The New Old-School Threat: Why Hackers Love Paper
You'd think cryptocurrency—built on cutting-edge encryption and blockchain technology—would be immune to threats delivered by the postal service. But here's the thing: sometimes the oldest tricks work best.
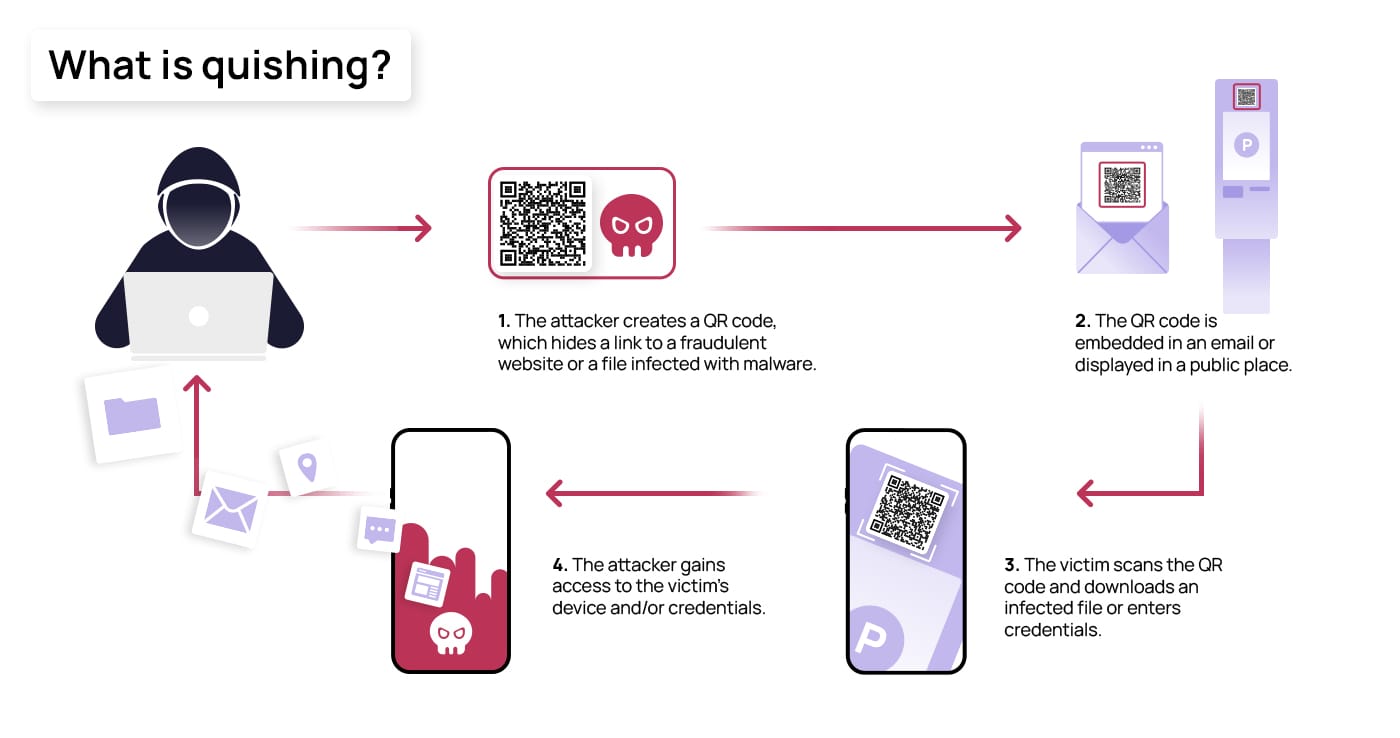
Cybercriminals are abandoning email for something far more tangible. They're printing letters. Real, physical envelopes arriving in mailboxes with urgent warnings and QR codes that link straight to fake cryptocurrency wallet authentication pages. It sounds almost quaint, like a phishing attack from 2005. But the simplicity is exactly why it works.
Over the past year, security researchers have documented an increasing number of these campaigns targeting hardware wallet owners. The letters appear to come from legitimate companies like Trezor and Ledger, claiming urgent security checks are required. Victims scan the QR code, land on a professional-looking website, and within minutes, they've handed over their wallet recovery phrase—the digital equivalent of a master key to their cryptocurrency.
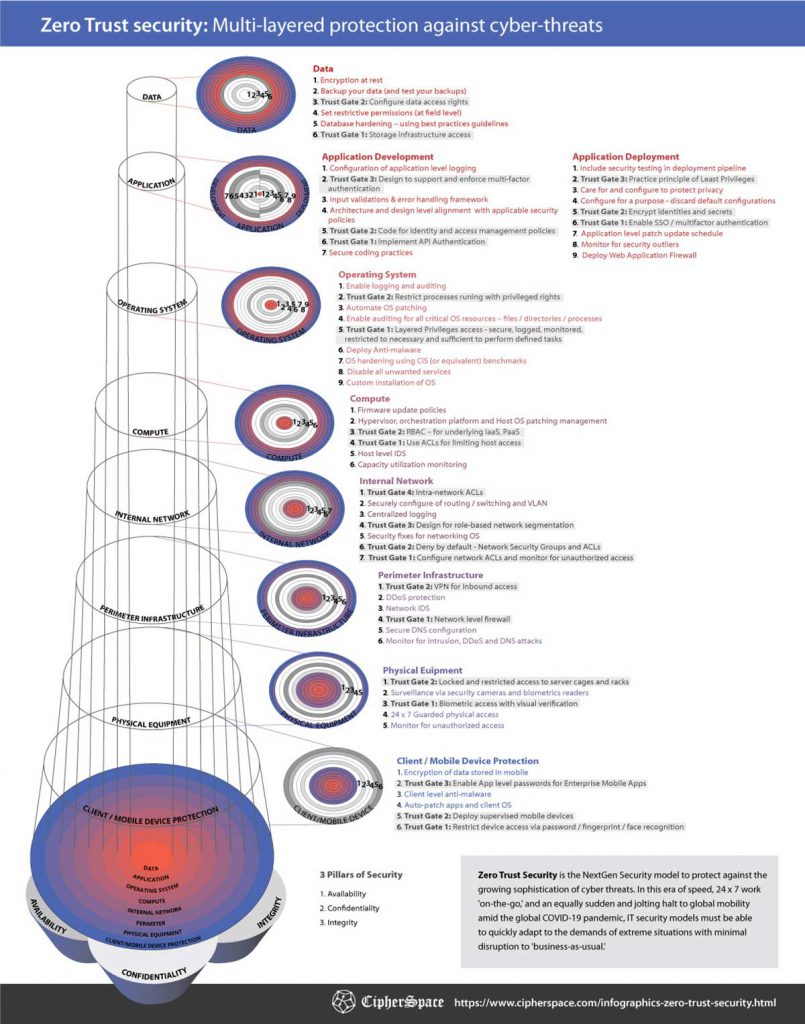
What makes this attack vector so effective? It bypasses almost every digital security layer we've built. Spam filters don't catch postal mail. Two-factor authentication doesn't protect against social engineering. Firewalls mean nothing when the threat arrives in your letter box.
The psychology is equally brilliant. Email phishing attempts have trained us to be suspicious. But physical mail still carries an air of legitimacy. When something shows up at your address, it feels official. It feels urgent. And for many crypto holders, especially those who've already been burned by digital threats, a letter in hand seems more trustworthy than a message in their inbox.
This shift represents something important about cybersecurity in 2025: attackers will exploit whatever channel is least defended. And right now, physical mail is largely undefended.
TL; DR
- New attack vector: Cybercriminals are sending physical letters with malicious QR codes to cryptocurrency wallet owners instead of relying on email phishing.
- The targets: Primarily Trezor and Ledger hardware wallet owners, with letters claiming urgent authentication or transaction checks are required.
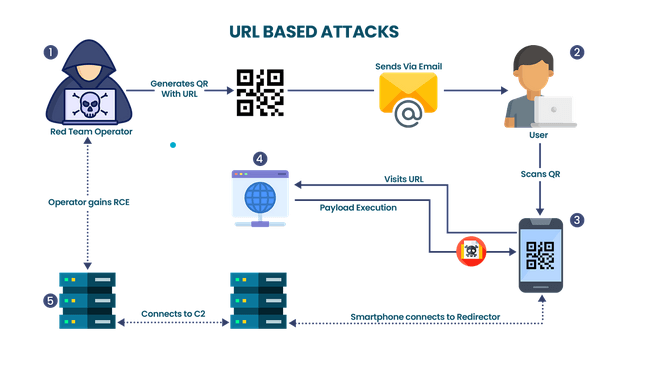
- The mechanism: QR codes direct victims to fake credential harvesting websites that mimic official wallet setup pages and prompt users to enter their recovery phrase.
