Understanding the Surge: A Tenfold Growth in Botnet Size and the Future of DDoS Attacks [2025]
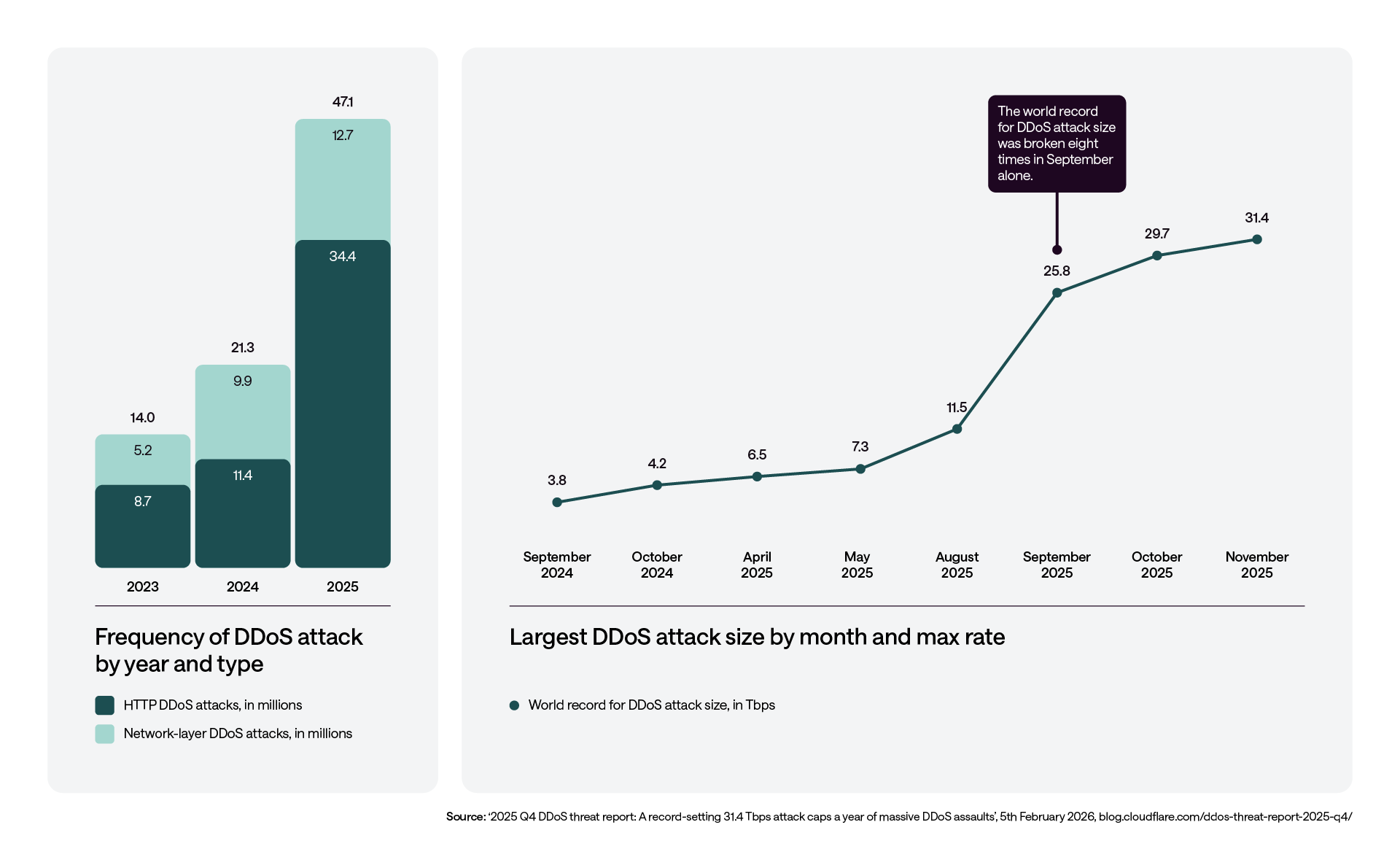
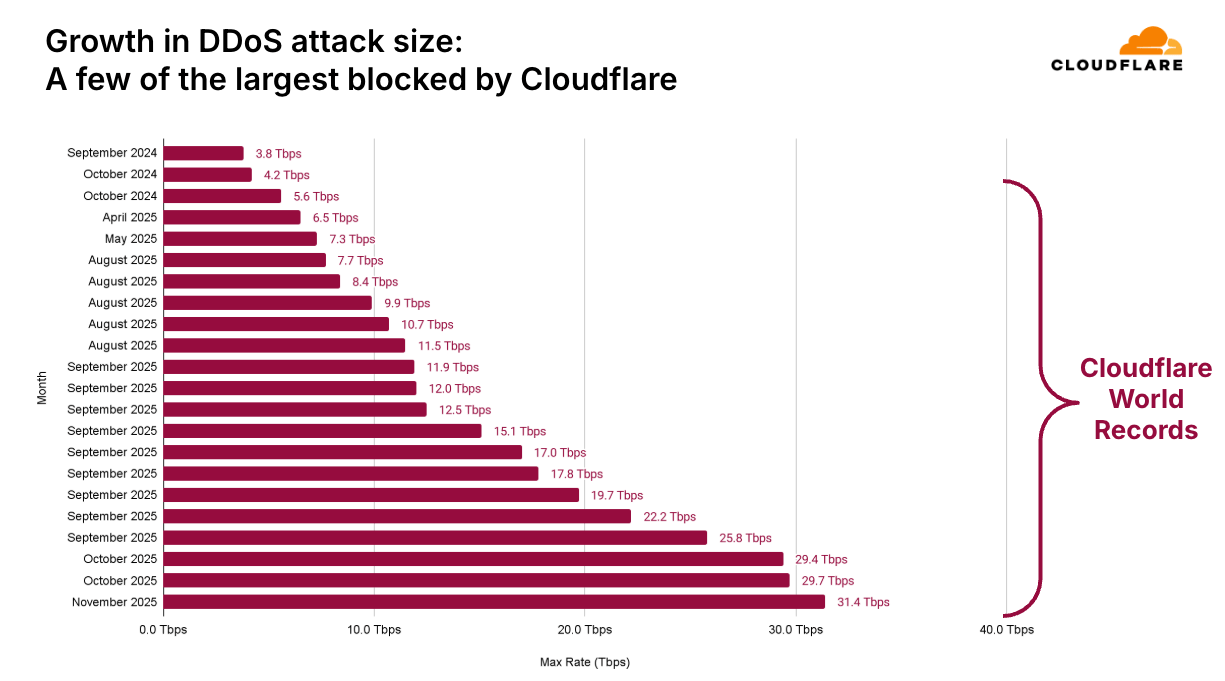
The world of cybersecurity is constantly evolving, and with it, the threats that organizations face. Among these, Distributed Denial-of-Service (DDoS) attacks have seen a dramatic transformation, both in scale and complexity. In recent times, the largest botnet on record has expanded tenfold, with attack capacities reaching an astounding 2 Tbps. This surge signals a worrying trend in the scale of modern DDoS campaigns. Let's delve into what this means for businesses and how they can protect themselves.
TL; DR
- Botnet Growth: The largest botnet has grown by 10x, reaching capabilities to launch 2 Tbps DDoS attacks. According to Palo Alto Networks' Unit 42, this expansion is unprecedented.
- Complexity Increase: Modern DDoS attacks use multi-vector strategies, making them harder to mitigate. PV Magazine explains how these strategies are evolving.
- Attack Duration: Recent incidents have lasted up to two weeks, indicating sustained threat capabilities.
- Mitigation Strategies: Organizations need robust, multi-layered security solutions to defend against these threats.
- Future Trends: Expect continued evolution in attack strategies and increased focus on AI-driven defense mechanisms.
