Identity is the New Perimeter: The Shift from Breaking In to Logging In [2025]
The cybersecurity landscape is undergoing a seismic shift. For decades, the focus was on building formidable walls around networks. The idea was simple: keep the bad actors out, and everything inside remains safe. But the digital world has evolved, and so must our approach to security. In today's cloud-first era, identity has emerged as the new perimeter.
TL; DR
- Identity as the New Frontier: Modern cybersecurity focuses on verifying user identity rather than just securing network perimeters.
- Zero Trust Revolution: Emphasizes 'never trust, always verify,' ensuring continuous authentication.
- Authentication Tools: Multi-factor authentication (MFA) and single sign-on (SSO) are crucial.
- Common Pitfalls: Over-reliance on passwords and poor identity management practices.
- Future Trends: Biometrics and AI-driven identity verification are on the rise.
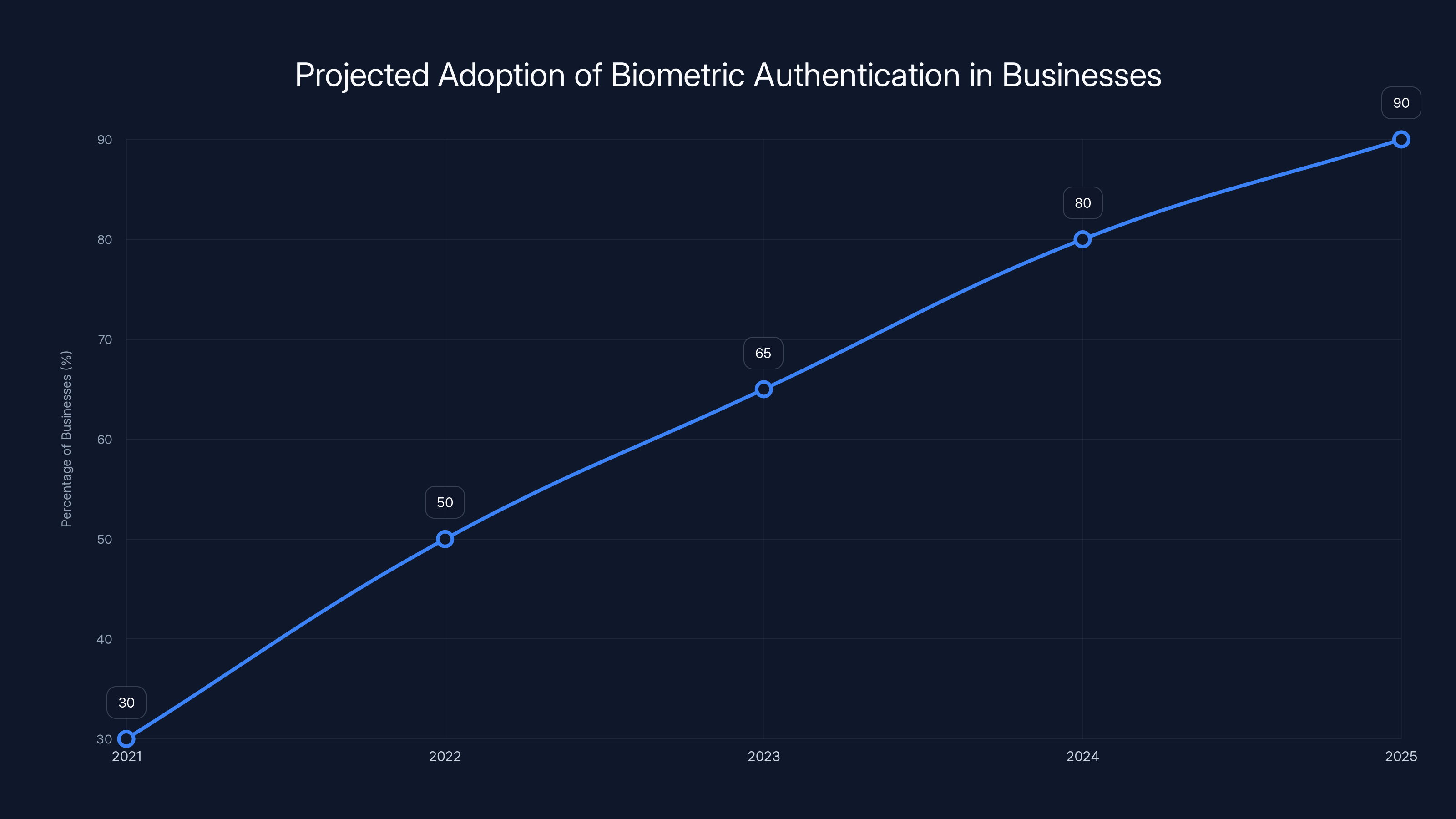
By 2025, it's estimated that 90% of businesses will use biometric authentication, indicating a significant upward trend in adoption. (Estimated data)
The Obsolete Perimeter Defense Model
For years, cybersecurity strategies revolved around the idea of a fortified perimeter. It was akin to building a castle: erect high walls, dig deep moats, and guard the gates. But as businesses migrated to the cloud and embraced Software as a Service (SaaS) solutions, this model proved inadequate.
