Understanding Phishing Campaigns: How Fake Email Chains Exploit Urgency [2025]
Phishing attacks have been a pervasive threat in the digital world, evolving continuously to trick even the most vigilant users. Recently, LastPass warned about a new type of phishing scam that utilizes fake email chains to spoof account hacking and create urgency. This article delves into how these scams work, how to recognize them, and effective strategies to protect yourself and your organization.
TL; DR
- Phishing campaigns use fake email chains to create a false sense of urgency, tricking users into revealing sensitive information.
- Last Pass's warning highlights the increased sophistication of social engineering tactics.
- Practical defense strategies include training, email filtering, and two-factor authentication.
- Future trends suggest more personalized phishing attacks as AI technology advances.
- Staying informed and vigilant is crucial in mitigating phishing risks.
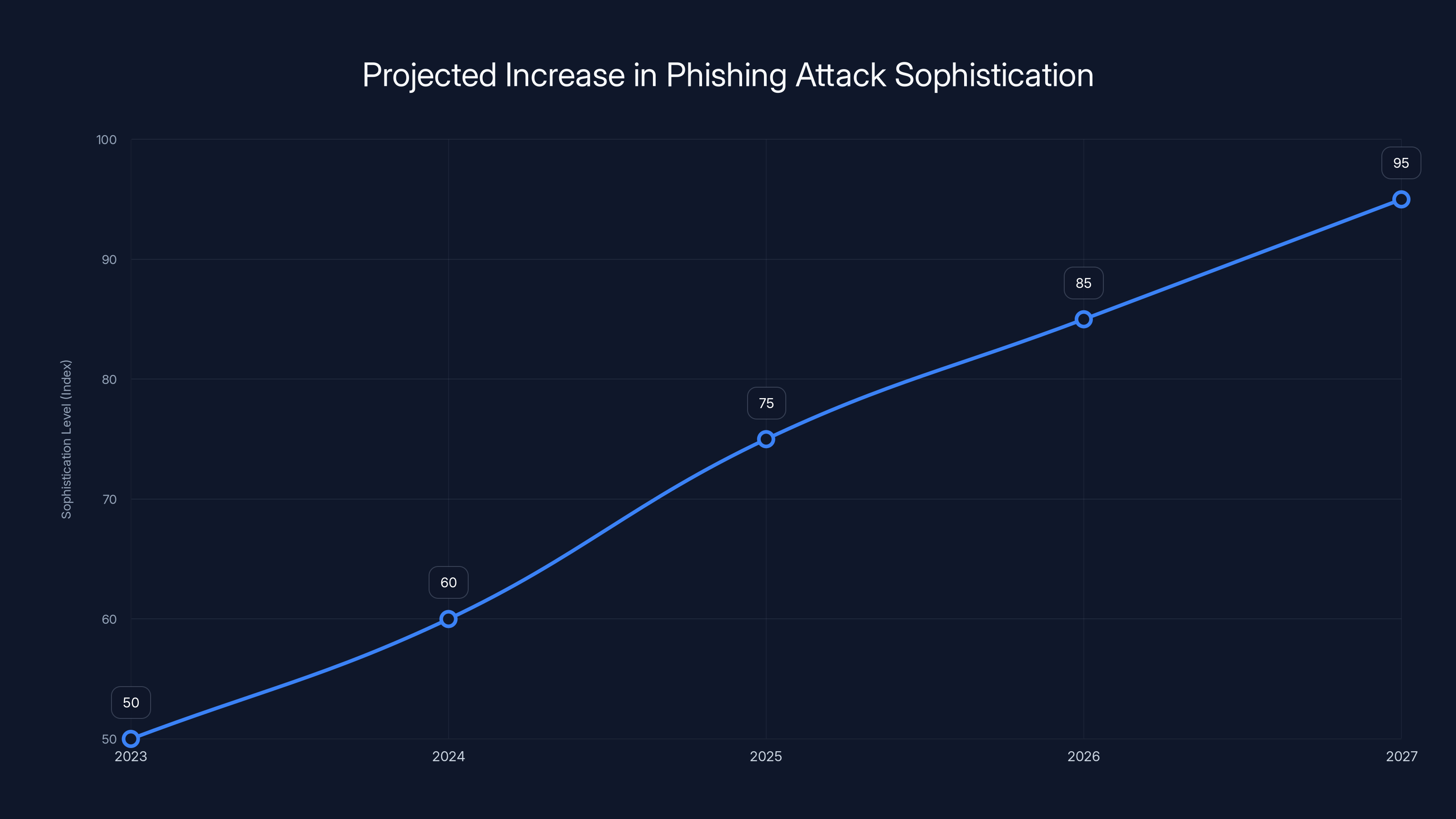
Phishing attacks are projected to become significantly more sophisticated by 2027, driven by AI and multi-vector strategies. Estimated data.
