Why AES 128 Remains Secure in a Post-Quantum World [2025]
Last year, a friend called me in a panic. He'd read an article proclaiming the imminent demise of AES 128 encryption due to the rise of quantum computing. "Should I switch everything to AES 256?" he asked. My answer: Not so fast.
The truth is, there's a lot of confusion and fear surrounding quantum computing's impact on encryption. But when it comes to AES 128, the panic is largely misplaced. Let's dive deep into why AES 128 is more resilient than many think, even in a future dominated by quantum tech.
TL; DR
- AES 128 remains secure against quantum threats due to its robust structure.
- Grover's algorithm reduces security by half, but AES 128 still offers a 64-bit security level.
- Transitioning to AES 256 isn't urgent for most applications.
- Quantum readiness requires holistic planning, not just key size changes.
- AES 128's efficiency makes it ideal for resource-constrained devices.
- Future-proofing involves hybrid solutions, combining classical and quantum-resistant algorithms.

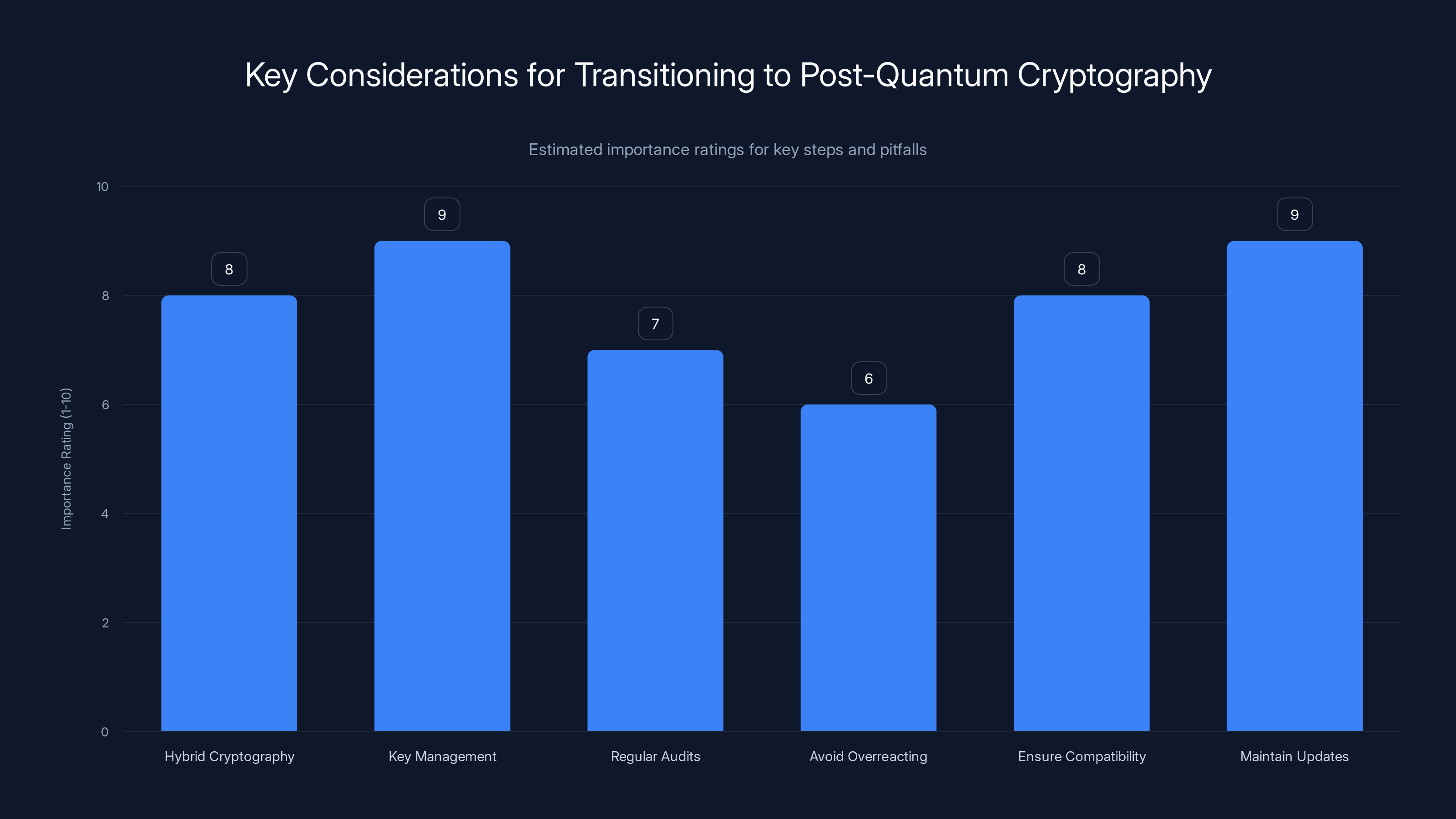
Key management and maintaining updates are rated highest in importance for transitioning to post-quantum cryptography. Estimated data.