Why Perimeter Defense Fails
- Cloud Adoption: The cloud dissolves traditional network boundaries, making perimeter-based security ineffective. According to FedTech Magazine, the shift to cloud services has necessitated a new approach to security.
- Remote Work: Employees access corporate resources from outside the network, bypassing perimeter defenses. This trend has been accelerated by the global shift to remote work, as noted in Kaseya's insights on Zero Trust security.
- SaaS Integration: Using third-party apps increases the attack surface beyond the traditional perimeter, as highlighted by MSSP Alert.
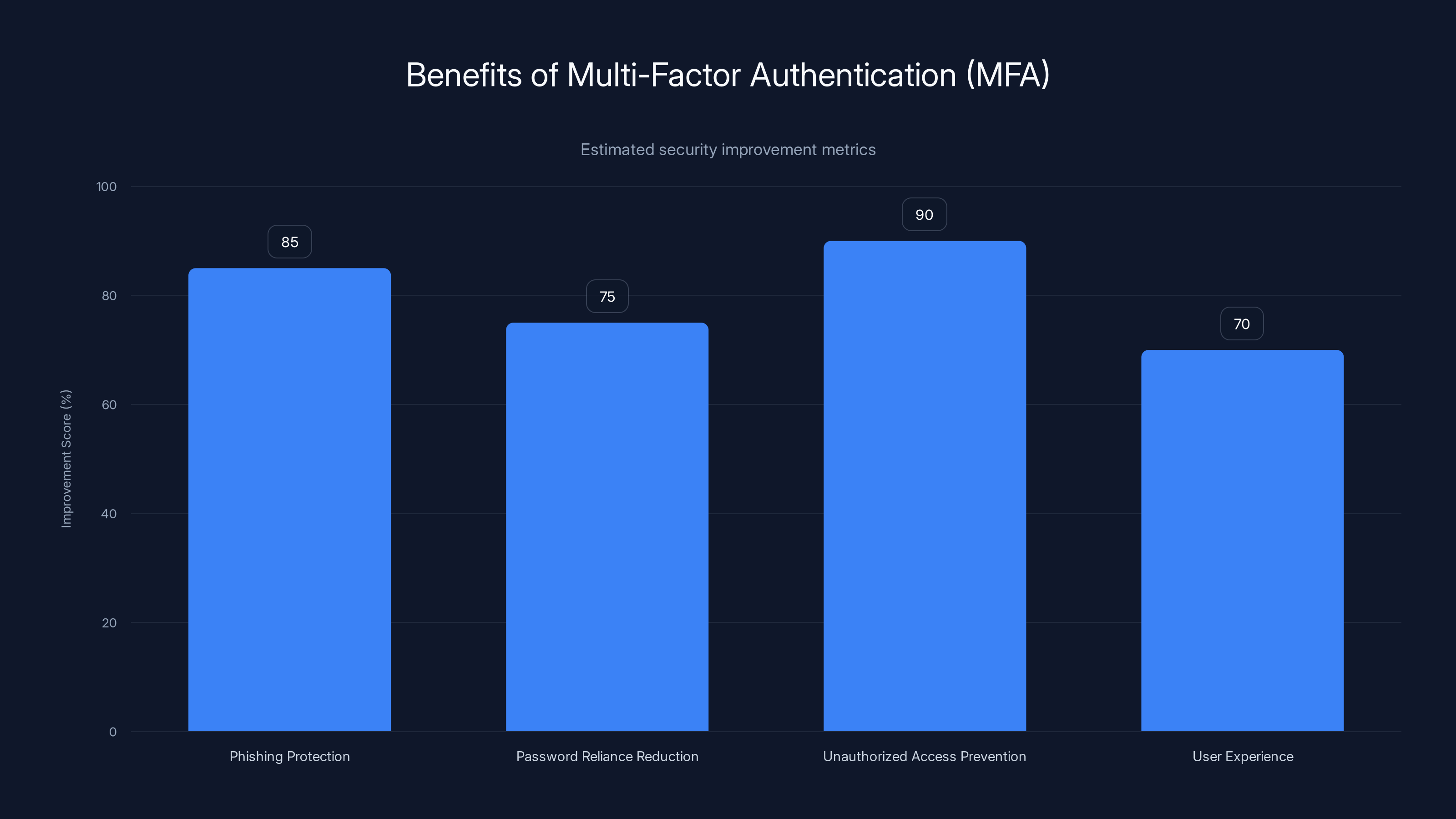
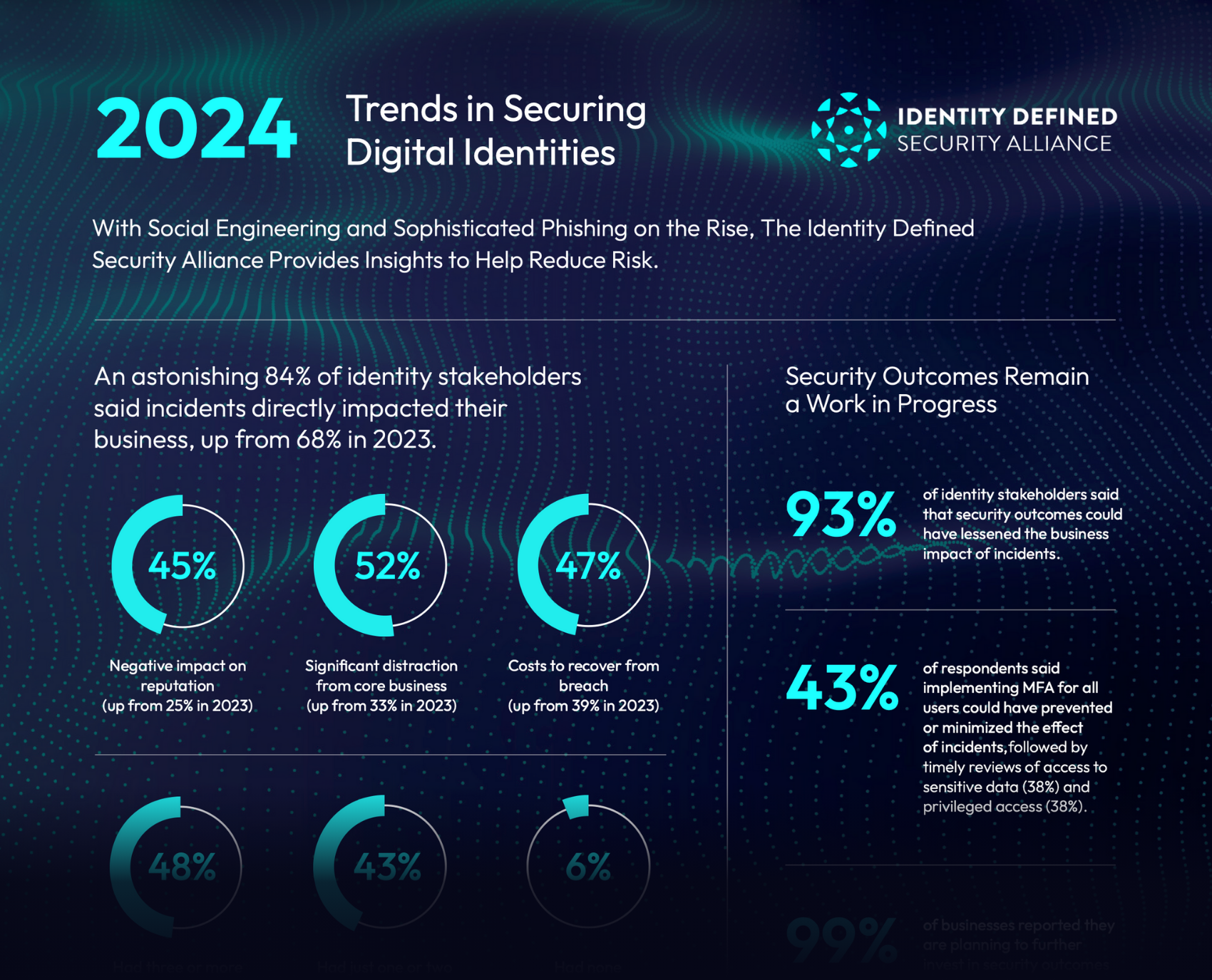
Multi-Factor Authentication (MFA) significantly enhances security by providing high protection against phishing (85%) and unauthorized access (90%). Estimated data.
