China-Nexus Cyber Actors Turning IoT Infrastructure into Botnets [2025]
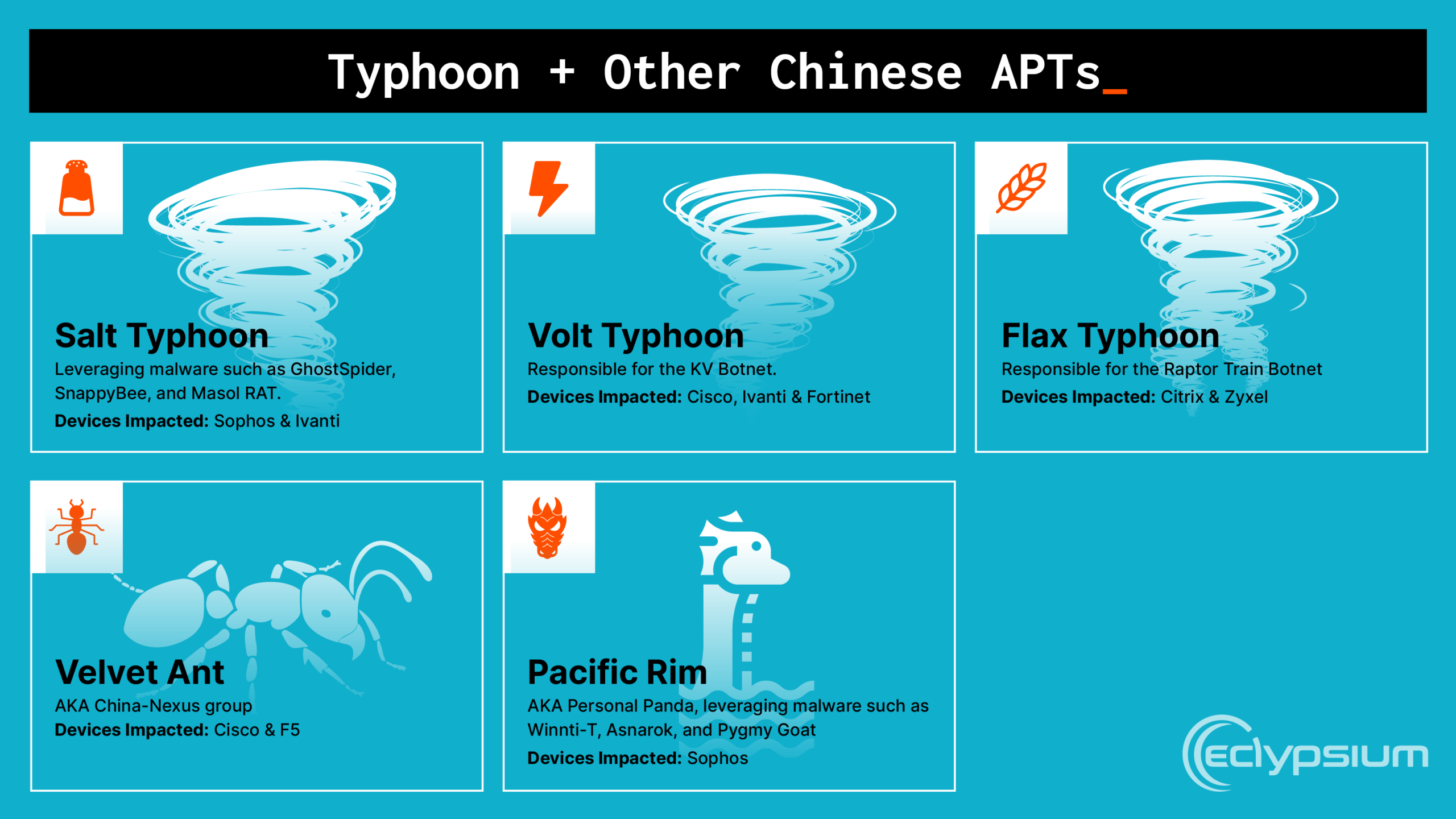
In the world of cybersecurity, threats evolve as rapidly as the technology designed to combat them. Lately, a new wave of cyber threats has emerged, centered around the misuse of Internet of Things (IoT) devices and routers. But here's the twist: these aren't just any cyber actors. They're part of a China-nexus group, designated as Typhoon, turning everyday devices into massive botnets. This isn't a plot from a cyber-thriller—it's reality, and authorities like the National Cyber Security Centre (NCSC) and the Five Eyes alliance are raising the alarm.
