How Hackers Hijack Your Inbox with Clever Tactics [2025]
Securing your inbox isn't just about using a strong password anymore. Hackers have evolved, and so have their tactics. From manipulating email rules to sophisticated phishing schemes, the methods are diverse and alarmingly common.
TL; DR
- Inbox Rule Exploitation: Hackers use email rule manipulation to hide alerts and forward sensitive data.
- Phishing Schemes: Over 90% of cyberattacks begin with a phishing email, as highlighted by Verizon's Data Breach Investigations Report.
- Credential Stuffing: Hackers leverage leaked passwords for unauthorized access.
- Social Engineering: Personal details are used to gain trust and access.
- Multi-Factor Authentication (MFA): A critical defense against unauthorized access.
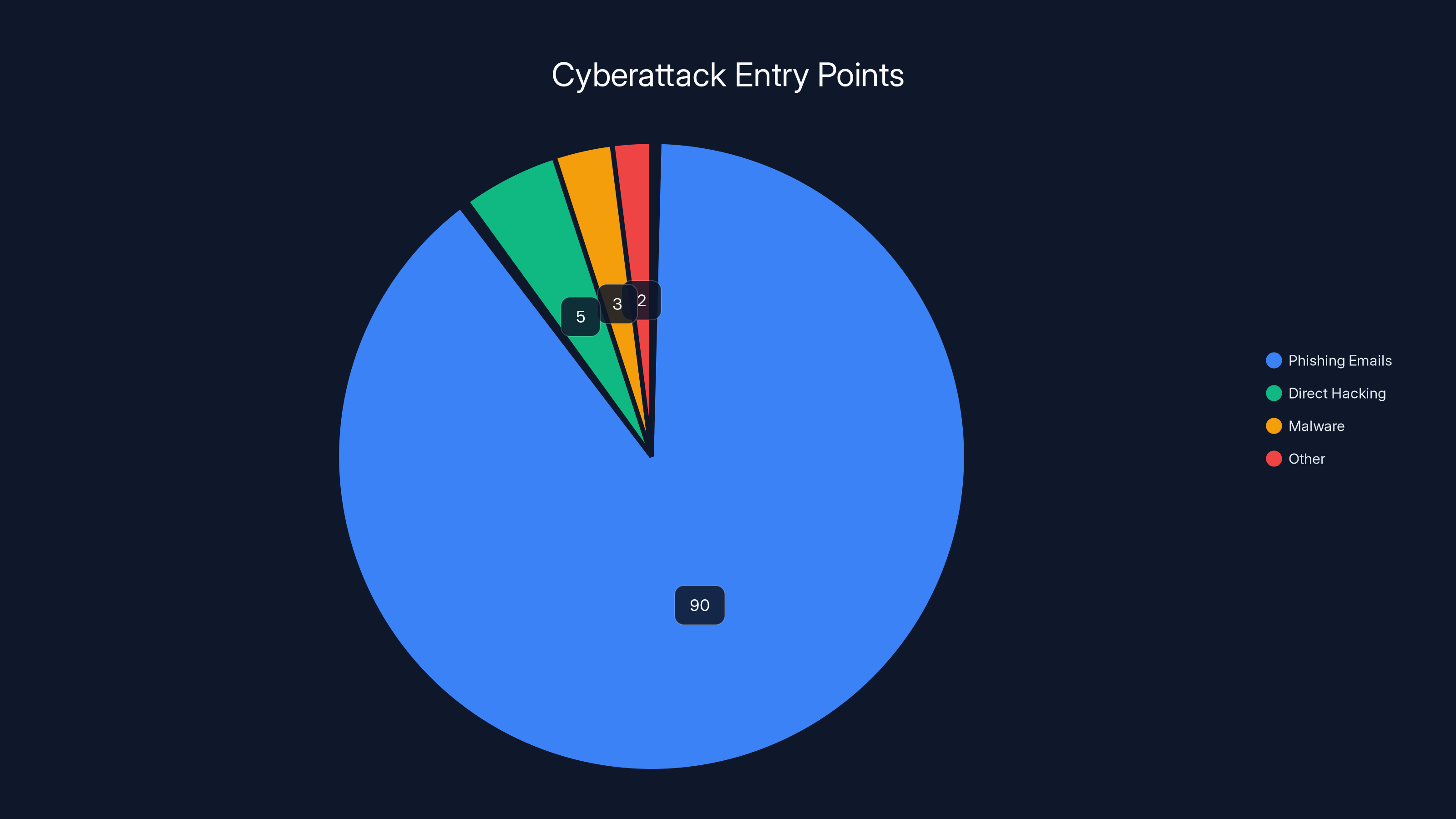
Phishing emails account for over 90% of cyberattacks, highlighting the need for robust email security measures. (Estimated data)
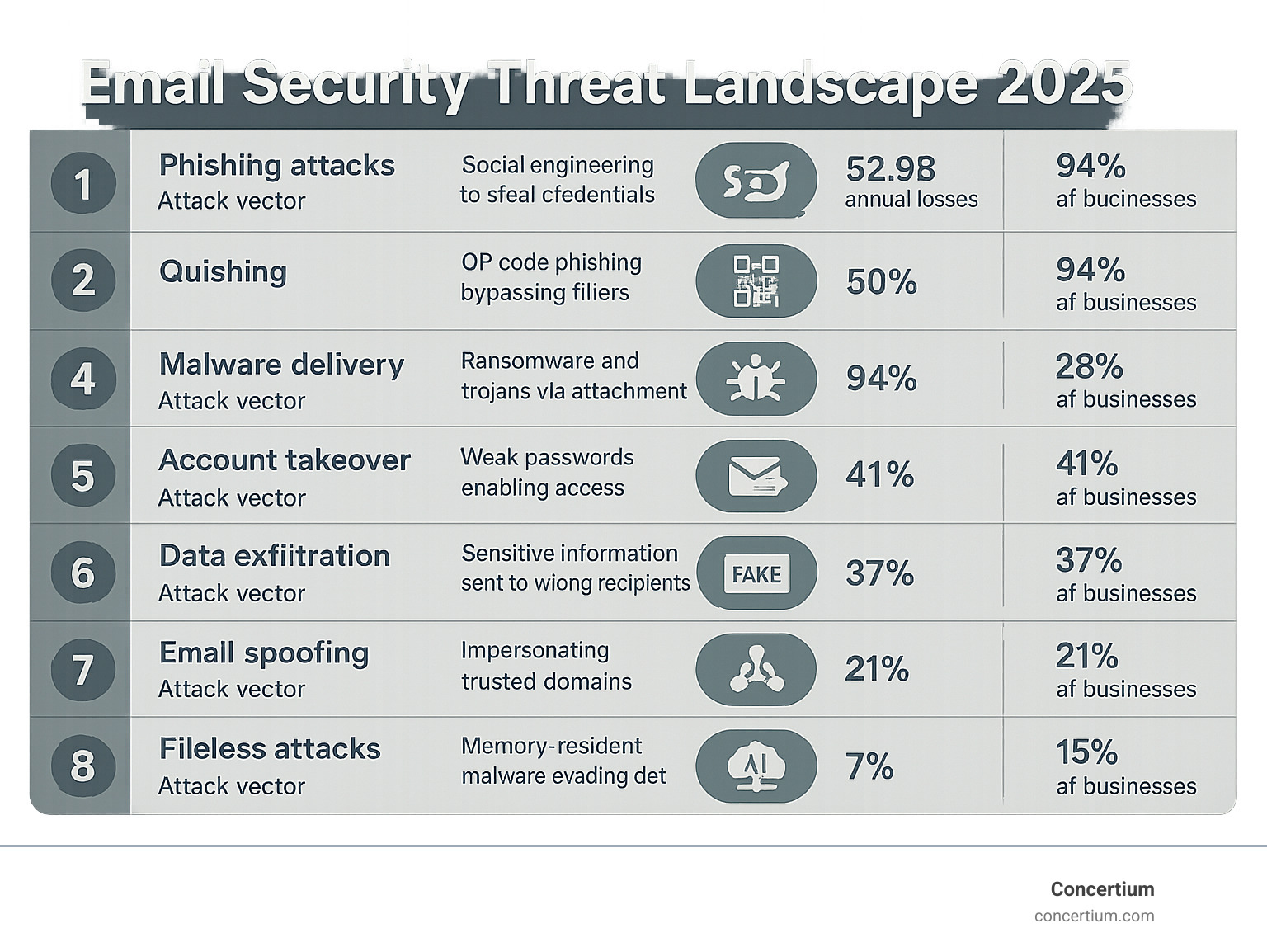
The Growing Threat Landscape
Email: A Prime Target
Email remains a core communication tool, making it a prime target for hackers. With over 300 billion emails sent daily, the attack surface is vast and enticing for cybercriminals, as noted by Forbes.
