Understanding the Vimeo Data Breach and Protecting Your Digital Footprint [2025]
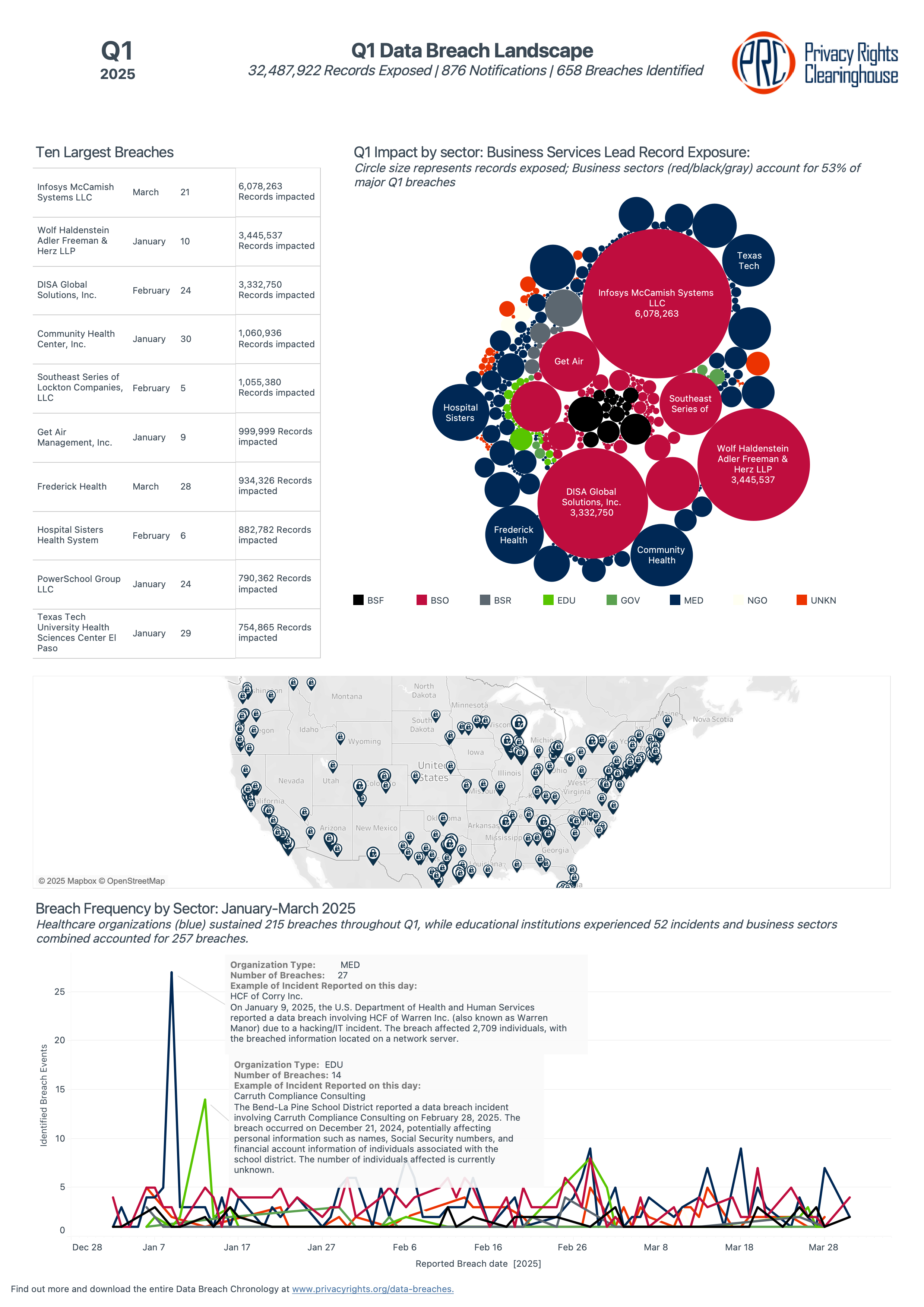
Last year, the Vimeo data breach sent ripples across the digital landscape, affecting approximately 119,000 users. This incident not only exposed sensitive personal information but also served as a wake-up call for individuals and companies alike to reassess their cybersecurity strategies. In this comprehensive guide, we will delve into the specifics of the breach, explore best practices for safeguarding your digital footprint, and discuss future trends in cybersecurity.
TL; DR
- 119,000 users affected: Personal information exposed in the Vimeo breach.
- Shiny Hunters involvement: The notorious group leaked 106GB of data.
