Google's 2025 Report on Zero-Day Vulnerabilities: The AI Impact [2025]
In a world increasingly driven by digital interactions, cybersecurity remains a critical concern. Google's 2025 Threat Intelligence report sheds light on a growing challenge: zero-day vulnerabilities. With 90 zero-day exploits identified and patched last year, the role of AI in shaping both attacks and defenses is more significant than ever. This article explores the intricacies of zero-day vulnerabilities, AI's dual role in cybersecurity, and what it means for the future.
TL; DR
- 90 zero-day vulnerabilities were patched by Google in 2025, highlighting persistent cybersecurity threats.
- AI is accelerating both attack and defense cycles, making cyber threats more dynamic.
- Enterprise systems are increasingly targeted, shifting focus from traditional browser exploits.
- Future trends suggest AI will play a crucial role in both identifying and exploiting vulnerabilities.
- Organizations must adapt by enhancing their AI-driven defenses.
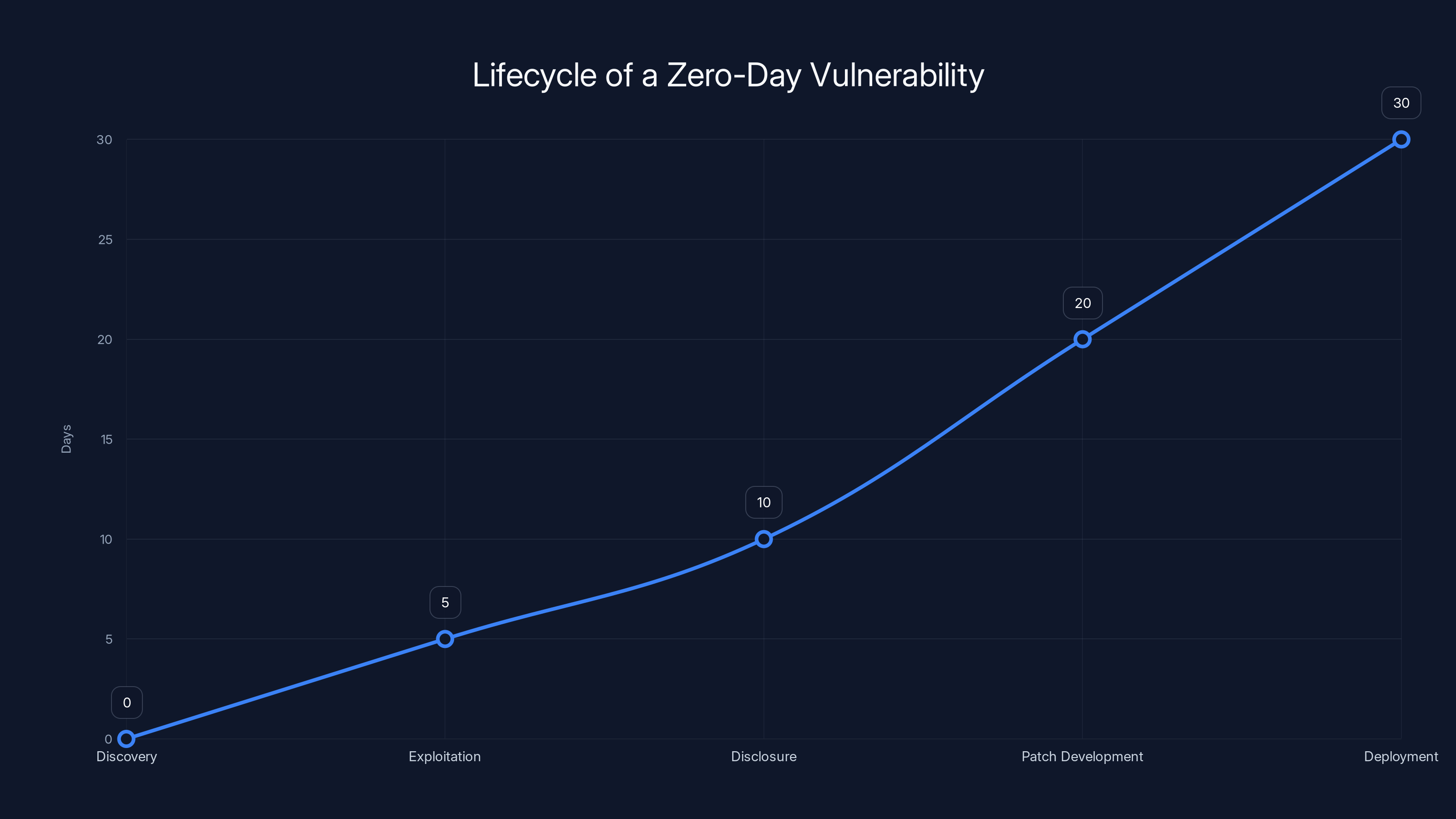
This chart illustrates the estimated timeline of a zero-day vulnerability from discovery to patch deployment. Exploitation often occurs shortly after discovery, with patch deployment taking the longest time. Estimated data.