Evolving Tactics
Hackers continually adapt. They exploit human psychology and technical vulnerabilities, making their methods increasingly difficult to detect, as discussed in Panda Security's insights.
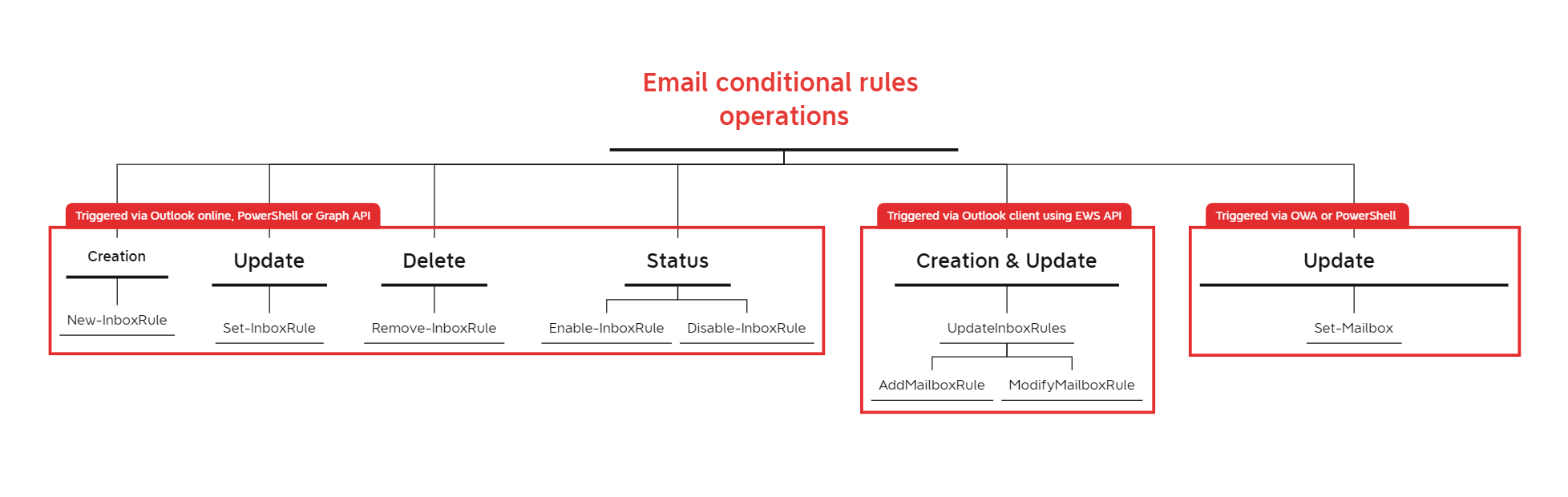
Understanding Email Rule Exploitation
What Are Email Rules?
Email rules are automated instructions that sort, move, or flag incoming messages based on predefined criteria. While handy for organization, they can be exploited.
How Attackers Exploit Rules
Hackers gain unauthorized access to an email account and set rules to:
- Hide Security Alerts: Automatically delete or move alerts from security systems.
- Forward Emails: Send copies of incoming emails to an external address, maintaining access to sensitive information.
- Bypass Password Changes: Continue monitoring an account even after a password reset.

