Understanding Supply-Chain Attacks: The Daemon Tools Incident and Its Implications [2025]
Introduction
Last year, the cybersecurity world was rocked by the news of a supply-chain attack involving Daemon Tools, a popular disk imaging software. This incident highlighted the vulnerabilities present in software supply chains and the potential risks they pose to users worldwide. In this article, we'll delve into the details of what happened, why it matters, and how you can protect your systems from similar threats.
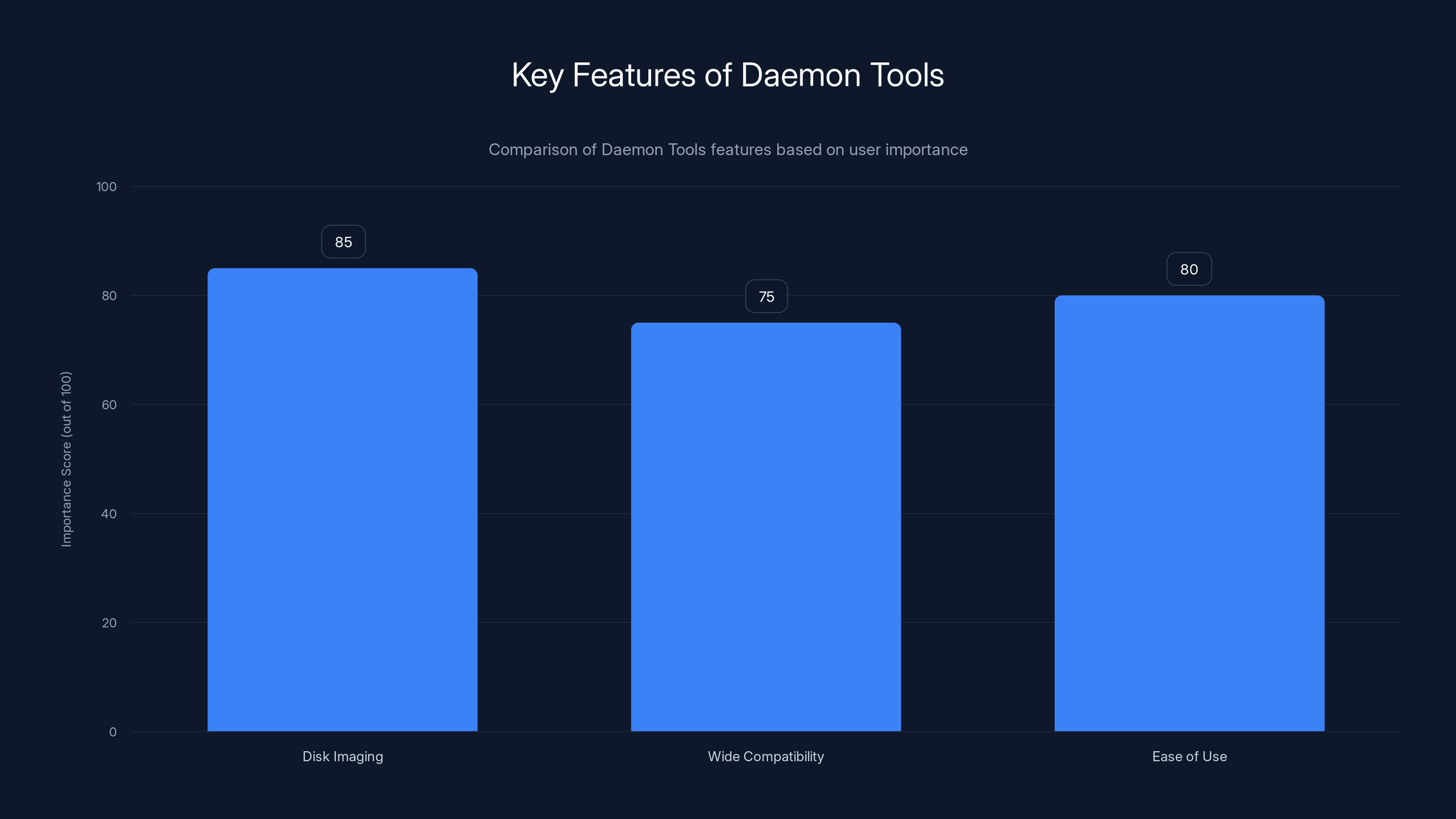
Disk Imaging is the most valued feature of Daemon Tools, followed closely by Ease of Use and Wide Compatibility. (Estimated data)
TL; DR
- Daemon Tools: A popular disk imaging app was compromised in a supply-chain attack.