- The impact: A wallet recovery phrase gives attackers complete control over all funds stored in that wallet, allowing instant theft without further authentication.
- The why: Physical mail bypasses email filters, spam detection, and seems more legitimate than digital phishing, making it devastatingly effective.
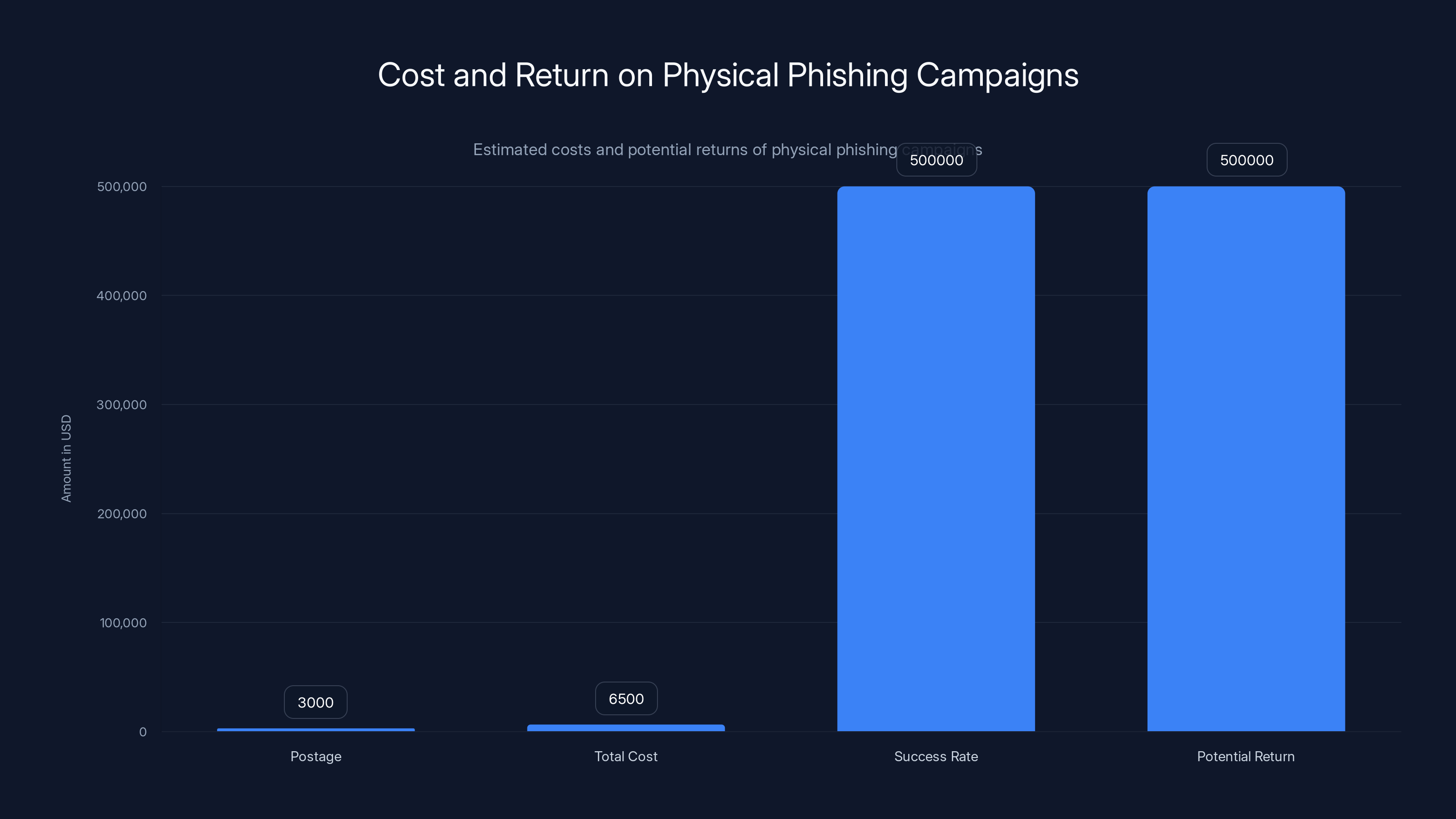
Physical phishing campaigns, though costly, can yield a 60:1 return on investment, making them attractive despite higher upfront costs. Estimated data.
How the Physical QR Code Scam Actually Works
Let's walk through exactly what happens when one of these letters arrives at your door.
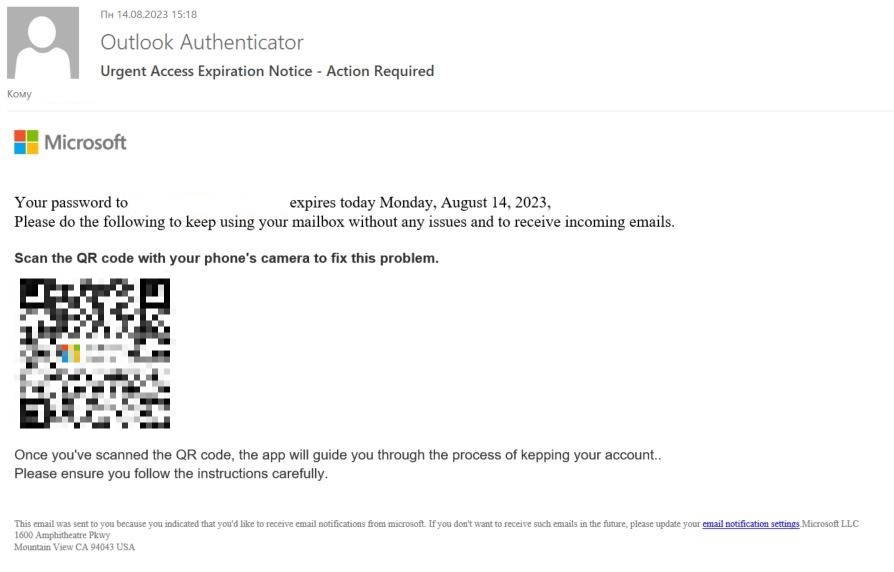
The envelope looks professional. It carries real postage. The return address might reference something like "Trezor Security Team" or "Ledger Authentication Services." Inside is a single page with an urgent message.
The letter claims one of two things: either an "Authentication Check" is required for continued access, or a "Transaction Check" needs completion. The language is carefully crafted to create pressure. It mentions deadlines—often stretching into early 2026—and warns of consequences. Failure to comply could restrict wallet access. Transactions might be blocked. Your funds could be locked.
Then comes the call to action: scan the QR code below to verify your identity.
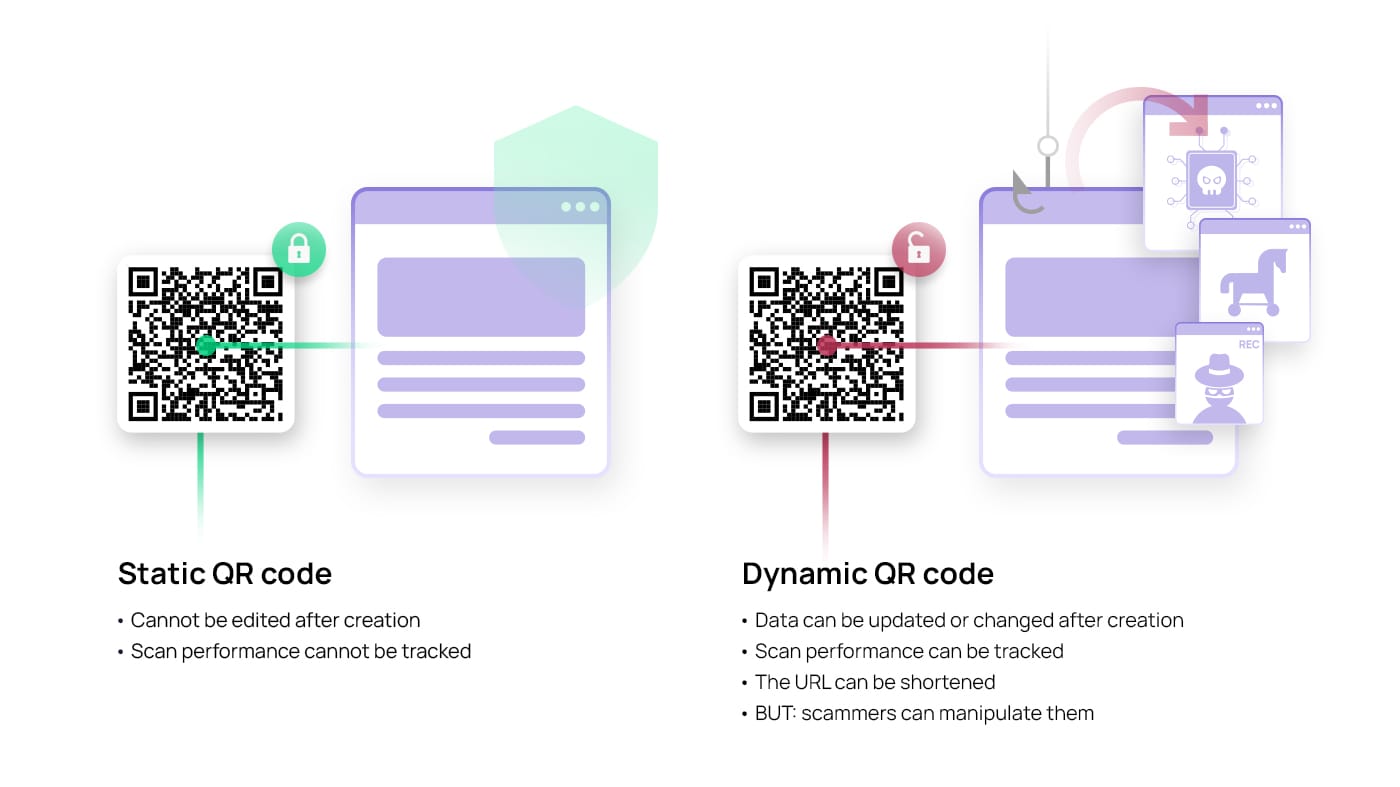
The moment a victim scans the code with their smartphone, they're taken to a fraudulent website. But here's where the sophistication kicks in. This isn't some obviously fake site with broken English and blurry logos. The attackers have invested time in replicating the official Trezor or Ledger setup interface. The design matches. The language matches. The branding matches.
