Lexis Nexis Data Breach: Unraveling the Impact and Future Implications [2025]
Last month, Lexis Nexis confirmed a data breach that exposed critical customer and business information. The breach, reported by Tech Radar, has sparked significant concern across industries reliant on Lexis Nexis's data solutions. This article delves into the ramifications of the breach, the methods employed by the hackers, and the measures businesses can take to protect themselves in the future.
TL; DR
- Breach Overview: Hackers accessed outdated but significant data at Lexis Nexis, involving customer and business information.
- Data Compromised: Includes 2GB of files with sensitive business contacts and user credentials.
- Security Measures: Companies must enhance cybersecurity frameworks to prevent future breaches.
- Industry Impact: The breach affects legal, corporate, and government sectors globally.
- Future Steps: Regular audits and updates to cybersecurity protocols are recommended.

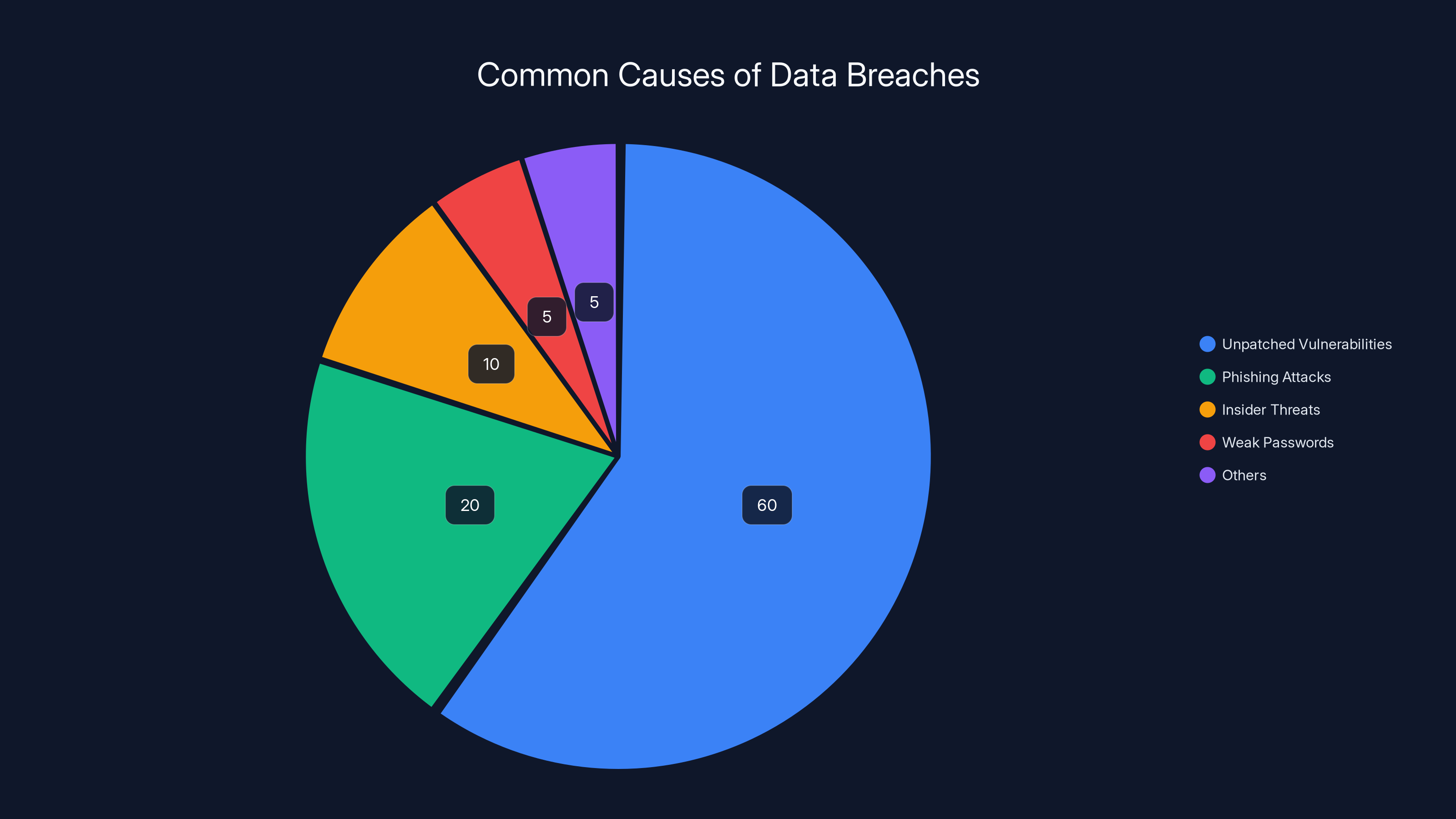
Unpatched vulnerabilities account for 60% of data breaches, highlighting the importance of regular updates and patches. (Estimated data)
Understanding the Lexis Nexis Data Breach
The Lexis Nexis data breach has brought to light vulnerabilities in even the most secure systems. The breach involved 2GB of data, including sensitive information about businesses and government entities. Lexis Nexis, a leading provider of legal, regulatory, and business information, confirmed the breach but downplayed its impact by stating that the data was outdated, as noted by Bleeping Computer.