Understanding AES 128
AES, or Advanced Encryption Standard, is a symmetric block cipher standardized by NIST in 2001. It operates on blocks of 128 bits using keys of 128, 192, or 256 bits. The AES 128 variant strikes a balance between security and computational efficiency, making it the most popular choice for a wide range of applications.
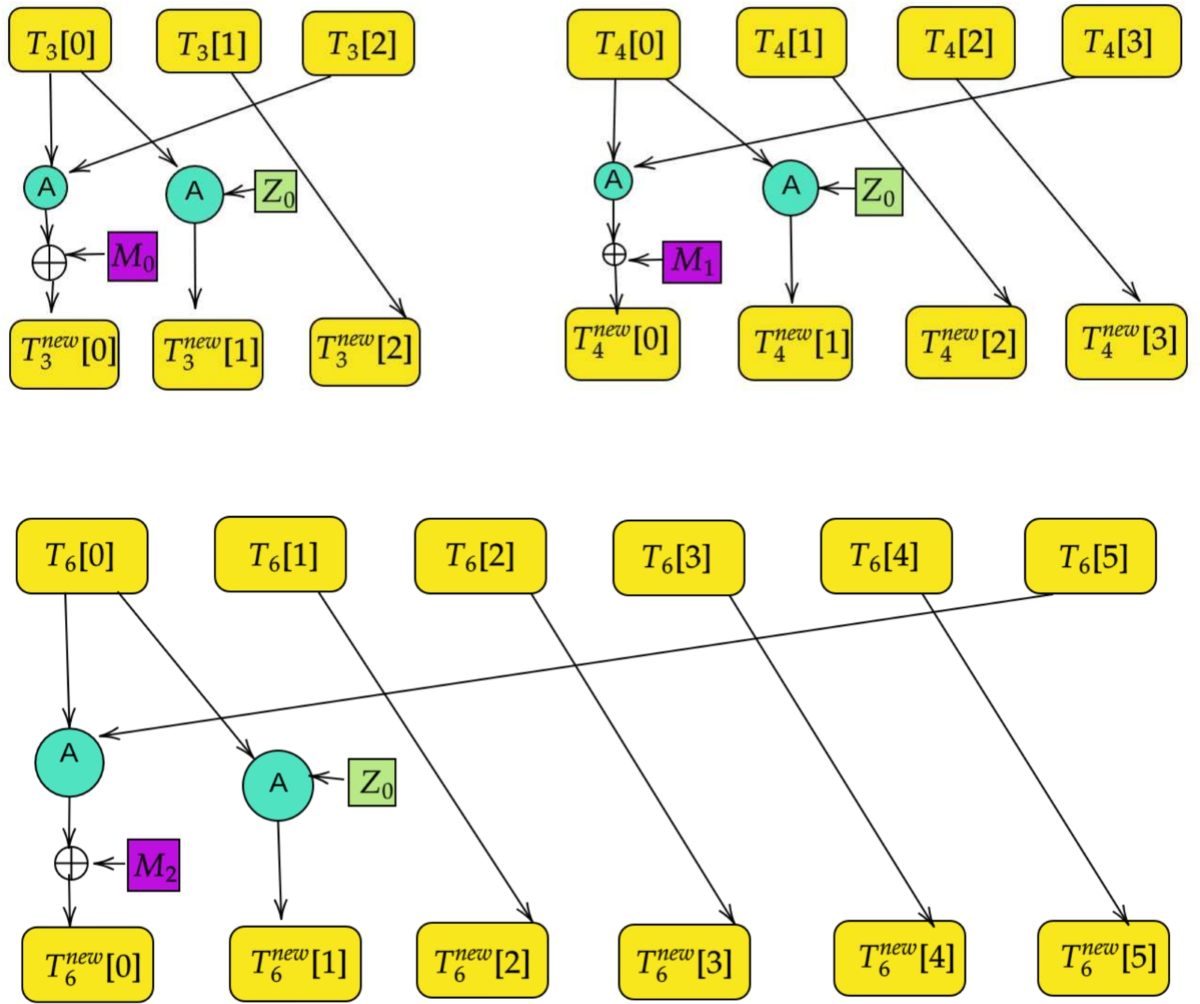
How AES 128 Works
AES 128 encryption involves several transformation steps on the data block, including substitution, permutation, mixing, and key addition. Here's a simplified breakdown:
- Sub Bytes: Each byte in the block is replaced with another according to a fixed substitution table.
- Shift Rows: Rows of the block are shifted cyclically to the left.
- Mix Columns: Columns are mixed using a linear transformation.
- Add Round Key: The block is XORed with a round key derived from the original AES 128 key.