On this fake page, victims are prompted to verify ownership of their wallet. They're told this is a standard security procedure. The site accepts 12-word, 20-word, or 24-word recovery phrases—matching the formats that legitimate hardware wallets use. There's typically a warning about entering their phrase, which sounds like security advice but is actually there to make the request seem more legitimate.
When a victim enters their recovery phrase and clicks "verify," they've essentially handed the attacker the master key to their wallet.
The technical backend is simple but effective. The entered phrase is sent through an API endpoint controlled by the attackers. From there, they can import the wallet into any tool they want—Metamask, my Ether Wallet, or any number of crypto software wallets. And then they can move the funds out immediately.
No additional authentication is needed. No second factor. No alert to the victim. The money is gone in minutes.
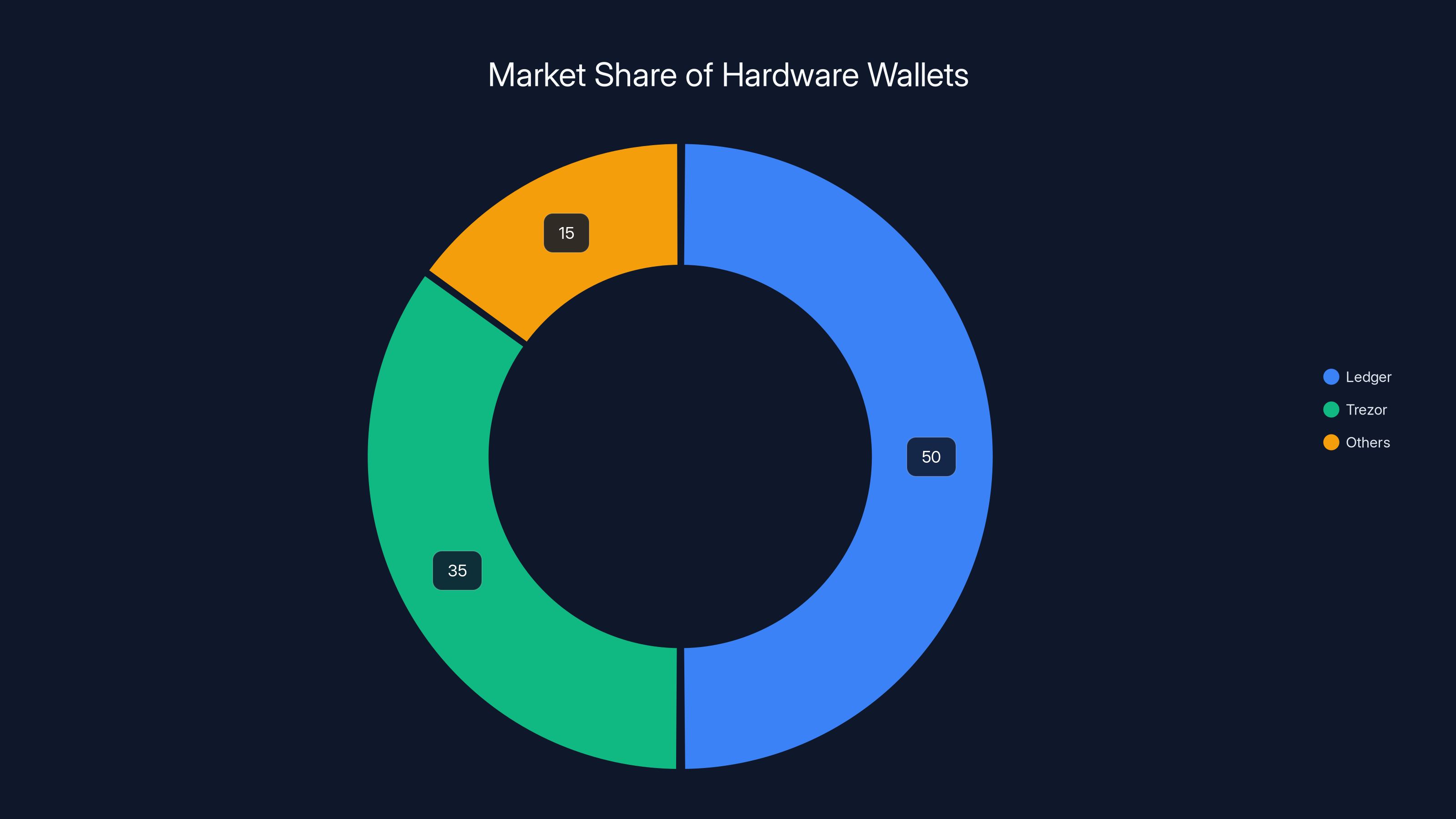
Ledger and Trezor dominate the hardware wallet market, together holding an estimated 85% share, making them prime targets for phishing attacks. (Estimated data)
Why Physical Mail Bypasses Our Digital Defenses
Cybersecurity has become incredibly sophisticated. Email systems use machine learning to detect phishing. Browsers warn you about suspicious websites. Your phone probably alerts you to malicious links. Companies deploy multiple layers of detection.
But none of this works on a piece of paper.
This is actually a known principle in security research called the attack surface paradox. The more sophisticated our defenses become in one channel, the more attackers migrate to less-defended channels. Email filters improved? Move to SMS. SMS defenses improved? Move to WhatsApp. Social media defenses improved? Move to physical mail.
There are a few reasons physical mail is so effective right now for cryptographic attacks.
First, there's the legitimacy bias. Our brains evolved in a time when physical documents meant something. They required resources to produce. They required postage. A letter in your mailbox carries weight—sometimes literally. When an email arrives, your brain immediately goes into skeptical mode. When paper arrives, your brain defaults to trust until proven otherwise. This is a cognitive bias that's incredibly hard to override.
Second, there's the personal touch. Receiving mail addressed specifically to you at your home address creates a sense of directed threat. It's not a mass email that went to thousands of people. This specific attacker went through enough effort to find your address and send this specific letter to you. That level of effort signals legitimacy.
Third, there's the effort barrier. It's relatively expensive to send physical mail at scale. A phishing email costs basically nothing to send to a million people. A physical phishing campaign requires envelopes, paper, stamps, and postal service. This scarcity of volume makes each letter feel more valuable and therefore more real.
Finally, there's the time delay. An email arrives and can be acted on immediately, and that creates skepticism—why is this urgent? But mail takes days to arrive. By the time the recipient gets the letter, there's psychological distance from whenever the attacker originally sent it. The natural assumption is that if this company bothered to mail something, it must be genuinely important.
The result is a perfect storm of psychology and technology. A threat that's cheaper to execute than high-tech hacking but more effective than most digital phishing.
The Recovery Phrase: Why It's the Keys to the Kingdom
To understand how dangerous these scams are, you need to understand what a recovery phrase actually is.
When you set up a hardware wallet like Trezor or Ledger, the device generates a random sequence of words—typically 12, 18, or 24 words depending on the security level you choose. These words are derived from a cryptographic process called BIP39 (Bitcoin Improvement Proposal 39), which converts a random number into a memorable phrase.