The Role of Fulcrum Sec
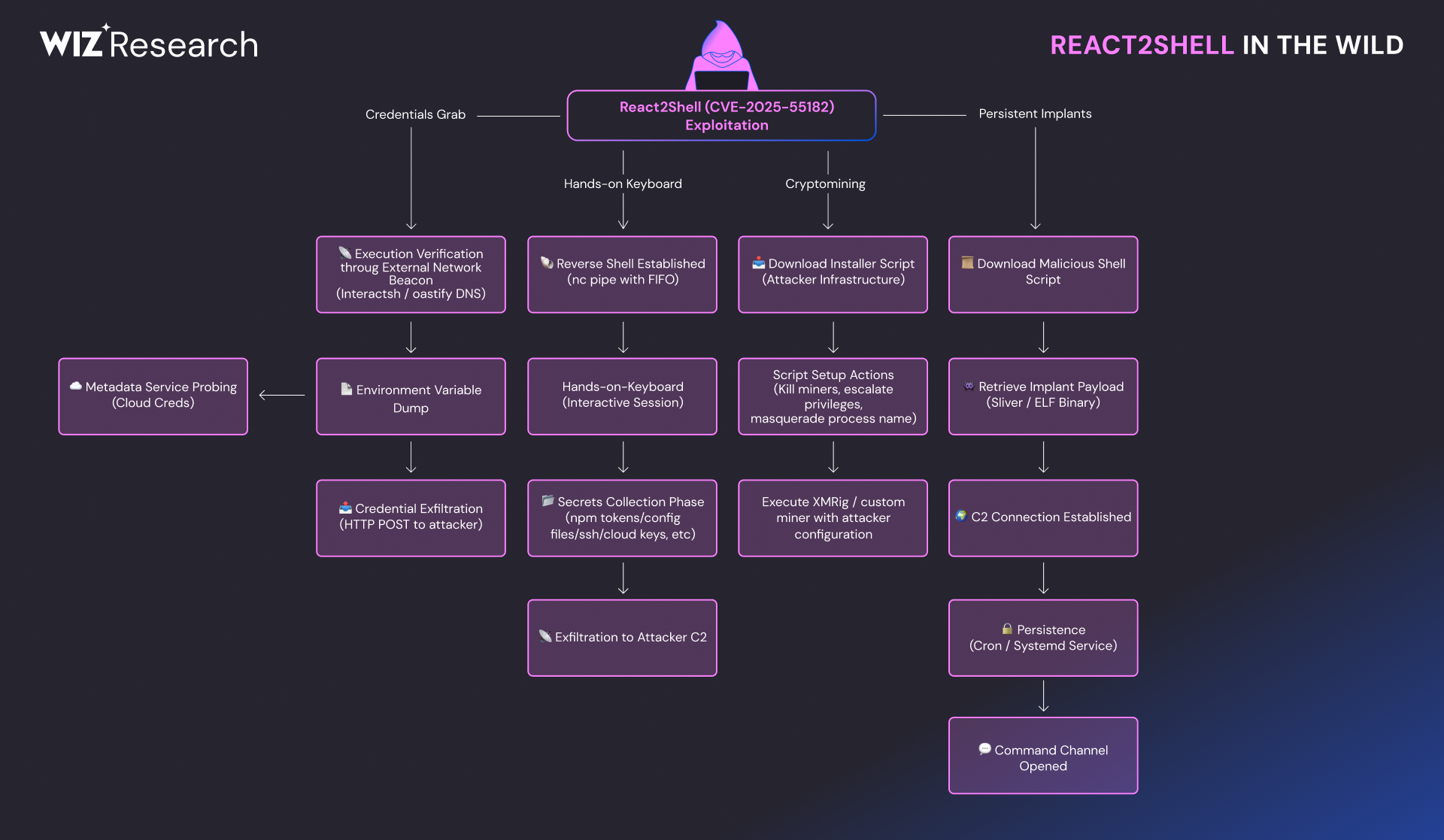
Fulcrum Sec, the hacker group responsible for the breach, claims to have used an open-source post-exploitation framework known as React 2 Shell. This tool allowed them to exploit a vulnerability in an unpatched React frontend app, gaining access to a wealth of sensitive information, as detailed by The Hacker News.