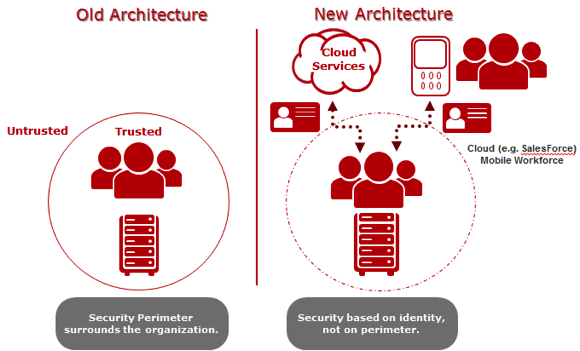
Identity as the New Perimeter
With the dissolution of clear network boundaries, identity verification has become crucial. Instead of focusing solely on keeping unauthorized users out, modern cybersecurity emphasizes ensuring the right users have appropriate access.
Core Principles of Identity-Based Security
- Authentication: Ensure that users are who they claim to be.
- Authorization: Grant access based on verified identity and role.
- Continuous Monitoring: Regularly check user activities to detect anomalies.
Implementing Identity-Based Security
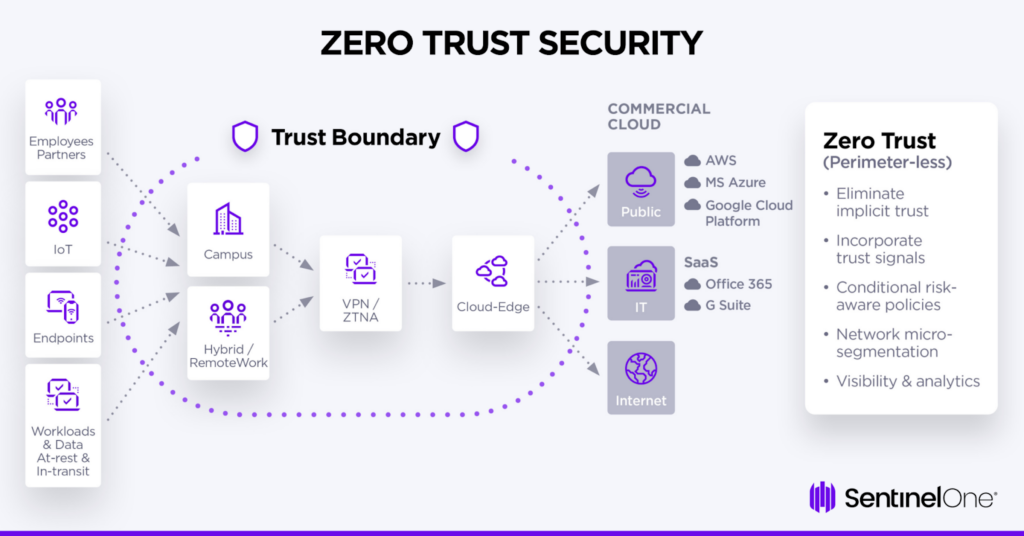
Zero Trust Architecture
The Zero Trust model operates on the principle of "never trust, always verify." This shift requires a fundamental rethink of how trust is established and maintained. Kaseya's blog discusses the importance of this model in modern security frameworks.
- Micro-Segmentation: Break networks into smaller parts to reduce the attack surface.