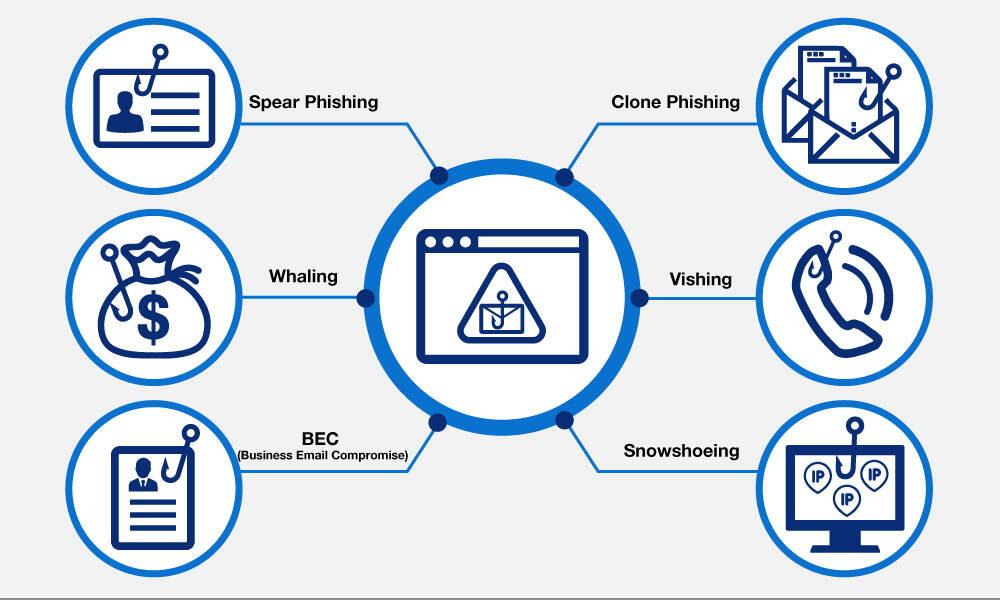
What Are Phishing Attacks?
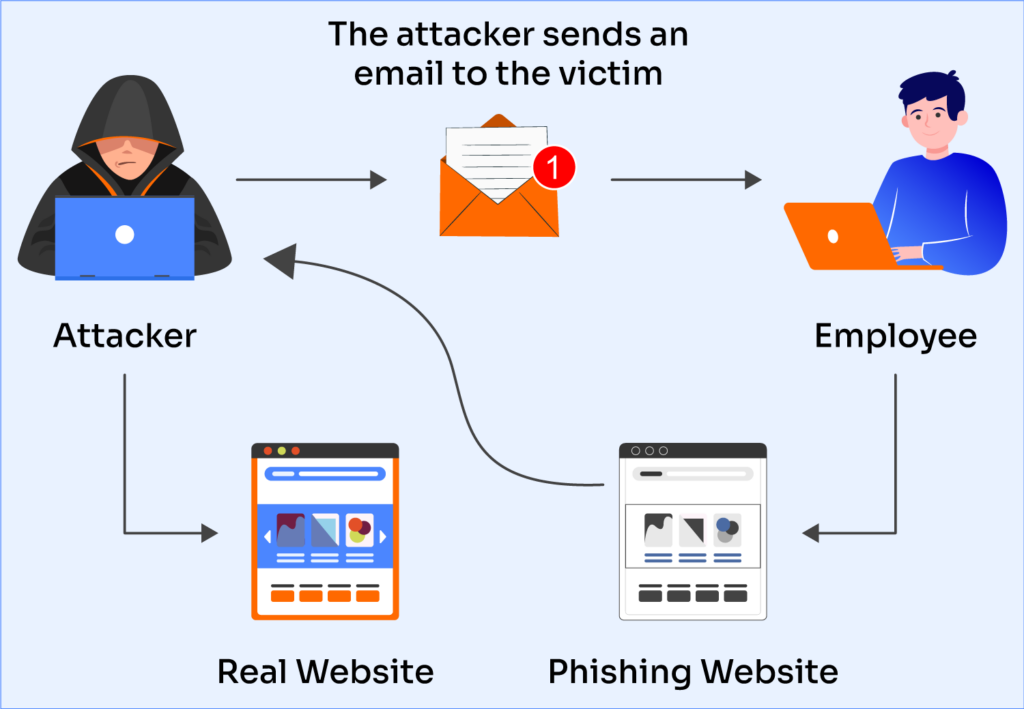
Phishing is a type of cyber attack that involves tricking individuals into revealing sensitive information such as passwords, credit card numbers, or other personal details. Attackers typically masquerade as trustworthy entities in electronic communications, and email is one of the most common vectors for these attacks.