- Protective measures: Enhance password security and enable 2FA.
- Risk mitigation: Regularly update software and conduct security audits.
- Future trends: Emphasis on AI-driven cybersecurity solutions.
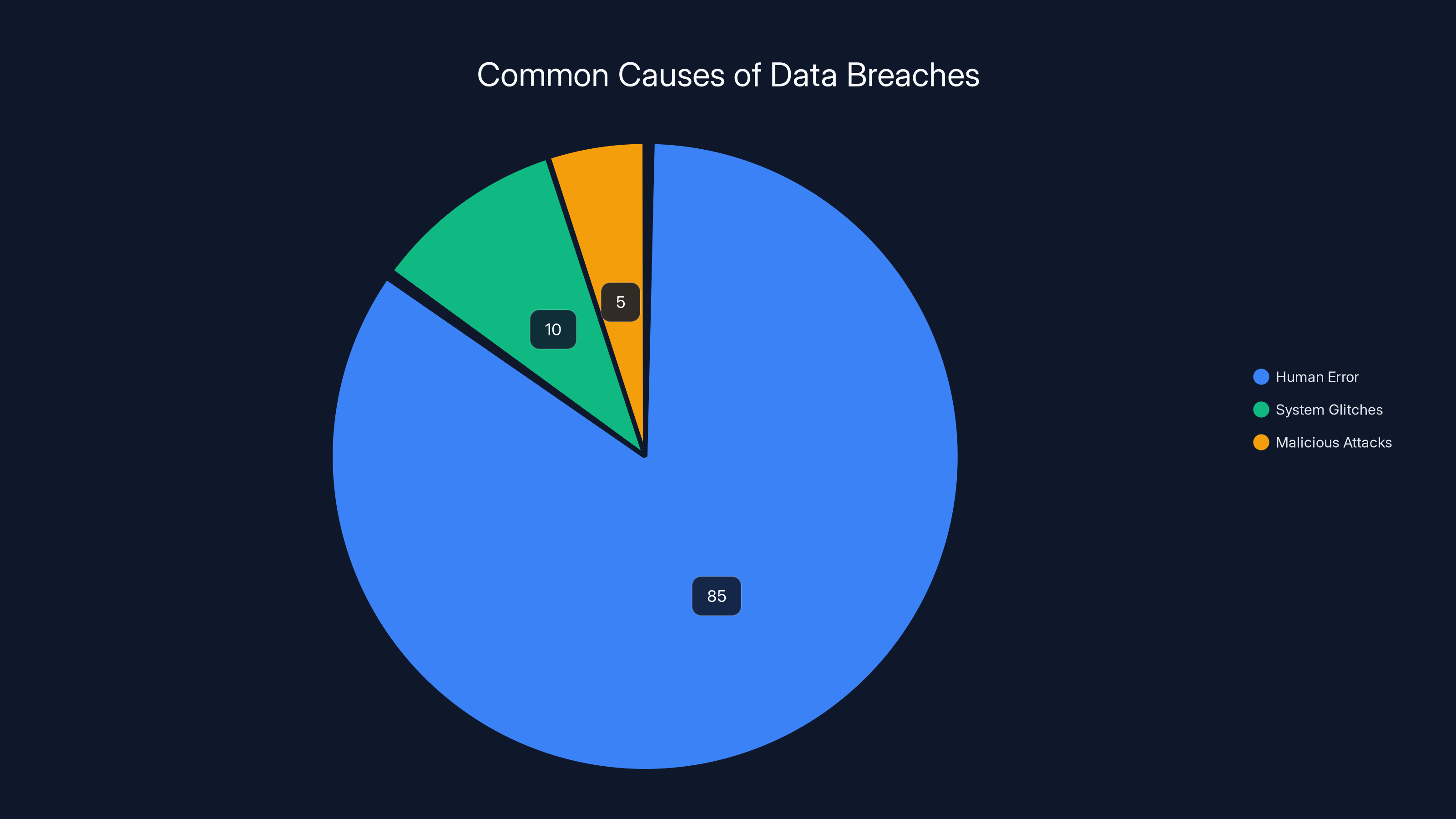
Human error accounts for 85% of data breaches, highlighting the importance of employee training and awareness. (Estimated data)
The Anatomy of the Vimeo Breach
In April 2026, Vimeo, a popular video-sharing platform, experienced a significant data breach. The breach exposed the names and email addresses of around 119,000 users, making them susceptible to phishing attacks and identity theft.
Who is Shiny Hunters?
