Why Your IT Helpdesk is Getting Weird Calls: LinkedIn Data Threats [2025]
The landscape of cybersecurity threats is constantly evolving, and the latest trend involves attackers leveraging LinkedIn data to impersonate executives and manipulate IT helpdesks. This article delves into how these attacks work, with detailed explanations, examples, and strategies to protect your organization.
TL; DR
- Increasing Threat: Attackers use LinkedIn data to impersonate executives, tricking IT helpdesks.
- Social Engineering: These attacks rely heavily on psychological manipulation.
- Vulnerabilities: Lack of verification processes in helpdesks can be exploited.
- Best Practices: Implement multi-factor authentication and employee training.
- Future Trends: Expect more sophisticated impersonation tactics as AI evolves.

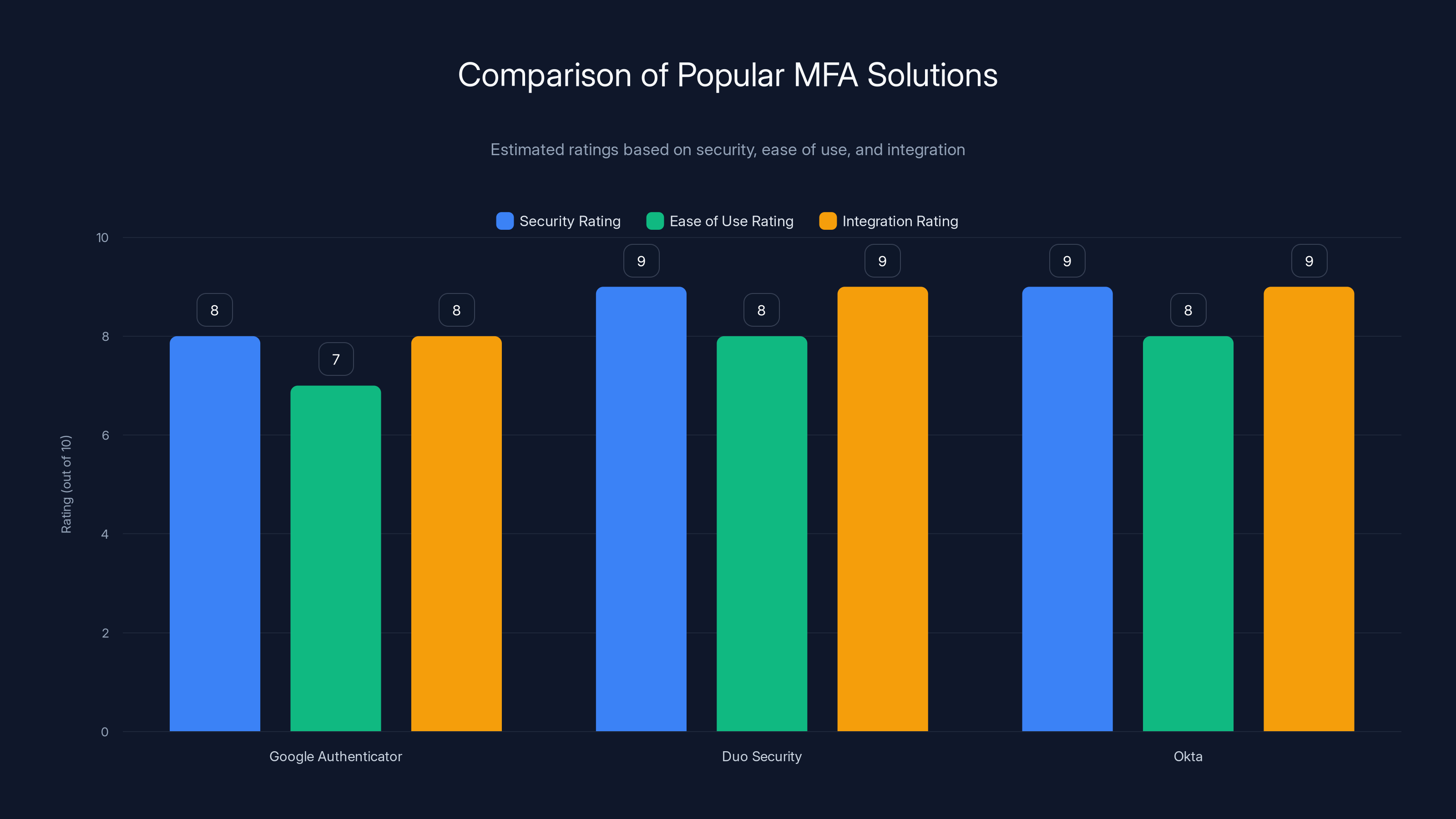
Estimated data shows that Duo Security and Okta score high in security and integration, while Google Authenticator is slightly lower in ease of use.