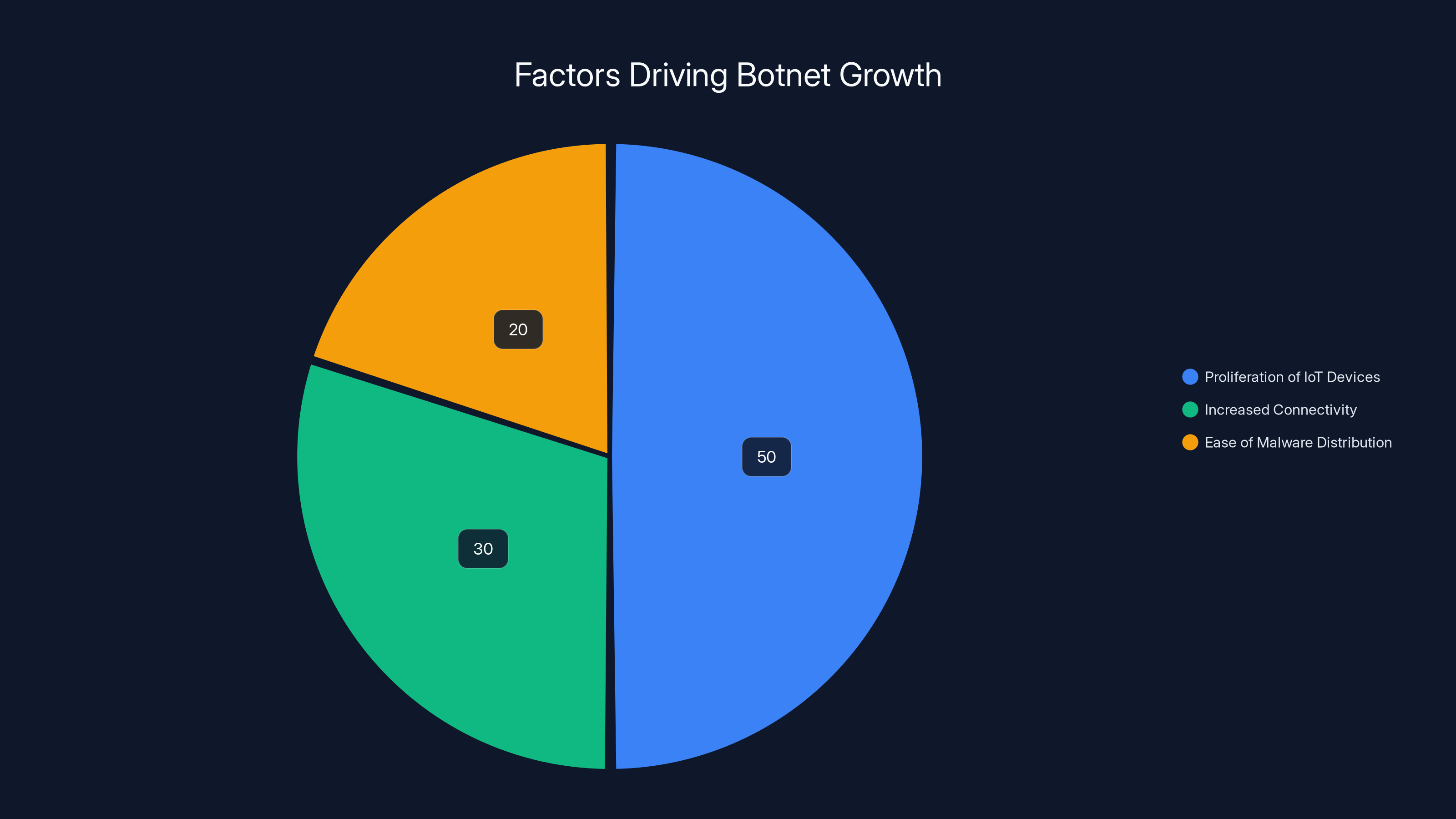
Proliferation of IoT devices is the largest driver of botnet growth, contributing to 50% of the expansion. Estimated data.
