The Alinto Data Breach: Lessons in Cybersecurity for Enterprises [2025]
In an era where data breaches have become alarmingly frequent, the recent leak involving the French email provider Alinto stands out due to its staggering scale and the high-profile nature of the entities affected. This breach, which exposed 40 million records, including data from renowned companies like L’Oreal and Renault, as well as the French government, highlights critical vulnerabilities in data management protocols. In this article, we’ll dissect the Alinto breach, explore its ramifications, and provide a comprehensive guide on bolstering cybersecurity defenses.
TL; DR
- 40 million records exposed: Included data from L’Oreal, Renault, and the French government.
- Core vulnerability: An unprotected Elasticsearch cluster was the primary breach vector.
- Impacts: Reputational damage, potential regulatory penalties, and increased cybersecurity scrutiny.
- Key Takeaway: Implement strict access controls and regular security audits.
- Future Trend: Increasing reliance on AI for real-time threat detection.
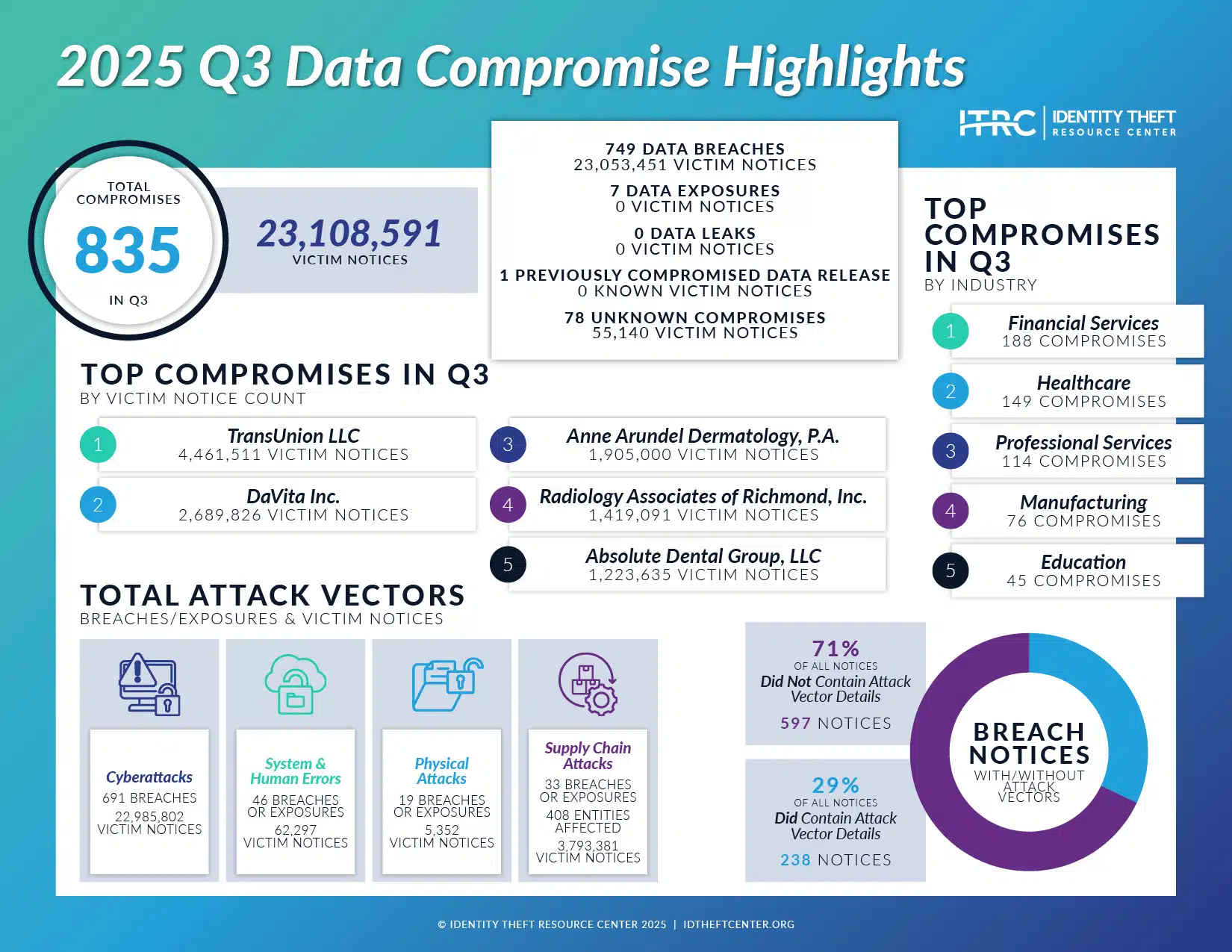
Estimated data shows financial costs and reputational damage as the most significant impacts of data breaches, with scores of 9 and 8 respectively.