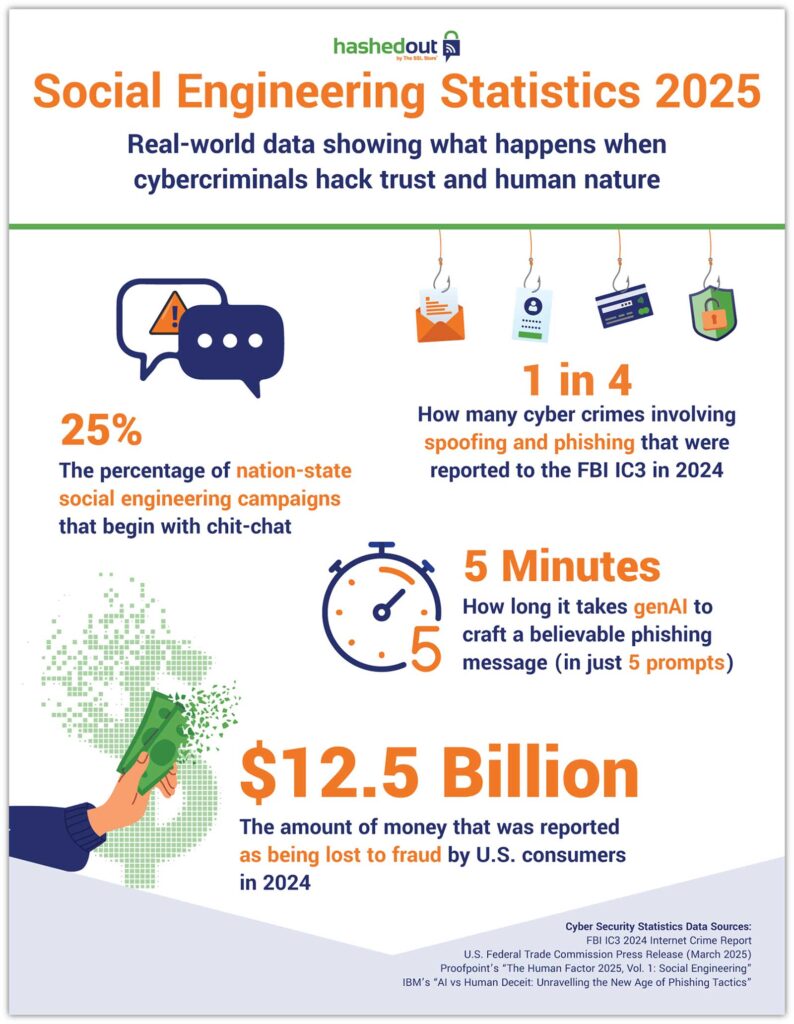
The Emergence of Social Engineering Attacks
Social engineering attacks have always been a part of the cybersecurity landscape, but their sophistication has drastically increased. Today, attackers are not just relying on generic phishing emails. They are using detailed social media data, like LinkedIn profiles, to craft convincing impersonations.
How Attackers Use LinkedIn Data
LinkedIn, being a professional networking platform, is a goldmine for attackers. They can gather information on company hierarchies, employee roles, and even personal details to create a believable identity.
- Profile Information: Names, job titles, and connections.
- Professional History: Previous roles and company experience.
- Endorsements and Skills: Insight into an individual's expertise and responsibilities.
