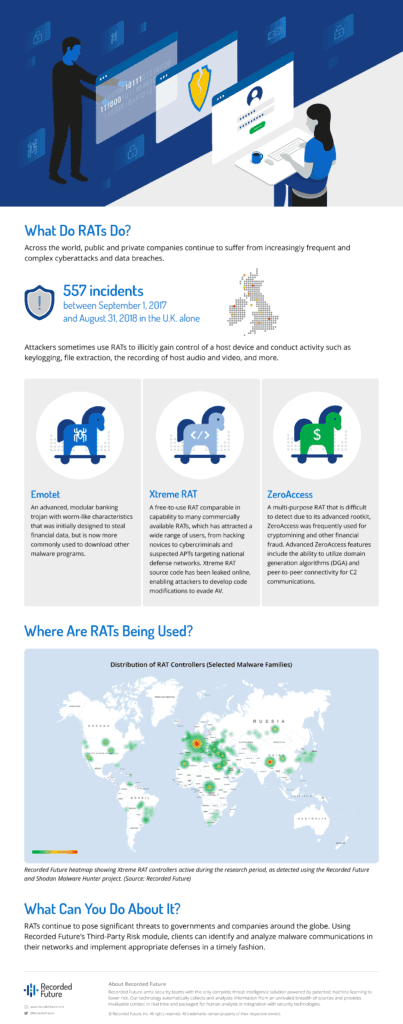
Fake Enterprise Software Hiding RATs: A Deep Dive Into Trust Connect [2025]
Someone put in a lot of effort to hide a remote access trojan in plain sight. And that detail alone should scare every IT security professional reading this.
In early 2024, security researchers at Proofpoint discovered something they hadn't encountered before: cybercriminals building an entirely fake enterprise software product, complete with a professional website, legitimate SSL certificates, and a subscription model charging $300 per month. But beneath the polished surface lay a sophisticated remote access trojan designed to give attackers complete control over victim systems.
The tool was called Trust Connect, and it represented a troubling evolution in how threat actors operate. Rather than compromising legitimate software or deploying malware through backdoor channels, these criminals invested thousands of dollars to create something that looked completely legitimate. Companies willingly installed it. They paid for subscriptions. And they had no idea they were hosting a backdoor on their critical infrastructure.
This isn't just another malware story. It's a cautionary tale about how the line between legitimate enterprise software and weaponized malware continues to blur, and how sophisticated social engineering now extends to the product level itself.
TL; DR
- Criminals built a fake RMM tool: Trust Connect appeared as a legitimate remote monitoring and management platform but was actually a remote access trojan distribution mechanism
- Professional deception required investment: Attackers paid thousands for SSL certificates and built entire websites, demonstrating unprecedented commitment to legitimacy
- Full system compromise capability: The tool granted attackers mouse and keyboard control, screen recording, file transfer, and command execution capabilities
- Advanced validation bypassed: Threat actors completed certificate validation procedures meant to prevent exactly this kind of attack
- Enterprise targets at risk: Organizations without proper software vetting procedures remain vulnerable to similar supply chain and social engineering attacks
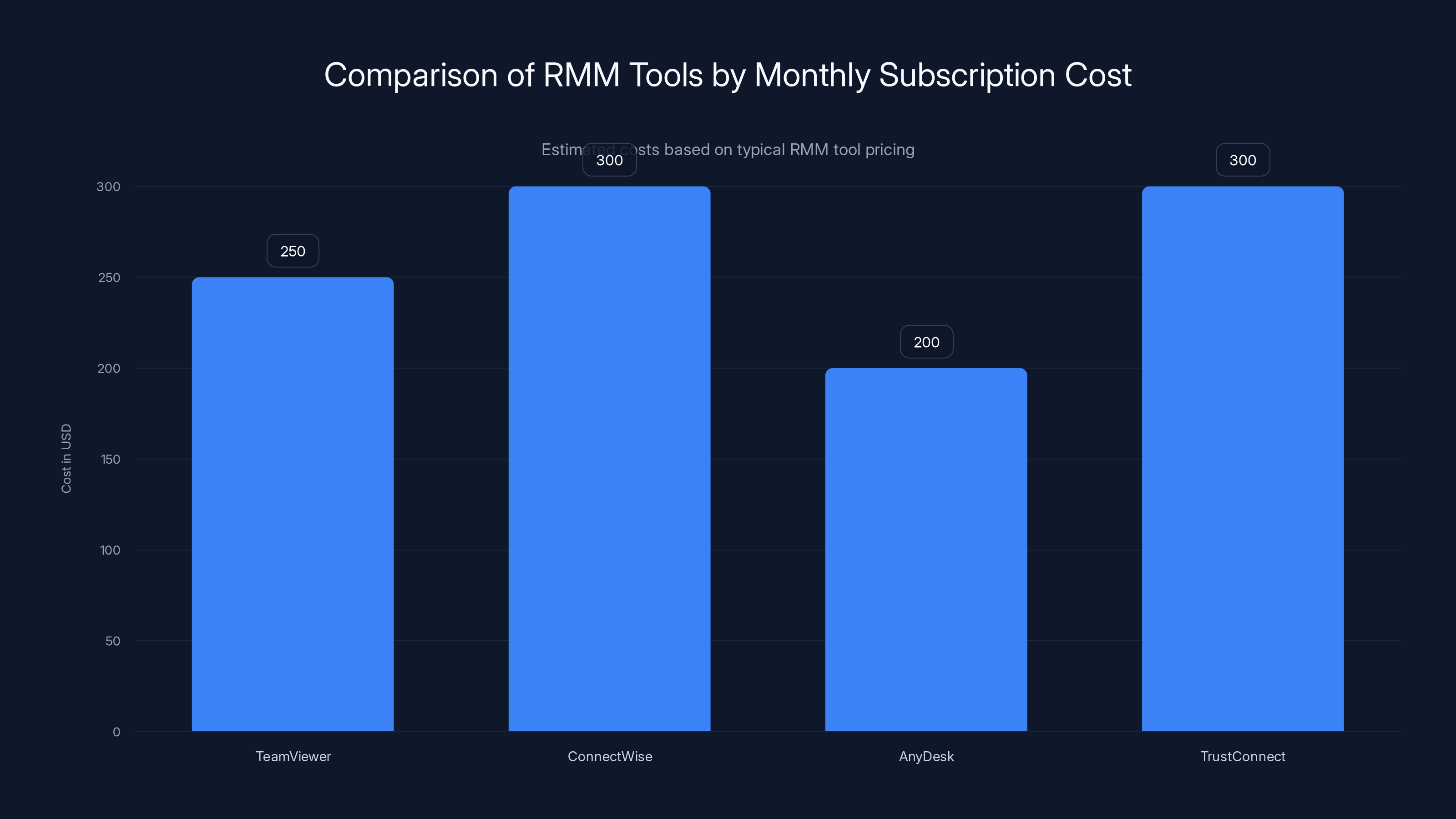
TrustConnect's pricing is comparable to legitimate RMM tools, making it deceptively appealing. Estimated data.