- Least Privilege: Users get the minimum access necessary for their role.
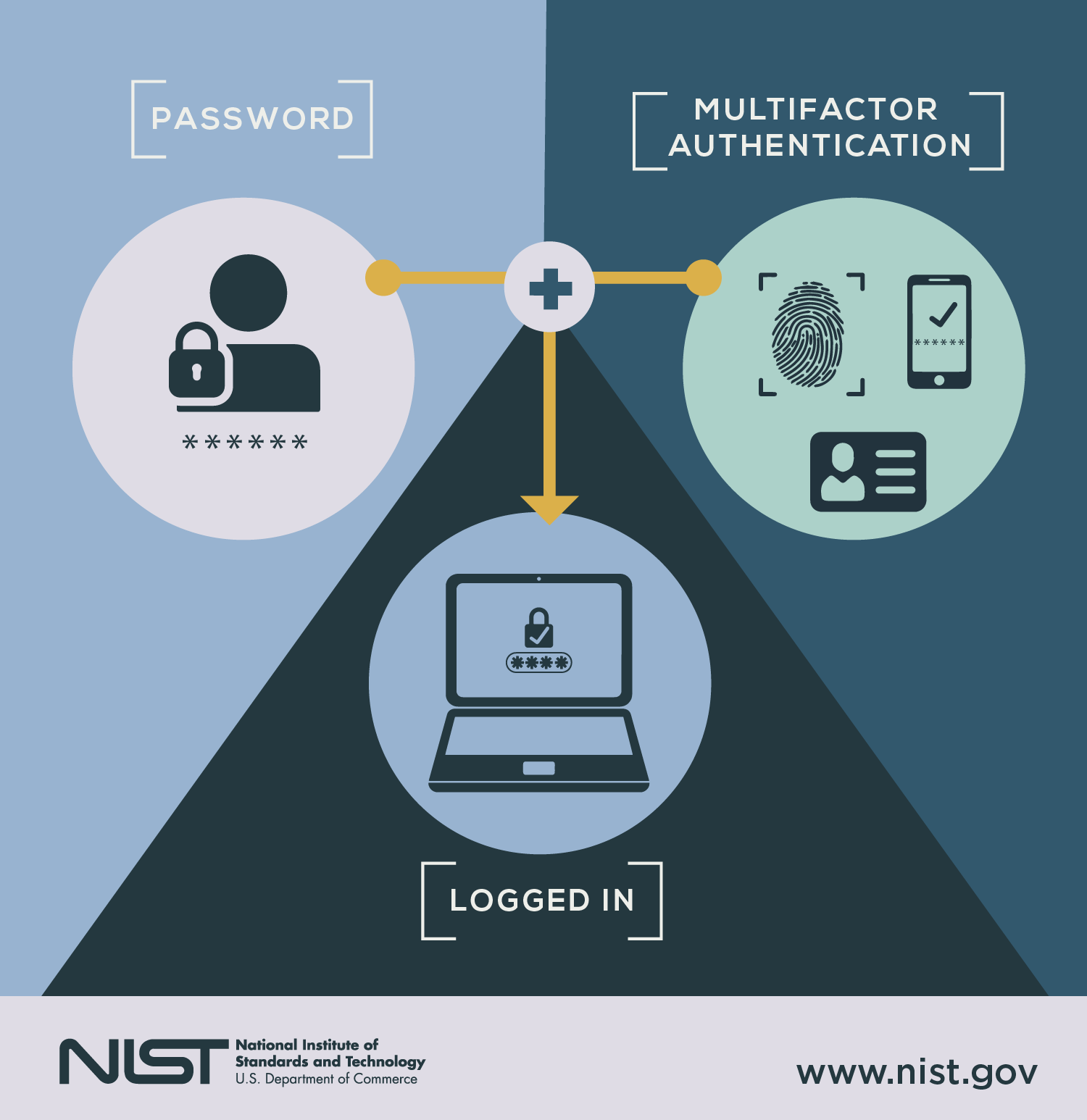
- Multi-Factor Authentication (MFA): Adds layers of verification to user identity.
Multi-Factor Authentication (MFA)
MFA strengthens security by requiring two or more verification factors. These factors typically include:
- Something You Know: Passwords or PINs.
- Something You Have: Tokens or smartphones.
- Something You Are: Biometrics like fingerprints or facial recognition.
QUICK TIP: Implement MFA across all critical applications to drastically reduce the risk of unauthorized access, as emphasized by IBM's insights on MFA implementation.
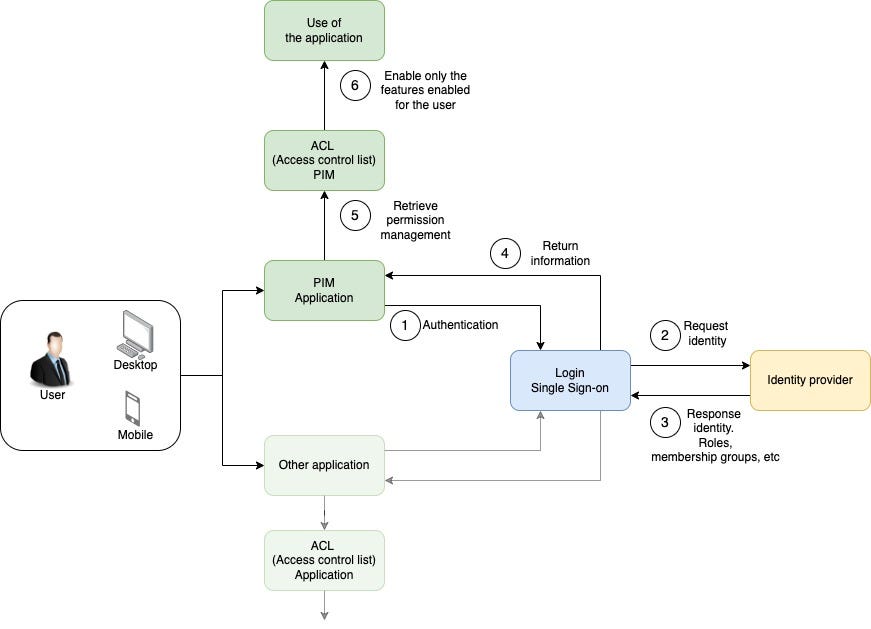
Single Sign-On (SSO)
SSO simplifies user experience by allowing access to multiple applications with a single set of credentials. It enhances security by reducing password fatigue, thus minimizing the risk of password reuse across platforms.
