North Korean Job Scammers Target Developers with Fake Interviews: Operation Dream Job Evolves [2025]
Introduction: The New Face of Recruitment Scams
You're scrolling through LinkedIn one afternoon, and a recruiter messages you about an incredible job opportunity. The salary's competitive. The company sounds legitimate. The role matches your exact skillset. So you apply.
Three days later, you're doing a coding challenge. It feels real. The repo is on GitHub or PyPI. The code looks professional. You download it, run it, and suddenly your crypto wallet is empty.
This isn't a hypothetical scenario anymore. This is happening to developers right now, and the people behind it aren't some random cybercriminals operating from a basement. They're North Korean state-sponsored hackers working under an umbrella campaign called Operation Dream Job.
The campaign has been running for years, but what makes 2025 different is how sophisticated the attacks have become. Security researchers recently uncovered a new variant called Graphalgo that's spreading malicious packages across legitimate code repositories like PyPI and npm. The attackers have learned how to blend in, how to make their malicious code look legitimate, and how to target developers where they're most vulnerable—during the hiring process.
For JavaScript and Python developers, this is a wake-up call. These are the two most popular programming languages globally, and the attackers know that targeting them casts the widest net. They're not just stealing credentials anymore. They're after cryptocurrency, access to development environments, and potentially backdoor access to company infrastructure.
This article breaks down exactly what Operation Dream Job is, how the new Graphalgo variant works, what makes these scams so effective, and most importantly, how you can protect yourself. By the end, you'll understand the threat landscape and have actionable steps to stay safe.

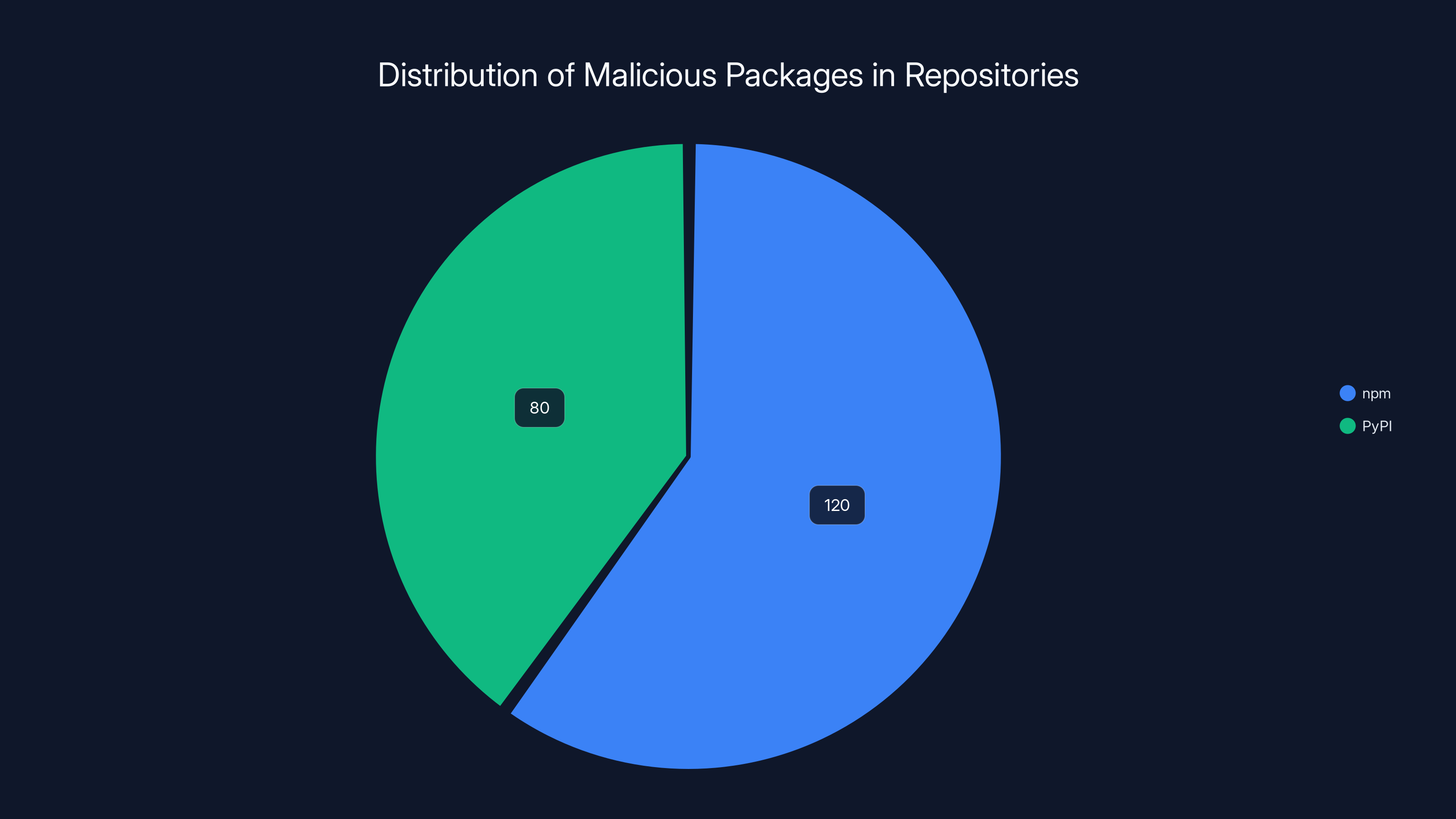
Approximately 200 malicious packages were found, with a higher concentration in npm repositories. Estimated data based on security research findings.
TL; DR
- Lazarus Group Evolution: North Korean state-sponsored hackers continue evolving Operation Dream Job to target developers with increasingly sophisticated fake job opportunities
- Graphalgo Variant: New variant discovered in May 2025 uses malicious dependencies hidden in legitimate bare-bone projects on PyPI and npm repositories
- Scale of Attack: Security researchers found approximately 200 malicious packages spoofing legitimate libraries like graphlib, biglib, and graph-related utilities
- Primary Targets: JavaScript and Python developers in Web 3 and cryptocurrency industries, though traditional software developers are also at risk
- Attack Method: Fake job postings on LinkedIn lead to coding challenges that require downloading and executing malicious code packages
