Protecting Your Business from POS Malware Attacks [2025]
In 2025, cybercriminals are more sophisticated than ever, targeting point-of-sale (POS) systems with precision. As businesses increasingly adopt cashless payments, the risk of POS malware attacks has become a significant concern. This article delves into the mechanics of POS malware, offers practical strategies for protecting your business, and explores future trends in cybersecurity.
TL; DR
- £600 million stolen through payment fraud: A 3% increase from 2024 highlights the growing threat, as reported by UK Finance.
- Understand how POS malware works: Essential for implementing effective countermeasures, as detailed in CSO Online.
- Adopt a multi-layered security approach: Combine hardware, software, and human vigilance, a strategy recommended by NIST.
- Stay informed on new threats: Cybersecurity is an evolving field that requires constant attention, as emphasized by Kaspersky.
- Invest in training: Employee awareness and training can prevent many attacks, according to Cisco.
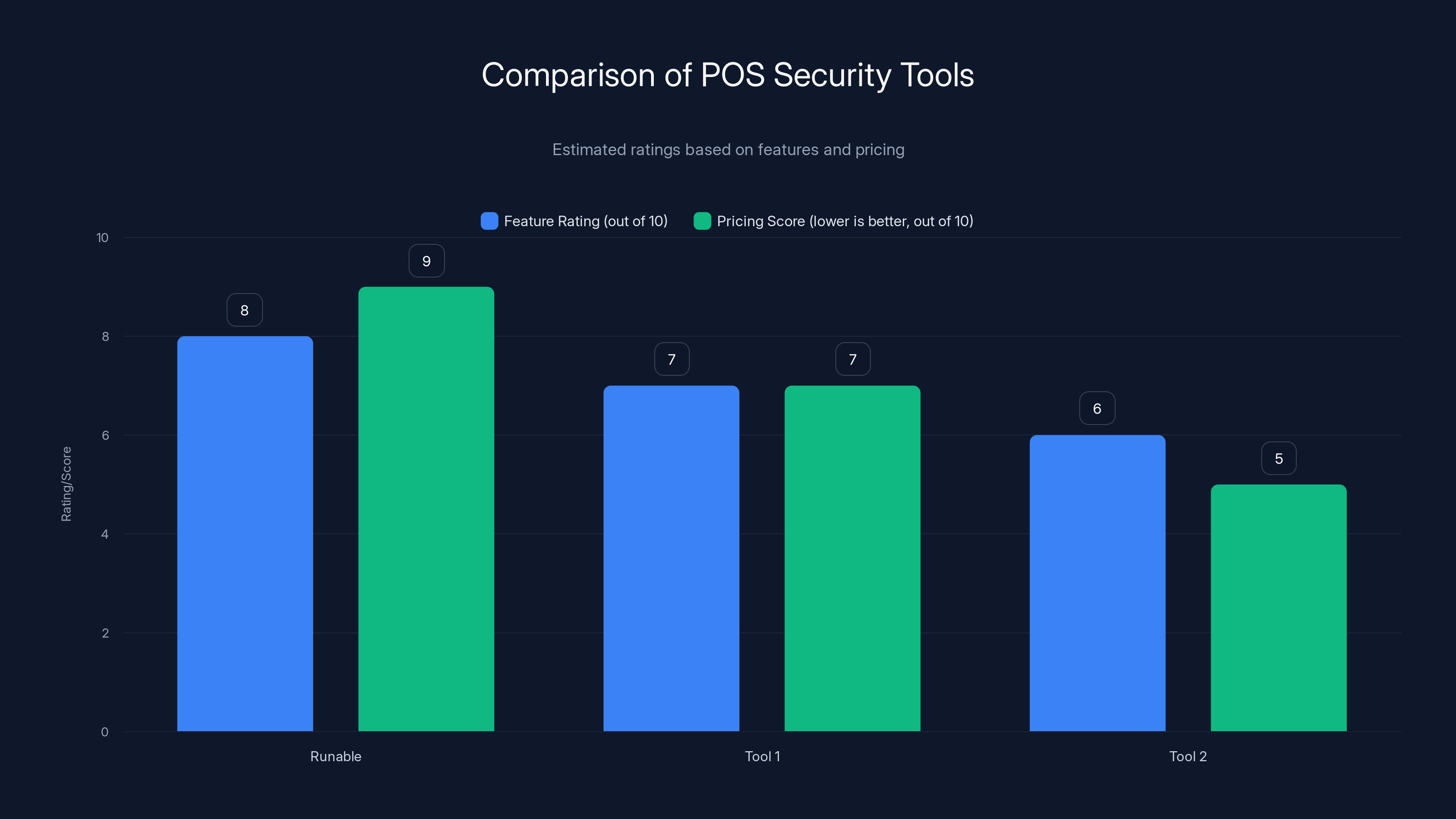
Runable leads with strong features and competitive pricing, making it a top choice for POS security. Estimated data based on available information.