Anatomy of a Phishing Attack
A typical phishing attack involves a deceptive email that appears to be from a legitimate source, such as a bank, a social media platform, or a trusted company like LastPass. The email often contains a sense of urgency, prompting the recipient to take immediate action.
Key Elements of a Phishing Email:
- Sender Spoofing: The email appears to come from a legitimate organization.
- Urgent Language: Phrases like "Your account has been compromised" or "Immediate action required."
- Malicious Links or Attachments: Clicking these can lead to malware installation or credential theft.

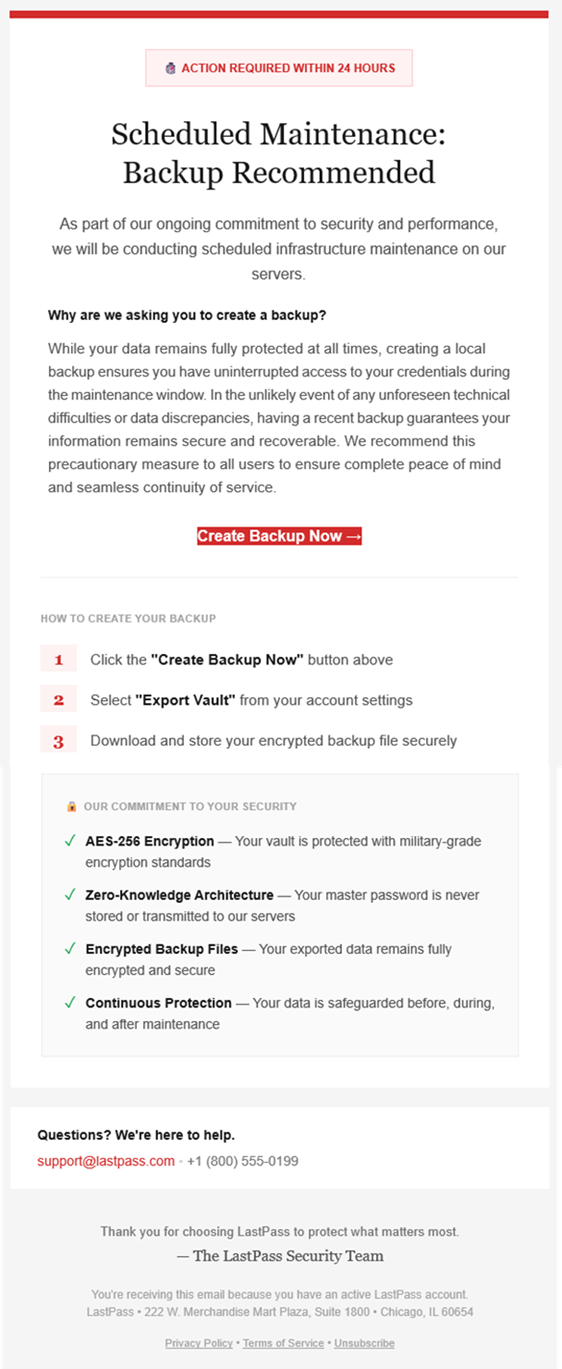
The Last Pass Warning: A New Twist on an Old Trick
LastPass recently highlighted a phishing campaign that uses fake email chains to exploit users' fear of account hacking. The scam positions victims as silent observers to an ongoing attack, making them believe they are uniquely positioned to stop it by acting quickly.