These steps are repeated in a series of rounds (10 for AES 128), ensuring thorough diffusion and confusion, two fundamental principles of cryptographic security.
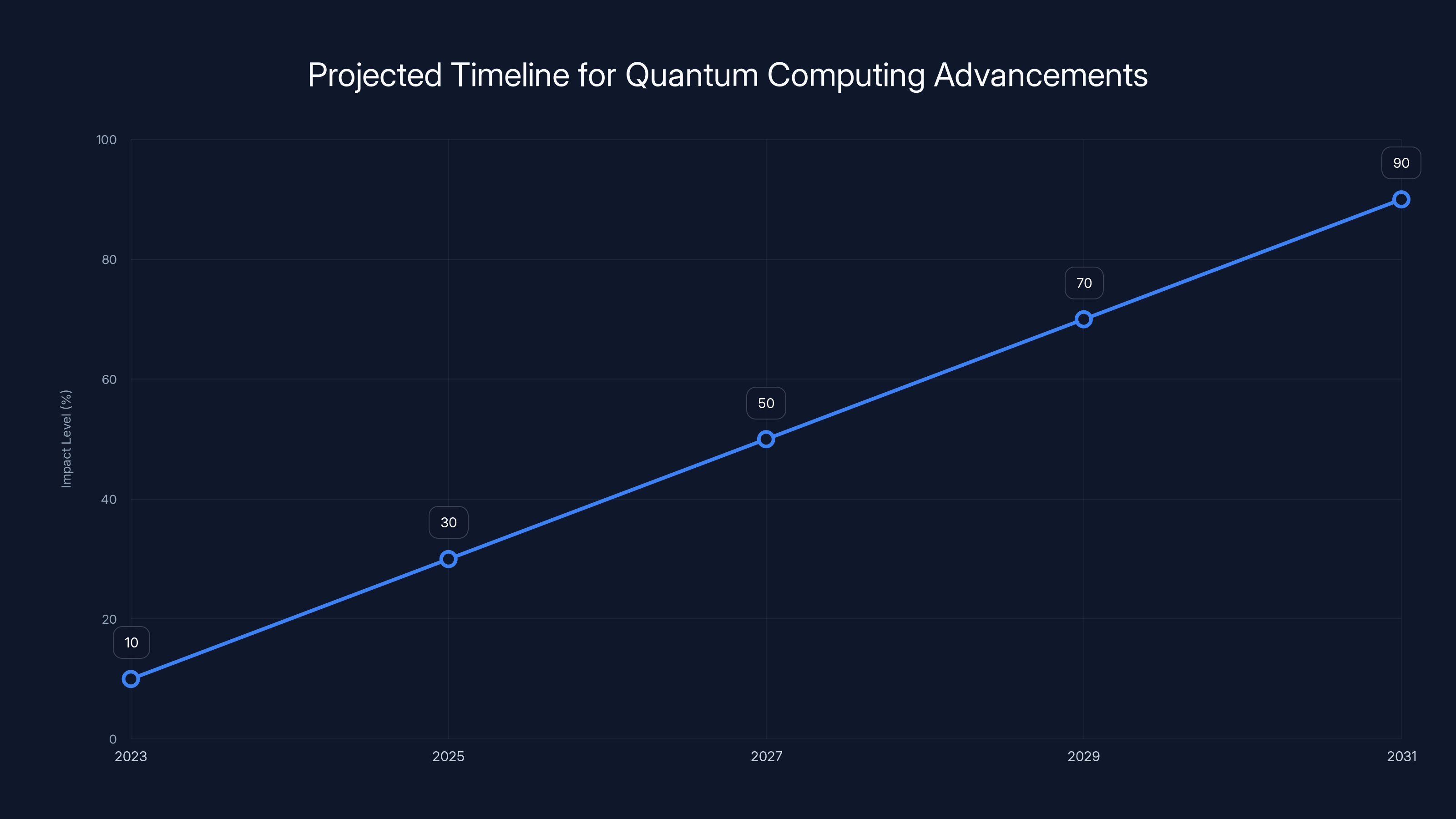
Estimated data shows a significant increase in quantum computing's impact on encryption by 2031, highlighting the need for hybrid solutions and ongoing research.
The Quantum Threat: Grover's Algorithm
Quantum computing introduces new algorithms that can disrupt traditional cryptographic methods. Grover's algorithm, in particular, threatens symmetric encryption by reducing the effective key length by half. For AES 128, this means a security reduction from 128 bits to 64 bits.
Why 64-Bit Security is Still Strong
A common misconception is that 64-bit security is inherently weak. However, this isn't the case. A 64-bit key space still involves 1.8 x 10^19 possible keys, requiring a significant computational effort even for a quantum computer.
Why AES 128 is Still Viable
Computational Efficiency
AES 128's efficiency makes it particularly suitable for devices with limited computational resources, such as IoT devices and embedded systems. The smaller key size results in faster encryption and decryption processes, conserving power and reducing latency.
Implementation Simplicity
AES 128 offers simplicity in implementation, which reduces the risk of errors and vulnerabilities in real-world applications. Its widespread adoption means that it has been thoroughly vetted and optimized by the cryptographic community.
Real-World Attack Scenarios
In practical terms, an attack leveraging Grover's algorithm would require a quantum computer with a significant number of qubits, far beyond current capabilities. Until such machines are developed, AES 128 remains a robust choice.