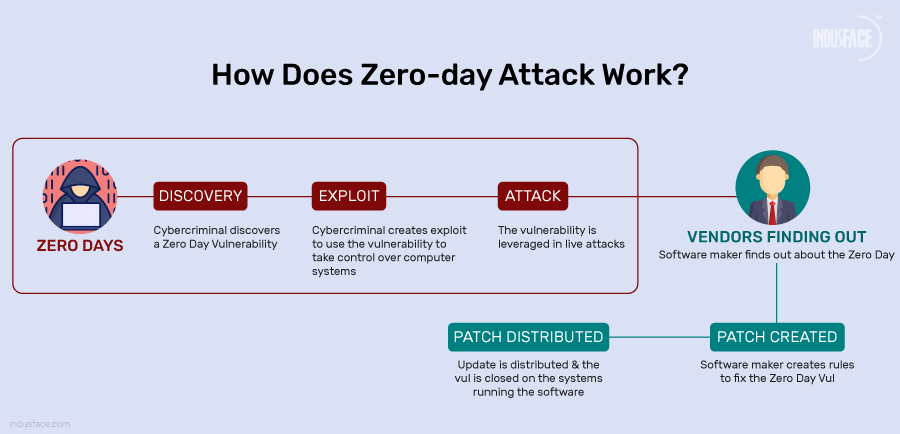
Understanding Zero-Day Vulnerabilities
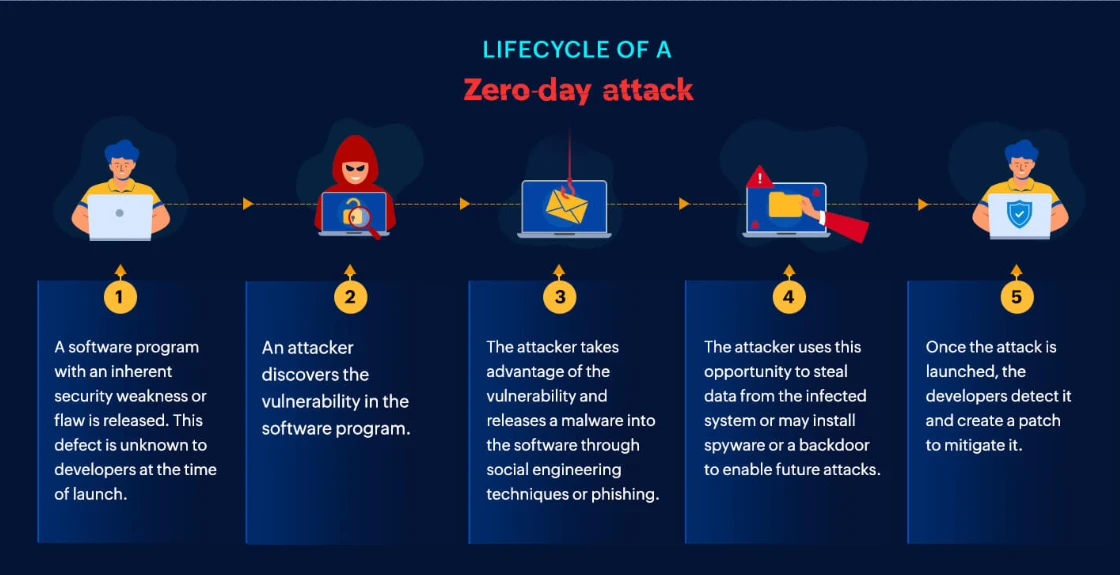
A zero-day vulnerability is a software flaw that is unknown to the vendor and, consequently, lacks a patch at the time of discovery. These vulnerabilities are particularly dangerous because they can be exploited by malicious actors before a fix is available.