- Immediate Action: Verify package sources, audit your dependencies, enable two-factor authentication on all accounts, and never execute unvetted code during interviews

Estimated data shows that crypto wallets are the primary target in compromises, followed by private exchange APIs and wallet signing keys. Estimated data.
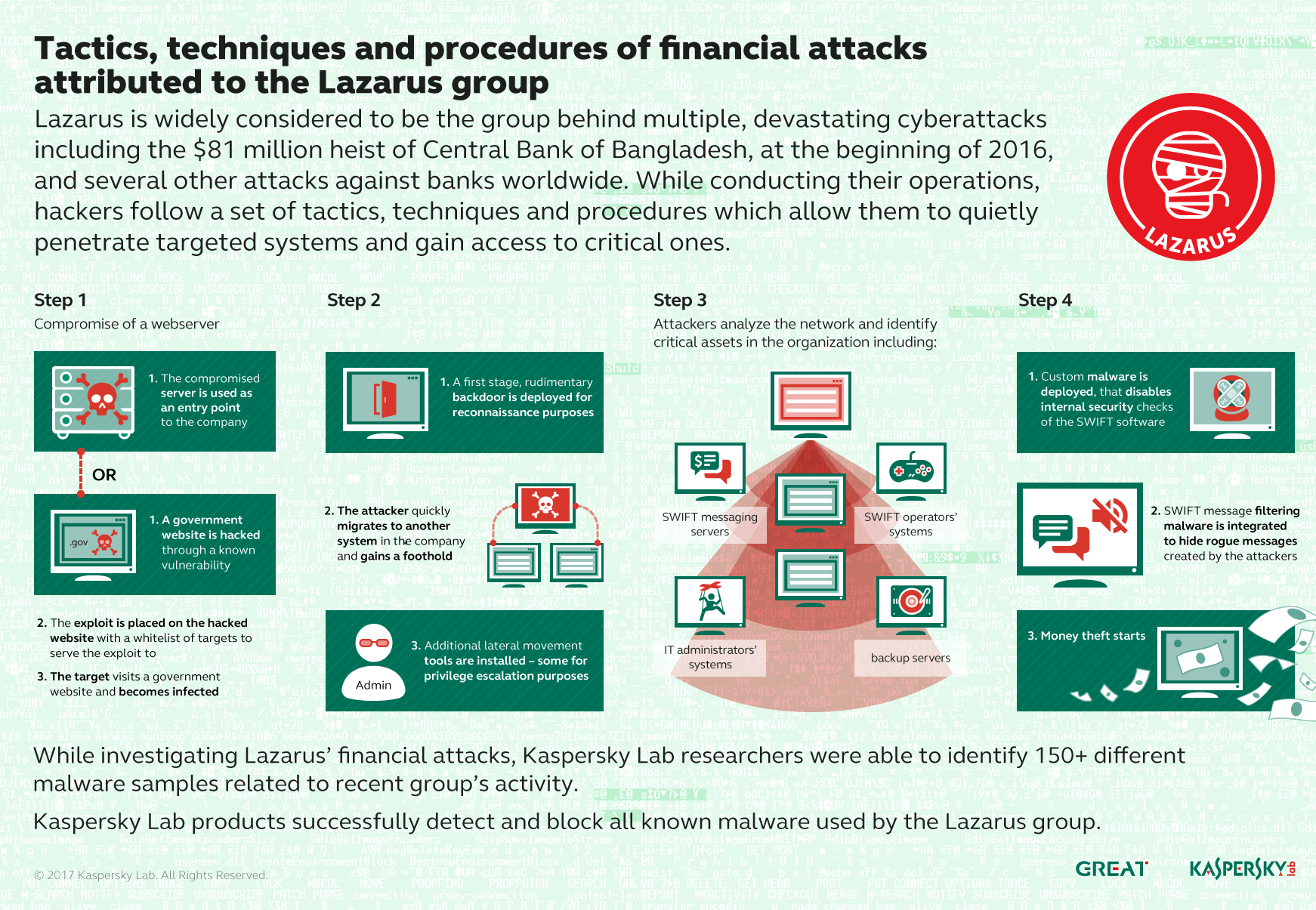
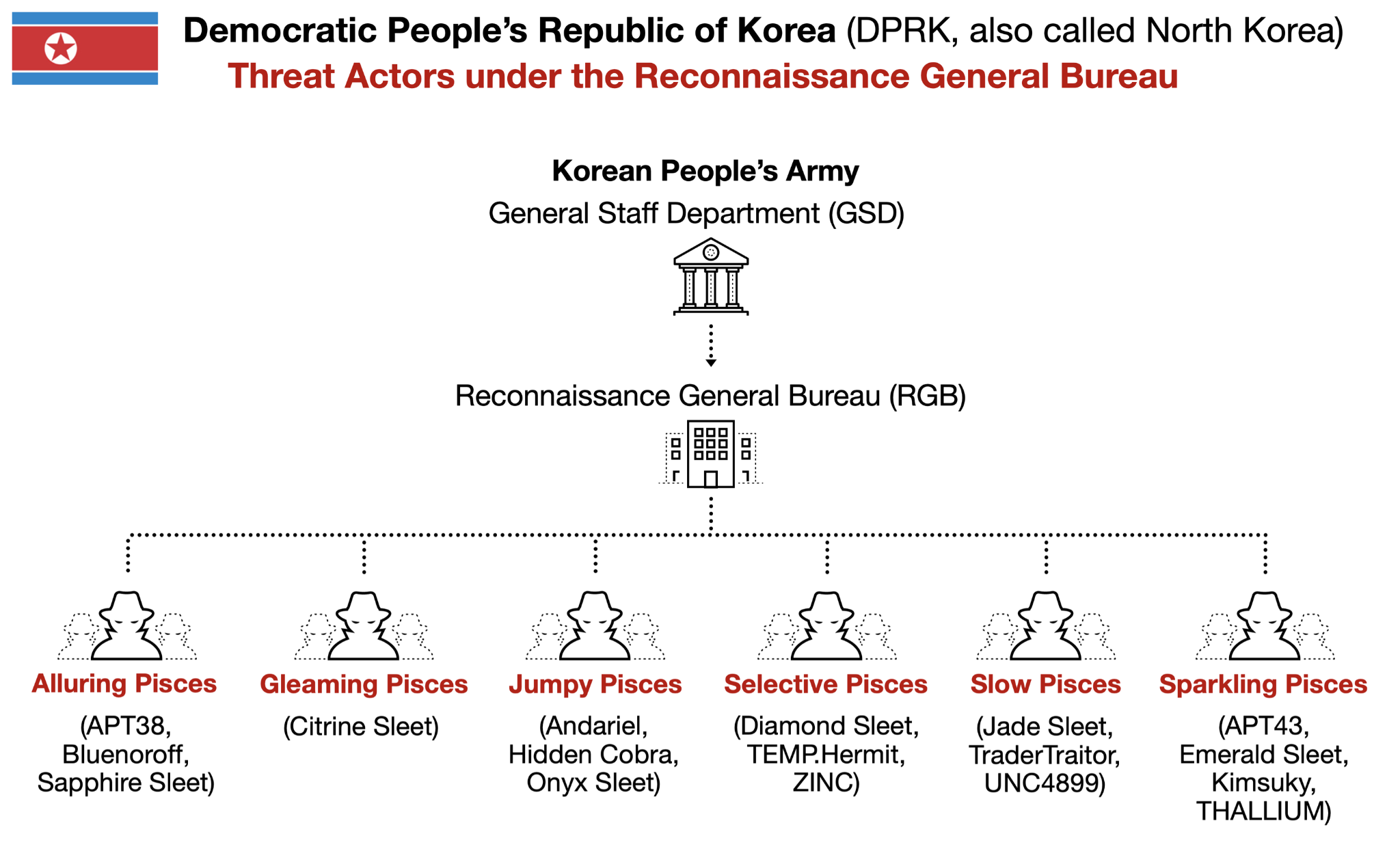
Who Is the Lazarus Group and Why Should You Care?
The Lazarus Group isn't a name you hear in casual tech conversations, but it should be. This is one of the most dangerous hacking organizations in the world, and they're backed by a nation-state. We're talking about North Korea.
The group's origins trace back to around 2009, but they gained worldwide infamy for several major attacks. They were responsible for the Sony Pictures hack in 2014, which deleted massive amounts of data and released unreleased films. They orchestrated the Bangladesh Bank heist in 2016, stealing approximately 81 million dollars. More recently, they've been linked to attacks on cryptocurrency exchanges and blockchain companies.
What makes Lazarus different from typical criminal organizations is their resources, patience, and sophistication. They have time. They have funding. They have state support. This means they can plan operations over months or years, invest in infrastructure, and constantly evolve their tactics when defenses improve.
Operation Dream Job specifically launched years ago as a way to fund North Korean operations through cryptocurrency theft. Instead of breaking into exchanges directly, they realized something smarter: recruit developers directly by offering them jobs. The appeal is undeniable. A job offer beats a phishing email every single time. People are far more likely to trust and engage with a hiring process than a random message asking them to click a link.
The beauty of this approach from the attacker's perspective is that it's highly targeted. They're not sending 10,000 emails hoping 10 people click. They're finding specific developers, researching their profiles, crafting personalized messages, and building trust over days or weeks. When they finally ask for that coding challenge, the developer has already mentally committed to the "hiring process."
Why should you care? Because if you're a software developer, you're on their radar. Your skills are valuable. Your access to systems could be worth hundreds of thousands of dollars. And if you have any connection to crypto, Web 3, or blockchain, you're a priority target.
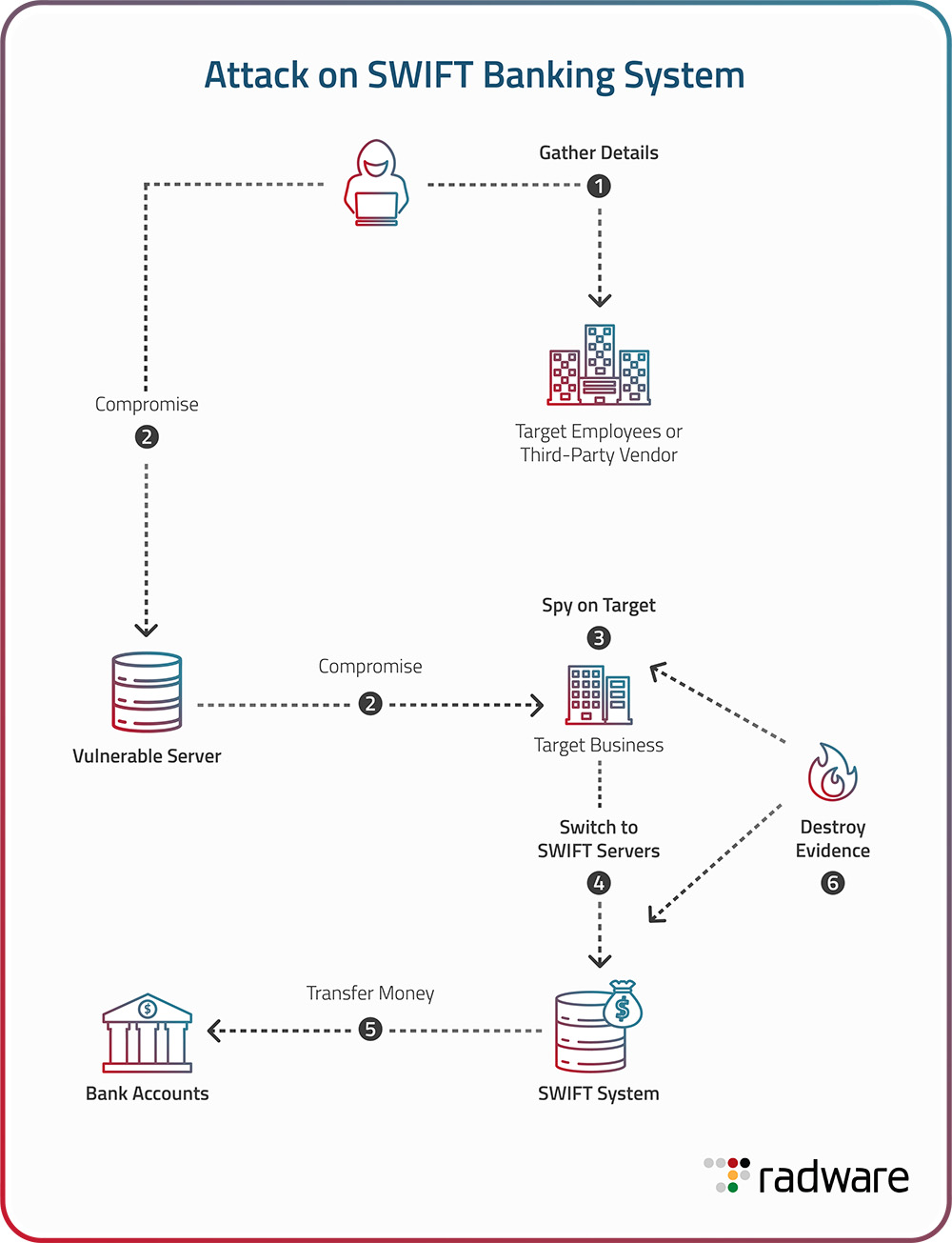
How Operation Dream Job Works: The Attack Flow
Understanding the attack flow is crucial because each step has vulnerabilities you can spot. Operation Dream Job follows a remarkably consistent playbook:
Step 1: The Outreach
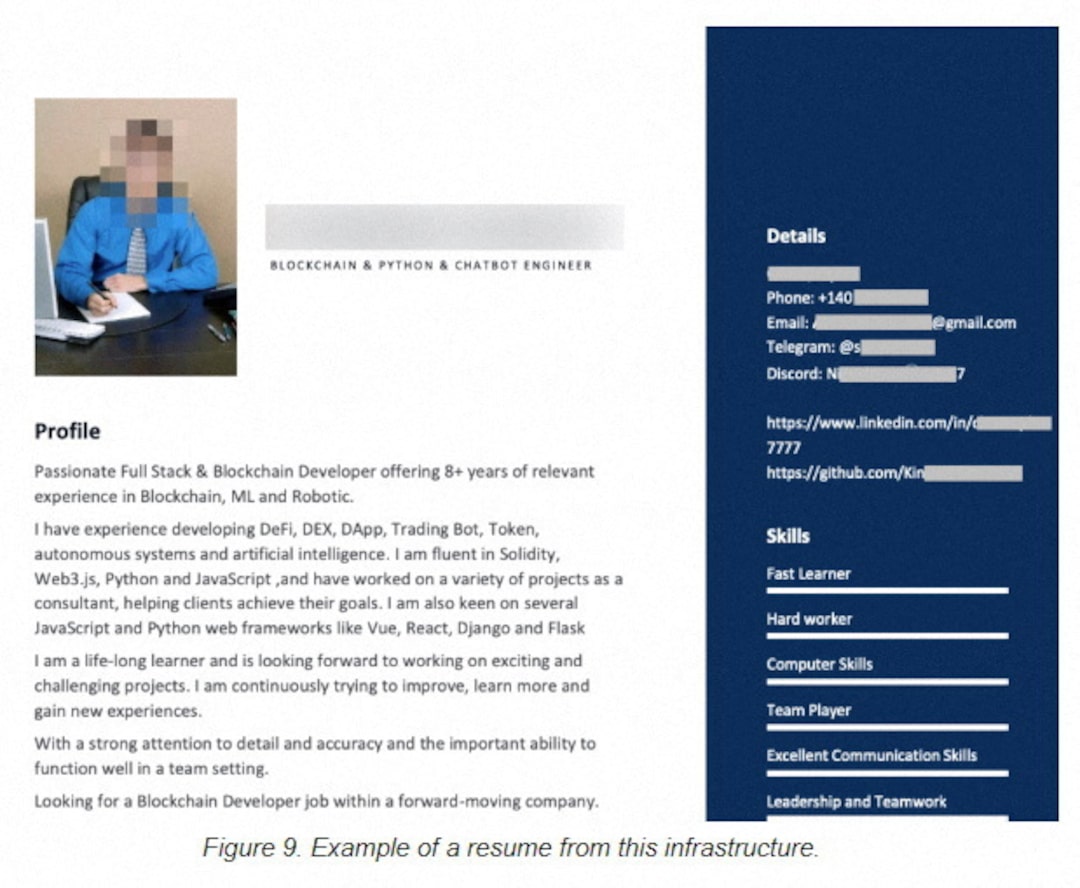
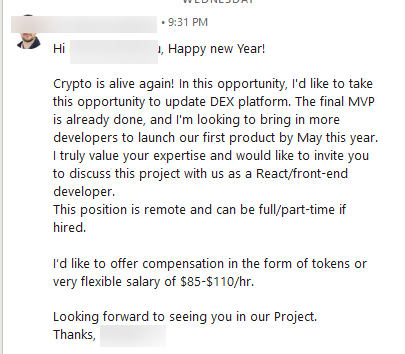
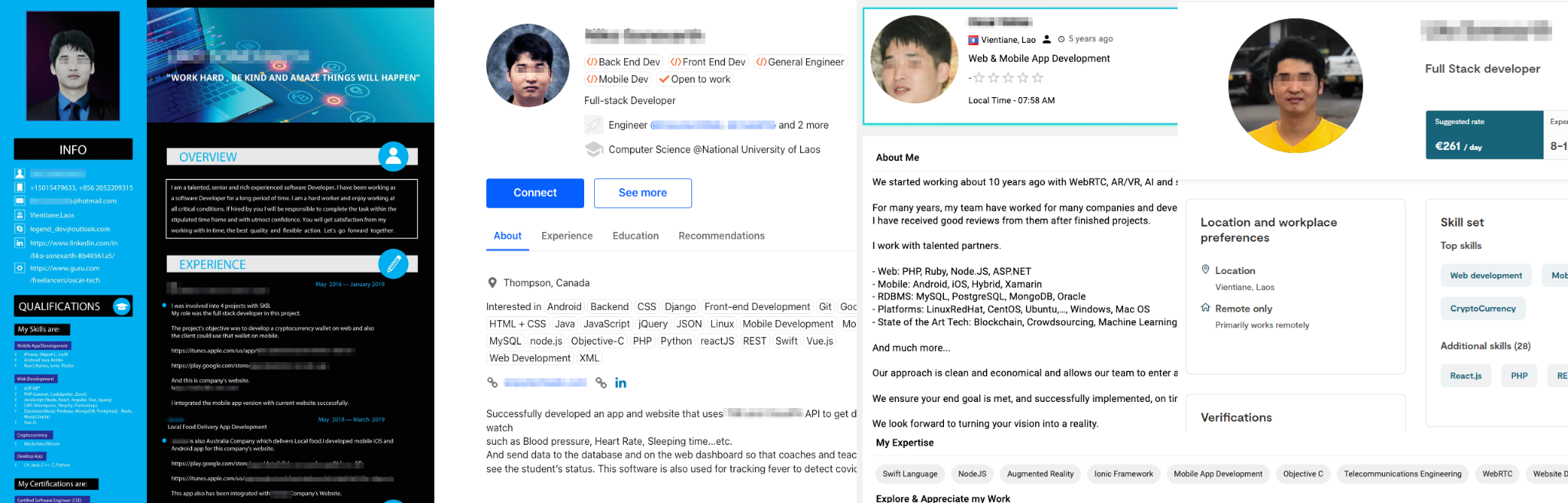
