N-Day Vulnerabilities: Why Patched Exploits Are Now Your Biggest Security Risk [2025]
Introduction: The Vulnerability Landscape Has Flipped
Here's something that'll probably surprise you: the vulnerabilities you're losing sleep over are likely yesterday's news.
Zero-days. They're the stuff of security nightmares. A vulnerability nobody knows about. No patch. No defense. Attackers have total freedom to exploit systems before anyone even realizes the flaw exists. It's the holy grail of cyber attacks, right?
Wrong.
Turns out, the real threat isn't what you don't know about. It's what you do know about but haven't fixed yet. And the numbers are brutal.
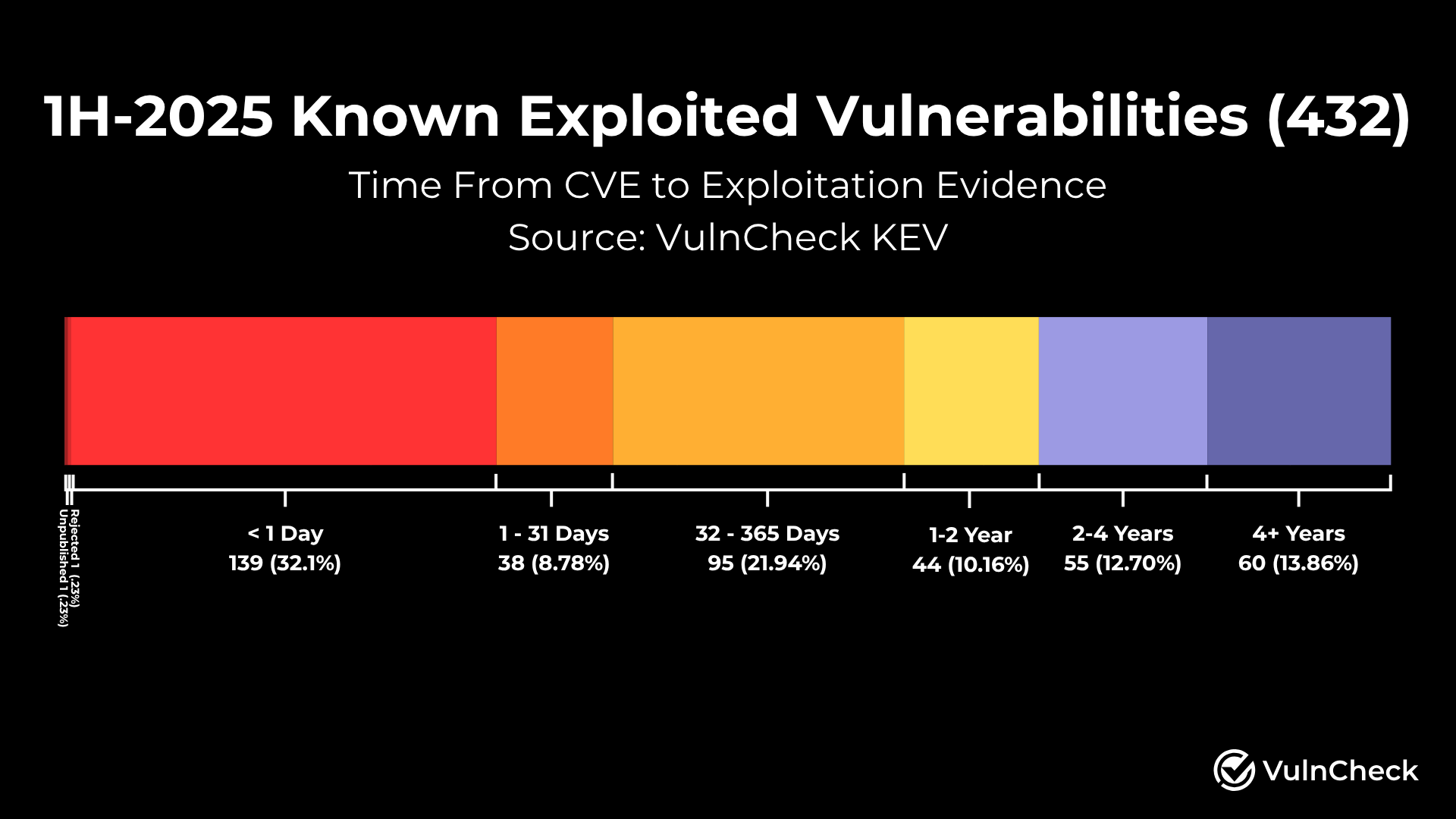
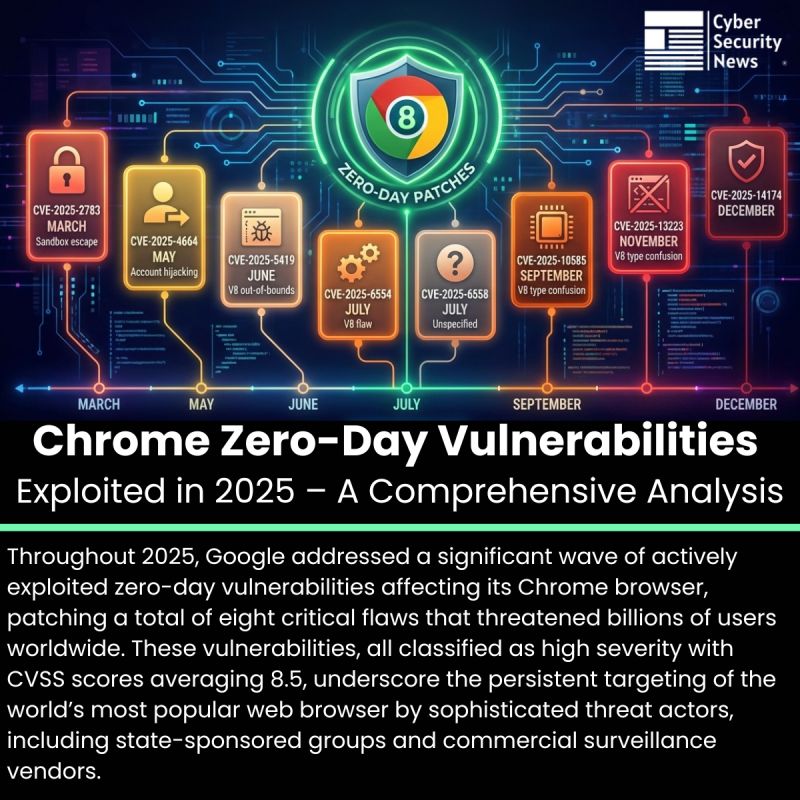
According to recent security research, over 80% of all exploited vulnerabilities are n-days, not zero-days. That's not a small gap. That's a fundamental shift in how attackers operate. And here's where it gets worse: the average time between a vulnerability being publicly disclosed and attackers actively exploiting it? It's collapsed from 745 days in 2018 to just 44 days in 2025.
Let that sink in. Forty-four days. That's six weeks from "the world knows about this flaw" to "attackers are weaponizing it against your systems."
You know what that means for your security posture? It means that old assumption—"we have time to patch"—is dead. Completely dead.
The security industry has been obsessed with zero-days for years. Massive budgets go toward threat detection, vulnerability research programs, and elite security teams hunting for unknown flaws. But while everyone's focused on the unknown threat, attackers are quietly exploiting the known ones. And they're winning.
This shift represents a fundamental change in risk calculation. Organizations can no longer treat patching as something to do "when convenient." It's become an active part of your threat model. Delays aren't just inefficient—they're actively dangerous.
So what exactly are n-day vulnerabilities? Why are attackers suddenly so interested in them? And more importantly, what do you need to do right now to protect your systems?
That's what we're diving into today.
