Understanding WordPress Plugin Vulnerabilities: Protect Your Site [2025]
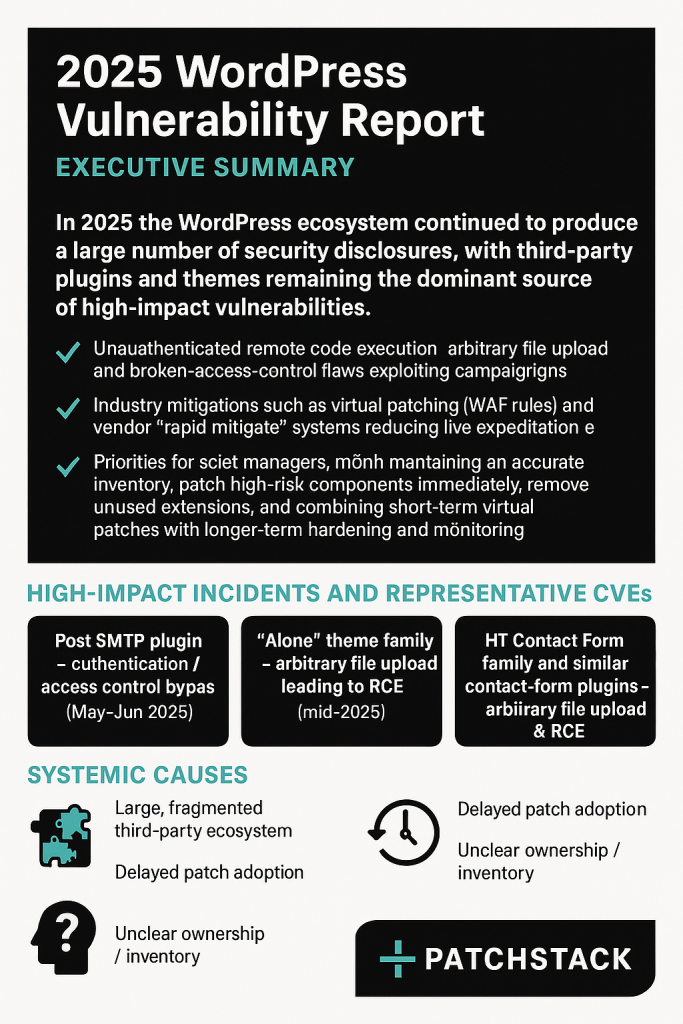
In the world of website management, maintaining security is paramount. WordPress, which powers over 40% of the web, offers unparalleled flexibility and ease of use. However, with great power comes great responsibility, especially when it comes to third-party plugins. A recent vulnerability in the Ally plugin, affecting nearly 250,000 websites, underscores the importance of vigilance in plugin management, as highlighted by Security Affairs.
TL; DR
- Ally Plugin Vulnerability: Affected ~246,600 sites due to an SQL injection flaw, according to Bleeping Computer.
- Immediate Action Required: Update to version 4.1.0 to mitigate risks.
- Security Best Practices: Regular updates and vulnerability scanning are essential.
- Future Trends: Expect increased focus on plugin security from developers.
- Bottom Line: Proactive security measures are crucial for WordPress site owners.