It starts on LinkedIn. The attacker creates a profile for a recruiter, sometimes using stolen or AI-generated photos. They do basic research on you, noting your skills, previous jobs, and interests. The message is personalized. They mention a specific technology you've worked with. They reference your previous role. This isn't automated spam—it's targeted hunting.
The company name they're recruiting for is usually legitimate but slightly modified. Or they use a real company's name but claim to be a subsidiary or newly acquired division. The job title matches what you'd want. The location might be remote (convenient). The salary is significantly higher than market rate (a red flag people often miss in excitement).
Step 2: Building Trust
Over several messages, the "recruiter" asks you questions about your background, experience, and interests. They answer your questions about the company. They might schedule a call where you talk for 20 minutes. If they have a fake video of someone speaking, even better. The goal is to create enough rapport that you believe this is a real opportunity.
This phase can last days or even weeks. Patience is their advantage. They're not in a hurry.
Step 3: The Coding Challenge
Eventually, they get to it. "We'd like you to complete a technical assessment," they say. "It's a standard part of our hiring process for all candidates."
They send you a link to a GitHub repository, a PyPI package repository, or an npm package. The repo or package looks professional. There's a README file with instructions. The code structure looks clean. There might even be actual functionality that works.
This is where the attack payload is hidden. The malicious code is either:
- A dependency that gets pulled in when you run
npm installorpip install - Code hidden in the main codebase that executes silently in the background
- A file that runs automatically on download or execution
Step 4: Execution and Compromise
You follow the instructions. You clone the repo or install the package. You run the code or execute the test. That's the moment the malicious code activates.
From here, the attacker has several options:
- Cryptocurrency wallet theft: If you have any crypto wallets or extensions installed, the malware can drain them
- Credential harvesting: Steal your API keys, SSH keys, authentication tokens
- Browser persistence: Install an extension that stays active, intercepting future transactions
- System compromise: Establish a backdoor for future attacks
- Data exfiltration: Access your development files, private repos, confidential information
The genius of this approach is that the victim often doesn't realize they've been compromised immediately. They might dismiss the file downloads or suspicious processes as part of the "legitimate" coding challenge.
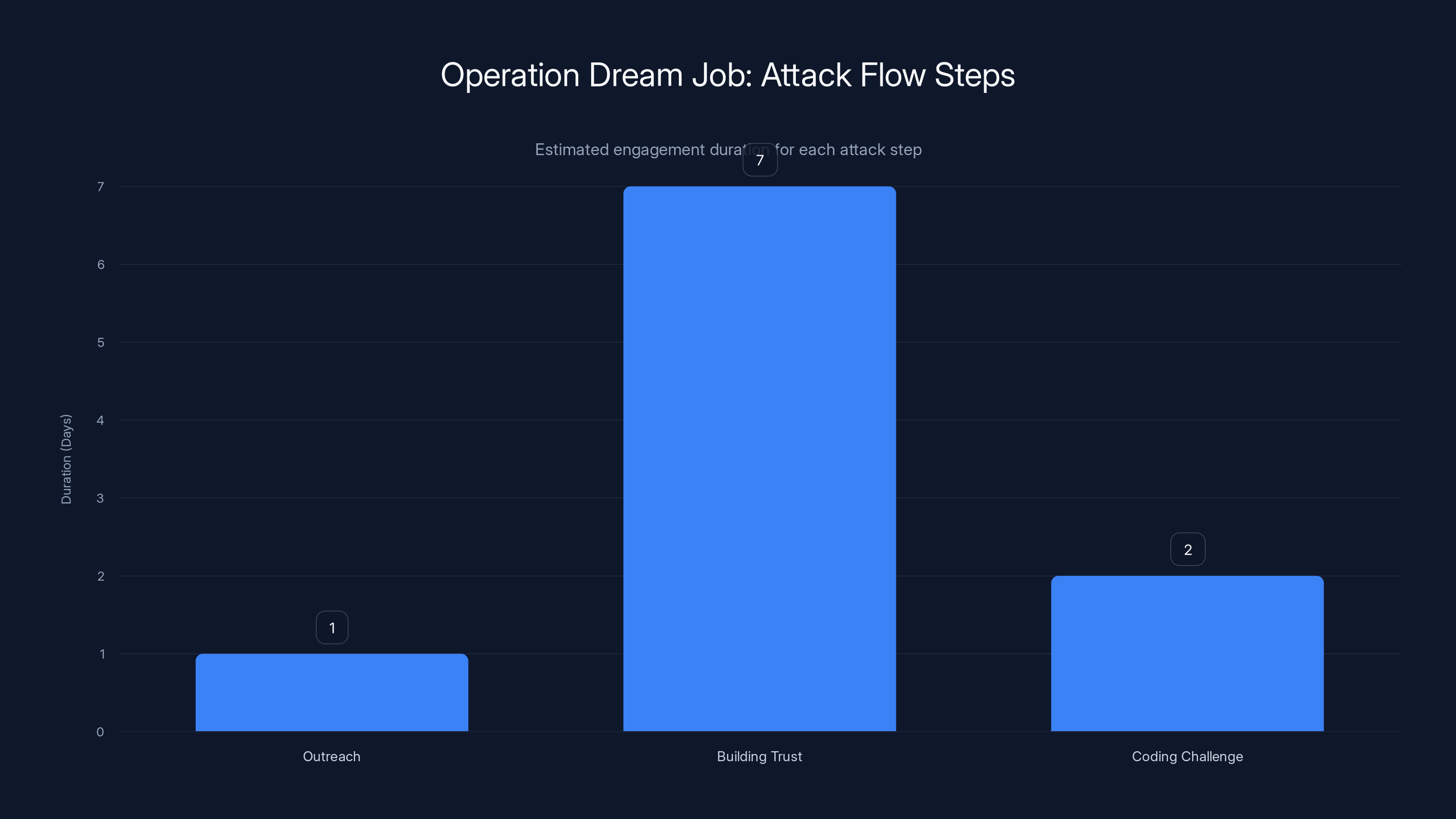
The 'Building Trust' phase is the longest, often lasting up to a week, allowing attackers to establish credibility. Estimated data.