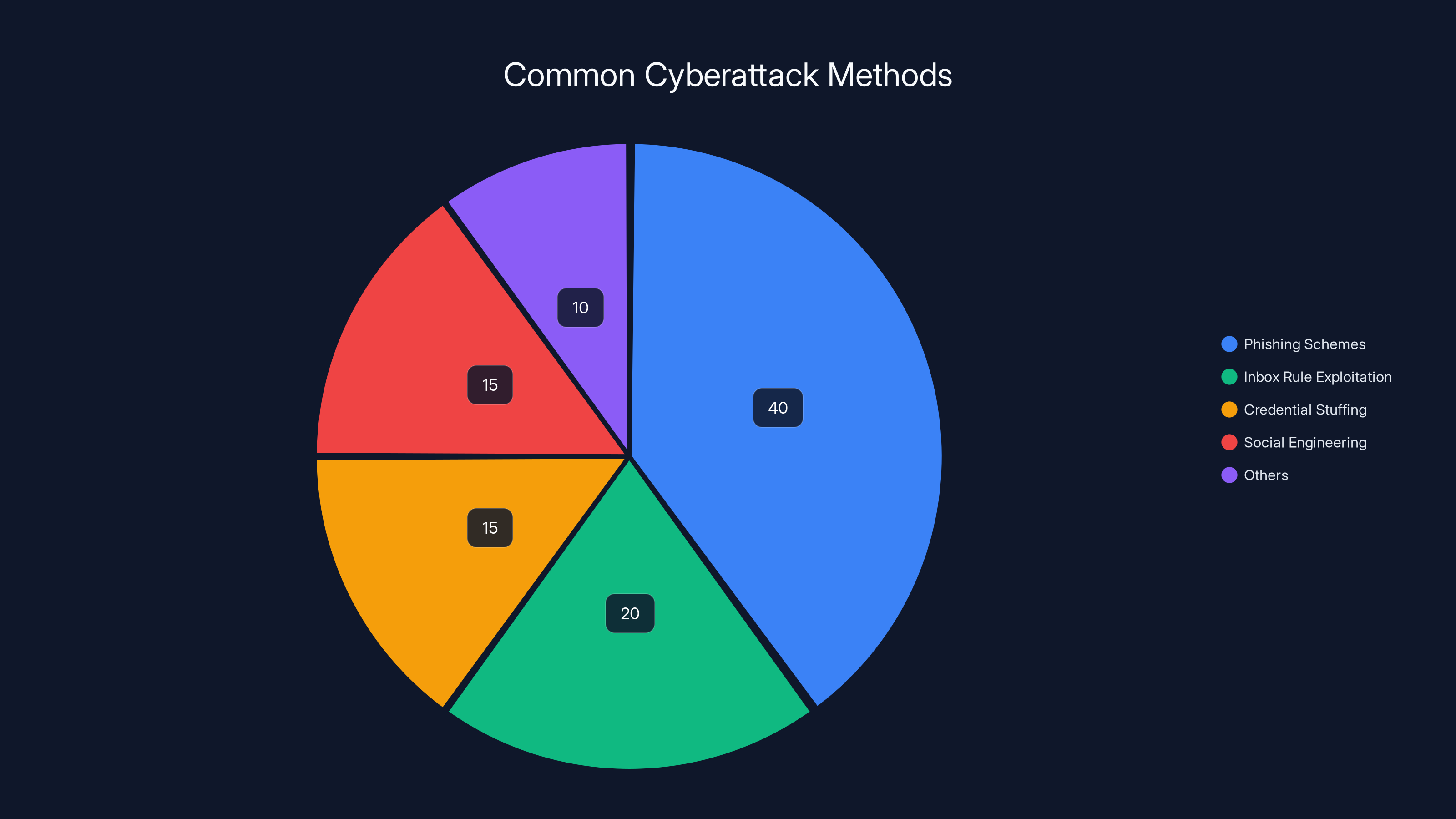
Phishing schemes account for the largest share of cyberattacks, making up an estimated 40% of incidents. Estimated data.
Phishing: The Gateway to Your Inbox
Anatomy of a Phishing Attack
Phishing emails often mimic trusted entities, urging recipients to click malicious links or download attachments. These emails leverage urgency and fear to prompt quick actions, as detailed in Security Boulevard's guide.
Real-World Example
Imagine receiving an email from your "bank" stating that your account is compromised. The email looks authentic, complete with branding and a "secure" link. Clicking it, however, takes you to a fraudulent site designed to steal your credentials, as illustrated in The Register's report.
Spotting the Signs
- Suspicious URLs: Hover over links without clicking to verify their destination.
- Generic Greetings: Be wary of emails that don't address you specifically.
- Urgent Language: Phrases like "act now" or "your account will be closed" are red flags.
