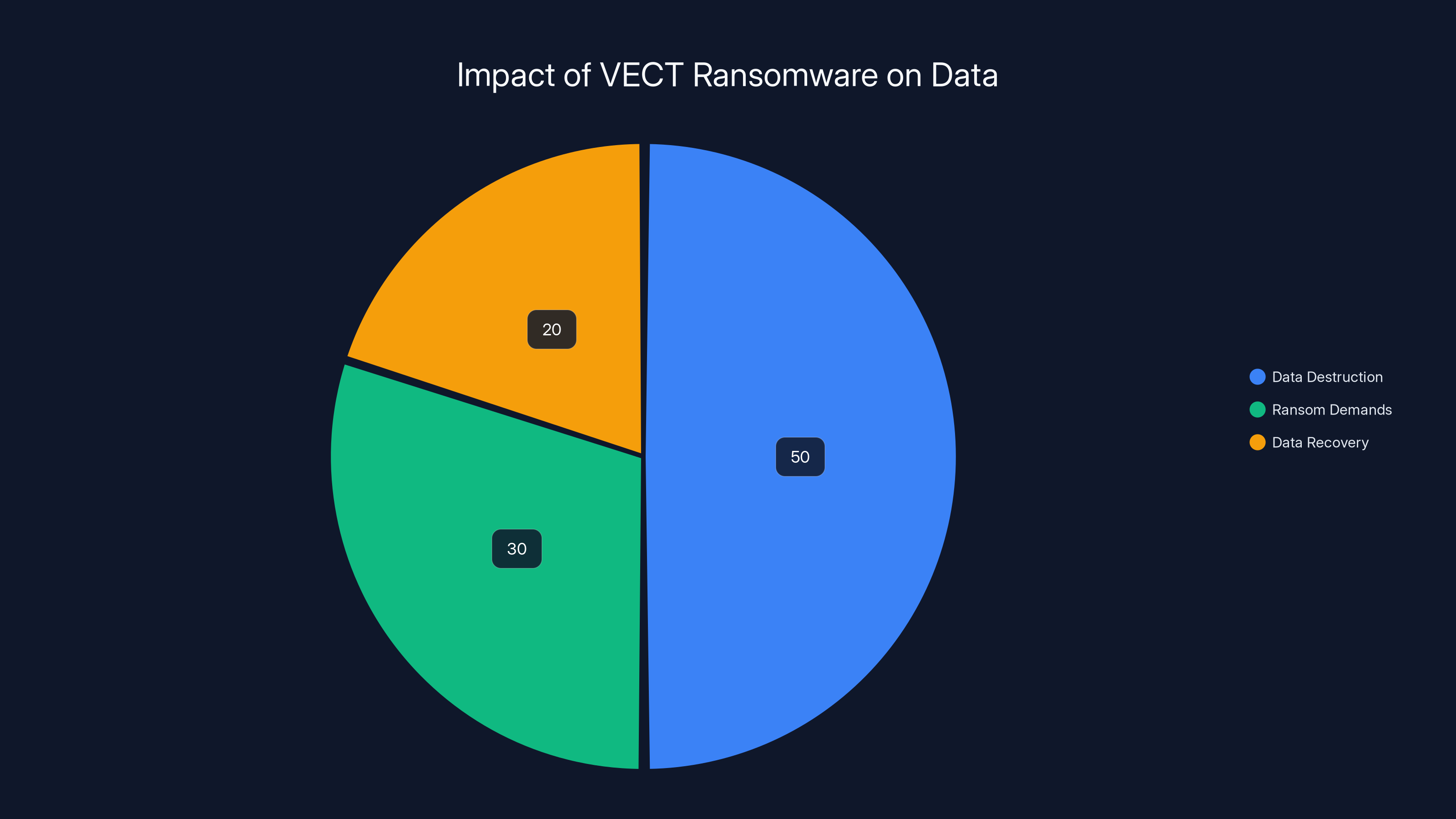
VECT ransomware is estimated to focus 50% on data destruction, diverging from traditional ransomware which primarily demands ransom. Estimated data.
Common Pitfalls and How to Avoid Them
As organizations scramble to protect against VECT, several common pitfalls can undermine these efforts.
Overreliance on Traditional Ransomware Solutions
Many defenses are built specifically for encryption-based ransomware. VECT bypasses these by not encrypting.
- Solution: Use comprehensive security solutions that detect unusual file operations, not just encryption.
Insufficient Backup Verification
Backups are only as good as their ability to restore data after a breach.