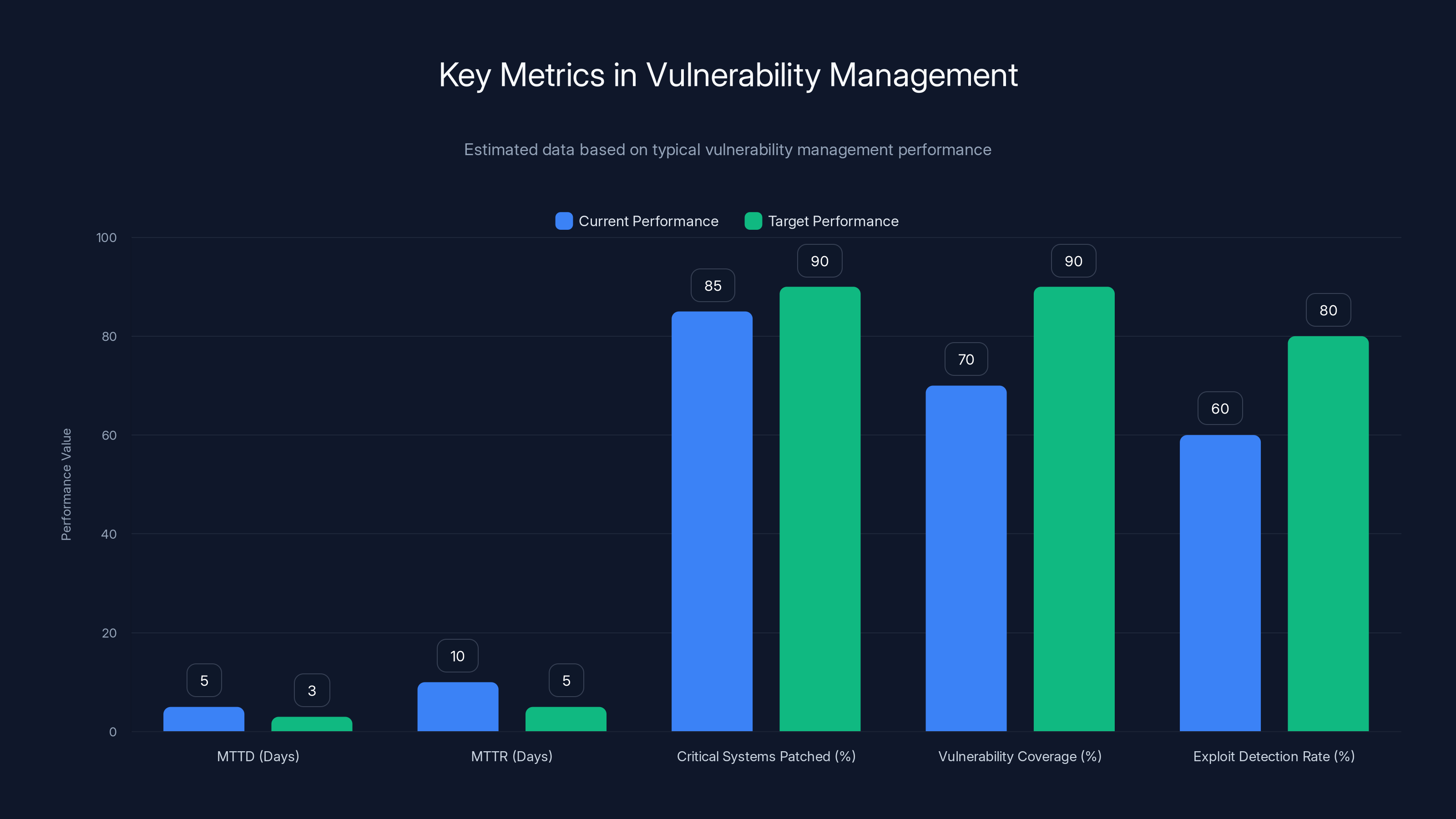
Estimated data shows that improving MTTD and MTTR can significantly enhance vulnerability management. Organizations should aim for higher percentages in critical systems patched and vulnerability coverage.
TL; DR
- N-day vulnerabilities now account for over 80% of exploited flaws, far exceeding zero-day exploitation rates
- Average exploitation time has dropped dramatically from 745 days (2018) to 44 days (2025), creating a narrow patching window
- Firewalls, VPNs, and edge devices are primary targets because they must remain internet-facing and provide initial attack vectors
- Nation-state actors, particularly China, lead exploitation campaigns, using patches to quickly weaponize known flaws
- Patching velocity is now a core security metric, with organizations needing to deploy patches within weeks, not months
- Security teams need to shift from reactive to proactive vulnerability management with real-time monitoring and rapid response protocols
What Are N-Day Vulnerabilities? The Basics Explained
Let's start with terminology because it matters here.
A zero-day vulnerability is a flaw that nobody knows about. Not the vendor. Not security researchers. Not hackers (well, some hackers, but not the general population). The software vendor has "zero days" to fix it because the exploit is already in the wild. By the time they release a patch, the vulnerability has already been weaponized.
An n-day vulnerability is literally the opposite. It's been publicly disclosed. A patch exists (or a workaround does). The information is out there for anyone to find. The vendor has had time to acknowledge it, fix it, and tell users about it. In security terms, an n-day is a vulnerability that someone could patch if they wanted to.
But here's the twist: most organizations don't patch immediately. Some can't patch. Some don't know they need to. Some are waiting for testing environments to clear it. Some have business processes that mean patches happen on quarterly schedules, not when threats emerge.
Attackers have figured this out.
Instead of burning expensive, hard-to-find zero-day exploits, they're monitoring security disclosures. When a new vulnerability drops, they grab the proof-of-concept code (often publicly available on GitHub or in security forums). They start scanning the internet for systems that haven't patched yet. And they attack.
It's like knowing there's an unlocked door in a building. You don't need to find a secret passage. The front door is sitting wide open.
The math is actually pretty straightforward. If an attacker has to spend a year finding a zero-day, or they can find a list of vulnerable systems within weeks after a patch drops, which would they choose? The cost-benefit analysis is completely one-sided.