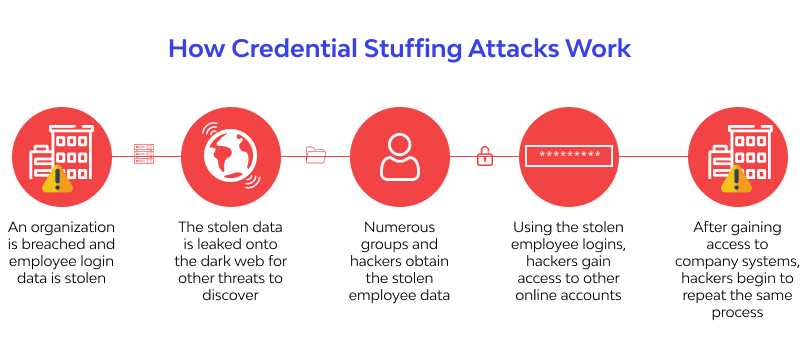
Credential Stuffing: The Domino Effect
What Is Credential Stuffing?
Credential stuffing involves using stolen username-password pairs from one site to access accounts on other sites. Given the reuse of passwords, it's alarmingly effective, as explained by Bitdefender.
Protecting Yourself
- Unique Passwords: Use different passwords for different sites.
- Password Managers: Tools like Last Pass or 1 Password can help manage multiple passwords securely.
Social Engineering: Manipulating Trust
The Human Factor
Social engineering exploits human psychology to gain access to sensitive information. Hackers might impersonate a colleague or IT support to gain trust, as noted in The Cyber Express.
Common Tactics
- Pretexting: Fabricating a scenario to extract information.
- Baiting: Offering something enticing to garner personal details.


Physical tokens like YubiKey offer the highest security level, while email codes are less secure. Estimated data based on typical security assessments.
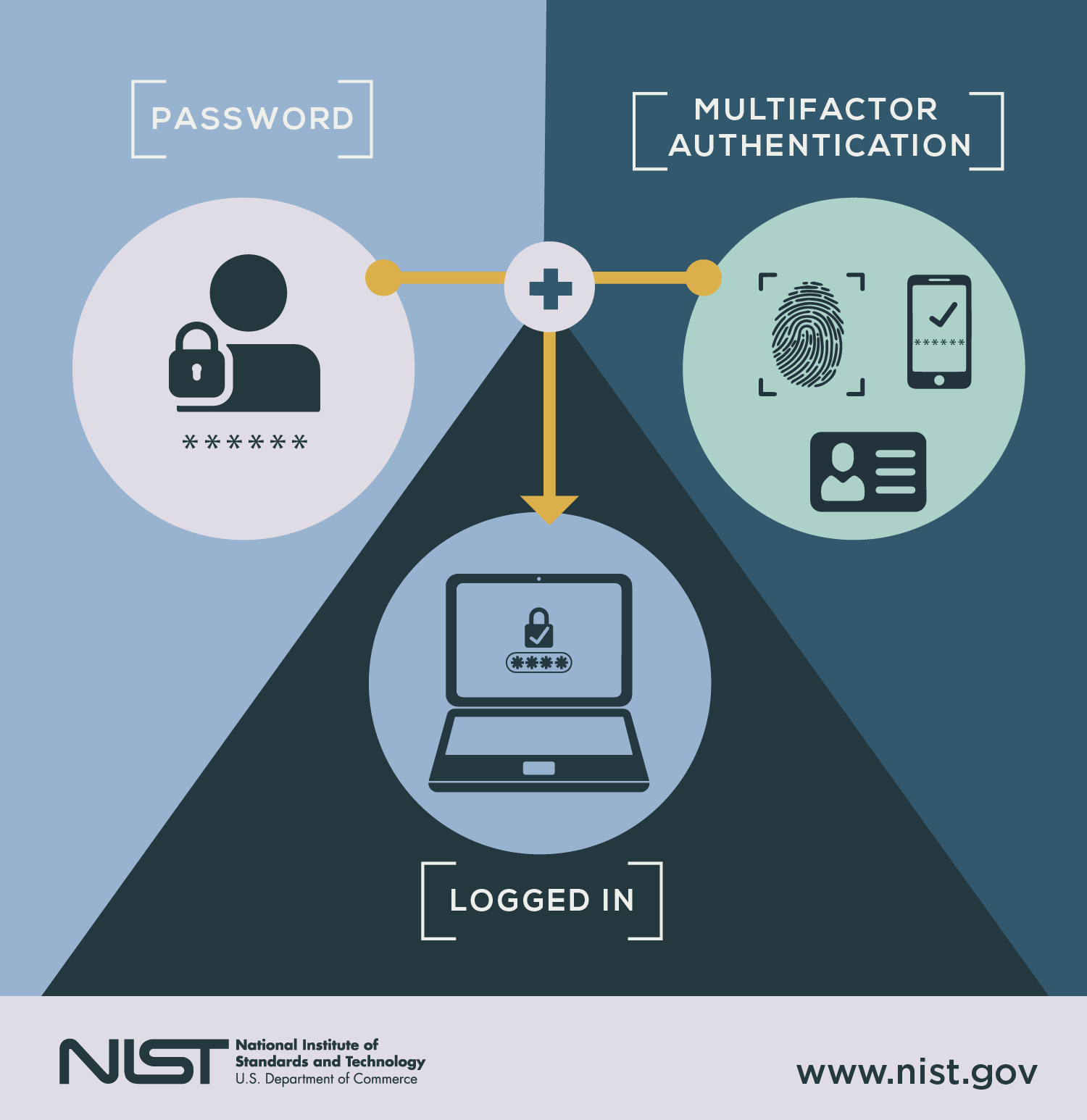
Multi-Factor Authentication: A Robust Defense
Why MFA Matters
Multi-Factor Authentication (MFA) adds an additional layer of security by requiring something you know (password) and something you have (a code sent to your phone), as emphasized by Cisco's blog.