What Was Compromised?
The data compromised included customer names, user IDs, business contact information, and other non-sensitive data. However, the breach exposed the risk of relying on outdated security measures, according to Cybersecurity News.

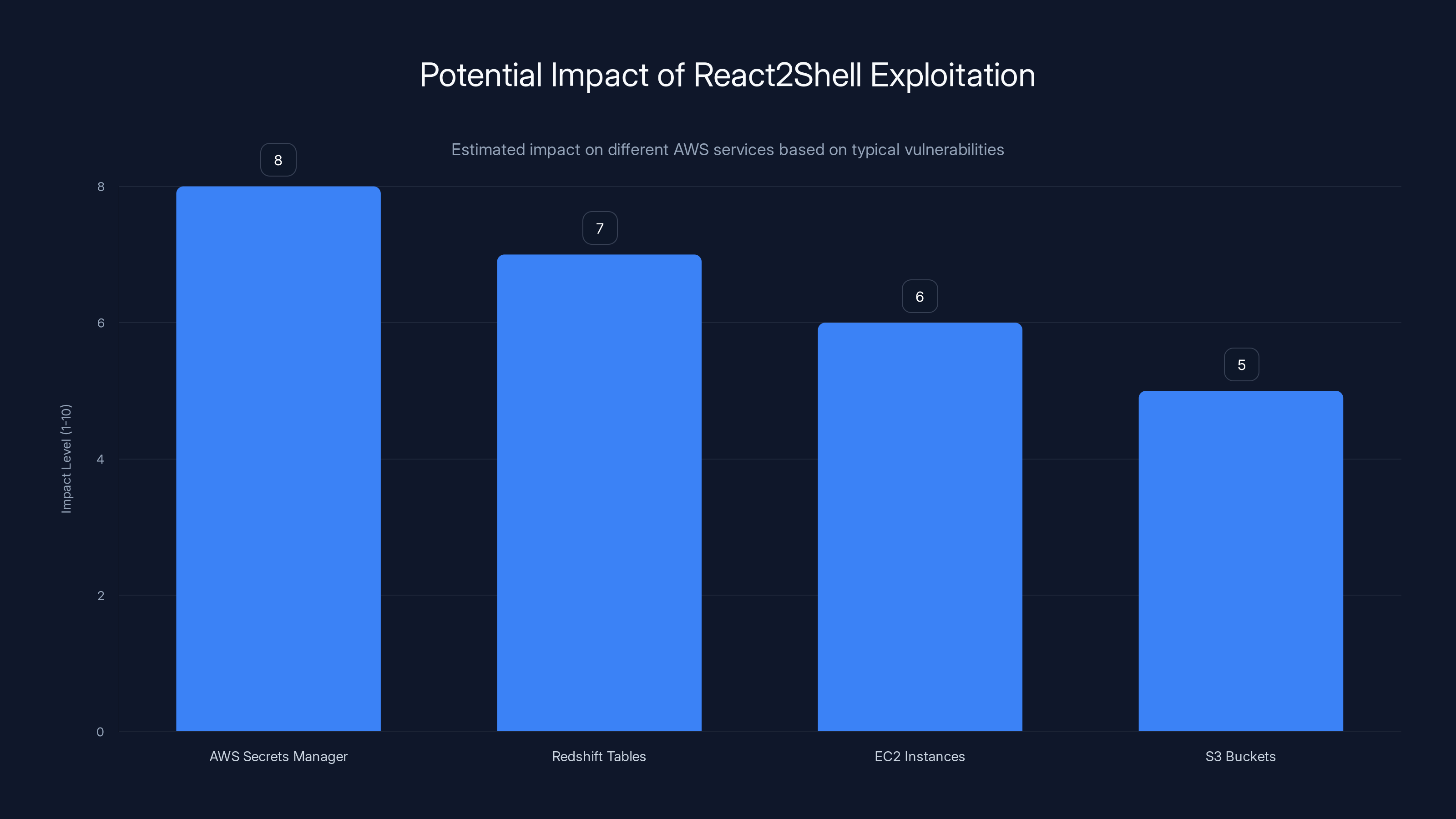
The chart estimates the impact level of React2Shell exploitation on various AWS services. AWS Secrets Manager and Redshift Tables are most vulnerable. Estimated data.