What Is Trust Connect? Understanding the Fake RMM Tool
When Proofpoint's researchers first encountered Trust Connect, their initial assessment made sense given the threat landscape. Remote monitoring and management (RMM) tools have become increasingly popular targets for malware distribution and compromise. Legitimate RMM software from vendors like TeamViewer, ConnectWise, or AnyDesk have been weaponized by threat actors multiple times over the past five years.
But Trust Connect wasn't a compromised legitimate tool. It was something entirely different.
The tool presented itself as a professional remote monitoring and management solution designed for MSPs (managed service providers) and enterprise IT departments. On the surface, Trust Connect offered everything you'd expect from a legitimate RMM platform: remote desktop access, file transfer capabilities, command execution, and system monitoring features. The website looked professional. The pricing ($300/month) fell within typical RMM subscription ranges. The branding communicated competence and reliability.
What made this different wasn't the feature set or the presentation. It was the underlying purpose. Every installation of Trust Connect was an installation of a remote access trojan. Every subscription payment went directly to funding criminal operations. Every company that deployed it was unknowingly granting attackers complete remote control over their systems.
The sophistication required to pull this off shouldn't be underestimated. Building fake enterprise software isn't something amateur cybercriminals do on weekends. It requires technical expertise to create functional software, web development skills to build a convincing website, financial resources to purchase legitimate SSL certificates, and operational security discipline to maintain the deception across multiple victim organizations.


Estimated data shows that with 50 customers, TrustConnect could generate $15,000 monthly, highlighting the potential financial incentive for threat actors.
The Anatomy of Deception: How the Attack Was Structured
What set Trust Connect apart from other malware campaigns wasn't just the fake software itself. It was the entire operational structure built around distributing and legitimizing it.
First, the criminals registered a domain with a .com extension. This choice matters. Many threat actors use unusual TLDs like .tk or .ml to save money, and security researchers actively monitor those domains. But .com is so common that suspicious domains can hide in plain sight among millions of legitimate businesses.
Second, they applied for an SSL certificate. This step is crucial because any modern web browser warns users when a website lacks HTTPS encryption or has an invalid certificate. Many users have learned to avoid such sites. But with a valid SSL certificate, the website appeared completely legitimate. Visitors would see the green lock icon indicating a secure connection. Nothing would suggest the site was hosting malware distribution.
What makes this step particularly remarkable is that the attackers had to go through the certificate validation process. Depending on the certificate type, this might involve email verification, domain ownership confirmation, or in some cases (for extended validation certificates), actual business verification. The criminals either created fake business documentation, used identity fraud, or had accomplices with legitimate business credentials help them through this process.
Third, they created functional software. We're not talking about a simple executable wrapper that drops malware. The criminals built what appeared to be a legitimate RMM tool with actual functionality. It could establish remote sessions, transfer files, execute commands, and monitor system activity. When someone installed Trust Connect and tested basic features, they would work as expected. The malicious functionality didn't interfere with legitimate operations. This is how they avoided immediate detection.
Fourth, they invested in customer acquisition. The criminals didn't just upload the software to random file sharing sites and hope people found it. They likely used targeted outreach, potentially posing as sales representatives from the "company," reaching out to MSPs and IT departments with marketing materials and trial offers. They might have purchased advertising or conducted spear-phishing campaigns. Every step was designed to make Trust Connect appear as a legitimate business opportunity.
Fifth, they maintained operational security throughout the campaign. The infrastructure supporting Trust Connect didn't overlap with other malware campaigns in obvious ways. They likely used separate payment processing, hosted the website on legitimate hosting providers, and compartmentalized information between the technical team building the software and the team handling customer acquisition.
When security researchers examined the certificate details, they found that it was revoked on February 6, 2024. But here's the catch: any files signed with the certificate before that date would remain valid. This means victims running Trust Connect installations from before the revocation date wouldn't get warnings from their systems even after the certificate became invalid. The software would continue functioning normally, continuing to grant attackers remote access.
The Technical Capabilities: What Attackers Could Actually Do
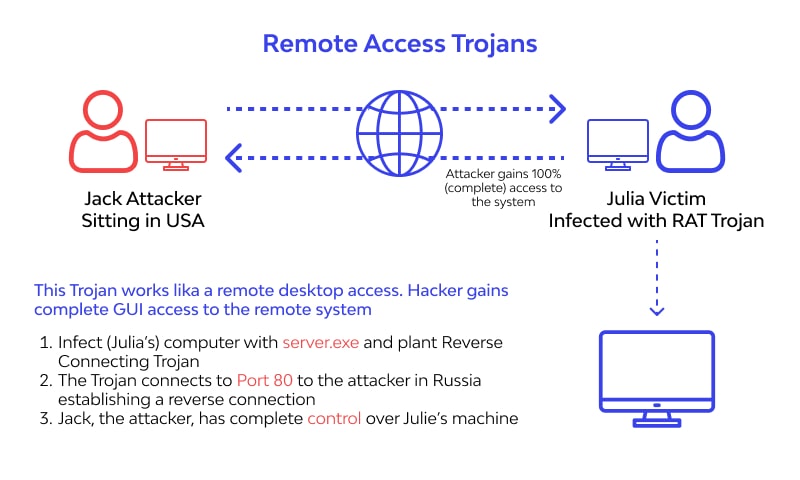
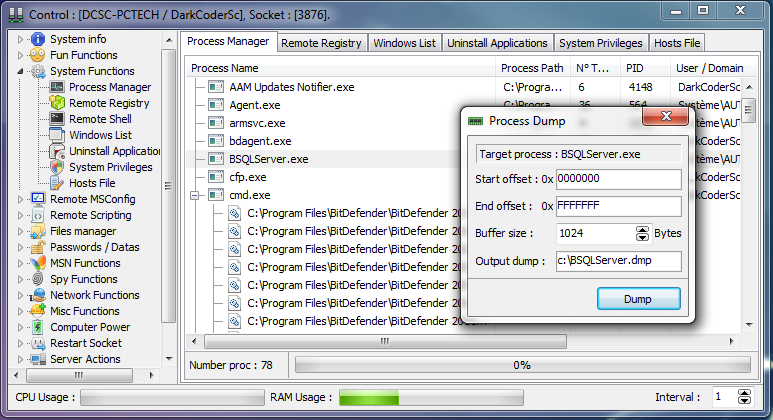
Trust Connect wasn't just a proxy tool that redirected traffic to other malware. It was a fully functional remote access trojan with comprehensive system control capabilities.
Once installed, Trust Connect gave attackers several critical capabilities:
Complete Remote Desktop Access: Attackers could establish remote sessions with full mouse and keyboard control. They could navigate the Windows desktop, open applications, interact with files, and perform any action that a legitimate user with those credentials could perform. For victims with elevated privileges, this meant complete system control.
Screen Recording and Streaming: The tool could record activity on the victim's screen and stream it in real-time to attackers. This served multiple purposes: confirming successful exploitation, monitoring user behavior to identify when to move laterally or exfiltrate data, and gathering intelligence about the victim's environment and security tools.
File Transfer Capabilities: Attackers could upload malware, tools, or legitimate utilities to the victim system. They could also download files, including sensitive documents, databases, source code, and other intellectual property. This made Trust Connect an ideal first-stage access tool for ransomware operations or data theft campaigns.