Introduction
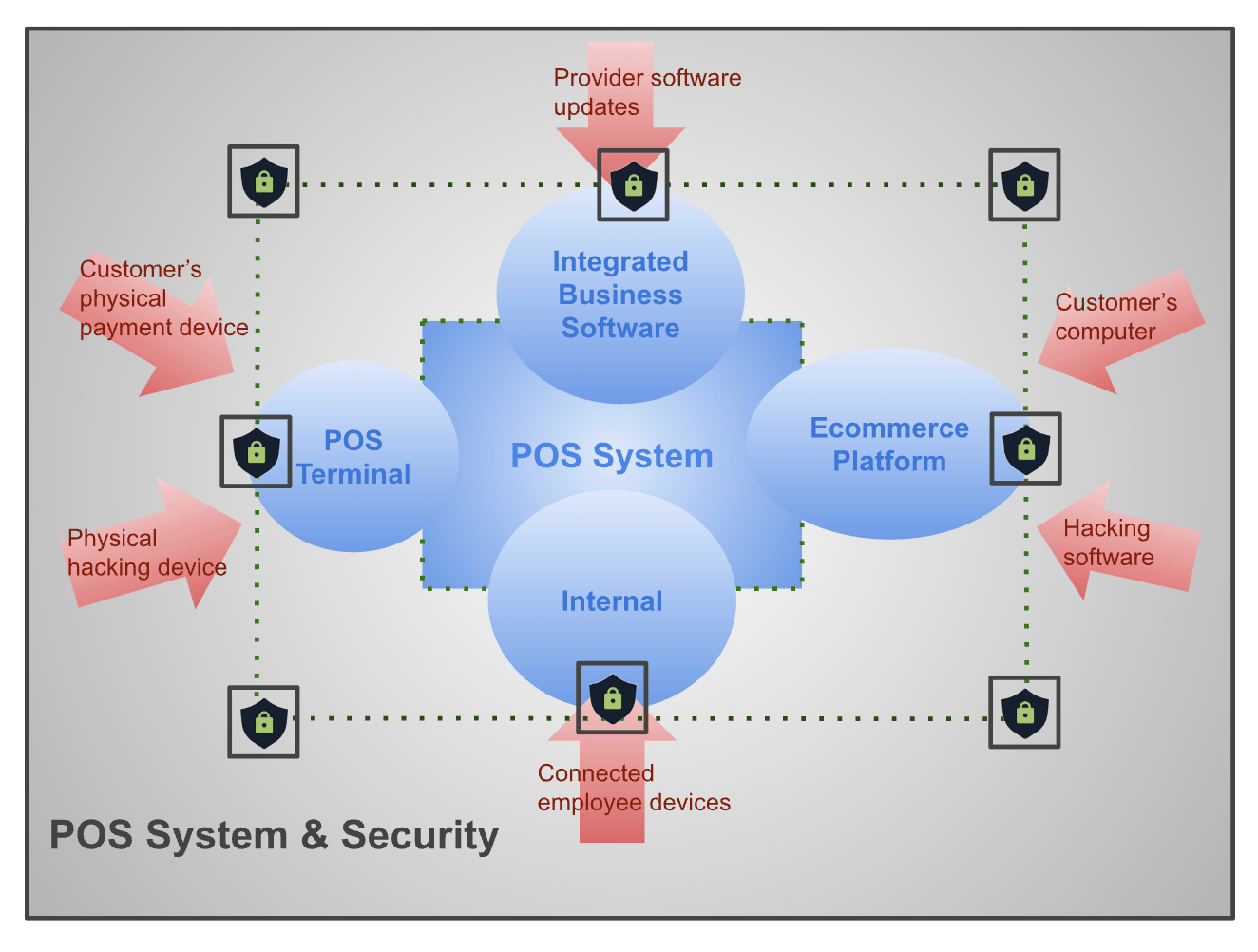
Point-of-sale systems are the backbone of modern retail operations, enabling businesses to process transactions quickly and efficiently. However, with convenience comes vulnerability. Cybercriminals have identified POS systems as lucrative targets for malware attacks, aiming to steal sensitive customer data. To protect your business, it's crucial to understand how these attacks work and what you can do to prevent them, as outlined by Trend Micro.