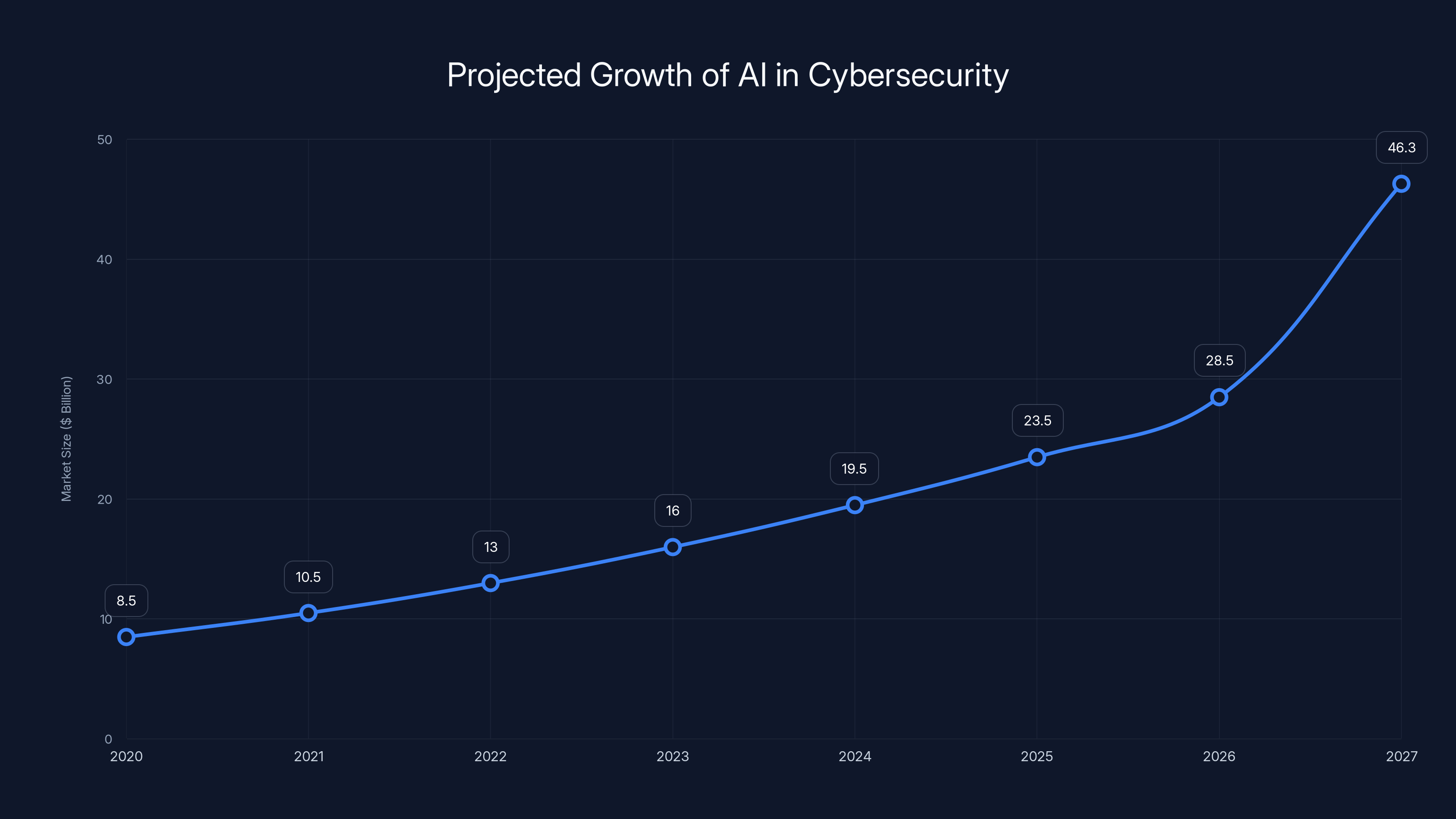
AI's role in cybersecurity is expected to grow significantly, reaching $46.3 billion by 2027, indicating a strong trend towards AI-powered security solutions, as reported by OpenPR.
The Ally Plugin Incident
The recent discovery of an SQL injection vulnerability in the Ally plugin highlights a critical issue in WordPress security. This flaw, identified as CVE-2026-2413, allowed attackers to exploit the database layer of websites, potentially leading to data theft and unauthorized access, as detailed by CyberPress.
What Happened?
The Ally plugin, developed by Elementor, is designed to enhance web accessibility by identifying and resolving accessibility issues. However, a security researcher from Acquia, Drew Webber, discovered a vulnerability that could be exploited via SQL injection. This type of attack involves injecting malicious SQL queries through input fields, allowing attackers to manipulate the database, as explained by Cisco Blogs.
Impact on Websites
The vulnerability put approximately 246,600 websites at risk, emphasizing the scale and potential impact of such security flaws. Attackers could potentially gain unauthorized access to sensitive data, including user credentials and personal information, as noted by TechRadar.