The Graphalgo Variant: What Changed in 2025
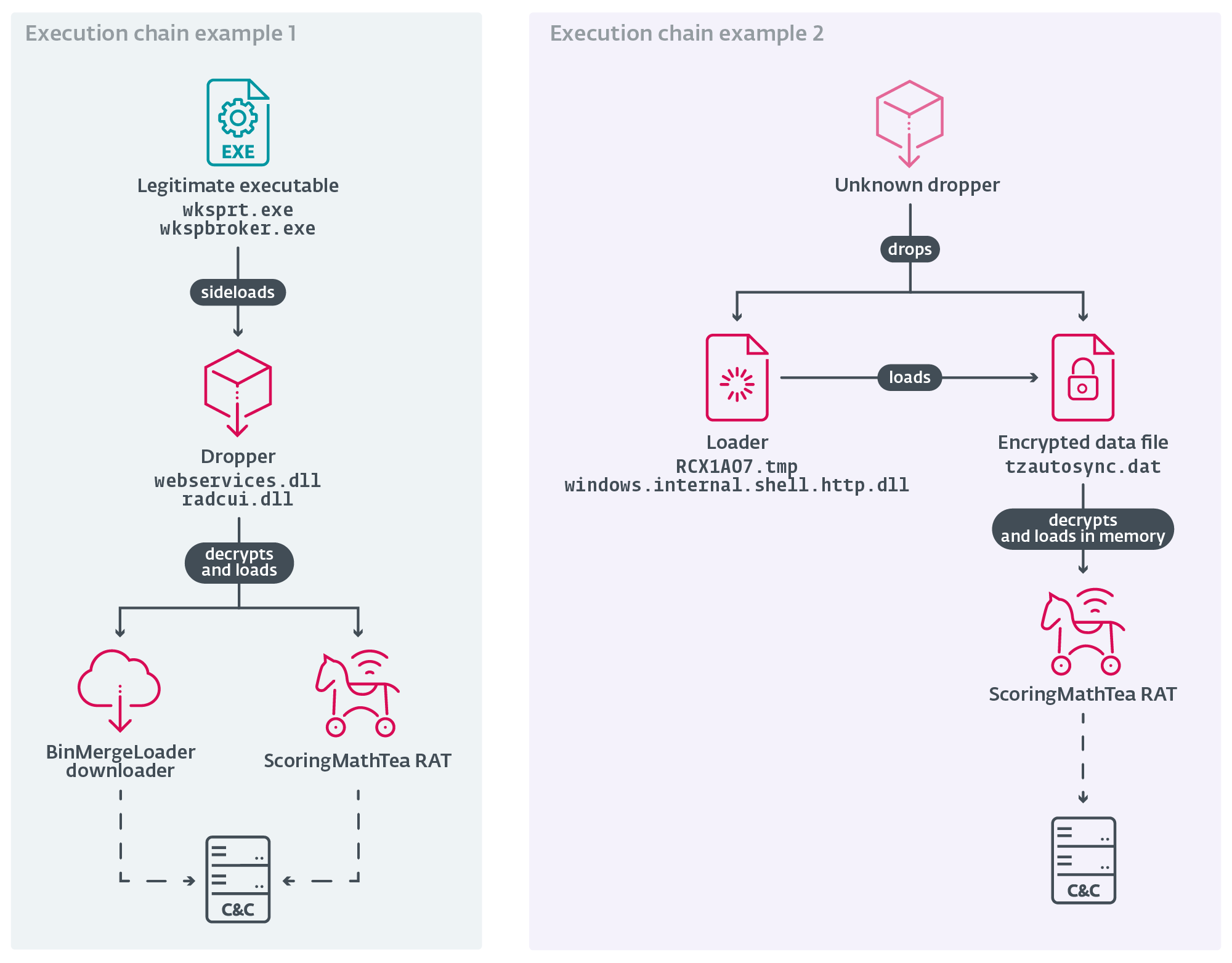
In May 2025, security researchers identified a new variant of Operation Dream Job called Graphalgo. This isn't just a minor tweak. It represents a meaningful evolution in the attackers' methodology.
How Graphalgo Works
The name "Graphalgo" comes from a specific pattern the attackers used: all malicious packages had the prefix "graph" in their name. They were spoofing legitimate libraries like graphlib, a JavaScript library for graph data structures. The idea is genius in its simplicity. When a developer sees a dependency named "graphlib" or a similar variant, they might assume it's the legitimate library they've heard of.
What makes Graphalgo different is the mechanism of delivery. Instead of creating entirely new malicious repositories from scratch, the attackers are taking legitimate, bare-bone projects and injecting malicious dependencies into them. Here's the key difference:
Old approach: Create a completely fake project that does exactly what the fake coding challenge requires, but includes malicious code throughout.
New approach: Take a real, minimal project from GitHub (maybe a simple starter template or an example project), add the real functionality it's supposed to have, and then inject a malicious dependency that pulls in via npm or PyPI.
This is harder to detect because the code you're looking at is partially legitimate. If you audit the main code files, they might look fine. The malicious payload is hidden in the dependency declaration, and it only becomes active when you install dependencies and run the code.
The Scale of Graphalgo
Reversing Labs, the security firm that discovered the Graphalgo variant, found approximately 200 malicious packages across PyPI (Python) and npm (JavaScript). This is significant. It suggests the attackers aren't doing this on a small scale. They're operating an industrial-grade malware distribution network.
The packages had various names designed to mimic legitimate libraries:
- graphlib (and variations like graphlib-python)
- graph-utilities
- graph-parser
- graph-analysis
More recent variants replaced "graph" with "big" (biglib, big-data, etc.), suggesting the attackers are still active and adapting their naming conventions.
Detection Difficulty
One critical point: the researchers note that "it is easy to create such job task repositories." This is both a warning and an explanation of why the campaign is so effective. The barrier to entry is low. The attackers don't need sophisticated technical skills to set up the infrastructure. They need:
- Access to npm or PyPI (trivial—these are public registries anyone can publish to)
- A legitimate-looking bare-bone project (freely available on GitHub)
- A malicious dependency (code that steals credentials or crypto)
- A way to distribute the project to targets (fake job listings)
That's it. The entire operation can be run by a small team with basic programming knowledge.
Why JavaScript and Python Developers Are Primary Targets
You might be wondering: why specifically JavaScript and Python developers? Why not C++ developers or Rust developers?
The answer is market penetration and cryptocurrency infrastructure. JavaScript is the most popular programming language globally, according to every major survey from Stack Overflow to GitHub. It's used everywhere: web development, Node.js backends, browser extensions, Electron desktop apps. If you want to compromise a developer who has broad access across different systems, JavaScript is the language to target.
Python is similar. It's the dominant language in data science, machine learning, automation, and increasingly in backend development. If you target Python developers, you're hitting data scientists, ML engineers, DevOps engineers, and infrastructure specialists.
But there's another reason: Web 3 and cryptocurrency adoption is highest among JavaScript and Python developers. These are the communities that built the blockchain ecosystem. If you're specifically targeting developers with cryptocurrency wallets, high-value accounts, or access to blockchain infrastructure, JavaScript and Python are where the money is.
The Lazarus Group is absolutely aware of this. They're not randomly selecting languages to target. They're making calculated decisions about which communities have the highest concentration of targets with valuable assets or access.
JavaScript developers are also more likely to install third-party packages without extensive scrutiny. The JavaScript ecosystem (npm) has a culture of rapid development and reusable packages. It's common to add dozens of dependencies to a project. This actually increases the attack surface. If one package is malicious, you might not notice among 50 legitimate packages.
Python has similar characteristics. The Python ecosystem encourages dependency reuse, and tools like pip make it easy to install packages. A Python developer in the data science or ML space might have 20-30 core dependencies plus additional packages for specific tasks.