Zero-days are prized by attackers because they offer the opportunity to breach systems undetected. The term "zero-day" refers to the fact that developers have had zero days to address the problem before it is exploited.
How Zero-Days are Exploited
Attackers typically leverage zero-day vulnerabilities in a few key ways:
- Phishing Campaigns: By tricking users into downloading malicious software that exploits the zero-day.
- Drive-by Downloads: Where users inadvertently download harmful code simply by visiting a compromised website.
- Direct Attacks: Against specific systems or networks to gain unauthorized access.
The Lifecycle of a Zero-Day
- Discovery: Often discovered by security researchers or hackers.
- Exploitation: Malicious actors exploit the vulnerability.
- Disclosure: The vulnerability is reported to the vendor or becomes public.
- Patch Development: The vendor works on a fix.
- Deployment: The patch is released and applied to affected systems.
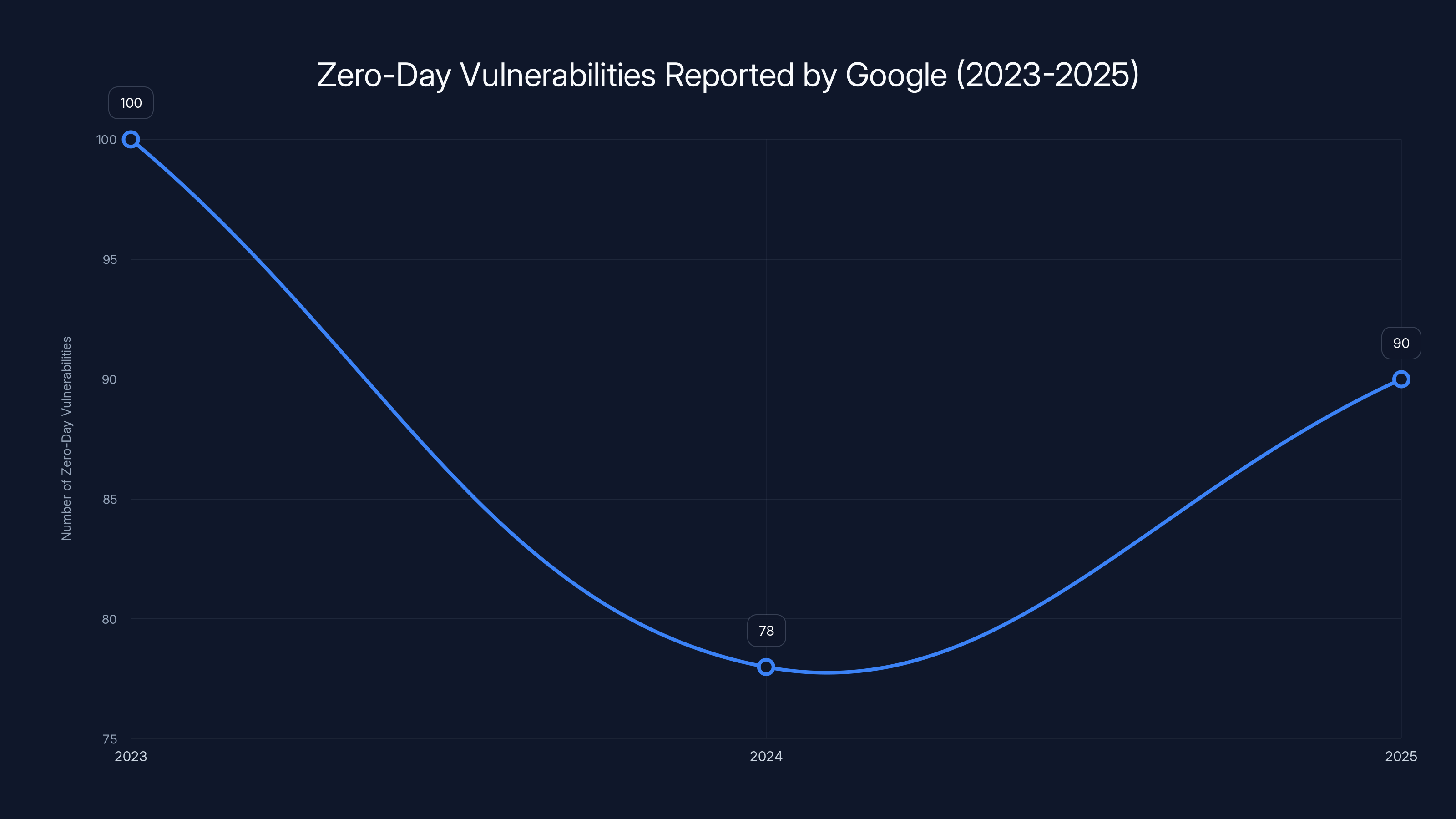
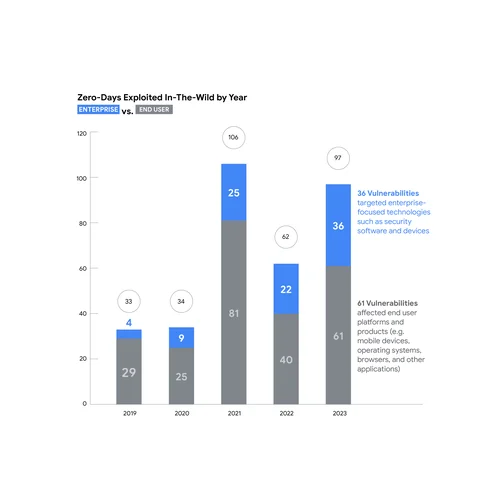
The number of zero-day vulnerabilities reported by Google shows a trend towards stabilization, with a slight decrease from 2023 to 2025. Estimated data.
Google's 2025 Report: Key Findings
Google's Threat Intelligence Group (GTIG) reported 90 zero-day vulnerabilities in 2025. While this number is slightly lower than the 100 reported in 2023, it marks an increase from 2024's 78, suggesting a trend towards stabilization rather than reduction.
Notable Trends
- Increased Targeting of Enterprise Systems: Attackers are shifting focus from traditional browser exploits to enterprise systems, which often hold more valuable data.