Command Execution: Through command-line interfaces (both Windows Command Prompt and Power Shell), attackers could execute system commands directly. This allowed them to install additional malware, disable security tools, create new user accounts for persistence, modify system settings, or launch attacks against other systems on the network.
User Account Control Bypass: One of the most dangerous capabilities was the ability to bypass Windows UAC (User Account Control) prompts. UAC is a security feature that prevents unauthorized system changes even if an attacker gains user-level access. By bypassing it, Trust Connect attackers could modify system settings, install drivers, or access protected areas that would normally require administrator interaction. This dramatically increased the scope of what attackers could accomplish.
Beyond these direct control capabilities, Trust Connect also provided the foundation for what security researchers call "post-exploitation" activities. Once inside a network through one system, attackers could use Trust Connect to scout the environment, identify valuable targets, create persistence mechanisms to maintain access even after the initial malware is removed, and launch lateral movement attacks to compromise additional systems.
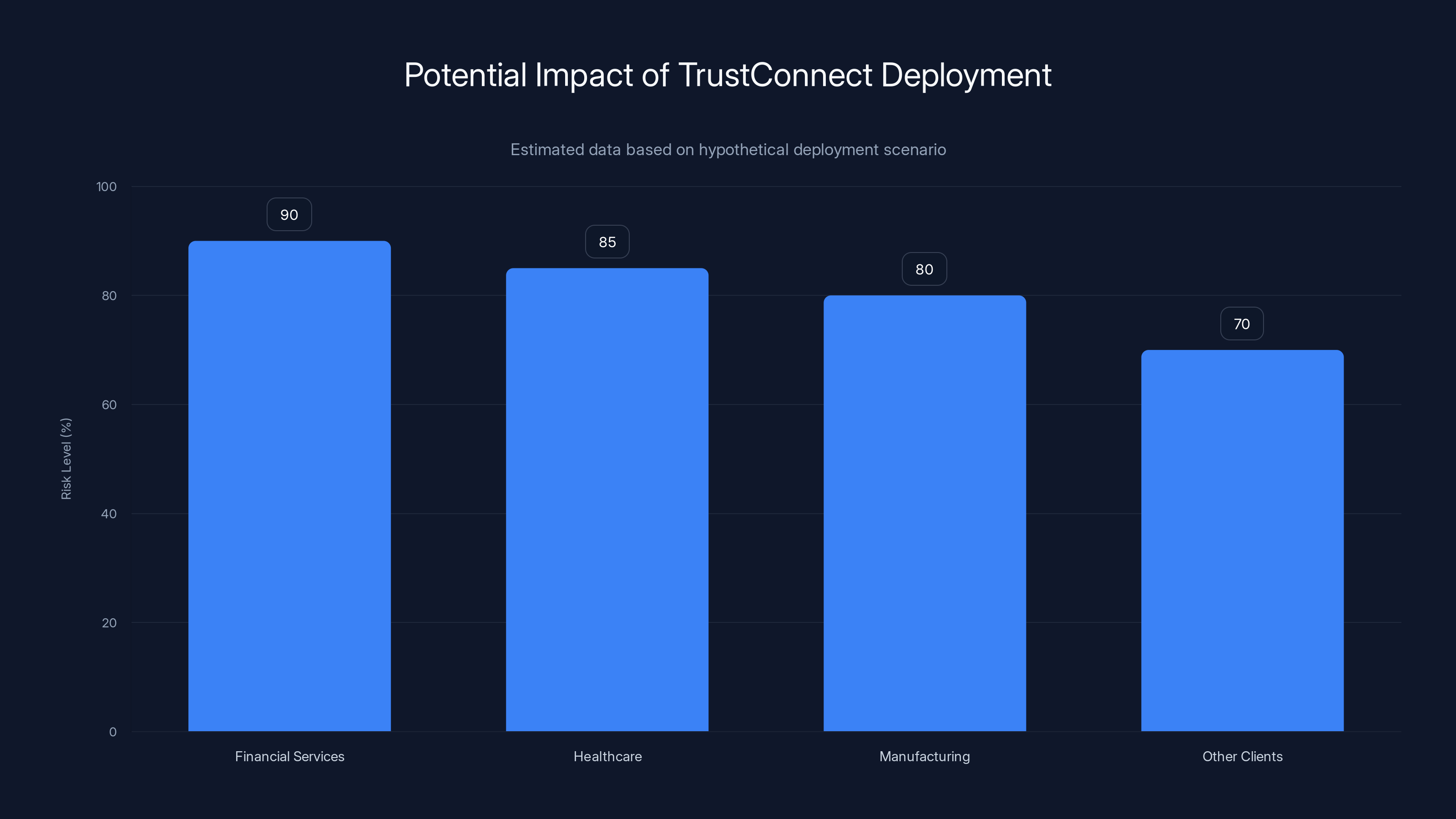
Estimated data shows that financial services clients face the highest risk level at 90%, followed closely by healthcare and manufacturing clients. Estimated data.
The Connection to Redline: Understanding the Criminal Infrastructure
Proofpoint researchers made a crucial connection when analyzing Trust Connect: they found evidence linking it to Redline, a sophisticated infostealer malware that's been active since at least 2020.
Redline isn't sold to random customers. It operates on a selective customer basis, meaning that access to Redline is restricted to trusted threat actors who've been vetted by the Redline development and sales team. This isn't amateur-hour cybercrime. Redline is a professional criminal tool used by organized crime groups, financially motivated threat actors, and possibly state-sponsored operations.
The connection between Trust Connect and Redline wasn't a chance encounter. Proofpoint found evidence suggesting that Trust Connect was developed by someone with close ties to Redline's operations. They used the phrase "moderately confident," which in security research language means they have substantial evidence but can't definitively prove it without access to the criminals' internal communications or financial records.
Why would a Redline customer build their own RMM tool? Several reasons become apparent:
First, distribution diversification: Redline's primary distribution method had likely been detected and countered by security vendors and enterprises. By building a new tool that appeared to be legitimate software, the criminals created a distribution channel that security tools wouldn't recognize as malicious.
Second, operational flexibility: Redline is designed to steal information and credentials. Trust Connect, as a remote access trojan, provided direct system access. Using them together created a powerful combination. Redline could identify valuable systems and steal credentials, then Trust Connect could be deployed to those systems to enable direct exploitation.
Third, compartmentalization: By creating a distinct tool separate from Redline, the criminals could operate it independently without compromising their primary infostealer operation if Trust Connect was discovered or taken down.
Fourth, monetization: Running Trust Connect as a "legitimate" Saa S product with subscription fees created a direct revenue stream that could be laundered through payment processors more easily than malware licensing fees.

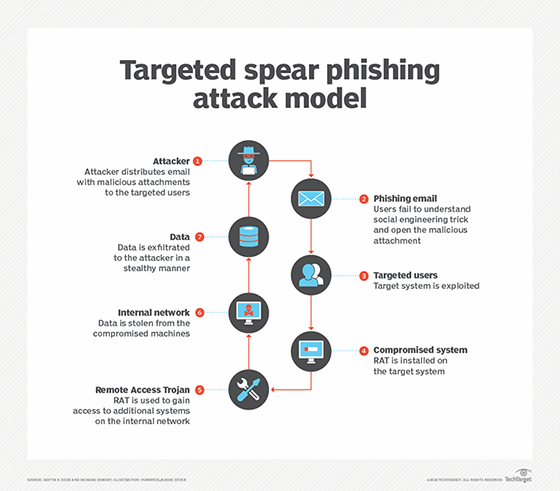
The Targeting Strategy: Who Was Vulnerable?