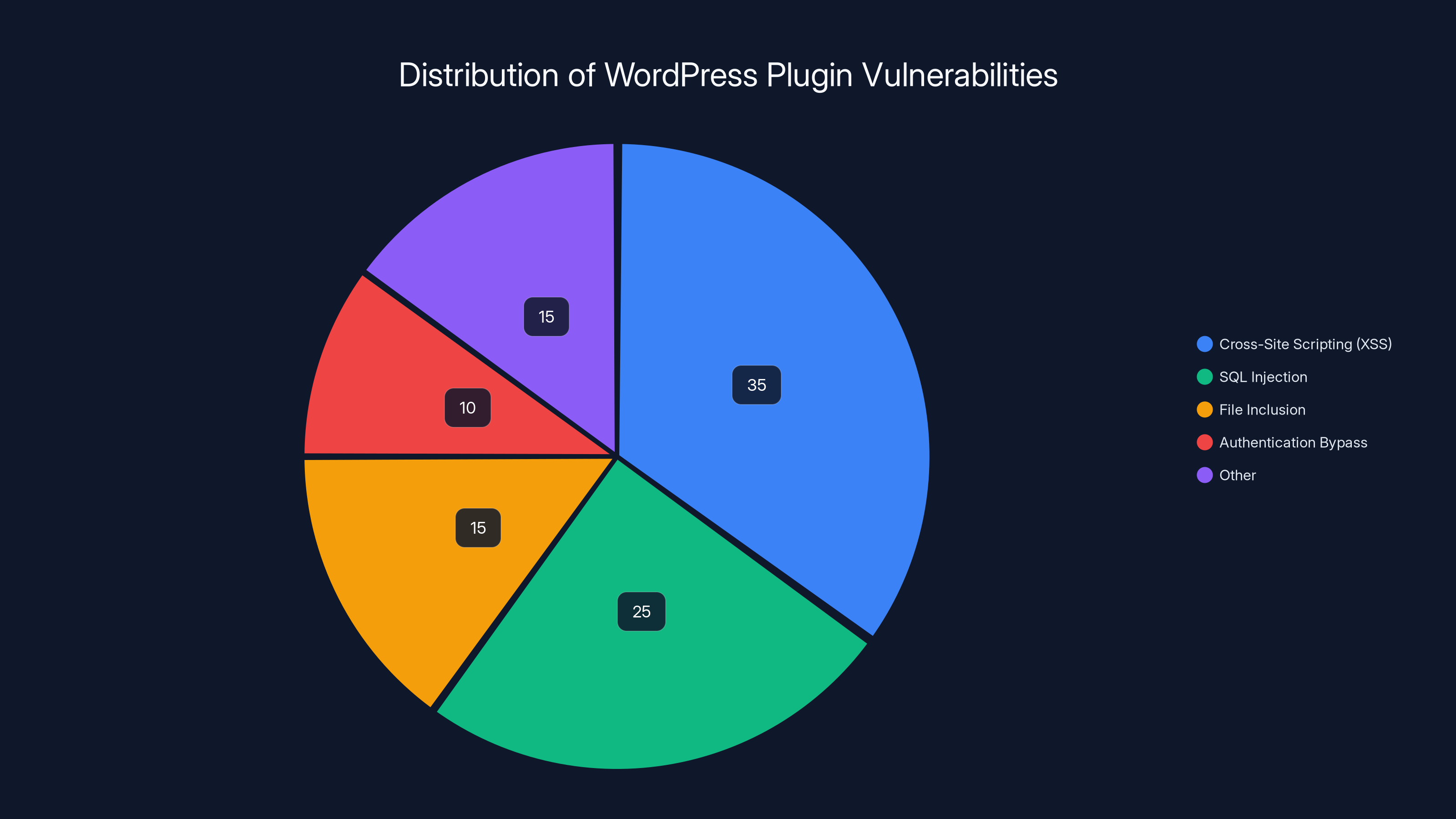
Cross-Site Scripting (XSS) is the most common vulnerability in WordPress plugins, accounting for 35% of issues. Estimated data.
Understanding SQL Injection
What is SQL Injection?