- AI in Cybersecurity: AI is being used to both identify vulnerabilities faster and automate attacks, making the threat landscape more dynamic.
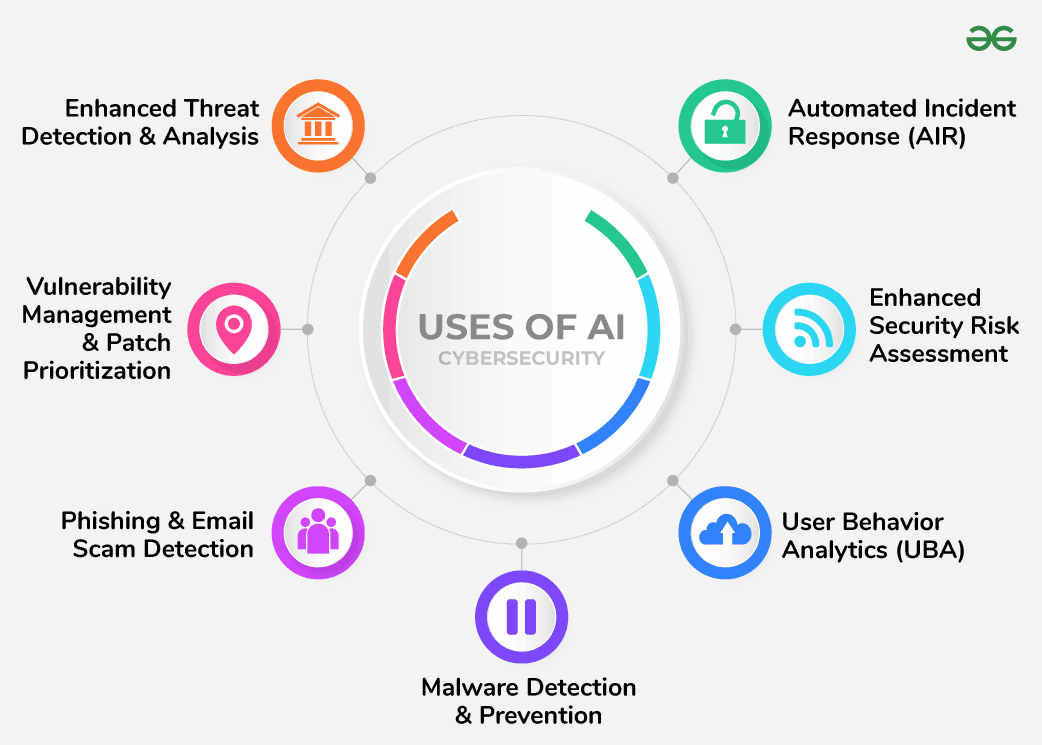
AI's Role in Cybersecurity
AI's involvement in cybersecurity is a double-edged sword. On one hand, AI can help detect and patch vulnerabilities more quickly. On the other, it also enables more sophisticated attack strategies.
AI-Powered Attacks
- Automated Exploitation: AI tools can scan for vulnerabilities and exploit them faster than human hackers.
- Adaptive Malware: AI allows malware to adapt to different environments, making it harder to detect and neutralize.
AI-Driven Defense
- Predictive Analytics: AI can predict potential vulnerabilities by analyzing patterns and trends in data.