This phrase is called a recovery phrase, seed phrase, or mnemonic. It's the foundation of everything.
Here's the crucial part: that phrase contains all the mathematical information needed to recreate your wallet from scratch. It's not just a password. It's not just an access code. It's the actual cryptographic seed that generates every private key for every address in your wallet.
If you lose your hardware wallet, the recovery phrase is the only thing you need to restore it on a new device. Import the phrase into a new Trezor or Ledger, and everything comes back exactly as it was.
But there's a massive security implication: if anyone else has your recovery phrase, they have complete control over your wallet. They don't need your hardware device. They don't need your PIN. They don't need anything else. They can import the phrase into their own wallet and move all your cryptocurrency to an address they control.
The damage is instantaneous and irreversible. Blockchain transactions are immutable. Once your funds are transferred to an attacker-controlled address, there's no way to reverse it. The transaction can't be cancelled. The funds can't be recovered. The attacker now owns them legally from a blockchain perspective.
This is why hardware wallet manufacturers are so insistent that users never, ever enter their recovery phrase into any software, website, or application. The phrase is supposed to be written down on paper (kept in a safe place) or memorized. That's it. Nothing else.
When victims of these physical phishing attacks enter their recovery phrase into the fraudulent website, they've essentially signed a digital deed transferring all their cryptocurrency to the attacker. And unlike a regular deed, there's no authority to appeal to. The blockchain is the final arbiter, and it says the attacker now owns those funds.
This is the core equation of these attacks. Get the phrase, get complete control. Simple as that.

Email phishing success rates have dramatically declined from 0.5% in 2015 to 0.01% in 2023 due to enhanced security measures and increased user awareness. Estimated data.
Trezor and Ledger: The Primary Targets
These phishing campaigns specifically target two companies: Trezor and Ledger. Why? Because they're the most popular hardware wallet manufacturers by far.
Trezor, owned by Satoshi Labs, has been in the business of hardware wallet design since 2013. Their devices are known for being user-friendly and offering open-source code for security verification. Ledger, founded in 2014, is even larger by market share, with millions of devices in circulation globally.
Together, these two companies probably represent 80-90% of the hardware wallet market. When you're a criminal targeting hardware wallet users, targeting Trezor and Ledger makes simple mathematical sense. That's where the targets are.
Research has documented specific malicious domains created to mimic Trezor and Ledger infrastructure. One domain designed to look like a Ledger authentication page has already been taken offline by security researchers. A Trezor-themed domain remains accessible but has been flagged by Cloudflare as phishing infrastructure.
The sophistication of these fake sites is noteworthy. The attackers didn't just throw together something obviously fake. They've studied the official setup flows. They've replicated the visual design. They've matched the language and tone. Someone who received one of these letters and scanned the QR code would see a website that, for all practical purposes, looks identical to the real thing.
Both Trezor and Ledger have issued warnings about these campaigns. They've publicly stated that they will never ask users to enter recovery phrases online, and they encourage users to report any suspicious mail. But the warnings only reach people who follow their social media accounts or visit their websites regularly. Many cryptocurrency holders, especially older users or those less tech-savvy, might not see these warnings until after they've already fallen victim.
This creates a targeting advantage for the attackers. The people most likely to fall for a phishing attack—those less familiar with cryptocurrency security norms—are also the least likely to have seen the warnings.
How Your Mailing Address Got Leaked
The obvious question: how did attackers get your home address in the first place?
The answer almost certainly involves previous data breaches.
Trezor experienced a data breach in 2020 that exposed customer email addresses. Ledger suffered a much more serious breach in 2020 that exposed customer email addresses, names, phone numbers, and in some cases, mailing addresses. These breaches weren't secret—they were widely reported. But many users might not have realized the full extent of what was compromised.
Security researchers have found evidence suggesting that the mailing addresses used in current phishing campaigns match the data exposed in those previous breaches. In other words, attackers are taking decade-old leaked databases and weaponizing them for physical mail attacks.
This highlights a critical principle in cybersecurity: the value of compromised data doesn't expire. Information stolen in 2020 might not be useful for immediate attacks. But it remains in criminal databases, waiting for the right attack vector to make it valuable again.
Beyond Trezor and Ledger directly, there are other potential sources. Cryptocurrency exchanges sometimes experience breaches. Payment processors that sell hardware wallets sometimes leak customer data. Even the postal service itself has been compromised before. Any company that sold you a hardware wallet and captured your mailing address is a potential source.
The frightening part: you might not even know your address was leaked. Many data breaches go undetected for months or years. Victims aren't notified. The data simply circulates in criminal underground forums, where people with bad intentions can purchase it.

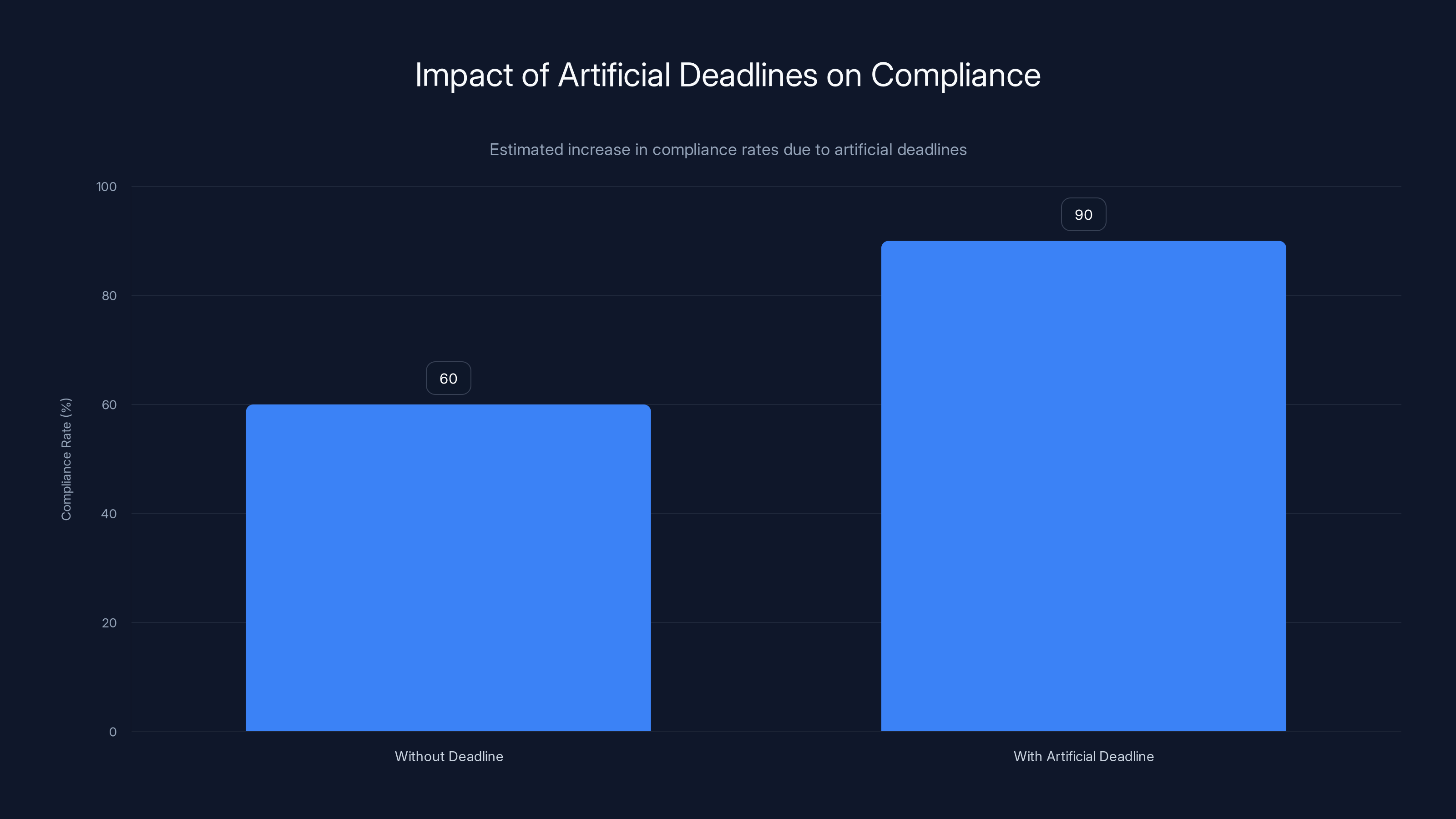
Artificial deadlines can increase compliance rates by 30-40%, as they create a sense of urgency that prompts quicker decision-making. Estimated data.