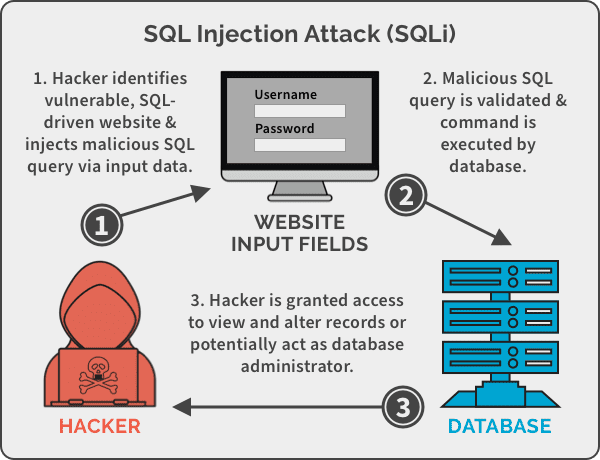
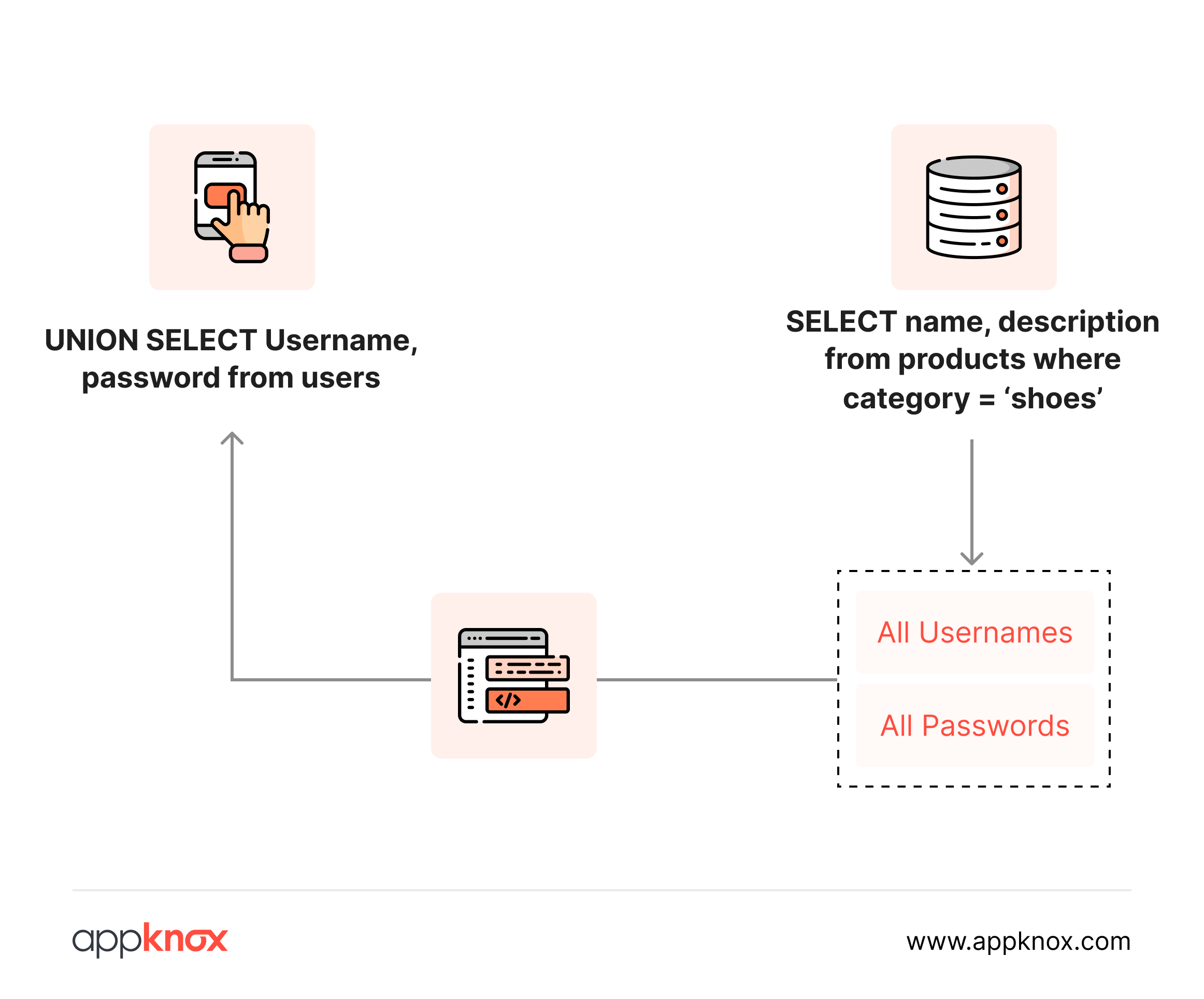
SQL injection is a code injection technique that exploits vulnerabilities in an application's software by inserting or "injecting" malicious SQL statements into an entry field for execution (e.g., to dump the database contents to the attacker). It is one of the most common attack vectors against web applications, as described by Wiz.io.
How Does It Work?
Attackers target unvalidated input fields on a website, such as login forms or search boxes. By inserting malicious SQL code, they can manipulate the database to extract, modify, or delete data.
sql-- Example of a vulnerable SQL query
SELECT * FROM users WHERE username = 'admin' AND password = '' OR '1'='1';
In this example, if the input fields are not properly sanitized, the query could potentially bypass authentication checks, granting attackers admin access.