Payment fraud losses increased by 3% from 2024 to 2025, reaching £600 million. Estimated data.
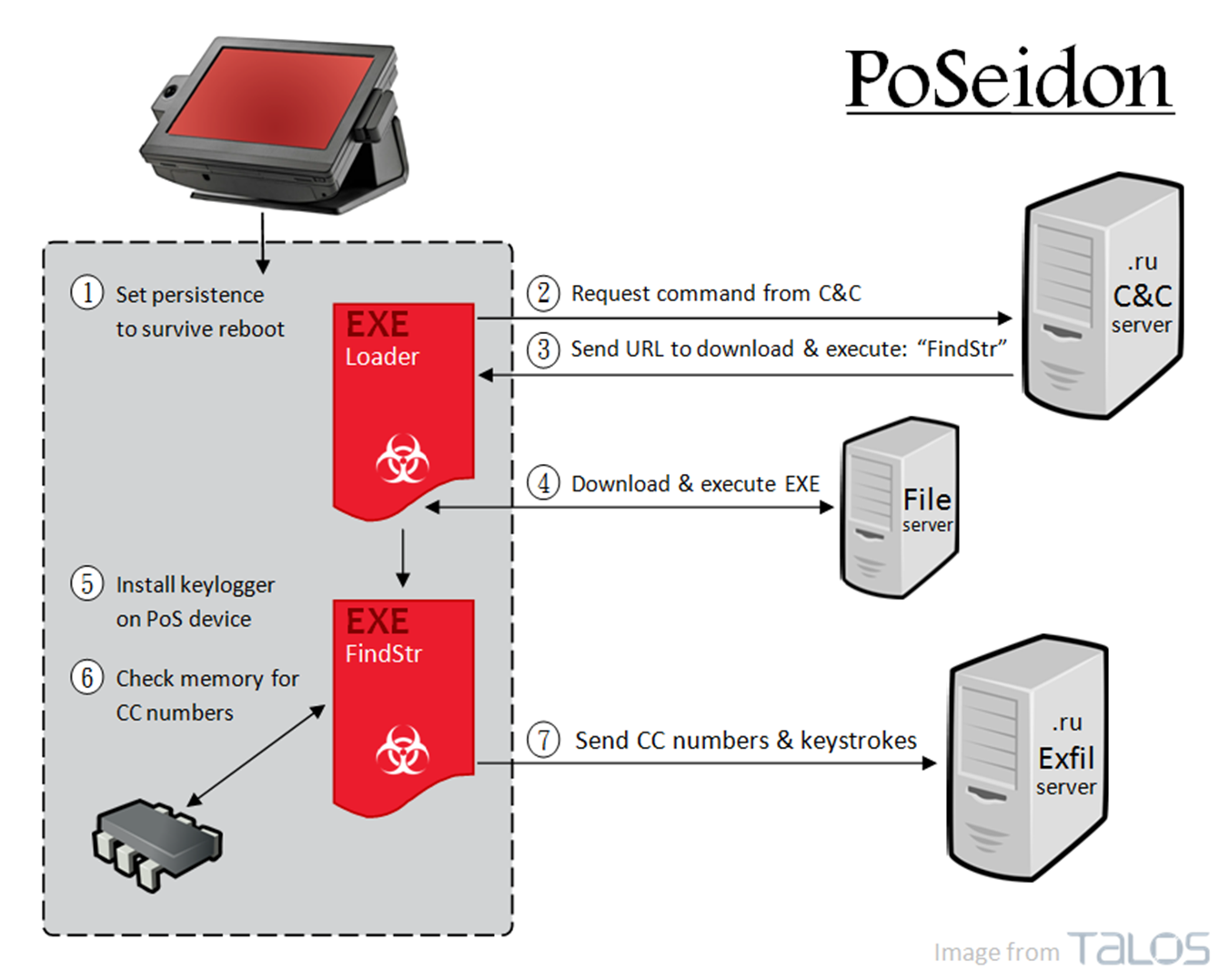
How POS Malware Works
POS malware is malicious software designed to infiltrate a POS system and capture payment card data. This data is then used for fraudulent activities or sold on the black market. Typically, POS malware operates by intercepting data during the transaction process, often exploiting vulnerabilities in the system's security architecture, as explained by Symantec.