The Psychology of Postal Phishing
Why do so many people fall for these scams despite the warnings? The answer lies in how our brains are wired.
A phenomenon called authority bias makes us trust official-looking documents more than we should. When something arrives on letterhead (even fake letterhead) with official-sounding language, our critical thinking takes a back seat. We assume whoever sent this had the authority and resources to do so properly.
There's also urgency bias. The letters contain deadlines. They claim that failure to act will result in consequences. Our brains are evolutionarily wired to respond to immediate threats by taking action quickly. When something feels urgent, we think less carefully.
Another factor is confirmation bias. If you've ever had actual issues with your cryptocurrency wallet—maybe you forgot a password, or you genuinely had security concerns—this letter confirms your fears. It's not surprising that there's an issue. It makes sense. Of course there would be a verification process.
There's also the contrast effect. You probably get dozens of emails trying to scam you every week. Your email filters catch most of them. But this letter? This one made it through multiple layers of postal service. It arrived at your physical address. It must have been harder to send. That contrast with the typical digital phishing makes it seem more legitimate.
Finally, there's social proof in reverse. You might assume that because you've heard of these companies (Trezor, Ledger), and these companies seem legitimate, anything claiming to come from them must be legitimate. You haven't heard of the vast majority of people being scammed. So you assume they're doing proper security checks.
All of these biases work together. Individually, any one of them might not fool you. But combined, they create a compelling narrative that makes victims let their guard down.
Identifying a Phishing Letter: What to Look For
Not every letter claiming to be from Trezor or Ledger is phishing. But how do you tell the difference?
First, check the logical impossibility. Has your wallet actually been flagged for issues? If your hardware wallet is sitting safely on your desk, and the device itself hasn't alerted you to anything, then no legitimate company would be sending you urgent security notices. Hardware wallets are designed to be self-contained secure devices. They don't need remote verification checks from the manufacturer.
Second, examine the request. Legitimate companies will never ask you to enter your recovery phrase into any website, software, or application. Never. Not even on an official-looking website. Not even with urgent warnings. This is a fundamental principle of cryptographic security that every legitimate hardware wallet manufacturer publicly commits to. If a letter asks you to do this (even implicitly), it's phishing.
Third, check the contact information. The letter should provide a phone number to verify authenticity. Call that number—but don't use the number from the letter. Instead, look up the official company contact information on their official website directly. Call that number instead. Ask them if they sent the letter. They'll tell you immediately if it's fake.
Fourth, look at the language quality. Professional companies employ professional writers. Phishing letters sometimes have subtle grammatical errors, awkward phrasing, or language that doesn't quite match the company's official tone. This isn't always reliable—some phishing is professionally written—but it's worth checking.
Fifth, examine the urgency. Phishing letters create artificial urgency. They mention tight deadlines, consequences, and account lockouts. But these are claims, not facts. Your hardware wallet will work exactly the same regardless of what any letter claims. No company can remotely lock your hardware wallet. It's not connected to the internet.
Sixth, be suspicious of physical mail from technology companies requesting digital authentication. Think about this logically: if the company wanted to verify you, they have your email address. They use email for everything else. Why would they suddenly resort to physical mail for something as critical as a security verification? They wouldn't. This is a red flag.

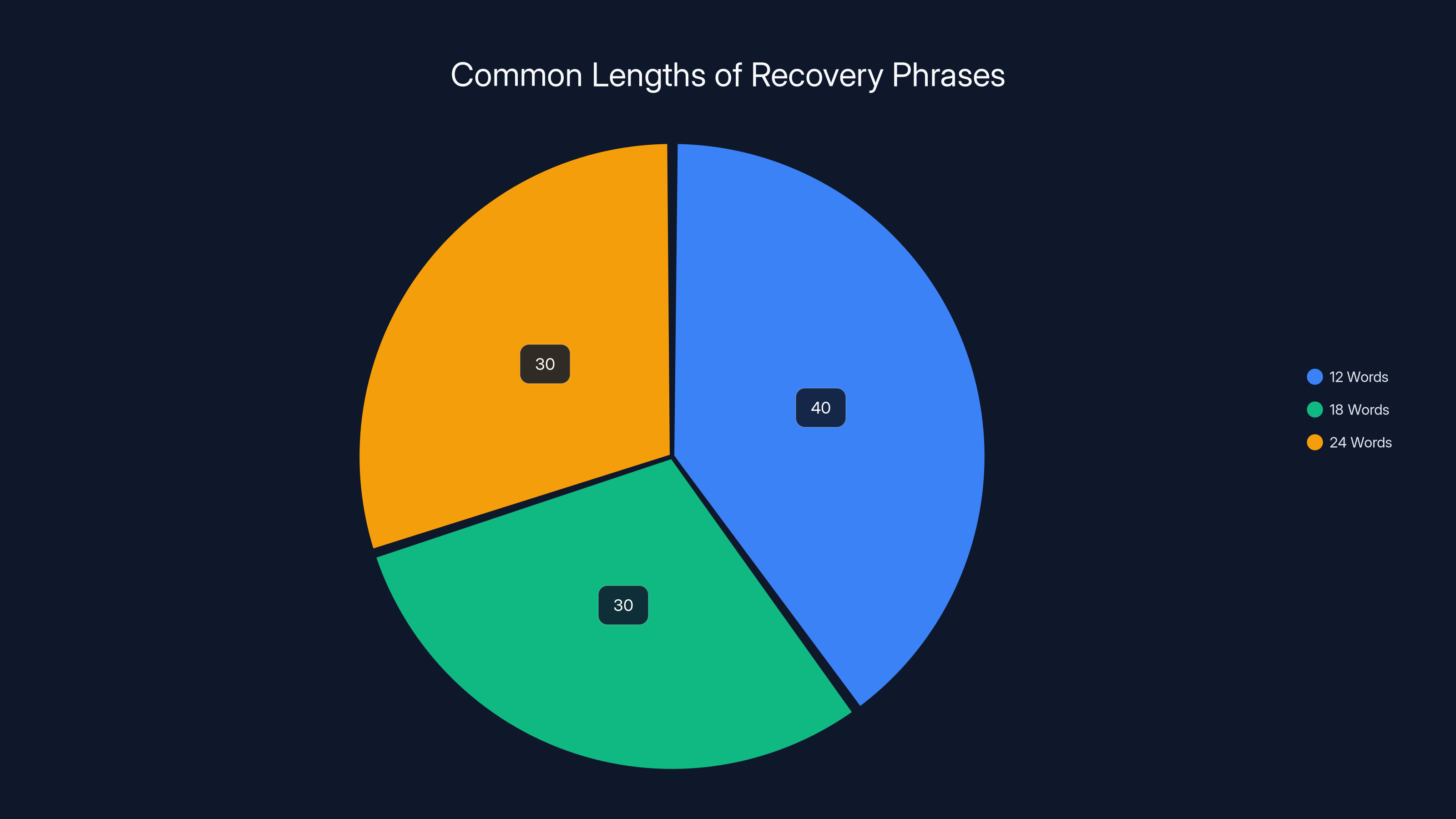
Recovery phrases are typically 12, 18, or 24 words long, with 12-word phrases being the most common. Estimated data.
What Happens If You've Already Compromised
If you've already scanned the QR code and entered your recovery phrase, don't panic. There are still steps you can take.
First, stop. Don't enter any additional information. Don't scan any more codes. If you're still on the fraudulent website, close the browser immediately.
Second, act immediately. If you entered your recovery phrase, the attacker now theoretically has the ability to drain your wallet. But they might not have done it yet. They might be waiting, hoping more victims enter their phrases so they can attack multiple wallets at once. Or they might be setting up infrastructure. The window of time between when they get access and when they actually steal funds can sometimes be minutes, but can sometimes be longer.
Third, move your funds. If you still have access to your hardware wallet via its legitimate interface, transfer all your cryptocurrency out immediately. Send it to a brand new wallet created from a new recovery phrase generated on a fresh, clean device. This has to be done from the legitimate hardware wallet itself, not through the compromised interface. The legitimate hardware wallet is still secure as long as no one has physical access to it.
Fourth, generate a new recovery phrase. On your hardware wallet device, look for an option to reset the wallet or generate a new seed. This process is different for Trezor and Ledger, so check the official manufacturer documentation. Once you've created a new seed, that old compromise recovery phrase becomes worthless to the attacker. Even if they have it, they can't access your funds because your wallet now uses a completely different seed.
Fifth, wipe the old wallet. Make sure you've successfully transferred all funds to the new wallet address, confirmed the transactions on the blockchain, and then reset or reinitialize your hardware wallet with the new seed phrase.