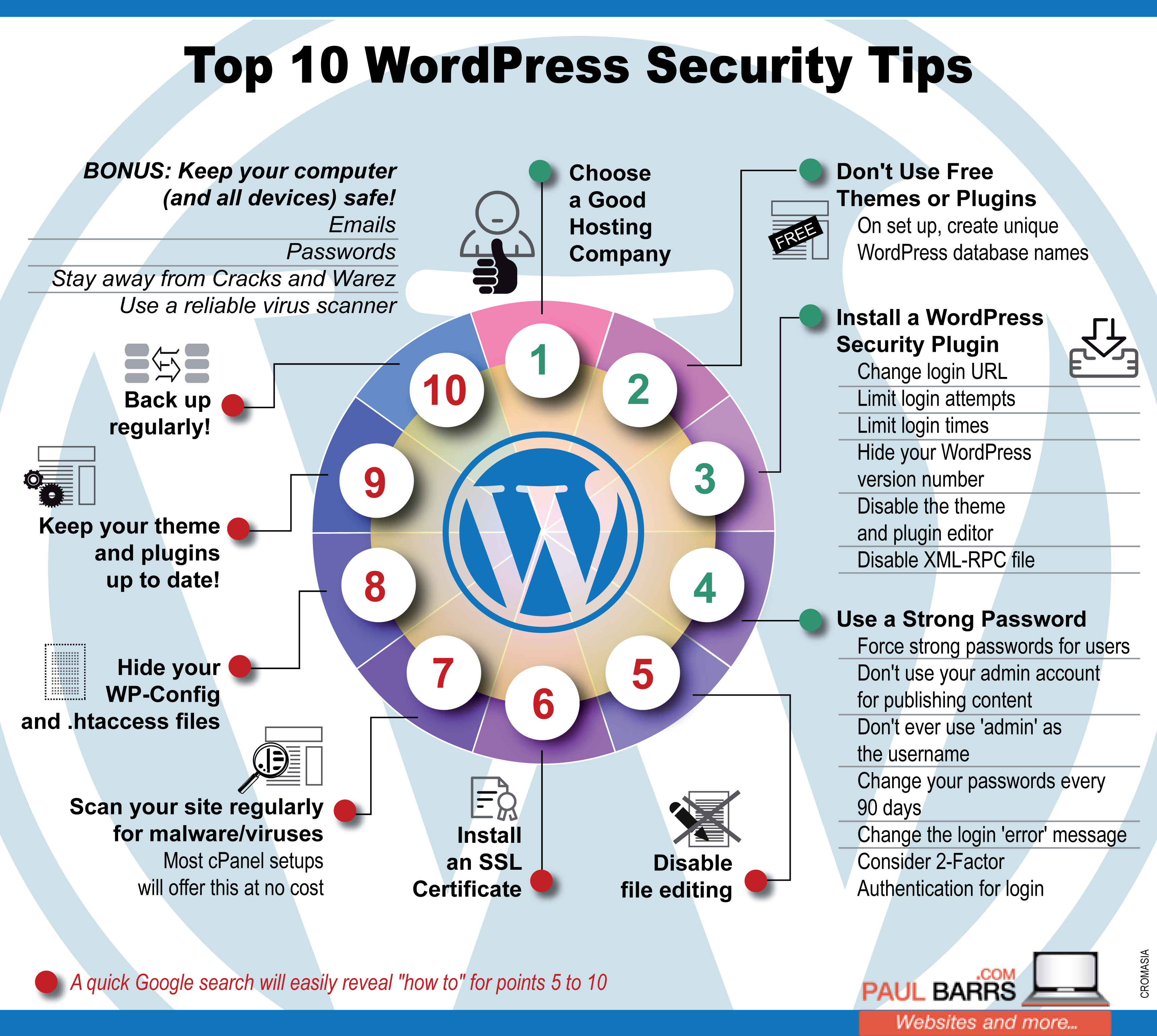
Best Practices for WordPress Security
To mitigate risks and protect your WordPress site from similar vulnerabilities, consider implementing the following security best practices:
Regular Plugin Updates
Keep all plugins, themes, and WordPress itself updated to the latest versions. Developers frequently release patches to fix known vulnerabilities, as advised by Cloudflare.
Use Security Plugins
Install reputable security plugins that offer features like firewall protection, malware scanning, and login auditing. Some popular options include:
- Wordfence: Offers firewall protection and malware scanning.
- Sucuri Security: Provides security activity auditing and file integrity monitoring.
- iThemes Security: Focuses on brute force protection and file change detection.
