Inside the FBI's Cybersecurity Breach: Unraveling the Hijacking of Wiretaps and Search Warrants [2025]
Last month, the Federal Bureau of Investigation (FBI) found itself at the center of attention after suspicious activities on its internal networks were identified. While the FBI remains tight-lipped about the specifics, the incident reportedly involved the hijacking of wiretap and surveillance systems—critical tools in the agency's operations. This article explores the potential implications of such a breach, the technical intricacies involved, and the future of cybersecurity in sensitive governmental operations.
TL; DR
- Critical Breach: FBI systems managing wiretaps and surveillance were reportedly compromised.
- Suspected Actors: Media suggests involvement of a group known as Salt Typhoon.
- Technical Response: FBI claims to have leveraged all technical capabilities to address the issue.
- Future Measures: Emphasis on enhanced cybersecurity protocols and AI-driven monitoring systems.
- Bottom Line: The breach highlights vulnerabilities in critical systems and the urgent need for robust cybersecurity measures.
The Scope of the Breach
The breach reportedly affected systems used to manage wiretapping and foreign intelligence surveillance. These are not just any systems; they are integral to national security operations, often involving sensitive and classified information. The potential hijacking of such systems raises significant concerns about the integrity of ongoing investigations and the protection of classified data.
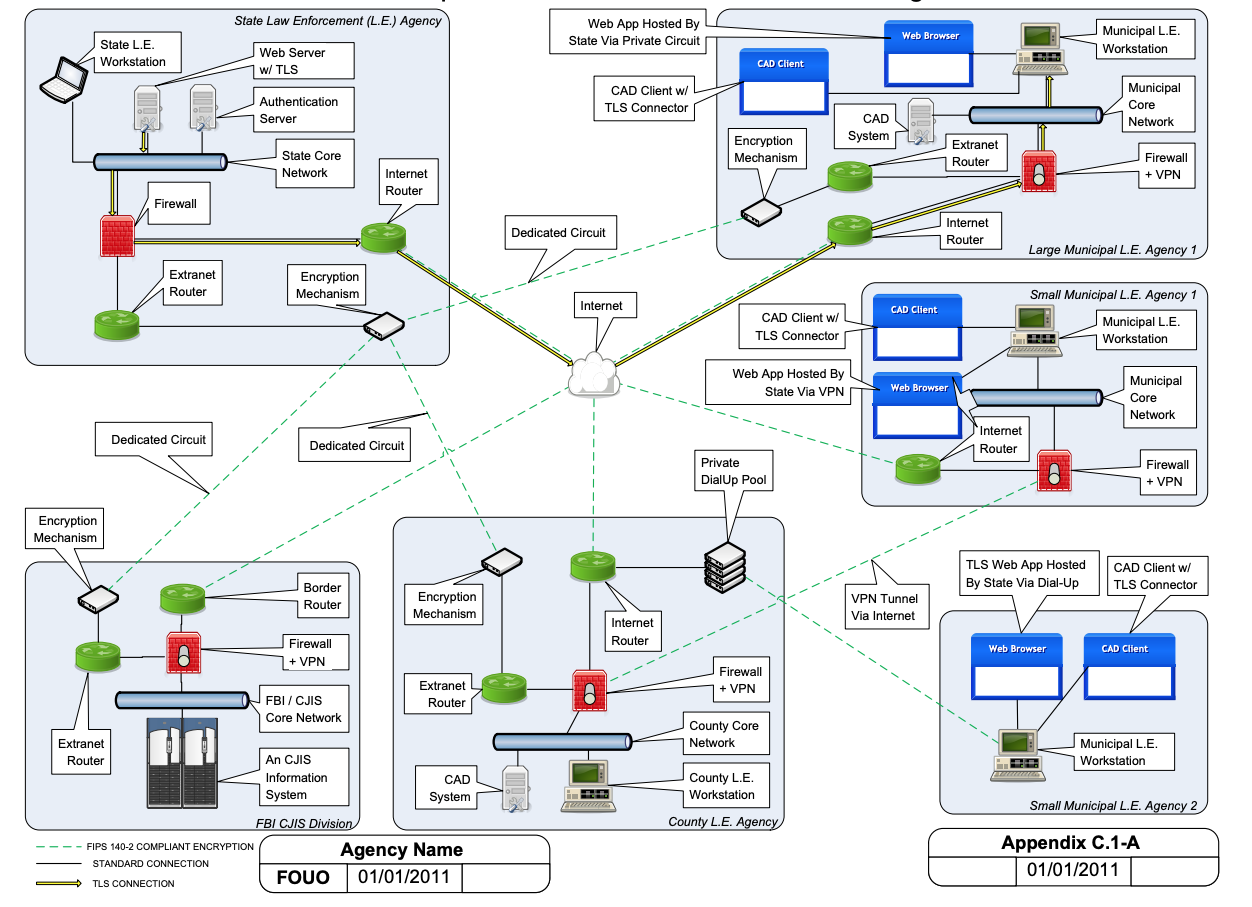
Key Components of Wiretap and Surveillance Systems
Wiretap and surveillance systems are complex networks that require seamless integration of software and hardware to function effectively. They typically include:
- Communication Interception Software: Allows the monitoring of phone calls, emails, and other digital communications.
- Data Storage Solutions: Securely store intercepted data for analysis and evidence.
- Analysis Tools: Utilize machine learning algorithms to identify patterns and threats.
- Access Control Mechanisms: Ensure that only authorized personnel access sensitive data.
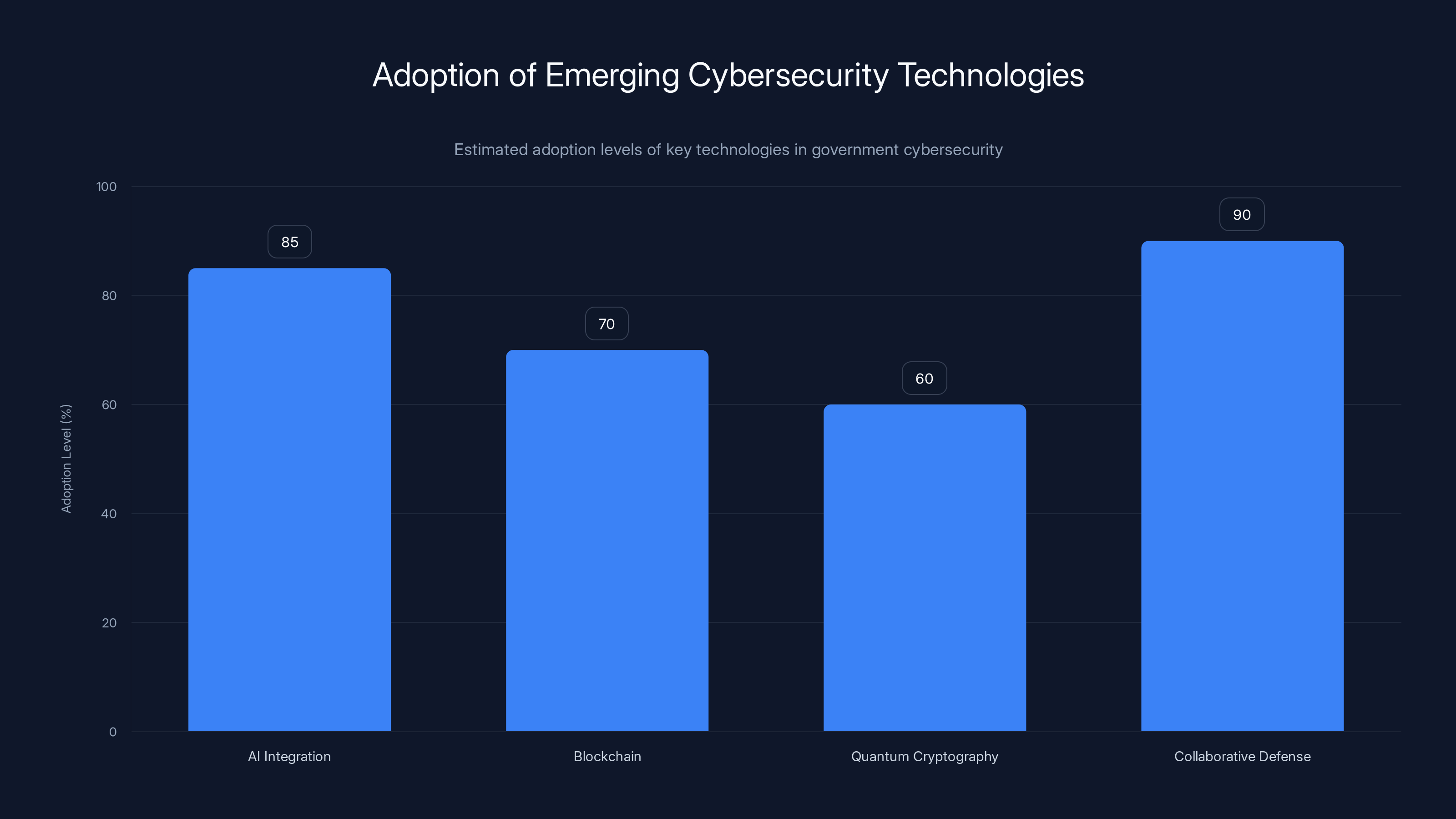