The Anatomy of a Modern Botnet
Botnets are networks of compromised computers, often controlled remotely by cybercriminals, to perform coordinated attacks. Historically, botnets consisted of thousands of devices, but the latest developments indicate networks comprising millions.
What Drives the Growth?
Several factors contribute to the exponential growth in botnet sizes:
- Proliferation of IoT Devices: With billions of IoT devices connected globally, each with varying degrees of security, they become prime targets for botnet recruitment. The Hacker News highlights the vulnerabilities in IoT devices that are often exploited.
- Increased Connectivity: Faster internet speeds allow more devices to participate effectively in botnets, increasing their potential attack power.
- Ease of Malware Distribution: Modern malware can spread quickly via phishing campaigns, software vulnerabilities, and unsecured networks.
How Do Botnets Work?
Botnets operate by exploiting vulnerabilities in devices and systems. Once compromised, these devices, known as 'zombies,' are controlled by a botmaster. The botmaster can issue commands to perform various tasks, including launching DDoS attacks, sending spam, or stealing data.
Key Components of a Botnet:
- Command and Control Servers (C&C): Centralized servers that manage the botnet.
- Zombies: Compromised devices within the botnet.
- Botmaster: The entity controlling the botnet.

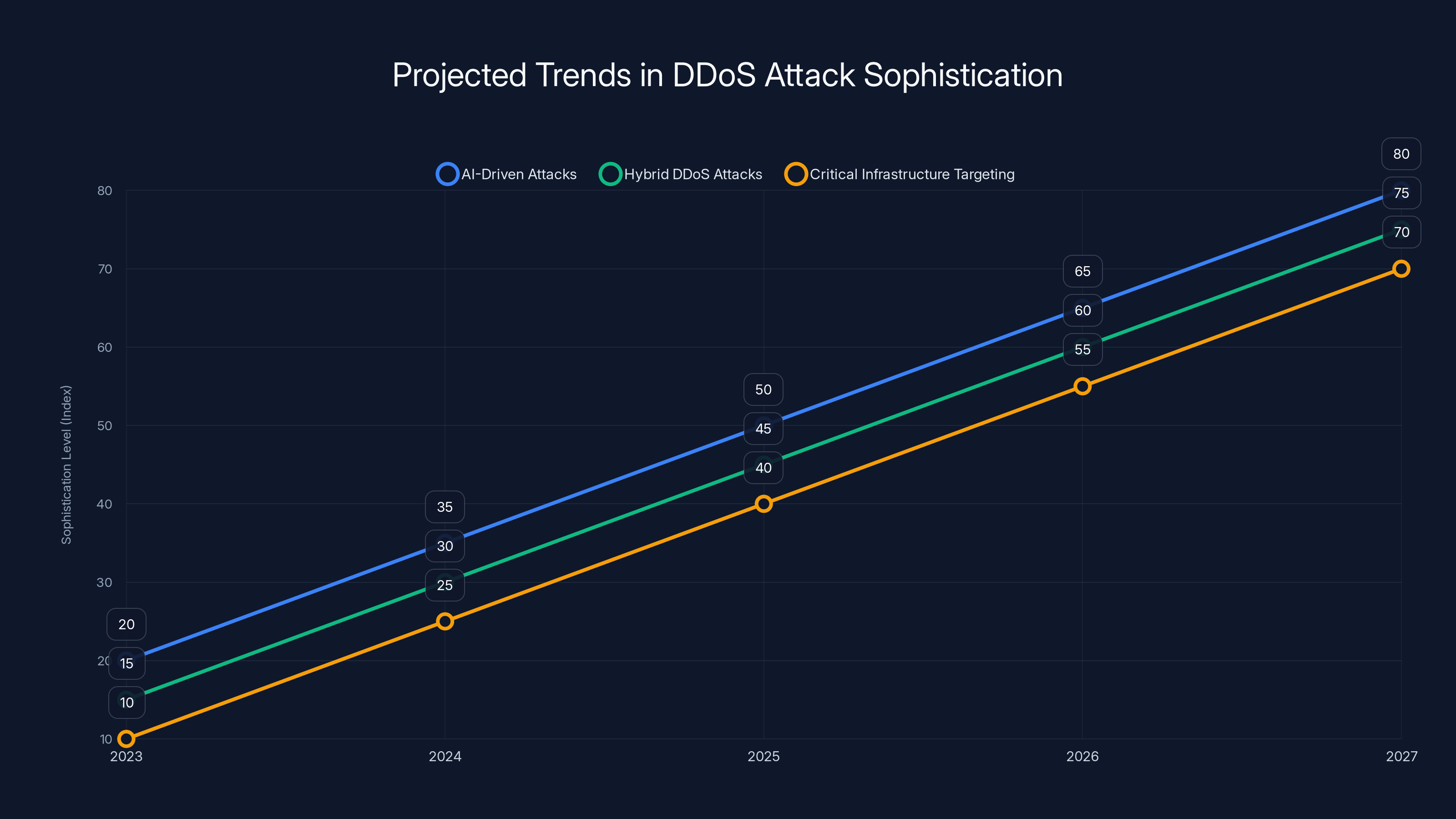