Shiny Hunters is a well-known hacking group in the cybersecurity community, infamous for orchestrating high-profile data breaches. They have targeted various platforms, leveraging sophisticated techniques to extract valuable data. According to Techzine, Shiny Hunters often leaks stolen data online when ransom negotiations fail.
Impact of the Breach
The immediate impact of the breach was the exposure of personal information, which could lead to:
- Phishing attacks: Cybercriminals use leaked email addresses to send deceptive messages designed to steal additional personal information, as noted by the National Cyber Security Alliance.
- Identity theft: With access to names and emails, malicious actors can impersonate individuals to commit fraud.
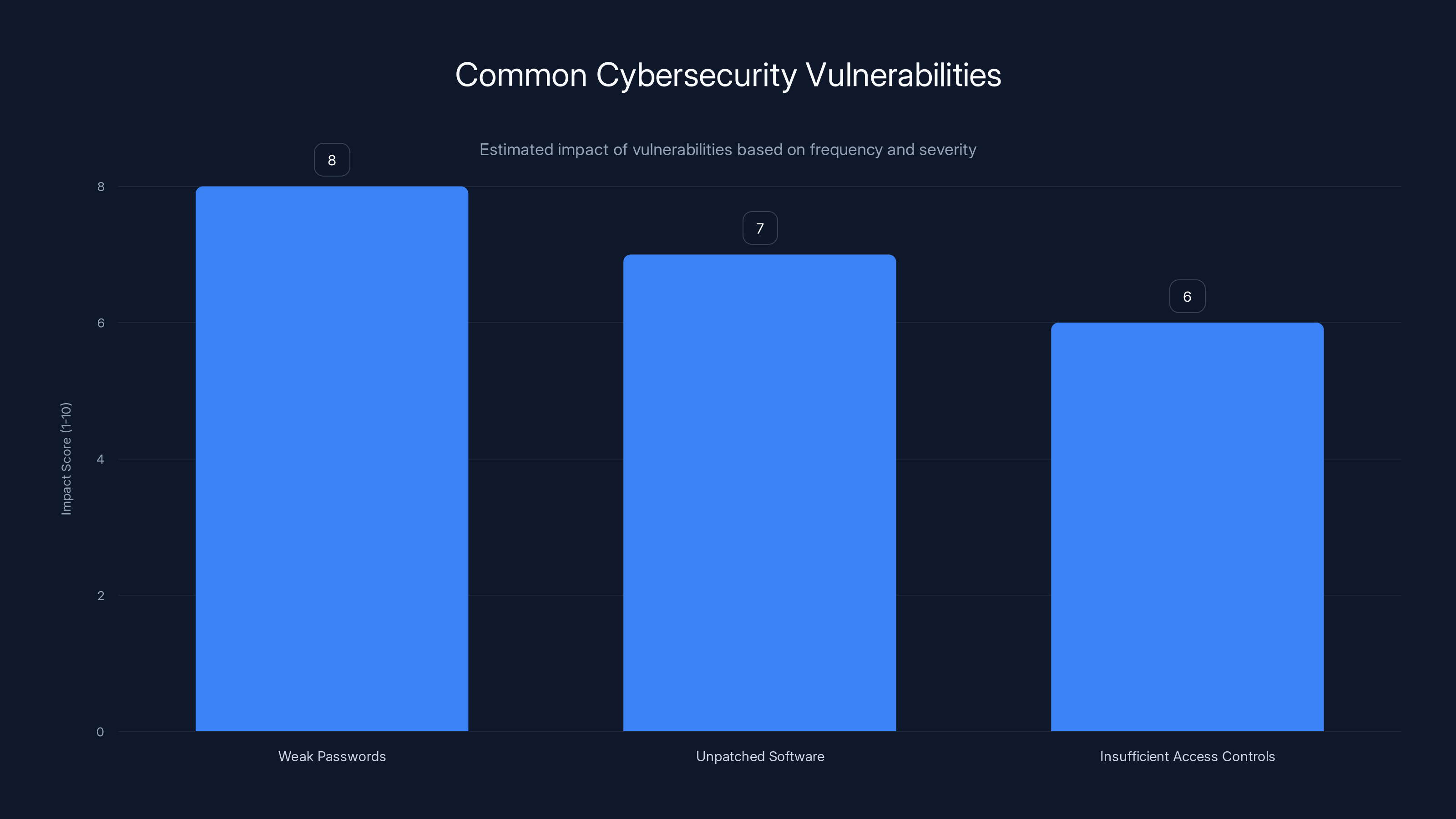
Weak passwords are the most impactful vulnerability, scoring 8 out of 10 in terms of frequency and severity. Estimated data.