Sixth, report the scam. Contact Trezor or Ledger directly through official channels. Report the malicious domain to Cloudflare or other hosting providers. File a report with law enforcement (though international cryptocurrency theft is almost never prosecuted). Post in cryptocurrency security forums to warn others.
Seventh, update your security practices. Use a strong password manager. Enable two-factor authentication on all cryptocurrency exchanges. Keep your hardware wallet updated with the latest firmware. Be paranoid about recovery phrase security going forward.
The goal is to move faster than the attacker. If they haven't stolen your funds yet, and you move them first, you've effectively nullified the compromise.

How Attackers Scale Physical Phishing Campaigns
Physical mail is expensive, which seems like it would naturally limit how many people attackers can target. But in practice, these campaigns can still reach thousands of people.
Here's the economics. A single physical mail campaign targeting 5,000 people might cost approximately
That seems expensive until you consider the potential return. If the campaign has even a 1% success rate—which is low for phishing but entirely plausible for physical mail—that means 50 people enter their recovery phrases. If the average person targeted holds just
The math is simple: 60:1 return on investment.
In cryptocurrency, high-value targets are absolutely worth significant investment. Someone holding
This is why attackers are willing to send physical mail. It's not cheaper than email. It's more expensive. But it's dramatically more effective. The ROI on physical phishing is better than the ROI on digital phishing, which is why the channel is growing.
Attackers can scale by purchasing large batches of mailing addresses from previous breaches. A database of 100,000 leaked Ledger customer addresses is worth thousands of dollars in the criminal underground. Buy it, segment it (maybe focus on addresses in wealthy areas), print and mail to a subset, and wait for the money to roll in.
Some sophisticated criminal groups use A/B testing to optimize their phishing campaigns. They'll send slightly different versions of the letter to different segments. Different QR codes leading to slightly different fake websites. Different calls to action. Then they track which versions get higher conversion rates and scale those versions.
Others use multi-stage campaigns. The first letter is soft—just a warning about potential security issues, encouraging you to update security settings (which you don't actually do). Then a second letter arrives weeks later claiming the situation has become urgent. By the time the second letter arrives, victims are primed and more likely to take action.
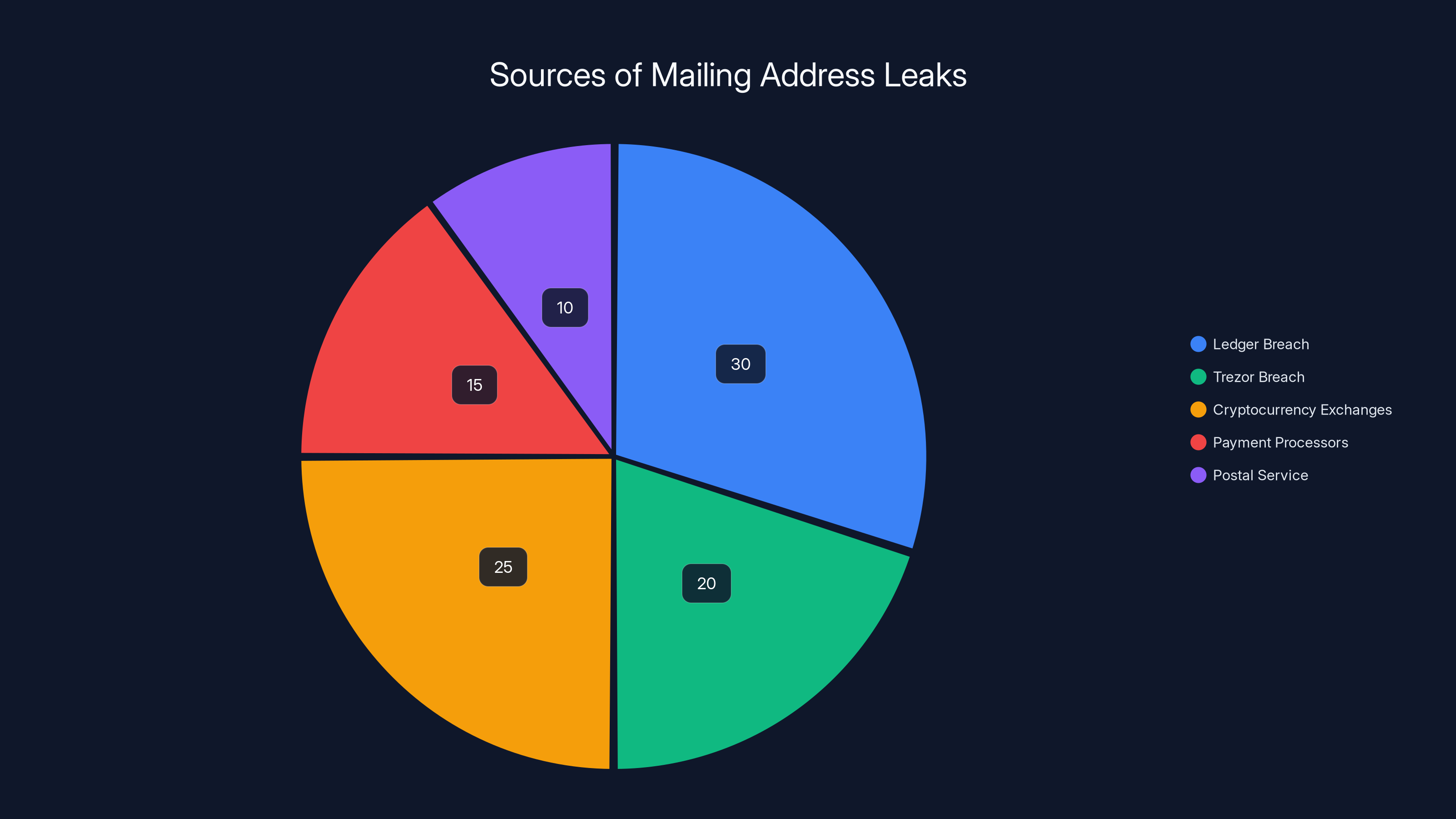
Estimated data shows Ledger and cryptocurrency exchanges as major sources of mailing address leaks, highlighting the widespread nature of data vulnerabilities.
The Role of Artificial Urgency and Deadlines
Every effective phishing campaign includes an artificial deadline. "Update by January 15, 2026 or your account will be locked." "Verify before December 31, 2025 or transactions will be blocked."
Why is this so effective?
It bypasses rational decision-making. When you have infinite time to verify something, you can think carefully. You can research. You can check official websites. You can call customer service. But when there's a deadline, you feel pressure to act now.
This is called temporal scarcity, and it's one of the most effective persuasion techniques known. Your brain literally processes information differently when it perceives time scarcity. You take more risks. You make less deliberate decisions. You trust your first instinct instead of questioning it.
Hardware wallet manufacturers could actually counteract this by publicly stating: "We will never send unsolicited mail asking for recovery phrases. We do not have security deadlines. Our security is passive and doesn't require ongoing verification." By removing the perception of legitimate deadlines, they could reduce effectiveness.
But many victims don't see these messages. And even if they did, the letter in hand still feels more urgent than a warning from a website they haven't visited in months.

Technical Defenses: What Actually Works
From a technical perspective, users can implement several defenses that make these attacks much less effective.
Multi-signature wallets are the gold standard. Instead of requiring just one recovery phrase to access funds, multi-signature wallets require multiple independent approvals. You might have one signature key on your Ledger, another on your Trezor, and a third on a third-party service. To move funds, an attacker would need to compromise all three. Even with your Ledger recovery phrase, they can't do anything without the other keys.
Watch-only wallets on a separate device create an additional layer. You keep your cryptocurrency on an offline hardware wallet, but you monitor it from a separate software wallet that can only view balances and addresses—it can't move funds. If you notice unusual activity, you know something's wrong before the attacker can steal anything.
Regular key rotation reduces the time window for exploitation. If you regenerate your wallet every 6 months with a new recovery phrase, then any leaked phrases become worthless. This is impractical for most users, but high-value targets sometimes do this.
Air-gapped signing means your fund-moving device is completely disconnected from the internet. An attacker might compromise your software, but they can't actually move funds without physical access to your offline device.
Endpoint protection software like Malwarebytes can detect and block the fake websites if you try to access them from a computer. It won't catch physical mail, but it can prevent you from entering your recovery phrase if malware redirects you even if you somehow got to the fake site.
Hardware firewall rules can block traffic to known phishing domains. If your home router has a blocklist of known malicious URLs, it will prevent access even if you click the link.
None of these are perfect. None of them stop a determined attacker with your recovery phrase. But they all add friction and reduce the attacker's advantage.

The Attacker Infrastructure Behind These Scams
When researchers investigate these campaigns, they find sophisticated infrastructure.