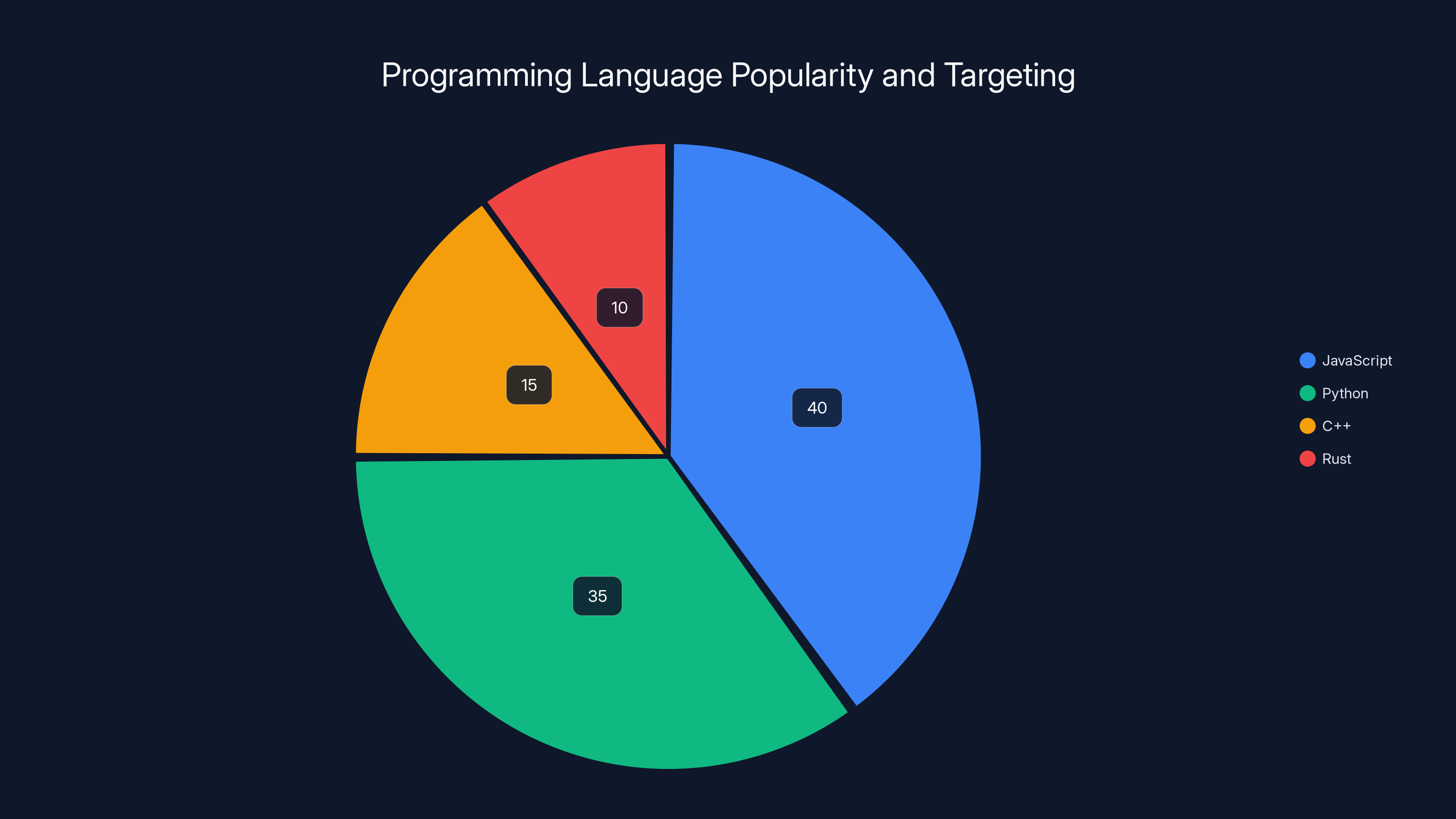
JavaScript and Python developers are primary targets due to their widespread use and involvement in cryptocurrency, making up 75% of the targeting share. Estimated data.
The Cryptocurrency Angle: Why Crypto Wallets Are the Prize
Operating a nation-state requires funding. North Korea is under international sanctions, which means they can't access the traditional banking system. They can't apply for loans, transfer money internationally, or maintain normal business accounts.
Cryptocurrency is the solution. Bitcoin, Ethereum, and other cryptocurrencies operate outside traditional banking infrastructure. They can't be frozen by sanctions. They can be exchanged for cash in certain markets. A billion-dollar cryptocurrency heist is worth more to North Korea's government than most legitimate industries.
This is why Operation Dream Job specifically targets cryptocurrency holders and developers. Every developer they compromise with a crypto wallet is a potential theft target. If they can install malware that monitors wallet activity or intercepts transactions, they've essentially placed a device between the victim's money and their control of it.
A single developer might have
Beyond direct theft, compromising a developer can provide access to:
- Private crypto exchange APIs: Some developers work on projects that interact with crypto exchanges. Access to these APIs could allow traders to manipulate markets or steal funds
- Wallet signing keys: If you can get access to the keys that sign cryptocurrency transactions, you can create transactions without the owner's permission
- Smart contract code: Developers working on blockchain projects might have access to undeployed smart contracts that contain valuable logic or exploit other systems
- DeFi protocols: Developers working on DeFi (decentralized finance) might have access to protocol code that controls billions in locked funds
This is why the Lazarus Group has been so relentless in targeting this specific community. The ROI on a single successful compromise can be enormous.
Identifying Fake Job Scams: Red Flags and Warning Signs
Now let's get practical. How do you identify these scams before you become a victim? Here are the signs:
Communication Red Flags
Rapid progression: The scammer wants to move quickly through the hiring process. They might skip phone interviews, skip video calls, and jump straight to the technical assessment. Real hiring processes are slower because they involve multiple teams and stakeholders.
Grammatical errors: Even if the initial outreach seems professional, look for subtle grammar issues or awkward phrasing. Many Operation Dream Job recruiters are not native English speakers, and sometimes their writing shows it. This isn't always a red flag alone, but combined with other factors, it's worth noting.
Generic conversations: The recruiter might ask generic questions that could apply to any developer. Real recruiters do deep dives into your specific experience and ask detailed follow-up questions.
Limited communication channels: Real recruiters have verified company email addresses and phone numbers. If a recruiter is communicating exclusively through LinkedIn messages or personal email, that's suspicious.
Opportunity Red Flags
Salary too high: If the salary is 20-50% above market rate for your location and experience level, that's unusual. Real companies don't need to vastly overpay to attract developers. Scammers use inflated salaries as bait.
Remote position in a country with different labor laws: Some scammers claim to be hiring for remote positions but offer salary and benefits that don't match any real country's standards. If something seems financially impossible, it probably is.
No clear company structure: You can't find the company on Google, their office doesn't exist, or their website is extremely new. Real companies have an online presence.
Unusual interview structure: The company skips initial screening interviews and jumps straight to technical challenges. Or they want you to prove your skills before even confirming you're interested.
Code Challenge Red Flags
Pressure to install and run immediately: They want you to complete the challenge quickly, without time to review the code. Real technical assessments give you time (usually a few hours or a few days).
Unusual dependencies: The challenge requires installing libraries you've never heard of. Before you install anything, look up the package on npm or PyPI. Check the package's creation date, number of downloads, and who created it. If the account is brand new or the package has zero legitimate downloads, it's suspicious.
Download unusual files: The challenge asks you to download and execute binary files (.exe, .dll, .so) directly. Most legitimate coding challenges don't require compiled binaries.
Requests for credentials or API keys: The challenge asks you to input your API keys, SSH keys, or credentials during the process. Real assessments never ask for this.
No documentation or support: You can't find documentation for the project anywhere. There's no GitHub repository for reference. There's no maintainer you can contact with questions. Real projects have support.
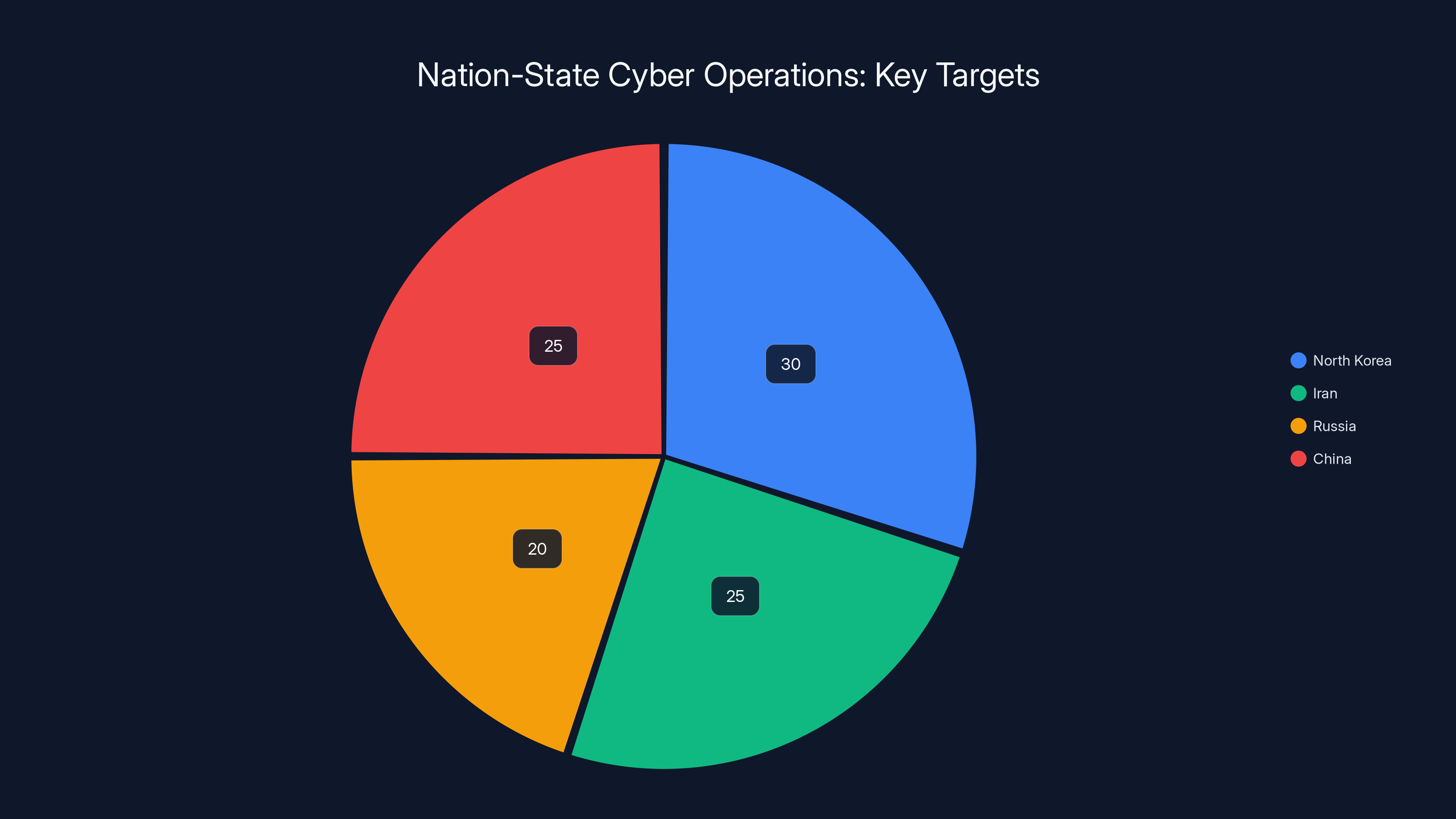
Estimated data shows that North Korea, Iran, Russia, and China have diverse cyber operation targets, with North Korea focusing significantly on revenue generation.