How This Scam Works
- Initial Contact: The victim receives an email purporting to be a part of an ongoing conversation about a security breach.
- Observer Role: The email suggests the victim is merely an observer but can act to prevent further damage.
- Call to Action: The victim is urged to click a link or provide credentials to "secure" their account.

The majority of effort in responding to a phishing attack was dedicated to investigation and recovery, highlighting the importance of thorough analysis and system restoration. Estimated data.
Recognizing Phishing Emails
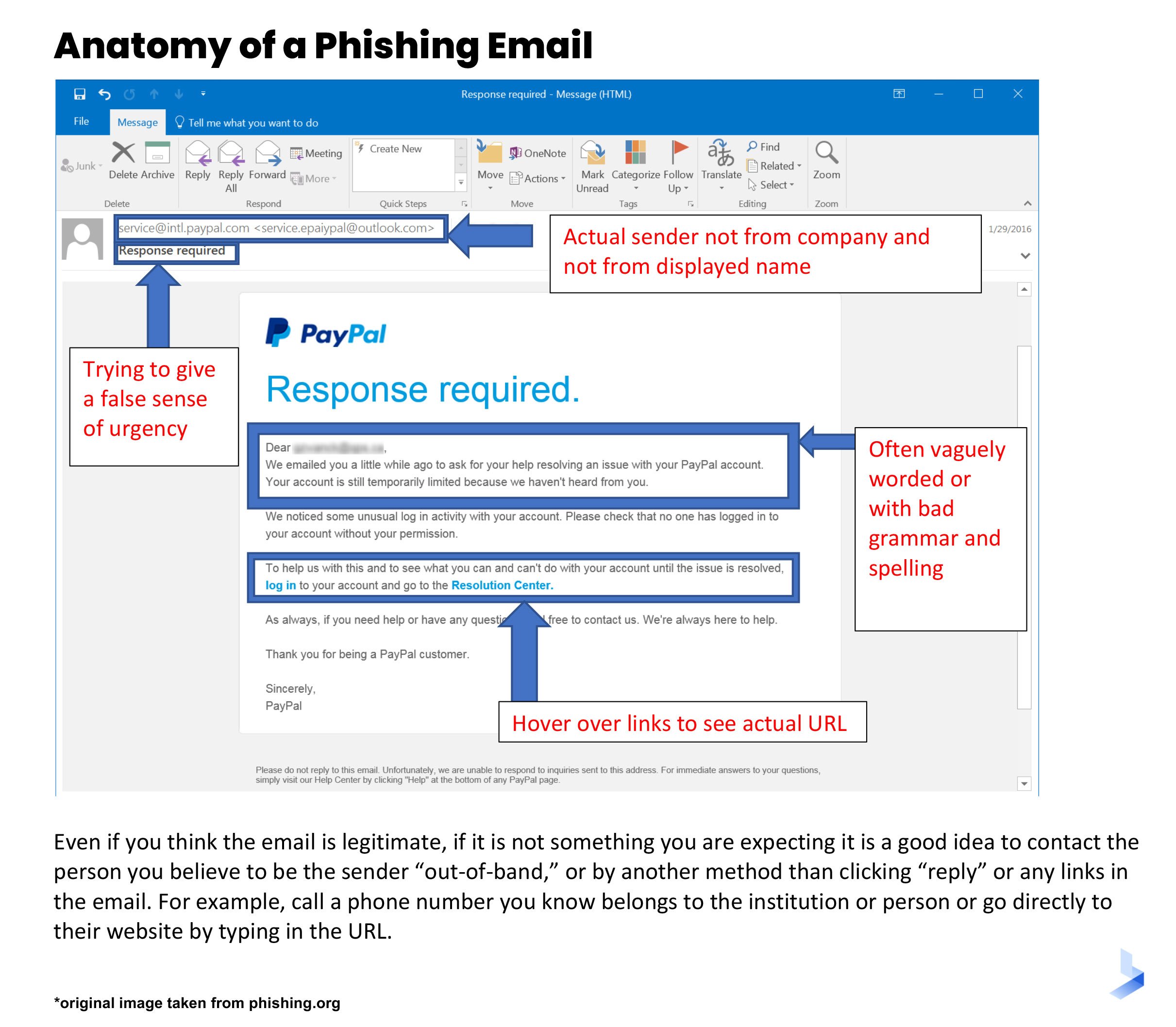
Spotting a phishing email can be challenging, especially as attackers become more sophisticated. However, there are several red flags to watch for:
- Mismatch in Sender's Address: Check if the sender's email address matches the organization's official domain.