DDoS attacks are projected to become more sophisticated, with AI-driven and hybrid attacks increasing significantly by 2027. Estimated data.
The Rise of the 2 Tbps DDoS Attack
DDoS attacks aim to overwhelm a target's resources, rendering services unavailable. The recent 2 Tbps attack highlights the potential devastation these attacks can cause.
Record-Breaking Attack
A 2 Tbps attack represents a massive amount of data being directed at a target every second. This is equivalent to streaming 320,000 HD Netflix videos simultaneously. Such attacks can cripple even the most robust infrastructures.
Why This Matters:
- Increased Attack Surface: With greater bandwidth, attackers can target multiple services simultaneously.
- Heightened Complexity: Multi-vector attacks combine different methods, such as volumetric floods, protocol attacks, and application layer attacks.
Real-World Implications
The implications of such massive DDoS attacks are far-reaching. Businesses can suffer from prolonged downtime, reputational damage, and financial losses. The recent attack lasting over two weeks illustrates the potential for sustained disruption.
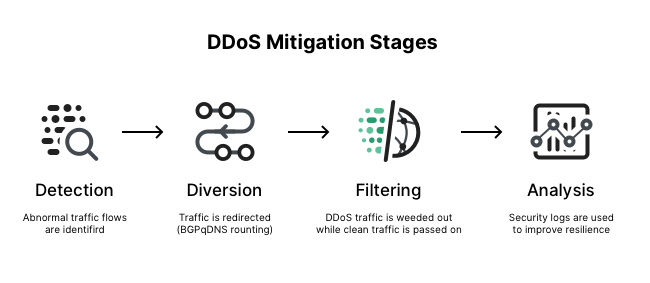
Mitigating the Threat
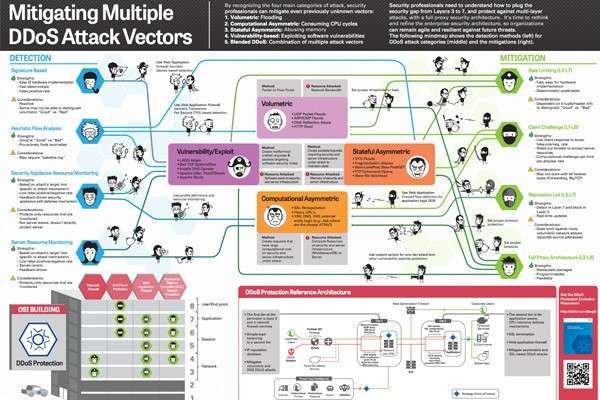
Defending against modern DDoS attacks requires a comprehensive, multi-layered approach. Here are some strategies that organizations can implement:
- Network Redundancy: Distribute resources across multiple locations to prevent a single point of failure.