Implementing MFA
- Authentication Apps: Use apps like Authy or Google Authenticator for generating secure codes.
- Physical Tokens: Devices like Yubi Key provide a physical means of authentication.
Best Practices for Securing Your Inbox
Regular Audits
- Review Access Logs: Check for unauthorized logins.
- Verify Email Rules: Ensure no unexpected rules have been set.
Training and Awareness
- Phishing Simulations: Regularly test employees with simulated phishing attempts.
- Security Training: Educate users on recognizing and responding to threats, as recommended by the CISO Series.

Common Pitfalls and How to Avoid Them
Ignoring Updates
Failing to update your software and systems can leave you vulnerable to known exploits, as highlighted by BGR.
Relying Solely on Passwords
Passwords alone aren't enough. Implement MFA to strengthen your security posture.
Future Trends in Email Security
AI-Powered Threat Detection
AI and machine learning will play a significant role in identifying and mitigating threats by analyzing patterns and anomalies in real-time, as discussed by Anthropic.
Zero Trust Architecture
Adopting a Zero Trust model, which assumes no actor, system, or network is trustworthy by default, will become more prevalent.

Conclusion: Proactive Defense
Securing your inbox requires vigilance and proactive measures. By staying informed about the latest tactics and implementing robust security practices, you can protect your personal and professional information from malicious actors.
Use Case: Automate your email security audits with AI-powered tools and gain peace of mind.
Try Runable For FreeFAQ
What is email rule exploitation?
Email rule exploitation involves hackers gaining access to an email account and setting automated rules to hide security alerts or forward sensitive information.
How can I recognize phishing emails?
Look for suspicious URLs, generic greetings, and urgent language that pressures you to act quickly.
What is credential stuffing?
Credential stuffing uses compromised username-password combinations from one site to access accounts on other sites, exploiting password reuse.
How does multi-factor authentication enhance security?
MFA requires additional verification, such as a code from an authentication app, making unauthorized access significantly more difficult.
Why is security training important?
Training helps users recognize phishing attempts and other threats, reducing the likelihood of successful attacks.
What are future trends in email security?
AI-driven threat detection and Zero Trust architectures are emerging as key components in modern email security strategies.
Key Takeaways
- Hackers use email rules to hide alerts and forward sensitive data.
- Phishing remains the most common method to initiate cyberattacks.
- Credential stuffing exploits password reuse across sites.
- Social engineering leverages human psychology for unauthorized access.
- Multi-Factor Authentication is critical for robust security.
Related Articles
- Understanding the Basic-Fit Data Breach: A Comprehensive Guide to Data Security [2025]
- Agility is the Key to Protecting Against Malware-as-a-Service [2025]
- Booking.com Data Breach: What Customers Need to Know [2025]
- The Complex World of Data Breaches: Lessons from the Rockstar Games Leak [2025]
- Tech Support Scams and How to Combat Them [2025]
- Future-Proof Your Privacy with Next-Generation VPN Encryption [2026]
![How Hackers Hijack Your Inbox with Clever Tactics [2025]](https://tryrunable.com/blog/how-hackers-hijack-your-inbox-with-clever-tactics-2025/image-1-1776182659202.jpg)