Protecting Yourself: Technical Defenses
If you're going to survive in this threat landscape, you need both defensive awareness and technical protections. Let's start with technical measures:
Dependency Auditing
Before running any new project, audit its dependencies. For npm projects, check the package.json file. For Python projects, check the requirements.txt or setup.py file. For each dependency, ask yourself:
- Do I recognize this package name?
- Can I find it on the official registry (npmjs.com or pypi.org)?
- How old is the package? (Days old is suspicious. Years old is more trustworthy.)
- How many weekly downloads does it have?
- Who is the maintainer? Can I find information about them?
- Does it have GitHub stars or other indicators of legitimate use?
For JavaScript, run npm audit before installing. This will flag known security vulnerabilities. For Python, use tools like safety or bandit.
Sandboxing and Isolation
Never run untrusted code on your main development machine or on any machine with access to your cryptocurrency wallets or company infrastructure. Use virtual machines or containers. Create a separate user account on your computer specifically for running untrusted code. Use tools like Docker to isolate code execution.
Better yet: use a completely separate computer or a cloud sandbox service like Replit, Glitch, or similar platforms where you can run code without any risk to your main system.
Wallet and Key Management
If you have cryptocurrency, never store private keys or seed phrases on your development machine. Use a hardware wallet like Ledger or Trezor. These keep your keys offline and separate from your computer.
For API keys and authentication tokens: never hardcode them in projects. Use environment variables or secrets management tools like 1Password, Vault, or AWS Secrets Manager. Enable rotation of keys regularly.
Multi-Factor Authentication Everywhere
Enable two-factor authentication (2FA) on every account that matters: your email, your crypto exchanges, your GitHub account, your npm account, your job sites, everything.
Better yet, use authenticator apps (Google Authenticator, Authy) instead of SMS for 2FA. SMS can be intercepted. Authenticator apps are more secure.
Browser Extensions Caution
Browser extensions have permission to intercept all your web traffic. This makes them a prime target for malware. If a "coding challenge" or any other source asks you to install a browser extension, decline unless you can verify the source independently.
Regularly audit the extensions you have installed. Remove anything you don't actively use.
Organizational and Educational Defense Strategies
If you're a hiring manager or work in security, you need organization-wide strategies:
Internal Hiring Process Security
Verify job postings: Before any recruiter reaches out to developers on your behalf, ensure they're using your official company email and phone numbers. Make a list of authorized recruiters or recruitment agencies.
Internal code repositories: When developers are doing technical assessments as part of hiring, make sure they're using your internal servers or verified platforms. Don't ask candidates to install and run code from external sources.
Candidate guidance: Provide clear instructions to candidates about what they should expect. Include warnings about common scams. Make it clear that legitimate assessments will be done on verified platforms.
Developer Security Training
Conducting regular security training for developers is invaluable. The training should cover:
- How social engineering works
- The specific tactics used in Operation Dream Job
- How to identify fake job postings
- Safe practices for handling untrusted code
- Credential and key management best practices
Incident Response Planning
If a developer does get compromised, you need a plan. This includes:
- How to detect compromise (unusual account activity, unauthorized access, missing funds)
- Who to contact immediately (security team, law enforcement, cryptocurrency exchange)
- How to contain the damage (revoke API keys, change passwords, freeze accounts)
- How to recover and investigate
Supply Chain Monitoring
For organizations, implement tools that monitor dependencies for vulnerabilities and suspicious activity. Tools like Snyk, Dependabot, or similar services can alert you when dependencies have known issues or when packages are updated in unusual ways.
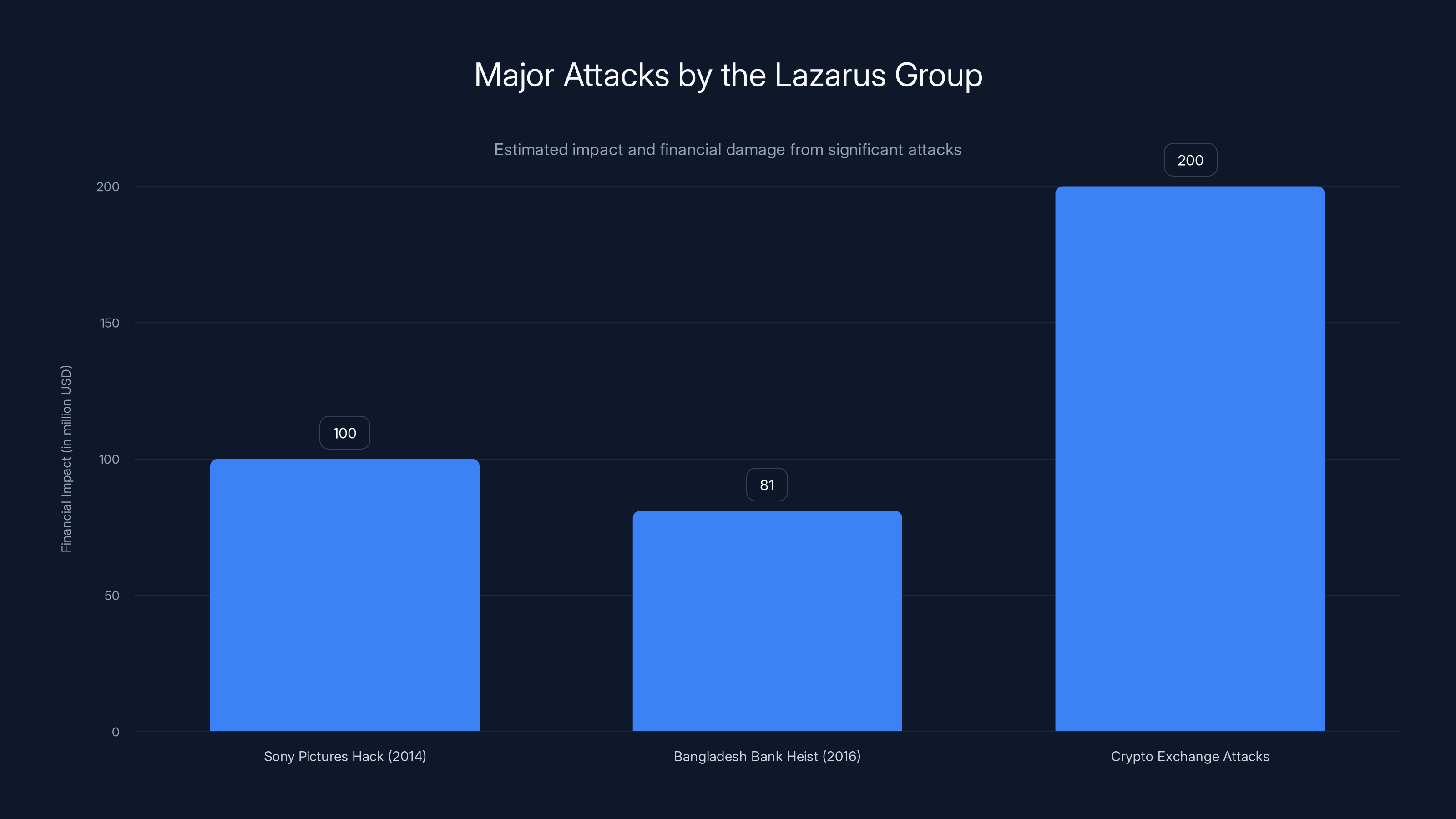
The Lazarus Group has executed high-profile attacks with significant financial impacts, including the
The Broader Context: Nation-State Cyber Operations
Operation Dream Job isn't just a curiosity. It's part of a broader pattern of nation-state cyber operations that target private citizens and companies. Understanding the broader context helps explain why this threat is so serious.
North Korea's cyber operations are well-documented by intelligence agencies and security researchers. The country's government sanctions against the country have made legitimate funding extremely difficult. This creates an incentive structure where cyber operations are not just military tools—they're economically essential.
According to various security reports, North Korean cyber operations have generated hundreds of millions of dollars for the regime. This funding supports the government's weapons development, leadership lifestyle, and military operations. When you see Operation Dream Job as a revenue generation tool rather than just a crime, it explains the sophistication, persistence, and scale of the operation.
Other nation-states run similar operations:
- Iran targets oil and gas companies with fake job postings
- Russia uses cryptocurrency scams to fund intelligence operations
- China targets technology companies to steal intellectual property
These aren't isolated incidents. They're systematic, well-resourced operations backed by governments that have as much patience and funding as necessary to achieve their objectives.
The implications are significant. If you're a software developer, you're not just competing in a market—you're potentially a target for nation-state intelligence operations. Your time, your access, and your cryptographic keys are valuable to governments that operate outside normal legal and ethical constraints.