Understanding the Breach
Alinto, a well-regarded French email services provider, inadvertently left an Elasticsearch cluster exposed to the internet without any security authentication measures in place. This oversight allowed unauthorized parties to access sensitive SMTP records, revealing the email addresses and potentially sensitive communications of millions of users, as reported by CyberNews.
What is Elasticsearch?
Elasticsearch is a powerful tool, but when improperly configured, it can become a significant liability. In the case of Alinto, the lack of access controls on their Elasticsearch cluster meant that anyone with an internet connection could view the stored records, as noted by HPCwire.
The Scale of the Exposure
The breach included 40 million SMTP records, with 4.5 million unique email addresses. This data set affected a wide array of stakeholders, from corporate giants like L’Oreal and Renault to governmental bodies. The exposure of such a diverse range of entities underscores the interconnected nature of modern digital ecosystems, as highlighted in a recent report.

Balancing security with usability and managing emerging threats are among the top challenges for organizations. Estimated data.
Implications of the Breach
Reputational Damage
For companies like L’Oreal and Renault, the exposure of sensitive communications can lead to significant reputational damage. Consumers and partners expect these organizations to uphold the highest standards of data security. Any lapse can erode trust and drive customers to competitors perceived as more secure, as discussed in Industrial Cyber.
Regulatory Repercussions
In the European Union, the General Data Protection Regulation (GDPR) imposes strict requirements on data protection. A breach of this magnitude could result in hefty fines and increased scrutiny from regulatory bodies. Organizations must not only address the immediate aftermath of such incidents but also demonstrate compliance through detailed documentation and proactive measures, as outlined by Inside Privacy.
Operational Disruptions
Breaches often lead to operational disruptions as companies scramble to identify and mitigate vulnerabilities. This process can divert resources from core business functions, impacting productivity and profitability, according to CYFIRMA.
Preventive Measures and Best Practices
Strengthening Access Controls
The first line of defense against unauthorized access is robust access control. This involves setting strict permissions on who can access specific data and systems. For platforms like Elasticsearch, this means implementing authentication protocols such as OAuth or LDAP.
- Role-based Access Control (RBAC): Assigns permissions based on user roles, limiting access to only what is necessary for a specific task.
- Multi-factor Authentication (MFA): Adds an extra layer of verification, making it harder for unauthorized users to gain access, as recommended by JD Supra.
Regular Security Audits
Conducting regular security audits is essential for identifying vulnerabilities before they can be exploited. These audits should include:
- Penetration Testing: Simulating attacks to identify weaknesses.
- Vulnerability Scanning: Automated tools to detect known vulnerabilities.
- Configuration Reviews: Ensuring systems are set up according to security best practices.
Data Encryption
Encrypting data both at rest and in transit can prevent unauthorized access even if a breach occurs. Encryption ensures that intercepted data is unreadable without the proper decryption keys.
- At Rest: Use strong encryption standards such as AES-256 for stored data.
- In Transit: Implement SSL/TLS protocols to secure data moving across networks, as advised by The Hacker News.