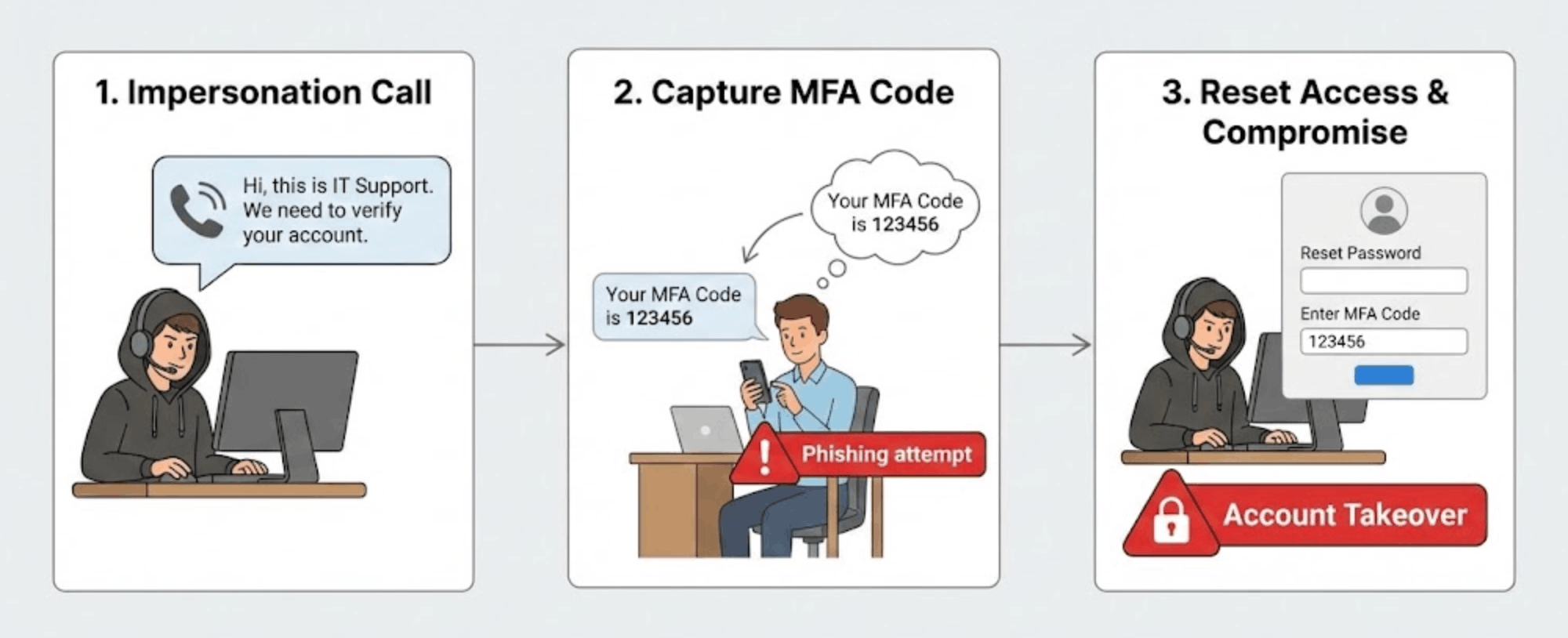
Attackers use this information to pose as high-ranking executives, contacting IT helpdesks with urgent requests such as password resets or access to sensitive systems.
Example Scenario
Imagine this: An IT helpdesk receives a call from someone claiming to be the CTO of the company. The caller, using information gleaned from LinkedIn, knows the CTO's professional background and current projects. They urgently request a password reset, citing a critical deadline.
Without proper verification processes, the helpdesk might comply, unwittingly giving access to an attacker.