Evolution and Future Threats: What's Coming
The Graphalgo variant represents an evolution, but it's unlikely to be the final form of Operation Dream Job. The attackers will continue to adapt. Here's what we can expect:
Increased Sophistication
Future variants will likely include:
- Polymorphic malware: Code that changes itself to avoid detection
- Multi-stage payloads: Initial infection is benign, but later stages download the real malware
- Custom exploitation: Malware tailored to specific targets or environments
- Evasion techniques: Code that detects if it's running in a sandbox or security research environment and behaves differently
Expanded Target Scope
While JavaScript and Python are primary targets, future campaigns might expand to:
- Golang and Rust developers: Growing ecosystems with less developed security practices
- Cloud infrastructure specialists: Access to production environments
- Security researchers and incident responders: Attacking the people who defend against attacks
- Blockchain developers: Still valuable but increasingly security-conscious
Social Engineering Refinement
As defenders get better at technical detection, attackers will focus on social engineering improvements:
- More convincing recruiting personas: Better grammar, deeper research, longer trust-building phases
- Impersonation of real companies: Using legitimate company infrastructure to send messages
- Community infiltration: Creating long-term presence in developer communities to build credibility
- Personalized exploits: Custom malware for high-value targets rather than generic packages
Supply Chain Attacks Beyond Packages
While PyPI and npm are current vectors, future attacks might exploit:
- GitHub repositories: Compromising legitimate projects and injecting malicious code
- Docker images: Malicious container images in registries
- IDE extensions: Malicious extensions for VS Code, JetBrains IDEs
- Build tools: Compromised CI/CD pipelines that inject malware during the build process

Industry Response and Detection Efforts
It's not all bad news. Security companies, platform operators, and governments are taking action.
Registry Protections
npm and PyPI have implemented various protections:
- Automated scanning for malicious packages: Using static analysis and behavioral analysis
- Reputation systems: Flagging newly created accounts or packages with suspicious patterns
- Verified publishers: Allowing maintainers to verify their identity and mark packages as official
- Package removal procedures: Rapid takedown of malicious packages when discovered
These protections help, but they're not perfect. The sheer volume of packages makes it impossible to catch everything, and sophisticated attackers can sometimes bypass automated detection.
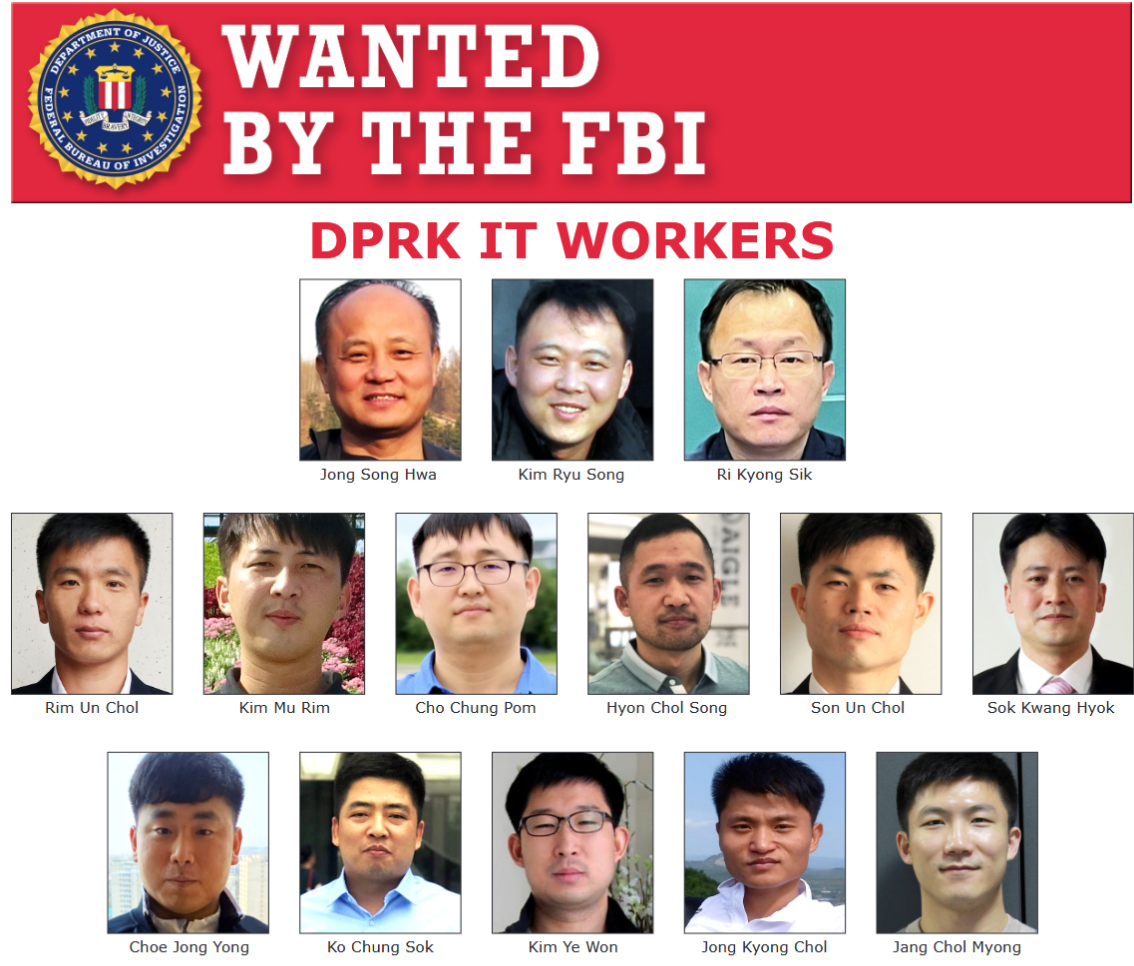
Government and Law Enforcement Response
Various government agencies and law enforcement organizations are tracking these operations:
- FBI and Cybersecurity and Infrastructure Security Agency (CISA) issue advisories about known North Korean campaigns
- Department of Treasury sanctions individuals and organizations involved in cyber operations
- International law enforcement coordinates investigations and attempts to disrupt operations
However, the effectiveness of these measures is limited by the fact that North Korea operates outside normal international jurisdiction.
Academic and Security Research
Security researchers continue to publish findings about Operation Dream Job and similar campaigns. This research helps developers and organizations understand threats and improve defenses. Services like Reversinglabs, Mandiant, CrowdStrike, and others publish threat intelligence that organizations can use to protect themselves.

Real-World Impact: Case Studies and Victim Stories
While specific victim stories are often confidential, the security community has documented various Operation Dream Job compromises:
Pattern 1: The Crypto Drain
Multiple documented cases show developers who received fake job offers, completed the coding challenge, and within hours or days noticed their cryptocurrency wallets were empty. In some cases, the developers had hardware wallets with significant funds. After installation of malware, their hardware wallet was somehow compromised (possibly through a keystroke logger capturing their PIN).
Losses ranged from a few thousand dollars to over $100,000 in a single case.
Pattern 2: The Extended Access
Some victims didn't notice immediate losses because the attacker was patient. Instead of stealing cryptocurrency immediately, the malware established persistent access. Over months, the attacker could monitor the victim's system, wait for lucrative opportunities (like a large cryptocurrency purchase or a business transaction), and strike when the timing was optimal.
This approach is particularly effective because the victim might not realize they've been compromised for a long time.
Pattern 3: The Supply Chain Propagation
The most dangerous cases are when compromised developers don't immediately notice they've been infected and continue their work. If they install the malicious package in a project they're working on for an employer, the malware could propagate to:
- The entire company's codebase
- Every server or machine that runs that code
- Every customer or client who uses the software
This turns a single victim into a potential vector for compromising an entire organization.

Practical Checklist: Are You Being Targeted?
Here's a practical checklist to help you assess whether you might be at risk:
Vulnerability Assessment
- You're a software developer (JavaScript, Python, Go, Rust, etc.)
- You have publicly visible LinkedIn or GitHub profiles
- You work in or have interest in cryptocurrency or blockchain
- You have cryptocurrency holdings
- You use open-source software and haven't audited your dependencies recently
- You don't use hardware wallets or multi-factor authentication
- You've never attended security training
- Your organization doesn't have a secure code review process
If more than half of these apply to you, you're in a higher-risk group.
Response Actions
If you're concerned about potential risk or compromise:
- Audit your dependencies now: Go through every project you're working on and verify the legitimacy of dependencies
- Check your accounts: Look for unauthorized access to GitHub, npm, PyPI, or other platforms
- Secure your cryptocurrency: If you have holdings, move them to a hardware wallet immediately
- Enable 2FA everywhere: Start with your most important accounts (email, exchanges, GitHub)
- Change critical passwords: Focus on accounts that have access to money or infrastructure
- Run malware scans: Use reputable security software to scan your development machines
- Monitor unusual activity: Check your crypto exchange transaction history, bank statements, and system activity logs
The Human Factor: Why Social Engineering Remains Effective
All the technical defenses in the world won't help if you fall for a social engineering attack. And here's the uncomfortable truth: social engineering is remarkably effective because it exploits human psychology, not technical flaws.
When you're job hunting, you're in a vulnerable state. You might be:
- Financially stressed: The job market is competitive. Better salary is tempting.
- Mentally excited: A job offer creates a dopamine response. Your guard is down.
- Time-pressured: You want to move quickly through the hiring process.
- Trusting: You assume that job postings and recruiters are legitimate by default.
- Eager to prove yourself: You want to demonstrate your skills and show you're the right fit.
All of these factors make you more likely to take risks you wouldn't normally take. The attacker knows this. They're deliberately using psychological tactics to manipulate you.
The defense against social engineering is awareness and healthy skepticism. Not paranoia—that's exhausting and unhelpful. But healthy skepticism means:
- Verifying information independently before taking action
- Trusting your instincts when something feels off
- Asking questions and being willing to slow down the process
- Assuming malicious intent until you've verified otherwise
The recruiting team at a legitimate company will understand this skepticism and support you being cautious. They'll provide verification information. They'll be patient. They'll explain the process clearly.
A scammer will pressure you, create artificial urgency, and get irritated if you ask too many questions.
Building a Security-First Developer Culture
If you're in a position of leadership—whether as a team lead, security manager, or C-level executive—you have a responsibility to build a security-first culture.
This doesn't mean making security so burdensome that developers can't do their jobs. It means integrating security thinking into everyday decisions.
What This Looks Like
In hiring: Screen candidates on official company channels. Use verified recruitment services. Clearly communicate the interview process and make it easy for candidates to verify they're talking to your company.