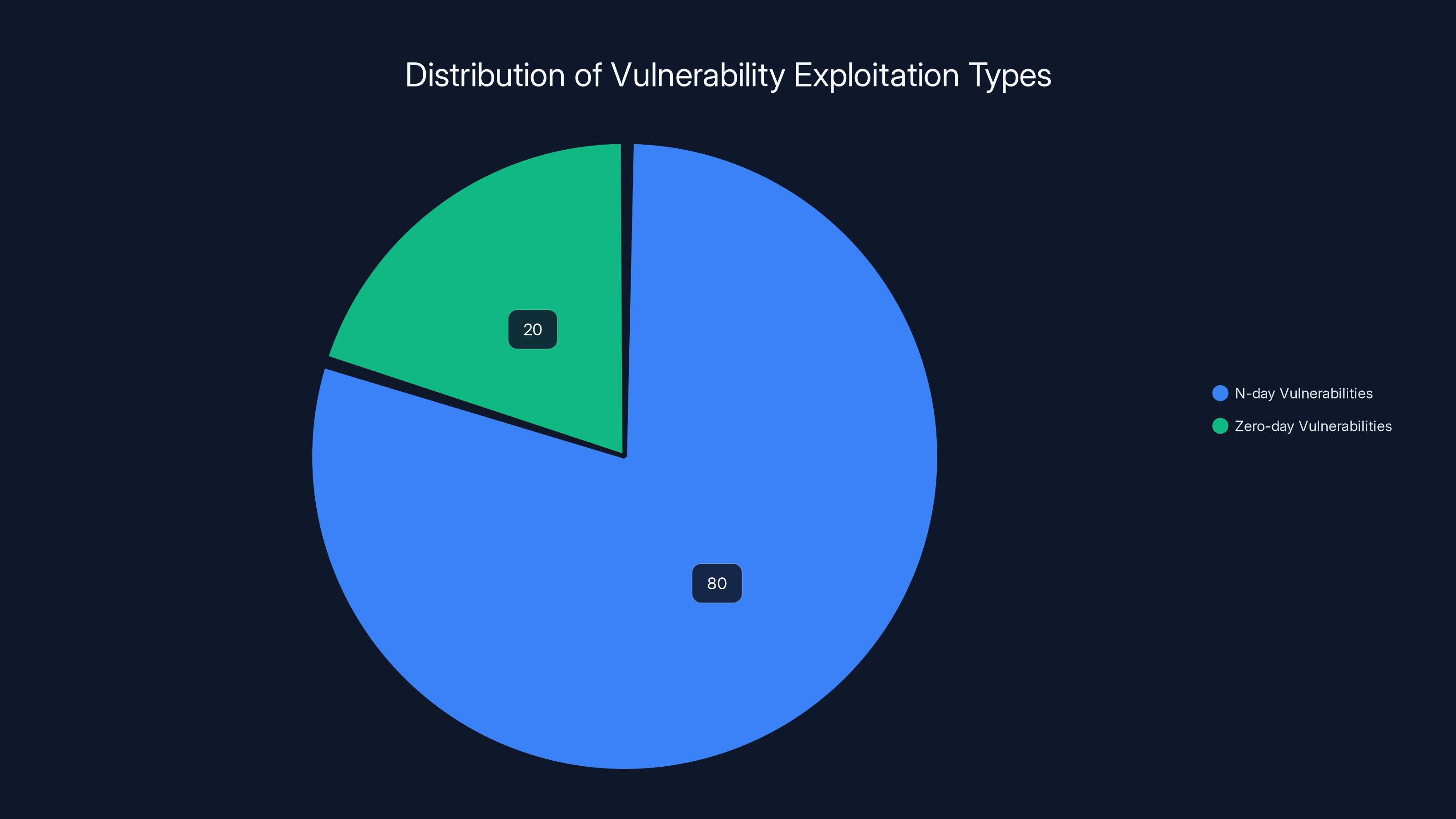
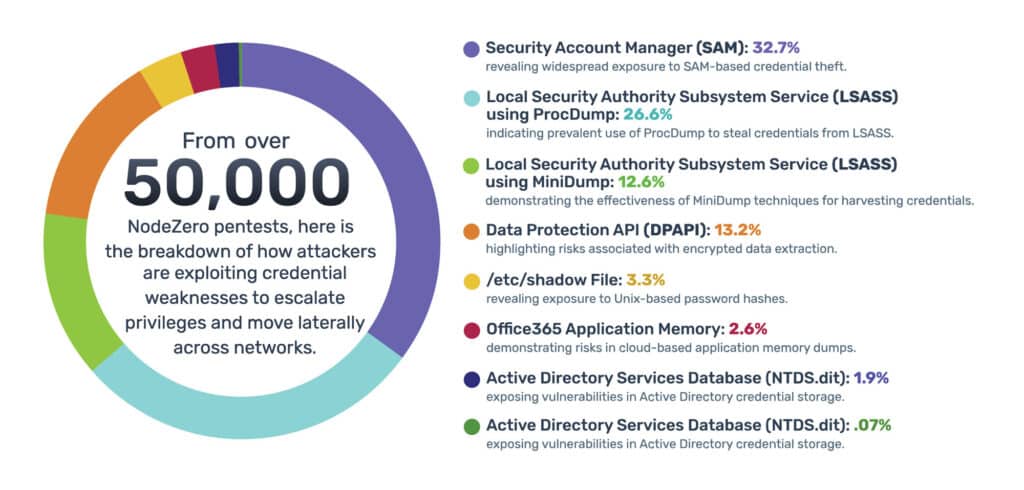
N-day vulnerabilities account for 80% of exploited vulnerabilities, highlighting the need for proactive vulnerability management. Estimated data.
The Timeline Collapse: From 745 Days to 44 Days
This is the scariest number in modern cybersecurity.
Time to Exploit (TTE) measures the gap between when a vulnerability becomes publicly known and when attackers actively exploit it in the wild. It's essentially your patching window. Your grace period.
Back in 2018, that window was enormous. Organizations had roughly 745 days—almost two full years—before they could expect active exploitation. That sounds absurd in retrospect, but it actually made sense. Vulnerabilities were less common. Exploit code wasn't immediately public. Attackers had less infrastructure to scan the internet quickly.
Then things changed.
By 2024, that number had compressed to around 100-120 days. Already concerning. But now we're at 44 days. And the trend isn't slowing down.
Why the collapse? Several factors converge:
Public vulnerability databases are accessible. When a vulnerability gets disclosed, it goes into CISA's Known Exploited Vulnerabilities (KEV) catalog and other public databases. Attackers have automated tools that monitor these databases in real-time. When something new appears, they get an alert.
Proof-of-concept code is freely shared. Security researchers publish working exploits, often on GitHub. Attackers don't need to reverse-engineer anything. The code is ready to use.
Scanning infrastructure is cheap and fast. Tools like Shodan, Censys, and open-source scanners let attackers identify vulnerable systems in hours. They can check millions of IPs quickly. If your system hasn't patched, they'll find it.
Automation is everywhere. Attackers use automated frameworks that can deploy exploits across hundreds of systems simultaneously. It's not a skilled attacker doing surgical strikes anymore. It's industrial-scale exploitation at machine speed.
The result? That comfortable two-year patching window has evaporated. You have about six weeks before your systems become active targets for known flaws.
Why Attackers Prefer N-Days Over Zero-Days
This is the strategic shift that broke the security industry's mental models.
Zero-days have mystique. They cost money. Serious money. A single zero-day exploit kit can cost hundreds of thousands of dollars on dark markets. Nation-states use zero-days as strategic weapons. They're valuable because they're scarce.
But here's what nobody talks about: zero-days are inefficient.
Think about it from an attacker's perspective. You spend a fortune acquiring a zero-day. You use it to breach one system. Maybe two. Once it's used, it's burned. Vendors patch it. Your expensive asset is worthless. The ROI is terrible.
Now compare that to n-day exploitation:
You wait for a patch to drop. It's free intelligence. You get the details of what was broken. You build an exploit or find one that's already been published. You scan for unpatched systems. In 2025, you typically find thousands of them. You attack them all simultaneously with automated tools. Your cost is near-zero. Your return is massive.
It's the difference between spending a million dollars to rob one bank versus getting a key that opens a thousand unlocked doors.
This is why the vulnerability threat model has fundamentally inverted. Patching velocity is now a core competitive intelligence metric. When a vendor releases a patch, it's essentially a roadmap for attackers. They see exactly what was broken. They build exploits. They attack systems that haven't deployed the fix.
Attackers have weaponized the patching process itself.
The Geography of Exploitation: Nation-State Actors Lead the Charge
N-day exploitation isn't random. It's strategic.
Research shows nation-state actors are the primary drivers of n-day exploitation campaigns. They're not trying to steal credit cards or extort Bitcoin. They're engaged in long-term espionage, infrastructure disruption, and geopolitical leverage.
China emerges as the most active nation-state in vulnerability exploitation campaigns. This isn't about criminals opportunistically scanning for vulnerabilities. This is coordinated, funded, state-sponsored activity. Chinese threat groups are running systematic exploitation operations against specific industries and organizations.
Why the focus on n-days for nation-states?
Zero-days are actually worse for strategic actors. If you use a zero-day against a target, you're signaling capability and interest. You're burning a valuable asset. Nations prefer n-days because they're deniable. "We were just using publicly available tools and patches you didn't deploy. Not our problem."
N-days also scale. A nation-state actor can compromise thousands of systems across multiple countries using the same exploit. The scale of impact is much higher.
But here's what's important: if nation-state actors are exploiting n-days, that means criminals are too. What starts with state-sponsored operations quickly trickles down to organized crime groups, ransomware crews, and individual threat actors. The exploits get recycled, reused, and turned into commodities.