- Traffic Filtering: Use firewalls and intrusion prevention systems (IPS) to filter malicious traffic.
- Rate Limiting: Limit the number of requests a server will accept over a certain period.
- Cloud-Based DDoS Protection: Leverage cloud providers with scalable resources to absorb and mitigate large-scale attacks.
QUICK TIP: Regularly update your network's security policies and conduct stress tests to identify vulnerabilities.
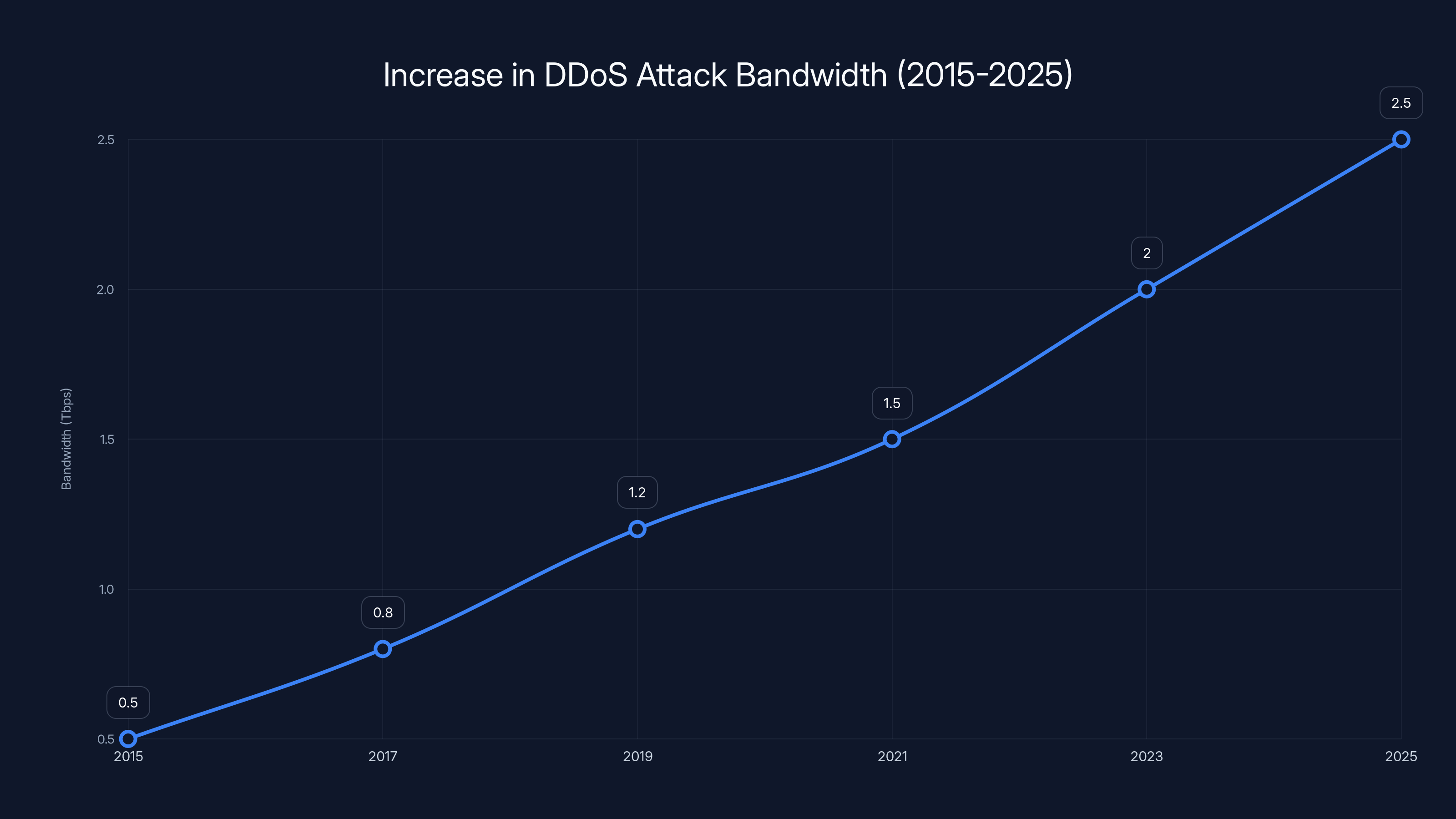
The chart illustrates the estimated increase in DDoS attack bandwidth from 0.5 Tbps in 2015 to a projected 2.5 Tbps by 2025, highlighting the growing threat of these attacks. Estimated data.