Criminals don't randomly distribute malware. They have targets in mind, and Trust Connect's distribution strategy reflects careful targeting.
MSPs (Managed Service Providers) were likely the primary target. MSPs manage IT infrastructure for multiple client organizations, often handling hundreds or thousands of systems remotely. Compromising an MSP means gaining access to all their client organizations at once. A single MSP breach could expose dozens or hundreds of companies to attackers.
Security researchers and threat hunters were secondary targets. By making Trust Connect appear legitimate, criminals could potentially get security researchers to "test" it in controlled lab environments, potentially gathering information about detection methods or even compromising the researchers' systems.
Enterprise IT departments with less sophisticated security practices were also targets. Larger enterprises often have multiple tools and subscriptions, and IT personnel might not have the time or resources to thoroughly vet every new piece of software before deploying it.
The targeting likely involved social engineering. Someone claiming to represent Trust Connect's sales team might contact MSP owners or IT managers, offering a trial period, demonstrating the software's features, or providing testimonials from supposed other customers. For victims, there would be no indication that anything was wrong until attackers started their exploitation.

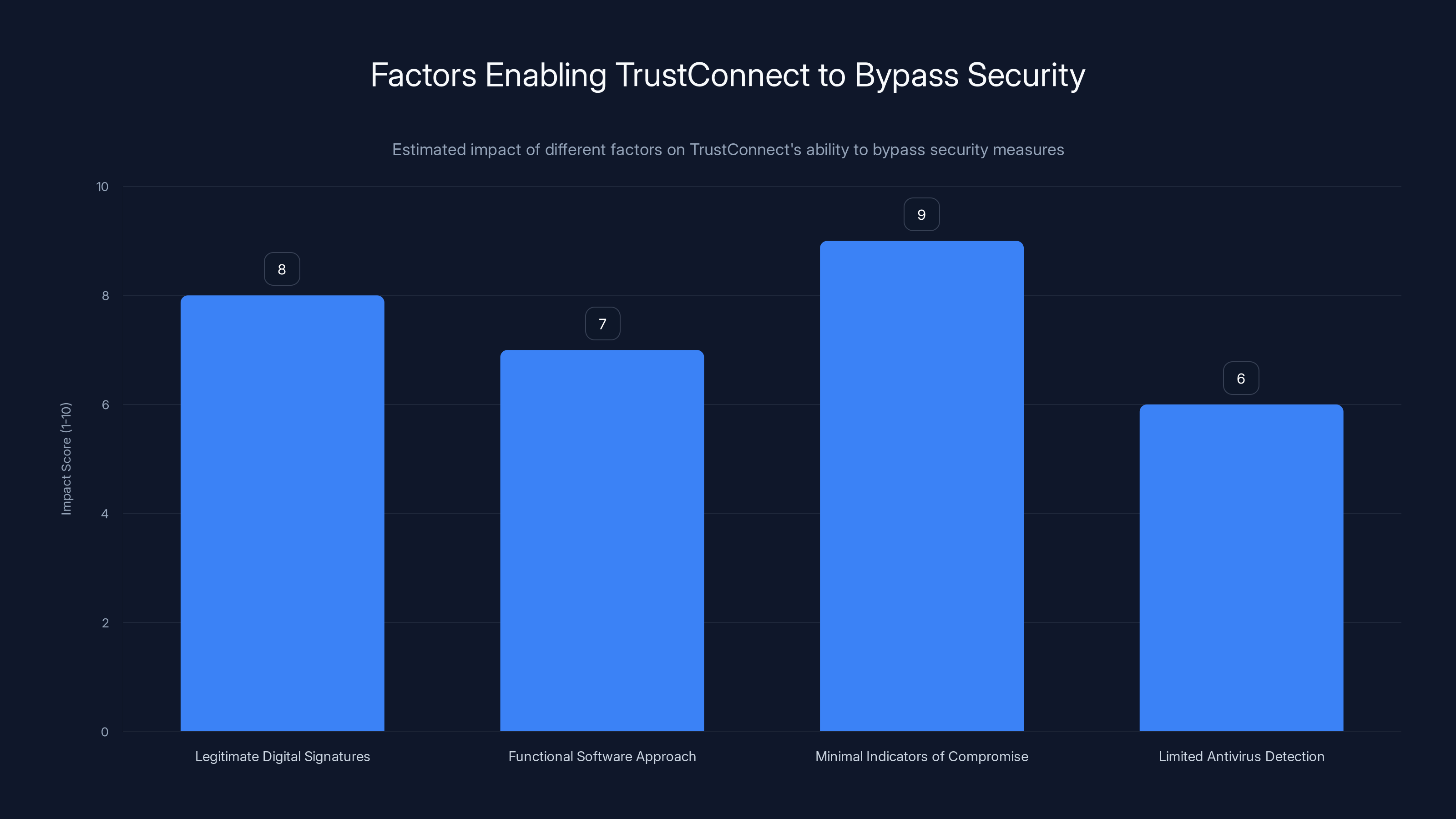
Estimated data suggests that 'Minimal Indicators of Compromise' had the highest impact on TrustConnect's ability to bypass security measures, followed by 'Legitimate Digital Signatures'.
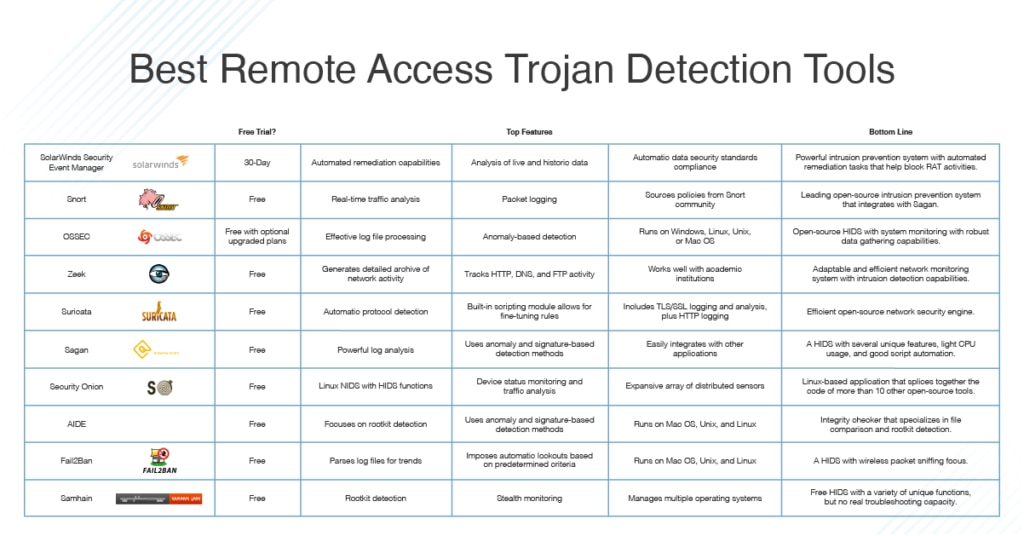
How the Deception Bypassed Security Measures
Modern security practices should theoretically catch something like Trust Connect. Organizations should be vetting software, scanning for malware, monitoring for suspicious behavior. So how did this threat get past these defenses?