TL; DR
- China-nexus cyber actors are leveraging IoT devices to create covert botnets, posing significant security risks. According to a CISA advisory, these activities are becoming increasingly sophisticated.
- Typhoon-designated groups are at the forefront of these campaigns, exploiting vulnerabilities in routers and IoT infrastructure. The Security Affairs report highlights how these groups evade detection.
- Best practices for safeguarding networks include regular firmware updates, strong password policies, and network segmentation. Appinventiv provides insights into effective cybersecurity measures.
- Future trends indicate an increase in sophisticated cyber tactics involving AI and machine learning. The Atlantic Council discusses the integration of AI in cybersecurity.
- Organizations must adopt proactive security measures to mitigate risks from evolving cyber threats, as emphasized by BitSight's analysis of ransomware botnets.
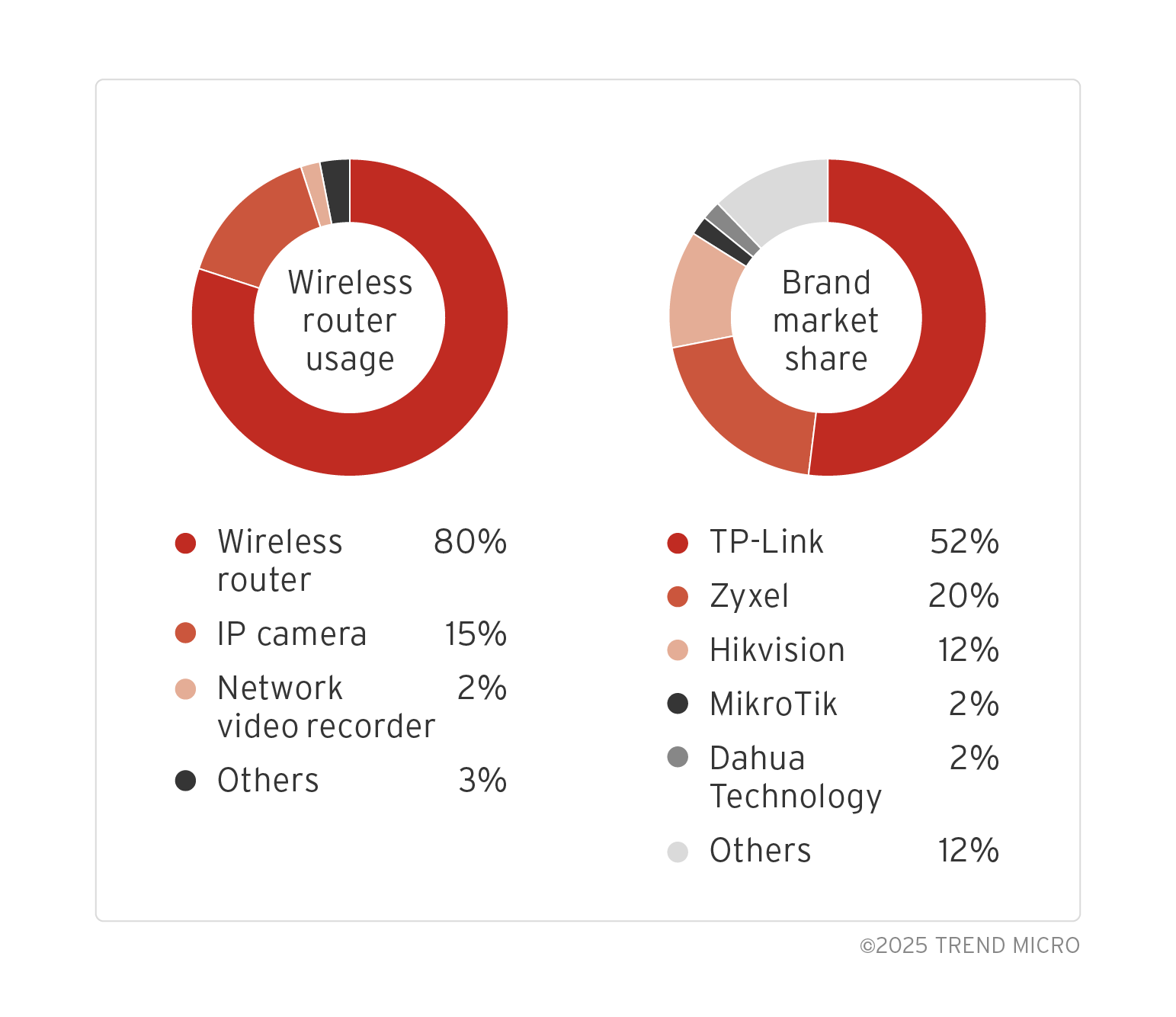
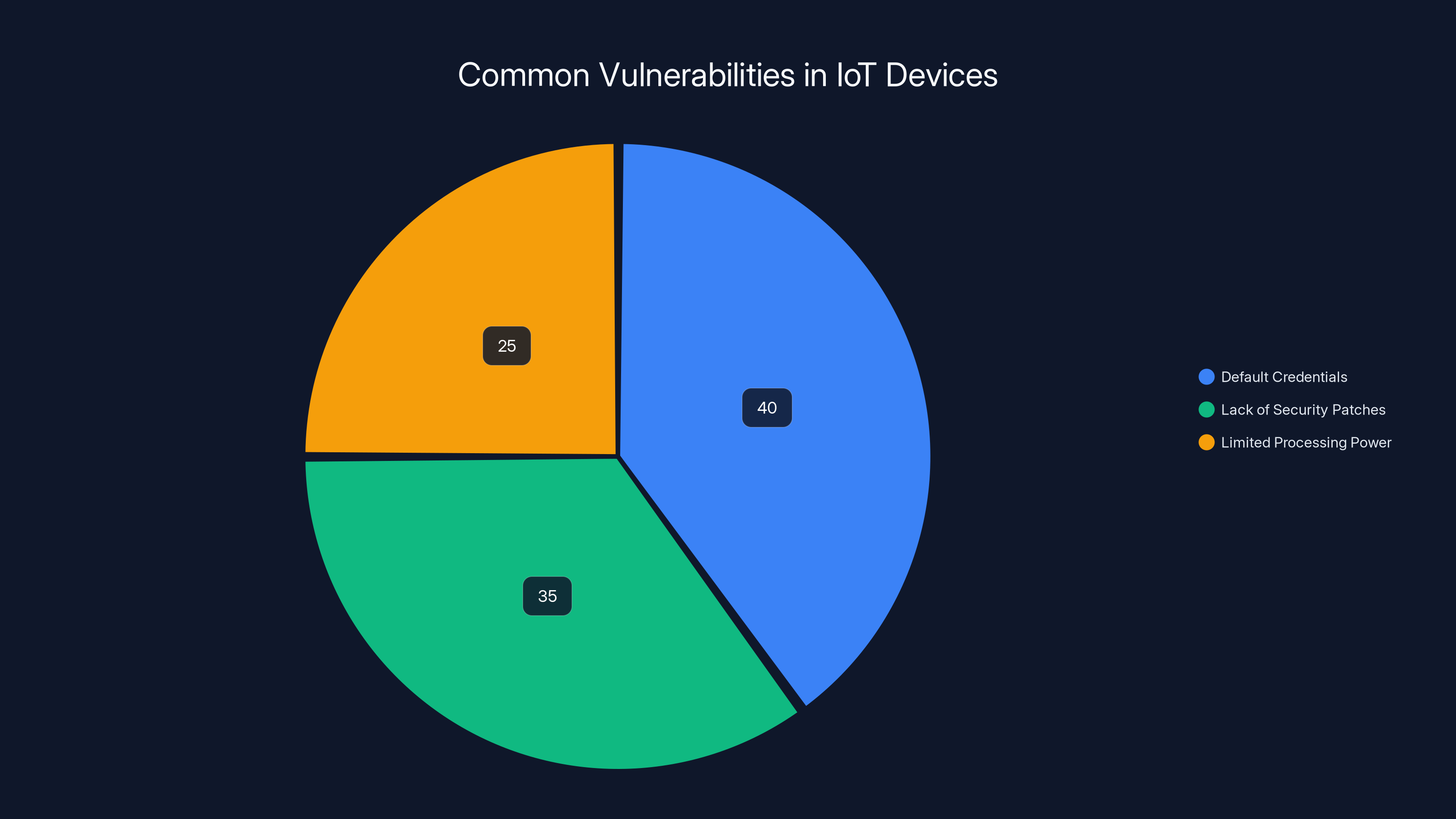
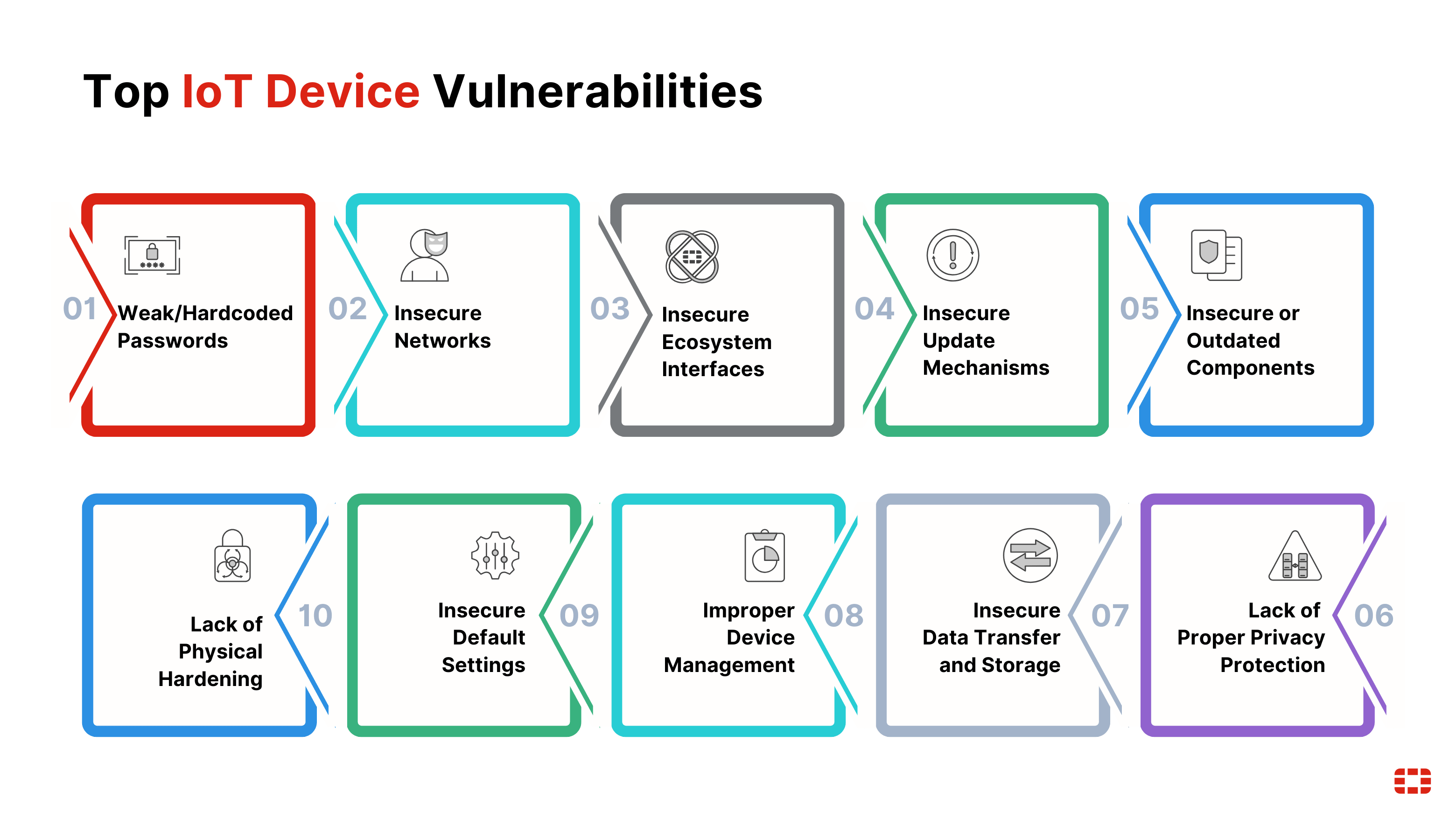
Default credentials account for the largest share of IoT vulnerabilities, followed by lack of security patches and limited processing power. (Estimated data)
Understanding the Threat Landscape
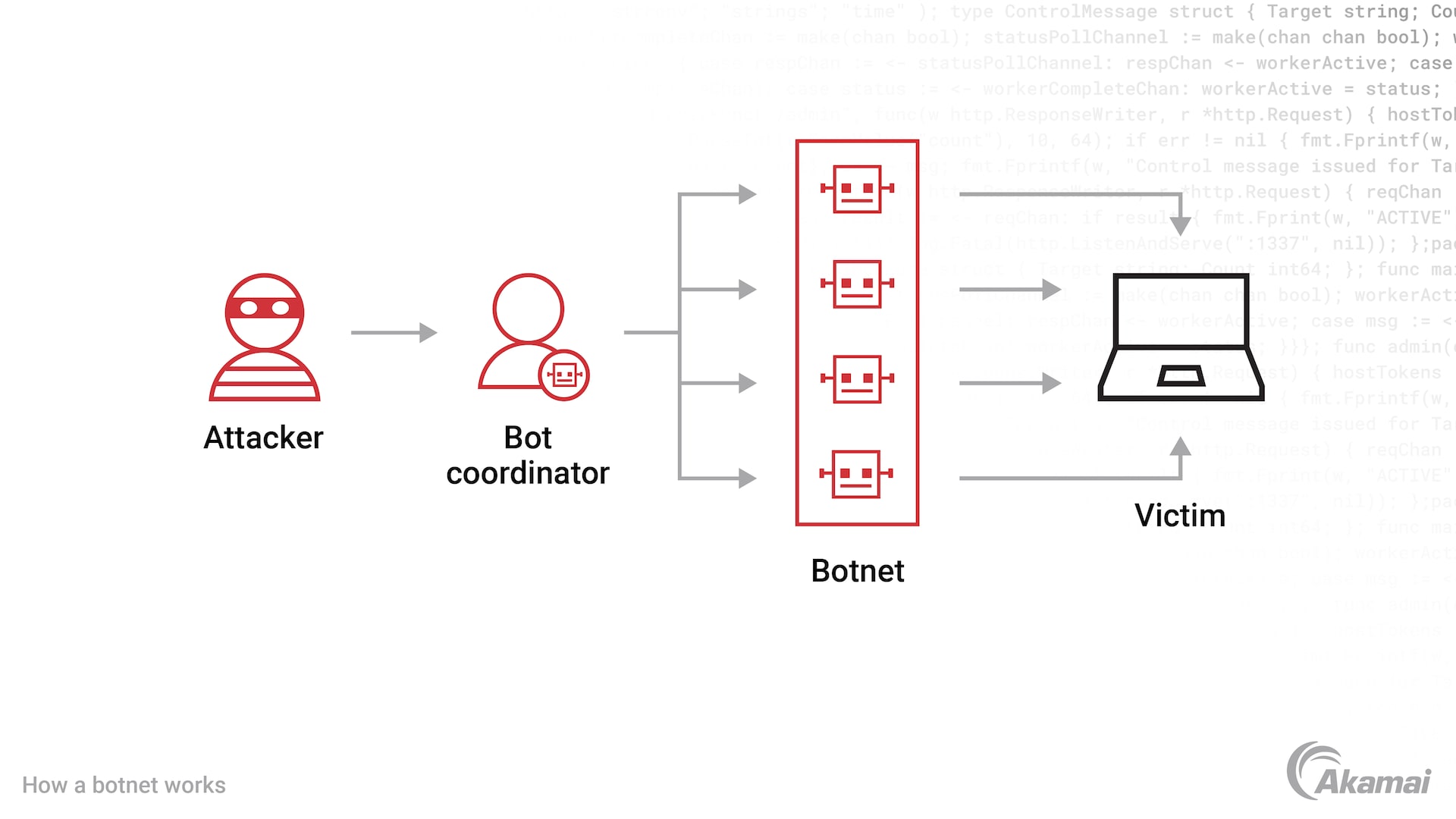
Cyber actors are increasingly targeting IoT devices and routers, turning them into botnets—networks of compromised devices that can be controlled remotely. These botnets can be used for a variety of malicious activities, such as launching Distributed Denial of Service (DDoS) attacks, infiltrating sensitive networks, or facilitating data breaches. The SecurityWeek article provides an example of such DDoS attacks.
What Makes IoT Devices Vulnerable?
IoT devices are inherently vulnerable due to several factors:
- Default Credentials: Many IoT devices come with default usernames and passwords that users often neglect to change, as noted by TechRadar.
- Lack of Security Patches: Manufacturers sometimes fail to provide timely updates for security vulnerabilities.
- Limited Processing Power: IoT devices often lack the resources to run advanced security software.
How Botnets Operate
Botnets typically operate by:
- Infecting Devices: Using malware to take control of vulnerable devices.
- Command and Control Infrastructure: Establishing a centralized system to control the botnet.
- Executing Attacks: Launching coordinated attacks, often without the device owner's knowledge.
In the case of China-nexus actors, these botnets are used to mask the perpetrators' locations, making it harder for authorities to track them down, as detailed in a Hacker News report.