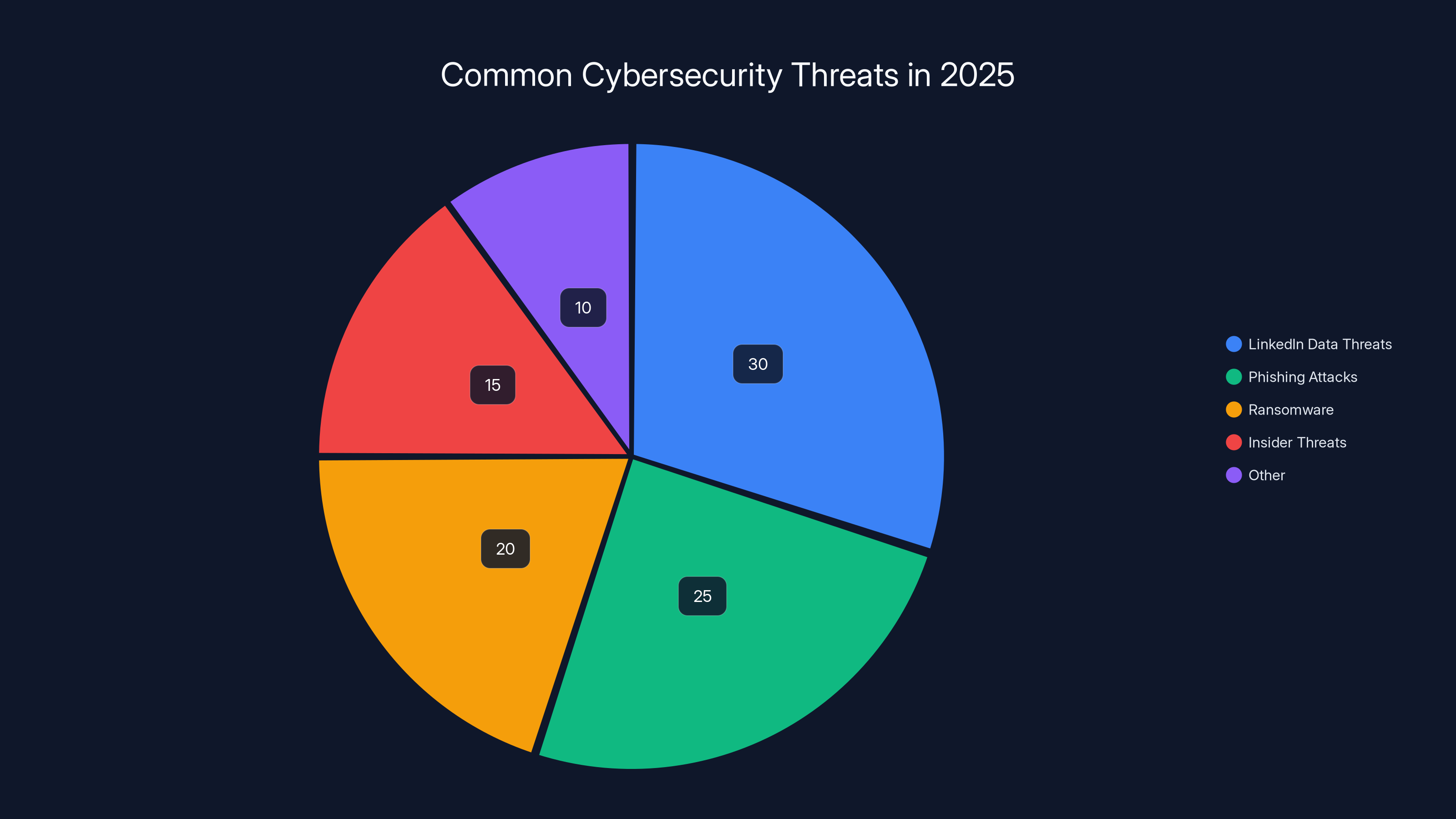
LinkedIn data threats are estimated to account for 30% of cybersecurity issues in 2025, highlighting the growing importance of securing social media data. Estimated data.
The Mechanics of Impersonation Attacks
These attacks are a form of social engineering, where attackers exploit human psychology to bypass technical defenses. The goal is to gain trust and manipulate individuals into divulging confidential information or performing actions that compromise security.
Psychological Manipulation Techniques
- Authority Exploitation: Impersonating a high-ranking executive to leverage authority and urgency.
- Urgency and Pressure: Creating a sense of immediate need to bypass standard procedures.
- Familiarity and Rapport: Using personal details to create a false sense of acquaintance.

Common Pitfalls and Solutions
Pitfalls
- Lack of Verification: Many helpdesks do not have robust identity verification processes.
- Over-reliance on Caller ID: Attackers can spoof phone numbers, making it appear as if the call is from a legitimate source.
- Inadequate Training: Employees might not be trained to recognize and respond to social engineering attempts.