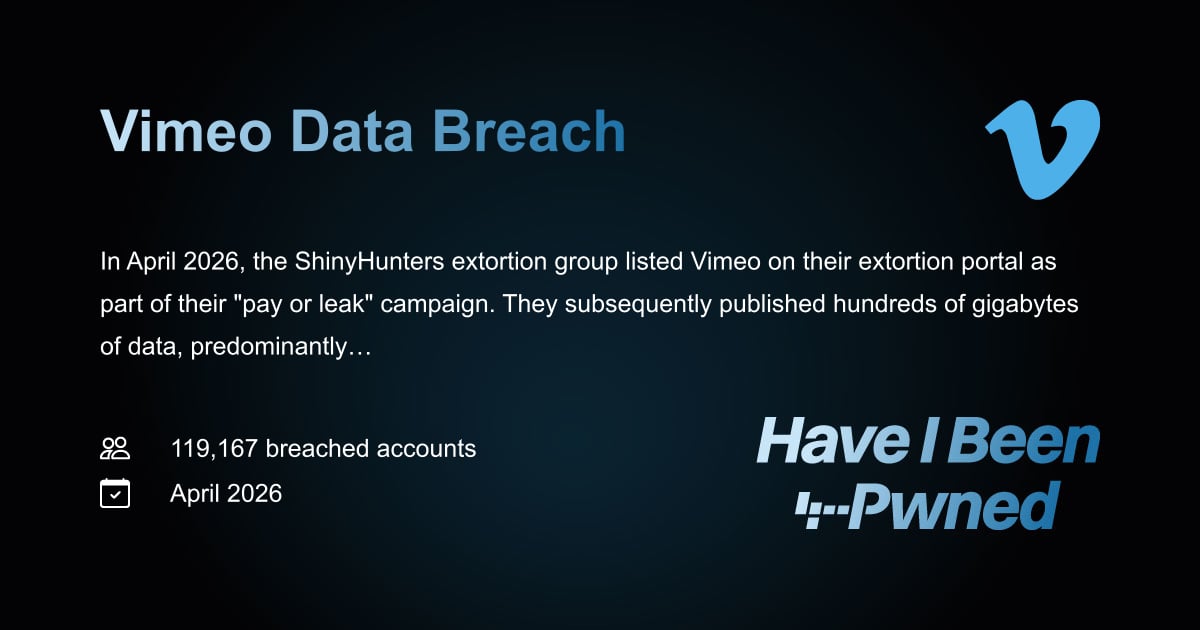
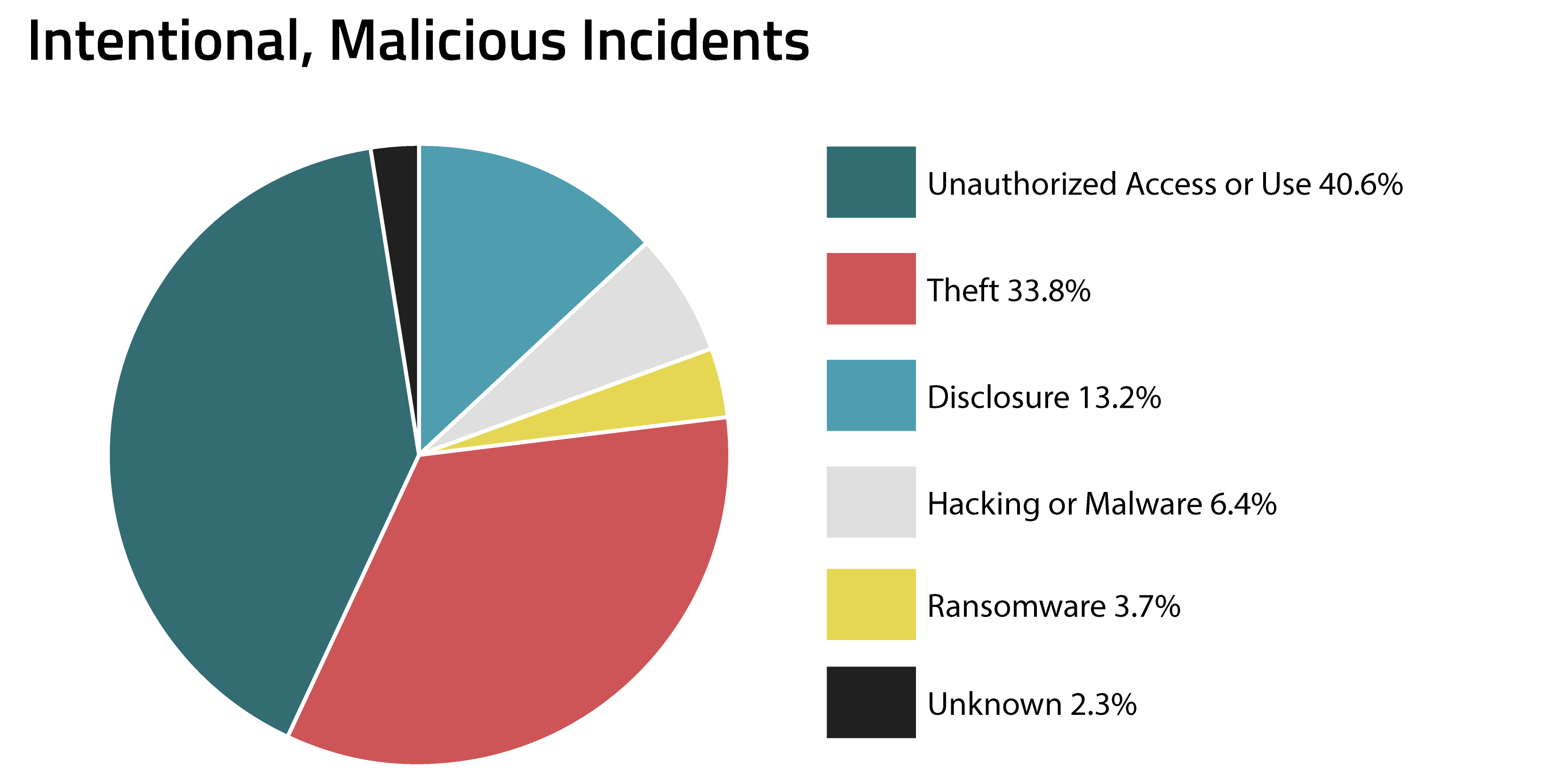
How the Breach Occurred
Vimeo's breach was a result of inadequate security measures that allowed Shiny Hunters to infiltrate their systems. Understanding the technical underpinnings of such breaches is crucial for prevention.
Common Vulnerabilities Exploited
- Weak Passwords: Easily guessable passwords can be cracked using brute force attacks, as highlighted by HIPAA Journal.
- Unpatched Software: Failing to update software can leave systems vulnerable to known exploits.
- Insufficient Access Controls: Poorly managed permissions can grant attackers unnecessary access.
Preventive Measures
To protect against similar breaches, organizations should:
- Implement strong password policies: Encourage the use of complex passwords and regular updates.