- Generic Greetings: Phishing emails often use generic salutations like "Dear User."
- Poor Grammar and Spelling: Many phishing emails contain grammatical errors or awkward phrasing.
- Unusual Requests: Be wary of emails asking for sensitive information or urgent action.
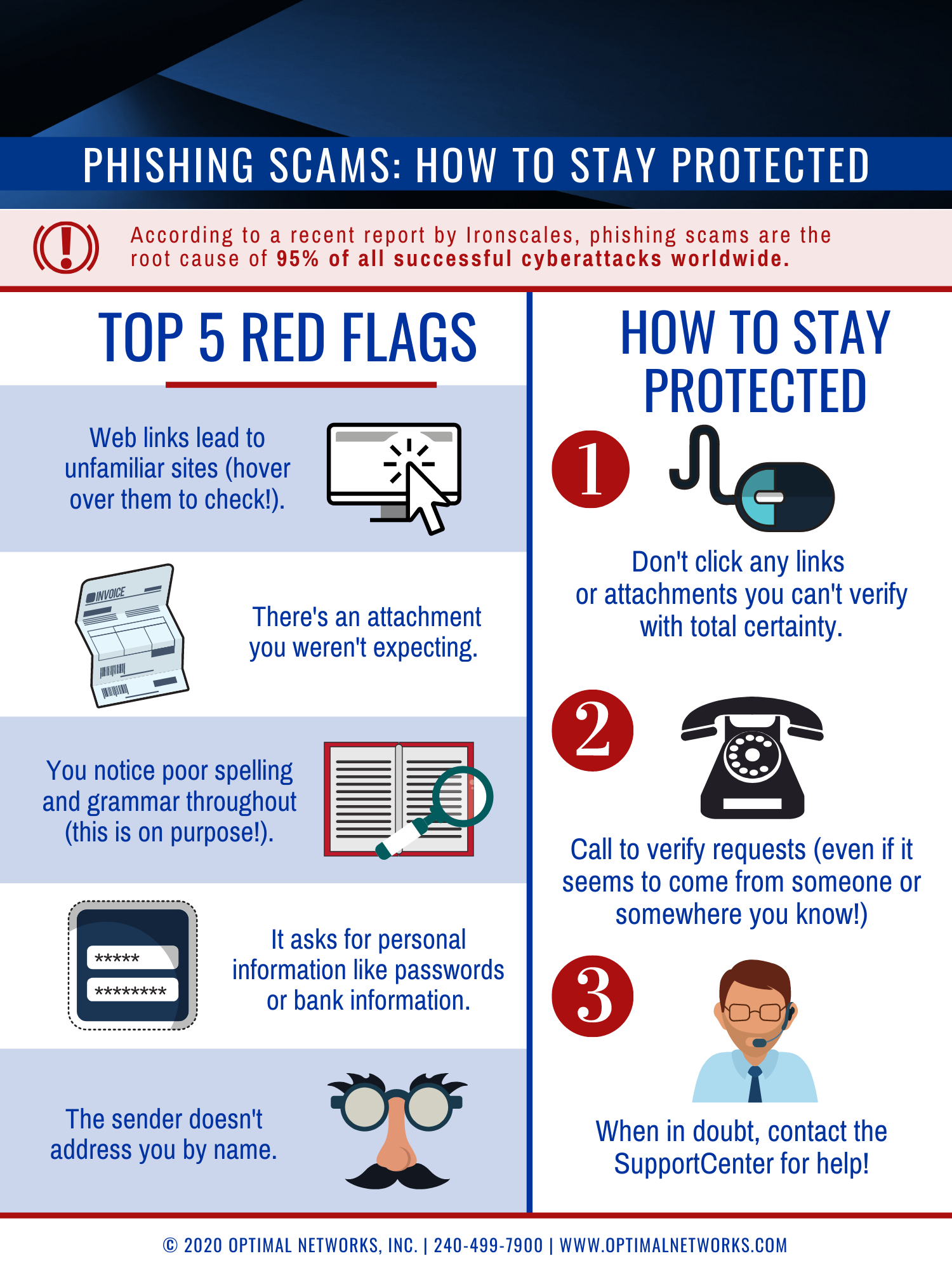
Protecting Yourself from Phishing Scams
Prevention is the best defense against phishing attacks. Here are some strategies to protect yourself and your organization:
Implementing Security Measures
- Email Filtering: Use advanced email filtering solutions to detect and block phishing attempts before they reach users.