Legitimate Digital Signatures: The SSL certificate wasn't the only legitimate credential Trust Connect possessed. The executable files were likely digitally signed with a legitimate code signing certificate. Code signing allows developers to prove that their software hasn't been modified and identifies who published it. It's a trust mechanism built into Windows and other operating systems. With valid code signing certificates, Trust Connect's installer would pass initial security checks that many organizations rely on.
Functional Software Approach: Unlike many malware variants that are basically legitimate executables with malicious payloads attached, Trust Connect was built as legitimate-appearing software. It had a real installer, proper registry entries, legitimate-looking services and processes. When an administrator launched it and tested basic features like remote access or file transfer, it worked correctly. There was nothing obviously wrong.
Minimal Indicators of Compromise: Well-written malware doesn't scream its presence. Trust Connect likely communicated with command and control (C2) servers over HTTPS using legitimate-looking traffic patterns. It probably didn't create unusual registry entries or system artifacts. It likely didn't immediately consume excessive system resources. For the first hours or days of operation, a system running Trust Connect might appear completely normal.
Limited Antivirus Detection: At the time of discovery, many antivirus and endpoint detection and response (EDR) systems might not have had signatures for Trust Connect. It was a new tool. Detection depends on either discovering it in the wild and analyzing it, or on security researchers obtaining samples and sharing them with the broader security community. The gap between when new malware appears and when security vendors detect it is often weeks or months.
Supply Chain Legitimacy: Because Trust Connect was distributed through ostensibly legitimate sales channels rather than malicious links or spam emails, many organizations would perceive it as having supply chain legitimacy. "Someone in our industry uses this" or "The salesman seemed professional" creates trust that security measures aren't designed to overcome.

The Shift in Threat Actor Sophistication: What Trust Connect Represents
Trust Connect is significant not because it's the first malware ever created, but because of what it reveals about how threat actors are evolving their tactics.
For decades, the cybercrime ecosystem operated primarily through abuse and compromise. Attackers found legitimate tools with vulnerabilities or design flaws, then weaponized them. They created malware that mimicked legitimate processes, hiding in noise. They used social engineering to trick users into installing malicious software by disguising it as something else.
Trust Connect represents a different approach: legitimacy as camouflage. Rather than trying to hide malicious intent, the criminals created something that genuinely appeared to be legitimate enterprise software. They weren't trying to sneak past defenses by being invisible. They were trying to walk through the front door by being indistinguishable from legitimate vendors.
This approach requires different skills than traditional malware development. You need product managers who understand what features a legitimate RMM tool would have and how they should behave. You need software engineers who can implement those features properly. You need web developers, Dev Ops engineers, customer support staff, and sales people. You need to maintain the deception consistently across all customer interactions.
Why would threat actors invest this much effort? Several reasons:
Economies of Scale: A legitimate-appearing tool can be sold to many customers at once. Unlike traditional malware distribution, where success rates might be measured in percentages, Trust Connect could potentially be sold to hundreds of organizations. At
Reduced Detection Risk: Traditional malware campaigns are race-against-time situations. Once security vendors detect malware, its usefulness drops dramatically. But a legitimate-appearing product can operate openly. Security researchers might take weeks or months to realize it's malicious, especially if the attacks using it are subtle.
Operational Consistency: Maintaining a fake business creates a veneer of professionalism that helps attract higher-value targets. An MSP considering a new RMM tool would conduct due diligence differently than someone receiving an unsolicited email with an executable attachment.
Sustained Revenue: Unlike one-time malware sales, a subscription model creates ongoing revenue. Customers pay monthly, creating predictable income that can be laundered through legitimate financial channels more easily than direct malware licensing fees.
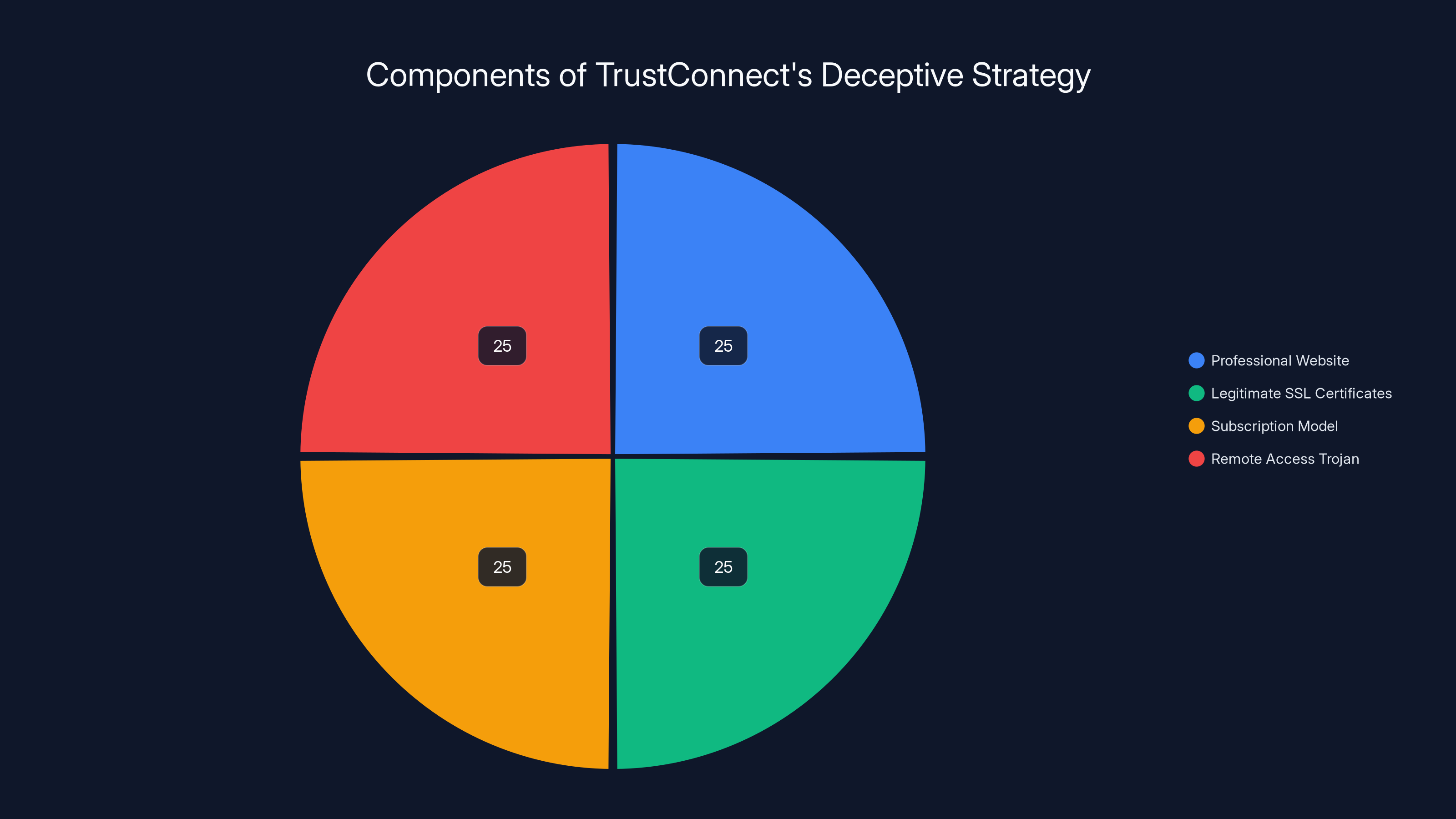
TrustConnect's strategy involved equal emphasis on a professional facade and hidden malware, showcasing a new level of sophistication in cyber threats. Estimated data.