- Regular software updates: Ensure all systems are up to date with the latest security patches.
- Access management: Regularly review and restrict user access to sensitive data.
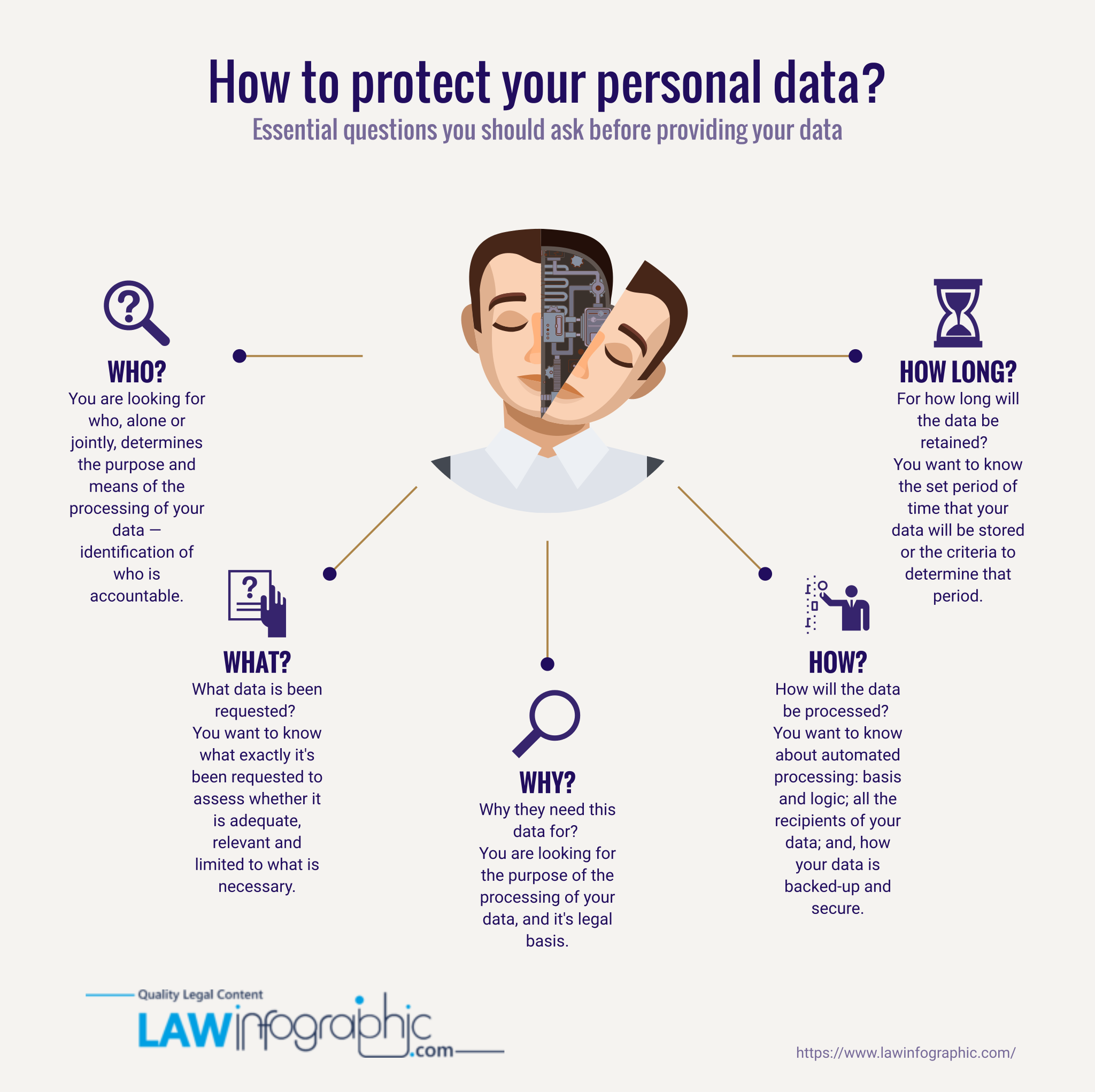
Personal Data Protection Best Practices
In the wake of the Vimeo breach, individuals must take proactive steps to safeguard their personal information.
Enhancing Password Security
- Use a password manager: Tools like LastPass or 1Password can generate and store complex passwords.
- Enable two-factor authentication (2FA): Adds an extra layer of security by requiring a second form of verification.
Monitoring Digital Footprint
Regularly check for unauthorized activity by:
- Monitoring credit reports: Services like Credit Karma provide free credit monitoring.
- Checking email breach notifications: Websites like Have I Been Pwned alert users if their email appears in a data breach.