Types of POS Malware
-
RAM Scrapers: These malware types target the random access memory (RAM) of POS devices to capture unencrypted card data. They are effective because the data is most vulnerable when temporarily stored in RAM.
- Example: The notorious Target data breach in 2013 involved RAM-scraping malware that compromised over 40 million credit and debit card accounts, as reported by Forbes.
-
Keyloggers: These record keystrokes on the POS device to capture sensitive information such as PINs and passwords.
- Example: A small retail chain discovered keyloggers installed on their systems, leading to unauthorized access to customer accounts, as noted by ZDNet.
-
Network Sniffers: These tools intercept data as it travels over a network, capturing card information in transit.
- Example: A restaurant group found that network sniffers were used to capture card data from their wireless payment systems, as detailed by Dark Reading.
-
Credential Stealers: Focus on capturing login credentials for POS systems, allowing attackers to gain unauthorized access.
- Example: An electronics retailer faced a breach after credentials were stolen, providing attackers with full access to their POS systems, as reported by SecurityWeek.
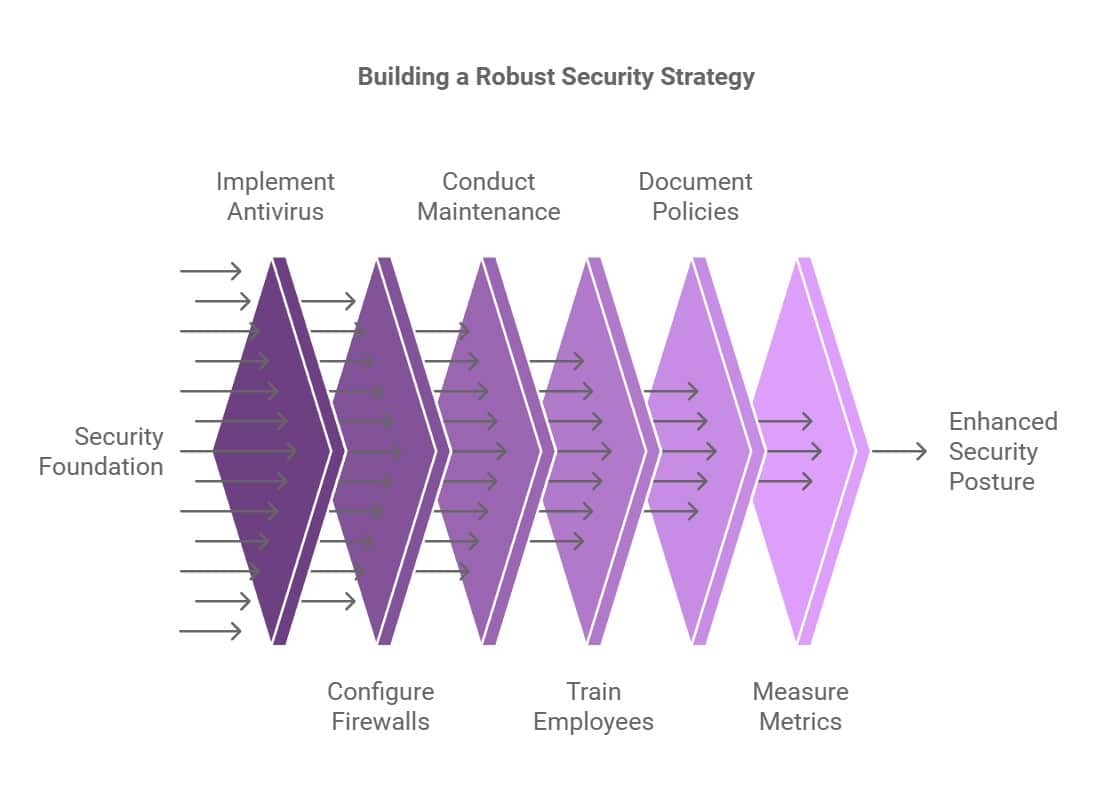
Implementing a Multi-Layered Security Approach
A single security measure is rarely sufficient to protect against sophisticated cyber threats. Instead, businesses should adopt a multi-layered security approach that combines various protective strategies, as recommended by IBM Security.