- Backdoored Versions: Affected versions were 12.5.0.2421 to 12.5.0.2434.
- Wide Impact: Users received malicious updates directly from the developer's servers.
- Supply-Chain Vulnerability: Highlights the risks in software distribution channels.
- Future Focus: Emphasizes the need for enhanced security measures and vigilance.

Estimated data shows a significant number of users affected across different versions, highlighting the widespread impact of the supply-chain attack.
What Happened with Daemon Tools?
In April last year, a stealthy operation began targeting Daemon Tools users. The attackers managed to inject malicious code into the software updates distributed from the official servers. This kind of attack, known as a supply-chain attack, exploits the trust users place in legitimate software updates.
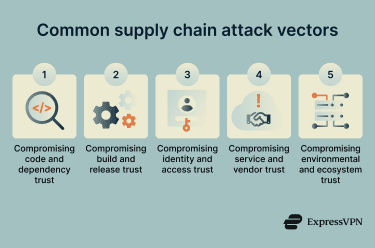
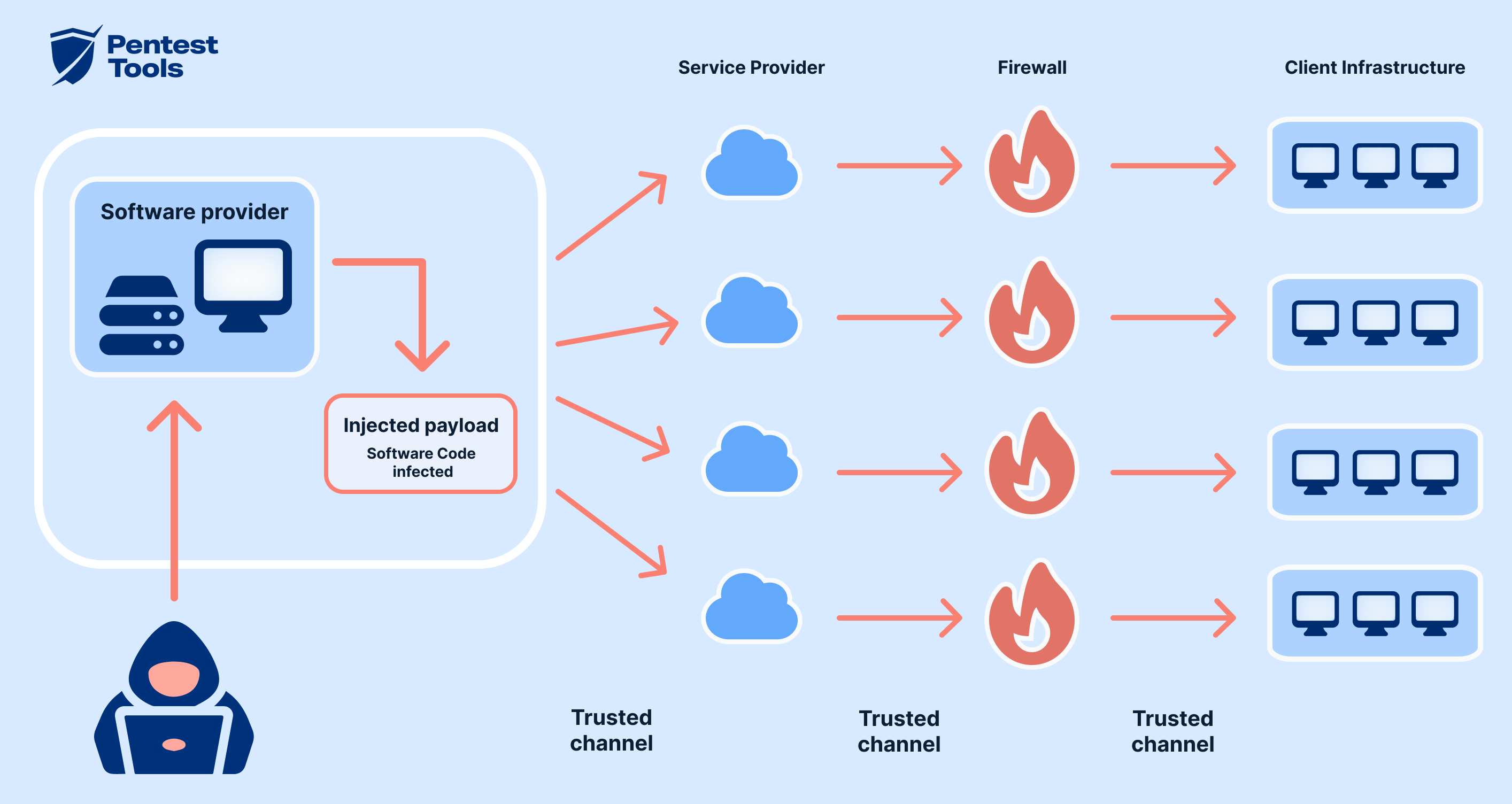
Understanding Supply-Chain Attacks
A supply-chain attack occurs when hackers infiltrate software systems by compromising the processes that deliver software updates or components. By targeting trusted vendors, attackers can distribute malware to a wide audience without detection.
Why Daemon Tools?
Daemon Tools is a widely used application for mounting disk images, making it an attractive target. By compromising this software, attackers could potentially access sensitive data stored on users' computers.
Key Features of Daemon Tools:
- Disk Imaging: Allows users to create and mount ISO images.
- Wide Compatibility: Supports various file formats and operating systems.
- Ease of Use: Simple interface for managing virtual drives.
Technical Breakdown of the Attack
The Daemon Tools incident involved injecting malicious code into the executables distributed as part of software updates. Here's how the attack unfolded:
- Initial Compromise: Attackers gained access to the developer's update servers.
- Code Injection: Malicious code was inserted into the executable files.
- Distribution: Infected files were distributed as legitimate updates.
- Execution: Once installed, the malware executed at system startup.
Technical Details
The malicious updates were signed with the developer's official digital certificate, making them appear legitimate. This tactic is particularly effective because it bypasses many traditional security measures that rely on verifying the authenticity of software based on its digital signature.