The Technical Breakdown
Understanding the technical aspects of the breach is crucial for preventing future incidents. Fulcrum Sec's use of React 2 Shell showcases the importance of securing all aspects of a tech stack.
Exploiting React 2 Shell
React 2 Shell is a post-exploitation framework that targets vulnerabilities in React applications. By exploiting these weaknesses, hackers can gain unauthorized access to sensitive data, as highlighted by Zero Day Initiative.
Impact on AWS Infrastructure
Fulcrum Sec reportedly accessed AWS Secrets Manager secrets and Redshift tables. This highlights the importance of securing cloud infrastructure and regularly rotating credentials, as emphasized by The Record.

The Broader Implications
The breach's implications extend far beyond Lexis Nexis, affecting industries that depend on accurate and secure data.
Legal and Government Sectors
Lexis Nexis is a critical resource for legal professionals and government agencies. The breach exposed data related to federal judges, US DoJ attorneys, and SEC staff, raising concerns about data integrity and confidentiality, as reported by LawNext.
Corporate Impact
With thousands of customer accounts compromised, businesses must reassess their data security strategies. The breach serves as a wake-up call for companies to strengthen their cybersecurity measures, as noted by CRN.

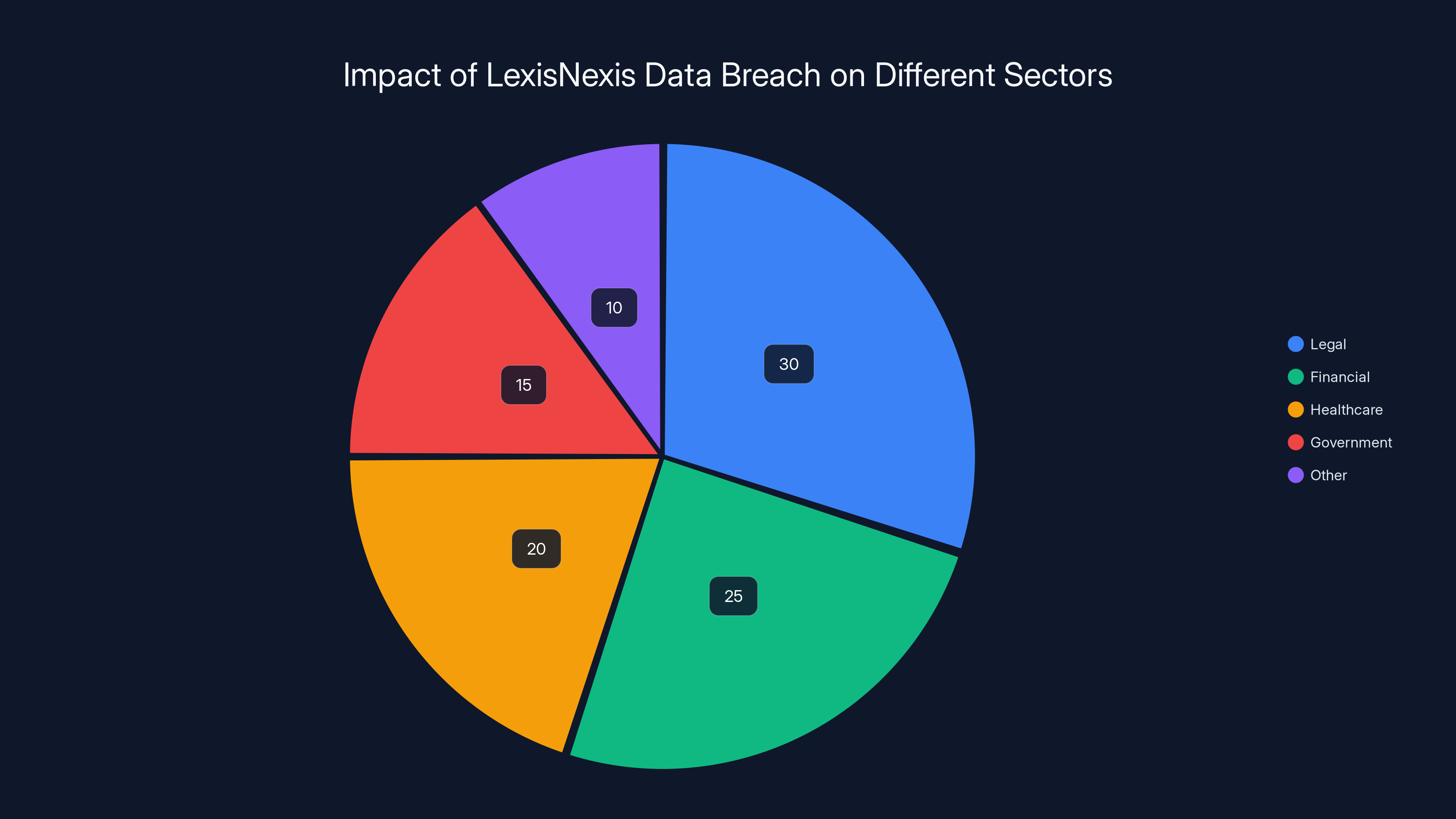
Estimated data shows the legal sector is most affected by the LexisNexis data breach, followed by financial and healthcare industries.