- Anomaly Detection: AI systems can detect unusual patterns that might indicate a breach.
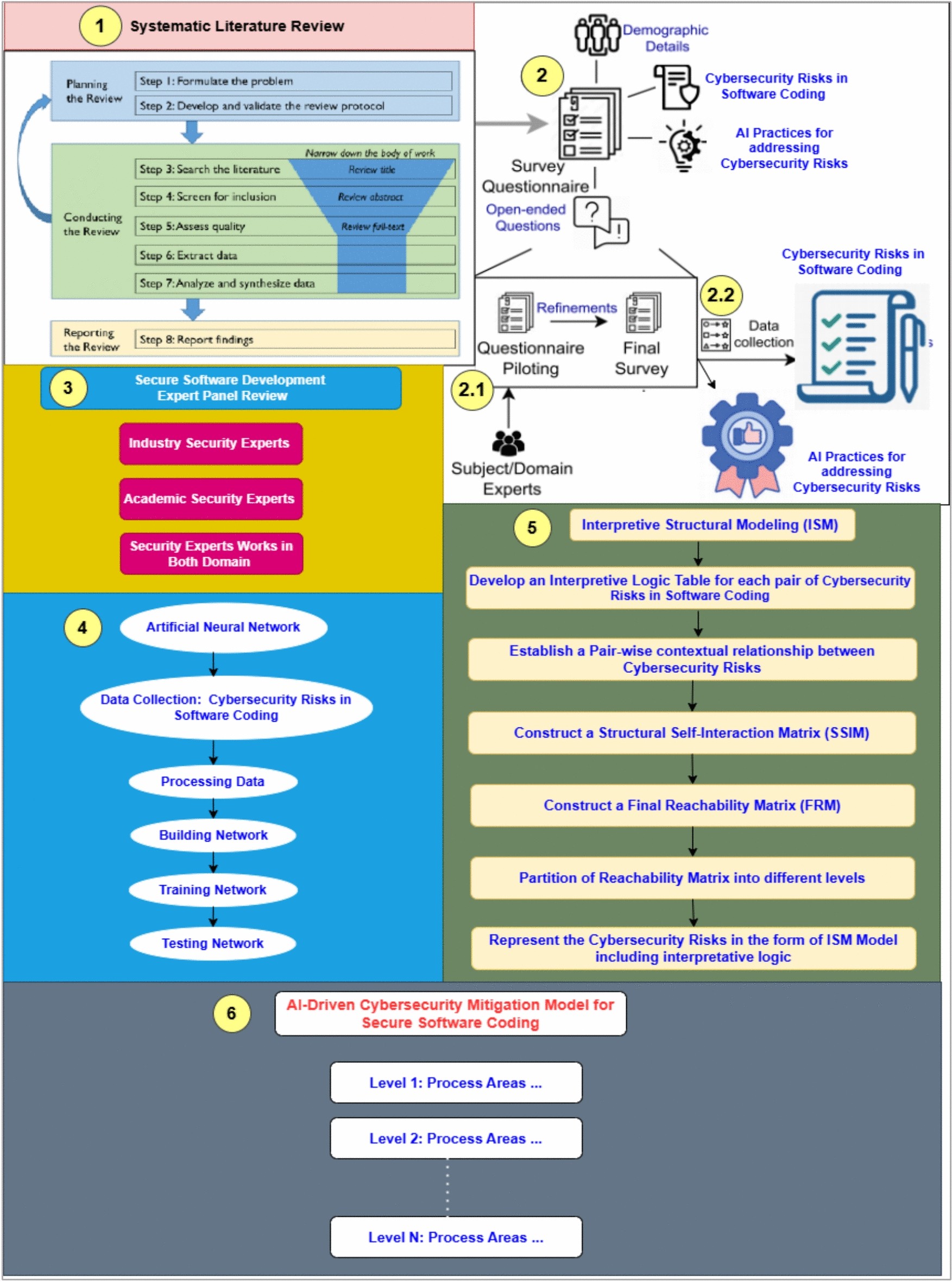
Practical Implementation Guides
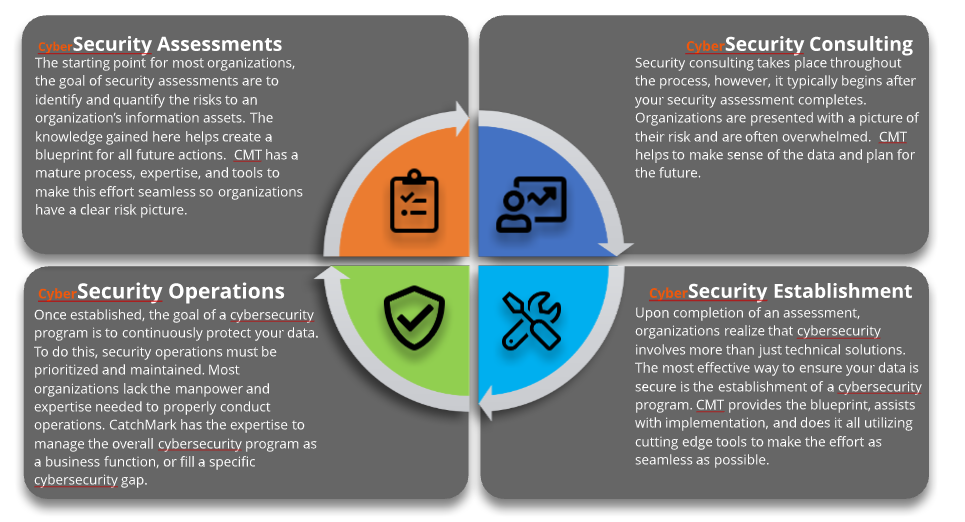
Strengthening Cyber Defenses with AI
Organizations can leverage AI to bolster their cybersecurity measures in several ways:
- Deploy AI-Driven Monitoring Tools: Use AI to continuously monitor network traffic and flag anomalies.
- Implement Machine Learning Algorithms: These can learn from past incidents to predict and prevent future threats.
- Regularly Update AI Models: Ensure that AI systems are updated with the latest threat intelligence.
Best Practices for Cybersecurity
- Patch Management: Regularly update all software and systems to close known vulnerabilities.
- Security Training: Educate employees about phishing and other common attack vectors.