Solutions
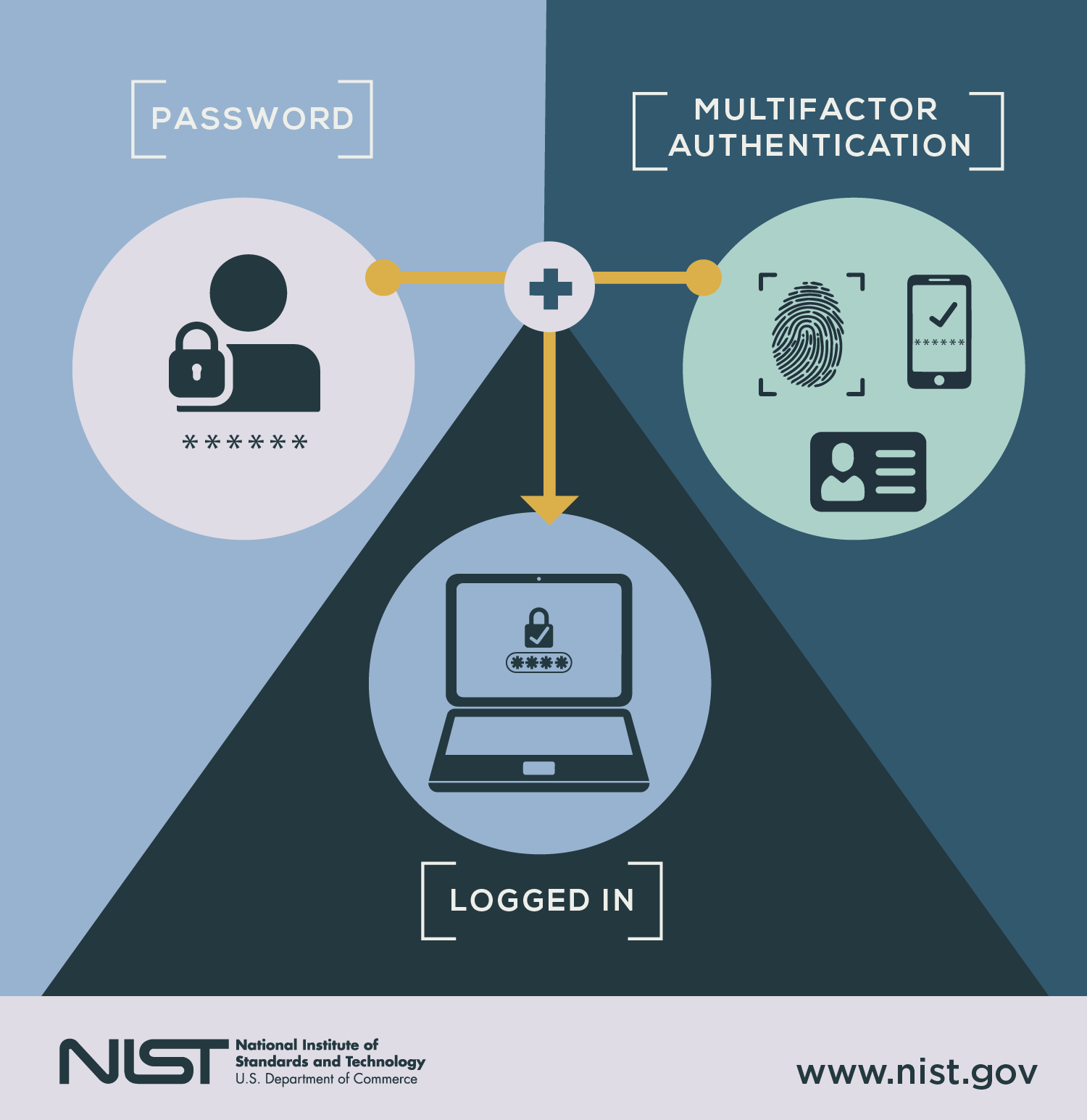
- Multi-Factor Authentication (MFA): Implement MFA for sensitive operations, such as password resets.
- Employee Training: Regular training sessions to help employees spot phishing and social engineering tactics.
- Verification Protocols: Establish strict verification protocols for any request involving sensitive actions or information.


Estimated data shows that updating security policies has the highest adoption rate at 80%, while encouraging reporting is adopted by 65% of organizations.
Technical Implementation Guide
Setting Up Multi-Factor Authentication
Multi-Factor Authentication (MFA) adds an extra layer of security by requiring more than one form of verification.
- Choose an MFA Solution: Evaluate options like Google Authenticator, Duo Security, or Okta.
- Integrate with Existing Systems: Ensure compatibility with your current IT infrastructure.
- Educate Employees: Provide training on how to set up and use MFA.