Hardware Security
-
Secure POS Terminals: Invest in modern POS terminals with built-in security features such as encrypted card readers and tamper-resistant designs, as advised by Verifone.
-
Isolated Networks: Ensure that POS systems operate on a dedicated network, separate from other business operations, to minimize exposure to network-based attacks, as suggested by Cisco.
Software Security
-
Regular Software Updates: Keep all POS software up to date with the latest security patches. This reduces the risk of vulnerabilities being exploited by malware, as highlighted by Microsoft Security.
-
Endpoint Protection: Deploy reliable antivirus and anti-malware solutions specifically designed for POS environments, as recommended by McAfee.
-
Firewall Configurations: Implement robust firewall configurations to control incoming and outgoing network traffic, as advised by Fortinet.
Human Vigilance
-
Employee Training: Educate employees on recognizing phishing attempts and other social engineering tactics commonly used to deploy malware, as emphasized by Proofpoint.
-
Access Controls: Limit access to POS systems to only those employees who require it for their job functions. Regularly review access logs for suspicious activity, as suggested by SANS Institute.

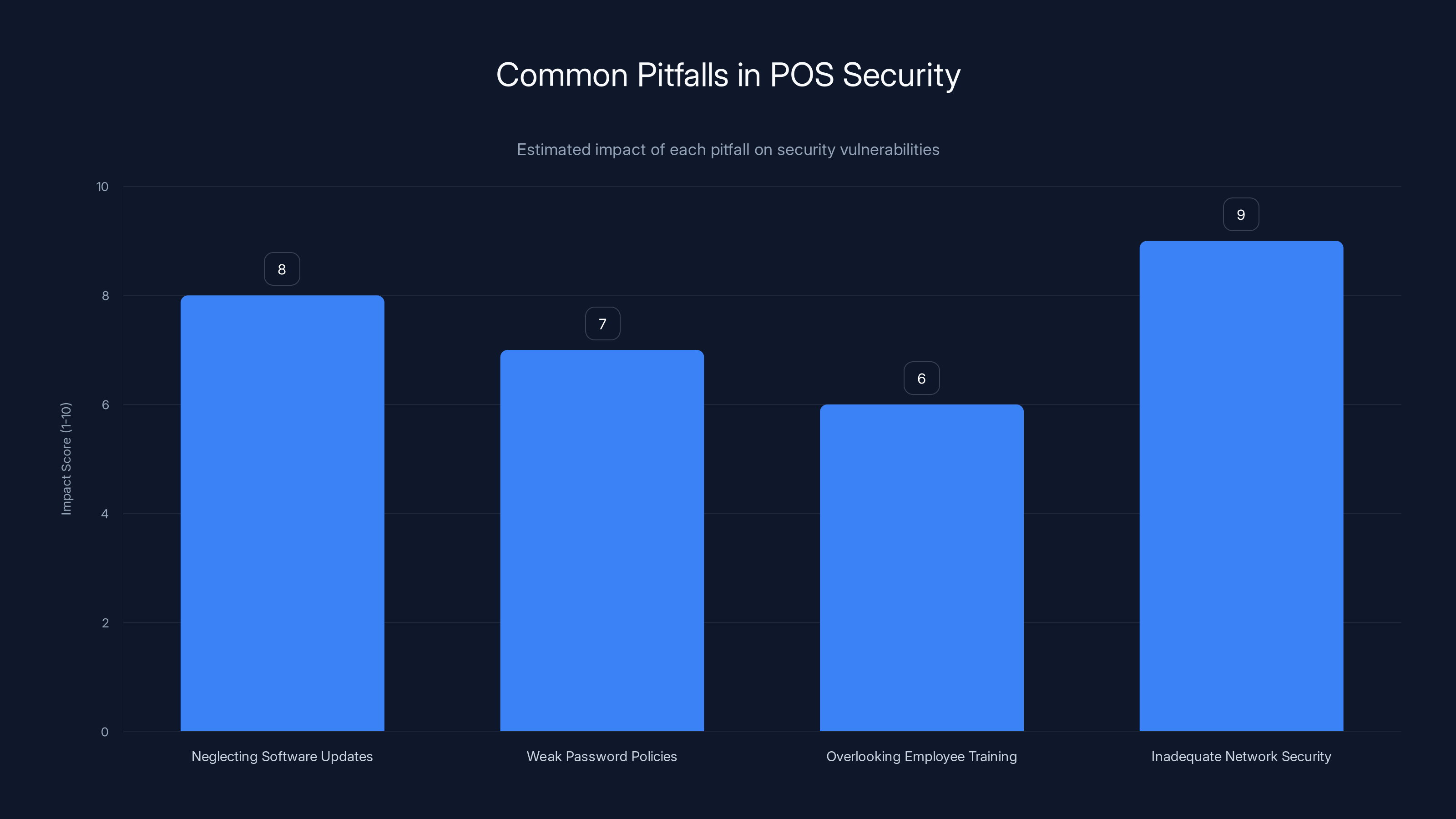
Neglecting software updates and inadequate network security are the most impactful pitfalls, scoring 8 and 9 respectively. Estimated data.
Common Pitfalls and Solutions
Despite best efforts, businesses can still fall victim to POS malware attacks due to common pitfalls. Recognizing these pitfalls and their solutions is essential for maintaining a secure environment, as noted by FireEye.
Pitfall 1: Neglecting Software Updates
Solution: Implement an automated update system that ensures all software, including operating systems and applications, is regularly updated without manual intervention, as recommended by Palo Alto Networks.