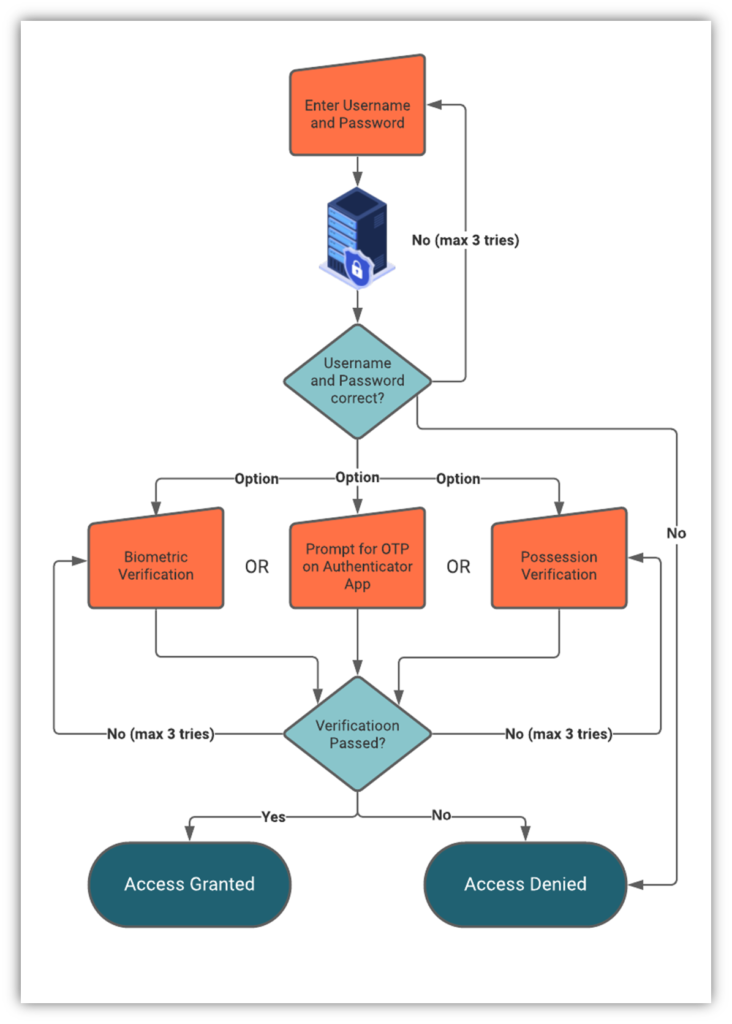
- Two-Factor Authentication (2FA): Enable 2FA on all accounts to add an extra layer of security.
- Regular Software Updates: Ensure all systems and applications are updated to protect against vulnerabilities.
Educating Users and Employees
- Phishing Awareness Training: Conduct regular training sessions to educate users about the latest phishing tactics and how to recognize them.