Two-factor authentication and password managers are highly effective in protecting personal data. Estimated data based on security expert recommendations.
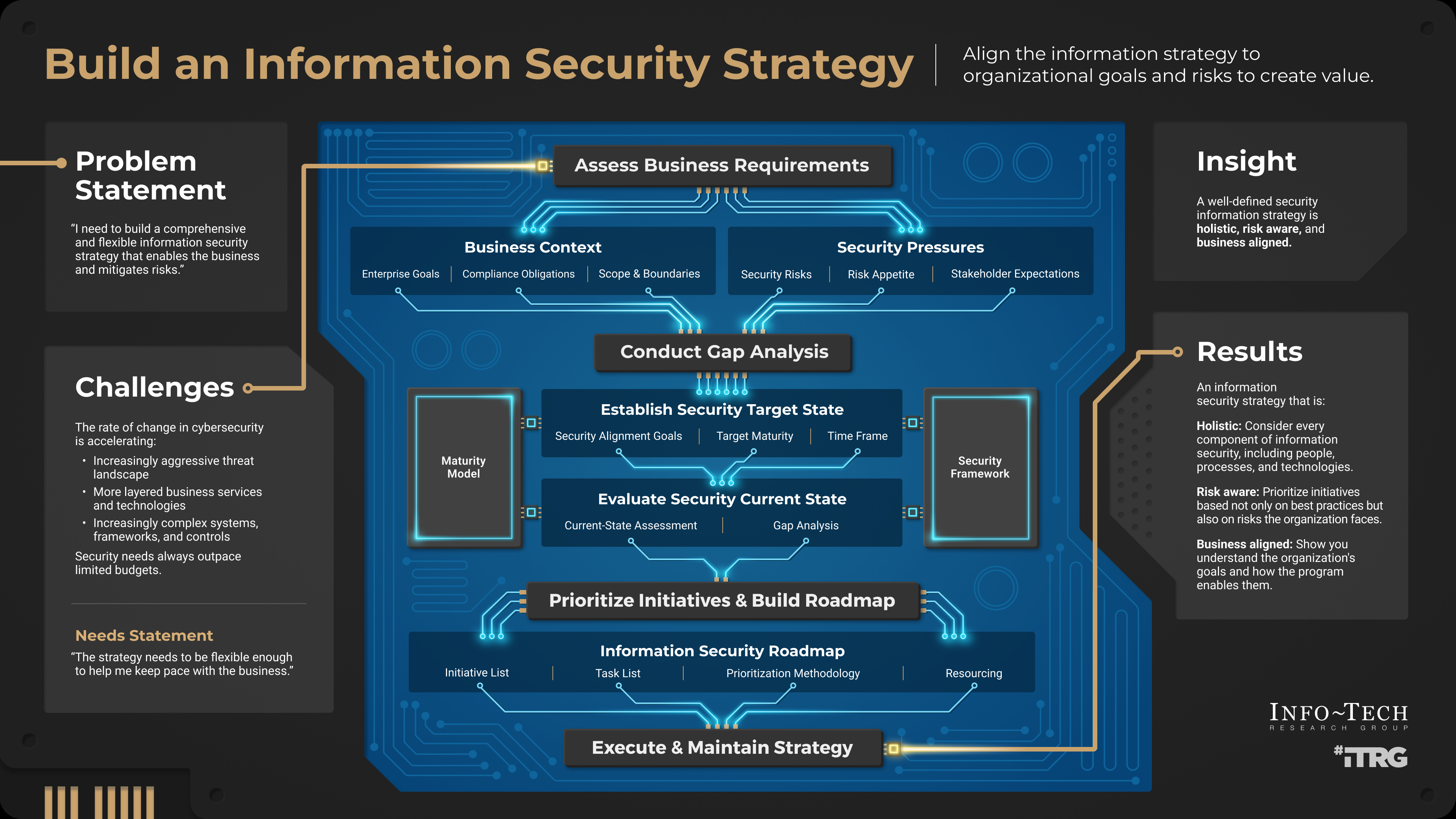
Organizational Cybersecurity Strategies
Organizations can learn from the Vimeo breach by strengthening their cybersecurity frameworks.
Conducting Security Audits
Regular audits help identify vulnerabilities before they can be exploited. Key components include:
- Penetration testing: Simulate attacks to test defenses.
- Vulnerability assessments: Systematic reviews of security weaknesses.
Employee Training and Awareness
Human error is a significant factor in data breaches. Educating employees on recognizing phishing attempts and securing sensitive data is essential. According to The Inquirer, small businesses are particularly vulnerable to cybercrime due to lack of training.