Benefits of SSO:
- Streamlined user experience.
- Reduced password management issues.
- Improved compliance with security policies.
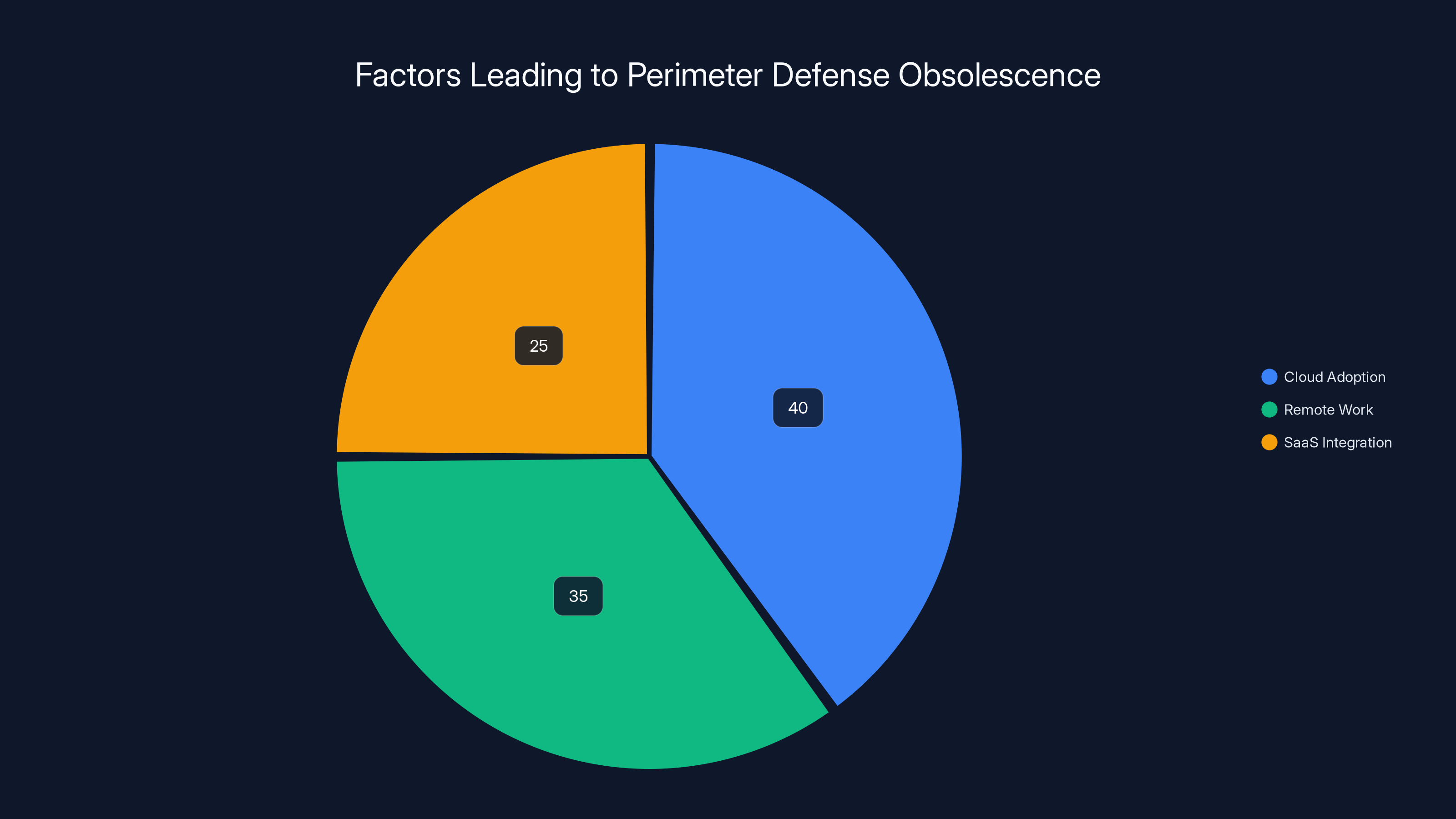
Cloud adoption, remote work, and SaaS integration are key factors making perimeter defense models obsolete. Estimated data.
Common Pitfalls in Identity Management
Over-Reliance on Passwords
Despite advancements, many organizations still rely heavily on passwords as the primary authentication method. The Microsoft Security Blog highlights the risks associated with password reliance.