Government agencies are expected to highly adopt AI and collaborative defense strategies, with blockchain and quantum cryptography also gaining traction. Estimated data.
Potential Risks and Consequences
The implications of a breach in such systems are vast. Let's explore some potential risks:
Compromised Investigations
When wiretap and surveillance systems are compromised, ongoing investigations could be jeopardized. Sensitive information might be leaked, or worse, manipulated to mislead investigators. This could delay justice or lead to wrongful convictions.
National Security Threats
If foreign actors are involved, as suspected in this case, the breach could pose a significant national security threat. Access to surveillance data might allow adversaries to anticipate and counteract law enforcement actions.
Loss of Public Trust
The FBI is a cornerstone of national security. A breach of this magnitude could erode public trust, leading to skepticism about the agency's ability to protect sensitive information and execute its duties effectively.
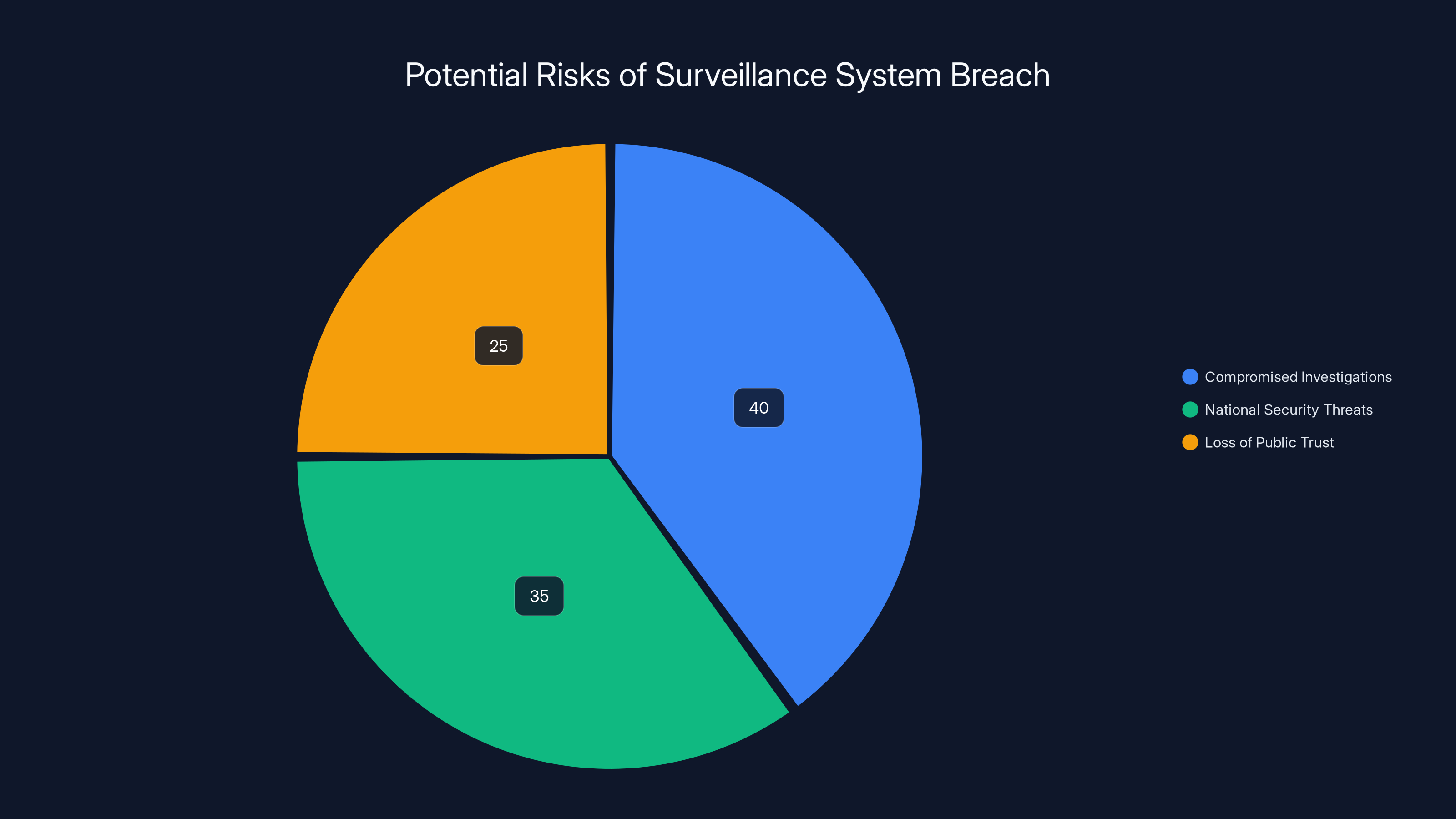