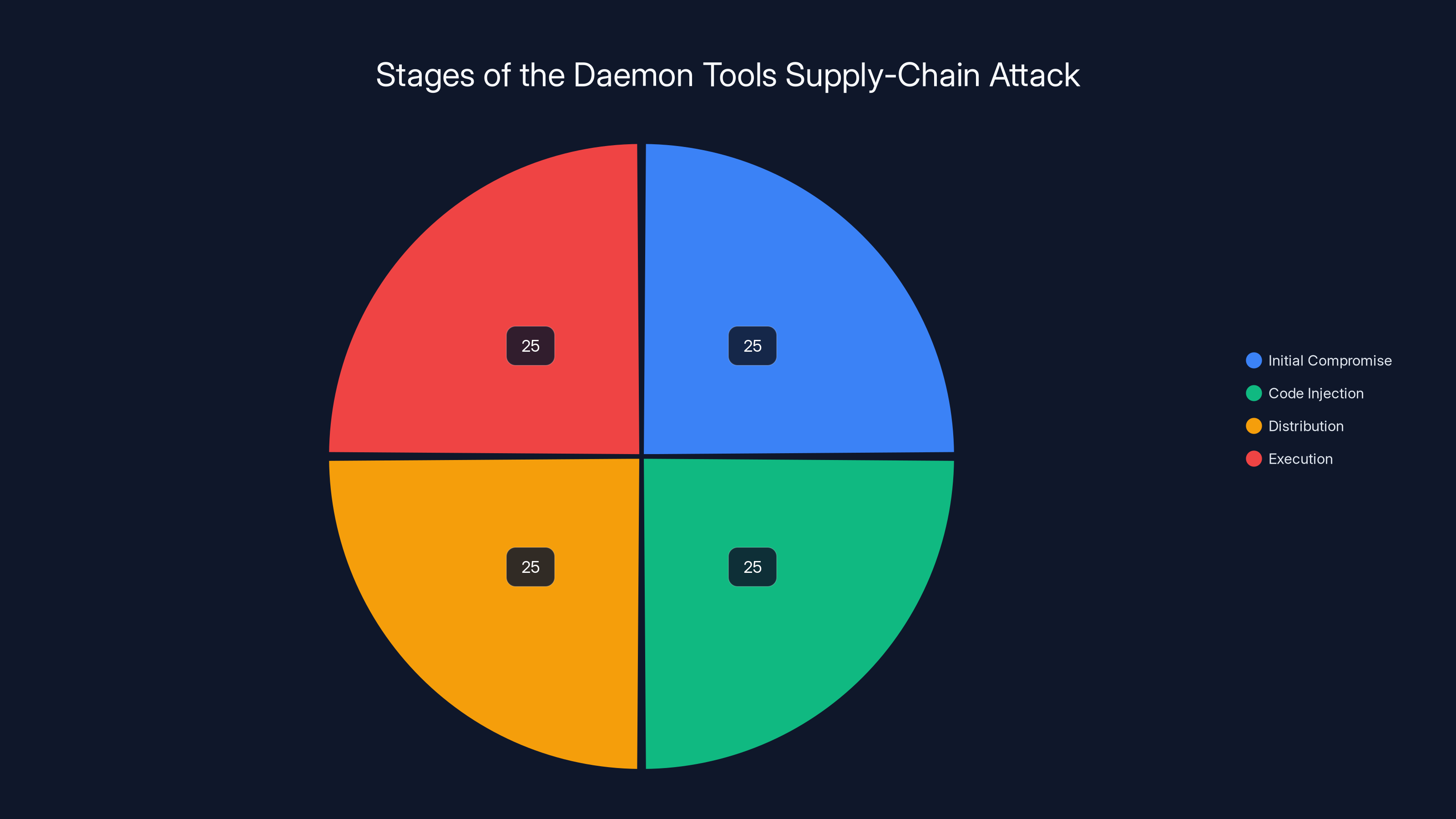
The attack progressed evenly through four main stages: compromise, code injection, distribution, and execution. Estimated data.
Common Pitfalls in Software Security
Supply-chain attacks exploit several common weaknesses in software security practices. Understanding these pitfalls can help in fortifying defenses against future threats.
- Over-Reliance on Digital Signatures: While digital signatures are crucial, they can be compromised if attackers gain access to the signing keys.
- Lack of Code Review: Regular audits and reviews of both source code and compiled binaries are essential.
- Inadequate Monitoring: Continuous monitoring of software distribution channels can detect anomalies early.
Best Practices for Defending Against Supply-Chain Attacks
To mitigate the risk of supply-chain attacks, organizations and developers should adopt the following practices:
- Implement Multi-Factor Authentication (MFA): Protect access to critical systems with MFA.