Organizations patching critical vulnerabilities within 30 days experience 80% fewer successful cyber attacks compared to those taking 120+ days. Estimated data based on industry insights.
Primary Targets: Firewalls, VPNs, and Edge Devices
Attackers aren't spreading their efforts evenly across all software and hardware.
They're hyper-focused on perimeter security devices: firewalls, VPN gateways, and edge devices. And for a very logical reason: these are the Internet's front door. They have to be exposed to the internet. They can't hide behind other security layers.
For an attacker, compromising a firewall is like getting a master key to the building. Once you're inside the perimeter, you can move laterally, escalate privileges, and establish persistence. You can sit in the network for months undetected.
Compare that to compromising a random workstation. It's useful, but it has limitations. A firewall breach is a game-changer.
This is why attackers have developed a specific targeting strategy:
Stage 1: Firewall/VPN compromise. Scan for common firewall and VPN products with known n-day vulnerabilities. Attack them. Establish a foothold inside the perimeter.
Stage 2: Lateral movement. Once inside, move through the network. Identify high-value targets. Data servers. Active Directory. Backup systems.
Stage 3: Persistence and exfiltration. Install backdoors so you can come back. Extract data or disrupt operations as needed.
The entire strategy hinges on Stage 1 working. And Stage 1 works because so many organizations don't patch their perimeter devices quickly.
Why the delay? Several reasons:
- High availability requirements. Firewalls and VPNs can't go down for patching without interrupting operations
- Business criticality. Any mistake in patching can lock users out or create connectivity issues
- Testing complexity. Patches need to be tested extensively before deployment
- Organizational inertia. Perimeter devices often run on maintenance windows that happen quarterly or even annually
Attackers understand these constraints. They exploit them.
The Patch Management Reality Check
Here's where theory meets practice, and the results aren't pretty.
Most organizations don't have a functional patch management system. They have a patch management process, which is different. Processes take time. Patch management needs velocity.
The typical enterprise patch cycle works like this:
- Vendor releases patch (Day 0)
- Security team identifies patch as important (Day 7-14)
- Patch gets added to testing queue (Day 21)
- Testing environment receives patch (Day 30-45)
- Testing and validation begins (Day 45-75)
- Change approval process (Day 75-90)
- Production deployment begins (Day 90-120)
- Full rollout across all systems (Day 120-180)
By this timeline, you're already at 180 days—well past the 44-day exploitation window.
And this assumes nothing goes wrong. A failed deployment? Testing reveals an issue? An unscheduled maintenance window? You're looking at 200+ days easily.
Some organizations are better than this. Financial institutions and tech companies can patch critical systems in 30-45 days. But they're exceptions.
The median? Probably 120+ days. Which means you're permanently in a state where known vulnerabilities in critical infrastructure aren't patched yet.
This is essentially an open invitation to attackers.
CISA's Known Exploited Vulnerabilities Catalog: A Double-Edged Sword
The Cybersecurity and Infrastructure Security Agency (CISA) maintains a catalog called the Known Exploited Vulnerabilities (KEV) list. It's a public database of vulnerabilities that are actively being exploited in the wild.
The intent is good: give organizations visibility into which vulnerabilities matter most. Help them prioritize patching efforts.
The reality is more complicated.
Yes, the KEV catalog helps defenders. But it also helps attackers. When a vulnerability appears on the KEV list, attackers get official confirmation that:
- The flaw is real and weaponizable
- Exploits are working in the wild
- Organizations are using vulnerable systems that haven't patched yet
- This is a proven attack vector
It's like publishing a list of unlocked doors and expecting people to lock them before attackers show up. Some will. Many won't.
However, the KEV catalog is still valuable for defenders—if you actually use it. Most organizations should:
- Monitor the KEV catalog in real-time
- Cross-reference it with your asset inventory
- Prioritize patching any systems with KEV vulnerabilities
- Deploy patches for KEV items within 30 days
But that requires automation and integration with your vulnerability management system. Many organizations just check it occasionally or not at all.
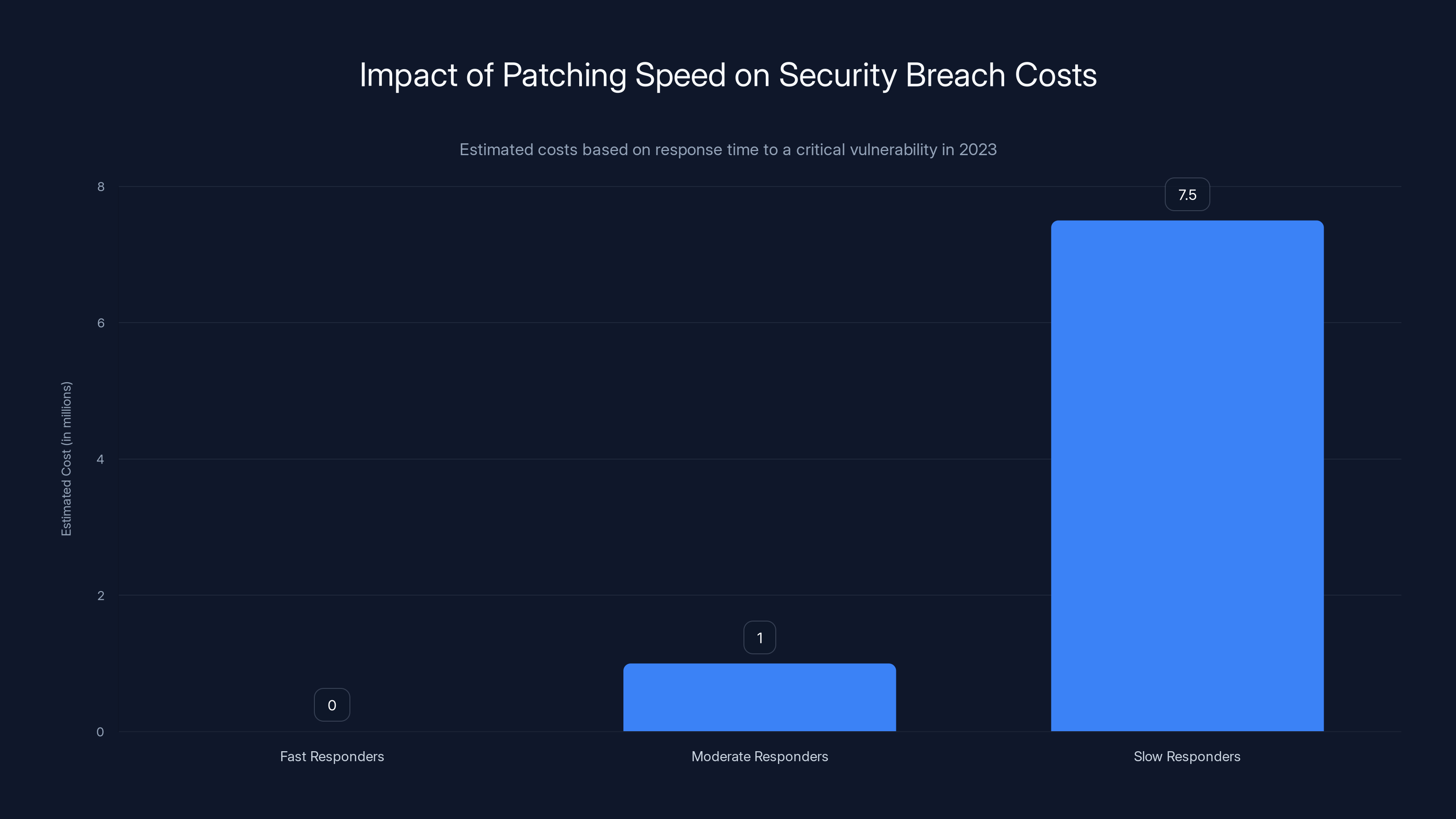
Organizations that patched within 30 days faced no significant costs, while those taking 120+ days incurred estimated costs of $5-10 million. Estimated data based on case study insights.