In development: Implement dependency reviews as part of code review. Ask questions about new packages before they're merged into production. Use automated tools to flag suspicious packages.
In training: Regularly educate team members about threats. Make it safe to report suspicious activity without blame. Celebrate people who caught potential attacks.
In incident response: When something goes wrong, treat it as a learning opportunity, not a failure. Document what happened, improve processes, and share learnings across the organization.
In tools: Invest in security tools that make secure practices the path of least resistance. If it's harder to do insecure things than secure things, developers will naturally make better choices.
Conclusion: Staying Secure in an Insecure World
Operation Dream Job is real, it's active, it's getting more sophisticated, and it's specifically targeting people like you. There's no way around that reality.
But here's the good news: knowing about the threat puts you ahead of most potential victims. You can implement technical defenses, you can practice healthy skepticism about job offers, and you can help protect your organization by raising awareness.
The threat isn't going away. Nation-states have too much incentive to fund cyber operations through cryptocurrency theft. But you can dramatically reduce your personal risk by:
- Auditing your dependencies right now
- Securing your cryptocurrency with a hardware wallet
- Enabling multi-factor authentication on all critical accounts
- Verifying job opportunities independently before engaging
- Never executing untrusted code on your main development machine
- Staying informed about active threats through security advisories
These steps take hours, maybe a day of your time. The cost of being compromised—losing cryptocurrency, compromising your employer, having your identity stolen, losing access to your accounts—is measured in tens of thousands of dollars or more.
The math is straightforward. Invest in your security now, and you'll have eliminated most of your risk. Ignore the threat, and you're betting against some of the most well-resourced attackers in the world.
Choose wisely.
FAQ
What is Operation Dream Job exactly?
Operation Dream Job is an ongoing campaign created by North Korean state-sponsored hackers (the Lazarus Group) that began around 2020. The attackers create fake job postings on LinkedIn targeting software developers, particularly those in the cryptocurrency and blockchain industries. During the fake "hiring process," they ask candidates to complete coding challenges that actually contain malicious code designed to steal cryptocurrency, credentials, or establish backdoor access to the victim's systems. The campaign has evolved significantly, with the latest variant (Graphalgo) discovered in May 2025 using malicious dependencies hidden in legitimate code repositories on PyPI and npm.
How does the Graphalgo variant specifically work?
Graphalgo is a new variant of Operation Dream Job that takes legitimate, bare-bone coding projects and injects malicious dependencies into them. The attacker takes a real project template, keeps its actual functionality intact, and adds a malicious package dependency that gets installed when a developer runs npm install or pip install. The malicious packages are designed to mimic legitimate libraries like graphlib or biglib, making them harder to detect. When the code runs, the malicious dependency executes silently in the background, potentially stealing cryptocurrency wallet access, credentials, or API keys. Security researchers found approximately 200 such malicious packages across npm and PyPI repositories.
Why are JavaScript and Python developers specifically targeted?
JavaScript is the most popular programming language globally, used across web development, Node.js backends, browser extensions, and desktop applications. Python is dominant in data science, machine learning, DevOps, and blockchain development. Attackers target these communities because they offer the widest reach and highest concentration of high-value targets. Additionally, both JavaScript and Python developers commonly work with cryptocurrency and Web 3 technologies, making them more likely to have cryptocurrency wallets with significant assets. Both ecosystems also encourage dependency reuse, creating multiple attack surfaces within a single project.
What are the most obvious red flags when a recruiter contacts me about a job opportunity?
Red flags include: salary significantly above market rate (20-50% higher), rapid progression through the hiring process skipping normal steps like phone screens or video interviews, communication exclusively through LinkedIn rather than company email, grammatical errors or awkward phrasing, inability to verify the company's existence or legitimacy through independent searches, requests to install and execute code immediately without review time, dependencies on packages you don't recognize, requests for API keys or credentials during the "coding challenge," and pressure to move quickly through the process. Real hiring managers don't need to pressure candidates or overpay to attract developers. If something feels off, it probably is.
How can I verify that a job opportunity is legitimate?
Contact the company independently using their official website—don't use contact information provided by the recruiter. Call their main phone number, not a number they gave you. Ask to be connected to the hiring manager directly. Look up the recruiter on the company's official website and LinkedIn to verify they actually work there. Check the company's official social media accounts and job posting sites to see if the position is listed. Ask the recruiter for detailed information about the company structure, the team you'd be joining, and the person who would be your manager, then verify these details independently. If the company is legitimate, they'll understand and support this verification process.
What should I do if I've already downloaded and executed code from a suspicious job offer?
Immediately: Change all passwords for critical accounts (email, GitHub, npm, crypto exchanges), enable multi-factor authentication on all accounts, check your cryptocurrency wallet and accounts for unauthorized transactions, scan your computer for malware using reputable security software, revoke all API keys and authentication tokens and generate new ones, review your SSH keys and certificates for unauthorized additions, check your account activity logs on GitHub, npm, and other services for unauthorized access, and notify your employer's security team if the code was for your work. Don't delay—malware can drain accounts or establish persistent access within hours. Contact your cryptocurrency exchange immediately if you notice any unauthorized activity, and consider moving funds to a fresh, secure wallet if you have substantial holdings.
How can I protect myself going forward besides just being cautious about job offers?
Technical protections include: using a hardware wallet for cryptocurrency holdings, enabling multi-factor authentication on all critical accounts (especially email, exchanges, GitHub), auditing dependencies in every project you work on before installing, using tools like npm audit and bandit to check for vulnerabilities, running untrusted code in isolated virtual machines or containers rather than on your main system, using environment variables and secrets management tools instead of hardcoding credentials, keeping software and systems patched and updated, using reputable antivirus or endpoint security software, avoiding installing browser extensions from unverified sources, and regularly rotating API keys and authentication tokens. Culturally, staying informed about active threats through security advisories, attending security training, and sharing threat intelligence with colleagues multiplies your defenses.
What's the connection between North Korea and Operation Dream Job?
The Lazarus Group, which runs Operation Dream Job, is a state-sponsored hacking organization backed by North Korea's government. North Korea is under international sanctions that restrict its access to traditional banking and international financial systems. This creates an economic incentive for the government to use cyber operations for revenue generation. According to security and intelligence agencies, North Korean cyber operations have generated hundreds of millions of dollars over the past decade. Operation Dream Job is one component of this broader strategy, specifically targeting cryptocurrency holdings and blockchain infrastructure. Understanding this context explains why the campaign is so sophisticated, persistent, and well-resourced—it's not a crime ring, it's a government-backed operation treating cyber theft as a national revenue source.
Are large organizations and enterprises also targeted, or just individual developers?
Both. While Operation Dream Job primarily targets individual developers for direct cryptocurrency theft, successful compromises of developers have historically led to broader organizational breaches. If an attacker successfully compromises a developer who has access to production systems, company repositories, or infrastructure, they can potentially establish access to the entire organization. For this reason, enterprises are increasingly at risk from Operation Dream Job. If a developer at your company falls victim to the scam and unknowingly installs malware that they then use in company work, the malware could propagate throughout your entire infrastructure. This makes organizational security awareness and secure code practices critical defensive measures.
What is the likelihood this threat will decrease in the future?
Unfortunately, the threat is likely to increase or at minimum remain at current levels. The economic incentive for North Korea is strong—the organization needs funding that it can't acquire through traditional means due to sanctions. The attack method is highly scalable and requires relatively low technical sophistication to execute at scale. Detection is difficult because the attacks exploit human psychology rather than technical vulnerabilities. New programming languages and ecosystems can be targeted as they grow (Golang, Rust, etc.). Therefore, the security community should expect continued evolution of Operation Dream Job and similar campaigns, with increasing sophistication in social engineering tactics, supply chain attacks, and evasion techniques. The defense is an ongoing arms race, not a problem with a final solution.
Conclusion
The threat landscape for software developers has fundamentally changed. You're no longer just competing in a technical job market—you're potentially a target for nation-state cyber operations. Operation Dream Job represents a calculated, well-resourced, and persistent threat that will continue to evolve.
But knowledge is power. By understanding how the attacks work, recognizing the warning signs, implementing technical defenses, and building security awareness into your personal and organizational practices, you can dramatically reduce your risk.
Start today. Audit your dependencies. Secure your cryptocurrency. Enable multi-factor authentication. Verify job opportunities. Share this information with colleagues. The hour you spend on these actions could prevent losses worth tens or hundreds of thousands of dollars.
The attackers are patient, sophisticated, and well-funded. Your best defense is staying informed and taking action before you become a victim.
Stay secure.

Key Takeaways
- Operation Dream Job is a North Korean state-sponsored campaign that evolved with Graphalgo variant in May 2025, injecting malicious dependencies into legitimate code repositories on PyPI and npm.
- Approximately 200 malicious packages have been discovered spoofing legitimate libraries, making supply chain attacks a critical threat to developers.
- JavaScript and Python developers are primary targets due to high cryptocurrency adoption, broad system access, and established dependency management practices.
- Technical defenses include hardware wallets for cryptocurrency, multi-factor authentication, dependency auditing, and sandboxed code execution for untrusted projects.
- Social engineering remains the most effective attack vector, with fake job opportunities bypassing technical defenses through psychological manipulation and trust-building tactics.
Related Articles
- N-Day Vulnerabilities: Why Patched Exploits Are Now Your Biggest Security Risk [2025]
- 6.8 Billion Email Addresses Leaked: What You Need to Know [2025]
- Apple Zero-Day Flaw CVE-2026-20700: What You Need to Know [2025]
- How Hackers Are Using AI: The Threats Reshaping Cybersecurity [2025]
- Lumma Stealer's Dangerous Comeback: ClickFix, CastleLoader, and Credential Theft [2025]
- Trenchant Exploit Sale to Russian Broker: How a Defense Contractor Employee Sold Hacking Tools [2025]
![North Korean Job Scammers Target Developers with Fake Interviews [2025]](https://tryrunable.com/blog/north-korean-job-scammers-target-developers-with-fake-interv/image-1-1771256372463.jpg)