Enterprise Software Vetting: Why Traditional Approaches Failed
Most organizations have some process for evaluating new software before deployment. So why did legitimate-appearing vendors like Trust Connect slip through?
Compressed Vetting Timelines: In the race to digital transformation, many organizations shortened their software evaluation processes. A tool that would have been evaluated over weeks or months five years ago might now be approved in days. Faster decisions leave less time for thorough investigation.
Trust in Professional Appearances: The quality of web design, professional branding, and legitimate-seeming business documentation has become easier to produce and harder to verify. A small team using modern web frameworks and design tools can create a website that's indistinguishable from a legitimate mid-sized software company.
Fragmented Responsibility: In larger organizations, the person discovering the software, the person evaluating it, and the person approving it might be different people with incomplete communication between them. This fragmentation means no single person has enough context to spot red flags.
Limited Threat Intelligence Integration: Many organizations don't actively check new software vendors against threat intelligence databases or recent security advisories. They might not search the vendor name in security research forums or check if the software has been flagged as suspicious.
False Sense of Supply Chain Security: Just because software appears on the internet and looks professional doesn't mean it's legitimate. But many organizations haven't yet developed the skepticism necessary to treat new vendors with appropriate caution.
Certificate Authority Trust: When an SSL certificate is valid and a code-signing certificate is legitimate, it signals legitimacy to both humans and security tools. We've trained everyone (humans and systems) that valid certificates equal safe software. Trust Connect exploited this assumption.

The Detection Process: How Proofpoint Found It
Understanding how security researchers discovered Trust Connect provides insight into how similar threats might be found in the future.
Proofpoint likely encountered Trust Connect through one or more of these vectors:
Customer Telemetry: Someone who had deployed Trust Connect submitted sample files to Proofpoint for analysis, either because their security tools flagged it or because they were suspicious of suspicious behavior.
Threat Hunting: Proofpoint researchers might have been investigating related malware campaigns or analyzing Redline infrastructure when they discovered connections to Trust Connect.
OSINT (Open Source Intelligence): Researchers monitoring domain registrations, SSL certificate transparency logs, or similar infrastructure might have flagged Trust Connect's domain as suspicious based on patterns associated with malicious activity.
Incident Response: Proofpoint consultants might have encountered Trust Connect while responding to client breach investigations, discovering it on compromised systems and recognizing it as something new.
Once they had a sample, the analysis process would have involved:
Static Analysis: Examining the executable's structure, imports, and resources without running it. Legitimate RMM software might have similar characteristics, but analysts look for code patterns associated with malware.
Dynamic Analysis: Running Trust Connect in a controlled lab environment and monitoring what it does: what network connections it makes, what files it creates, what registry keys it modifies, what processes it launches. This reveals the actual functionality and intent.
Infrastructure Analysis: Tracing the command and control servers that Trust Connect communicated with, examining domain registration details, hosting provider, SSL certificates, and historical DNS records. This often reveals connections between different malware campaigns.
Behavioral Analysis: Examining the actual attacks enabled by Trust Connect: what kind of network reconnaissance did attackers perform, what was exfiltrated, what follow-up malware was deployed.
The confidence level ("moderately confident") that Proofpoint expressed about the Redline connection likely came from analyzing the infrastructure overlap: similar command and control infrastructure, similar operational patterns, or direct evidence in the code or configuration files.
Managed Service Providers were the primary target of TrustConnect malware, estimated at 50% of the targeting strategy, due to their access to multiple client systems. Estimated data.
Broader Implications: The Legitimacy Trend in Malware Development
Trust Connect isn't an isolated incident. It represents a broader trend in how sophisticated threat actors operate.
In recent years, the cybercrime ecosystem has increasingly realized that appearing legitimate is more effective than trying to hide. This manifests in several ways:
Fake Saa S Platforms: Beyond Trust Connect, criminals have created fake productivity software, business intelligence tools, security software, and development utilities. Each maintains the appearance of legitimacy through professional websites, customer reviews (often fake), and functional software.
Legitimate Business Operations: Some malware-as-a-service operations now run like actual software companies. They maintain customer support channels, publish updates, fix bugs, and provide documentation. From a user perspective, it feels like dealing with any other Saa S vendor.
Supply Chain Exploitation: Rather than compromising legitimate software, some threat actors are creating their own "legitimate" supply chain. They develop software under multiple brand names, build affiliate networks of "resellers," and create an entire ecosystem of legitimacy.
Professional Branding: The polish and professionalism of malware platforms has increased dramatically. Gone are the days of obvious malware installers or suspicious-looking download pages. Modern threats often look and feel indistinguishable from legitimate enterprise software.
Persistence Through Legitimacy: Unlike traditional malware that becomes obsolete once detected, fake-legitimate platforms can persist as long as the deception holds. They can operate openly, advertise (carefully), and build customer bases without the operational security constraints of traditional underground malware.
This trend creates a fundamental challenge for defenders: traditional security approaches based on distinguishing malicious from legitimate traffic break down when attackers present themselves as legitimate.

Defense Strategy: Protecting Against Legitimate-Appearing Malware
Given that threat actors are investing significant resources into creating legitimate-appearing malware, how should organizations defend themselves?
Software Source Verification: Never install software based solely on finding it online or receiving a sales pitch. Verify the vendor through independent channels. Check if they have a physical office address, active team members on Linked In, presence in industry directories, or coverage in reputable technology press. Create a whitelist of approved software vendors.
Centralized Procurement: Require all software purchases to go through a centralized procurement process where someone with security knowledge evaluates each new tool. This prevents individual team members from independently choosing tools that security hasn't reviewed.
Behavioral Analysis Over File Analysis: Rather than relying solely on malware signatures (which don't exist for new tools), focus on behavioral analysis. What network connections does the software make? What files does it access? What system resources does it consume? Modern EDR (Endpoint Detection and Response) tools excel at identifying suspicious behaviors even from previously unknown malware.
Least Privilege Enforcement: Even if malware infiltrates a system, limiting user privileges restricts what attackers can accomplish. Require administrative credentials for legitimate RMM tools and monitor their usage carefully. Most business users shouldn't have admin rights.
Network Segmentation: If Trust Connect compromises a system, it shouldn't automatically have access to the entire network. Network segmentation ensures that compromising one system doesn't compromise the entire infrastructure. MSPs should especially implement strict network segmentation since they manage critical infrastructure.
Supply Chain Security Programs: Implement formal vendor management processes that include security questionnaires, verification of certifications, and ongoing compliance monitoring. Organizations in regulated industries often require this for compliance reasons, but it should be standard practice for all organizations.