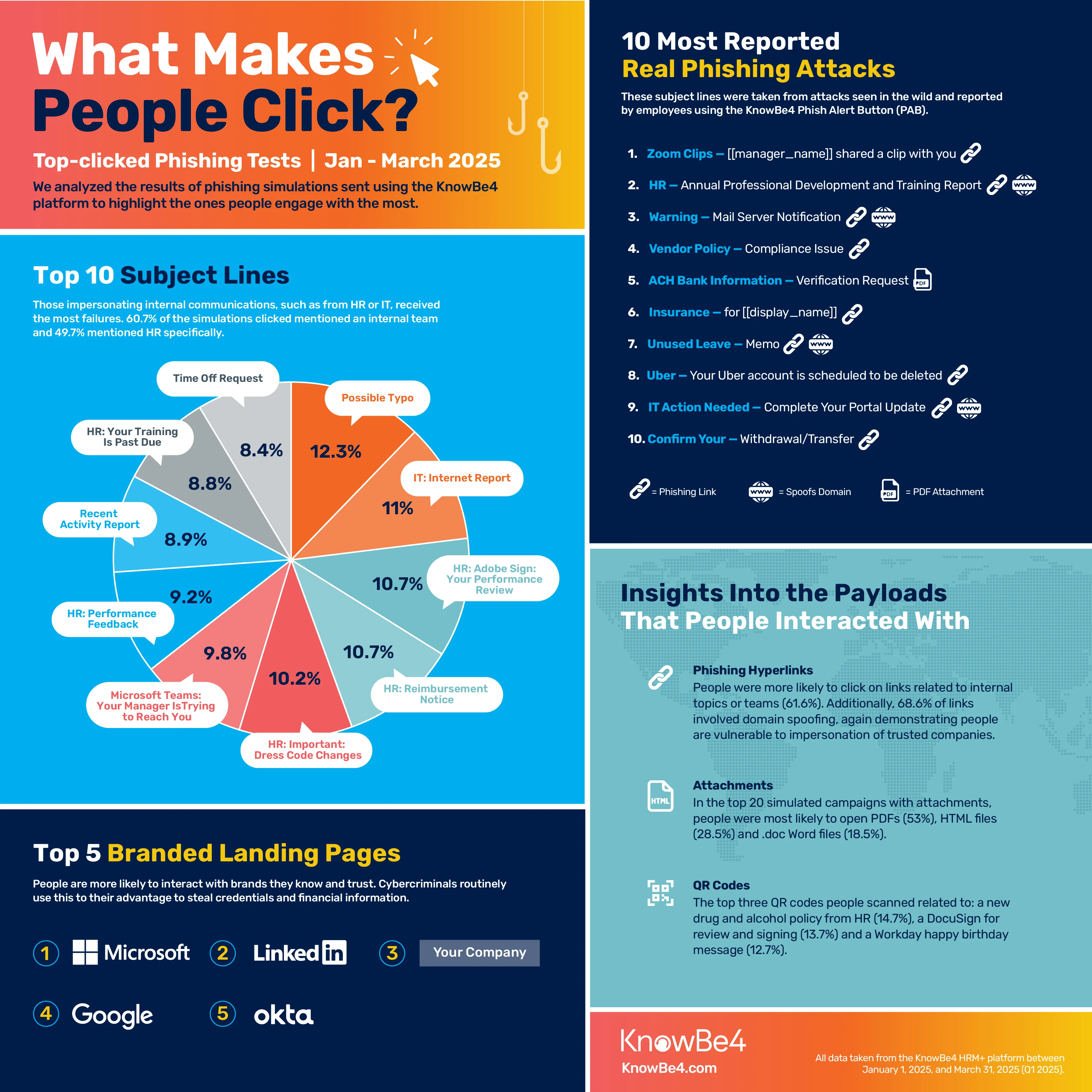
- Simulated Phishing Attacks: Use simulated attacks to test and improve user readiness and response.
Common Pitfalls in Phishing Defense
While many organizations implement basic phishing defenses, there are common pitfalls that can undermine these efforts.
Overreliance on Technology
Relying solely on technological solutions like spam filters can create a false sense of security. Human vigilance is equally important.
Inadequate Training
Training that focuses only on theoretical knowledge without practical exercises may not effectively prepare users for real-world scenarios.

User training and technical controls are estimated to be the most effective strategies in reducing phishing incidents. Estimated data.
Future Trends in Phishing Attacks
As technology advances, phishing attacks are likely to become more sophisticated. Here are some trends to watch:
Use of AI and Machine Learning
Attackers may leverage AI to craft more personalized and convincing phishing emails by analyzing user behavior and preferences. According to Trend Micro, AI can be used to turn public photos into targeted attacks within minutes.