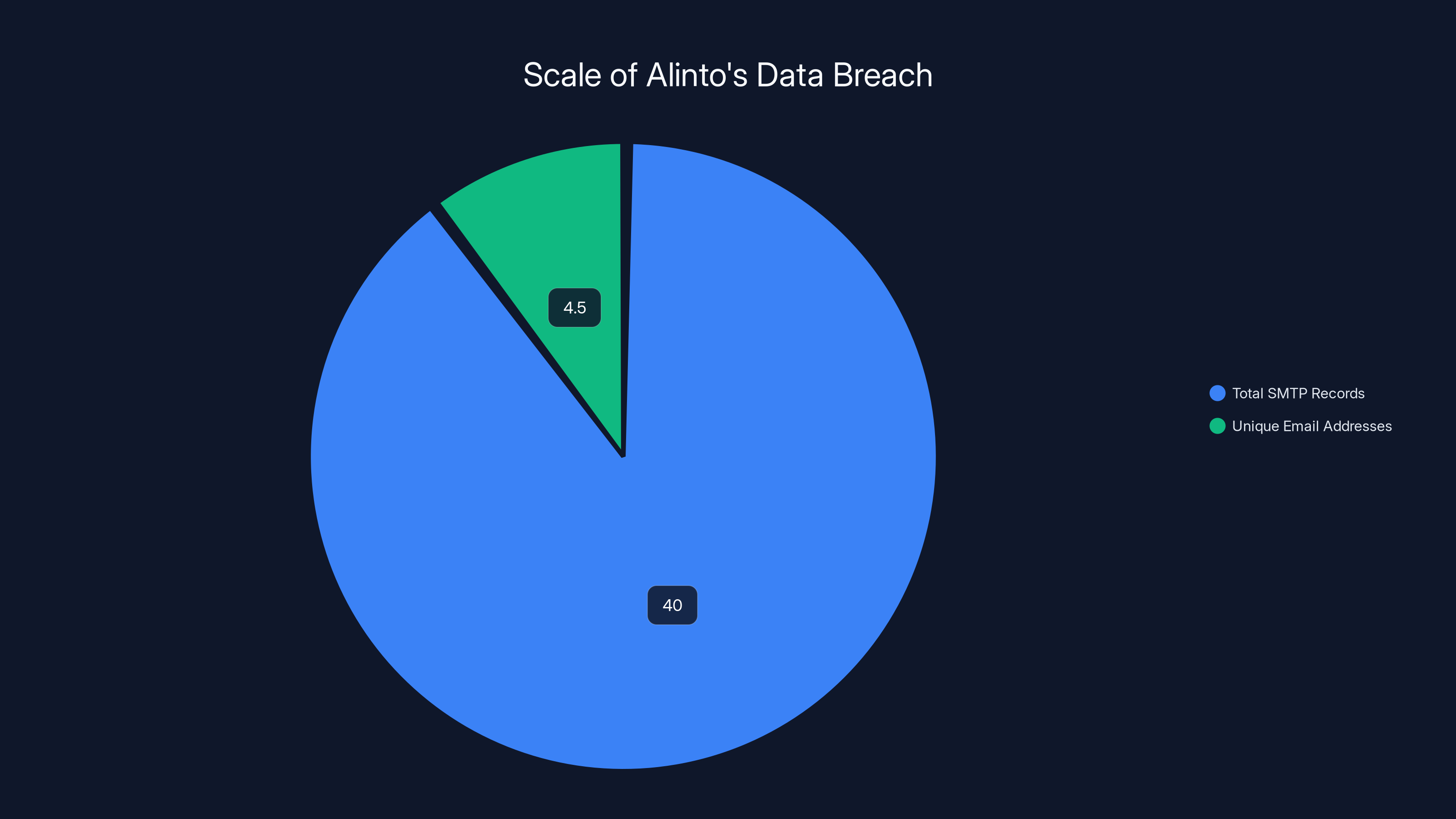
The breach exposed 40 million SMTP records, including 4.5 million unique email addresses, highlighting the scale of the security lapse.