- Regular Code Audits: Conduct thorough reviews of source code and compiled binaries.
- Secure Software Distribution: Use secure channels and encrypt updates.
- Monitor Software Integrity: Employ tools that verify the integrity of software during distribution.
- Limit Access: Restrict access to critical systems and signing keys to essential personnel only.
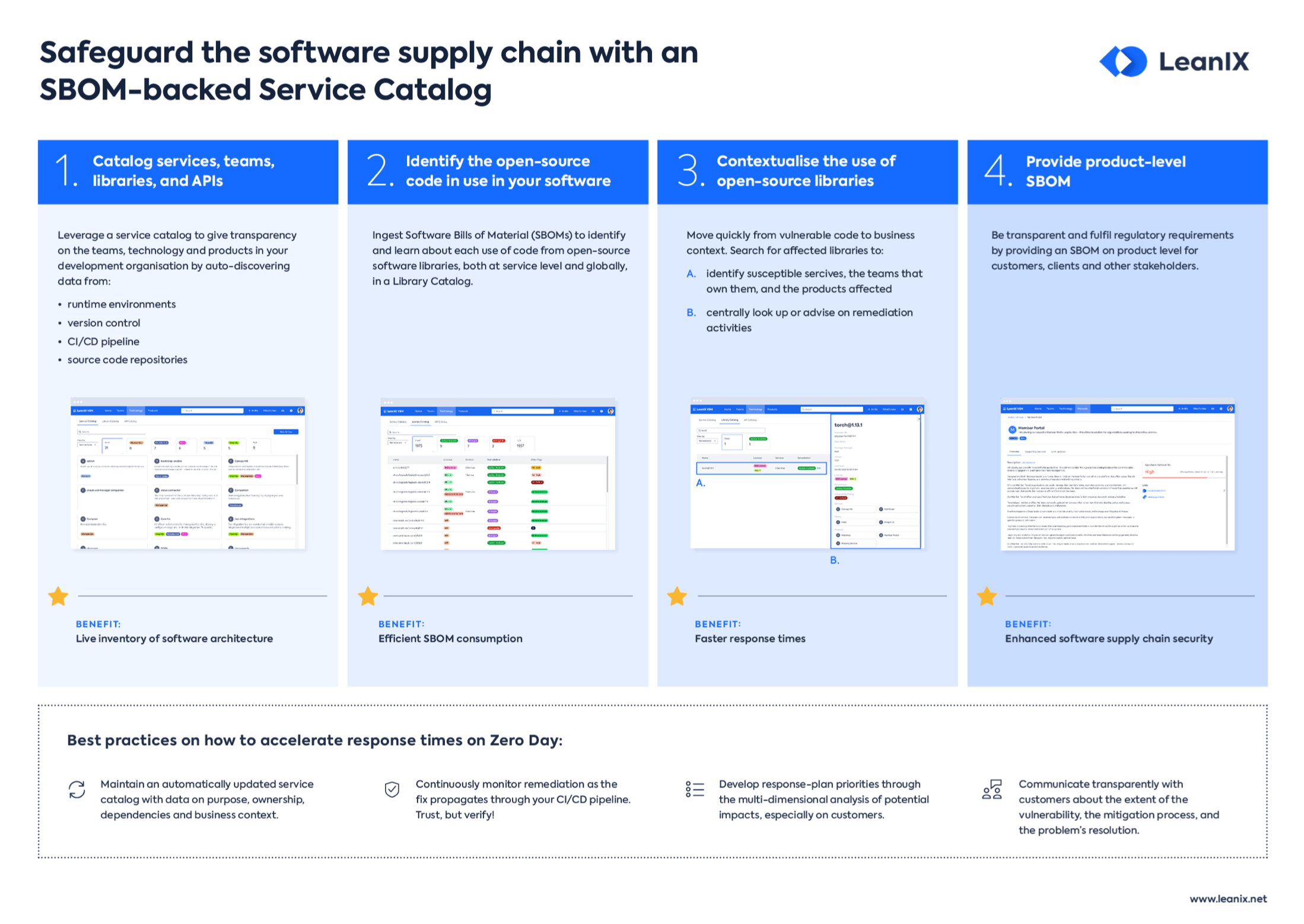
Future Trends in Supply-Chain Security
As the sophistication of cyberattacks continues to evolve, so too must our defense mechanisms. Here are some emerging trends in supply-chain security:
- Increased Automation: AI and machine learning are being deployed to detect anomalies in software distribution.