Implementing Multi-Layered Security
Utilizing a multi-layered security approach can provide comprehensive protection. This includes:
- Firewalls: Monitor and control network traffic.
- Intrusion detection systems (IDS): Identify potential security breaches in real-time.
- Encryption: Protect sensitive data by converting it into unreadable code.
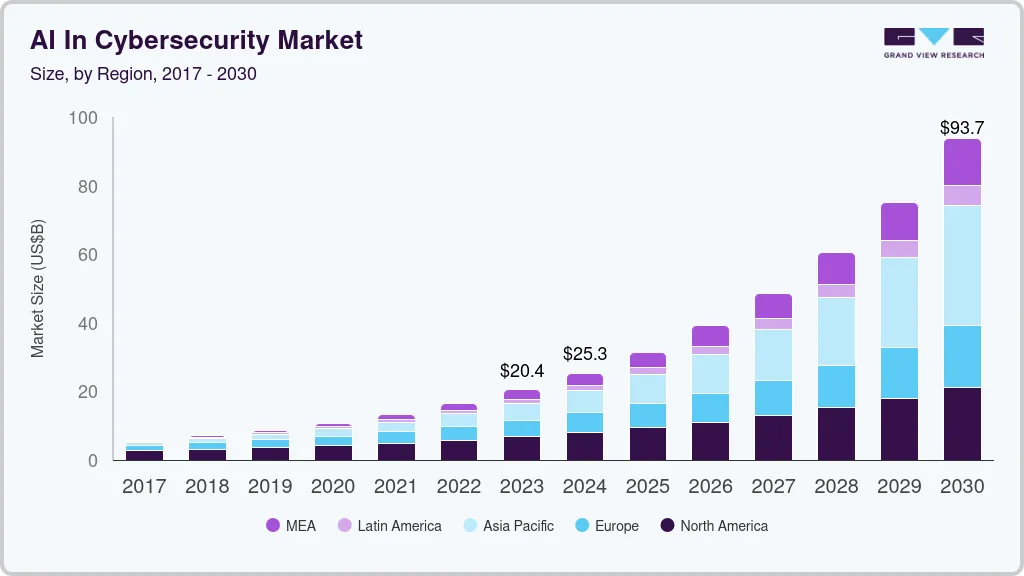
Future Trends in Cybersecurity
As cyber threats evolve, so too must our defense strategies. Here are some emerging trends:
AI-Driven Security Solutions
Artificial Intelligence (AI) is increasingly being used to detect and respond to threats in real-time. AI can analyze vast amounts of data to identify anomalies indicative of a breach. Oracle's blog highlights how AI is enhancing database security.
