Google's $1.5 Million Bounty for Security Bugs in Android and Chrome [2025]
Last month, Google announced a significant increase in its bug bounty program, offering up to $1.5 million for identifying critical vulnerabilities in Android and Chrome. This move highlights Google's commitment to enhancing security and its reliance on the global research community. Let's dive into the details of Google's initiative, explore the technical landscape of security research, and understand what this means for developers and users alike.
TL; DR
- Increased Bounties: Google now offers up to $1.5 million for critical Android and Chrome bugs, as reported by SecurityWeek.
- Focus on Hard-to-Detect Bugs: The program prioritizes vulnerabilities that AI can't easily find, according to Dark Reading.
- Collaboration with Researchers: Google values contributions from independent security experts, as noted by Help Net Security.
- Best Practices for Researchers: Tips on effectively identifying and reporting vulnerabilities are outlined by New America.
- Future Trends: The evolution of security research and potential new threats are discussed by Comcast.

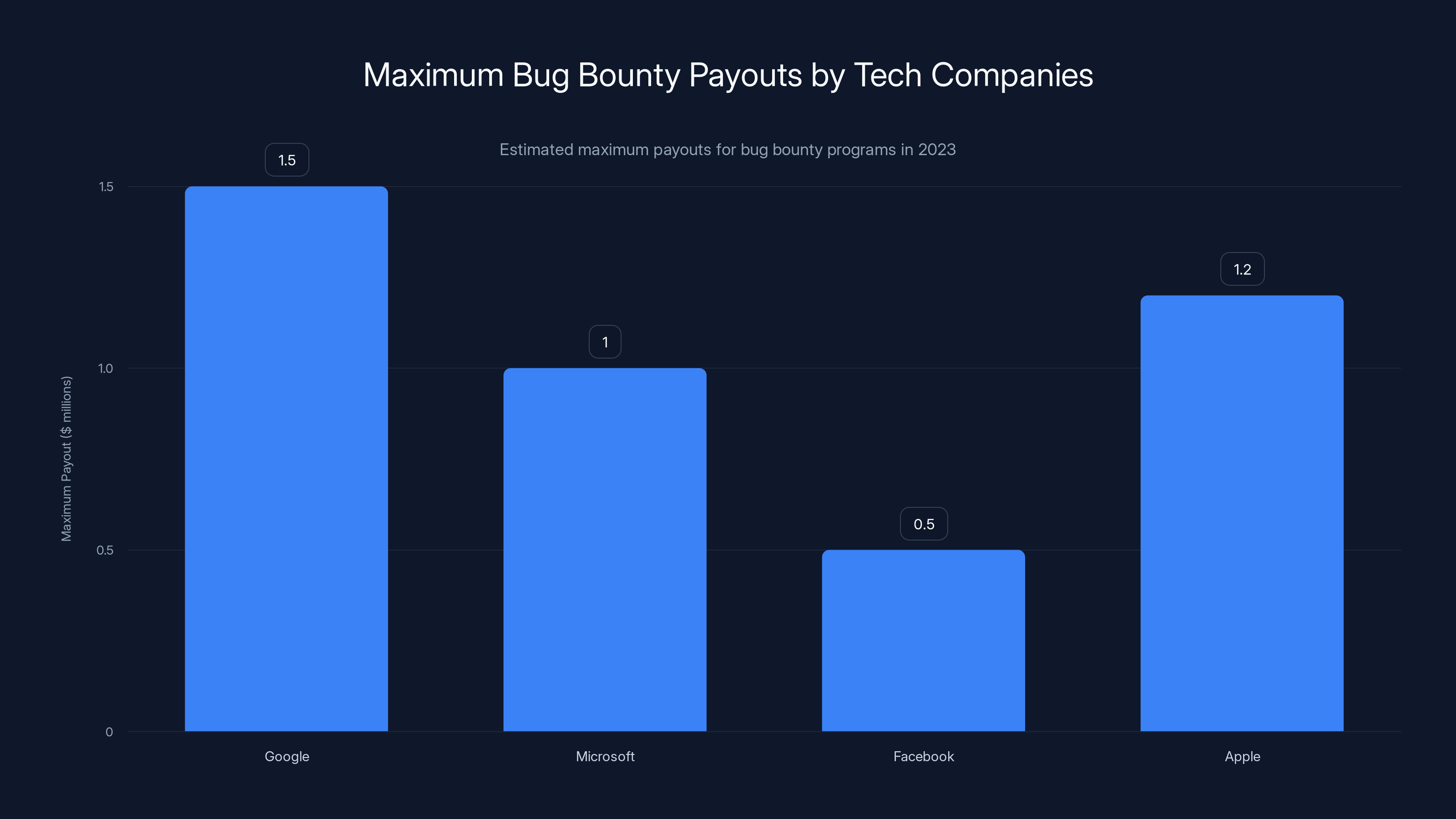
Google offers the highest maximum bug bounty payout at $1.5 million, highlighting its strong commitment to cybersecurity. (Estimated data)