Estimated data shows that compromised investigations account for the largest share of risks (40%), followed by national security threats (35%) and loss of public trust (25%).
Technical Details and Analysis
Understanding the technical aspects of such a breach involves exploring the potential vulnerabilities and attack vectors that could have been exploited.
Common Vulnerabilities in Surveillance Systems
- Outdated Software: Many government systems run on legacy software that lacks modern security features.
- Insufficient Encryption: Weak or improperly implemented encryption protocols can make intercepted data vulnerable to unauthorized access.
- Phishing Attacks: Social engineering attacks targeting personnel to gain access credentials.
- Insider Threats: Disgruntled or compromised employees with access to critical systems.
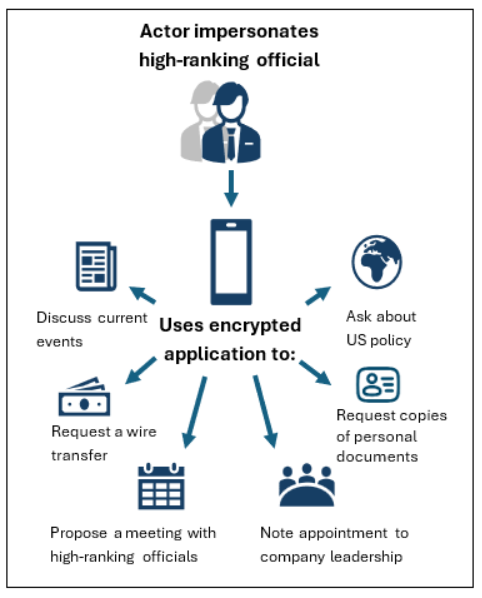
Example Attack Vector: Phishing and Social Engineering
A common method employed by attackers involves phishing campaigns aimed at tricking FBI employees into revealing their credentials. Once inside the network, attackers can plant malware or exploit vulnerabilities to gain deeper access.