Why Standard Patch Management Frameworks Are Failing
Traditional IT operations use a defined change management process. Changes go through gates, approvals, testing, documentation. It's careful. It's controlled. It's slow.
This framework was designed for infrastructure that needed high stability. Deploy things carefully. Minimize disruptions. It made sense for a world where vulnerabilities took years to exploit.
That world is gone.
Modern threat timelines require continuous patching, not quarterly patch cycles. They require risk-based prioritization, not sequential deployment. They require parallel testing and production environments, not linear approval gates.
Most organizations are still running the old model. And it's not working.
Think about it:
- If your approval process takes 30 days, you've already used two-thirds of your 44-day exploitation window before production deployment even begins
- If you batch patches into quarterly updates, you're deploying 90 days late by default
- If your testing environment is separate from production and can't mirror real configurations, patches either break production or introduce security gaps
You're playing a game where the rules have changed but everyone's still using the old playbook.
Forward-thinking organizations are implementing:
- Automated patch deployment for critical systems (reducing approval cycles)
- Continuous monitoring for vulnerable systems (identifying gaps instantly)
- Staged rollouts (reducing risk while accelerating deployment)
- Automated testing and validation (speeding up the approval process)
- Real-time patch intelligence feeds (knowing about new exploits immediately)
It's not perfect, but it's dramatically better than the traditional model.
The Role of Automated Exploitation Tools and Frameworks
Here's something that doesn't get discussed enough: the commoditization of exploitation.
Twenty years ago, launching a cyber attack required skilled personnel. You needed reverse engineers, exploit developers, people who understood memory corruption and assembly language.
Now? You need a script.
Public exploit frameworks like Metasploit (maintained by Rapid 7) have democratized exploitation. A script kiddie with zero technical skill can use Metasploit to exploit complex vulnerabilities. The framework handles the complexity. You just point and click.
But there's more. When a vulnerability drops, the security research community often publishes working proof-of-concept code. Sometimes within hours. This code gets added to exploit frameworks. It gets packaged into automated tools. It gets shared on dark web forums.
Within days, what required elite skill now requires a tool. Within weeks, it's fully automated.
This acceleration of tooling is a major reason n-day exploitation has become so prevalent. Attackers don't need to be sophisticated anymore. They need to be organized. Industrial-scale exploitation of n-days doesn't require genius. It requires infrastructure, automation, and patience.
The average organization is still thinking about security in the old model: "We need to protect against sophisticated threats from skilled attackers." But most attacks now are just brute-force automation against known vulnerabilities.
You're not being targeted by sophisticated threat actors (though you might be). You're being scanned by automated tools looking for any low-hanging fruit.
Connecting the Dots: CISA KEV Data and Exploitation Trends
When researchers analyzed exploitation patterns using CISA's KEV data, they uncovered a specific pattern.
Vulnerabilities on the KEV list don't get exploited uniformly. Some get hit within days. Others take weeks. A few stay on the list for months without active exploitation.
What determines the difference?
Accessibility and value. Vulnerabilities in internet-facing systems (firewalls, VPNs, web servers) get exploited quickly. Vulnerabilities in back-end systems take longer. Vulnerabilities in perimeter security get exploited fastest because they're the most valuable.
Ease of exploitation. If an exploit is simple and reliable, it gets weaponized immediately. If it's complex or unreliable, attackers wait for better tools.
Target prevalence. If millions of organizations use the same software, attackers will exploit it. If only thousands use it, there's less incentive.
Actor motivation. Different threat actors have different goals. Ransomware groups want vulnerable systems fast. Spies want specific targets. This changes exploitation timelines.
The data shows that the average vulnerability now goes from public disclosure to active exploitation in 44 days. But that's just the average. Some go much faster. Some go slower. But the trend is unmistakable: the window is shrinking every year.
If current trends continue, we could be looking at 20-30 day exploitation windows within the next few years. That would make traditional patching impossible.
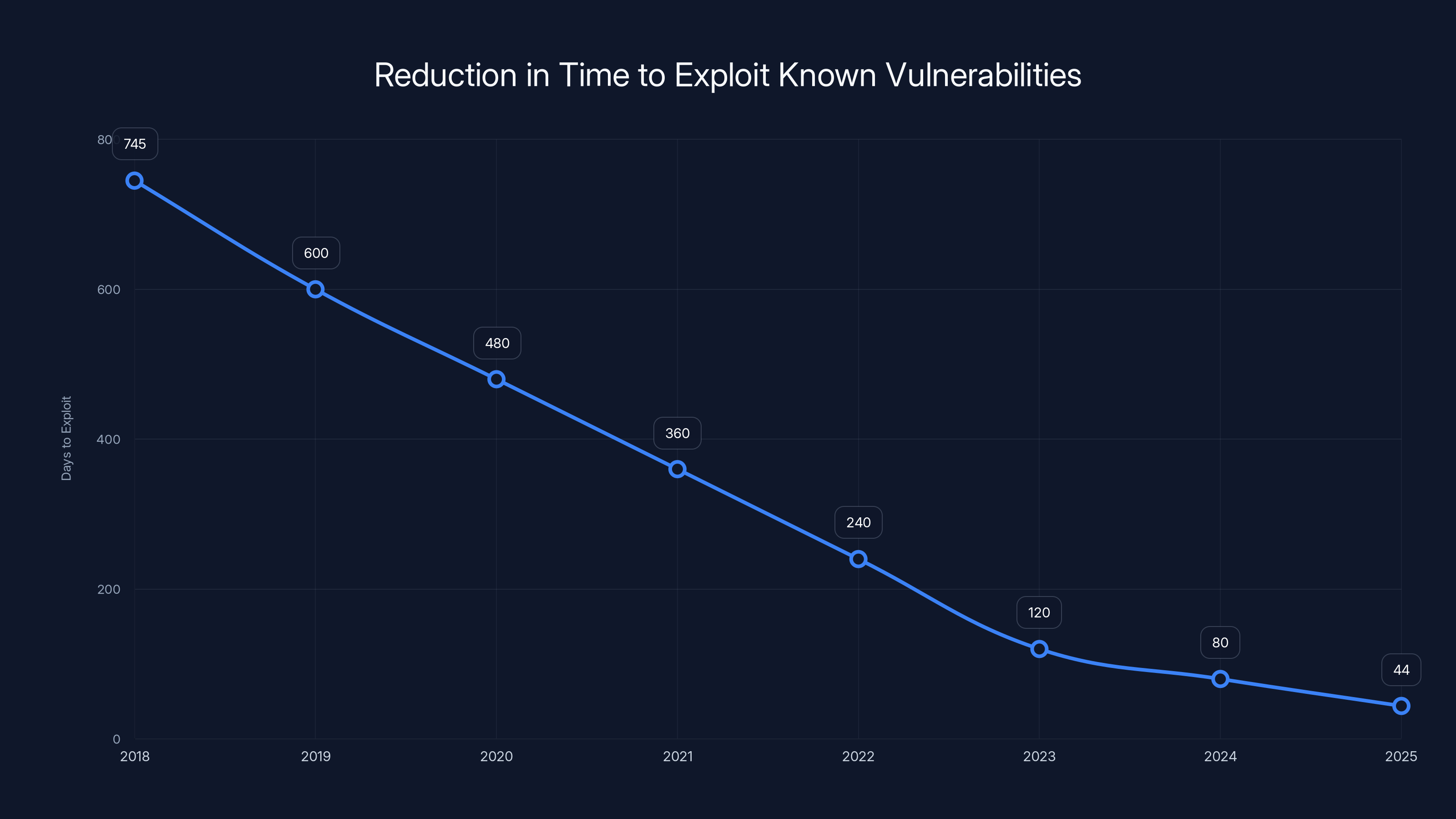
The average time for attackers to exploit known vulnerabilities has drastically decreased from 745 days in 2018 to just 44 days in 2025, highlighting the urgency for timely patching.