Input Validation and Sanitization
Ensure all user inputs are validated and sanitized. Use prepared statements and parameterized queries to prevent SQL injection attacks.
php// Example of using prepared statements in PHP
$stmt = $mysqli->prepare("SELECT * FROM users WHERE username = ? AND password = ?");
$stmt->bind_param("ss", $username, $password);
$stmt->execute();
Regular Backups
Schedule regular backups of your website data. In case of a security breach, having recent backups allows you to restore your site to a previous, secure state.
Monitor for Vulnerabilities
Stay informed about known vulnerabilities by subscribing to security bulletins and following cybersecurity news. Websites like the WPScan Vulnerability Database provide valuable insights into plugin vulnerabilities.
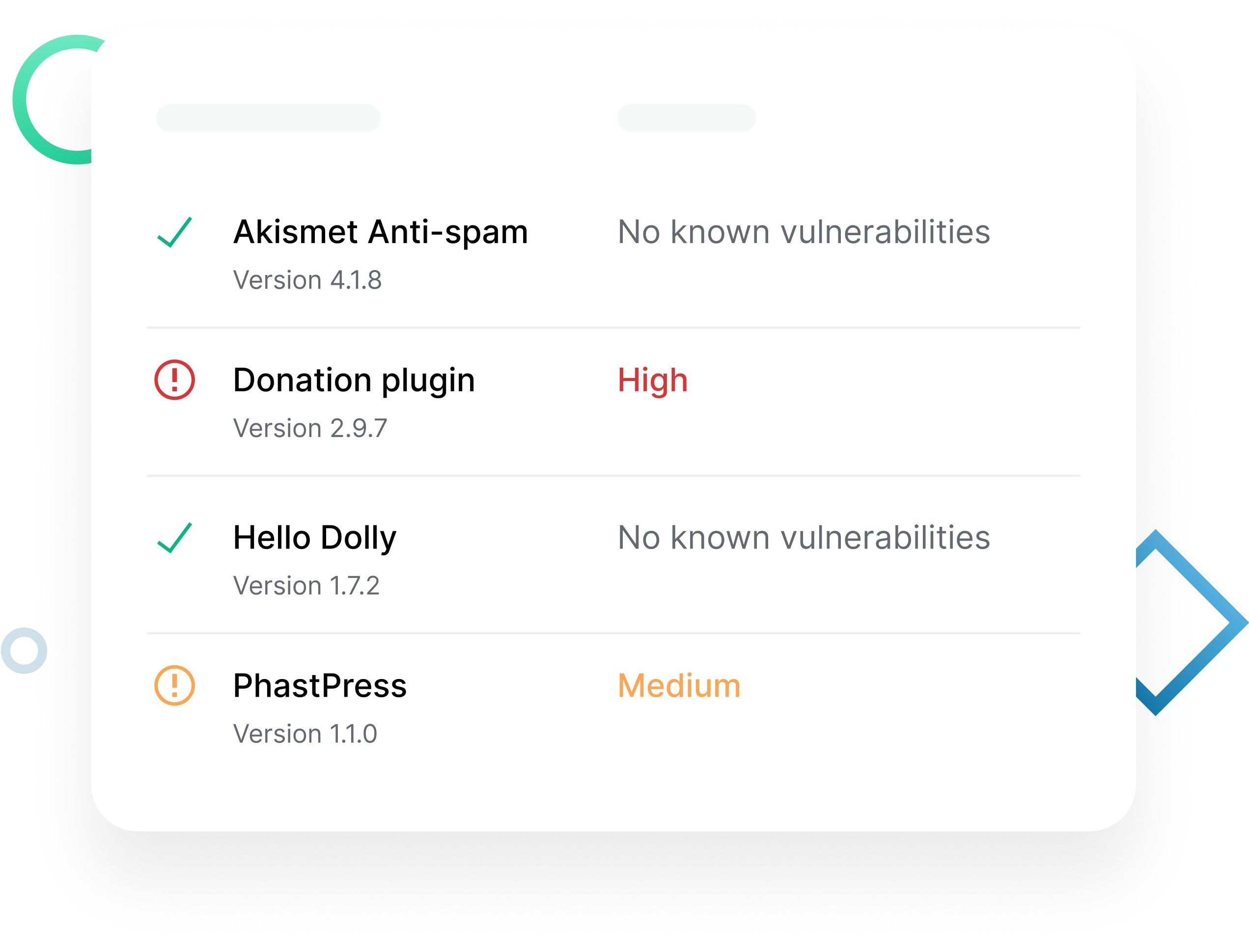
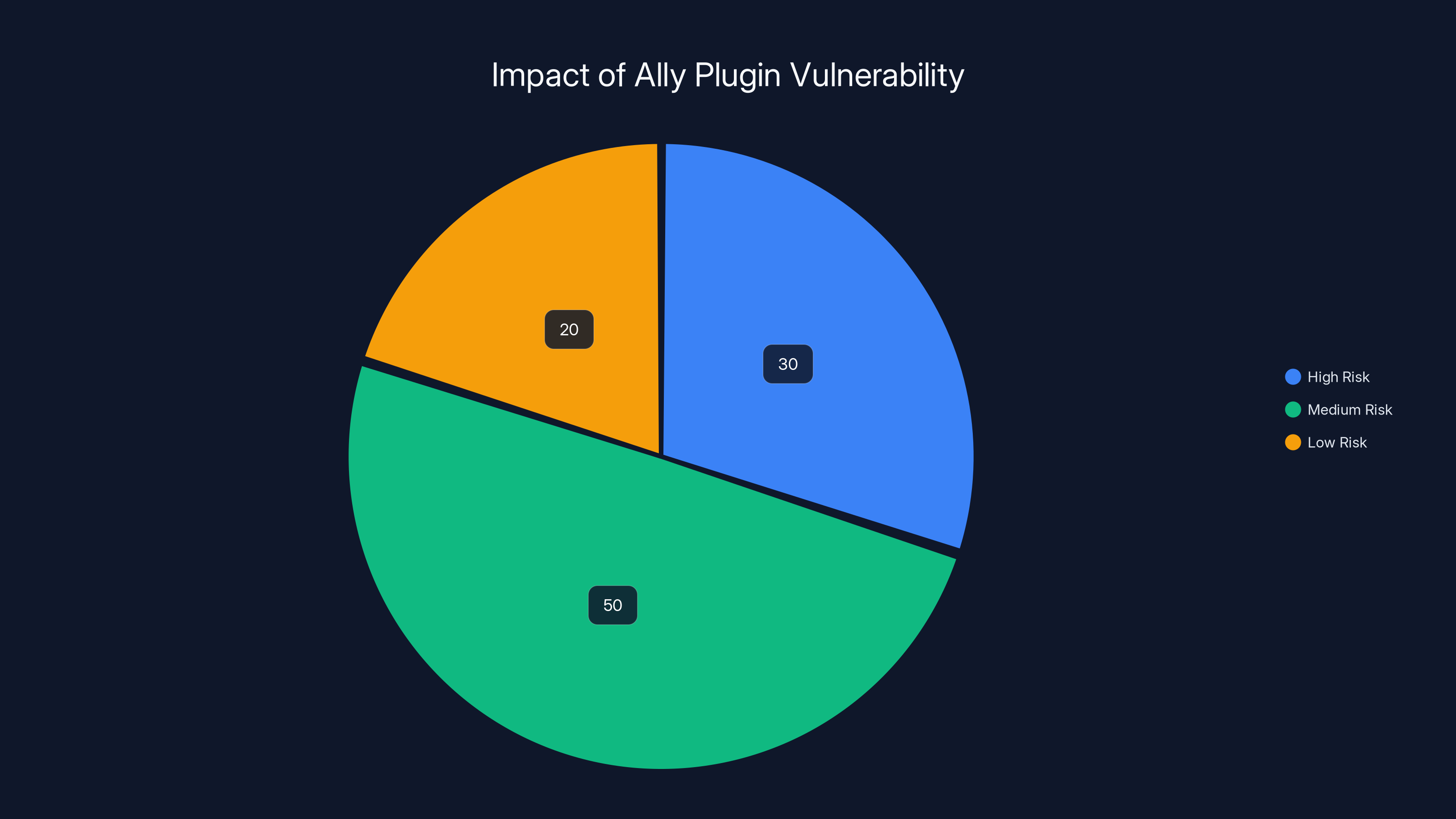
Estimated data shows that 30% of affected websites were at high risk, 50% at medium risk, and 20% at low risk due to the Ally plugin vulnerability.
Common Pitfalls and Solutions
Overlooking Security Updates
Many site owners neglect regular updates, leaving their sites vulnerable to attacks. Set up automatic updates for plugins and themes when possible, or schedule regular review sessions to ensure all components are up to date.
Ignoring User Permissions
Ensure that user roles and permissions are properly configured. Limit administrative access to trusted users only and regularly review user accounts for any suspicious activity.
Misconfigured Security Plugins
While security plugins can be powerful tools, misconfiguration can lead to false positives or missed threats. Take the time to understand and configure the settings appropriately.