- Solution: Regularly test backups to ensure data can be restored.
Ignoring Insider Threats
While VECT is an external threat, insiders can unknowingly aid its spread.
- Solution: Train employees on phishing detection and secure data handling practices.
Future Trends in Ransomware
Ransomware is evolving, with VECT heralding a new era of destructive cyber threats. Here’s what to watch for:
Destructive Variants
Expect more ransomware strains to adopt destructive behaviors as a strategy to maximize damage and urgency.
AI-Driven Attacks
Artificial intelligence may soon be used to improve the effectiveness of ransomware, adapting attacks in real-time. According to SQ Magazine, AI-driven cyberattacks are predicted to increase by 30% annually.
Enhanced Cyber Defenses
As threats evolve, so too will defenses. Expect advancements in AI-driven cybersecurity tools that can predict and neutralize threats before they strike.
Implementation Guide: Protecting Against VECT
Here’s a step-by-step guide to implementing a robust defense against this new breed of ransomware.
Step 1: Conduct a Risk Assessment
Identify critical assets and vulnerabilities. Focus on:
- Data Prioritization: Determine which data is most critical.
- Vulnerability Scanning: Use tools to identify weak points in your system.
Step 2: Strengthen Your Security Posture
- Upgrade Security Software: Ensure you have the latest security patches.
- Implement Access Controls: Limit data access based on roles.
Step 3: Educate and Train Staff
- Phishing Simulations: Conduct regular tests to improve employee awareness.
- Incident Response Training: Prepare staff for quick, coordinated responses to breaches.
Step 4: Regularly Test Your Defenses
Conduct thorough penetration testing to simulate attacks and identify areas for improvement.

Case Study: A Real-World Encounter with VECT
A mid-sized financial firm recently fell victim to VECT. Despite having traditional ransomware defenses, the firm suffered significant data loss. Here’s how it unfolded:
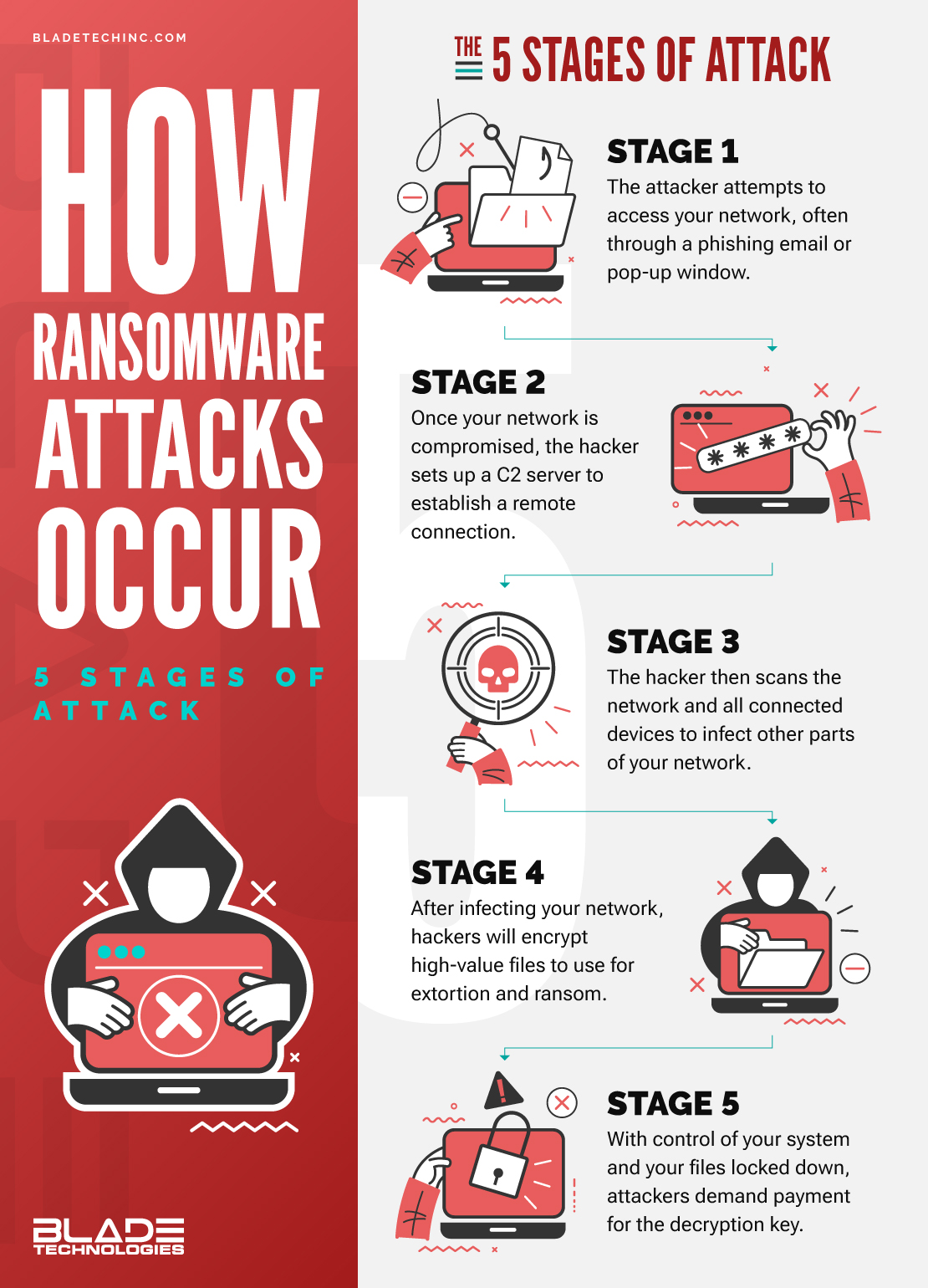
- Initial Infection: A phishing email led to the installation of VECT on an employee’s computer.
- Spread: The ransomware spread through the network, targeting files over 128KB.
- Data Loss: Critical client data was wiped, leading to a major operational disruption.
- Response: The firm had to implement extensive data recovery efforts and enhance its cybersecurity measures.
Lessons Learned:
- Proactive Measures: Regular employee training and advanced security practices could have mitigated the attack.
- Backup Importance: The firm’s regular backups saved it from complete data loss.
Conclusion: The Path Forward