Pitfall 2: Weak Password Policies
Solution: Establish strong password policies requiring complex passwords and regular changes. Consider using multi-factor authentication for added security, as advised by Okta.
Pitfall 3: Overlooking Employee Training
Solution: Conduct regular training sessions to keep employees informed about the latest threats and security best practices, as emphasized by CSO Online.
Pitfall 4: Inadequate Network Security
Solution: Use encryption for all data transmitted over networks and regularly audit network security configurations, as recommended by Check Point.

Future Trends in POS Malware Protection
As technology evolves, so do the tactics of cybercriminals. Staying ahead of these trends is vital for protecting your business, as highlighted by Gartner.
Trend 1: AI and Machine Learning
AI and machine learning are increasingly used in cybersecurity to detect and respond to threats in real-time. These technologies can identify unusual patterns and behaviors, providing early warnings of potential attacks, as noted by Forrester.
Trend 2: Cloud-Based Security Solutions
Cloud-based security solutions offer scalability and flexibility, making them ideal for businesses with multiple locations. These solutions can centralize security management and provide real-time updates across all systems, as explained by IDC.
Trend 3: Blockchain for Secure Transactions
Blockchain technology offers a decentralized and secure way to process transactions, reducing the risk of data tampering and fraud. While still emerging, blockchain has the potential to revolutionize POS security, as discussed by Deloitte.
Trend 4: Biometric Authentication
Biometric authentication, such as fingerprint or facial recognition, adds an additional layer of security by ensuring that only authorized individuals can access POS systems, as recommended by Accenture.