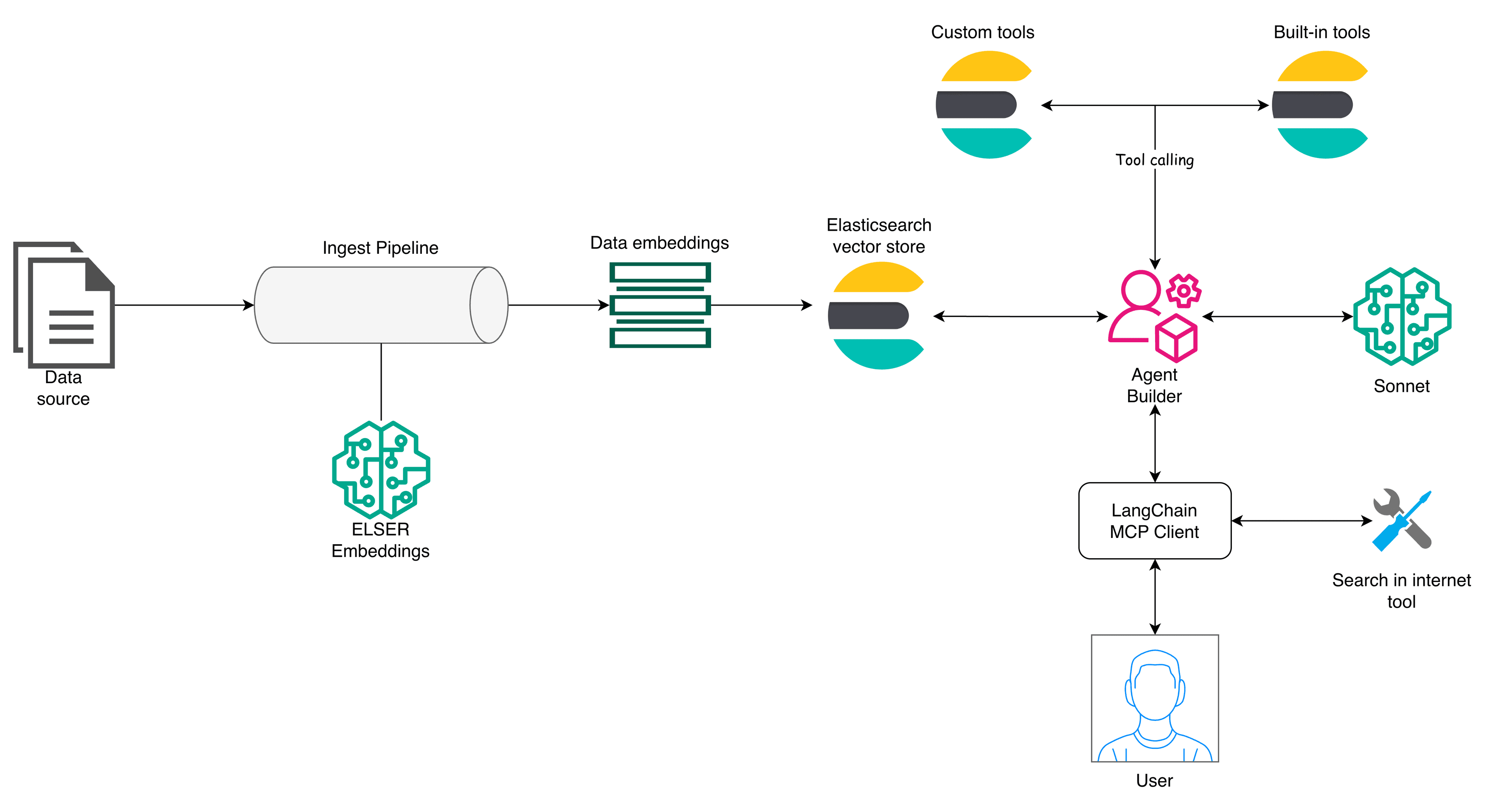
The Role of AI in Cybersecurity
As data volumes increase, manual monitoring becomes impractical. Artificial Intelligence (AI) offers significant advantages in cybersecurity by automating threat detection and response.
AI-Powered Threat Detection
AI systems can analyze vast amounts of data in real-time, identifying anomalies that may indicate a security threat. These systems learn from past incidents to improve their detection capabilities over time, as explored by Wiz.
- Behavioral Analytics: AI can establish a baseline of normal activity and detect deviations that may signal an intrusion.
- Automated Responses: AI can execute predefined actions to mitigate threats, such as isolating compromised systems.

Future Trends in Data Security
Zero Trust Architecture
The Zero Trust model operates on the principle of "never trust, always verify." This approach assumes that threats could exist both outside and inside the network, requiring verification for all access requests.
- Microsegmentation: Dividing the network into smaller, isolated segments to limit lateral movement by attackers.
- Continuous Monitoring: Real-time network analysis to detect and respond to threats as they occur.
Cloud Security Enhancements
With the increasing migration to cloud services, ensuring cloud security is paramount. Providers are enhancing their offerings with advanced security features such as:
- Identity and Access Management (IAM): Tools for managing user identities and permissions in the cloud.
- Cloud Security Posture Management (CSPM): Automated solutions for continuous compliance and risk management.