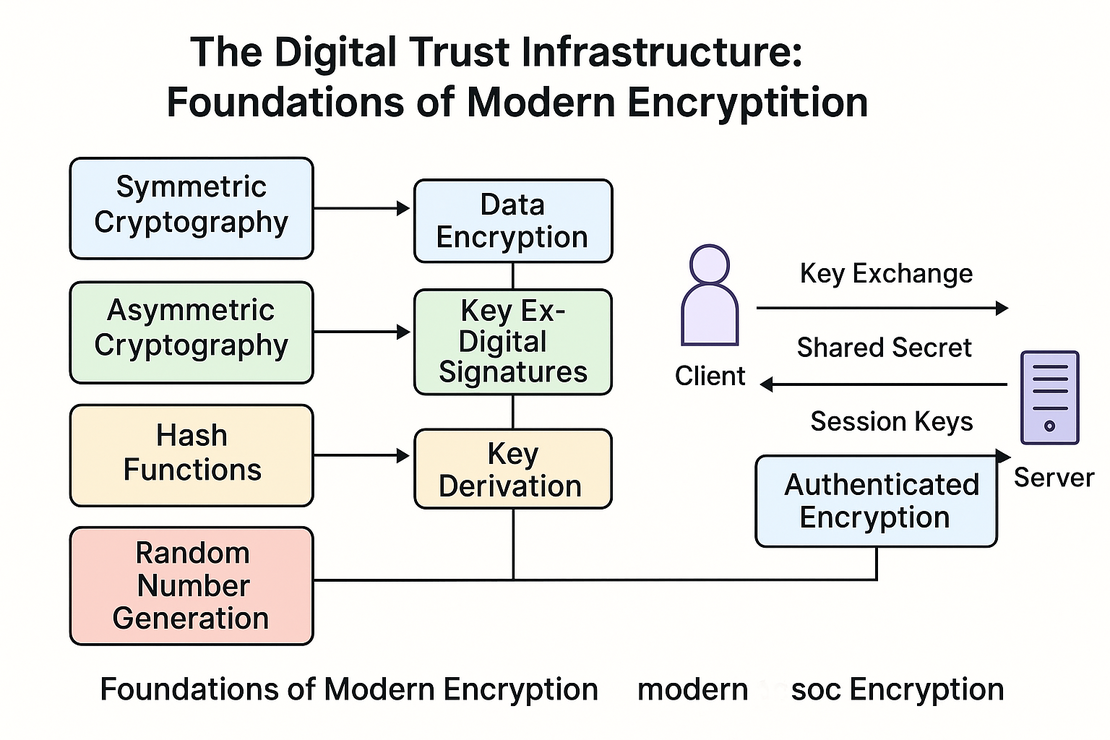
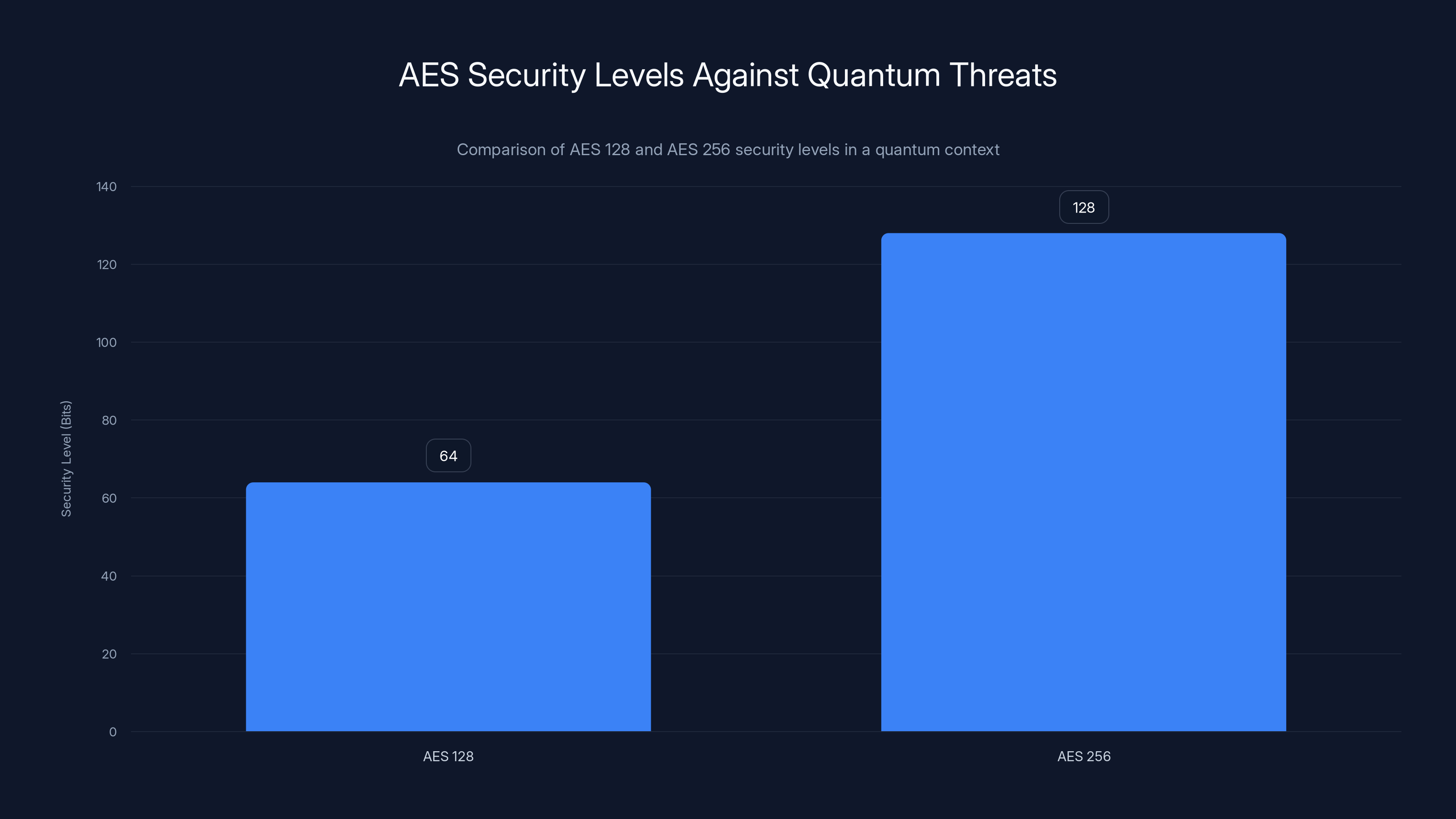
AES 128 offers a 64-bit security level under quantum threats due to Grover's algorithm, while AES 256 maintains a 128-bit level. Estimated data for illustration.
Practical Implementation Guide
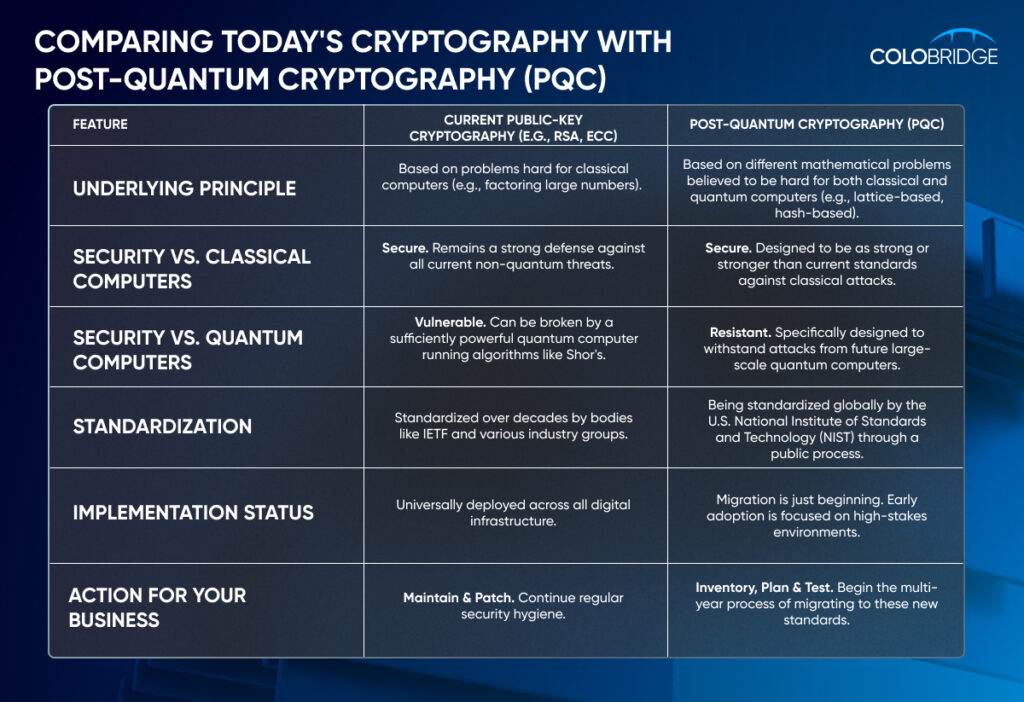
Transitioning to Post-Quantum Cryptography
While AES 128 is secure for now, forward-looking organizations should start preparing for a quantum future. Here are some steps to consider:
- Hybrid Cryptography: Combine AES 128 with quantum-resistant algorithms to hedge against future risks.