Best Practices for Data Security
In light of the breach, what steps can businesses take to protect themselves?
Regular Security Audits
Conducting regular security audits can identify vulnerabilities before they are exploited. Audits should cover both software and hardware components of a company's IT infrastructure, as recommended by Sci-Tech Today.
Employee Training
Employees are often the weakest link in cybersecurity. Regular training can help employees recognize phishing attempts and other common threats, as emphasized by PR Newswire.

Future Predictions and Trends
As data breaches become more sophisticated, staying ahead of the curve is essential.
The Rise of AI in Cybersecurity
AI and machine learning are increasingly used to predict and mitigate cyber threats. These technologies can identify patterns and anomalies that may indicate a breach attempt, as discussed by The Record.
Enhanced Encryption Techniques
Future trends suggest a move towards more robust encryption methods to protect data in transit and at rest. This will be crucial in safeguarding sensitive information, as highlighted by Cybersecurity News.
Conclusion
The Lexis Nexis data breach serves as a stark reminder of the vulnerabilities present in modern IT infrastructures. By understanding the breach's implications and implementing robust security measures, businesses can protect themselves from future threats. Continuous vigilance and adaptation to new security trends will be key in safeguarding sensitive data.
FAQ
What is the Lexis Nexis data breach?
The Lexis Nexis data breach involved unauthorized access to customer and business information, including 2GB of files. The breach was executed by a hacker group known as Fulcrum Sec.
How did the breach occur?
The breach occurred through a vulnerability in an unpatched React frontend app, using the React 2 Shell framework. This allowed hackers to access sensitive data stored in Lexis Nexis databases.
What data was compromised?
The compromised data included business contact information, user IDs, and customer names. However, sensitive information such as Social Security numbers and financial data was not affected.
What steps can businesses take to protect against similar breaches?
Businesses can protect against similar breaches by conducting regular security audits, implementing multi-factor authentication, and ensuring all software components are updated and patched.
What are the broader implications of the breach?
The breach affects industries reliant on Lexis Nexis data, including legal, corporate, and government sectors. It highlights the importance of robust cybersecurity measures.
How can AI help in cybersecurity?
AI can predict and mitigate cyber threats by identifying patterns and anomalies that may indicate a breach attempt. This can enhance the overall security posture of an organization.
Key Takeaways
- Data breaches expose critical vulnerabilities in IT infrastructures.
- Regular audits and updates are essential for cybersecurity.
- AI and machine learning are pivotal in modern cybersecurity strategies.
- The legal and government sectors must prioritize data integrity.
Related Articles
- Massive Data Breach on French Medical Platform: Lessons and Future Implications [2025]
- Understanding Computer Vulnerabilities to TEMPEST Attacks [2025]
- Hackers Are Turning to Easy, Fast AI Solutions to Roll Out Attacks: How to Keep Your Business Safe [2025]
- The Rise of Government Hacking Tools in Cybercrime: A Deep Dive [2025]
- A Possible US Government iPhone-Hacking Toolkit Is Now in the Hands of Foreign Spies and Criminals | WIRED
- Digital Warfare: The Role of Cyber Operations in Modern Conflicts [2025]
![LexisNexis Data Breach: What You Need to Know [2025]](https://tryrunable.com/blog/lexisnexis-data-breach-what-you-need-to-know-2025/image-1-1772638860488.jpg)