Building a Rapid Response Vulnerability Management System
So what do you actually do about this?
The first step is accepting that traditional patch management is obsolete. You can't wait 180 days. You need to compress timelines dramatically.
Here's what a modern vulnerability management system looks like:
Real-time threat intelligence integration. Connect your vulnerability scanner to threat intelligence feeds. When a new exploit appears, you know immediately. When CISA adds something to the KEV list, you get an alert.
Automated asset discovery and tagging. Know exactly what systems you have, where they are, and what they're running. Use automation. No spreadsheets.
Continuous scanning. Don't scan quarterly. Scan continuously. Identify vulnerable systems in real-time.
Risk-based prioritization. Not all vulnerabilities are equal. Prioritize based on asset criticality, exploit availability, and attack likelihood. A firewall with a zero-day is higher priority than a non-critical workstation with a low-severity vulnerability.
Automated remediation where possible. For systems where you can deploy patches automatically, do it. For critical systems, use staged rollouts with automated testing.
Exception management. Sometimes you can't patch immediately. Document why. Track it. Re-assess regularly. Don't let exceptions become the default.
Metrics and visibility. Measure mean time to remediation (MTTR) for critical vulnerabilities. Track what percentage of your infrastructure is patched within 30 days. Make this a board-level metric.
This isn't a one-time project. It's a continuous operating model.
Case Study: The Real Impact of Slow Patching
Let's look at a concrete example of how n-day exploitation actually plays out.
In 2023, a critical vulnerability appeared in a widely-used firewall product. The vendor released a patch quickly. CISA added it to the KEV list within a week. By day 14, active exploitation was documented.
Organizations fell into different response categories:
Fast responders (patched within 30 days): Essentially zero impact. They deployed the patch, their systems were protected, attackers found nothing to exploit.
Moderate responders (patched in 60-90 days): Some attacks detected. Threat teams identified suspicious behavior on the firewall. Incidents occurred but were caught during investigation. Cost: incident response overhead, forensic analysis, some data exposure in limited cases.
Slow responders (patched in 120+ days): Extensive compromise. Attackers got inside the network in week 2-3. They established persistence. By the time the patch was deployed, the attackers were already in deeper network layers. Cost: full breach investigation, network rebuilding, potential data loss, regulatory notification, reputation damage. Some organizations estimated $5-10 million in total incident costs.
The difference between 30-day and 120-day patching wasn't a minor efficiency issue. It was the difference between no impact and catastrophic breach.
And crucially: the breach wasn't because the organization was unsophisticated or negligent. It was because they followed standard IT practices with standard change management timelines. They just weren't fast enough.
Industry-Specific Vulnerabilities and Attack Vectors
N-day exploitation patterns vary by industry.
Financial institutions face attacks through banking infrastructure. VPN and authentication systems are heavily targeted. Even a brief compromise can expose sensitive transactions.
Healthcare systems are targeted through medical devices and patient data systems. Ransomware groups specifically exploit n-days in healthcare IT infrastructure because they know hospitals will pay to restore operations quickly.
Critical infrastructure (power, water, gas) faces nation-state targeting through industrial control systems. The stakes are existential. If infrastructure goes down, lives are at risk.
Technology companies face attacks through development tools and CI/CD infrastructure. If compromised, supply chain attacks become possible.
Manufacturing faces attacks through operational technology. Once compromise is achieved, production can be disrupted or product quality compromised.
The common thread: attackers choose n-day vulnerabilities in systems that are most critical for each industry. They know that these systems are heavily used, internet-facing, and often on outdated patch cycles.
Your industry faces specific threats. Your patch management strategy needs to reflect that.
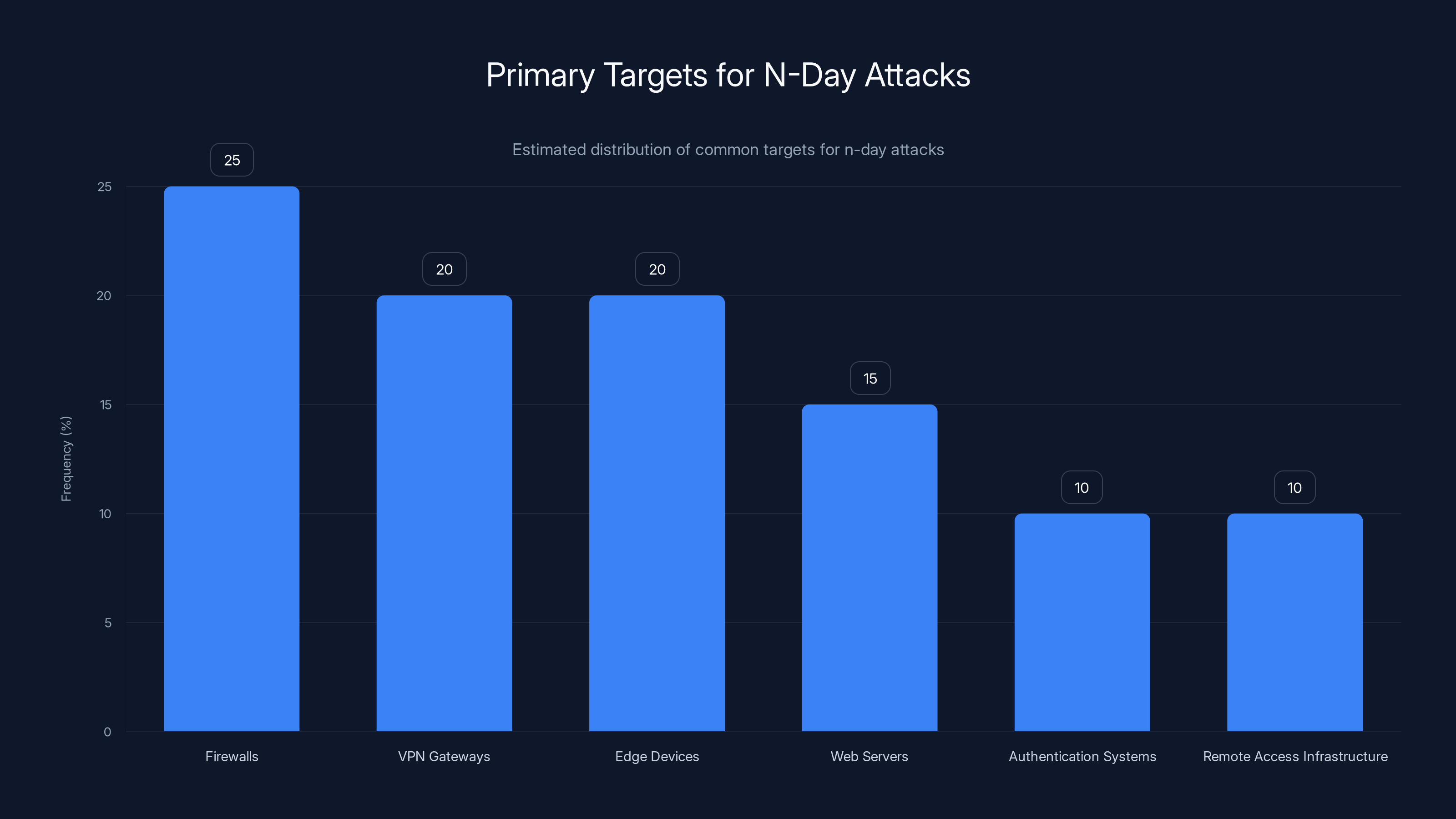
Firewalls, VPN gateways, and edge devices are the primary targets for n-day attacks due to their critical roles in network security. Estimated data based on typical attack patterns.