Security Awareness Training: Train employees to be suspicious of new software, to verify vendors independently, and to report suspicious solicitations. Many malware campaigns succeed because someone made a decision based on incomplete information.
Incident Response Readiness: Despite best efforts, some threats will get through. Prepare for that by ensuring you can detect and respond to compromises quickly. This means monitoring for indicators of compromise, having security playbooks ready, and conducting regular incident response drills.

The Role of Certificate Authorities and Trust Infrastructure
One of the most troubling aspects of Trust Connect is that the attackers successfully obtained legitimate SSL and code-signing certificates. This raises important questions about how certificate authorities verify identity and whether the current system is adequate.
SSL certificates are issued by Certificate Authorities (CAs), trusted entities that verify the ownership of domains before issuing certificates. In theory, you can't get an SSL certificate for a domain you don't own. CAs use various verification methods: email to the domain registrant, DNS record verification, HTTP file verification, or for high-assurance certificates, actual business verification.
But here's the problem: obtaining a domain is trivial. Anyone can register a domain using fake information (and many registrars don't verify identity). Once you "own" a domain (even through false registration), you can easily obtain an SSL certificate for it.
The Trust Connect attackers either:
- Registered a domain using fraudulent information and then obtained a certificate
- Used stolen identity information or documents to register and verify the domain
- Compromised a legitimate domain and used it for their purposes
- Had accomplices with legitimate business identities help them through the verification process
For code-signing certificates (which digitally sign executable files), the verification process is often more rigorous, involving actual business verification. That the attackers successfully obtained one suggests either significant effort to create fake business credentials or potentially insider help from someone with legitimate credentials.
This raises a critical question: Is the current certificate infrastructure adequate for establishing trust? Many security experts argue that it isn't, which is why modern browsers and operating systems increasingly rely on other signals for establishing trust: reputation databases, community feedback, installation sources, and user behavior analysis.
Future Landscape: What Comes Next
If Trust Connect represents a trend in threat actor evolution, what should we expect going forward?
More Sophisticated Fake Platforms: We'll likely see threat actors creating entire fake software ecosystems. Instead of a single Trust Connect, criminals might create a suite of complementary tools (a fake RMM, a fake security software, a fake backup utility) that integrate with each other, creating an even more convincing appearance of legitimacy.
Longer Operational Lifespans: As detection mechanisms become more sophisticated, legitimate-appearing malware will operate for longer periods before discovery. Trust Connect might represent months of undetected operations, and future variants might operate for years.
More Targeted Fake Products: Rather than creating one generic tool for everyone, threat actors might develop industry-specific or organization-specific fake software. Fake tools designed specifically for financial services companies, healthcare organizations, or government agencies would have even higher success rates.
Persistent Marketing Infrastructure: Threat actors will invest more in maintaining the appearance of legitimate businesses, including real customer support, realistic marketing, and seemingly authentic business operations that persist even after the malware functionality is discovered.
Blurred Lines Between Legitimate and Malicious: As threats become more sophisticated, the distinction between a software vendor's legitimate business model and their malware distribution model might blur. Some legitimate vendors might cut corners on security or be coerced into assisting threat actors.
For defenders, this means adapting security philosophies. Rather than trusting software sources, we need to assume all software is potentially malicious and design defenses based on behavioral analysis, privilege minimization, and network isolation. The assumptions that worked in the past—"legitimate software from a legitimate vendor can be trusted"—are increasingly inadequate.

Case Study: A Hypothetical Trust Connect Deployment
To fully understand the threat Trust Connect represented, consider a hypothetical deployment scenario:
An MSP called "Cloud Tech Solutions" manages IT infrastructure for 30 client organizations, ranging from 50 employees to 500 employees each. One of Cloud Tech's IT managers sees a sales email about Trust Connect, a new RMM tool that's supposedly cheaper and more feature-rich than their current tool (Connect Wise). Interested, the manager visits the Trust Connect website, which looks professional and includes case studies from other MSPs.
After a brief trial, Cloud Tech deploys Trust Connect to their management server. Over the next week, they integrate it with their client systems. Soon, Trust Connect is monitoring and managing infrastructure across all 30 clients.
Unknown to Cloud Tech, the Trust Connect installation provides attackers with remote access to their management infrastructure. The attackers begin reconnaissance: identifying high-value targets among Cloud Tech's clients (maybe the financial services company, the healthcare provider, the manufacturing firm with valuable IP), mapping network topology, and identifying security tools in place.
Over the next month, attackers use Trust Connect to deploy additional malware to selected target systems. They might install ransomware loaders, data exfiltration tools, or secondary backdoors for persistence. Meanwhile, Cloud Tech has no indication that anything is wrong.
Eventually, attackers launch their primary attack: deploying ransomware across multiple client organizations simultaneously. By the time anyone realizes what's happened, critical data has been exfiltrated, systems are encrypted, and recovery will cost months and millions of dollars.
Postmortem investigation reveals Trust Connect. By that point, the attackers have already moved their infrastructure. The legitimate-looking Saa S platform has disappeared. The fake company is gone. All that remains is damage and questions about how the threat got through.
This scenario, while hypothetical, illustrates why Trust Connect is significant. It's not just malware. It's a blueprint for sophisticated attacks that leverage human trust in professional software and legitimacy.
Key Lessons for Security Professionals
What should security teams take away from the Trust Connect incident?
First, elevate your software vetting process: If you don't have a formal procedure for evaluating new software before deployment, create one now. This doesn't need to be burdensome, but it should include independent verification of vendor legitimacy.
Second, implement behavioral monitoring: Signature-based detection can't catch threats that look legitimate. Implement EDR solutions that monitor for behavioral anomalies. What network connections is the software making? What files is it accessing? What system resources is it consuming?
Third, enforce privilege minimization: Even legitimate software should run with the minimum privileges necessary. RMM tools should have administrative credentials, but user accounts shouldn't. This principle applies to all software.
Fourth, develop supply chain security practices: Especially if you manage infrastructure for clients or operate as an MSP, formalize how you evaluate, test, and deploy new tools. Make it a repeatable process that catches issues before they spread.
Fifth, foster healthy skepticism: Encourage your team to be suspicious of new tools, especially those offered by vendors with minimal history or verifiable track record. A professional-looking website and friendly sales pitch aren't evidence of legitimacy.
Sixth, maintain incident response readiness: Assuming some threats will get through, ensure you can detect and respond to them quickly. This means threat hunting capabilities, incident response plans, and regular tabletop exercises.
FAQ
What exactly is Trust Connect and how did it deceive companies?
Trust Connect was a fake remote monitoring and management (RMM) tool created by cybercriminals to distribute a remote access trojan. The attackers registered a legitimate domain, obtained valid SSL certificates, built functional RMM software, and created a professional website. To companies investigating before purchase, Trust Connect appeared to be a legitimate enterprise software product. Organizations actually paid $300 monthly subscriptions believing they were purchasing a legitimate tool, when in fact they were installing malware that gave attackers complete control over their systems.
How did the criminals bypass security measures and obtain legitimate certificates?