Best Practices for Securing Sensitive Systems
Securing systems as critical as those used for wiretapping and surveillance requires a multi-layered approach. Here are some best practices:
- Regular Software Updates: Ensure all systems run the latest software versions with patched vulnerabilities.
- Advanced Encryption Standards: Implement robust encryption protocols for all data at rest and in transit.
- Comprehensive Employee Training: Educate staff about phishing and social engineering tactics.
- Zero Trust Architecture: Adopt a zero trust model where verification is required at every step.
- AI-Driven Threat Detection: Utilize AI to monitor network traffic and identify suspicious activities in real-time.
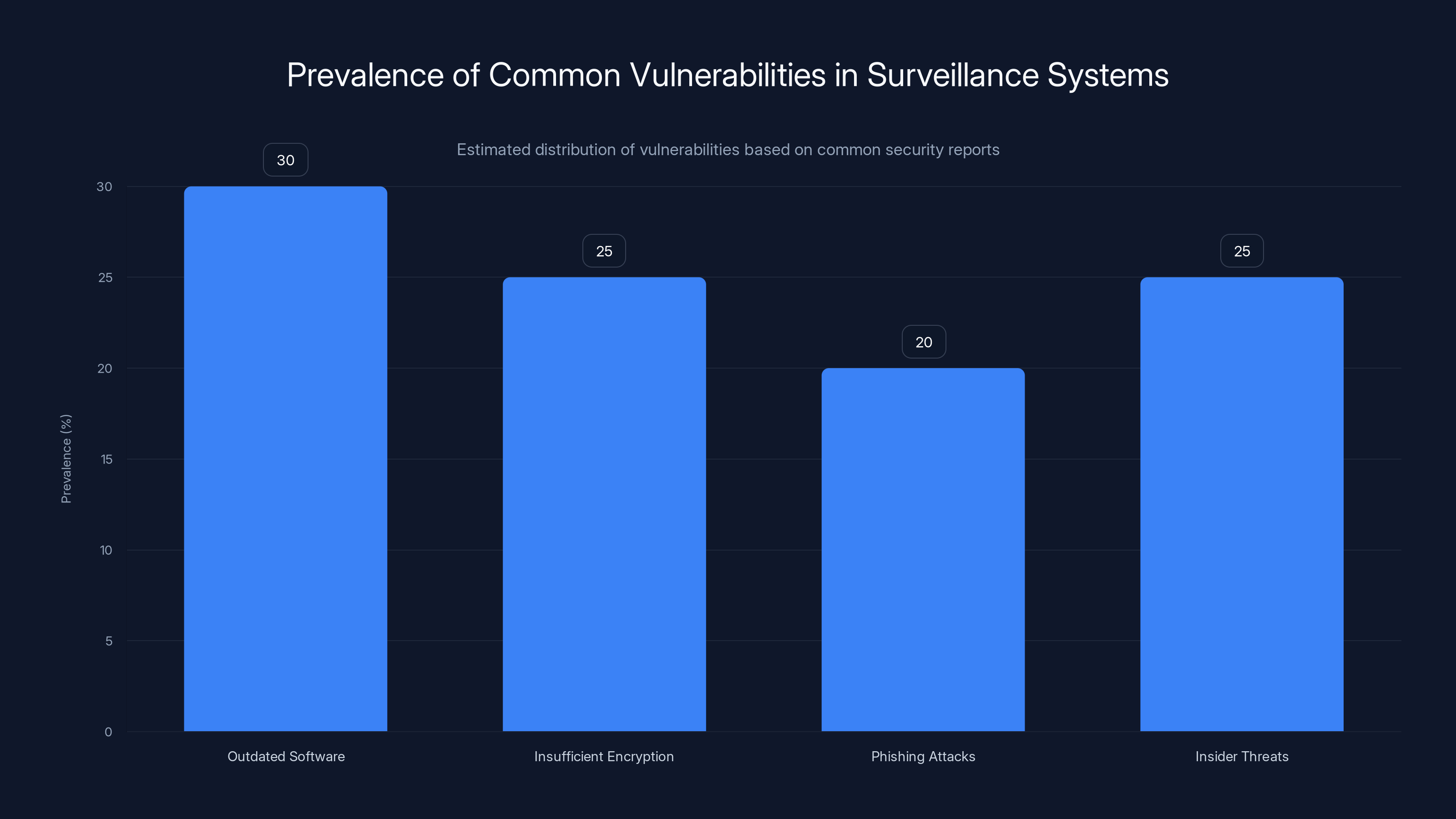
Outdated software and insider threats are estimated to be the most prevalent vulnerabilities in surveillance systems, each accounting for around 25-30% of issues. Estimated data.