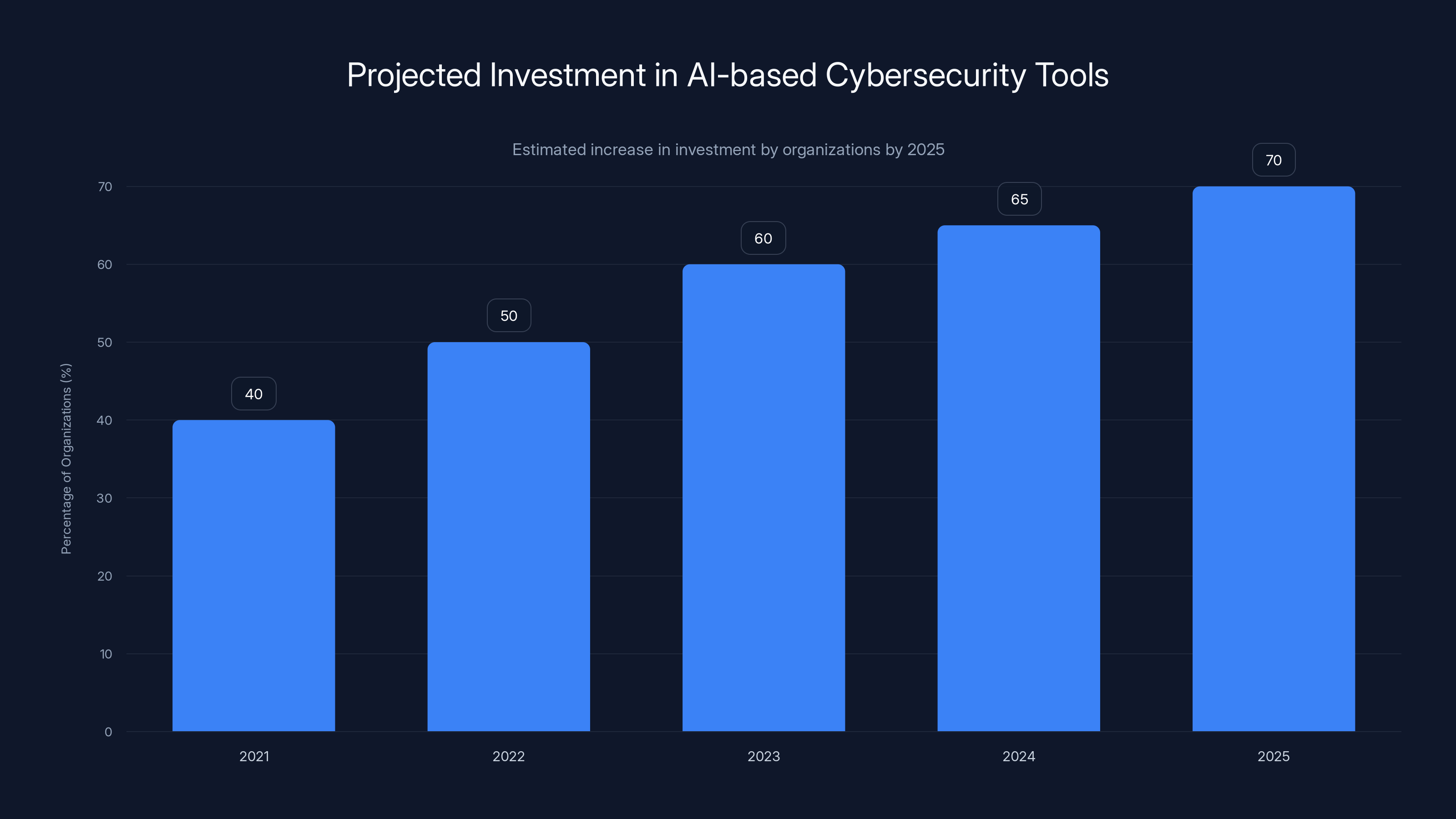
By 2025, over 70% of organizations are expected to invest in AI-based cybersecurity tools, indicating a significant trend towards advanced threat defense. Estimated data.
The Role of Typhoon-Designated Groups
Who Are the Typhoon Groups?
Typhoon is a designation for a collection of state-sponsored cyber groups linked to China. These groups are sophisticated and have access to significant resources, allowing them to execute complex cyber campaigns. The Nature journal provides insights into their operational tactics.