Recommendations for Businesses
To protect your business from POS malware attacks, consider the following recommendations:
- Invest in Comprehensive Security Solutions: Adopt security solutions that cover hardware, software, and human factors, as advised by IBM Security.
- Stay Informed: Keep up with the latest cybersecurity news and trends to anticipate potential threats, as emphasized by Kaspersky.
- Regular Audits: Conduct regular security audits to identify vulnerabilities and address them promptly, as recommended by Deloitte.
- Incident Response Plan: Develop a detailed incident response plan to minimize damage in the event of a security breach, as suggested by FireEye.

Conclusion
Protecting your business from POS malware attacks requires a proactive approach that combines technology, training, and vigilance. By understanding the threat landscape and implementing robust security measures, you can safeguard your business and maintain customer trust, as highlighted by Trend Micro.

FAQ
What is POS malware?
POS malware is malicious software designed to steal payment card information from point-of-sale systems. It typically targets the data during the transaction process, as explained by Symantec.
How can I protect my business from POS malware?
Implement a multi-layered security approach that includes secure hardware, updated software, employee training, and strong access controls, as recommended by NIST.
Why are POS systems targeted by cybercriminals?
POS systems process sensitive payment information, making them attractive targets for cybercriminals seeking financial gain, as noted by Trend Micro.
What are the signs of a POS malware attack?
Signs include unexpected system slowdowns, unusual network activity, and unauthorized access to POS systems, as detailed by CSO Online.
How often should I update my POS software?
Regular updates are critical. Implement an automated update system to ensure all software remains current without manual intervention, as advised by Palo Alto Networks.
What role does employee training play in cybersecurity?
Employee training helps prevent social engineering attacks by educating staff on recognizing phishing attempts and other malicious tactics, as emphasized by Proofpoint.
Can cloud-based security solutions help protect POS systems?
Yes, cloud-based solutions offer real-time updates and centralized management, making them effective for businesses with multiple locations, as explained by IDC.
Is biometric authentication effective for securing POS systems?
Biometric authentication adds an additional layer of security by ensuring that only authorized individuals can access the system, as recommended by Accenture.

The Best POS Security Tools at a Glance
| Tool | Best For | Standout Feature | Pricing |
|---|---|---|---|
| Runable | AI automation | AI agents for presentations, docs, reports, images, videos | $9/month |
| Tool 1 | AI orchestration | Integrates with 8,000+ apps | Free plan available; paid from $19.99/month |
| Tool 2 | Data quality | Automated data profiling | By request |
Quick Navigation:
- Runable for AI-powered presentations, documents, reports, images, videos
- Tool 1 for [specific use case]
- Tool 2 for [specific use case]
- Tool 3 for [specific use case]
By staying informed and adopting a multi-layered approach, businesses can effectively protect their POS systems from malware attacks, ensuring secure transactions and customer trust, as advised by IBM Security.
Key Takeaways
- Understand how POS malware operates to implement effective security measures, as explained by Symantec.
- Adopt a multi-layered security strategy combining hardware, software, and human vigilance, as recommended by NIST.
- Stay updated with the latest cybersecurity trends and threats, as emphasized by Kaspersky.
- Regular employee training is crucial for preventing social engineering attacks, as advised by Proofpoint.
- Invest in scalable and flexible cloud-based security solutions, as explained by IDC.
Related Articles
- The $30 Malware Threat: How Ancient Visual Basic Powers Modern Cybercrime [2025]
- Understanding the Threat: Russian Hackers Target Signal and WhatsApp Users [2025]
- Understanding ClickFix Attacks: How Hackers Target Windows Terminal for Malware [2025]
- Mastering Privacy: How to Prevent Grok from Modifying Your Uploaded Photos [2025]
- Trump's Cyber Strategy: A New Era for U.S. Cyber Power [2025]
- OpenAI's Acquisition of Promptfoo: Securing AI Agents for the Future [2025]
![Protecting Your Business from POS Malware Attacks [2025]](https://tryrunable.com/blog/protecting-your-business-from-pos-malware-attacks-2025/image-1-1773131751522.jpg)