The Importance of Bug Bounty Programs
Bug bounty programs have become a cornerstone of cybersecurity strategies for large tech companies. By incentivizing independent researchers to find and report vulnerabilities, companies like Google can proactively address security issues before they are exploited by malicious actors.
Why Bug Bounties Matter
The primary goal of a bug bounty program is to identify vulnerabilities that might be overlooked by internal security teams. These programs provide a structured way for external researchers to safely disclose security issues, ensuring that companies can patch vulnerabilities promptly.
Google's Commitment to Security
Google's decision to increase its maximum bounty to $1.5 million underscores its dedication to maintaining robust security standards. This move not only attracts top talent from the security research community but also serves as a warning to potential cybercriminals that Google is actively investing in its defenses, as highlighted by SecurityWeek.
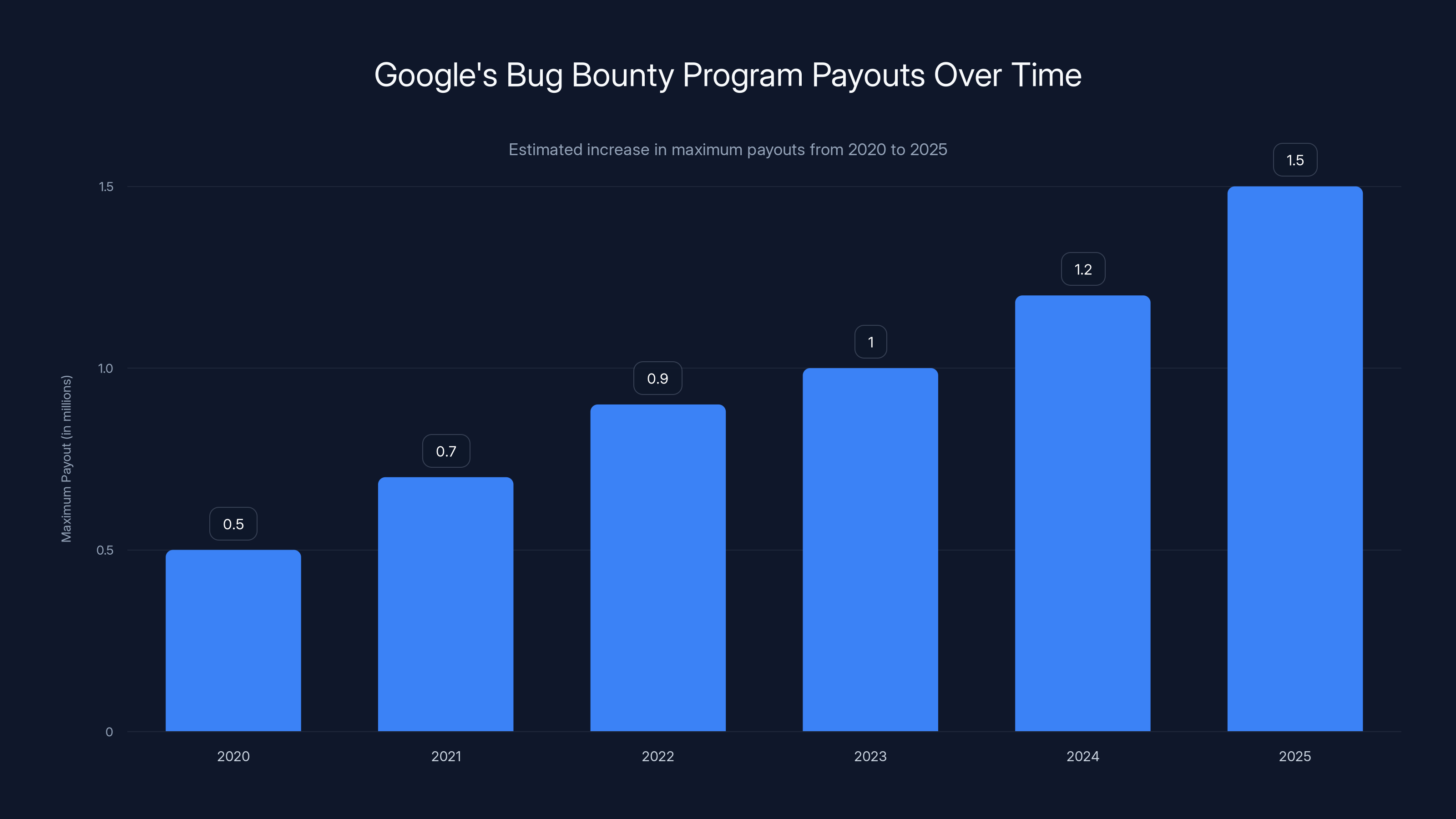
Google's bug bounty program has seen a steady increase in maximum payouts, reaching $1.5 million in 2025. Estimated data based on program trends.
Understanding the Technical Landscape
Before diving into the specifics of Google's bounty program, it's essential to understand the types of vulnerabilities that researchers focus on.
Common Vulnerability Types
- Remote Code Execution (RCE): Allows attackers to execute arbitrary code on a remote system, as detailed in a Wiz blog post.
- Privilege Escalation: Enables attackers to gain elevated access to resources that are normally protected from an application or user.
- Cross-Site Scripting (XSS): Affects web applications by injecting malicious scripts into content from otherwise trusted websites, as discussed by Aikido.
- SQL Injection: Involves inserting malicious SQL queries via input fields, affecting databases.
- Zero-Day Vulnerabilities: Unknown vulnerabilities that are exploited before the vendor becomes aware and patches them, as seen in a SecurityWeek report.
Tools and Techniques for Bug Hunting
Security researchers employ a variety of tools and techniques to discover vulnerabilities. These include:
- Static Analysis: Examining code without executing it to find potential vulnerabilities.
- Dynamic Analysis: Running applications in real-time to identify flaws as they occur.
- Fuzz Testing: Providing invalid, unexpected, or random data to the inputs of a program to find bugs.