- Key Management: Implement robust key management practices to streamline transitions when needed.
- Regular Audits: Conduct regular security audits to ensure your encryption strategies remain effective.
Avoid Common Pitfalls
- Overreacting to Hype: Don't rush to increase key sizes without understanding the trade-offs.
- Ignoring Compatibility: Ensure that any transition plan maintains compatibility with existing systems.
- Neglecting Updates: Keep your cryptographic libraries and protocols up to date to benefit from the latest security enhancements.
Future Trends and Recommendations
Quantum computing's impact on encryption is significant but not insurmountable. Here are some trends and recommendations to consider:
Embrace Hybrid Solutions
Combining classical and quantum-resistant algorithms offers a balanced approach to security. This strategy provides protection against both current threats and future quantum attacks.
Monitor Quantum Developments
Stay informed about advancements in quantum computing and cryptography. This knowledge will help you make timely decisions about when and how to upgrade your systems.
Invest in Research
Support research into quantum-resistant algorithms and protocols. Engagement with the cryptographic community will keep you at the forefront of security innovation.
Conclusion
AES 128 remains a secure and efficient choice, even in a world on the brink of quantum computing breakthroughs. By understanding its strengths and limitations, and preparing for future challenges, organizations can maintain robust security while navigating the transition to post-quantum cryptography.
For those considering upgrades, remember that the best security strategies are adaptive and informed by the latest research and technological developments.
Key Takeaways
- AES 128 remains secure against quantum threats due to its robust structure.
- Grover's algorithm reduces AES 128's security level to 64 bits, which is still strong.
- Transitioning to AES 256 isn't urgent for most applications.
- Quantum readiness requires holistic planning, not just key size changes.
- AES 128's efficiency makes it ideal for resource-constrained devices.
- Future-proofing involves hybrid solutions, combining classical and quantum-resistant algorithms.
- Regular security audits ensure encryption strategies remain effective.
- Stay informed about advancements in quantum computing and cryptography.
Related Articles
- They Built a Legendary Privacy Tool. Now They’re Sworn Enemies | WIRED
- WordPress Vulnerability: How Hackers Exploit Simple Plugin Flaws [2025]
- Understanding and Mitigating Microsoft Teams Helpdesk Impersonation Attacks [2025]
- Spotting the Spyware: How Modern Spies Are Weaponizing Phishing [2025]
- Quantum Computing Revolutionizes Genome Analysis: Faster DNA Insights [2025]
- US Security Agency Still Using Mythos Despite Ban: Navigating the Complex World of Supply Chain Risks [2025]
FAQ
What is Why AES 128 Remains Secure in a Post-Quantum World [2025]?
He'd read an article proclaiming the imminent demise of AES 128 encryption due to the rise of quantum computing
What does tl; dr mean?
The truth is, there's a lot of confusion and fear surrounding quantum computing's impact on encryption
Why is Why AES 128 Remains Secure in a Post-Quantum World [2025] important in 2025?
But when it comes to AES 128, the panic is largely misplaced
How can I get started with Why AES 128 Remains Secure in a Post-Quantum World [2025]?
Let's dive deep into why AES 128 is more resilient than many think, even in a future dominated by quantum tech
What are the key benefits of Why AES 128 Remains Secure in a Post-Quantum World [2025]?
- AES 128 remains secure against quantum threats due to its robust structure
What challenges should I expect?
- Grover's algorithm reduces security by half, but AES 128 still offers a 64-bit security level
![Why AES 128 Remains Secure in a Post-Quantum World [2025]](https://tryrunable.com/blog/why-aes-128-remains-secure-in-a-post-quantum-world-2025/image-1-1776776762680.jpg)