- Weak Passwords: Users often choose easily guessable passwords.
- Password Reuse: Reusing passwords across platforms increases vulnerability.
- Phishing Attacks: Attackers trick users into revealing passwords.
Solution: Educate users on creating strong passwords and implement MFA to mitigate risks.
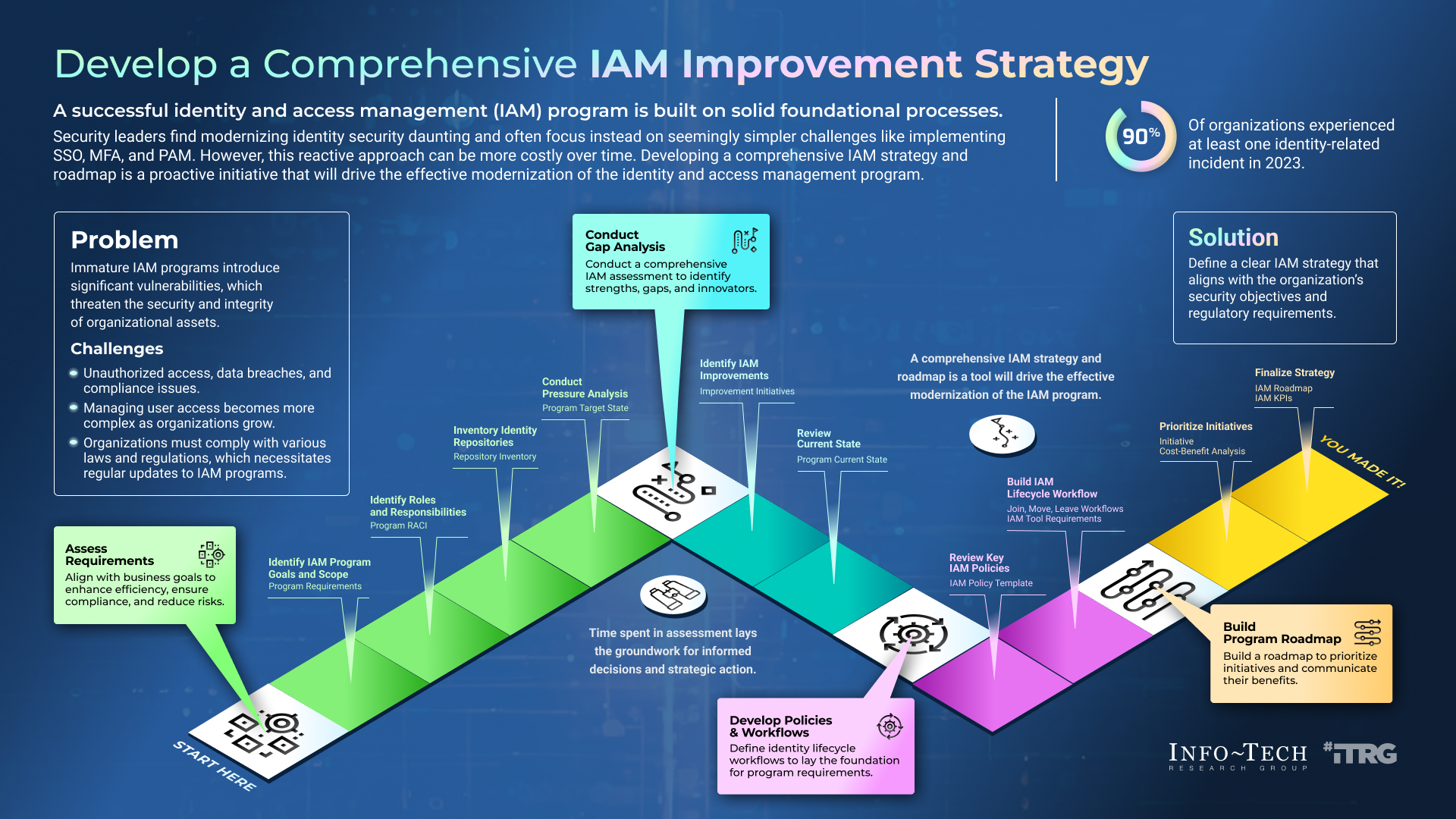
Poor Identity Governance
Without proper governance, identity management can quickly become chaotic. Common issues include:
- Lack of Visibility: Difficulty tracking who has access to what resources.
- Inconsistent Policies: Varying access policies across departments.
- Delayed Revocation: Slow removal of access for former employees.
Best Practices:
- Regularly audit access logs and identity policies.