How Google's Bounty Program Works
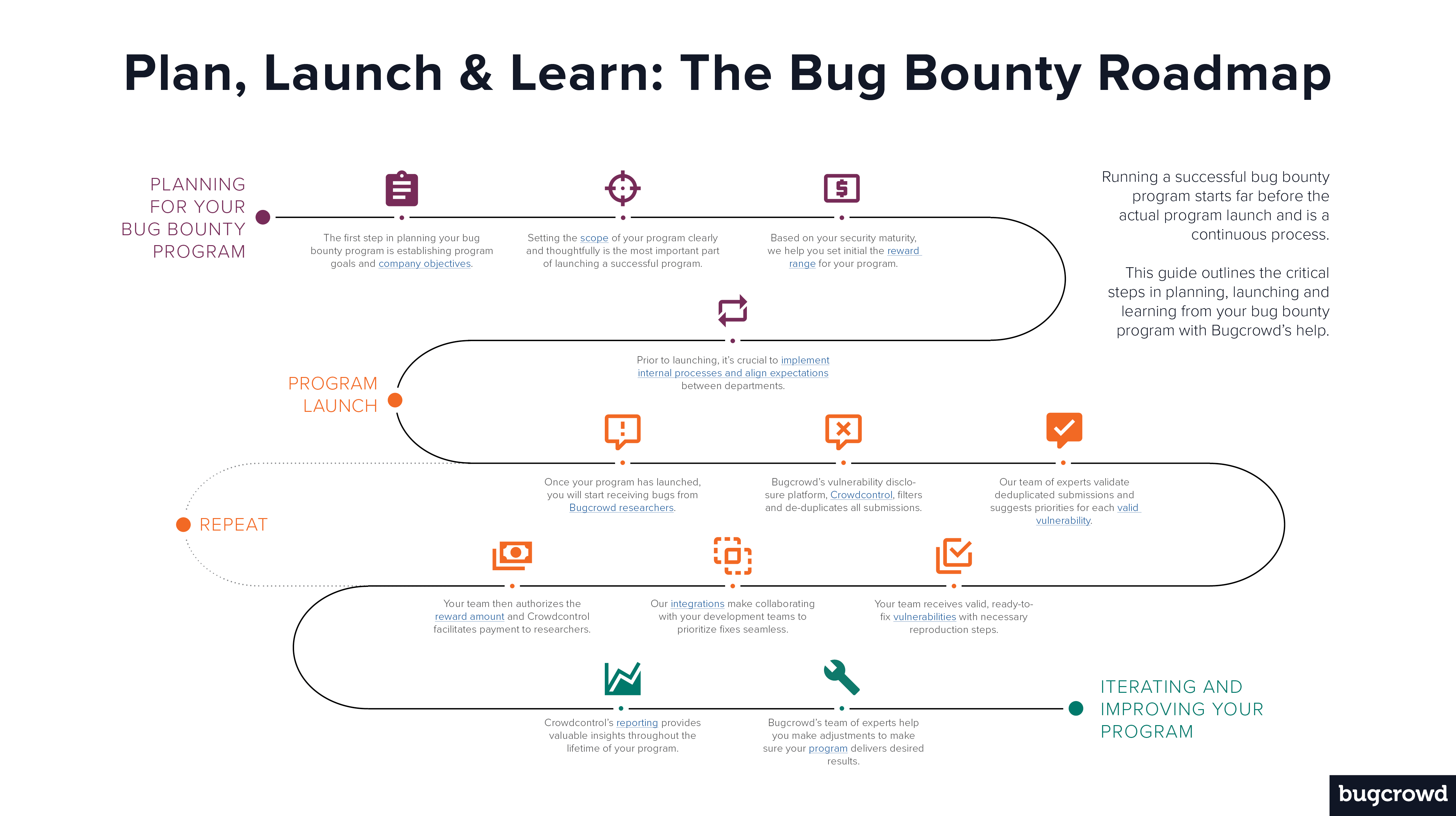
Google's bug bounty program is designed to encourage the discovery and responsible disclosure of security vulnerabilities. Here's how it operates:
Submission Process
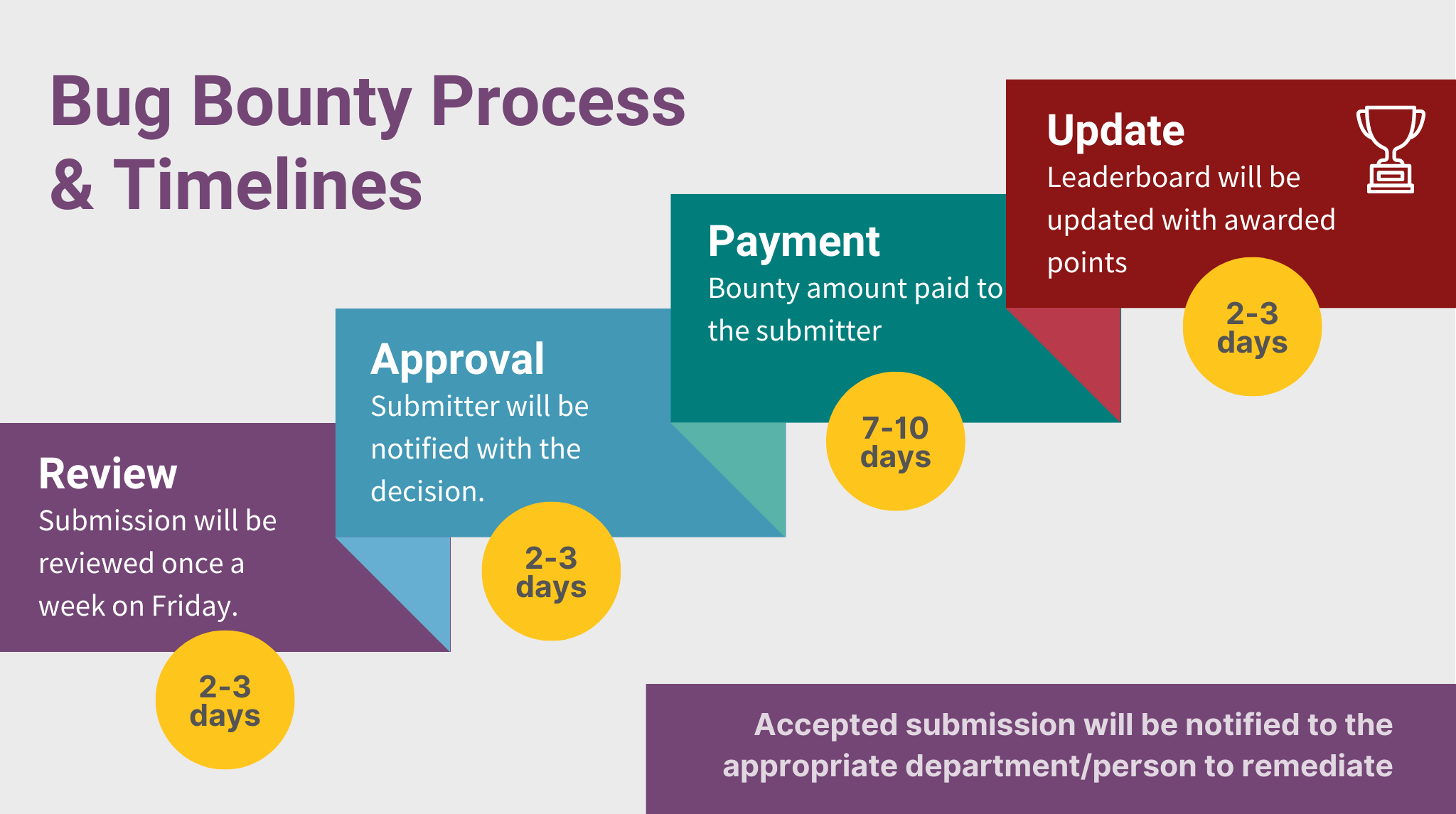
Researchers who identify a potential vulnerability in Android or Chrome can submit their findings through Google's dedicated platform. The submission should include detailed information about the vulnerability, steps to reproduce it, and any potential impact.
Evaluation and Reward
Once submitted, Google's security team evaluates the report. Factors like the severity of the vulnerability, potential impact, and the quality of the submission affect the reward amount. The top-tier rewards are reserved for vulnerabilities that can lead to significant security breaches.
Payment and Recognition
Eligible reports are rewarded with a monetary prize, and researchers are often recognized in Google's official security bulletins. This recognition can be an invaluable addition to a researcher's professional portfolio.