Future Trends in WordPress Security
As the WordPress ecosystem continues to grow, expect the following trends to shape the future of security:
Enhanced Plugin Scrutiny
With incidents like the Ally vulnerability, developers and users will likely demand more rigorous security standards for plugins. Expect to see increased scrutiny and possibly certification processes for plugins in the WordPress repository.
AI-Powered Security Tools
Artificial Intelligence (AI) and machine learning will play a larger role in detecting and mitigating security threats. AI-powered tools can analyze patterns and anomalies in real-time, offering proactive defense mechanisms.
User Education and Awareness
Expect more resources dedicated to educating users about security best practices. Awareness campaigns and training modules will become commonplace, empowering users to better protect their websites.

Practical Implementation Guide
Step-by-Step Security Audit
Conducting a security audit can help identify and mitigate potential threats. Here's how to perform a basic audit:
- Inventory Plugins and Themes: List all installed plugins and themes and remove any that are unused or unsupported.
- Check for Updates: Ensure all components are up to date.
- Review User Accounts: Verify current users and their access levels.
- Scan for Malware: Use security plugins to perform a comprehensive malware scan.
- Review Logs: Check server and application logs for any unusual activity.
Implementing Two-Factor Authentication (2FA)
Two-factor authentication adds an additional layer of security by requiring users to provide a second form of verification, typically a code sent to their mobile device.
- Choose a Plugin: Select a 2FA plugin like Google Authenticator or Two Factor Authentication.
- Configure Settings: Set up 2FA for all admin accounts and encourage its use for other user roles.
Case Studies
Case Study 1: E-Commerce Site Breach
An e-commerce website using a vulnerable plugin experienced a data breach, resulting in the theft of customer credit card information. The site owner failed to update the plugin in a timely manner, highlighting the importance of regular updates and monitoring.
Case Study 2: Successful Mitigation
A media company proactively implemented security measures, including regular updates, security plugins, and 2FA. When a vulnerability was discovered in a plugin, the site was already prepared, and no data was compromised.

Conclusion
The Ally plugin vulnerability serves as a stark reminder of the importance of WordPress security. By staying informed, implementing robust security measures, and conducting regular audits, website owners can significantly reduce the risk of becoming victims of cyberattacks.

FAQ
What is WordPress plugin vulnerability?
A WordPress plugin vulnerability is a flaw in a plugin's code that can be exploited by attackers to gain unauthorized access, manipulate data, or launch attacks on a website.
How does SQL injection work?
SQL injection works by inserting malicious SQL code into input fields, allowing attackers to manipulate a site's database. This can lead to unauthorized data access or modification.
What are the benefits of using security plugins?
Security plugins provide features like malware scanning, firewall protection, and activity logging, which help safeguard your website against common threats.
How can I protect my WordPress site from vulnerabilities?
Regular updates, using security plugins, implementing 2FA, and conducting security audits are effective ways to protect your WordPress site from vulnerabilities.
What should I do if my site is compromised?
If your site is compromised, immediately take it offline, change passwords, restore from a clean backup, and investigate the breach to prevent future incidents.
Why is two-factor authentication important?
Two-factor authentication adds an extra layer of security by requiring users to provide a second form of verification, reducing the risk of unauthorized access.
Are free security plugins reliable?
While some free security plugins offer basic protection, premium versions often provide more comprehensive features and support. Evaluate your site's needs before choosing.
How often should I update my plugins?
Regularly check for updates and apply them as soon as they become available to ensure your site remains secure and functional.
Key Takeaways
- Regular updates are crucial for security.
- SQL injection remains a prevalent threat.
- Security plugins can significantly mitigate risks.
- Two-factor authentication enhances site security.
- Proactive monitoring prevents potential breaches.
Related Articles
- How Hackers Hijack WordPress Sites with Fake CAPTCHA Malware [2025]
- WordPress Revolutionizes Web Design with In-Browser Website Creator [2025]
- Understanding Cybersecurity Threats: Lessons from the Stryker Cyberattack [2025]
- Mastering Mouse-Free Web Design with Microsoft's Focusgroup [2025]
- The Rise of KadNap: Understanding and Combating a Resilient Router Botnet [2025]
- Exploring WordPress's New Private Workspace: A Browser-Based Publishing Revolution [2025]
![Understanding WordPress Plugin Vulnerabilities: Protect Your Site [2025]](https://tryrunable.com/blog/understanding-wordpress-plugin-vulnerabilities-protect-your-/image-1-1773331639167.jpg)