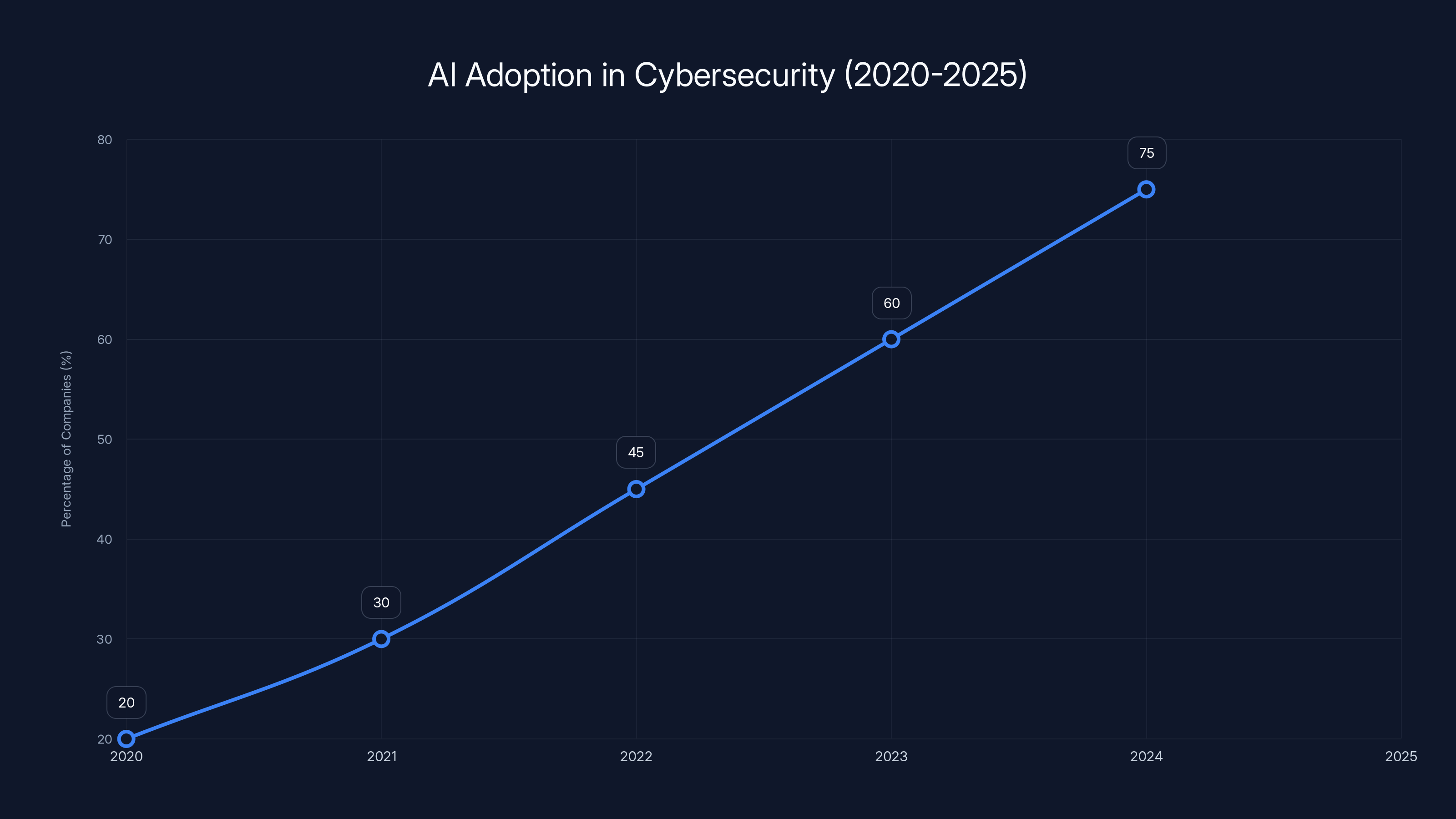
The chart shows a significant increase in AI adoption for cybersecurity, with an estimated rise from 20% in 2020 to 75% by 2025. Estimated data.
Implementing a Comprehensive Security Strategy
Developing a Security-First Culture
Creating a culture that prioritizes security is crucial. This involves training employees on best practices and making security considerations a part of everyday decision-making.
- Security Training Programs: Regular workshops and updates on emerging threats.
- Incident Response Plans: Clearly defined procedures for responding to a breach, minimizing damage, and ensuring continuity.
Leveraging Automation
Automation can streamline security processes, reducing the burden on IT teams and increasing efficiency.