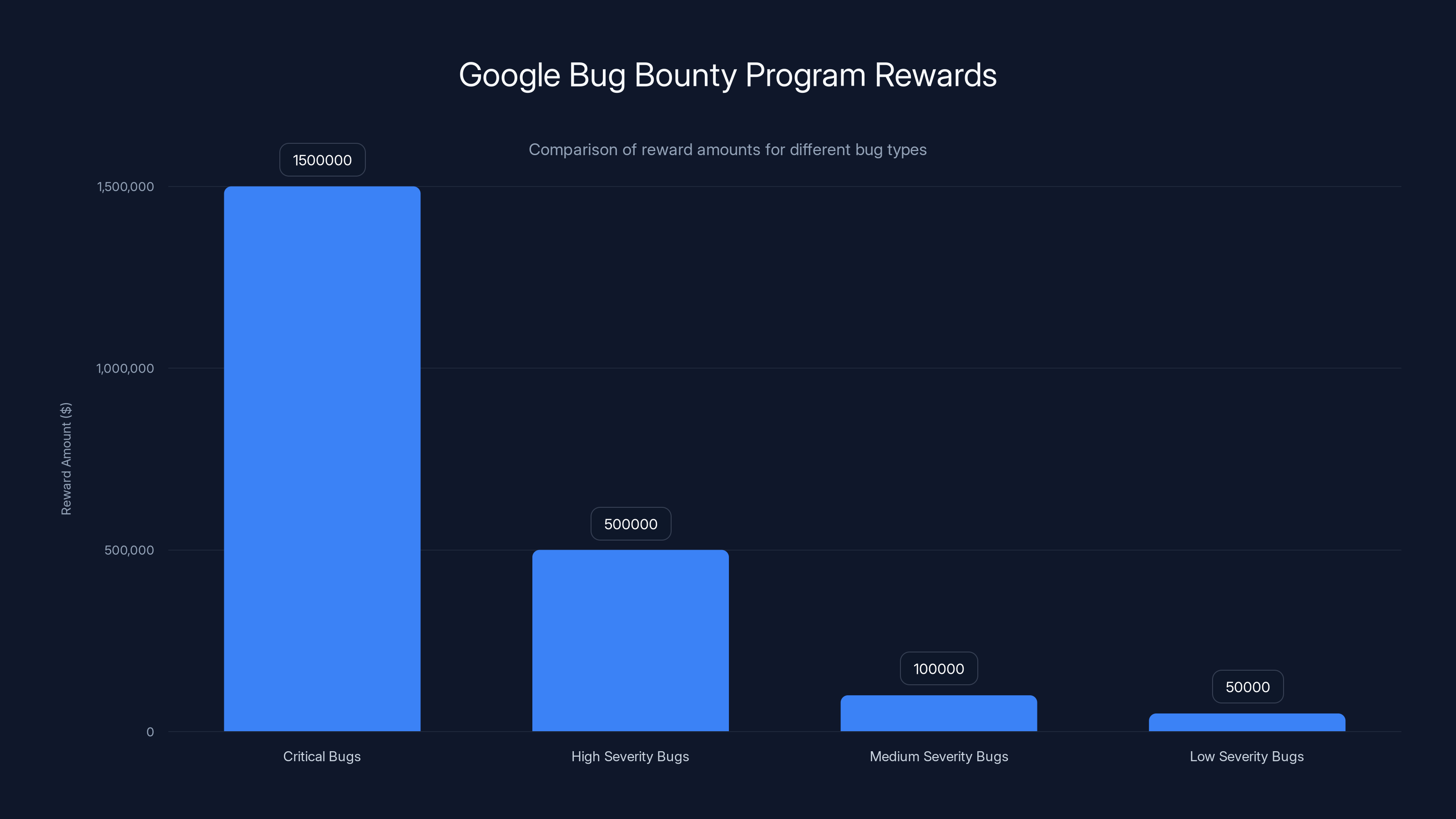
Google offers up to $1.5 million for critical Android and Chrome bugs, with lower rewards for less severe vulnerabilities. Estimated data for lower severity bugs.
Best Practices for Security Researchers
Security researchers aiming to participate in Google's bug bounty program should adhere to best practices to maximize their chances of success.
Stay Updated
Keeping abreast of the latest security trends, patches, and updates is crucial. This knowledge helps researchers identify potential vulnerabilities in the most current versions of Android and Chrome, as emphasized by ComputerWeekly.