Multi-Vector Attacks
Future phishing campaigns might combine multiple attack vectors, such as email, SMS, and social media, to increase their chances of success.

Best Practices for Organizations
Organizations can adopt several best practices to strengthen their phishing defenses:
- Comprehensive Security Policies: Develop and enforce policies that cover email usage, password management, and incident response.
- Regular Audits and Penetration Testing: Conduct periodic security audits and penetration tests to identify and address vulnerabilities.
- Incident Response Plan: Have a clear plan for responding to phishing incidents, including isolating affected systems and notifying stakeholders.
Real-World Example: A Case Study
Consider the case of a mid-sized company that fell victim to a phishing attack despite having basic email security measures. Here's how they addressed the issue:
- Incident Identification: An employee reported a suspicious email that bypassed the spam filter.
- Immediate Response: The IT team isolated the affected systems to prevent further damage.
- Investigation and Recovery: A thorough investigation revealed that the email contained a malicious link intended to harvest credentials.
- Post-Incident Review: The company implemented additional security measures, including enhanced email filtering and employee training.
Implementing a Phishing Defense Strategy
Developing a comprehensive phishing defense strategy involves several key steps:
Step 1: Risk Assessment
Evaluate the organization's exposure to phishing attacks and identify potential vulnerabilities.
Step 2: Policy Development
Create policies that define acceptable email usage and outline procedures for reporting suspicious emails.
Step 3: Technical Controls
Implement technical controls such as email authentication protocols (e.g., SPF, DKIM, DMARC) to verify the legitimacy of incoming emails.
Step 4: User Training and Awareness
Conduct ongoing training sessions and awareness campaigns to keep employees informed about the latest phishing threats.
Conclusion: Staying Ahead of Phishing Threats
Phishing attacks are a persistent threat, but with the right strategies and vigilance, individuals and organizations can protect themselves. Staying informed about evolving phishing tactics and implementing comprehensive security measures are crucial steps in mitigating these risks.
Use Case: Automate your incident response processes with Runable's AI-powered workflow automation tools.
Try Runable For FreeFAQ
What is phishing?
Phishing is a type of cyber attack where attackers trick individuals into revealing sensitive information by masquerading as trustworthy entities in electronic communications.
How do phishing scams create urgency?
Phishing scams often use urgent language and scenarios, such as fake security alerts or account compromise warnings, to prompt victims to act quickly without verifying the legitimacy of the request.
What are some common signs of a phishing email?
Common signs include mismatched sender addresses, generic greetings, poor grammar, unusual requests, and suspicious links or attachments.
How can organizations protect against phishing attacks?
Organizations can protect against phishing by implementing email filtering, enabling two-factor authentication, conducting regular training, and developing comprehensive security policies.
What should you do if you suspect a phishing email?
Do not click on any links or provide information. Instead, verify the request by contacting the organization directly through official channels.
How are phishing attacks evolving?
Phishing attacks are becoming more sophisticated, with attackers using AI to craft personalized emails and combining multiple attack vectors to increase success rates.
Key Takeaways
- Phishing campaigns exploit urgency to trick users.
- LastPass warns about sophisticated email spoofing.
- AI may lead to more personalized phishing attacks.
- Email filtering and 2FA are critical defenses.
- Awareness training is vital for organizational security.
Related Articles
- The Rise and Fall of Tycoon 2FA: Lessons from a Global Phishing Takedown [2025]
- Understanding the IPVanish VPN Flaw: What It Means for Mac Users [2025]
- LexisNexis Data Breach: What You Need to Know [2025]
- Hacking Security Cameras: A New Weapon in Modern Warfare [2025]
- Why Amazon.com is Experiencing Issues and Failing to Load Prices [2025]
- Secure Your MacBook Neo with This Essential $2.49 Monthly Add-On [2025]
![Understanding Phishing Campaigns: How Fake Email Chains Exploit Urgency [2025]](https://tryrunable.com/blog/understanding-phishing-campaigns-how-fake-email-chains-explo/image-1-1772800731883.jpg)