Zero Trust Architecture
Zero Trust assumes that threats can come from within the network as well as outside. This approach requires:
- Continuous verification: Always verify access requests.
- Least privilege access: Grant users the minimum level of access necessary.
Practical Implementation Guides
For organizations looking to bolster their cybersecurity posture, here are some practical steps:
Setting Up a Zero Trust Network
- Identify sensitive data and assets: Determine what needs the most protection.
- Segment networks: Divide the network into smaller, manageable segments.
- Enforce strict access controls: Use identity and access management (IAM) tools to control who accesses what.
Deploying AI-Based Threat Detection
- Integrate AI with existing systems: Ensure compatibility with current infrastructure.
- Train AI models: Use historical data to refine the accuracy of threat detection.
- Monitor and adjust: Continuously evaluate AI performance and make necessary adjustments.
Common Pitfalls and Solutions
Even with robust security measures, pitfalls can occur. Here are some common issues and how to address them:
Overreliance on Technology
Problem: Dependence on automated systems can lead to complacency.
Solution: Regularly review and update security protocols to adapt to new threats.
Lack of Incident Response Plan
Problem: Delayed response to a breach can exacerbate damage.
Solution: Develop a detailed incident response plan and conduct regular drills.

Conclusion
The Vimeo data breach serves as a stark reminder of the importance of cybersecurity. By understanding the factors that led to the breach and implementing robust security measures, both individuals and organizations can better protect their digital assets. As technology continues to evolve, staying informed and proactive is essential to safeguarding our digital lives.
FAQ
What happened in the Vimeo data breach?
The breach exposed the names and email addresses of approximately 119,000 users, making them vulnerable to phishing attacks and identity theft.
Who is behind the Vimeo data breach?
The notorious hacking group Shiny Hunters orchestrated the breach, known for their high-profile attacks on various platforms.
How can individuals protect themselves from data breaches?
By using strong passwords, enabling two-factor authentication, and regularly monitoring their digital footprint.
What are some cybersecurity best practices for organizations?
Conducting regular security audits, implementing multi-layered security, and training employees to recognize threats.
How does AI contribute to cybersecurity?
AI helps detect and respond to threats in real-time by analyzing large data sets for anomalies.
What is Zero Trust Architecture?
A security model that assumes threats can come from inside the network, requiring continuous verification and least privilege access.

Key Takeaways
- 119,000 users' data exposed in Vimeo breach, highlighting cybersecurity risks.
- ShinyHunters, a notorious hacking group, leaked 106GB of data when ransom negotiations failed.
- Enhance password security and enable two-factor authentication to protect personal information.
- Organizations should conduct regular security audits and train employees to recognize threats.
- AI-driven security solutions are crucial for real-time threat detection and response.
Related Articles
- Understanding Supply-Chain Attacks: The Daemon Tools Incident and Its Implications [2025]
- How Canada Uses Canary Traps for Election Security: An In-Depth Analysis [2025]
- Ultimate Guide to Using a $2 VPN for Enhanced Security on All Devices [2025]
- Robots on the Rails: How Automation is Shaping Public Transport [2025]
- Understanding the Impact of DDoS Attacks on Ubuntu Services [2025]
- Murena /e/OS Tablet Review: Privacy for a Price [2025]
![Understanding the Vimeo Data Breach and Protecting Your Digital Footprint [2025]](https://tryrunable.com/blog/understanding-the-vimeo-data-breach-and-protecting-your-digi/image-1-1778074539272.jpg)