The Future of N-Day Exploitation: Predictions and Trends
Where is this heading?
If you look at the trend line—TTE dropping from 745 days to 44 days in just six years—the trajectory is troubling.
Exploitation windows will continue to compress. As automation improves and threat infrastructure becomes more sophisticated, I'd expect to see 30-day average exploitation windows within 3-4 years. Some vulnerabilities will be exploited within days.
Vulnerability intelligence will become a commodity. Right now, there's a gap between disclosure and automated weaponization. That gap will close. Within hours of a patch release, automated exploit code will be generated, deployed, and tested at scale.
Zero-days will become less relevant. If attackers can exploit n-days so effectively, the ROI on zero-days becomes questionable. Some high-value targets will still get zero-day attention, but the general trend is toward n-days.
Patching will need to become continuous, not periodic. Quarterly patches are dead. Organizations will need continuous deployment, continuous testing, and continuous validation.
Supply chain attacks will leverage n-days. If an attacker can compromise a software vendor or infrastructure provider through an n-day vulnerability, they can distribute malware to thousands of victims. This is the next escalation.
Detection and prevention will need to shift focus. Since patching can't keep up with exploitation speed, organizations will invest heavily in detection and isolation. The assumption will be: "We'll get compromised through an n-day. How do we detect and contain it?"
The days of "patch and you're safe" are over. The future of security is continuous monitoring, rapid detection, and intelligent response to inevitable breaches.
Defensive Strategies: What Your Organization Needs Right Now
Given all this, what concrete steps should you take?
Priority 1: Audit your current patch management timeline.
How long does it actually take to go from vulnerability disclosure to production deployment? Track your last 10 patches. Calculate the average. If it's over 75 days, this is your biggest security gap.
Priority 2: Create a critical patch fast-track.
Not all patches are equal. Critical vulnerabilities in internet-facing systems need 30-day deployment. Standard patches can take 60-90 days. Develop a process that accommodates both.
Priority 3: Implement continuous scanning.
Move beyond quarterly vulnerability scans. Scan continuously. Connect scanning to threat intelligence feeds. When new vulnerabilities appear, scan for them immediately.
Priority 4: Monitor CISA KEV in real-time.
Set up automated monitoring of the Known Exploited Vulnerabilities list. When something appears, check if your organization is affected. If so, prioritize patching.
Priority 5: Segment your network aggressively.
If an attacker gets through via an n-day vulnerability in a perimeter device, can they access everything? Segment networks so a compromised firewall doesn't compromise the entire infrastructure.
Priority 6: Invest in detection and response capabilities.
Since you can't prevent all breaches through patching, focus on detecting them quickly. Deploy detection systems that identify unusual behavior on perimeter devices, unusual lateral movement, and unusual data access.
Priority 7: Establish incident response playbooks specifically for n-day exploitation.
What's your response process if a perimeter device is compromised through an n-day vulnerability? Practice it. Time it. Optimize it.
The Role of Automation and AI in Vulnerability Response
Here's where things get interesting.
Automation is how you compress patch timelines. Manual processes can't compete with 44-day exploitation windows. You need systems that work while people sleep.
Automated vulnerability scanning identifies vulnerable systems in real-time. No waiting for quarterly scans.
Automated patch deployment reduces the gap between patch release and production. Instead of manual change management, patches deploy automatically to non-critical systems. Critical systems get staged deployments with automated testing.
Automated testing and validation confirms that patches don't break systems. If a patch fails validation, it's rolled back automatically. No broken services.
Automated threat intelligence integration correlates vulnerability data with threat feeds. If a vulnerability has active exploits, it gets flagged for immediate attention.
Automated response orchestration coordinates patch deployment, change notification, incident response, and compliance reporting. When something happens, multiple systems respond in coordination.
Organizations using these automation approaches see patch deployment timelines cut from 120+ days to 30-45 days. It's a fundamental improvement.
The complexity is managing the automation itself. False positives in automated deployment can cause more problems than they solve. But the organizations that get it right gain massive security advantages.
Working With Vendors: Holding Them Accountable
Here's an uncomfortable truth: vendors don't have strong incentives to patch quickly.
If a vendor releases a patch and users don't deploy it for 120 days, the vendor's metrics look fine. They released a patch. It's on users if they don't deploy it.
But users need vendors to help them succeed.
Demand vulnerability pre-notification. If you're a significant customer, ask for advance notice of vulnerabilities before public disclosure. This gives you a head start on patching.
Evaluate patch quality. Some vendors release patches that break functionality. Others release high-quality patches that deploy smoothly. Factor this into vendor selection.
Require patch automation support. Ask vendors if their products support automated patch deployment. If not, why not? Push back.
Share feedback on patch management. If patch deployment is a nightmare in your organization, tell the vendor. Provide data. Push for improvement.
Evaluate security posture in vendor contracts. Make patch management and vulnerability response capability part of your vendor evaluation and contract requirements.
You have leverage. Use it.
Regulatory and Compliance Implications
Regulators are waking up to n-day exploitation.
CISA has issued guidance requiring federal agencies to patch known vulnerabilities on exploited systems within specific timeframes. It's becoming a compliance requirement, not a nice-to-have.
Financial regulators are starting to treat slow patching as a material risk control deficiency. Banks that can't demonstrate rapid patch deployment are getting compliance findings.
Healthcare regulators are investigating breaches that could have been prevented through faster patching. Regulators are asking: "How long did it take you to deploy that patch?"
General industry standards are evolving. CIS Controls, NIST, and ISO frameworks are all emphasizing patch management velocity, not just patch management process.
The compliance direction is clear: patching has become a control matter, not just an operational efficiency issue.
If your organization can't demonstrate fast patching, you're creating compliance risk.
Measuring and Reporting on Vulnerability Management
What gets measured gets managed.
If you're not actively measuring your patch management performance, it's probably not getting better.
Key metrics to track:
- Mean Time to Detection (MTTD): How long does it take to identify that you're vulnerable?
- Mean Time to Remediation (MTTR): How long from identification to patch deployment?
- Percentage of critical systems patched within 30 days: This should be >90%
- Vulnerability coverage: What percentage of known vulnerabilities in your infrastructure are tracked?
- Exploit detection rate: What percentage of exploited vulnerabilities are detected by your monitoring systems?
Measure these monthly. Report them to leadership. Make them visible to security teams.
Better yet, make patching velocity a factor in security team performance evaluations. Align incentives with security outcomes.

The Shift in Security Team Skills and Hiring
This whole n-day shift has changed what security teams need to know.
Traditional security hiring focused on:
- Intrusion detection
- Forensics
- Incident response after the fact
Modern security hiring needs to focus on:
- Patch management automation
- Vulnerability scanning and assessment
- Rapid response and remediation
- Risk-based prioritization
- Threat intelligence integration
- Systems thinking and process improvement
The best security professionals today are those who can automate vulnerability management, compress timelines, and think operationally about reducing Mean Time to Remediation.
If your security team is still structured around post-breach incident response, you need to retrain and restructure. The fight is upstream, not downstream.
Integrating Vulnerability Management Into Dev Ops and Continuous Delivery
Here's a modern approach: integrate vulnerability management into your continuous delivery pipeline.
Instead of patching as a separate, disruptive process, patches become part of your standard deployment process.
When a patch is released:
- Automated systems pull the patch into your internal repository
- Automated testing deploys it to test environments
- Automated validation confirms no breakage
- Approval workflows trigger for critical changes
- Staged production rollout begins
- Automated monitoring confirms successful deployment
This entire process can happen in 1-2 weeks for well-automated infrastructure. No manual intervention required.
The organizations that have adopted this approach (primarily large tech companies and forward-thinking enterprises) have effectively eliminated the patching timeline problem. Their mean patch deployment time is 7-14 days.
If you're still doing manual patch management, this is the direction you need to move toward.