- Zero Trust Architecture: Adopting a zero trust model reduces reliance on trusted networks and devices.
- Enhanced Collaboration: Industry-wide collaboration on threat intelligence sharing is vital for early detection of threats.

Case Study: Mitigating a Supply-Chain Attack
Consider a hypothetical scenario where a software company successfully mitigated a supply-chain attack using best practices. Here's how:
- Early Detection: Anomaly detection systems flagged unusual behavior in the software distribution process.
- Rapid Response: The security team isolated affected systems and halted further distribution of infected updates.
- Comprehensive Audit: A full audit was conducted to identify the breach's scope and prevent future occurrences.
Conclusion
The Daemon Tools supply-chain attack serves as a stark reminder of the vulnerabilities in our software distribution systems. By understanding the mechanics of such attacks and implementing robust security measures, we can better protect ourselves from future threats. As technology evolves, staying informed and proactive is key to ensuring the safety and integrity of our digital ecosystems.
FAQ
What is a supply-chain attack?
A supply-chain attack involves compromising a trusted vendor's system to distribute malware to end users. Attackers target the software delivery process, injecting malicious code into legitimate updates.
How can I protect my systems from supply-chain attacks?
Implementing best practices such as multi-factor authentication, regular code audits, and secure distribution channels can significantly reduce the risk of supply-chain attacks.
What should I do if I suspect my software has been compromised?
If you suspect a compromise, isolate the affected systems, conduct a thorough audit, and update your security protocols to prevent further breaches.
Why are supply-chain attacks becoming more common?
The growing complexity and interconnectedness of software ecosystems make supply-chain attacks an attractive method for cybercriminals to reach a broad audience.
Can digital signatures prevent supply-chain attacks?
While digital signatures are an important security measure, they are not foolproof. Attackers who gain access to signing keys can still distribute malicious software.
What role does AI play in defending against cyberattacks?
AI and machine learning are increasingly used to detect anomalies and potential threats in software distribution processes, enhancing our ability to prevent and respond to cyberattacks.
Key Takeaways
- Supply-chain attacks exploit trusted software delivery channels.
- Daemon Tools' compromise highlights vulnerabilities in software distribution.
- Implementing MFA and secure distribution channels can mitigate risks.
- AI and machine learning enhance detection capabilities against attacks.
- Zero trust architecture reduces reliance on trusted networks.
- Industry collaboration is vital for effective threat intelligence sharing.
- Regular code audits and monitoring are crucial for software integrity.
- Digital signatures alone are insufficient; comprehensive security measures are needed.
Related Articles
- Robots on the Rails: How Automation is Shaping Public Transport [2025]
- Understanding the Impact of DDoS Attacks on Ubuntu Services [2025]
- AI is Scaling a Billion-Dollar Fraud Problem, and You’re the Victim [2025]
- How Canada Uses Canary Traps for Election Security: An In-Depth Analysis [2025]
- AI-Generated Phishing Attacks: Beyond the Inbox and How to Protect Yourself [2025]
- Autonomous AI Tools Revolutionize Pentagon Operations [2025]
![Understanding Supply-Chain Attacks: The Daemon Tools Incident and Its Implications [2025]](https://tryrunable.com/blog/understanding-supply-chain-attacks-the-daemon-tools-incident/image-1-1778011456577.jpg)