- Access Controls: Limit access to sensitive data and systems to only those who need it.
- Incident Response: Develop a clear plan for responding to breaches.
By 2025, AI-powered cybersecurity solutions are projected to account for over 50% of the global market, indicating a significant shift towards AI integration in threat management. Estimated data.
Common Pitfalls and Solutions
Over-Reliance on Technology
While technology is crucial, over-reliance can lead to complacency. It's essential to maintain a balance between technology and human oversight.
Solution
- Regular Audits: Conduct regular security audits to identify and address any gaps in defenses.
- Human Oversight: Ensure that human experts regularly review AI-driven security measures and incidents.
Ignoring Insider Threats
Not all threats come from external actors. Insider threats, whether malicious or accidental, can be just as damaging.
Solution
- Behavioral Analytics: Implement systems to monitor for unusual behavior by insiders.
- Strict Access Control: Limit data access based on an employee's role and responsibilities.
Future Trends and Recommendations
The Evolving Threat Landscape
As AI technology advances, so too will the sophistication of cyber threats. Here are some trends and recommendations for staying ahead:
- AI-Enhanced Security Protocols: Develop protocols that leverage AI to predict and neutralize threats before they materialize.
- Collaborative Intelligence: Encourage collaboration between AI systems and human experts to enhance threat detection and response.
Building a Resilient Cybersecurity Framework
- Integrate AI with Traditional Methods: Use AI as a complement to, not a replacement for, traditional cybersecurity measures.
- Continuous Learning: Ensure that cybersecurity systems continuously learn from new threats and adapt accordingly.
Conclusion
Google's 2025 report on zero-day vulnerabilities underscores the evolving nature of cybersecurity threats. As AI continues to change the game, organizations must adapt by enhancing their defenses with both AI-driven and traditional methods. By understanding the dual role of AI in cybersecurity, companies can better prepare for the future.
FAQ
What is a zero-day vulnerability?
A zero-day vulnerability is a software flaw unknown to the vendor, which means there is no patch available at the time of its discovery. It poses significant risks as attackers can exploit it before it's fixed.
How does AI influence cybersecurity?
AI influences cybersecurity by both enhancing defensive measures through predictive analytics and anomaly detection, and by enabling more sophisticated attack strategies through automation and adaptation.
What are the benefits of using AI in cybersecurity?
Benefits include faster threat detection, predictive analytics for potential vulnerabilities, and improved incident response times.
How can organizations protect against zero-day vulnerabilities?
Organizations can protect against zero-day vulnerabilities by implementing robust patch management, deploying AI-driven monitoring tools, and conducting regular security audits.
What role do employees play in cybersecurity?
Employees play a crucial role in cybersecurity as they are often the first line of defense. Providing regular training on phishing and other common threats is essential.
How should companies prepare for future cyber threats?
Companies should prepare by adopting AI-enhanced security protocols, encouraging collaboration between humans and AI, and ensuring their security frameworks are resilient and adaptable.
Key Takeaways
- Google patched 90 zero-day vulnerabilities in 2025.
- AI accelerates both cyber attacks and defenses.
- Enterprise systems are increasingly targeted over browsers.
- AI will play a crucial role in future cybersecurity.
- Organizations must enhance AI-driven defenses.
- Zero-day exploits remain a significant threat.
Related Articles
- Understanding and Mitigating the Cisco Catalyst SD-WAN Vulnerability [2025]
- Understanding Phishing Campaigns: How Fake Email Chains Exploit Urgency [2025]
- Understanding the IPVanish VPN Flaw: What It Means for Mac Users [2025]
- The Rise and Fall of Tycoon 2FA: Lessons from a Global Phishing Takedown [2025]
- LexisNexis Data Breach: What You Need to Know [2025]
- Hackers Are Turning to Easy, Fast AI Solutions to Roll Out Attacks: How to Keep Your Business Safe [2025]
![Google's 2025 Report on Zero-Day Vulnerabilities: The AI Impact [2025]](https://tryrunable.com/blog/google-s-2025-report-on-zero-day-vulnerabilities-the-ai-impa/image-1-1772807896912.jpg)