The attackers registered a domain (potentially using fraudulent information), then obtained SSL certificates by completing certificate authority verification processes. The verification for SSL certificates often requires only domain ownership confirmation, which is easy to achieve if you control the domain. For code-signing certificates, they likely either created sophisticated fake business documentation or potentially had insider help. Once they had valid certificates, security tools and web browsers recognized their software as legitimate, significantly reducing detection risks.
What capabilities did Trust Connect give attackers once installed?
Trust Connect provided complete remote system control, including mouse and keyboard access, screen recording and streaming capabilities, file transfer functionality, command execution privileges, and the ability to bypass Windows User Account Control. These capabilities transformed infected systems into fully controllable platforms for attackers. From a single compromised system, attackers could move laterally across networks, install additional malware, exfiltrate data, or launch targeted attacks against other systems in the same organization.
Why would criminals invest this much effort into building fake software?
This represents an evolution in threat actor sophistication. Creating legitimate-appearing software allows criminals to operate openly without hiding in shadows, reach more victims through professional sales channels, avoid detection for longer periods, and generate sustained revenue through subscription models. Unlike traditional malware that becomes useless once detected, fake legitimate products can persist for months or years. The return on investment—potentially hundreds of thousands in monthly revenue—justifies the technical effort required to build functional software and maintain a fake business operation.
How is Trust Connect connected to Redline infostealer?
Proofpoint researchers determined with "moderate confidence" that Trust Connect was developed by someone with close ties to Redline, a sophisticated infostealer malware operated by organized cybercriminals on a selective customer basis. The connection suggests integration between Redline's credential theft capabilities and Trust Connect's direct system access. Attackers could use Redline to identify high-value systems and steal credentials, then use Trust Connect for direct exploitation. This compartmentalization protects their primary tool (Redline) if Trust Connect is discovered.
What defense strategies are most effective against legitimate-appearing malware?
Effective defenses include: implementing formal software vetting procedures before deployment, using behavioral analysis rather than relying solely on malware signatures, enforcing strict privilege minimization so compromised systems can't do unlimited damage, implementing network segmentation to contain breaches, developing comprehensive vendor management and supply chain security programs, and maintaining incident response readiness with threat hunting capabilities. No single defense catches everything, but layering multiple approaches makes attacks significantly more difficult and easier to detect.
How should MSPs specifically protect themselves from supply chain attacks like Trust Connect?
MSPs managing client infrastructure should implement software change control processes for any new tools before deployment across clients. This might include: security questionnaire requirements for new vendors, independent verification of vendor legitimacy through multiple channels, testing in isolated environments before client deployment, and behavioral monitoring of new tools in production. Given that compromising an MSP provides access to all their clients simultaneously, the stakes for MSPs are higher than individual organizations. Even brief verification before deploying something to hundreds of systems could prevent catastrophic breaches.
What trends suggest Trust Connect represents broader changes in how threat actors operate?
Trust Connect exemplifies a shift from "hiding in plain sight" to "hiding in legitimacy." Sophisticated threat actors increasingly recognize that appearing legitimate—with professional websites, valid certificates, functional software, customer support—is more effective than attempting to avoid detection. This trend manifests in fake Saa S platforms, malware-as-a-service operations that mimic legitimate companies, and fake supply chains. Future threats will likely operate longer before discovery, be more targeted to specific industries, and maintain increasingly convincing appearances of legitimacy. This fundamentally changes how defenders must approach security, shifting from trusting sources to monitoring behavior and implementing technical controls that limit what any software—legitimate or malicious—can accomplish.
Conclusion: A New Era of Enterprise Threats
The Trust Connect incident represents a watershed moment in the evolution of enterprise-focused cybercrime. For years, the conventional wisdom held that professional-looking software from established vendors was relatively safe, while suspicious downloads and unusual emails should be avoided. Trust Connect demolishes that assumption by showing that threat actors are willing and able to create entirely fake businesses complete with legitimate credentials to distribute malware.
What makes Trust Connect particularly significant isn't just the technical execution—building an RMM tool with malicious backdoors isn't trivial, but it's within the capabilities of sophisticated threat actors. What's significant is the commitment to legitimacy. Registering domains, obtaining SSL certificates, building professional websites, maintaining operational security, and conducting targeted outreach all require coordination, funding, and discipline. The attackers didn't cut corners. They didn't create obviously suspicious software. They created something indistinguishable from legitimate products that thousands of organizations use daily.
This approach works because traditional security measures rely on distinguishing legitimate from malicious. We've trained everyone—humans and security tools—to trust valid certificates, professional branding, and legitimate business operations. Trust Connect exploited these exact assumptions.
For security professionals, the implications are sobering. The threat landscape has evolved beyond malware that tricks users into installing it through deception about what it does. The new frontier involves threat actors creating entirely fake companies and products that legitimately appear to be what they claim. Defending against this requires different approaches than defending against traditional malware.
This doesn't mean legitimate software is now inherently untrustworthy. It means that trust can't be based solely on appearance, certificates, or vendor legitimacy claims. Instead, defenses must assume the worst about all software and implement technical controls—behavioral monitoring, privilege minimization, network segmentation—that limit what any software can accomplish regardless of its legitimacy.
Organizations that adapt to this new threat landscape—by implementing rigorous software vetting, behavioral monitoring, privilege restrictions, and incident response readiness—will be significantly more resilient. Those that continue assuming legitimate-appearing software can be trusted will remain vulnerable.
The rise of threats like Trust Connect signals that cybercrime has matured into an operational discipline indistinguishable from legitimate business practice. Defending against it requires matching that sophistication with equally mature security practices.
For teams building critical applications and managing security operations, implementing automated security workflows and compliance monitoring can significantly reduce the attack surface. Tools that enable rapid incident response, automated threat detection, and streamlined security operations become increasingly essential as threats evolve. Consider how your security stack adapts to threats that exploit legitimacy rather than attempting to hide.

Key Takeaways
- TrustConnect represents an unprecedented threat: criminals building entirely fake enterprise software with legitimate certificates, not just compromising existing tools
- The attackers invested thousands in SSL certificates and business infrastructure, indicating a fundamental shift in threat actor sophistication and resources
- Traditional security measures that trust legitimate-appearing software are inadequate against adversaries who perfect the appearance of legitimacy
- Behavioral monitoring and privilege minimization have become more important than signature-based detection for catching threats that genuinely appear legitimate
- Organizations managing infrastructure for clients (MSPs especially) face exponentially higher risks from supply chain compromises through tools like TrustConnect
Related Articles
- Notepad++ Server Hijacking: Inside the Six-Month Supply Chain Attack [2025]
- Microsoft's Copilot AI Email Bug: What Happened and Why It Matters [2025]
- NordVPN & CrowdStrike Partnership: Enterprise Security for Everyone [2025]
- Windows 11 Notepad Security Flaw: What You Need to Know [2025]
- dYdX Supply Chain Attack: How Malicious NPM Packages Emptied Wallets [2025]
- OpenClaw AI Assistant Security Threats: How Hackers Exploit Skills to Steal Data [2025]
![Fake Enterprise Software Hiding RATs: A Deep Dive Into TrustConnect [2025]](https://tryrunable.com/blog/fake-enterprise-software-hiding-rats-a-deep-dive-into-trustc/image-1-1771590947911.jpg)