The fraudulent domains are typically registered through privacy-focused registrars that don't publicly display ownership information. They're hosted on bulletproof hosting providers—companies that knowingly host malicious content and don't cooperate with law enforcement takedown requests.
The fake websites themselves often use legitimate web builders and platforms that have been compromised or purchased. An attacker might buy a legitimate-looking WordPress theme, customize it to match Ledger's interface, and deploy it on cheap hosting in a jurisdiction with weak cybercrime enforcement.
The infrastructure often includes multiple redundancy. If one domain gets shut down, there are backups. If one hosting provider terminates service, the site moves to another. This is why researchers find multiple malicious domains associated with single campaigns.
The backend API endpoints—the servers that receive your recovery phrases—are often separate from the frontend website. This compartmentalization makes takedown harder. Shutting down one server doesn't stop the entire operation because the attacker has already copied the data elsewhere.
Sometimes attackers use cryptocurrency payment processors to collect funds that victims are tricked into sending. Sometimes they use mixers or tumblers to obfuscate the trail of stolen cryptocurrency. The technical sophistication is substantial.
Cyber threat intelligence firms have tracked some of these operations and found that the same attacker group runs multiple phishing campaigns simultaneously. They might run malicious Ledger domains, malicious Trezor domains, malicious hardware wallet retailer domains, and malicious exchange domains all under one operation.
They share infrastructure, techniques, and sometimes even mailing address lists. This suggests organized criminal networks rather than individual scammers, which explains the sophistication.

International Dimensions: This Isn't Just a US Problem
Physical phishing campaigns have been documented in multiple countries. Reports indicate campaigns in the United States, Europe, and Asia.
The fact that this is happening across multiple continents suggests either:
- Multiple independent criminal groups discovered this technique simultaneously
- One major criminal group is running coordinated campaigns across multiple countries
- Criminal groups are selling "phishing kits" that others deploy locally
The more likely scenario is a combination of all three. Some of the sophistication suggests organized international crime syndicates. But the technique is simple enough that local scammers can also implement it independently.
This makes it harder for law enforcement to respond. A local police department in the US can't pursue criminals in Eastern Europe or Southeast Asia. Postal service investigations are limited to domestic mail. Interpol involvement requires extreme cases.
For victims, this means there's virtually no law enforcement recourse. You can report the scam. Your report will go into a database. But unless you're a major victim with substantial resources to pursue your own investigation, nothing will happen.
This places the full burden of defense on users themselves. You have to protect yourself through awareness, good security practices, and quick response to compromise.

The Evolution of Attack Vectors: Why Email Failed
To understand why attackers switched to physical mail, it helps to understand why email phishing became less effective.
Email security has improved dramatically. Spam filters catch an enormous percentage of phishing attempts. Domain authentication protocols like SPF, DKIM, and DMARC make it harder to spoof legitimate company email addresses. Browser warnings alert users when they navigate to known phishing sites. Email sandboxing detonates suspicious attachments in isolated environments to detect malware.
Most importantly, user awareness has increased. People have gotten better at spotting phishing emails. They know not to click suspicious links. They know to hover over email addresses to see if they're real.
The result is that email phishing success rates have dropped. Attackers might send a million phishing emails but achieve less than a 0.01% success rate. The volume makes up for the low rate, but the channel is becoming less profitable.
Physical mail, on the other hand, remains largely undefended. There's no equivalent to spam filters for postal mail. Your mailbox accepts everything. There's no browser warning when you scan a QR code to a phishing site from physical mail because your phone has no way to know that the letter you received is suspicious.
As traditional channels become harder, attackers migrate to new ones. SMS phishing (smishing) increased as email phishing became harder. Social engineering and voice calls became more common. And now physical mail is getting serious attention.
This represents a predictable cycle. Attackers find a new channel. Defenses are built. Attackers find another new channel. We're currently in the phase where physical mail is relatively undefended, so attackers are exploiting it.

Best Practices for Hardware Wallet Security in 2025
Given these new threats, what's the right way to secure your cryptocurrency?
First, assume breach. Assume your mailing address has been leaked. Assume your email has been compromised. Assume previous vendors have had breaches. Operate as if adversaries know things about you. This mindset makes you more careful.
Second, compartmentalize. Don't keep all your cryptocurrency in one wallet. Use multiple hardware wallets. Split your holdings across different devices. If one is compromised, not all funds are lost.
Third, verify independently. Before trusting any communication claiming to be from Trezor or Ledger, verify it through an independent channel. Call their official phone numbers. Visit their official websites (type the URL yourself rather than clicking a link). Don't trust the contact information in the suspicious letter.
Fourth, keep firmware updated. Hardware wallet manufacturers regularly release firmware updates that patch security vulnerabilities. Don't ignore these. Keep your device updated.
Fifth, use strong passphrases. Many hardware wallets support additional passphrase protection beyond the recovery phrase. This adds an extra layer. An attacker with your recovery phrase can't access your funds without the passphrase.
Sixth, store recovery phrases securely. Write them down. Use Stainless steel backup cards if you want maximum durability. Store in a safe deposit box or home safe. Never store in cloud services. Never photograph them. Never digitize them unless using encrypted password managers with zero-knowledge architecture.
Seventh, be paranoid about QR codes. If you receive a physical letter asking you to scan a QR code, that's a massive red flag. Legitimate companies don't use QR codes for security-critical operations. Don't scan QR codes from unsolicited mail.
Eighth, monitor actively. Use blockchain explorers to periodically check your wallet addresses. Make sure the balances match what you expect. If something looks wrong, investigate immediately.
Ninth, educate yourself. Spend time understanding how cryptocurrency actually works. Understand what recovery phrases are, how they work, why they're dangerous if leaked. The more you understand, the harder you are to scam.
Tenth, educate others. If you know people with hardware wallets, share this information. These attacks succeed because victims don't understand the threat. Awareness is defense.

What Happens If the Industry Doesn't Respond
If hardware wallet manufacturers and the broader cryptocurrency security community don't respond effectively, these attacks will continue to grow.
More people will be victimized. More addresses will be compromised in data breaches and added to attacker mailing lists. Criminal networks will continue to refine their campaigns. Physical phishing for cryptocurrency will become as common as email phishing is today.
Some possible industry responses:
Hardware manufacturers could send proactive counter-mail. Trezor and Ledger could mail brochures to all known customers warning them about these attacks before the criminals do. A friendly letter from the company explaining the threat might be more effective than online warnings.
Cryptocurrency exchanges could implement watch lists. If suspicious addresses suddenly receive large transfers from known wallets, exchanges could flag this and ask for verification. This wouldn't stop the theft but might provide intelligence.
Law enforcement agencies could increase focus. International cooperation on cryptocurrency theft investigations is limited but could be improved. Tracking the money on the blockchain is actually easier than most crimes—once you know where the stolen funds go, you have a permanent record.
Postal services could partner with cybersecurity firms. The postal service could train mail carriers to recognize obvious phishing letters and flag suspicious mailings. They could provide education about reporting suspicious mail.
The cryptocurrency community could develop standards. There could be industry agreement that no legitimate company uses physical mail for security-critical operations. This would make any physical mail claiming to require authentication immediately suspicious.
Some of these are happening in limited ways, but there's no coordinated industry response yet.
The Broader Implications for Security
Physical mail phishing teaches us something important about security: the most sophisticated systems can be compromised by targeting human psychology rather than technical defenses.
Cryptography is strong. Hardware wallets are well-designed. The technology is sound. But you can't cryptographically secure against social engineering. You can't encrypt your way out of someone voluntarily giving you their recovery phrase.
This applies far beyond cryptocurrency. Banks might have excellent online security, but you can still be tricked into transferring money through physical mail. Companies might have strong computer security, but employees can be tricked into revealing credentials through printed forms. The most advanced technical systems can be bypassed by old-school social engineering.
This suggests that the future of security threats isn't necessarily in better attacks against better defenses. It's in finding the weakest link in the chain. And right now, the weakest link is the human brain, especially when approached through unexpected channels like the postal system.
The defense is awareness, education, and skepticism. When something seems too important to ignore, verify independently. When something asks for something you've been told never to share, pause and verify that the request is real. When something arrives through an unexpected channel requesting something sensitive, treat that as a red flag rather than a reason to trust it more.

FAQ
What is a recovery phrase and why is it so important?
A recovery phrase (also called a seed phrase or mnemonic) is a sequence of 12, 18, or 24 randomly generated words that contain all the cryptographic information needed to recreate your cryptocurrency wallet. If you lose your hardware wallet, entering this phrase into a new device restores all your wallets, addresses, and funds. However, because this phrase is the master key to all funds, anyone who obtains it gains complete control over your cryptocurrency. This is why hardware wallet manufacturers emphasize that recovery phrases must never be entered into websites, software applications, or anywhere except the physical hardware wallet device itself.