Comprehensive Testing
Thorough testing across different device configurations and software versions can reveal hidden vulnerabilities. Researchers should employ both automated tools and manual techniques to ensure comprehensive coverage.
Clear Documentation
Providing clear, detailed documentation of the vulnerability is essential. This includes reproduction steps, potential impacts, and any suggestions for mitigation.

Common Pitfalls and Solutions
Even experienced researchers can encounter pitfalls when participating in bug bounty programs. Here are some common issues and solutions:
Overlooking Updates
Pitfall: Missing vulnerabilities due to outdated software versions. Solution: Regularly check for updates and test on the latest software versions.
Incomplete Submissions
Pitfall: Submitting reports with insufficient detail. Solution: Include comprehensive details and follow Google's submission guidelines rigorously.
Misjudging Severity
Pitfall: Misjudging the potential impact of a vulnerability. Solution: Assess the vulnerability's impact from various angles and consider consulting with peers for a second opinion.
Future Trends and Recommendations
As technology evolves, so do the threats and challenges in cybersecurity. Here are some anticipated trends and recommendations for researchers:
The Rise of AI in Security
AI is increasingly being used to identify and mitigate security threats. While AI can automate many tasks, it still requires expert oversight to address complex vulnerabilities effectively, as noted by Dark Reading.
Emphasis on Mobile Security
With the growing reliance on mobile devices, security research in this domain is more critical than ever. Researchers should focus on mobile-specific vulnerabilities and cross-platform threats.
Collaborative Defense
Collaboration between the tech industry, academia, and independent researchers will be vital in addressing future security challenges. Sharing knowledge and resources can lead to more effective solutions, as highlighted by New America.

Conclusion
Google's enhanced bug bounty program represents a significant investment in cybersecurity. By offering up to $1.5 million for critical vulnerabilities, Google not only protects its users but also fosters a collaborative environment for the global security research community.
The program's success depends on the expertise and diligence of security researchers worldwide. As technology continues to advance, these collaborations will be essential in safeguarding digital ecosystems.

FAQ
What is a bug bounty program?
A bug bounty program is an initiative by companies to incentivize individuals to find and report security vulnerabilities in their software or systems.
How does Google's bug bounty program work?
Google's program encourages researchers to find vulnerabilities in Android and Chrome, offering monetary rewards based on the severity and impact of the findings.
What types of vulnerabilities are prioritized?
Google prioritizes hard-to-detect vulnerabilities, such as those that AI cannot easily identify, and those that could lead to significant security breaches.
How can researchers participate in the program?
Researchers can participate by identifying vulnerabilities and submitting detailed reports through Google's official platform.
What are the rewards for finding vulnerabilities?
Rewards vary based on the severity of the vulnerability, with top-tier rewards reaching up to $1.5 million.
Why is collaboration with researchers important for Google?
Collaboration allows Google to leverage external expertise, identify vulnerabilities more effectively, and improve the security of their products.
Key Takeaways
- Google offers $1.5 million for critical security bugs.
- Program focuses on vulnerabilities not easily detected by AI.
- Collaboration with researchers enhances security measures.
- Researchers must provide detailed documentation of vulnerabilities.
- Future trends include AI in security and mobile threats.
Related Articles
- Unlocking Privacy: Share Your Approximate Location with Chrome on Android [2025]
- Understanding Supply-Chain Attacks: The Daemon Tools Incident and Its Implications [2025]
- Understanding the Vimeo Data Breach and Protecting Your Digital Footprint [2025]
- Scaling AI into Production: The New Frontier in Enterprise Infrastructure [2025]
- Robots on the Rails: How Automation is Shaping Public Transport [2025]
- Understanding the Impact of DDoS Attacks on Ubuntu Services [2025]
![Google's $1.5 Million Bounty for Security Bugs in Android and Chrome [2025]](https://tryrunable.com/blog/google-s-1-5-million-bounty-for-security-bugs-in-android-and/image-1-1778083594307.jpg)