As ransomware continues to evolve, the onus is on organizations to stay ahead. VECT serves as a stark reminder of the importance of robust cybersecurity measures and proactive defense strategies. By understanding the unique threats posed by data-wiping ransomware, businesses can better protect themselves and ensure data integrity in the face of evolving cyber threats.
Use Case: Automate your security alert monitoring to catch ransomware attacks faster with Runable.
Try Runable For Free
FAQ
What is VECT ransomware?
VECT is a type of malware marketed as ransomware but functions as a data destruction tool, deleting files instead of encrypting them.
How does VECT destroy data?
VECT uses flawed encryption processes with poor nonce handling, leading to the permanent erasure of data larger than 128KB.
What can I do to protect my files from VECT?
Implementing robust backup strategies, using comprehensive security solutions, educating staff, and conducting regular security drills are essential for protection.
Are traditional ransomware defenses effective against VECT?
Traditional defenses may not suffice, as VECT bypasses encryption detection by erasing data. Advanced detection methods are recommended.
What are the future trends in ransomware?
Expect more ransomware adopting destructive tactics, AI-driven attacks, and enhanced cybersecurity defenses in response.
How can I recover from a VECT attack?
Recovery involves using backups to restore data, improving security measures, and performing a thorough post-incident analysis to prevent future breaches.
Is VECT a standalone threat?
While VECT is significant, it's part of a broader trend of evolving cyber threats. Comprehensive cybersecurity strategies are necessary to combat various risks.
Key Takeaways
- VECT acts as a data wiper, erasing files over 128KB.
- Flawed nonce handling leads to data destruction.
- Backup strategies are crucial for data protection.
- Expect more ransomware to adopt destructive behaviors.
- AI-driven cybersecurity tools will enhance defenses.
Related Articles
- Understanding the Threat: Attack of the Killer Script Kiddies [2025]
- The Extradition of Xu Zewei: A Deep Dive into Cyber Espionage and Global Security [2025]
- Understanding Cybersecurity Threats in the Medical Sector: Lessons from Recent Breaches [2025]
- Inside the New Cyber Scam: How Hackers Exploit Microsoft Teams to Steal Your Data [2025]
- GitHub's Race Against Time: Fixing a Critical Vulnerability in Record Time [2025]
- 'The Attacker Completed in Under Five Minutes': Unpacking the North Korea-Linked Crypto Attack [2025]
![VECT: The Ransomware That's Secretly Destroying Your Data [2025]](https://tryrunable.com/blog/vect-the-ransomware-that-s-secretly-destroying-your-data-202/image-1-1777462480019.jpg)