Future Trends in DDoS Attacks
As technology advances, so too will the sophistication of DDoS attacks. Here are some trends to watch:
- AI-Driven Attacks and Defense: Both attackers and defenders will increasingly use AI to outmaneuver each other.
- Hybrid DDoS Attacks: Combining DDoS with other attack vectors like ransomware to increase impact.
- Increased Targeting of Critical Infrastructure: As seen in recent attacks on power grids and healthcare systems.
DID YOU KNOW: The average cost of a DDoS attack for a business is over $2 million, including downtime, lost revenue, and recovery efforts.
Best Practices for Organizations
To combat the growing threat of DDoS attacks, organizations should adopt the following best practices:
- Incorporate DDoS Protection in Security Policies: Ensure that DDoS mitigation is a core component of your overall cybersecurity strategy.
- Educate Employees: Conduct regular training to recognize phishing attempts and other social engineering tactics that could lead to botnet infections.
- Collaborate with ISPs: Work with internet service providers to quickly detect and block malicious traffic.
Conclusion
The rapid growth of botnets and the increasing scale of DDoS attacks present significant challenges for businesses today. By understanding the mechanics of these threats and implementing robust defenses, organizations can safeguard their assets and maintain operational resilience.
FAQ
What is a botnet?
A botnet is a network of compromised devices controlled by a malicious actor to perform coordinated attacks, such as DDoS.
How do botnets grow?
Botnets grow by recruiting unsecured devices in the network, exploiting vulnerabilities, and spreading malware.
What are the signs of a DDoS attack?
Common signs include network slowdown, increased traffic from unusual sources, and service outages.
How can businesses protect themselves from DDoS attacks?
Implementing multi-layered security measures, network redundancy, and partnering with cloud-based DDoS protection services are effective strategies.
What role does AI play in DDoS attacks?
AI is used to enhance both attack strategies and defense mechanisms, enabling more sophisticated and adaptive techniques.
Can DDoS attacks be completely prevented?
While complete prevention is challenging, the impact of DDoS attacks can be significantly reduced through proactive measures and vigilant monitoring.
Key Takeaways
- Botnets have grown tenfold, increasing DDoS attack capabilities.
- Modern attacks are multi-vector and increasingly complex.
- Organizations need comprehensive security strategies to mitigate threats.
- AI will play a significant role in future attack and defense strategies.
- Proactive measures can reduce the impact of DDoS attacks.
Related Articles
- Inside Europol's Operation PowerOFF: A Game-Changer in Combating DDoS-for-Hire Services [2025]
- How AI Like Anthropic’s Mythos is Revolutionizing Cybersecurity [2025]
- Understanding the FCC Router Ban: What's Running in Your Network? [2025]
- How to Protect Your macOS from North Korean Cyber Threats [2025]
- 'Trusted Access for the Next Era of Cyber Defense': OpenAI's Cybersecurity Revolution [2025]
- Understanding the Rise of SIM Farms: A Deep Dive into Global Network Exploitation [2025]
![Understanding the Surge: A Tenfold Growth in Botnet Size and the Future of DDoS Attacks [2025]](https://tryrunable.com/blog/understanding-the-surge-a-tenfold-growth-in-botnet-size-and-/image-1-1776963972745.jpg)