Future Trends in Cybersecurity for Government Agencies
The FBI breach underscores the evolving landscape of cybersecurity threats. Here are some anticipated trends and recommendations:
Increased AI Integration
AI technologies are becoming indispensable in cybersecurity. They can process vast amounts of data to detect anomalies that might indicate a breach, allowing for faster response times.
Blockchain for Data Integrity
Blockchain technology could be employed to ensure the integrity of logs and data. By creating immutable records, any unauthorized changes can be immediately identified.
Quantum Cryptography
As quantum computing becomes more prevalent, traditional encryption methods may become obsolete. Government agencies will need to adopt quantum cryptography to protect sensitive data.
Collaborative Defense Strategies
The interconnected nature of cyber threats means that no single entity can defend against them alone. Collaborative efforts between government agencies, private sectors, and international partners will be crucial.

Conclusion
The reported breach of the FBI's wiretap and surveillance systems highlights the critical need for robust cybersecurity measures in protecting national security interests. Moving forward, it will be essential for government agencies to adopt cutting-edge technologies and best practices to safeguard sensitive information.

FAQ
What systems were compromised in the FBI breach?
The breach reportedly affected systems used for managing wiretaps and foreign intelligence surveillance, critical components of the FBI's operations.
How did the attackers potentially breach FBI systems?
Attackers may have used phishing and social engineering tactics to gain access credentials, exploiting vulnerabilities in legacy software systems.
What are the implications of such a breach?
Potential implications include compromised investigations, national security threats, and a loss of public trust in the FBI's ability to protect sensitive information.
What best practices can prevent similar breaches?
Implementing regular software updates, advanced encryption standards, comprehensive employee training, and AI-driven threat detection are vital.
How can AI help in cybersecurity?
AI can process large volumes of data to detect anomalies and potential breaches in real-time, allowing for quicker response and mitigation.
What role does blockchain play in cybersecurity?
Blockchain can provide immutable records ensuring data integrity, making it easier to detect unauthorized changes in logs and data.
Why is a collaborative defense strategy important?
Cyber threats often span multiple sectors and jurisdictions, requiring collaborative efforts between government agencies, private sectors, and international partners to effectively counteract them.

Key Takeaways
- A significant breach in FBI systems highlights vulnerabilities in critical national security operations.
- The breach underscores the importance of robust cybersecurity measures and the need for advanced technologies like AI and blockchain.
- Collaborative defense strategies are crucial in addressing the evolving landscape of cybersecurity threats.
- Government agencies must adopt a proactive approach to cybersecurity, integrating best practices and cutting-edge solutions.
- The FBI's response to the breach will likely shape future cybersecurity policies and practices in governmental operations.

Related Articles
- Understanding Phishing Campaigns: How Fake Email Chains Exploit Urgency [2025]
- Understanding the IPVanish VPN Flaw: What It Means for Mac Users [2025]
- Google's 2025 Report on Zero-Day Vulnerabilities: The AI Impact [2025]
- TriZetto Data Breach: Lessons and Future Implications for Healthcare Security [2025]
- Hacking Security Cameras: A New Weapon in Modern Warfare [2025]
- Why Amazon.com is Experiencing Issues and Failing to Load Prices [2025]
![Inside the FBI's Cybersecurity Breach: Unraveling the Hijacking of Wiretaps and Search Warrants [2025]](https://tryrunable.com/blog/inside-the-fbi-s-cybersecurity-breach-unraveling-the-hijacki/image-1-1772811386736.jpg)