How do physical QR code phishing attacks work differently than email phishing?
Physical QR code phishing attacks bypass digital security layers like email filters and spam detection that users have become accustomed to. Instead of clicking a link in an email, you receive an urgent-looking letter in your mailbox that appears to come from a legitimate company like Trezor or Ledger. The psychological effect is stronger because physical mail is harder to produce than email and carries an air of official legitimacy. Once you scan the QR code with your phone, you're directed to a fraudulent website that perfectly mimics the official interface, making it difficult to distinguish from the real thing. By the time you realize it's phishing, you've already entered your recovery phrase.
What should I do if I accidentally entered my recovery phrase on a phishing website?
If you've compromised your recovery phrase, you need to act immediately. First, stop entering any more information and close the browser. Second, if you still have control of your legitimate hardware wallet device, transfer all your cryptocurrency to a brand new wallet address created from a fresh recovery phrase on a completely new hardware device. This must be done from the legitimate device, not through the compromised interface. Third, once funds are safely transferred, reset your original hardware wallet to generate a new recovery phrase, which makes the compromised phrase worthless to the attacker. Fourth, report the incident to the affected company and law enforcement. The key is speed—move your funds before the attacker realizes they have your recovery phrase and attempts to steal them.
How do attackers get my mailing address for these campaigns?
Mailing addresses used in phishing campaigns typically come from previous data breaches. Trezor and Ledger both experienced significant breaches that exposed customer information including mailing addresses. These breached databases circulate in criminal underground forums where attackers can purchase them in bulk. Other sources include data breaches at cryptocurrency exchanges, payment processors that sell hardware wallets, or even postal service records. Once attackers have a database of addresses from people known to own cryptocurrency, they can easily scale physical phishing campaigns by printing and mailing to thousands of addresses simultaneously.
Why can't law enforcement stop these attacks?
Law enforcement faces several challenges with international cryptocurrency theft. First, these attacks often originate from countries with weak cybercrime enforcement or jurisdictions where attackers have protection. An American police department cannot pursue criminals in Eastern Europe or Southeast Asia. Second, cryptocurrency transactions are pseudonymous—while they're recorded on the blockchain, tracing them back to real-world identities requires cooperation from exchanges and service providers that may not operate in the victim's jurisdiction. Third, the volume of these attacks exceeds law enforcement resources. Finally, the cryptocurrency itself, once stolen, is often immediately mixed and moved through multiple accounts, making recovery extremely difficult. This means personal vigilance and prevention are far more effective than relying on post-incident law enforcement investigation.
Are hardware wallets still safe after these attacks were discovered?
Yes, hardware wallets themselves remain extremely secure from a technical standpoint. The devices use strong cryptography and are specifically designed to never expose recovery phrases to internet-connected computers. The vulnerability is not in the hardware or encryption—it's in social engineering. An attacker can't remotely hack a hardware wallet. They can't extract the recovery phrase from the device. The only way they can compromise your wallet is by tricking you into voluntarily giving them your recovery phrase through phishing. Hardware wallets are still the best way to store cryptocurrency. The attacks demonstrate that having secure technology means nothing if you're socially engineered into compromising it yourself.
How can I verify if a letter claiming to be from Trezor or Ledger is legitimate?
Legitimate companies will never send unsolicited mail asking you to enter your recovery phrase. If you receive such a letter, it's definitely phishing. You can verify by contacting the company directly through channels you identify yourself. Look up their official phone number from their website (not from the letter) and call to ask if they sent the mail. You can also check their official social media accounts for warnings about phishing campaigns. Legitimate verification processes from hardware wallet manufacturers never require entering recovery phrases, never have artificial deadlines, and are never delivered via unsolicited physical mail. Any letter claiming otherwise is a scam.
What's the best way to store my recovery phrase securely?
The safest storage method depends on your risk profile and the amount of cryptocurrency involved. For large holdings, write the recovery phrase on paper using waterproof ink and store it in a safe deposit box at a bank or a home safe. For high security, use stainless steel backup cards that are resistant to fire and water damage. Some people memorize their phrases if they can reliably do so. For convenience without compromising security, use zero-knowledge password managers like Bitwarden or 1 Password that store encrypted information client-side. Never screenshot or photograph your recovery phrase. Never email it to yourself. Never store it in cloud services without strong encryption. The principle is simple: the recovery phrase should be secured like the master key to all your wealth, because that's exactly what it is.
What can I do if I noticed suspicious activity in my wallet?
If you notice transactions you didn't make or funds moving to unfamiliar addresses, act immediately even if you're not sure what happened. First, stop using the wallet for any reason. Second, if you still have control of your hardware device and access to move funds, transfer everything to a new wallet created from a fresh recovery phrase on a different device. Third, document the suspicious transactions by taking screenshots of the blockchain explorer showing the unauthorized transfers. Fourth, report the incident to the hardware wallet manufacturer, your country's law enforcement cyber crime unit, and the FBI's Internet Crime Complaint Center. Fifth, monitor the compromised wallet address on the blockchain to see if the attacker moves the funds further, which can provide intelligence about the scam operation. While you likely won't recover stolen funds, your report helps law enforcement identify patterns in these attacks.
Are there other devices or methods I can use beyond hardware wallets?
Hardware wallets are currently the most secure option for cryptocurrency storage, but other methods exist with different tradeoffs. Cold storage on a completely offline device (air-gapped) offers maximum security but reduced convenience. Paper wallets (printed private keys) avoid digital compromise but create physical security risks. Multi-signature wallets spread risk across multiple devices and keys, requiring compromising multiple separate security factors. Cryptocurrency exchanges have convenience but custody risk—you don't control the private keys. For most people, hardware wallets represent the optimal balance of security and usability, but they're most secure when combined with good operational security practices like those outlined above.
Staying Ahead of Evolving Threats
Physical mail phishing represents the evolution of attacker tactics in response to improving digital defenses. As long as there's value to steal, attackers will find ways to exploit human psychology and trust.
The good news is that this particular attack vector is highly preventable through awareness. You don't need special software. You don't need expensive security services. You just need to understand what legitimate requests look like and what red flags to watch for.
The responsibility ultimately falls on you. No company can protect you from voluntarily giving away your recovery phrase. No firewall can block social engineering. No amount of encryption helps if you're tricked into decrypting your wallet yourself.
But informed users are extremely difficult to scam. Someone who understands that Trezor will never mail a recovery phrase request can immediately identify a fraudulent letter. Someone who knows that hardware wallets don't have remote security verification processes can safely ignore urgent claims about authentication checks. Someone who comprehends that entry of recovery phrases into websites represents guaranteed wallet compromise will refuse the request, no matter how urgent it seems.
The security community is slowly waking up to these attacks. Major hardware wallet manufacturers are issuing warnings. Cryptocurrency exchanges are becoming more cautious about sudden large transfers. Security researchers are tracking the infrastructure. But prevention is far easier than post-incident recovery.
In the end, defending yourself against physical QR code phishing requires the same thing that defends against all social engineering: healthy skepticism, independent verification, and the willingness to double-check before taking action that can't be undone.
Your cryptocurrency is only as secure as your awareness of the threats to it. Stay informed. Stay skeptical. And never, ever enter your recovery phrase into anything except your legitimate hardware device.

Key Takeaways
- Physical QR code phishing bypasses email filters and digital security, achieving 100+ times higher success rates than email phishing attacks
- Recovery phrases are the complete cryptographic keys to cryptocurrency wallets—anyone with them has absolute control over all funds
- Legitimate hardware wallet manufacturers never ask for recovery phrases via mail, email, or websites under any circumstances
- Previous data breaches exposed millions of customer mailing addresses, which are now weaponized for physical phishing campaigns targeting cryptocurrency holders
- Defending yourself requires awareness and skepticism rather than technical solutions, as these are social engineering attacks exploiting human psychology
Related Articles
- Authentication Beyond MFA in 2026: Phishing-Resistant Methods [2025]
- How Industry Season 4 Captures Tech Fraud Better Than Reality [2025]
- OpenClaw AI Security Risks: How Malicious Extensions Threaten Users [2025]
- North Korean Labyrinth Chollima Malware Splits Into Three Entities [2025]
- Device Protection Beyond Hardware: Securing Your Digital Identity [2025]
- Microsoft Teams Phishing Attacks: How Hackers Steal Email Credentials [2025]
![Physical QR Code Phishing: How Hackers Are Stealing Crypto Via Snail Mail [2025]](https://tryrunable.com/blog/physical-qr-code-phishing-how-hackers-are-stealing-crypto-vi/image-1-1771362698391.jpg)