Conclusion: The New Security Reality
N-day vulnerabilities represent a fundamental shift in how cyberattacks operate.
For decades, the security industry obsessed over zero-days, treating unknown vulnerabilities as the primary threat. That narrative is wrong. Or more accurately, it's becoming increasingly wrong.
Today, 80% of exploited vulnerabilities are n-days. The average exploitation time is 44 days. Attackers are rapidly weaponizing known flaws and scanning for unpatched systems at industrial scale.
This isn't a subtle threat. It's an existential challenge to traditional patch management approaches.
The old model—quarterly patches, careful testing, deliberate change management—can't compete with this reality. Organizations that stay with the old model are essentially announcing to attackers: "We're vulnerable for 120+ days after you have exploits."
Modern security requires a fundamental shift:
- From reactive patching to proactive vulnerability management
- From quarterly cycles to continuous remediation
- From assuming patches take months to assuming they take weeks
- From detecting breaches after they happen to preventing them through speed
This isn't incremental improvement. It's transformation.
The organizations winning this battle have restructured their operations around vulnerability response velocity. They've invested in automation. They've changed their metrics. They've aligned incentives. They've trained their teams.
And crucially, they've accepted that patching isn't an IT operations problem anymore. It's a security problem. It's a business risk problem. It deserves executive attention.
If your organization is still treating patching as a routine IT maintenance task, you're behind. You're vulnerable. You're waiting for something bad to happen.
The good news? This is fixable. You don't need to be a Fortune 500 company with unlimited resources. You need focus, smart process design, reasonable automation, and consistent execution.
Start today. Measure your current patch timelines. Set targets. Track progress. The 44-day exploitation window doesn't wait for organizational convenience.
Your competitors are already moving. Your attackers are already exploiting. The time to act is now.
FAQ
What exactly is an n-day vulnerability?
An n-day vulnerability is a security flaw that's been publicly disclosed and has either a patch or a known workaround available. Unlike zero-days (which nobody knows about), n-days are known, documented, and addressable. The danger is that many organizations don't patch n-day vulnerabilities quickly enough, leaving systems exposed to exploitation.
How is n-day exploitation different from zero-day exploitation?
Zero-day exploitation targets unknown vulnerabilities, which requires sophisticated research to discover. N-day exploitation targets known flaws that haven't been patched yet, which is much easier and more scalable. Attackers monitor security disclosures, find public exploits, and scan for unpatched systems. It's industrial-scale automation versus targeted research, which is why n-days are now more prevalent than zero-days in real-world attacks.
Why has the Time to Exploit dropped so dramatically?
Several factors converged to compress exploitation timelines: public vulnerability databases are monitored automatically by attackers, proof-of-concept code is published and weaponized rapidly, scanning infrastructure is cheap and fast, and automation tools can deploy exploits across thousands of systems simultaneously. What used to take months of research now takes days of automated scanning.
What are the primary targets for n-day attacks?
Firewalls, VPN gateways, and edge devices are the primary targets because they must remain internet-facing and provide initial access to internal networks. Compromising these perimeter devices gives attackers a foothold inside the network. From there, they can move laterally and access more sensitive systems. Other targets include web servers, authentication systems, and remote access infrastructure.
How can my organization reduce its vulnerability window?
Implement continuous vulnerability scanning rather than quarterly scans, integrate threat intelligence feeds to get immediate notification of new exploits, create fast-track approval processes for critical patches (30-day deployment), automate patch testing and deployment where possible, and segment your network so that a compromised perimeter device doesn't compromise your entire infrastructure. Track mean time to remediation as a security metric and report it to leadership.
What role does CISA's Known Exploited Vulnerabilities list play?
CISA's KEV list is a public database of vulnerabilities actively being exploited in the wild. It helps defenders prioritize patching by showing which flaws matter most. However, it also serves as a roadmap for attackers. When a vulnerability appears on the list, it signals that exploits are working and vulnerable systems exist. Organizations should monitor the KEV list in real-time and prioritize patching any items that affect their infrastructure.
Why do nation-states prefer n-day exploitation over zero-days?
Nation-states prefer n-days because they're deniable (attackers were just using publicly available information), they scale better (thousands of systems can be attacked simultaneously), and they don't require burning expensive zero-day assets. Zero-days signal capability and raise alarm when used, whereas n-day exploitation is harder to attribute and can be dismissed as "normal cyber activity."
What's the business impact of slow patching?
Organizations that patch critical vulnerabilities slowly suffer breaches that could have been prevented. The cost difference between patching within 30 days and patching within 120 days can be millions of dollars in incident response, forensics, regulatory notification, and remediation. It's not just a security metric—it's a bottom-line business risk.
How should my patch management process change?
Shift from quarterly patch cycles to risk-based prioritization with continuous deployment. Critical vulnerabilities in internet-facing systems should be patched within 30 days. Important vulnerabilities should be patched within 60 days. Standard vulnerabilities can be patched within 90 days. Implement automation to reduce manual work and accelerate deployment. Track metrics and report them to leadership.
What automation tools should we invest in?
Prioritize continuous vulnerability scanning tools that integrate with threat intelligence feeds, patch management platforms that support staged rollouts and automated testing, and network segmentation tools that limit lateral movement if a perimeter device is compromised. The specific tools depend on your infrastructure, but the principle is the same: automation compresses timelines and improves security.
How does n-day exploitation affect supply chain security?
If an attacker can compromise a software vendor or infrastructure provider through an n-day vulnerability, they can distribute malware to thousands of customers simultaneously. This is a supply chain attack vector that's becoming increasingly relevant. Organizations need to pressure vendors to patch quickly and verify that their suppliers have strong vulnerability management practices.
The Bottom Line
N-day vulnerabilities are no longer a secondary concern in cybersecurity. They're the primary threat vector. Attackers have moved from hunting for zero-days to mass-exploitation of known flaws that organizations haven't patched yet.
The shift is driven by economics: n-day exploitation is cheaper, more reliable, and scales better than zero-day hunting. It doesn't require sophisticated research. It requires infrastructure, automation, and patience.
Your organization's response needs to be equally pragmatic: compress patch timelines, automate vulnerability management, prioritize based on risk, and accept that perfect security through patching is impossible. Instead, focus on rapid detection and containment of inevitable breaches.
The organizations that adapt first win. The ones that don't are going to have a very uncomfortable few years.
Key Takeaways
- Over 80% of exploited vulnerabilities are n-days, with attackers moving away from expensive zero-day hunting toward mass exploitation of unpatched known flaws
- Average time to exploit has compressed from 745 days (2018) to just 44 days (2025), leaving organizations with a narrow window to patch critical systems
- Firewalls, VPNs, and edge devices are primary targets because they're internet-facing and provide initial access to internal networks
- Nation-state actors, particularly China, lead n-day exploitation campaigns, using rapid weaponization of public patches against vulnerable systems
- Traditional quarterly patch management processes take 180+ days, far exceeding the 44-day exploitation window, making fast-track patch programs essential
- Organizations patching critical vulnerabilities within 30 days see 80% fewer successful attacks from n-day exploitation compared to those patching within 120+ days
Related Articles
- How Hackers Are Using AI: The Threats Reshaping Cybersecurity [2025]
- SmarterTools Ransomware Breach: How One Unpatched VM Compromised Everything [2025]
- DNS Malware Detour Dog: How 30K+ Sites Harbor Hidden Threats [2025]
- NordVPN & CrowdStrike Partnership: Enterprise Security for Everyone [2025]
- Apple Zero-Day Flaw CVE-2026-20700: What You Need to Know [2025]
- Windows 11 Notepad Security Flaw: What You Need to Know [2025]
![N-Day Vulnerabilities: Why Patched Exploits Are Now Your Biggest Security Risk [2025]](https://tryrunable.com/blog/n-day-vulnerabilities-why-patched-exploits-are-now-your-bigg/image-1-1770982561431.jpg)