Recent Campaigns and Tactics
Recent advisories indicate that Typhoon groups have been:
- Exploiting Router Vulnerabilities: Targeting known vulnerabilities in popular router models, as reported by CISA.
- Leveraging IoT Devices: Using IoT devices like smart cameras and thermostats as entry points into larger networks.
Best Practices for Safeguarding Networks
Regular Firmware Updates
Ensuring that all devices are running the latest firmware is crucial. Firmware updates often include patches for known security vulnerabilities. Microsoft emphasizes the importance of regular updates in their security strategies.
Strong Password Policies
Implement complex passwords and change them regularly. Avoid using default credentials, which are often publicly available.
Network Segmentation
Divide your network into segments to limit the spread of any potential infection. Use firewalls to control traffic between segments.
Implementing Intrusion Detection Systems
Deploy intrusion detection systems (IDS) to monitor network traffic for suspicious activity. IDS can alert you to potential threats, allowing for quick action.

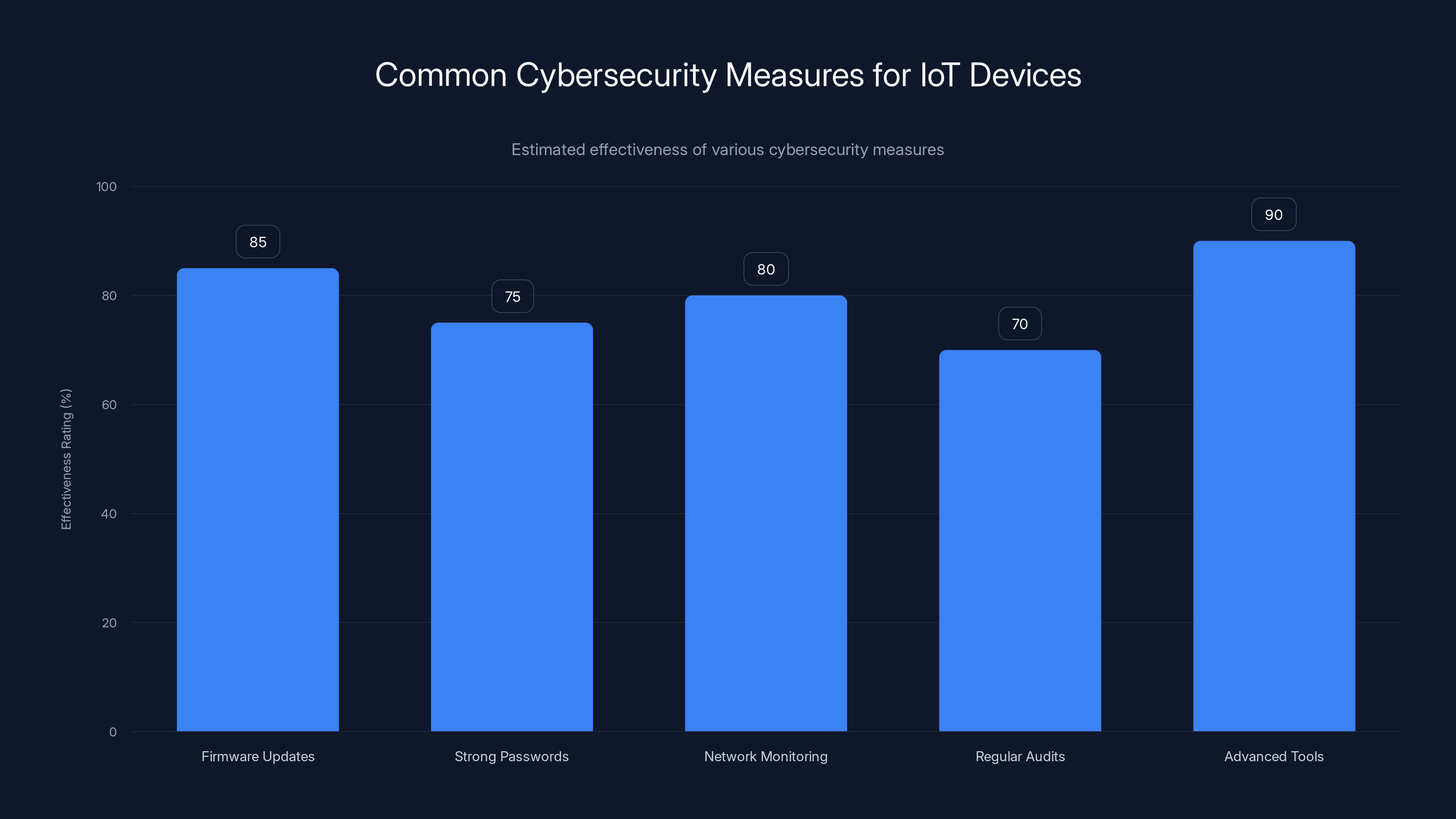
Regular firmware updates and advanced threat detection tools are estimated to be the most effective measures for protecting IoT devices. (Estimated data)
Common Pitfalls and Solutions
Ignoring Firmware Updates
Many users neglect to update their devices, leaving them vulnerable to known exploits. Schedule regular updates to minimize this risk.