- Implement automated identity lifecycle management, as suggested by IBM's best practices for handling insider threats.
Future Trends in Identity Security
Biometrics and Behavioral Analytics
Biometric authentication, such as fingerprint and facial recognition, is gaining traction. Paired with behavioral analytics, it offers robust security by continuously verifying user identity based on patterns and behaviors. The White House's focus on digital identity underscores the importance of these technologies.
- Adaptive Authentication: Adjusts security measures based on user behavior.
- Risk-Based Authentication: Dynamically applies authentication measures based on the risk level.
DID YOU KNOW: By 2025, it's estimated that 90% of businesses will use biometric authentication in some form, according to Fortune Business Insights.
AI and Machine Learning
AI-driven identity management systems can automatically detect and respond to threats. These systems learn from user behaviors and adapt security protocols in real-time. BitSight's analysis highlights the role of AI in vulnerability management.
- Anomaly Detection: Identifies unusual patterns that may indicate a breach.
- Predictive Analytics: Anticipates potential threats based on historical data.
Practical Implementation Guide
Step-by-Step: Implementing a Zero Trust Model
- Assess Current Security Posture: Identify gaps in existing identity management practices.
- Define Access Policies: Establish clear policies for who can access what resources.
- Deploy MFA Solutions: Implement MFA across all applications.
- Segment Networks: Use micro-segmentation to isolate sensitive data.
- Monitor and Adapt: Continuously monitor network activity and adapt policies as needed.
Tools and Technologies
- Identity Management Platforms: Solutions like Okta and Microsoft Azure Active Directory streamline identity governance.
- Endpoint Security Solutions: Tools that secure devices accessing the network.
- Security Information and Event Management (SIEM): Systems that provide real-time analysis of security alerts.
Conclusion
As the digital landscape evolves, so too must our approach to cybersecurity. By shifting the focus from perimeter defenses to identity verification, organizations can better protect themselves against modern threats. Implementing a Zero Trust architecture, coupled with robust identity management practices, is no longer optional—it's essential.
BOTTOM LINE: Identity is the new frontier in cybersecurity, and adopting an identity-first approach is crucial for safeguarding against evolving threats.
FAQ
What is identity-based security?
Identity-based security focuses on verifying who is accessing the system rather than where they are accessing it from. This approach emphasizes authentication and authorization to ensure that only legitimate users can access sensitive data.
How does Zero Trust architecture work?
Zero Trust operates on the principle of "never trust, always verify." It requires continuous authentication and verification of users, devices, and network traffic, regardless of their location.
What are the benefits of multi-factor authentication (MFA)?
MFA enhances security by requiring multiple forms of verification, reducing the risk of unauthorized access. Benefits include increased protection against phishing attacks and reduced reliance on passwords.
How can organizations improve identity governance?
Organizations can improve identity governance by implementing automated identity lifecycle management, regularly auditing access logs, and enforcing consistent access policies across all departments.
What role does AI play in identity security?
AI enhances identity security by enabling anomaly detection, predictive analytics, and adaptive authentication. These capabilities allow organizations to detect and respond to threats in real-time.
What is risk-based authentication?
Risk-based authentication dynamically adjusts security measures based on the assessed risk level of a user's access attempt, considering factors like location, device, and behavior.
Why is password reliance a security risk?
Over-reliance on passwords poses a security risk because weak or reused passwords can be easily exploited through phishing attacks or data breaches.
How does single sign-on (SSO) improve security?
SSO improves security by reducing password fatigue and the likelihood of users reusing passwords across platforms. It also streamlines the user experience, making it easier to enforce security policies.

Key Takeaways
- Identity is now central to cybersecurity, replacing the traditional perimeter focus.
- Zero Trust architecture emphasizes continuous authentication and micro-segmentation.
- Multi-factor authentication significantly reduces unauthorized access risks.
- Future trends include increased use of biometrics and AI-driven security.
- Organizations must adopt identity-first strategies to combat modern threats.
Related Articles
- Why Intelligence and Investigative Capability are Essential to Enterprise Security [2025]
- The FBI's Remote Router Resets: What It Means for Your Network [2025]
- Understanding Data Security in the Age of AI: Lessons from a US Bank Security Lapse [2025]
- Understanding the Security Implications of Running Claude Code in Chrome [2025]
- Google's Landmark Discovery: AI-Generated Zero-Day Exploit [2025]
- The Massive Banks of Malware: Visualizing the Data Giants [2025]
![Identity is the New Perimeter: The Shift from Breaking In to Logging In [2025]](https://tryrunable.com/blog/identity-is-the-new-perimeter-the-shift-from-breaking-in-to-/image-1-1778751261331.jpg)