- Automated Patch Management: Ensures systems are up-to-date with the latest security patches without manual intervention.
- Security Information and Event Management (SIEM): Aggregates data from across the network for centralized monitoring and analysis.
Overcoming Common Cybersecurity Challenges
Balancing Security and Usability
One of the key challenges in cybersecurity is maintaining a balance between stringent security measures and user experience.
- User-Friendly Authentication: Implementing methods like biometric authentication can enhance security without compromising usability.
- Adaptive Security: Dynamically adjusts security measures based on user behavior and risk levels.
Addressing Insider Threats
Insider threats pose a significant risk, as they involve individuals within the organization who have access to sensitive data.
- User Behavior Analytics (UBA): Monitors user activity for signs of malicious intent.
- Access Reviews: Regularly reviewing and updating user access permissions to ensure they are appropriate.
Conclusion
The Alinto data breach serves as a stark reminder of the critical importance of cybersecurity in today’s digital landscape. By understanding the vulnerabilities that led to the breach and implementing best practices, organizations can better protect themselves against similar threats. As technology continues to evolve, so too must our approaches to safeguarding sensitive data. By fostering a security-first culture and leveraging advancements in AI and automation, enterprises can stay ahead of the ever-changing threat landscape.
Use Case: Securely managing email communications and preventing data breaches with AI-driven solutions.
Try Runable For Free
FAQ
What caused the Alinto data breach?
The breach was caused by an exposed Elasticsearch cluster that lacked proper authentication measures, allowing unauthorized access to sensitive records, as detailed by CyberNews.
How can organizations prevent similar breaches?
Organizations can prevent similar breaches by implementing strict access controls, conducting regular security audits, and encrypting data at rest and in transit, as advised by JD Supra.
What is the role of AI in cybersecurity?
AI plays a crucial role in cybersecurity by automating threat detection and response, helping to identify anomalies and mitigate risks in real-time, as explored by Wiz.
What are some common cybersecurity challenges?
Common challenges include balancing security with usability, managing insider threats, and keeping up with emerging threats and vulnerabilities, as discussed in Industrial Cyber.
What is Zero Trust Architecture?
Zero Trust Architecture is a security model that requires verification for all access requests, assuming that threats could originate both inside and outside the network, as explained by CYFIRMA.
How does cloud security differ from traditional security?
Cloud security involves managing user identities and permissions in a cloud environment, often utilizing tools like IAM and CSPM for continuous compliance and risk management, as noted by The Hacker News.
Why is a security-first culture important?
A security-first culture ensures that security considerations are integrated into everyday decision-making, helping to prevent breaches and minimize damage if they occur, as emphasized by Reuters.
How can automation enhance cybersecurity?
Automation can streamline security processes, such as patch management and centralized monitoring, reducing the burden on IT teams and increasing efficiency, as recommended by JD Supra.
What are the financial implications of a data breach?
Data breaches can result in significant financial costs, including regulatory fines, operational disruptions, and reputational damage, with the average breach costing $4.45 million in 2023, as reported by Reuters.
How can organizations address insider threats?
Organizations can address insider threats by implementing user behavior analytics, conducting regular access reviews, and fostering a culture of security awareness, as outlined by Industrial Cyber.
Key Takeaways
- Data breaches can have severe reputational and financial impacts.
- Implementing robust access controls is critical to preventing unauthorized access.
- AI offers significant advantages in automating threat detection and response.
- Organizations must balance security with usability to maintain efficiency.
- A security-first culture is essential for preventing and mitigating data breaches.
Related Articles
- The Dark Side of Cybersecurity: NHS Scotland Domains and the Hidden Threats [2025]
- How Digital Devices Endanger Our Privacy Rights [2025]
- How Emojis Are Reshaping Cybercrime Tactics: A Deep Dive [2025]
- Understanding the LAPD Data Breach: Lessons in Cybersecurity [2025]
- Politicians Are Spending More Money on Security as They Increasingly Become Targets | WIRED
- Understanding Rowhammer Attacks on Nvidia GPUs and Mitigating Their Risks [2025]
![The Alinto Data Breach: Lessons in Cybersecurity for Enterprises [2025]](https://tryrunable.com/blog/the-alinto-data-breach-lessons-in-cybersecurity-for-enterpri/image-1-1775738082267.jpg)