Overlooking IoT Devices
It's easy to forget about IoT devices once they're installed. Keep an inventory of all devices connected to your network and monitor them regularly.
Weak Monitoring Practices
Without proper monitoring, it's difficult to detect and respond to threats. Implement continuous monitoring tools to stay vigilant.
Future Trends in Cybersecurity
Rise of AI and Machine Learning
Cyber actors are increasingly using AI and machine learning to automate attacks and improve their success rates. Organizations must adopt similar technologies to defend against these advanced threats, as discussed in a Nature study.
Increased Focus on Supply Chain Security
As supply chain attacks become more common, organizations must scrutinize their vendors and partners to ensure security across the board.
Greater Emphasis on User Education
Educating users about cybersecurity risks and best practices is essential. Many breaches occur due to human error, such as falling for phishing scams.

Recommendations for Organizations
Conduct Regular Security Audits
Regular audits can help identify vulnerabilities and ensure compliance with security policies.
Invest in Advanced Threat Detection
Advanced threat detection tools can help identify and mitigate threats before they cause significant damage.
Foster a Culture of Security
Encourage all employees to prioritize security in their daily tasks. This can be achieved through regular training and awareness programs.
Conclusion
The threat posed by China-nexus cyber actors is real and growing. By understanding the tactics used by these groups and implementing robust security measures, organizations can protect themselves from becoming the next victim. As technology continues to evolve, so too must our approaches to cybersecurity, ensuring that we stay one step ahead of potential threats.
FAQ
What is a botnet?
A botnet is a network of compromised devices that can be controlled remotely by a cyber actor. These networks are often used to launch large-scale cyber attacks.
How can I protect my IoT devices?
Protect your IoT devices by regularly updating their firmware, using strong passwords, and monitoring network activity for suspicious behavior.
Why are IoT devices targeted by cyber actors?
IoT devices are often targeted because they have weak security measures, making them easy to compromise and use in cyber attacks.
What steps can organizations take to improve cybersecurity?
Organizations can improve cybersecurity by conducting regular audits, investing in advanced threat detection tools, and fostering a culture of security among employees.
How does AI enhance cybersecurity efforts?
AI can enhance cybersecurity efforts by automating threat detection, analyzing large datasets for anomalies, and responding to threats more quickly than traditional methods.
What are the signs of a compromised device?
Signs of a compromised device include unusual network activity, slow performance, and unexpected reboots or crashes.
The Importance of Staying Informed
In today's digital age, staying informed about cybersecurity threats is crucial. By keeping up with the latest developments and implementing best practices, individuals and organizations can protect themselves from the ever-evolving landscape of cyber threats.
Key Takeaways
- China-nexus cyber actors are leveraging IoT devices to create covert botnets.
- Typhoon-designated groups are exploiting router vulnerabilities.
- Regular firmware updates and strong password policies are crucial for security.
- AI and machine learning are becoming integral in both cyber attacks and defenses.
- User education and network segmentation can mitigate risks.
Related Articles
- Unveiling the Precursor: The Hidden Malware Before Stuxnet [2025]
- Understanding the Surge: A Tenfold Growth in Botnet Size and the Future of DDoS Attacks [2025]
- Balancing Trust and Control to Unlock AI-Powered Networking [2025]
- How a 64-Year-Old Chinook Helicopter's Autonomous Landing Could Revolutionize Battlefield Aviation [2025]
- Why Your IT Helpdesk is Getting Weird Calls: LinkedIn Data Threats [2025]
- Anthropic’s Mythos Breach: Lessons Learned and Future Implications [2025]
![China-Nexus Cyber Actors Turning IoT Infrastructure into Botnets [2025]](https://tryrunable.com/blog/china-nexus-cyber-actors-turning-iot-infrastructure-into-bot/image-1-1777041274387.jpg)