Creating Robust Verification Processes
- Develop a Standard Operating Procedure (SOP): Outline the steps for verifying identity during sensitive requests.
- Use Challenge Questions: Incorporate questions that only the legitimate person would know.
- Implement Call-Back Procedures: Always call back using a verified number before proceeding with requests.
Future Trends in Social Engineering
AI and Deepfake Technologies
As AI and deepfake technologies become more advanced, attackers will have more tools to create convincing impersonations.
- Voice Cloning: AI can now mimic voices with high accuracy, making phone impersonations even more credible.
- Deepfake Videos: Attackers might use deepfake videos in video calls to impersonate executives.
Recommendations for Future-proofing
- Invest in AI Detection Tools: Use tools that can detect deepfakes and voice clones.
- Enhance Communication Security: Implement end-to-end encryption for all communications.
- Continuous Monitoring and Adaptation: Regularly update security protocols to adapt to new threats.

Case Studies and Real-world Examples
Case Study: Company A's Experience
Company A, a mid-sized tech firm, experienced a series of impersonation attacks targeting their IT helpdesk. Attackers used LinkedIn data to impersonate the CFO, requesting access to financial systems.
Outcome: By implementing a verification process and MFA, Company A successfully thwarted further attacks.
Lessons Learned
- Importance of Verification: Verification processes are crucial in preventing unauthorized access.
- Role of Employee Awareness: Continuous training helped employees recognize suspicious requests.
Best Practices for Organizations
- Regular Audits: Conduct regular audits of security protocols to identify potential weaknesses.
- Update Security Policies: Ensure that security policies are up-to-date with the latest threats.
- Encourage Reporting: Create a culture where employees feel comfortable reporting suspicious activity.
Conclusion
The rise of social engineering attacks using LinkedIn data is a stark reminder of the evolving nature of cybersecurity threats. Organizations must stay vigilant and adapt their security strategies to protect against these sophisticated attacks. By implementing robust verification processes, training employees, and leveraging advanced technologies, companies can defend against these impersonation threats and safeguard their sensitive information.
FAQ
What is social engineering?
Social engineering is a technique used by attackers to manipulate individuals into divulging confidential information or performing actions that compromise security.
How do attackers use LinkedIn data?
Attackers gather information from LinkedIn profiles, such as job titles and professional connections, to impersonate executives and manipulate IT helpdesks.
What are some common social engineering tactics?
Common tactics include impersonating authority figures, creating a sense of urgency, and exploiting familiarity.
How can organizations protect against these attacks?
Organizations can protect themselves by implementing multi-factor authentication, establishing verification protocols, and conducting regular employee training.
What role does AI play in social engineering attacks?
AI can be used to create convincing impersonations through voice cloning and deepfake videos, making social engineering attacks more sophisticated.
What are the future trends in social engineering?
Future trends include the use of AI and deepfake technologies to enhance impersonation tactics and the development of tools to detect such threats.
Why is employee training important?
Employee training is essential to help staff recognize and respond to social engineering attempts, thereby preventing unauthorized access.
How can companies encourage employees to report suspicious activity?
Companies can foster a culture of transparency and trust, where employees feel confident in reporting any unusual or suspicious activity without fear of repercussions.
Key Takeaways
- Social engineering attacks are increasingly leveraging LinkedIn data.
- Impersonation of executives is a common tactic to bypass helpdesk security.
- Multi-factor authentication and employee training are crucial defenses.
- AI and deepfake technologies pose future risks in social engineering.
- Organizations should implement robust verification processes.
Related Articles
- Vercel's Security Incident: A Deep Dive into Compromised Accounts [2025]
- Understanding the Vercel Data Breach: Implications, Security Best Practices, and Future Directions [2025]
- The Hidden Risks of AI-Generated Passwords [2025]
- France's Identity Management Agency Faces Data Breach: Implications and Next Steps [2025]
- Anthropic’s Mythos Breach: Lessons Learned and Future Implications [2025]
- AI Galaxy Hunters: The Role of GPUs in Unraveling the Universe [2025]
![Why Your IT Helpdesk is Getting Weird Calls: LinkedIn Data Threats [2025]](https://tryrunable.com/blog/why-your-it-helpdesk-is-getting-weird-calls-linkedin-data-th/image-1-1776971091371.jpg)



